一、算法简介
AES是一个分组密码,属于对称密码范畴,AES算法的模块在对称密码领域特别是分组密码领域常有使用。
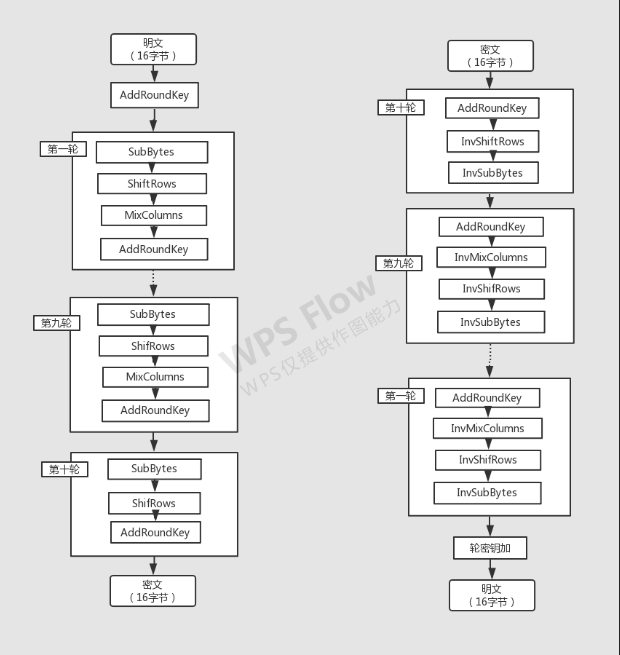
二、算法流程
AES加密算法涉及4种操作:字节替代(SubBytes)、行移位(ShiftRows)、列混淆(MixColumns)和轮密钥加(AddRoundKey)。
加解密中每轮的密钥分别由种子密钥经过密钥扩展算法得到。
算法中16字节的明文、密文和轮子密钥都以一个4x4的矩阵表示。
流程图:
左边加密、右边解密
具体过程:
https://www.cnblogs.com/luop/p/4334160.html
https://www.cnblogs.com/OneFri/p/5924605.html
AES加密算法动画:
https://coolshell.cn/articles/3161.html
加密过程:
///////////加密函数///////////////////////////
unsigned char* AES::Cipher(unsigned char* input)
{
unsigned char state[4][4];
int i,r,c;
////将数组转换为矩阵///////////////////
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
state[r][c] = input[c*4+r];
}
}
AddRoundKey(state,w[0]); ///////////////子密钥相加///////////////////
for(i=1;i<=9;i++){
SubBytes(state);
ShiftRows(state);
MixColumns(state);
AddRoundKey(state,w[i]);
}
SubBytes(state);
ShiftRows(state);
AddRoundKey(state,w[i]);
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
input[c*4+r] = state[r][c];
}
}
return input;
}
1.SubBytes:字节代替
通过S盒完成一个字节到另外一个字节的映射。
代码实现:
//////////////////AES类的构造函数////////////////////////
AES::AES(unsigned char* key)
{
unsigned char sBox[] =
{ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */
0x63,0x7c,0x77,0x7b,0xf2,0x6b,0x6f,0xc5,0x30,0x01,0x67,0x2b,0xfe,0xd7,0xab,0x76, /*0*/
0xca,0x82,0xc9,0x7d,0xfa,0x59,0x47,0xf0,0xad,0xd4,0xa2,0xaf,0x9c,0xa4,0x72,0xc0, /*1*/
0xb7,0xfd,0x93,0x26,0x36,0x3f,0xf7,0xcc,0x34,0xa5,0xe5,0xf1,0x71,0xd8,0x31,0x15, /*2*/
0x04,0xc7,0x23,0xc3,0x18,0x96,0x05,0x9a,0x07,0x12,0x80,0xe2,0xeb,0x27,0xb2,0x75, /*3*/
0x09,0x83,0x2c,0x1a,0x1b,0x6e,0x5a,0xa0,0x52,0x3b,0xd6,0xb3,0x29,0xe3,0x2f,0x84, /*4*/
0x53,0xd1,0x00,0xed,0x20,0xfc,0xb1,0x5b,0x6a,0xcb,0xbe,0x39,0x4a,0x4c,0x58,0xcf, /*5*/
0xd0,0xef,0xaa,0xfb,0x43,0x4d,0x33,0x85,0x45,0xf9,0x02,0x7f,0x50,0x3c,0x9f,0xa8, /*6*/
0x51,0xa3,0x40,0x8f,0x92,0x9d,0x38,0xf5,0xbc,0xb6,0xda,0x21,0x10,0xff,0xf3,0xd2, /*7*/
0xcd,0x0c,0x13,0xec,0x5f,0x97,0x44,0x17,0xc4,0xa7,0x7e,0x3d,0x64,0x5d,0x19,0x73, /*8*/
0x60,0x81,0x4f,0xdc,0x22,0x2a,0x90,0x88,0x46,0xee,0xb8,0x14,0xde,0x5e,0x0b,0xdb, /*9*/
0xe0,0x32,0x3a,0x0a,0x49,0x06,0x24,0x5c,0xc2,0xd3,0xac,0x62,0x91,0x95,0xe4,0x79, /*a*/
0xe7,0xc8,0x37,0x6d,0x8d,0xd5,0x4e,0xa9,0x6c,0x56,0xf4,0xea,0x65,0x7a,0xae,0x08, /*b*/
0xba,0x78,0x25,0x2e,0x1c,0xa6,0xb4,0xc6,0xe8,0xdd,0x74,0x1f,0x4b,0xbd,0x8b,0x8a, /*c*/
0x70,0x3e,0xb5,0x66,0x48,0x03,0xf6,0x0e,0x61,0x35,0x57,0xb9,0x86,0xc1,0x1d,0x9e, /*d*/
0xe1,0xf8,0x98,0x11,0x69,0xd9,0x8e,0x94,0x9b,0x1e,0x87,0xe9,0xce,0x55,0x28,0xdf, /*e*/
0x8c,0xa1,0x89,0x0d,0xbf,0xe6,0x42,0x68,0x41,0x99,0x2d,0x0f,0xb0,0x54,0xbb,0x16 /*f*/
};
//////////////////AES类的析构函数////////////////////////
unsigned char invsBox[256] =
{ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */
0x52,0x09,0x6a,0xd5,0x30,0x36,0xa5,0x38,0xbf,0x40,0xa3,0x9e,0x81,0xf3,0xd7,0xfb, /*0*/
0x7c,0xe3,0x39,0x82,0x9b,0x2f,0xff,0x87,0x34,0x8e,0x43,0x44,0xc4,0xde,0xe9,0xcb, /*1*/
0x54,0x7b,0x94,0x32,0xa6,0xc2,0x23,0x3d,0xee,0x4c,0x95,0x0b,0x42,0xfa,0xc3,0x4e, /*2*/
0x08,0x2e,0xa1,0x66,0x28,0xd9,0x24,0xb2,0x76,0x5b,0xa2,0x49,0x6d,0x8b,0xd1,0x25, /*3*/
0x72,0xf8,0xf6,0x64,0x86,0x68,0x98,0x16,0xd4,0xa4,0x5c,0xcc,0x5d,0x65,0xb6,0x92, /*4*/
0x6c,0x70,0x48,0x50,0xfd,0xed,0xb9,0xda,0x5e,0x15,0x46,0x57,0xa7,0x8d,0x9d,0x84, /*5*/
0x90,0xd8,0xab,0x00,0x8c,0xbc,0xd3,0x0a,0xf7,0xe4,0x58,0x05,0xb8,0xb3,0x45,0x06, /*6*/
0xd0,0x2c,0x1e,0x8f,0xca,0x3f,0x0f,0x02,0xc1,0xaf,0xbd,0x03,0x01,0x13,0x8a,0x6b, /*7*/
0x3a,0x91,0x11,0x41,0x4f,0x67,0xdc,0xea,0x97,0xf2,0xcf,0xce,0xf0,0xb4,0xe6,0x73, /*8*/
0x96,0xac,0x74,0x22,0xe7,0xad,0x35,0x85,0xe2,0xf9,0x37,0xe8,0x1c,0x75,0xdf,0x6e, /*9*/
0x47,0xf1,0x1a,0x71,0x1d,0x29,0xc5,0x89,0x6f,0xb7,0x62,0x0e,0xaa,0x18,0xbe,0x1b, /*a*/
0xfc,0x56,0x3e,0x4b,0xc6,0xd2,0x79,0x20,0x9a,0xdb,0xc0,0xfe,0x78,0xcd,0x5a,0xf4, /*b*/
0x1f,0xdd,0xa8,0x33,0x88,0x07,0xc7,0x31,0xb1,0x12,0x10,0x59,0x27,0x80,0xec,0x5f, /*c*/
0x60,0x51,0x7f,0xa9,0x19,0xb5,0x4a,0x0d,0x2d,0xe5,0x7a,0x9f,0x93,0xc9,0x9c,0xef, /*d*/
0xa0,0xe0,0x3b,0x4d,0xae,0x2a,0xf5,0xb0,0xc8,0xeb,0xbb,0x3c,0x83,0x53,0x99,0x61, /*e*/
0x17,0x2b,0x04,0x7e,0xba,0x77,0xd6,0x26,0xe1,0x69,0x14,0x63,0x55,0x21,0x0c,0x7d /*f*/
};
memcpy(Sbox, sBox, 256);
memcpy(InvSbox, invsBox, 256);
KeyExpansion(key, w);
}
///////////////字节替换//////////////////////
void AES::SubBytes(unsigned char state[][4])
{
int r,c;
for(r=0; r<4; r++)
{
for(c=0; c<4; c++)
{
state[r][c] = Sbox[state[r][c]];
}
}
}
2.ShiftRows:行位移
是一个4x4的矩阵内部字节之间的置换,用于提供算法的扩散性。
代码实现:
/////////////////////行位移//////////////////
void AES::ShiftRows(unsigned char state[][4])
{
unsigned char t[4];
int r,c;
for(r=1; r<4; r++)
{
for(c=0; c<4; c++)
{
t[c] = state[r][(c+r)%4];
}
for(c=0; c<4; c++)
{
state[r][c] = t[c];
}
}
}
3.MixCloumns: 列混淆
利用GF(28)域上算术特性的一个代替,同样用于提供算法的扩散性。
////////////////伽罗华域内的两个字符做乘法运算///////////////
unsigned char AES::FFmul(unsigned char a, unsigned char b)
{
unsigned char bw[4];
unsigned char res=0;
int i;
bw[0] = b;
for(i=1; i<4; i++)
{
bw[i] = bw[i-1]<<1;
if(bw[i-1]&0x80)
{
bw[i]^=0x1b;
}
}
for(i=0; i<4; i++)
{
if((a>>i)&0x01)
{
res ^= bw[i];
}
}
return res;
}
/////////////////////列混合///////////////////
void AES::MixColumns(unsigned char state[][4])
{
unsigned char t[4];
int r,c;
for(c=0; c< 4; c++)
{
for(r=0; r<4; r++)
{
t[r] = state[r][c];
}
for(r=0; r<4; r++)
{
state[r][c] = FFmul(0x02, t[r])
^ FFmul(0x03, t[(r+1)%4])
^ FFmul(0x01, t[(r+2)%4])
^ FFmul(0x01, t[(r+3)%4]);
}
}
}
4.AddRoundKey: 轮秘钥加
其依据的原理是“任何数和自身的异或结果为0”。加密过程中,每轮的输入与轮子密钥异或一次;因此,解密时再异或上该轮的轮子密钥即可恢复。
代码实现:
////////////////////////密钥扩展///////////////////////////
void AES::KeyExpansion(unsigned char* key, unsigned char w[][4][4])
{
int i,j,r,c;
unsigned char rc[] = {0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1b, 0x36};
for(r=0; r<4; r++)
{
for(c=0; c<4; c++)
{
w[0][r][c] = key[r+c*4];
}
}
for(i=1; i<=10; i++)
{
for(j=0; j<4; j++)
{
unsigned char t[4];
for(r=0; r<4; r++)
{
t[r] = j ? w[i][r][j-1] : w[i-1][r][3];
}
if(j == 0)
{
unsigned char temp = t[0];
for(r=0; r<3; r++)
{
t[r] = Sbox[t[(r+1)%4]];
}
t[3] = Sbox[temp];
t[0] ^= rc[i-1];
}
for(r=0; r<4; r++)
{
w[i][r][j] = w[i-1][r][j] ^ t[r];
}
}
}
}
//////////////////子密钥相加/////////////////////
void AES::AddRoundKey(unsigned char state[][4], unsigned char k[][4])
{
int r,c;
for(c=0; c<4; c++)
{
for(r=0; r<4; r++)
{
state[r][c] ^= k[r][c];
}
}
}
解密函数
//////////////////////解密函数/////////////////////////
unsigned char* AES::InvCipher(unsigned char* input)
{
unsigned char state[4][4];
int i,r,c;
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
state[r][c] = input[c*4+r];
}
}
AddRoundKey(state, w[10]);
InvShiftRows(state);
InvSubBytes(state);
for(i=9;i>=1;i--){
AddRoundKey(state,w[i]);
InvMixColumns(state);
InvShiftRows(state);
InvSubBytes(state);
}
AddRoundKey(state,w[i]);
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
input[c*4+r] = state[r][c];
}
}
return input;
}
1.InvSubBytes:字节代替
/////////////////字节替换的逆运算////////////////////
void AES::InvSubBytes(unsigned char state[][4])
{
int r,c;
for(r=0; r<4; r++)
{
for(c=0; c<4; c++)
{
state[r][c] = InvSbox[state[r][c]];
}
}
}
2.InvShiftRows:行位移
////////////////////行位移的逆运算///////////////////
void AES::InvShiftRows(unsigned char state[][4])
{
unsigned char t[4];
int r,c;
for(r=1; r<4; r++)
{
for(c=0; c<4; c++)
{
t[c] = state[r][(c-r+4)%4];
}
for(c=0; c<4; c++)
{
state[r][c] = t[c];
}
}
}
3.InvMixCloumns: 列混淆
///////////////////列混合的逆运算///////////////
void AES::InvMixColumns(unsigned char state[][4])
{
unsigned char t[4];
int r,c;
for(c=0; c< 4; c++)
{
for(r=0; r<4; r++)
{
t[r] = state[r][c];
}
for(r=0; r<4; r++)
{
state[r][c] = FFmul(0x0e, t[r])
^ FFmul(0x0b, t[(r+1)%4])
^ FFmul(0x0d, t[(r+2)%4])
^ FFmul(0x09, t[(r+3)%4]);
}
}
}
4.AddRoundKey: 轮秘钥加 同上
三、完整代码
AES.cpp
#include "stdafx.h"
#include "string.h"
#include "AES.h"
//////////////////AES类的构造函数////////////////////////
AES::AES(unsigned char* key)
{
unsigned char sBox[] =
{ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */
0x63,0x7c,0x77,0x7b,0xf2,0x6b,0x6f,0xc5,0x30,0x01,0x67,0x2b,0xfe,0xd7,0xab,0x76, /*0*/
0xca,0x82,0xc9,0x7d,0xfa,0x59,0x47,0xf0,0xad,0xd4,0xa2,0xaf,0x9c,0xa4,0x72,0xc0, /*1*/
0xb7,0xfd,0x93,0x26,0x36,0x3f,0xf7,0xcc,0x34,0xa5,0xe5,0xf1,0x71,0xd8,0x31,0x15, /*2*/
0x04,0xc7,0x23,0xc3,0x18,0x96,0x05,0x9a,0x07,0x12,0x80,0xe2,0xeb,0x27,0xb2,0x75, /*3*/
0x09,0x83,0x2c,0x1a,0x1b,0x6e,0x5a,0xa0,0x52,0x3b,0xd6,0xb3,0x29,0xe3,0x2f,0x84, /*4*/
0x53,0xd1,0x00,0xed,0x20,0xfc,0xb1,0x5b,0x6a,0xcb,0xbe,0x39,0x4a,0x4c,0x58,0xcf, /*5*/
0xd0,0xef,0xaa,0xfb,0x43,0x4d,0x33,0x85,0x45,0xf9,0x02,0x7f,0x50,0x3c,0x9f,0xa8, /*6*/
0x51,0xa3,0x40,0x8f,0x92,0x9d,0x38,0xf5,0xbc,0xb6,0xda,0x21,0x10,0xff,0xf3,0xd2, /*7*/
0xcd,0x0c,0x13,0xec,0x5f,0x97,0x44,0x17,0xc4,0xa7,0x7e,0x3d,0x64,0x5d,0x19,0x73, /*8*/
0x60,0x81,0x4f,0xdc,0x22,0x2a,0x90,0x88,0x46,0xee,0xb8,0x14,0xde,0x5e,0x0b,0xdb, /*9*/
0xe0,0x32,0x3a,0x0a,0x49,0x06,0x24,0x5c,0xc2,0xd3,0xac,0x62,0x91,0x95,0xe4,0x79, /*a*/
0xe7,0xc8,0x37,0x6d,0x8d,0xd5,0x4e,0xa9,0x6c,0x56,0xf4,0xea,0x65,0x7a,0xae,0x08, /*b*/
0xba,0x78,0x25,0x2e,0x1c,0xa6,0xb4,0xc6,0xe8,0xdd,0x74,0x1f,0x4b,0xbd,0x8b,0x8a, /*c*/
0x70,0x3e,0xb5,0x66,0x48,0x03,0xf6,0x0e,0x61,0x35,0x57,0xb9,0x86,0xc1,0x1d,0x9e, /*d*/
0xe1,0xf8,0x98,0x11,0x69,0xd9,0x8e,0x94,0x9b,0x1e,0x87,0xe9,0xce,0x55,0x28,0xdf, /*e*/
0x8c,0xa1,0x89,0x0d,0xbf,0xe6,0x42,0x68,0x41,0x99,0x2d,0x0f,0xb0,0x54,0xbb,0x16 /*f*/
};
//////////////////AES类的析构函数////////////////////////
unsigned char invsBox[256] =
{ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */
0x52,0x09,0x6a,0xd5,0x30,0x36,0xa5,0x38,0xbf,0x40,0xa3,0x9e,0x81,0xf3,0xd7,0xfb, /*0*/
0x7c,0xe3,0x39,0x82,0x9b,0x2f,0xff,0x87,0x34,0x8e,0x43,0x44,0xc4,0xde,0xe9,0xcb, /*1*/
0x54,0x7b,0x94,0x32,0xa6,0xc2,0x23,0x3d,0xee,0x4c,0x95,0x0b,0x42,0xfa,0xc3,0x4e, /*2*/
0x08,0x2e,0xa1,0x66,0x28,0xd9,0x24,0xb2,0x76,0x5b,0xa2,0x49,0x6d,0x8b,0xd1,0x25, /*3*/
0x72,0xf8,0xf6,0x64,0x86,0x68,0x98,0x16,0xd4,0xa4,0x5c,0xcc,0x5d,0x65,0xb6,0x92, /*4*/
0x6c,0x70,0x48,0x50,0xfd,0xed,0xb9,0xda,0x5e,0x15,0x46,0x57,0xa7,0x8d,0x9d,0x84, /*5*/
0x90,0xd8,0xab,0x00,0x8c,0xbc,0xd3,0x0a,0xf7,0xe4,0x58,0x05,0xb8,0xb3,0x45,0x06, /*6*/
0xd0,0x2c,0x1e,0x8f,0xca,0x3f,0x0f,0x02,0xc1,0xaf,0xbd,0x03,0x01,0x13,0x8a,0x6b, /*7*/
0x3a,0x91,0x11,0x41,0x4f,0x67,0xdc,0xea,0x97,0xf2,0xcf,0xce,0xf0,0xb4,0xe6,0x73, /*8*/
0x96,0xac,0x74,0x22,0xe7,0xad,0x35,0x85,0xe2,0xf9,0x37,0xe8,0x1c,0x75,0xdf,0x6e, /*9*/
0x47,0xf1,0x1a,0x71,0x1d,0x29,0xc5,0x89,0x6f,0xb7,0x62,0x0e,0xaa,0x18,0xbe,0x1b, /*a*/
0xfc,0x56,0x3e,0x4b,0xc6,0xd2,0x79,0x20,0x9a,0xdb,0xc0,0xfe,0x78,0xcd,0x5a,0xf4, /*b*/
0x1f,0xdd,0xa8,0x33,0x88,0x07,0xc7,0x31,0xb1,0x12,0x10,0x59,0x27,0x80,0xec,0x5f, /*c*/
0x60,0x51,0x7f,0xa9,0x19,0xb5,0x4a,0x0d,0x2d,0xe5,0x7a,0x9f,0x93,0xc9,0x9c,0xef, /*d*/
0xa0,0xe0,0x3b,0x4d,0xae,0x2a,0xf5,0xb0,0xc8,0xeb,0xbb,0x3c,0x83,0x53,0x99,0x61, /*e*/
0x17,0x2b,0x04,0x7e,0xba,0x77,0xd6,0x26,0xe1,0x69,0x14,0x63,0x55,0x21,0x0c,0x7d /*f*/
};
memcpy(Sbox, sBox, 256);
memcpy(InvSbox, invsBox, 256);
KeyExpansion(key, w);
}
AES::~AES()
{
}
///////////加密函数///////////////////////////
unsigned char* AES::Cipher(unsigned char* input)
{
unsigned char state[4][4];
int i,r,c;
////将数组转换为矩阵///////////////////
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
state[r][c] = input[c*4+r];
}
}
AddRoundKey(state,w[0]); ///////////////子密钥相加///////////////////
for(i=1;i<=9;i++){
SubBytes(state);
ShiftRows(state);
MixColumns(state);
AddRoundKey(state,w[i]);
}
SubBytes(state);
ShiftRows(state);
AddRoundKey(state,w[i]);
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
input[c*4+r] = state[r][c];
}
}
return input;
}
//////////////////////解密函数/////////////////////////
unsigned char* AES::InvCipher(unsigned char* input)
{
unsigned char state[4][4];
int i,r,c;
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
state[r][c] = input[c*4+r];
}
}
AddRoundKey(state, w[10]);
InvShiftRows(state);
InvSubBytes(state);
for(i=9;i>=1;i--){
AddRoundKey(state,w[i]);
InvMixColumns(state);
InvShiftRows(state);
InvSubBytes(state);
}
AddRoundKey(state,w[i]);
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
input[c*4+r] = state[r][c];
}
}
return input;
}
/////////////////对明文进行分组加密////////////////
void* AES::Cipher(void* input, int length)
{
unsigned char* in = (unsigned char*) input;
int i;
if(!length)
{
while(*(in+length++));
in = (unsigned char*) input;
}
for(i=0; i<length; i+=16)
{
Cipher(in+i);
}
return input;
}
////////////////////对密文进行分组解密/////////////////////
void* AES::InvCipher(void* input, int length)
{
unsigned char* in = (unsigned char*) input;
int i;
for(i=0; i<length; i+=16)
{
InvCipher(in+i);
}
return input;
}
////////////////////////密钥扩展///////////////////////////
void AES::KeyExpansion(unsigned char* key, unsigned char w[][4][4])
{
int i,j,r,c;
unsigned char rc[] = {0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1b, 0x36};
for(r=0; r<4; r++)
{
for(c=0; c<4; c++)
{
w[0][r][c] = key[r+c*4];
}
}
for(i=1; i<=10; i++)
{
for(j=0; j<4; j++)
{
unsigned char t[4];
for(r=0; r<4; r++)
{
t[r] = j ? w[i][r][j-1] : w[i-1][r][3];
}
if(j == 0)
{
unsigned char temp = t[0];
for(r=0; r<3; r++)
{
t[r] = Sbox[t[(r+1)%4]];
}
t[3] = Sbox[temp];
t[0] ^= rc[i-1];
}
for(r=0; r<4; r++)
{
w[i][r][j] = w[i-1][r][j] ^ t[r];
}
}
}
}
////////////////伽罗华域内的两个字符做乘法运算///////////////
unsigned char AES::FFmul(unsigned char a, unsigned char b)
{
unsigned char bw[4];
unsigned char res=0;
int i;
bw[0] = b;
for(i=1; i<4; i++)
{
bw[i] = bw[i-1]<<1;
if(bw[i-1]&0x80)
{
bw[i]^=0x1b;
}
}
for(i=0; i<4; i++)
{
if((a>>i)&0x01)
{
res ^= bw[i];
}
}
return res;
}
///////////////字节替换//////////////////////
void AES::SubBytes(unsigned char state[][4])
{
int r,c;
for(r=0; r<4; r++)
{
for(c=0; c<4; c++)
{
state[r][c] = Sbox[state[r][c]];
}
}
}
/////////////////////行位移//////////////////
void AES::ShiftRows(unsigned char state[][4])
{
unsigned char t[4];
int r,c;
for(r=1; r<4; r++)
{
for(c=0; c<4; c++)
{
t[c] = state[r][(c+r)%4];
}
for(c=0; c<4; c++)
{
state[r][c] = t[c];
}
}
}
/////////////////////列混合///////////////////
void AES::MixColumns(unsigned char state[][4])
{
unsigned char t[4];
int r,c;
for(c=0; c< 4; c++)
{
for(r=0; r<4; r++)
{
t[r] = state[r][c];
}
for(r=0; r<4; r++)
{
state[r][c] = FFmul(0x02, t[r])
^ FFmul(0x03, t[(r+1)%4])
^ FFmul(0x01, t[(r+2)%4])
^ FFmul(0x01, t[(r+3)%4]);
}
}
}
//////////////////子密钥相加/////////////////////
void AES::AddRoundKey(unsigned char state[][4], unsigned char k[][4])
{
int r,c;
for(c=0; c<4; c++)
{
for(r=0; r<4; r++)
{
state[r][c] ^= k[r][c];
}
}
}
/////////////////字节替换的逆运算////////////////////
void AES::InvSubBytes(unsigned char state[][4])
{
int r,c;
for(r=0; r<4; r++)
{
for(c=0; c<4; c++)
{
state[r][c] = InvSbox[state[r][c]];
}
}
}
////////////////////行位移的逆运算///////////////////
void AES::InvShiftRows(unsigned char state[][4])
{
unsigned char t[4];
int r,c;
for(r=1; r<4; r++)
{
for(c=0; c<4; c++)
{
t[c] = state[r][(c-r+4)%4];
}
for(c=0; c<4; c++)
{
state[r][c] = t[c];
}
}
}
///////////////////列混合的逆运算///////////////
void AES::InvMixColumns(unsigned char state[][4])
{
unsigned char t[4];
int r,c;
for(c=0; c< 4; c++)
{
for(r=0; r<4; r++)
{
t[r] = state[r][c];
}
for(r=0; r<4; r++)
{
state[r][c] = FFmul(0x0e, t[r])
^ FFmul(0x0b, t[(r+1)%4])
^ FFmul(0x0d, t[(r+2)%4])
^ FFmul(0x09, t[(r+3)%4]);
}
}
}
void print(unsigned char* state)
{
int i;
for(i=0; i<16; i++)
{
printf("%s%X ",state[i]>15 ? "" : "0", state[i]);
}
printf("
");
}
int main(int argc, char* argv[])
{
// unsigned char input[] =
// {
// 0x19, 0xa0, 0x9a, 0xe9,
// 0x3d, 0xf4, 0xc6, 0xf8,
// 0xe3, 0xe2, 0x8d, 0x48,
// 0xbe, 0x2b, 0x2a, 0x08
// };
//
//
//
// unsigned char key[] =
// {
// 0x2b, 0x28, 0xab, 0x09,
// 0x7e, 0xae, 0xf7, 0xcf,
// 0x15, 0xd2, 0x15, 0xef,
// 0x16, 0xa6, 0x88, 0x3c
// };
//
unsigned char input[] =
{
0x32, 0x43, 0xf6, 0xa8,
0x88, 0x5a, 0x30, 0x8d,
0x31, 0x31, 0x98, 0xa2,
0xe0, 0x37, 0x07, 0x34
};
unsigned char key[] =
{
0x2b, 0x7e, 0x15, 0x16,
0x28, 0xae, 0xd2, 0xa6,
0xab, 0xf7, 0x15, 0x88,
0x09, 0xcf, 0x4f, 0x3c
};
AES aes(key);
printf("Input:
");
print(input);
aes.Cipher(input);
printf("After Cipher:
");
print(input);
aes.InvCipher(input);
printf("After InvCipher:
");
print(input);
return 0;
}
AES.h
///////////////////////////////
// http://mingcn.cnblogs.com //
// xelz CopyRight (c) 2010 //
///////////////////////////////
#if !defined(AFX_AES_H__6BDD3760_BDE8_4C42_85EE_6F7A434B81C4__INCLUDED_)
#define AFX_AES_H__6BDD3760_BDE8_4C42_85EE_6F7A434B81C4__INCLUDED_
#if _MSC_VER > 1000
#pragma once
#endif // _MSC_VER > 1000
#include "stdafx.h"
class AES
{
public:
AES(unsigned char* key);
virtual ~AES();
unsigned char* Cipher(unsigned char* input);
unsigned char* InvCipher(unsigned char* input);
void* Cipher(void* input, int length=0);
void* InvCipher(void* input, int length);
private:
unsigned char Sbox[256];
unsigned char InvSbox[256];
unsigned char w[11][4][4];
void KeyExpansion(unsigned char* key, unsigned char w[][4][4]);
unsigned char FFmul(unsigned char a, unsigned char b);
void SubBytes(unsigned char state[][4]);
void ShiftRows(unsigned char state[][4]);
void MixColumns(unsigned char state[][4]);
void AddRoundKey(unsigned char state[][4], unsigned char k[][4]);
void InvSubBytes(unsigned char state[][4]);
void InvShiftRows(unsigned char state[][4]);
void InvMixColumns(unsigned char state[][4]);
};
#endif // !defined(AFX_AES_H__6BDD3760_BDE8_4C42_85EE_6F7A434B81C4__INCLUDED_)
StdAfx.h
// stdafx.h : include file for standard system include files,
// or project specific include files that are used frequently, but
// are changed infrequently
//
#if !defined(AFX_STDAFX_H__B4FEAA5A_7DE2_4988_9BAB_65CC27882DE5__INCLUDED_)
#define AFX_STDAFX_H__B4FEAA5A_7DE2_4988_9BAB_65CC27882DE5__INCLUDED_
#if _MSC_VER > 1000
#pragma once
#endif // _MSC_VER > 1000
#define WIN32_LEAN_AND_MEAN // Exclude rarely-used stuff from Windows headers
#include <stdio.h>
// TODO: reference additional headers your program requires here
//{{AFX_INSERT_LOCATION}}
// Microsoft Visual C++ will insert additional declarations immediately before the previous line.
#endif // !defined(AFX_STDAFX_H__B4FEAA5A_7DE2_4988_9BAB_65CC27882DE5__INCLUDED_)
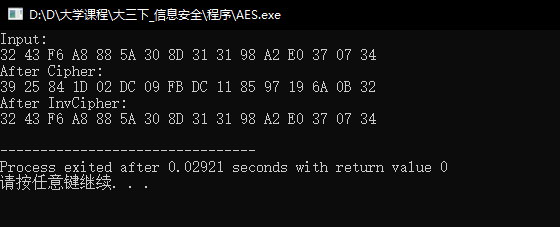
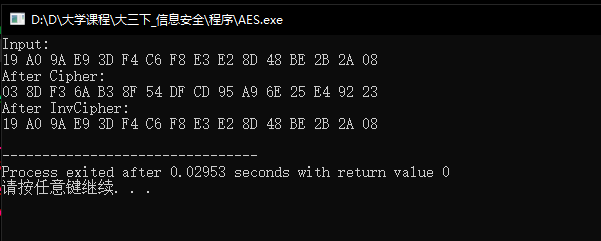
运行结果截图: