CA认证中心简述
CA :CertificateAuthority的缩写,通常翻译成认证权威或者认证中心,主要用途是为用户发放数字证书
功能:证书发放、证书更新、证书撤销和证书验证。
作用:身份认证,数据的不可否认性
端口:443
证书请求文件:CSR是Cerificate Signing Request的英文缩写,即证书请求文件,也就是证书申请者在申请数字证书时由CSP(加密服务提供者)在生成私钥的同时也生成证书请求文件,证书申请者只要把CSR文件提交给证书颁发机构后,证书颁发机构使用其根证书的私钥签名就生成了证书文件,也就是颁发给用户的证书
一:搭建CA认证中心
配置一个自己的CA认证中心
[root@ca ~]# vim /etc/pki/tls/openssl.cnf +172 basicConstraints=CA:FALSE # 把FALSE改成TRUE 把本机变成CA认证中心
配置认证中心,生成私钥与根证书
[root@ca ~]# /etc/pki/tls/misc/CA -newca

这里配置了CA认证中心 ,在里面就生成了CA认证根证书的私钥 ,在配置完结束之后 ,就会生成一个根证书,这个根证书中有这证书的公钥
到此CA认证中心就搭建好了
查看生成的CA根证书 :
[root@ca ~]# vim /etc/pki/CA/cacert.pem Certificate: Data: Version: 3 (0x2) Serial Number: d5:bc:ed:54:bb:7c:a9:3b Signature Algorithm: sha256WithRSAEncryption Issuer: C=CN, ST=beijing, O=IT, OU=IT-OPS, CN=damowang.cn/emailAddress=damowang.cn@gmail.com # 上面是CA认证中心信息
Validity Not Before: Aug 6 14:53:14 2018 GMT Not After : Aug 5 14:53:14 2021 GMT Subject: C=CN, ST=beijing, O=IT, OU=IT-OPS, CN=damowang.cn/emailAddress=damowang.cn@gmail.com Subject Public Key Info: # CA认证中心公钥信息 Public Key Algorithm: rsaEncryption Public-Key: (2048 bit) Modulus: 00:bc:f2:4e:b3:ac:cf:ec:c7:6c:9a:7f:25:8f:ab: bc:b0:2f:b6:36:a7:cd:26:82:a6:47:f3:92:3a:88: 8c:d5:88:44:3a:94:27:da:9f:ae:5d:b0:c1:34:3e: 8f:9e:37:10:2b:65:b5:40:d3:8e:c0:de:54:7d:e2: 24:15:07:6c:bf:b2:21:dc:16:30:b0:a5:2e:54:a4: 43:86:68:00:6e:df:f7:8e:3a:d5:ab:df:cb:5b:23: ee:a4:e9:e6:6c:ae:97:70:d2:a0:08:db:b7:17:23: f5:0e:30:3f:8c:a6:e8:08:5b:a1:01:da:1a:ec:18: 18:31:51:10:14:9e:dd:f0:3e:72:ea:a1:ff:54:47: c0:b1:03:30:5f:38:6e:31:c4:8d:e5:a2:b4:32:ff: 6d:b3:2b:db:60:42:fa:a6:72:d5:72:ec:ba:18:d4: f3:40:72:e9:16:c0:ba:f4:5b:20:e5:f5:f7:85:52: dc:01:bc:61:6b:2b:0e:40:39:84:45:3c:2a:37:a0: 69:38:92:77:af:ee:76:d5:3b:70:cc:34:cd:b2:ab: fa:79:5d:78:eb:8a:e5:3c:94:a2:3b:e3:8b:d0:97: 6e:54:85:0d:dd:6b:12:e4:75:82:5d:bc:16:da:4b: 4f:d2:c8:66:76:c6:c3:b8:b5:eb:e3:ff:69:f5:95: 60:ed Exponent: 65537 (0x10001) X509v3 extensions: X509v3 Subject Key Identifier: 89:51:C9:B3:C1:BF:F9:4D:D4:51:73:BC:9B:A5:C0:CC:6B:D9:5D:BD X509v3 Authority Key Identifier: keyid:89:51:C9:B3:C1:BF:F9:4D:D4:51:73:BC:9B:A5:C0:CC:6B:D9:5D:BD X509v3 Basic Constraints: CA:TRUE Signature Algorithm: sha256WithRSAEncryption 90:f7:14:3b:32:31:62:88:2e:ad:f6:af:27:4c:8b:52:ac:03: 98:8d:47:8b:48:6a:b8:1e:60:b0:5d:c1:ee:d2:c6:a6:1e:57: 4d:64:b6:65:2e:c3:81:a4:f0:f9:9e:d4:2f:c2:39:18:83:5e: b3:70:84:91:b4:93:1f:3d:cb:d7:2f:f8:76:6e:a5:8a:e6:f6: 8f:00:aa:4b:9a:84:b5:0e:db:52:19:0b:8a:9b:2b:59:6d:20: c0:42:8f:cd:85:85:09:78:d5:4f:4f:8e:eb:7a:23:2c:03:59: 8e:36:1c:11:3a:e8:26:b4:2e:45:4a:a4:45:1a:50:8d:17:d9: b5:6e:66:87:66:99:36:71:48:a4:ac:1b:68:dd:39:14:6f:8b: a9:ff:d4:d2:7e:9c:8f:4a:c7:40:e7:13:2b:32:89:88:5f:83: 6c:98:2d:b5:a7:1d:0c:f1:a2:d8:93:2c:70:84:00:3c:01:9c: 20:d4:1a:d1:7b:a3:7f:f6:66:77:e3:27:f1:7e:43:54:af:90: 2b:87:6d:cb:af:d0:43:ad:e4:80:1c:ee:b9:22:d8:74:38:24: 7b:30:ba:11:ac:14:f1:02:c0:12:2e:16:53:dd:95:7b:58:8f: 52:74:38:66:b3:a4:20:70:b9:27:ef:0b:49:7f:26:95:bf:2f: 63:01:9b:d6 -----BEGIN CERTIFICATE----- MIIDxTCCAq2gAwIBAgIJANW87VS7fKk7MA0GCSqGSIb3DQEBCwUAMHkxCzAJBgNV BAYTAkNOMRAwDgYDVQQIDAdiZWlqaW5nMQswCQYDVQQKDAJJVDEPMA0GA1UECwwG SVQtT1BTMRQwEgYDVQQDDAtkYW1vd2FuZy5jbjEkMCIGCSqGSIb3DQEJARYVZGFt b3dhbmcuY25AZ21haWwuY29tMB4XDTE4MDgwNjE0NTMxNFoXDTIxMDgwNTE0NTMx NFoweTELMAkGA1UEBhMCQ04xEDAOBgNVBAgMB2JlaWppbmcxCzAJBgNVBAoMAklU MQ8wDQYDVQQLDAZJVC1PUFMxFDASBgNVBAMMC2RhbW93YW5nLmNuMSQwIgYJKoZI hvcNAQkBFhVkYW1vd2FuZy5jbkBnbWFpbC5jb20wggEiMA0GCSqGSIb3DQEBAQUA A4IBDwAwggEKAoIBAQC88k6zrM/sx2yafyWPq7ywL7Y2p80mgqZH85I6iIzViEQ6 lCfan65dsME0Po+eNxArZbVA047A3lR94iQVB2y/siHcFjCwpS5UpEOGaABu3/eO OtWr38tbI+6k6eZsrpdw0qAI27cXI/UOMD+MpugIW6EB2hrsGBgxURAUnt3wPnLq of9UR8CxAzBfOG4xxI3lorQy/22zK9tgQvqmctVy7LoY1PNAcukWwLr0WyDl9feF UtwBvGFrKw5AOYRFPCo3oGk4knev7nbVO3DMNM2yq/p5XXjriuU8lKI744vQl25U hQ3daxLkdYJdvBbaS0/SyGZ2xsO4tevj/2n1lWDtAgMBAAGjUDBOMB0GA1UdDgQW BBSJUcmzwb/5TdRRc7ybpcDMa9ldvTAfBgNVHSMEGDAWgBSJUcmzwb/5TdRRc7yb pcDMa9ldvTAMBgNVHRMEBTADAQH/MA0GCSqGSIb3DQEBCwUAA4IBAQCQ9xQ7MjFi iC6t9q8nTItSrAOYjUeLSGq4HmCwXcHu0samHldNZLZlLsOBpPD5ntQvwjkYg16z cISRtJMfPcvXL/h2bqWK5vaPAKpLmoS1DttSGQuKmytZbSDAQo/NhYUJeNVPT47r eiMsA1mONhwROugmtC5FSqRFGlCNF9m1bmaHZpk2cUikrBto3TkUb4up/9TSfpyP SsdA5xMrMomIX4NsmC21px0M8aLYkyxwhAA8AZwg1BrRe6N/9mZ34yfxfkNUr5Ar h23Lr9BDreSAHO65Ith0OCR7MLoRrBTxAsASLhZT3ZV7WI9SdDhms6QgcLkn7wtJ fyaVvy9jAZvW -----END CERTIFICATE-----
查看根证书的私钥 :
[root@ca ~]# vim /etc/pki/CA/private/cakey.pem # CA认证下根证书的私钥 -----BEGIN ENCRYPTED PRIVATE KEY----- MIIFDjBABgkqhkiG9w0BBQ0wMzAbBgkqhkiG9w0BBQwwDgQInT7FONSpFscCAggA MBQGCCqGSIb3DQMHBAi1VvUPV2DgKwSCBMjHCgsNdj+BrCSvkFaHtX6iGaitR7WJ bBEWrarlcGGVdAHYW6Hwpb548FXXLhXagTcU1gj6EP8ylJ5+ZsQtXM6B/HlzX+c6 TKTdS4QBotFUqb2BRZkN0Une4k17RxDNW6Por4OEEk4hs6xpr0up5ihV5L2H3JWw Q+9zL8SUflXBXOsrdPFKzs5iE8u7zJgff1xR9W11IEXBs3ScqRQ6iuFJjebAam+7 BkHkpXeV0hOp7BjjJKMUg9wUAy7ar7kVJnGR5rq5FAD1r786J01jmc6V+yRkiL8g l6wrTOyVvunt+9qc+f7YkjwN9TZ1Fb4pTCIjbtziKmkrHKy/xQX3hMICgQbwMuFz /QlOWBrBTv14nyZpfg3UlFo1PacAG7l5prLO34K/6KqnvVSMFRw0m513eWVs5FUf 2DVjIqDhBVxnxRaX+S+FWjoGsptXpXNKExqhlGkbv/bZqLbBA0crotXKgG1I7qqI zSrKKynqjf1MUF7z2bt4AsAdpJgdRRT94+lKRxqrnCVnhF76KXEpAO98DNLVHMk9 xRI7xTKv32GnSgE5YraYBLoCXrhGoqM/6eMy70mAWleRE6JId/9ZiPQO23cme8rJ zzjAFgH9AtewXc4crG2yfVtqZ0pxJBfY9b20E730x5enIOjNEQ1cWAT4yk0KkliJ dv4lq9xwBQnvsPIs3hAI4JEDMrf+VQohhZ/EO5puAoSopAKppdJAq8Mt5RuXgEqT n3sd1WV6i/Crszvyjdhsdpms3HECpV2FDQyheGN1Ms7Evl4+T2LMjQSvimLRaM4G kxg+a/AqGgmTkxXh5mOAO4/jhNIr/xFTA6FjlEtzVMbqBOFFmWnOlmbr6Ik/iDxn AD2Ebqeoyj3t/q+najLHFBANOtboOISgCQFWqgIWNW5W2wdCTHVDqf/18v2eMKXo IYiNV3IwuzzXud2iFAsLnx1i136BwPXJr0Q2BxfI5k9+7JcPVKvtf8rzjes1a89j cnbepAepeHXCm8JFAQIFrWJI5FaInXf+kTlr/HrFlI7XxNTk49EugAq702EE75rZ EAenZrEj0dV4uOay+p+ay3mK6774FO5RxM6oZWzjbmydtTcXjrqqRqJn5WDjREfB XrsQnCbMPoHaCrrUpZOIyZJu6wNgAdiXI0CkPfWBAXHireBMzmS6iICE3C5dZ3k+ XoXiglggCuGw4M/cIdOOOPKFetrMe541k6w+p1ZQrK1jxJfKOb7xaR1a4CBzLh5s amt6sDqr2AR60e7uBpr8R2FKmKtj8AVVL4UZFvxiU532vMB4zWjsvjluXdCXTzzp Wzzw6TXs+pQvYRnJNqqTu6tUZtmZiA+RFlfmyi0wfV5MbL6UOE4SNQuMJCFGiXE4 gj2zKhb4jP/zgDEeppaE/RqAQ14zu0keTEp8srnZUrMakcBjSrX6mSdHddjtHOHJ k2bjsGJp7Iakx5H90UAQ4J5sgQ2cejpgTPpnEeLaij6iKz7Do4+IC5Lk8KkDsCYn VuMtxid3J8MTmTkRdpJCRK6KJNtf23AS1Uovxvek7Yg67PtKiAI55uXfLXdvxdfH DpT+LpxGGi1dYB7Y2kA61H8d3tFLcs8istSezdlTwVY6e+aE2Q6B+BOINECGRCSY jCM= -----END ENCRYPTED PRIVATE KEY-----
二:使用证书搭建https
1、安装httpd :
[root@client ~]# yum -y install httpd [root@client ~]# vim /etc/httpd/conf/httpd.conf // 把 #ServerName www.example.com:80 改成 ServerName 192.168.94.111:80 [root@client ~]# systemctl start httpd
2、client 生成证书请求文件
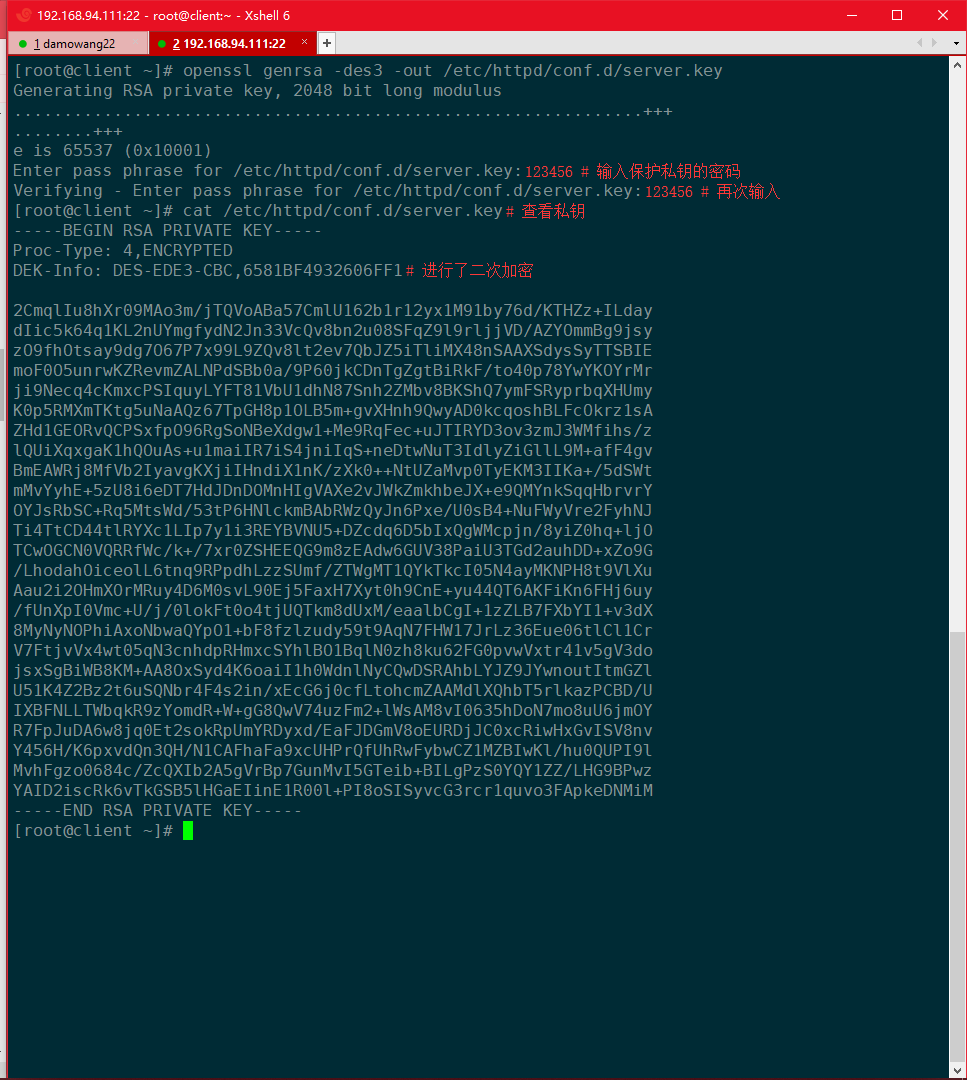
生一个私钥密钥 :
[root@client ~]# openssl genrsa -des3 -out /etc/httpd/conf.d/server.key
生成请求文件 :
[root@client ~]# openssl req -new -key /etc/httpd/conf.d/server.key -out /server.csr
# 注意后期添加的国家,省,城市等信息要和CA保持一致

3、将证书请求文件发给CA服务器:
[root@client ~]# scp /server.csr 192.168.94.22:/tmp/
4、CA认证中心进行CA签名
[root@ca ~]# openssl ca -keyfile /etc/pki/CA/private/cakey.pem -cert /etc/pki/CA/cacert.pem -in /tmp/server.csr -out /server.crt

这里的认证中心进行的签名是用自己的私钥进行签名
5、CA认证中心进行颁发证书
在颁发之前,CA认证中心会使用自己的公钥进行加密
[root@ca ~]# scp /server.crt 192.168.94.111:/
三:使用证书实现https
SSL:(Secure Socket Layer)安全套接字层,通过一种机制在互联网上提供密钥传输 其主要目标是保证两个应用间通信数据的保密性和可靠性,可在服务器端和用户端同时支持的一种加密算法 目前主流版本SSLV2、SSLV3(常用)。 SSL四次握手安全传输: 加密协议: SSL 3.0 或 TLS 1.0 C -------------------------------------------------> S 1. 请求一个安全的会话,协商算法 C <------------------------------------------------- S 2. 将自己Server端的证书给客户端,证书中包括了64自己的公钥 C -------------------------------------------------> S 3. 客户端用浏览器中存放CA的根证书检测client证书,如果对,使用CA根证书中的公钥解密 得到CA的公钥; 然后生成一把对称的加密密钥,用client的公钥加密这个密钥发给CA , 后期使用对称密钥加密数据 C <------------------------------------------------> S 4.client使用私钥解密,得到对称的加密密钥然后,使用对称加密密钥来进行安全快速传输数据
1、配置HTTPSweb服务器
[root@client ~]# yum -y install mod_ssl # 安装SSL模块 [root@client ~]# cp /server.crt /etc/httpd/conf.d/ # 复制证书 [root@client ~]# vim /etc/httpd/conf.d/ssl.conf # SSLCertificateFile /etc/pki/tls/certs/localhost.crt 把路径改成/etc/httpd/conf.d/server.crt # SSLCertificateKeyFile /etc/pki/tls/private/localhost.key 把路径改成/etc/httpd/conf.d/server.key [root@client ~]# systemctl restart httpd Enter SSL pass phrase for 192.168.94.111:443 (RSA) : ****** # 私钥密码
测试 :
[root@client ~]# netstat -antup | grep 443 tcp6 0 0 :::443 :::* LISTEN 1634/httpd
访问https://192.168.94.111

到这就已经认证成功了 但是没有被信任
查看一下证书
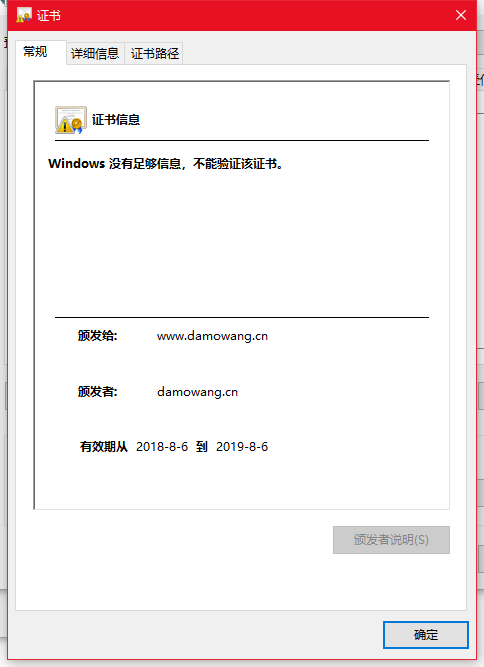
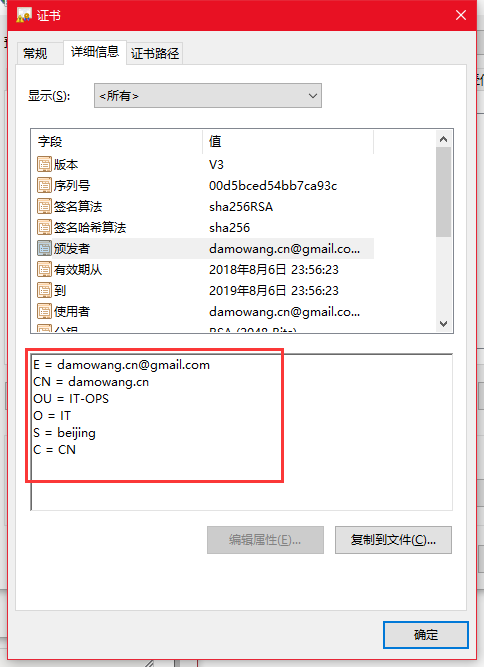
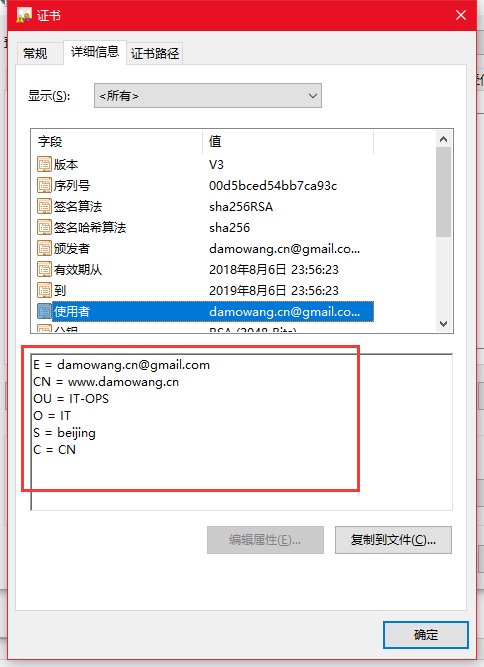
因为之前填写Common Name 是www.damowang.cn的域名
修改物理机hosts文件
192.168.94.111 www.damowang.cn
重新用域名访问应该就可以被信任了