此场景描述了使用ML2插件和Linux网桥的OpenStack网络服务的高可用性实现。
他的高可用性实施例增强了这样的场景:具有Linux网桥架构的传统使用了keepalived的虚拟路由器冗余协议(VRRP),以提供第3层服务的快速故障转移。
与传统的场景类似,一个项目网络上的所有网络流量都需要路由,而不管网络节点的数量是多少,路由都只需要一个网络节点。
因此,这种高可用性实现主要解决了故障情况,而不是限制性能的带宽约束。
然而,它支持不同网络节点上的路由器随机分布,以减少带宽限制的机会,并提高缩放比例。
而且,这种实现方式没有解决一个或多个第3层代理失败和底层虚拟网络继续正常操作的情况。
考虑部署场景:高可用性使用分布式虚拟路由(DVR)来增加冗余的性能。
在Kilo版,你不能结合DVR和L3HA机制。
注意:故障转移过程只保留具有浮动IP地址的实例的网络连接状态。
示例配置创建了一个Flat外部网络和一个VXLAN项目(租户)网络。然而,这种配置也支持VLAN外部和项目网络。
在Juno(最初)和基洛版本中,L3HA与Linux网桥支持VLAN和VXLAN项目网络。然而,由于一个缺陷,VXLAN项目网络必须使用多播而不是第2层的机制。
先决条件
这些先决条件定义了部署此场景所需的最小物理基础设施和立即的OpenStack服务依赖关系。
例如,网络服务直接依赖于身份服务,而计算服务直接依赖于网络服务。而像镜像服务没有依赖性的服务,是因为网络服务没有直接依赖它。
然而,计算服务依赖于镜像服务来启动一个实例。本场景中的示例配置假定了网络服务组件的基本配置知识。
基础设施
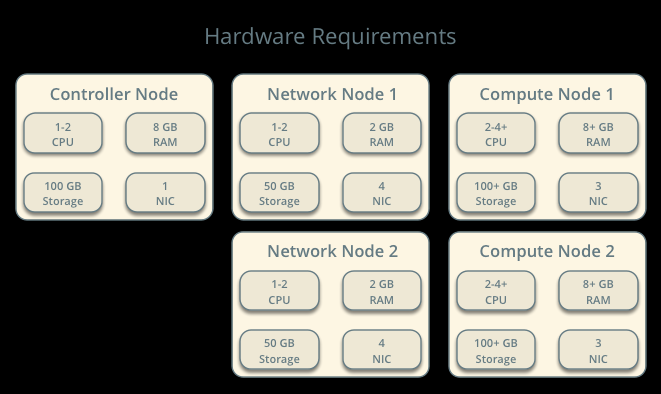
一个具有网络管理接口的控制器节点。
至少两个具有四个网络接口的网络节点:管理、项目隧道网络、项目VLAN网络和外部(通常是Internet)。
至少有两个具有三个网络接口的计算节点:管理、项目隧道网络和项目VLAN网络。
为了提高对网络流量的理解,网络和计算节点包含一个独立的网络接口,用于项目VLAN网络。在生产环境中,可以使用VLAN项目网络的任何网络接口。
在示例配置中,管理网络使用10.0.0 / 24,隧道网络使用10.0.1.0 / 24,VRRP网络使用169.254.192.0 / 18,外部网络使用203.0.113.0 / 24。VLAN网络不需要IP地址范围,因为它只处理二级连接。
硬件要求
网络布局

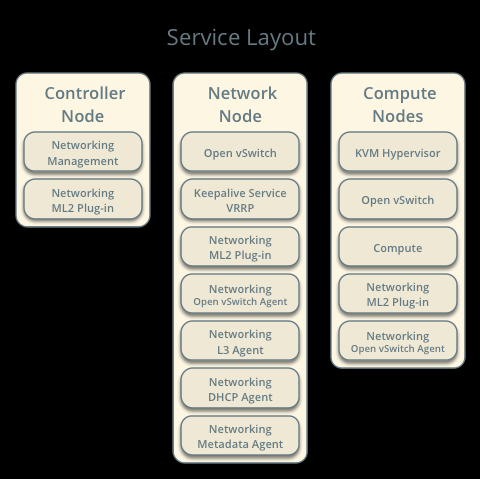
服务布局
注意:对于VLAN外部和项目网络,网络基础设施必须支持VLAN标记。为了获得VXLAN和GRE项目网络的最佳性能,网络基础设施应该支持巨型帧。
控制节点的OpenStack服务
在neutron.conf文件中具有数据库服务器的合适配置
在neutron.conf文件中具有消息队列服务的合适配置。
在neutron.conf文件中具有openstack keystone服务的合适配置
在nova.conf文件中具有openstack计算 控制/管理服务的合适配置去使用neutron
neutron服务器服务、ML2插件和任何依赖关系。
网络节点的Openstack服务
在neutron.conf文件中具有openstack keystone服务的合适配置
ML2插件、Linux网桥代理、L3代理、DHCP代理、元数据代理和任何依赖关系。
计算节点的Openstack服务
在neutron.conf文件中具有openstack keystone服务的合适配置
在nova.conf文件中具有openstack计算 控制/管理服务的合适配置去使用Openstack网络
ML2插件、Linux网桥代理和任何依赖项。
体系结构
一般的体系架构

网络节点包含以下组件:
1.Linux bridge代理管理虚拟交换机之间的连接性,以及通过虚拟端口与其他网络组件(如名称空间和底层接口)进行交互。
2.管理qdhcp名称空间的DHCP代理。qdhcp名称空间为使用项目网络的实例提供DHCP服务。
3.L3代理使用keepalived管理qrouter名称空间和VRRP。qrouter名称空间提供了项目和外部网络之间以及项目网络之间的路由。它们还在实例和元数据代理之间路由元数据通信。
4.元数据代理处理实例的元数据操作。
网络节点组件回顾

网络节点组件连接
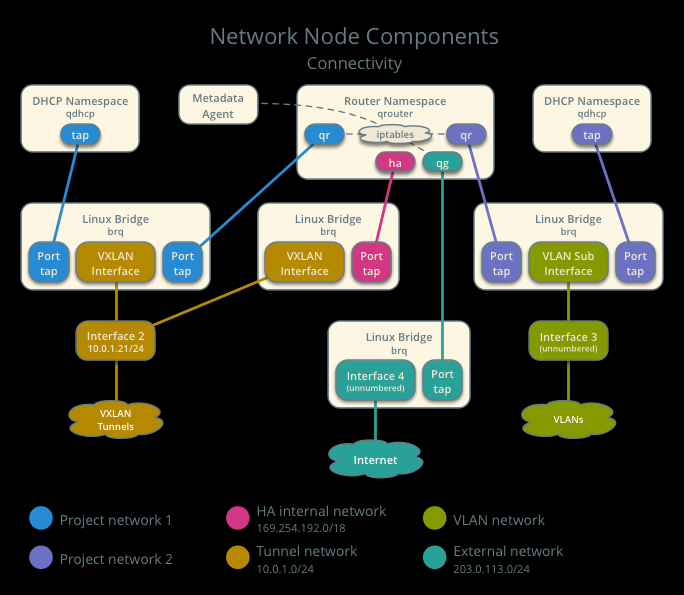
注意:为简单起见,为特定项目连接所有HA路由器的隐藏项目网络使用VXLAN网络类型。
计算节点包含以下网络组件:
1.Linux bridge代理管理虚拟交换机之间的连接,以及通过虚拟端口与其他网络组件(如名称空间、安全组和底层接口)的交互。
计算节点组件回顾
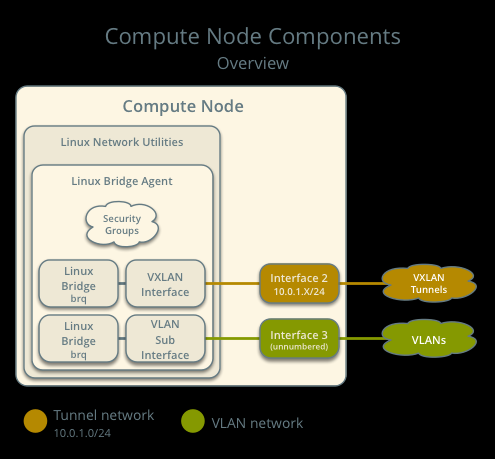
计算节点组件连接

数据包流
L3HA机制简单地增加了场景:如果主路由器失败,则使用Linux Bridge提供给另一个路由器的快速故障转移到另一个路由器。
在正常的操作过程中,主路由器定期地通过一个隐藏的项目网络来传输心跳数据包,该网络连接所有的HA路由器以完成特定的项目。
在默认情况下,这个网络使用的类型是在/etc/neutron/plugins/ml2_conf.ini的tenant_network_types选项中第一个值的类型。
如果备份路由器停止接收这些数据包,它就假定主路由器失效,并通过在qrouter名称空间中配置IP地址来提升自己到主路由器。在具有多个备份路由器的环境中,具有下一个最高优先级的路由器成为主路由器。
注意:L3HA机制对所有路由器使用相同的优先级。因此,VRRP会将IP地址最高的备份路由器提升到主路由器。
示例配置
使用下面的示例配置作为在您的环境中部署该场景的模板。
控制节点
1.配置常见的选项。编辑/etc/neutron/neutron.配置文件:
[DEFAULT] verbose = True core_plugin = ml2 service_plugins = router allow_overlapping_ips = True router_distributed = False l3_ha = True l3_ha_net_cidr = 169.254.192.0/18 max_l3_agents_per_router = 3 min_l3_agents_per_router = 2 dhcp_agents_per_network = 2
2.配置ML2插件。编辑/etc/neutron/plugins/ml2/ml2_conf.ini文件:
[ml2] type_drivers = flat,vlan,gre,vxlan tenant_network_types = vlan,gre,vxlan mechanism_drivers = linuxbridge [ml2_type_flat] flat_networks = external [ml2_type_vlan] network_vlan_ranges = external,vlan:MIN_VLAN_ID:MAX_VLAN_ID [ml2_type_vxlan] vni_ranges = MIN_VXLAN_ID:MAX_VXLAN_ID vxlan_group = 239.1.1.1 [securitygroup] firewall_driver = neutron.agent.linux.iptables_firewall.IptablesFirewallDriver enable_security_group = True enable_ipset = True
将MIN_VLAN_ID、MAX_VLAN_ID、MIN_VXLAN_ID和MAX_VXLAN_ID替换为VLAN和VXLAN ID最小值,最大值适合于您的环境。
请注意:
tenant_network_types选项中的第一个值在常规用户创建网络时成为默认项目网络类型。
network_vlan_range选项中的外部值缺少VLAN ID范围,以支持管理用户使用任意VLAN ID。
3.启动服务
网络节点
1.配置内核以启用包转发和禁用反向路径过滤。编辑/etc/sysctl.配置文件:
net.ipv4.ip_forward=1
net.ipv4.conf.default.rp_filter=0
net.ipv4.conf.all.rp_filter=0
2.加载新内核配置:
$ sysctl -p
3.配置常见的选项。编辑/etc/neutron/neutron.配置文件:
[DEFAULT]
verbose = True
4.配置Linux网桥代理。编辑/etc/neutron/plugins/ml2/ml2_conf.ini文件:
[linux_bridge] physical_interface_mappings = vlan:PROJECT_VLAN_INTERFACE,external:EXTERNAL_INTERFACE [vxlan] enable_vxlan = True local_ip = TUNNEL_INTERFACE_IP_ADDRESS l2_population = False [securitygroup] firewall_driver = neutron.agent.linux.iptables_firewall.IptablesFirewallDriver enable_security_group = True enable_ipset = True
将PROJECT_VLAN_INTERFACE和EXTERNAL_INTERFACE替换为处理VLAN项目网络和外部网络的底层接口的名称。用接口的IP地址替换TUNNEL_INTERFACE_IP_ADDRESS,该接口处理项目隧道网络。
5.配置L3代理。编辑/etc/neutron/l3_agent.ini文件:
[DEFAULT] verbose = True interface_driver = neutron.agent.linux.interface.BridgeInterfaceDriver use_namespaces = True external_network_bridge = router_delete_namespaces = True agent_mode = legacy
注意:external_network_bridge选项故意不包含任何值。
6.配置DHCP代理。编辑/etc/neutron/dhcp_agent.ini文件:
[DEFAULT] verbose = True interface_driver = neutron.agent.linux.interface.BridgeInterfaceDriver dhcp_driver = neutron.agent.linux.dhcp.Dnsmasq use_namespaces = True dhcp_delete_namespaces = True
7.(可选)为VXLAN项目网络减少MTU。
1.编辑/etc/neutron/dhcp_agent。ini文件:
[DEFAULT]
dnsmasq_config_file = /etc/neutron/dnsmasq-neutron.conf
2.编辑/etc/neutron/dnsmasq-neutron.conf文件:
dhcp-option-force=26,1450
8.配置元数据代理。编辑/etc/neutron/metadata_agent.ini文件:
[DEFAULT]
verbose = True
nova_metadata_ip = controller
metadata_proxy_shared_secret = METADATA_SECRET
用合适的环境值替换METADATA_SECRET。
9.开始以下服务:
Linux bridge agent
L3 agent
DHCP agent
Metadata agent
计算节点
1.配置内核以启用网桥上的iptables并禁用反向路径过滤。编辑/etc/sysctl.配置文件:
net.ipv4.conf.default.rp_filter=0
net.ipv4.conf.all.rp_filter=0
net.bridge.bridge-nf-call-iptables=1
net.bridge.bridge-nf-call-ip6tables=1
2.加载新内核配置:
$ sysctl -p
3.配置常见的选项。编辑/etc/neutron/neutron.配置文件:
[DEFAULT]
verbose = True
4.配置 Linux bridge代理。编辑/etc/neutron/plugins/ml2/ml2_conf.ini文件:
[linux_bridge] physical_interface_mappings = vlan:PROJECT_VLAN_INTERFACE [vxlan] enable_vxlan = True local_ip = TUNNEL_INTERFACE_IP_ADDRESS l2_population = False [securitygroup] firewall_driver = neutron.agent.linux.iptables_firewall.IptablesFirewallDriver enable_security_group = True enable_ipset = True
将PROJECT_VLAN_INTERFACE和EXTERNAL_INTERFACE替换为处理VLAN项目网络和外部网络的底层接口的名称。用接口的IP地址替换TUNNEL_INTERFACE_IP_ADDRESS,该接口处理项目隧道网络。
5.启动以下服务:
Linux bridge agent
验证服务操作
1.提供管理项目凭据。
2.验证代理的存在和操作:
$ neutron agent-list +--------------------------------------+--------------------+----------+-------+----------------+---------------------------+ | id | agent_type | host | alive | admin_state_up | binary | +--------------------------------------+--------------------+----------+-------+----------------+---------------------------+ | 7856ba29-5447-4392-b2e1-2c236bd5f479 | Metadata agent | network1 | :-) | True | neutron-metadata-agent | | 85d5c715-08f6-425d-9efc-73633736bf06 | Linux bridge agent | network2 | :-) | True | neutron-linuxbridge-agent | | 98d32a4d-1257-4b42-aea4-ad9bd7deea62 | Metadata agent | network2 | :-) | True | neutron-metadata-agent | | b45096a1-7bfa-4816-8b3c-900b752a9c08 | DHCP agent | network1 | :-) | True | neutron-dhcp-agent | | d4c45b8e-3b34-4192-80b1-bbdefb110c3f | Linux bridge agent | compute2 | :-) | True | neutron-linuxbridge-agent | | e5a4e06b-dd9d-4b97-a09a-c8ba07706753 | Linux bridge agent | network1 | :-) | True | neutron-linuxbridge-agent | | e8f8b228-5c3e-4378-b8f5-36b5c41cb3fe | L3 agent | network2 | :-) | True | neutron-l3-agent | | f2d10c26-2136-4e6a-86e5-d22f67ab22d7 | Linux bridge agent | compute1 | :-) | True | neutron-linuxbridge-agent | | f9f94732-08af-4f82-8908-fdcd69ab12e8 | L3 agent | network1 | :-) | True | neutron-l3-agent | | fbeebad9-6590-4f78-bb29-7d58ea867878 | DHCP agent | network2 | :-) | True | neutron-dhcp-agent | +--------------------------------------+--------------------+----------+-------+----------------+---------------------------+
创建初始网络
这个示例创建了一个flat外部网络和一个VXLAN项目网络。
1.提供管理项目凭据。
2.创建外部网络:
$ neutron net-create ext-net --router:external --provider:physical_network external --provider:network_type flat Created a new network: +---------------------------+--------------------------------------+ | Field | Value | +---------------------------+--------------------------------------+ | admin_state_up | True | | id | 5266fcbc-d429-4b21-8544-6170d1691826 | | name | ext-net | | provider:network_type | flat | | provider:physical_network | external | | provider:segmentation_id | | | router:external | True | | shared | False | | status | ACTIVE | | subnets | | | tenant_id | 96393622940e47728b6dcdb2ef405f50 | +---------------------------+--------------------------------------+
3.在外部网络上创建子网:
$ neutron subnet-create ext-net 203.0.113.0/24 --name ext-subnet --allocation-pool start=203.0.113.101,end=203.0.113.200 --disable-dhcp --gateway 203.0.113.1 Created a new subnet: +-------------------+----------------------------------------------------+ | Field | Value | +-------------------+----------------------------------------------------+ | allocation_pools | {"start": "203.0.113.101", "end": "203.0.113.200"} | | cidr | 203.0.113.0/24 | | dns_nameservers | | | enable_dhcp | False | | gateway_ip | 203.0.113.1 | | host_routes | | | id | b32e0efc-8cc3-43ff-9899-873b94df0db1 | | ip_version | 4 | | ipv6_address_mode | | | ipv6_ra_mode | | | name | ext-subnet | | network_id | 5266fcbc-d429-4b21-8544-6170d1691826 | | tenant_id | 96393622940e47728b6dcdb2ef405f50 | +-------------------+----------------------------------------------------+
请注意:
示例配置包含vlan作为第一个项目网络类型。只有管理用户才能创建其他类型的网络,比如GRE或VXLAN。下面的命令使用admin项目凭证创建一个VXLAN项目网络。
1.获得常规项目的ID。例如使用demo项目:
$ openstack project show demo
+-------------+----------------------------------+
| Field | Value |
+-------------+----------------------------------+
| description | Demo Tenant |
| enabled | True |
| id | 443cd1596b2e46d49965750771ebbfe1 |
| name | demo |
+-------------+----------------------------------+
2.创建项目网络:
$ neutron net-create demo-net --tenant-id f8207c03fd1e4b4aaf123efea4662819 --provider:network_type vxlan Created a new network: +---------------------------+--------------------------------------+ | Field | Value | +---------------------------+--------------------------------------+ | admin_state_up | True | | id | d990778b-49ea-4beb-9336-6ea2248edf7d | | name | demo-net | | provider:network_type | vxlan | | provider:physical_network | | | provider:segmentation_id | 1 | | router:external | False | | shared | False | | status | ACTIVE | | subnets | | | tenant_id | f8207c03fd1e4b4aaf123efea4662819 | +---------------------------+--------------------------------------+
3.提供常规项目凭证。下面的步骤使用demo项目。
4.在项目网络上创建子网:
$ neutron subnet-create demo-net 192.168.1.0/24 --name demo-subnet --gateway 192.168.1.1 Created a new subnet: +-------------------+--------------------------------------------------+ | Field | Value | +-------------------+--------------------------------------------------+ | allocation_pools | {"start": "192.168.1.2", "end": "192.168.1.254"} | | cidr | 192.168.1.0/24 | | dns_nameservers | | | enable_dhcp | True | | gateway_ip | 192.168.1.1 | | host_routes | | | id | b7fe4e86-65d5-4e88-8266-88795ae4ac53 | | ip_version | 4 | | ipv6_address_mode | | | ipv6_ra_mode | | | name | demo-subnet | | network_id | d990778b-49ea-4beb-9336-6ea2248edf7d | | tenant_id | f8207c03fd1e4b4aaf123efea4662819 | +-------------------+--------------------------------------------------+
5.创建一个项目路由器:
$ neutron router-create demo-router Created a new router: +-----------------------+--------------------------------------+ | Field | Value | +-----------------------+--------------------------------------+ | admin_state_up | True | | distributed | False | | external_gateway_info | | | ha | True | | id | 557bf478-6afe-48af-872f-63513f7e9b92 | | name | demo-router | | routes | | | status | ACTIVE | | tenant_id | f8207c03fd1e4b4aaf123efea4662819 | +-----------------------+--------------------------------------+
请注意:默认policy.json文件只允许管理项目在路由器创建期间启用/禁用HA,并查看路由器的HA标志。
6.在路由器上添加项目子网作为接口:
$ neutron router-interface-add demo-router demo-subnet Added interface 4cb8f7ea-28f2-4fe1-91f7-1c2823994fc4 to router demo-router.
7.在路由器上添加一个通向外部网络的网关:
$ neutron router-gateway-set demo-router ext-net Set gateway for router demo-router
验证网络操作
1.提供管理项目凭据。
2.在控制器节点上,验证HA网络的创建:
$ neutron net-list +--------------------------------------+----------------------------------------------------+-------------------------------------------------------+ | id | name | subnets | +--------------------------------------+----------------------------------------------------+-------------------------------------------------------+ | b304e495-b80d-4dd7-9345-5455302397a7 | HA network tenant f8207c03fd1e4b4aaf123efea4662819 | bbb53715-f4e9-4ce3-bf2b-44b2aed2f4ef 169.254.192.0/18 | | d990778b-49ea-4beb-9336-6ea2248edf7d | demo-net | b7fe4e86-65d5-4e88-8266-88795ae4ac53 192.168.1.0/24 | | fde31a29-3e23-470d-bc9d-6218375dca4f | ext-net | 2e1d865a-ef56-41e9-aa31-63fb8a591003 203.0.113.0/24 | +--------------------------------------+----------------------------------------------------+-------------------------------------------------------+
3.在控制器节点上,在多个网络节点上验证路由器的创建:
$ neutron l3-agent-list-hosting-router demo-router
+--------------------------------------+----------+----------------+-------+----------+
| id | host | admin_state_up | alive | ha_state |
+--------------------------------------+----------+----------------+-------+----------+
| e5a4e06b-dd9d-4b97-a09a-c8ba07706753 | network1 | True | :-) | active |
| 85d5c715-08f6-425d-9efc-73633736bf06 | network2 | True | :-) | standby |
+--------------------------------------+----------+----------------+-------+----------+
注意:老版本的python - neutronclient不支持ha_state字段。
4.在控制器节点上,在demo - router路由器上验证HA端口的创建:
$ neutron router-port-list demo-router +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+ | id | name | mac_address | fixed_ips | +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+ | 255d2e4b-33ba-4166-a13f-6531122641fe | HA port tenant f8207c03fd1e4b4aaf123efea4662819 | fa:16:3e:25:05:d7 | {"subnet_id": "bbb53715-f4e9-4ce3-bf2b-44b2aed2f4ef", "ip_address": "169.254.192.1"} | | 374587d7-2acd-4156-8993-4294f788b55e | | fa:16:3e:82:a0:59 | {"subnet_id": "2e1d865a-ef56-41e9-aa31-63fb8a591003", "ip_address": "203.0.113.101"} | | 8de3e172-5317-4c87-bdc1-f69e359de92e | | fa:16:3e:10:9f:f6 | {"subnet_id": "b7fe4e86-65d5-4e88-8266-88795ae4ac53", "ip_address": "192.168.1.1"} | | 90d1a59f-b122-459d-a94a-162a104de629 | HA port tenant f8207c03fd1e4b4aaf123efea4662819 | fa:16:3e:ae:3b:22 | {"subnet_id": "bbb53715-f4e9-4ce3-bf2b-44b2aed2f4ef", "ip_address": "169.254.192.2"} | +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+
5.在网络节点上,验证qrouter和qdhcp名称空间的创建:
网络节点1: $ ip netns qrouter-7a46dba8-8846-498c-9e10-588664558473 网络节点2: $ ip netns qrouter-7a46dba8-8846-498c-9e10-588664558473
两个qrouter名称空间都应该使用相同的UUID。
请注意
在启动实例之前,qdhcp名称空间可能不存在。
6.在网络节点上,验证HA操作:
网络节点1:
网络节点1: $ ip netns exec qrouter-7a46dba8-8846-498c-9e10-588664558473 ip addr show 11: ha-255d2e4b-33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:25:05:d7 brd ff:ff:ff:ff:ff:ff inet 169.254.192.1/18 brd 169.254.255.255 scope global ha-255d2e4b-33 valid_lft forever preferred_lft forever inet6 fe80::f816:3eff:fe25:5d7/64 scope link valid_lft forever preferred_lft forever 12: qr-8de3e172-53: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:10:9f:f6 brd ff:ff:ff:ff:ff:ff inet 192.168.1.1/24 scope global qr-8de3e172-53 valid_lft forever preferred_lft forever inet6 fe80::f816:3eff:fe10:9ff6/64 scope link valid_lft forever preferred_lft forever 13: qg-374587d7-2a: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:82:a0:59 brd ff:ff:ff:ff:ff:ff inet 203.0.113.101/24 scope global qg-374587d7-2a valid_lft forever preferred_lft forever inet6 fe80::f816:3eff:fe82:a059/64 scope link valid_lft forever preferred_lft forever
网络节点2:
$ ip netns exec qrouter-7a46dba8-8846-498c-9e10-588664558473 ip addr show 11: ha-90d1a59f-b1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:ae:3b:22 brd ff:ff:ff:ff:ff:ff inet 169.254.192.2/18 brd 169.254.255.255 scope global ha-90d1a59f-b1 valid_lft forever preferred_lft forever inet6 fe80::f816:3eff:feae:3b22/64 scope link valid_lft forever preferred_lft forever 12: qr-8de3e172-53: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:10:9f:f6 brd ff:ff:ff:ff:ff:ff inet6 fe80::f816:3eff:fe10:9ff6/64 scope link valid_lft forever preferred_lft forever 13: qg-374587d7-2a: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:82:a0:59 brd ff:ff:ff:ff:ff:ff inet6 fe80::f816:3eff:fe82:a059/64 scope link valid_lft forever preferred_lft forever
在每个网络节点上,qrouter命名空间应该包括ha、qr和qg接口。在主节点上,qr接口包含项目网络网关IP地址,qg接口包含外部网络上的项目路由器IP地址。在备份节点上,qr和qg接口不应该包含IP地址。在这两个节点上,ha接口应该在169.254.192.0 / 18范围内包含唯一的IP地址。
7.在网络节点上,在适当的网络接口上从主节点HA接口IP地址验证VRRP advertisements :
网络节点1:
$ tcpdump -lnpi eth1 16:50:16.857294 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20 16:50:18.858436 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20 16:50:20.859677 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20
网络节点2:
$ tcpdump -lnpi eth1 16:51:44.911640 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20 16:51:46.912591 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20 16:51:48.913900 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20
示例输出使用网络接口eth1。
8.在路由器上确定项目网络的外部网络网关IP地址,通常是外部子网IP分配范围内的最低IP地址:
$ neutron router-port-list demo-router +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+ | id | name | mac_address | fixed_ips | +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+ | 255d2e4b-33ba-4166-a13f-6531122641fe | HA port tenant 443cd1596b2e46d49965750771ebbfe1 | fa:16:3e:25:05:d7 | {"subnet_id": "8e8e4c7d-fa38-417d-a4e3-03ee5ab5493c", "ip_address": "169.254.192.1"} | | 374587d7-2acd-4156-8993-4294f788b55e | | fa:16:3e:82:a0:59 | {"subnet_id": "b32e0efc-8cc3-43ff-9899-873b94df0db1", "ip_address": "203.0.113.101"} | | 8de3e172-5317-4c87-bdc1-f69e359de92e | | fa:16:3e:10:9f:f6 | {"subnet_id": "2945790c-5999-4693-b8e7-50a9fc7f46f5", "ip_address": "192.168.1.1"} | | 90d1a59f-b122-459d-a94a-162a104de629 | HA port tenant 443cd1596b2e46d49965750771ebbfe1 | fa:16:3e:ae:3b:22 | {"subnet_id": "8e8e4c7d-fa38-417d-a4e3-03ee5ab5493c", "ip_address": "169.254.192.2"} | +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+
9.在控制器节点或任何有访问外部网络的主机上,在项目路由器上ping外部网络网关IP地址:
$ ping -c 4 203.0.113.101 PING 203.0.113.101 (203.0.113.101) 56(84) bytes of data. 64 bytes from 203.0.113.101: icmp_req=1 ttl=64 time=0.619 ms 64 bytes from 203.0.113.101: icmp_req=2 ttl=64 time=0.189 ms 64 bytes from 203.0.113.101: icmp_req=3 ttl=64 time=0.165 ms 64 bytes from 203.0.113.101: icmp_req=4 ttl=64 time=0.216 ms --- 203.0.113.101 ping statistics --- 4 packets transmitted, 4 received, 0% packet loss, time 2999ms rtt min/avg/max/mdev = 0.165/0.297/0.619/0.187 ms
10.提供常规项目凭证。下面的步骤使用演示项目。
11.创建适当的安全组规则,允许ping和SSH访问实例。例如:
$ nova secgroup-add-rule default icmp -1 -1 0.0.0.0/0 +-------------+-----------+---------+-----------+--------------+ | IP Protocol | From Port | To Port | IP Range | Source Group | +-------------+-----------+---------+-----------+--------------+ | icmp | -1 | -1 | 0.0.0.0/0 | | +-------------+-----------+---------+-----------+--------------+ $ nova secgroup-add-rule default tcp 22 22 0.0.0.0/0 +-------------+-----------+---------+-----------+--------------+ | IP Protocol | From Port | To Port | IP Range | Source Group | +-------------+-----------+---------+-----------+--------------+ | tcp | 22 | 22 | 0.0.0.0/0 | | +-------------+-----------+---------+-----------+--------------+
12.在项目网络上启动一个具有接口的实例。例如,使用现有的CirrOS镜像:
$ nova boot --flavor m1.tiny --image cirros --nic net-id=d990778b-49ea-4beb-9336-6ea2248edf7d demo-instance1 +--------------------------------------+-----------------------------------------------+ | Property | Value | +--------------------------------------+-----------------------------------------------+ | OS-DCF:diskConfig | MANUAL | | OS-EXT-AZ:availability_zone | nova | | OS-EXT-STS:power_state | 0 | | OS-EXT-STS:task_state | scheduling | | OS-EXT-STS:vm_state | building | | OS-SRV-USG:launched_at | - | | OS-SRV-USG:terminated_at | - | | accessIPv4 | | | accessIPv6 | | | adminPass | Z3uAd2utPUNu | | config_drive | | | created | 2015-08-10T15:06:24Z | | flavor | m1.tiny (1) | | hostId | | | id | 77149598-c839-400f-b948-db6993f0b40b | | image | cirros (125733d9-8d37-4d70-9a64-1c989cfa8e9c) | | key_name | | | metadata | {} | | name | demo-instance1 | | os-extended-volumes:volumes_attached | [] | | progress | 0 | | security_groups | default | | status | BUILD | | tenant_id | f8207c03fd1e4b4aaf123efea4662819 | | updated | 2015-08-10T15:06:25Z | | user_id | bdd4e165bdf94b258ddd4856340ed01c | +--------------------------------------+-----------------------------------------------+
13.获得对实例的控制台访问。
1.测试连接到项目路由器:
$ ping -c 4 192.168.1.1
PING 192.168.1.1 (192.168.1.1) 56(84) bytes of data.
64 bytes from 192.168.1.1: icmp_req=1 ttl=64 time=0.357 ms
64 bytes from 192.168.1.1: icmp_req=2 ttl=64 time=0.473 ms
64 bytes from 192.168.1.1: icmp_req=3 ttl=64 time=0.504 ms
64 bytes from 192.168.1.1: icmp_req=4 ttl=64 time=0.470 ms
--- 192.168.1.1 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 2998ms
rtt min/avg/max/mdev = 0.357/0.451/0.504/0.055 ms
2.测试连接到互联网:
$ ping -c 4 openstack.org
PING openstack.org (174.143.194.225) 56(84) bytes of data.
64 bytes from 174.143.194.225: icmp_req=1 ttl=53 time=17.4 ms
64 bytes from 174.143.194.225: icmp_req=2 ttl=53 time=17.5 ms
64 bytes from 174.143.194.225: icmp_req=3 ttl=53 time=17.7 ms
64 bytes from 174.143.194.225: icmp_req=4 ttl=53 time=17.5 ms
--- openstack.org ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3003ms
rtt min/avg/max/mdev = 17.431/17.575/17.734/0.143 ms
14.在外部网络上创建浮动IP地址:
$ neutron floatingip-create ext-net Created a new floatingip: +---------------------+--------------------------------------+ | Field | Value | +---------------------+--------------------------------------+ | fixed_ip_address | | | floating_ip_address | 203.0.113.102 | | floating_network_id | 5266fcbc-d429-4b21-8544-6170d1691826 | | id | 20a6b5dd-1c5c-460e-8a81-8b5cf1739307 | | port_id | | | router_id | | | status | DOWN | | tenant_id | 443cd1596b2e46d49965750771ebbfe1 | +---------------------+--------------------------------------+
15.将浮动IP地址与实例关联:
$ nova floating-ip-associate demo-instance1 203.0.113.102
16.验证添加到实例的浮动IP地址:
$ nova list +--------------------------------------+----------------+--------+------------+-------------+-----------------------------------------+ | ID | Name | Status | Task State | Power State | Networks | +--------------------------------------+----------------+--------+------------+-------------+-----------------------------------------+ | 77149598-c839-400f-b948-db6993f0b40b | demo-instance1 | ACTIVE | - | Running | demo-net=192.168.1.3, 203.0.113.102 | +--------------------------------------+----------------+--------+------------+-------------+-----------------------------------------+
17.在控制器节点或任何访问外部网络的主机上,ping与实例关联的浮动IP地址:
$ ping -c 4 203.0.113.102 PING 203.0.113.102 (203.0.113.112) 56(84) bytes of data. 64 bytes from 203.0.113.102: icmp_req=1 ttl=63 time=3.18 ms 64 bytes from 203.0.113.102: icmp_req=2 ttl=63 time=0.981 ms 64 bytes from 203.0.113.102: icmp_req=3 ttl=63 time=1.06 ms 64 bytes from 203.0.113.102: icmp_req=4 ttl=63 time=0.929 ms --- 203.0.113.102 ping statistics --- 4 packets transmitted, 4 received, 0% packet loss, time 3002ms rtt min/avg/max/mdev = 0.929/1.539/3.183/0.951 ms
Open vSwitch
Open vSwitch agent
L3 agent
DHCP agent
Metadata agent
计算节点
1.配置内核以启用网桥上的iptables并禁用反向路径过滤。编辑/etc/sysctl.配置文件:
net.ipv4.conf.default.rp_filter=0
net.ipv4.conf.all.rp_filter=0
net.bridge.bridge-nf-call-iptables=1
net.bridge.bridge-nf-call-ip6tables=1
2.加载新内核配置:
$ sysctl -p
3.配置常见的选项。编辑/etc/neutron/neutron.配置文件:
[DEFAULT]
verbose = True
4.配置Open vSwitch代理。编辑/etc/neutron/plugins/ml2/ml2_conf.ini文件:
[ovs] local_ip = TUNNEL_INTERFACE_IP_ADDRESS bridge_mappings = vlan:br-vlan [agent] tunnel_types = gre,vxlan l2_population = False [securitygroup] firewall_driver = neutron.agent.linux.iptables_firewall.OVSHybridIptablesFirewallDriver enable_security_group = True enable_ipset = True
使用处理GRE / VXLAN项目网络的接口的IP地址替换TUNNEL_INTERFACE_IP_ADDRESS。
7.启动以下服务:
Open vSwitch
Open vSwitch agent
验证服务操作
1.提供管理项目凭据。
2.验证代理的存在和操作:
$ neutron agent-list +--------------------------------------+--------------------+----------+-------+----------------+---------------------------+ | id | agent_type | host | alive | admin_state_up | binary | +--------------------------------------+--------------------+----------+-------+----------------+---------------------------+ | 0bfe5b5d-0b82-434e-b8a0-524cc18da3a4 | DHCP agent | network1 | :-) | True | neutron-dhcp-agent | | 25224bd5-0905-4ec9-9f2d-3b17cdaf5650 | Open vSwitch agent | compute2 | :-) | True | neutron-openvswitch-agent | | 29afe014-273d-42f3-ad71-8a226e40dea6 | L3 agent | network1 | :-) | True | neutron-l3-agent | | 3bed5093-e46c-4b0f-9460-3309c62254a3 | DHCP agent | network2 | :-) | True | neutron-dhcp-agent | | 54aefb1c-35f7-4ebf-a848-3bb4fe81dcf7 | Open vSwitch agent | network1 | :-) | True | neutron-openvswitch-agent | | 91c9cc03-1678-4d7a-b0a7-fa1ac24e5516 | Open vSwitch agent | compute1 | :-) | True | neutron-openvswitch-agent | | ac7b3f77-7e4d-47a6-9dbd-3358cfb67b61 | Open vSwitch agent | network2 | :-) | True | neutron-openvswitch-agent | | ceef5c49-3148-4c39-9e15-4985fc995113 | Metadata agent | network1 | :-) | True | neutron-metadata-agent | | d27ac19b-fb4d-4fec-b81d-e8c65557b6ec | L3 agent | network2 | :-) | True | neutron-l3-agent | | f072a1ec-f842-4223-a6b6-ec725419be85 | Metadata agent | network2 | :-) | True | neutron-metadata-agent | +--------------------------------------+--------------------+----------+-------+----------------+---------------------------+
创建初始网络
这个示例创建了一个flat外部网络和一个VXLAN项目网络。
1.提供管理项目凭据。
2.创建外部网络:
$ neutron net-create ext-net --router:external True --provider:physical_network external --provider:network_type flat Created a new network: +---------------------------+--------------------------------------+ | Field | Value | +---------------------------+--------------------------------------+ | admin_state_up | True | | id | 5266fcbc-d429-4b21-8544-6170d1691826 | | name | ext-net | | provider:network_type | flat | | provider:physical_network | external | | provider:segmentation_id | | | router:external | True | | shared | False | | status | ACTIVE | | subnets | | | tenant_id | 96393622940e47728b6dcdb2ef405f50 | +---------------------------+--------------------------------------+
3.在外部网络上创建子网:
$ neutron subnet-create ext-net 203.0.113.0/24 --name ext-subnet --allocation-pool start=203.0.113.101,end=203.0.113.200 --disable-dhcp --gateway 203.0.113.1 Created a new subnet: +-------------------+----------------------------------------------------+ | Field | Value | +-------------------+----------------------------------------------------+ | allocation_pools | {"start": "203.0.113.101", "end": "203.0.113.200"} | | cidr | 203.0.113.0/24 | | dns_nameservers | | | enable_dhcp | False | | gateway_ip | 203.0.113.1 | | host_routes | | | id | b32e0efc-8cc3-43ff-9899-873b94df0db1 | | ip_version | 4 | | ipv6_address_mode | | | ipv6_ra_mode | | | name | ext-subnet | | network_id | 5266fcbc-d429-4b21-8544-6170d1691826 | | tenant_id | 96393622940e47728b6dcdb2ef405f50 | +-------------------+----------------------------------------------------+
请注意:
示例配置包含vlan作为第一个项目网络类型。只有管理用户才能创建其他类型的网络,比如GRE或VXLAN。下面的命令使用admin项目凭证创建一个VXLAN项目网络。
1.获得常规项目的ID。例如使用demo项目:
$ openstack project show demo
+-------------+----------------------------------+
| Field | Value |
+-------------+----------------------------------+
| description | Demo Tenant |
| enabled | True |
| id | 443cd1596b2e46d49965750771ebbfe1 |
| name | demo |
+-------------+----------------------------------+
2.创建项目网络:
$ neutron net-create demo-net --tenant-id 443cd1596b2e46d49965750771ebbfe1 --provider:network_type vxlan Created a new network: +---------------------------+--------------------------------------+ | Field | Value | +---------------------------+--------------------------------------+ | admin_state_up | True | | id | 7ac9a268-1ddd-453f-857b-0fd9552b645f | | name | demo-net | | provider:network_type | vxlan | | provider:physical_network | | | provider:segmentation_id | 1 | | router:external | False | | shared | False | | status | ACTIVE | | subnets | | | tenant_id | 443cd1596b2e46d49965750771ebbfe1 | +---------------------------+--------------------------------------+
3.提供常规项目凭证。下面的步骤使用demo项目。
4.在项目网络上创建子网:
$ neutron subnet-create demo-net 192.168.1.0/24 --name demo-subnet --gateway 192.168.1.1 Created a new subnet: +-------------------+--------------------------------------------------+ | Field | Value | +-------------------+--------------------------------------------------+ | allocation_pools | {"start": "192.168.1.2", "end": "192.168.1.254"} | | cidr | 192.168.1.0/24 | | dns_nameservers | | | enable_dhcp | True | | gateway_ip | 192.168.1.1 | | host_routes | | | id | 2945790c-5999-4693-b8e7-50a9fc7f46f5 | | ip_version | 4 | | ipv6_address_mode | | | ipv6_ra_mode | | | name | demo-subnet | | network_id | 7ac9a268-1ddd-453f-857b-0fd9552b645f | | tenant_id | 443cd1596b2e46d49965750771ebbfe1 | +-------------------+--------------------------------------------------+
5.创建一个项目路由器:
$ neutron router-create demo-router Created a new router: +-----------------------+--------------------------------------+ | Field | Value | +-----------------------+--------------------------------------+ | admin_state_up | True | | distributed | False | | external_gateway_info | | | ha | True | | id | 7a46dba8-8846-498c-9e10-588664558473 | | name | demo-router | | routes | | | status | ACTIVE | | tenant_id | 443cd1596b2e46d49965750771ebbfe1 | +-----------------------+--------------------------------------+
注意:请注意
默认policy.json文件只允许管理项目在路由器创建期间启用/禁用HA,并查看路由器的HA标志。
6.在路由器上添加项目子网作为接口:
$ neutron router-interface-add demo-router demo-subnet Added interface 8de3e172-5317-4c87-bdc1-f69e359de92e to router demo-router.
7.在路由器上添加一个通向外部网络的网关:
$ neutron router-gateway-set demo-router ext-net Set gateway for router demo-router
验证网络操作
1.提供管理项目凭据。
2.在控制器节点上,验证HA网络的创建:
$ neutron net-list +--------------------------------------+----------------------------------------------------+-------------------------------------------------------+ | id | name | subnets | +--------------------------------------+----------------------------------------------------+-------------------------------------------------------+ | 5266fcbc-d429-4b21-8544-6170d1691826 | ext-net | b32e0efc-8cc3-43ff-9899-873b94df0db1 203.0.113.0/24 | | e029b568-0fd7-4d10-bb16-f9e014811d10 | HA network tenant 443cd1596b2e46d49965750771ebbfe1 | ee30083f-eb4c-41ea-8937-1bae65740af4 169.254.192.0/18 | | 7ac9a268-1ddd-453f-857b-0fd9552b645f | demo-net | 2945790c-5999-4693-b8e7-50a9fc7f46f5 192.168.1.0/24 | +--------------------------------------+----------------------------------------------------+-------------------------------------------------------+
3.在控制器节点上,在多个网络节点上验证路由器的创建:
$ neutron l3-agent-list-hosting-router demo-router
+--------------------------------------+----------+----------------+-------+----------+
| id | host | admin_state_up | alive | ha_state |
+--------------------------------------+----------+----------------+-------+----------+
| 29afe014-273d-42f3-ad71-8a226e40dea6 | network1 | True | :-) | active |
| d27ac19b-fb4d-4fec-b81d-e8c65557b6ec | network2 | True | :-) | standby |
+--------------------------------------+----------+----------------+-------+----------+
注意:老版本的python - neutronclient不支持ha_state字段。
4.在控制器节点上,在demo - router路由器上验证HA端口的创建:
$ neutron router-port-list demo-router +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+ | id | name | mac_address | fixed_ips | +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+ | 255d2e4b-33ba-4166-a13f-6531122641fe | HA port tenant 443cd1596b2e46d49965750771ebbfe1 | fa:16:3e:25:05:d7 | {"subnet_id": "8e8e4c7d-fa38-417d-a4e3-03ee5ab5493c", "ip_address": "169.254.192.1"} | | 374587d7-2acd-4156-8993-4294f788b55e | | fa:16:3e:82:a0:59 | {"subnet_id": "b32e0efc-8cc3-43ff-9899-873b94df0db1", "ip_address": "203.0.113.101"} | | 8de3e172-5317-4c87-bdc1-f69e359de92e | | fa:16:3e:10:9f:f6 | {"subnet_id": "2945790c-5999-4693-b8e7-50a9fc7f46f5", "ip_address": "192.168.1.1"} | | 90d1a59f-b122-459d-a94a-162a104de629 | HA port tenant 443cd1596b2e46d49965750771ebbfe1 | fa:16:3e:ae:3b:22 | {"subnet_id": "8e8e4c7d-fa38-417d-a4e3-03ee5ab5493c", "ip_address": "169.254.192.2"} | +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+
5.在网络节点上,验证qrouter和qdhcp名称空间的创建:
网络节点1: $ ip netns qrouter-7a46dba8-8846-498c-9e10-588664558473 网络节点2: $ ip netns qrouter-7a46dba8-8846-498c-9e10-588664558473
两个qrouter名称空间都应该使用相同的UUID。
请注意
在启动实例之前,qdhcp名称空间可能不存在。
6.在网络节点上,验证HA操作:
网络节点1:
网络节点1: $ ip netns exec qrouter-7a46dba8-8846-498c-9e10-588664558473 ip addr show 11: ha-255d2e4b-33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:25:05:d7 brd ff:ff:ff:ff:ff:ff inet 169.254.192.1/18 brd 169.254.255.255 scope global ha-255d2e4b-33 valid_lft forever preferred_lft forever inet6 fe80::f816:3eff:fe25:5d7/64 scope link valid_lft forever preferred_lft forever 12: qr-8de3e172-53: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:10:9f:f6 brd ff:ff:ff:ff:ff:ff inet 192.168.1.1/24 scope global qr-8de3e172-53 valid_lft forever preferred_lft forever inet6 fe80::f816:3eff:fe10:9ff6/64 scope link valid_lft forever preferred_lft forever 13: qg-374587d7-2a: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:82:a0:59 brd ff:ff:ff:ff:ff:ff inet 203.0.113.101/24 scope global qg-374587d7-2a valid_lft forever preferred_lft forever inet6 fe80::f816:3eff:fe82:a059/64 scope link valid_lft forever preferred_lft forever
网络节点2:
$ ip netns exec qrouter-7a46dba8-8846-498c-9e10-588664558473 ip addr show 11: ha-90d1a59f-b1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:ae:3b:22 brd ff:ff:ff:ff:ff:ff inet 169.254.192.2/18 brd 169.254.255.255 scope global ha-90d1a59f-b1 valid_lft forever preferred_lft forever inet6 fe80::f816:3eff:feae:3b22/64 scope link valid_lft forever preferred_lft forever 12: qr-8de3e172-53: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:10:9f:f6 brd ff:ff:ff:ff:ff:ff inet6 fe80::f816:3eff:fe10:9ff6/64 scope link valid_lft forever preferred_lft forever 13: qg-374587d7-2a: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UNKNOWN group default link/ether fa:16:3e:82:a0:59 brd ff:ff:ff:ff:ff:ff inet6 fe80::f816:3eff:fe82:a059/64 scope link valid_lft forever preferred_lft forever
在每个网络节点上,qrouter命名空间应该包括ha、qr和qg接口。在主节点上,qr接口包含项目网络网关IP地址,qg接口包含外部网络上的项目路由器IP地址。在备份节点上,qr和qg接口不应该包含IP地址。在这两个节点上,ha接口应该在169.254.192.0 / 18范围内包含唯一的IP地址。
7.在网络节点上,在适当的网络接口上从主节点HA接口IP地址验证VRRP advertisements :
网络节点1:
$ tcpdump -lnpi eth1 16:50:16.857294 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20 16:50:18.858436 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20 16:50:20.859677 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20
网络节点2:
$ tcpdump -lnpi eth1 16:51:44.911640 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20 16:51:46.912591 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20 16:51:48.913900 IP 169.254.192.1 > 224.0.0.18: VRRPv2, Advertisement, vrid 1, prio 50, authtype none, intvl 2s, length 20
示例输出使用网络接口eth1。
8.在路由器上确定项目网络的外部网络网关IP地址,通常是外部子网IP分配范围内的最低IP地址:
$ neutron router-port-list demo-router +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+ | id | name | mac_address | fixed_ips | +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+ | 255d2e4b-33ba-4166-a13f-6531122641fe | HA port tenant 443cd1596b2e46d49965750771ebbfe1 | fa:16:3e:25:05:d7 | {"subnet_id": "8e8e4c7d-fa38-417d-a4e3-03ee5ab5493c", "ip_address": "169.254.192.1"} | | 374587d7-2acd-4156-8993-4294f788b55e | | fa:16:3e:82:a0:59 | {"subnet_id": "b32e0efc-8cc3-43ff-9899-873b94df0db1", "ip_address": "203.0.113.101"} | | 8de3e172-5317-4c87-bdc1-f69e359de92e | | fa:16:3e:10:9f:f6 | {"subnet_id": "2945790c-5999-4693-b8e7-50a9fc7f46f5", "ip_address": "192.168.1.1"} | | 90d1a59f-b122-459d-a94a-162a104de629 | HA port tenant 443cd1596b2e46d49965750771ebbfe1 | fa:16:3e:ae:3b:22 | {"subnet_id": "8e8e4c7d-fa38-417d-a4e3-03ee5ab5493c", "ip_address": "169.254.192.2"} | +--------------------------------------+-------------------------------------------------+-------------------+----------------------------------------------------------------------------------------+
9.在控制器节点或任何有访问外部网络的主机上,在项目路由器上ping外部网络网关IP地址:
$ ping -c 4 203.0.113.101 PING 203.0.113.101 (203.0.113.101) 56(84) bytes of data. 64 bytes from 203.0.113.101: icmp_req=1 ttl=64 time=0.619 ms 64 bytes from 203.0.113.101: icmp_req=2 ttl=64 time=0.189 ms 64 bytes from 203.0.113.101: icmp_req=3 ttl=64 time=0.165 ms 64 bytes from 203.0.113.101: icmp_req=4 ttl=64 time=0.216 ms --- 203.0.113.101 ping statistics --- 4 packets transmitted, 4 received, 0% packet loss, time 2999ms rtt min/avg/max/mdev = 0.165/0.297/0.619/0.187 ms
10.提供常规项目凭证。下面的步骤使用演示项目。
11.创建适当的安全组规则,允许ping和SSH访问实例。例如:
$ nova secgroup-add-rule default icmp -1 -1 0.0.0.0/0 +-------------+-----------+---------+-----------+--------------+ | IP Protocol | From Port | To Port | IP Range | Source Group | +-------------+-----------+---------+-----------+--------------+ | icmp | -1 | -1 | 0.0.0.0/0 | | +-------------+-----------+---------+-----------+--------------+ $ nova secgroup-add-rule default tcp 22 22 0.0.0.0/0 +-------------+-----------+---------+-----------+--------------+ | IP Protocol | From Port | To Port | IP Range | Source Group | +-------------+-----------+---------+-----------+--------------+ | tcp | 22 | 22 | 0.0.0.0/0 | | +-------------+-----------+---------+-----------+--------------+
12.在项目网络上启动一个具有接口的实例。例如,使用现有的CirrOS镜像:
$ nova boot --flavor m1.tiny --image cirros --nic net-id=7ac9a268-1ddd-453f-857b-0fd9552b645f demo-instance1 +--------------------------------------+-----------------------------------------------+ | Property | Value | +--------------------------------------+-----------------------------------------------+ | OS-DCF:diskConfig | MANUAL | | OS-EXT-AZ:availability_zone | nova | | OS-EXT-STS:power_state | 0 | | OS-EXT-STS:task_state | scheduling | | OS-EXT-STS:vm_state | building | | OS-SRV-USG:launched_at | - | | OS-SRV-USG:terminated_at | - | | accessIPv4 | | | accessIPv6 | | | adminPass | Z3uAd2utPUNu | | config_drive | | | created | 2015-08-10T15:06:24Z | | flavor | m1.tiny (1) | | hostId | | | id | 77149598-c839-400f-b948-db6993f0b40b | | image | cirros (125733d9-8d37-4d70-9a64-1c989cfa8e9c) | | key_name | | | metadata | {} | | name | demo-instance1 | | os-extended-volumes:volumes_attached | [] | | progress | 0 | | security_groups | default | | status | BUILD | | tenant_id | 443cd1596b2e46d49965750771ebbfe1 | | updated | 2015-08-10T15:06:25Z | | user_id | bdd4e165bdf94b258ddd4856340ed01c | +--------------------------------------+-----------------------------------------------+
13.获得对实例的控制台访问。
1.测试连接到项目路由器:
$ ping -c 4 192.168.1.1
PING 192.168.1.1 (192.168.1.1) 56(84) bytes of data.
64 bytes from 192.168.1.1: icmp_req=1 ttl=64 time=0.357 ms
64 bytes from 192.168.1.1: icmp_req=2 ttl=64 time=0.473 ms
64 bytes from 192.168.1.1: icmp_req=3 ttl=64 time=0.504 ms
64 bytes from 192.168.1.1: icmp_req=4 ttl=64 time=0.470 ms
--- 192.168.1.1 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 2998ms
rtt min/avg/max/mdev = 0.357/0.451/0.504/0.055 ms
2.测试连接到互联网:
$ ping -c 4 openstack.org
PING openstack.org (174.143.194.225) 56(84) bytes of data.
64 bytes from 174.143.194.225: icmp_req=1 ttl=53 time=17.4 ms
64 bytes from 174.143.194.225: icmp_req=2 ttl=53 time=17.5 ms
64 bytes from 174.143.194.225: icmp_req=3 ttl=53 time=17.7 ms
64 bytes from 174.143.194.225: icmp_req=4 ttl=53 time=17.5 ms
--- openstack.org ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3003ms
rtt min/avg/max/mdev = 17.431/17.575/17.734/0.143 ms
14.在外部网络上创建浮动IP地址:
$ neutron floatingip-create ext-net Created a new floatingip: +---------------------+--------------------------------------+ | Field | Value | +---------------------+--------------------------------------+ | fixed_ip_address | | | floating_ip_address | 203.0.113.102 | | floating_network_id | 5266fcbc-d429-4b21-8544-6170d1691826 | | id | 20a6b5dd-1c5c-460e-8a81-8b5cf1739307 | | port_id | | | router_id | | | status | DOWN | | tenant_id | 443cd1596b2e46d49965750771ebbfe1 | +---------------------+--------------------------------------+
15.将浮动IP地址与实例关联:
$ nova floating-ip-associate demo-instance1 203.0.113.102
16.验证添加到实例的浮动IP地址:
$ nova list +--------------------------------------+----------------+--------+------------+-------------+-----------------------------------------+ | ID | Name | Status | Task State | Power State | Networks | +--------------------------------------+----------------+--------+------------+-------------+-----------------------------------------+ | 77149598-c839-400f-b948-db6993f0b40b | demo-instance1 | ACTIVE | - | Running | demo-net=192.168.1.3, 203.0.113.102 | +--------------------------------------+----------------+--------+------------+-------------+-----------------------------------------+
17.在控制器节点或任何访问外部网络的主机上,ping与实例关联的浮动IP地址:
$ ping -c 4 203.0.113.102 PING 203.0.113.102 (203.0.113.112) 56(84) bytes of data. 64 bytes from 203.0.113.102: icmp_req=1 ttl=63 time=3.18 ms 64 bytes from 203.0.113.102: icmp_req=2 ttl=63 time=0.981 ms 64 bytes from 203.0.113.102: icmp_req=3 ttl=63 time=1.06 ms 64 bytes from 203.0.113.102: icmp_req=4 ttl=63 time=0.929 ms --- 203.0.113.102 ping statistics --- 4 packets transmitted, 4 received, 0% packet loss, time 3002ms rtt min/avg/max/mdev = 0.929/1.539/3.183/0.951 ms
[Ctrl+Enter快捷键提交]





昵称: