本文所需步骤均在优麒麟20.10系统上实践(家目录:home/hollowman)
本文默认在家目录中打开终端
本文中的软件均默认下载和保存至家目录
一、下载navicat应用程序
官网地址:http://navicat.com.cn/download/navicat-premium,选择32/64位版本下载。
可以发现这是一个AppImage后缀的文件,怎么说这个类型的文件呢?只能用 “惊喜” 来形容了。
1.AppImage科普
AppImage后缀的文件可称之为AppImage格式分发Linux桌面应用程序。它能让所有常见Linux发行版的用户运行它。 一次打包,无需安装,无需改变依赖或系统配置,只要给予执行权限即可运行。
1)运行AppImage应用很简单:
$ chmod a+x appname.AppImage #增加执行权限
$ ./appname.AppImage #运行应用
2)AppImage应用的特点:
简单。AppImage的核心思想是一个应用程序 = 一个文件 。每个AppImage都包含应用程序以及应用程序运行所需的所有文件。换句话说,除了操作系统本身的基础组件,Appimage不需要依赖包即可运行。
可靠。AppImage 格式是上游应用打包的理想选择,这意味着你可以直接从开发者那里获取软件,而不需要任何中间步骤,这完全符合开发者意图。非常迅速。
快速。AppImage应用可以直接下载并且运行,无需安装,并且不需要root权限。
3)更多内容
AppImage网站:https://appimage.org/
AppImage资源:https://bintray.com/probono/AppImages
2.JH思路
1)修改原公钥(通过patcher工具来实现)
2)根据新公钥生成(通过keygen工具来实现)
二、提取AppImage应用程序中的文件
修改公钥文件,首先需要将AppImage应用程序中包含的文件提取到一个新的目录中。
这一步的思路是:将AppImage进行挂载—将挂载目录中的只读文件复制到一个新的目录-取消挂载
hollowman@hollowman-F117:~$ mkdir navicat15-premium-cs
hollowman@hollowman-F117:~$ sudo mount -o loop navicat15-premium-cs.AppImage navicat15-premium-cs
mount: /home/hollowman/navicat15-premium-cs: WARNING: source write-protected, mounted read-only.
hollowman@hollowman-F117:~$ cp -r navicat15-premium-cs navicat15-premium-cs-bak
hollowman@hollowman-F117:~$ sudo umount navicat15-premium-cs
hollowman@hollowman-F117:~$ rm -rf navicat15-premium-cs
三、编译patcher和keygen
patcher和keygen两个工具是由navicat-keygen编译后生成的,但navicat-keygen需要下载,而且它的编译还需要先解决依赖问题。
1.安装需要的依赖包
capstone、keystone、rapidjson、openssl,确保你的gcc支持C++17特性。
#安装capstone
hollowman@hollowman-F117:~$ sudo apt install libcapstone-dev
#安装keystone
hollowman@hollowman-F117:~$ sudo apt install cmake
hollowman@hollowman-F117:~$ sudo apt install git
hollowman@hollowman-F117:~$ git clone https://github.com/keystone-engine/keystone.git
hollowman@hollowman-F117:~$ cd keystone
hollowman@hollowman-F117:~/keystone$ mkdir build
hollowman@hollowman-F117:~/keystone$ cd build
hollowman@hollowman-F117:~/keystone/build$ ../make-share.sh
hollowman@hollowman-F117:~/keystone/build$ sudo make install
hollowman@hollowman-F117:~/keystone/build$ sudo ldconfig
#安装rapidjson
hollowman@hollowman-F117:~/keystone/build$ sudo apt install rapidjson-dev
#安装openssl
hollowman@hollowman-F117:~/keystone/build$ sudo apt install openssl
2.编译navicat-keygen
hollowman@hollowman-F117:~/keystone/build$ cd ~
hollowman@hollowman-F117:~$ git clone -b linux --single-branch https://gitee.com/andisolo/navicat-keygen.git
hollowman@hollowman-F117:~$ cd navicat-keygen
hollowman@hollowman-F117:~/navicat-keygen$ make all
此时,navicat-keygen目录下会生成一个bin目录,并且bin目录下也会生成两个文件keygen和patcher,下面的工作就要重点围绕这两个可执行文件来操作了。
四、通过navicat-patcher命令来修改原公钥
原公钥就在刚才我们从AppImage安装包中提取到的目录navicat15-premium-cs-bak内。前面也提到,修改公钥用到的工具是patcher。同时产生一个RSA-2048私钥文件RegPrivateKey.pem(存储于 navicat-keygen目录下)。
语法:navicat-patcher [--dry-run] <Navicat Installation Path> [RSA-2048 Private Key File]
hollowman@hollowman-F117:~/navicat-keygen$ ./bin/navicat-patcher ../navicat15-premium-cs-bak/
**********************************************************
* Navicat Patcher (Linux) by @DoubleLabyrinth *
* Version: 1.0 *
**********************************************************
Press ENTER to continue or Ctrl + C to abort.
[+] Try to open libcc.so ... Ok!
[+] PatchSolution0 ...... Ready to apply
RefSegment = 1
MachineCodeRva = 0x000000000141fbf0
PatchMarkOffset = +0x0000000002a25648
[*] Generating new RSA private key, it may take a long time...
[*] Your RSA private key:
-----BEGIN RSA PRIVATE KEY-----
MIIEpAIBAAKCAQEAoGGlxu8ihpmwySW+sSvO9aaQ2OLlabD0xpEWcb29VmKF3Oj5
R07MQ9Q6uSdvtp10nXQ6B1loezHVEU0mEvEap1oJhZATxn+SXWfHMylfQ/6+0PIg
7IFW+6spIZ8XDX2jeuvU2XlXfVqSzbqykp8YmK3UwtyuEBpGmuv4xB0G+puwJ6gq
dWXNbclrU2FGdSgViRN6DHyu9Z3RIn5sRygINeFjcBrRFb4ZOqYR+VlKxyuSBtsr
zZO+1HfsC1Z+XRxHZTqtFHvWqOPe4Htm9xAZ85l2Xy5Hn4UN8CnWwIjJN67spKg/
GdbEZwddiEYEdq0Y9AwykDxrUQGlLrbroc4atQIDAQABAoIBACzqa/UEr9SmYj5T
Fc6kiDd/yH0VPk6VQlgB9hkwnD//I6I0lOuFg+tTGocUJlMsUaZvEHlSbtJhqFxK
EOmpIF/R9Wy0ZvVmcOU71Svc4FM4mtQFm3bg2i1tR/2kgl5C22/ncBrfwsLWhNqc
+LnbWJYZyMYx64WS9kcY4vh5cKTqV6tj9h8IRarl/MYrCCwY3HRzhl6lTQafZGUa
wFI4xiGs3NEx41KWLjPdC1K4Tjc7VPI0KBXwSb7ve9kWee+uHIpKzFJfXNV43h1U
9V2sBmuzdguLm3I9KsQ/lk92OD/0EsLshjPX2dT0yUrreVW+XtgbPTXEPF9Cc32/
Ve9/zIECgYEAzxv28tVs3AYRVSAtGujIIMcVn6HcgfgzIMuBmJSN5oOgb7OhYRF4
o11QBgMTDDMhRq08VhJm5SLEizscF/4ynXQSvHj0ozzlUBE8kqzbFYBLcz0CFXry
l/qk9AXcB1394oPd36feQZx+YyanpAgLTKpQZHARMw0oNGciZ+VJMeUCgYEAxj3T
ghCjYHEuOuikFVr8G/YEgkNoo8V604mTHBoGR2CWuZKXx/ANxPLas+XuwAV4kGYT
EqBcsjRY/Bn67C9SYbbOowNOFM75EXFjju6bDxxFesrkNfd74QgJd3ummKVTm0GT
/PfCJX8KU9jrHVNhxNVLlv1OiLIcL04qfKrH+JECgYEAm9xHs+e5zLskQBO+3glg
0ooAU+nTsFvA3mVIWjMxttBH5MgiIpKrXwXSOzQFGaFA4ZdtWLjwhm/ryXvqYIQE
Q0oe74d3U4F4cREHrLo5Ba1PGqJG9zNXbdhKWvot471wWw8x4ibKtEW5N5TXhDIp
jsB9T5im2OyF3SngUp/SvaECgYAhcvknLwuCEFbOlcZp3ApB5YbpO9qCF6Yb31C1
IycAECoecb+uerC4FIoWZKueNs4a/z4knG5Hm1GQaAnQpENwPVosYzhfhnS8Hre/
vD7pk8mdaHKNMI70b1i5kmGPzAWJYs1Hl75oeUES2L0DG7iZb6vrdB42LmdXDAdb
Na28IQKBgQCGZ0A73ZE3pV5899/qtYd006zOrZ6L3BAjKJQRAgnCiKbk8flAV4Ij
GRRNwATM0jRQNkl/OfnAG4dnPlGg0/raQatWrX4yac9wk+leo8pl8tceJtRIEVa4
4vsB3HpZmNdNylWYt7JGFG/BVRfOCGTWNjuiw0CneEIE2cm+Ab9d4g==
-----END RSA PRIVATE KEY-----
[*] Your RSA public key:
-----BEGIN PUBLIC KEY-----
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAoGGlxu8ihpmwySW+sSvO
9aaQ2OLlabD0xpEWcb29VmKF3Oj5R07MQ9Q6uSdvtp10nXQ6B1loezHVEU0mEvEa
p1oJhZATxn+SXWfHMylfQ/6+0PIg7IFW+6spIZ8XDX2jeuvU2XlXfVqSzbqykp8Y
mK3UwtyuEBpGmuv4xB0G+puwJ6gqdWXNbclrU2FGdSgViRN6DHyu9Z3RIn5sRygI
NeFjcBrRFb4ZOqYR+VlKxyuSBtsrzZO+1HfsC1Z+XRxHZTqtFHvWqOPe4Htm9xAZ
85l2Xy5Hn4UN8CnWwIjJN67spKg/GdbEZwddiEYEdq0Y9AwykDxrUQGlLrbroc4a
tQIDAQAB
-----END PUBLIC KEY-----
*******************************************************
* PatchSolution0 *
*******************************************************
[*] Previous:
+0x0000000000000070 01 00 00 00 05 00 00 00 ........
+0x0000000000000080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000000000090 00 00 00 00 00 00 00 00 48 56 a2 02 00 00 00 00 ........HV......
+0x00000000000000a0 48 56 a2 02 00 00 00 00 00 10 00 00 00 00 00 00 HV..............
[*] After:
+0x0000000000000070 01 00 00 00 05 00 00 00 ........
+0x0000000000000080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000000000090 00 00 00 00 00 00 00 00 d8 57 a2 02 00 00 00 00 .........W......
+0x00000000000000a0 d8 57 a2 02 00 00 00 00 00 10 00 00 00 00 00 00 .W..............
[*] Previous:
+0x0000000002a25640 00 00 00 00 00 00 00 00 ........
+0x0000000002a25650 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25660 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25670 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25680 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25690 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a256a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a256b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a256c0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a256d0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a256e0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a256f0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25700 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25710 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25720 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25730 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25740 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25750 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25760 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25770 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25780 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a25790 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a257a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a257b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a257c0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
+0x0000000002a257d0 00 00 00 00 00 00 00 00 ........
[*] After:
+0x0000000002a25640 ef be ad de 4d 49 49 42 ....MIIB
+0x0000000002a25650 49 6a 41 4e 42 67 6b 71 68 6b 69 47 39 77 30 42 IjANBgkqhkiG9w0B
+0x0000000002a25660 41 51 45 46 41 41 4f 43 41 51 38 41 4d 49 49 42 AQEFAAOCAQ8AMIIB
+0x0000000002a25670 43 67 4b 43 41 51 45 41 6f 47 47 6c 78 75 38 69 CgKCAQEAoGGlxu8i
+0x0000000002a25680 68 70 6d 77 79 53 57 2b 73 53 76 4f 39 61 61 51 hpmwySW+sSvO9aaQ
+0x0000000002a25690 32 4f 4c 6c 61 62 44 30 78 70 45 57 63 62 32 39 2OLlabD0xpEWcb29
+0x0000000002a256a0 56 6d 4b 46 33 4f 6a 35 52 30 37 4d 51 39 51 36 VmKF3Oj5R07MQ9Q6
+0x0000000002a256b0 75 53 64 76 74 70 31 30 6e 58 51 36 42 31 6c 6f uSdvtp10nXQ6B1lo
+0x0000000002a256c0 65 7a 48 56 45 55 30 6d 45 76 45 61 70 31 6f 4a ezHVEU0mEvEap1oJ
+0x0000000002a256d0 68 5a 41 54 78 6e 2b 53 58 57 66 48 4d 79 6c 66 hZATxn+SXWfHMylf
+0x0000000002a256e0 51 2f 36 2b 30 50 49 67 37 49 46 57 2b 36 73 70 Q/6+0PIg7IFW+6sp
+0x0000000002a256f0 49 5a 38 58 44 58 32 6a 65 75 76 55 32 58 6c 58 IZ8XDX2jeuvU2XlX
+0x0000000002a25700 66 56 71 53 7a 62 71 79 6b 70 38 59 6d 4b 33 55 fVqSzbqykp8YmK3U
+0x0000000002a25710 77 74 79 75 45 42 70 47 6d 75 76 34 78 42 30 47 wtyuEBpGmuv4xB0G
+0x0000000002a25720 2b 70 75 77 4a 36 67 71 64 57 58 4e 62 63 6c 72 +puwJ6gqdWXNbclr
+0x0000000002a25730 55 32 46 47 64 53 67 56 69 52 4e 36 44 48 79 75 U2FGdSgViRN6DHyu
+0x0000000002a25740 39 5a 33 52 49 6e 35 73 52 79 67 49 4e 65 46 6a 9Z3RIn5sRygINeFj
+0x0000000002a25750 63 42 72 52 46 62 34 5a 4f 71 59 52 2b 56 6c 4b cBrRFb4ZOqYR+VlK
+0x0000000002a25760 78 79 75 53 42 74 73 72 7a 5a 4f 2b 31 48 66 73 xyuSBtsrzZO+1Hfs
+0x0000000002a25770 43 31 5a 2b 58 52 78 48 5a 54 71 74 46 48 76 57 C1Z+XRxHZTqtFHvW
+0x0000000002a25780 71 4f 50 65 34 48 74 6d 39 78 41 5a 38 35 6c 32 qOPe4Htm9xAZ85l2
+0x0000000002a25790 58 79 35 48 6e 34 55 4e 38 43 6e 57 77 49 6a 4a Xy5Hn4UN8CnWwIjJ
+0x0000000002a257a0 4e 36 37 73 70 4b 67 2f 47 64 62 45 5a 77 64 64 N67spKg/GdbEZwdd
+0x0000000002a257b0 69 45 59 45 64 71 30 59 39 41 77 79 6b 44 78 72 iEYEdq0Y9AwykDxr
+0x0000000002a257c0 55 51 47 6c 4c 72 62 72 6f 63 34 61 74 51 49 44 UQGlLrbroc4atQID
+0x0000000002a257d0 41 51 41 42 ad de ef be AQAB....
[*] Previous:
+0x000000000141fbf0 44 0f b6 24 18 48 8b 44 24 28 8b 50 f8 85 d2 79 D..$.H.D$(.P...y
+0x000000000141fc00 6f o
[*] After:
+0x000000000141fbf0 45 31 e4 48 8d 05 52 5a 60 01 90 90 90 90 90 90 E1.H..RZ`.......
+0x000000000141fc00 90 .
[*] New RSA-2048 private key has been saved to
/home/hollowman/navicat-keygen/RegPrivateKey.pem
*******************************************************
* PATCH HAS BEEN DONE SUCCESSFULLY! *
* HAVE FUN AND ENJOY~ *
*******************************************************
五、将文件重新打包成AppImage
修改公钥之后,再重新打包成AppImage应用程序,就可以运行并完成JH工作了。
打包成AppImage需要用到打包工具:appimagetool-x86_64.AppImage。
hollowman@hollowman-F117:~/navicat-keygen$ cd ..
hollowman@hollowman-F117:~$ wget 'https://github.com/AppImage/AppImageKit/releases/download/continuous/appimagetool-x86_64.AppImage'
hollowman@hollowman-F117:~$ chmod +x appimagetool-x86_64.AppImage
hollowman@hollowman-F117:~$ ./appimagetool-x86_64.AppImage navicat15-premium-cs-bak/ navicat15-premium-cs-2.AppImage
六、运行修改打包后的AppImage应用程序
hollowman@hollowman-F117:~$ chmod +x ~/Desktop/navicat15-premium-en-patched.AppImage
hollowman@hollowman-F117:~$ ./navicat15-premium-cs-2.AppImag
出现注册界面,暂时保留界面,进入第七步。
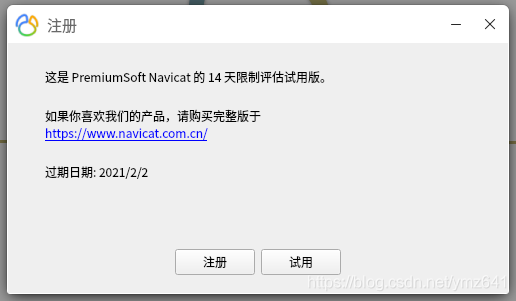
在这里插入图片描述
七、使用 navicat-keygen 来生成序列号和JH码。
语法: navicat-keygen <--bin|--text> [--adv] <RSA-2048 Private Key File>
回到家目录,右键新建一个终端,并切换至navicat-keygen子目录
hollowman@hollowman-F117:~$ cd navicat-keygen
hollowman@hollowman-F117:~/navicat-keygen$ ./bin/navicat-keygen --text ./RegPrivateKey.pem
按提示选择Navicat产品类别(1.Premium)、Navicat语言版本(1.)和填写主版本号(15),随后生成一个序列号,输入用户名和组织,出现Input request code in Base64: (Double press ENTER to end)
保留界面,进入第八步。
hollowman@hollowman-F117:~/navicat-keygen$ ./bin/navicat-keygen --text ./RegPrivateKey.pem
**********************************************************
* Navicat Keygen (Linux) by @DoubleLabyrinth *
* Version: 1.0 *
**********************************************************
[*] Select Navicat product:
0. DataModeler
1. Premium
2. MySQL
3. PostgreSQL
4. Oracle
5. SQLServer
6. SQLite
7. MariaDB
8. MongoDB
9. ReportViewer
(Input index)> 1
[*] Select product language:
0. English
1. Simplified Chinese
2. Traditional Chinese
3. Japanese
4. Polish
5. Spanish
6. French
7. German
8. Korean
9. Russian
10. Portuguese
(Input index)> 1
[*] Input major version number:
(range: 0 ~ 15, default: 12)> 15
[*] Serial number:
NAVI-EL2T-KC4E-AXSB
[*] Your name: hollowman
[*] Your organization: hollowman.cn
[*] Input request code in Base64: (Double press ENTER to end) #下面的内容来自第八步
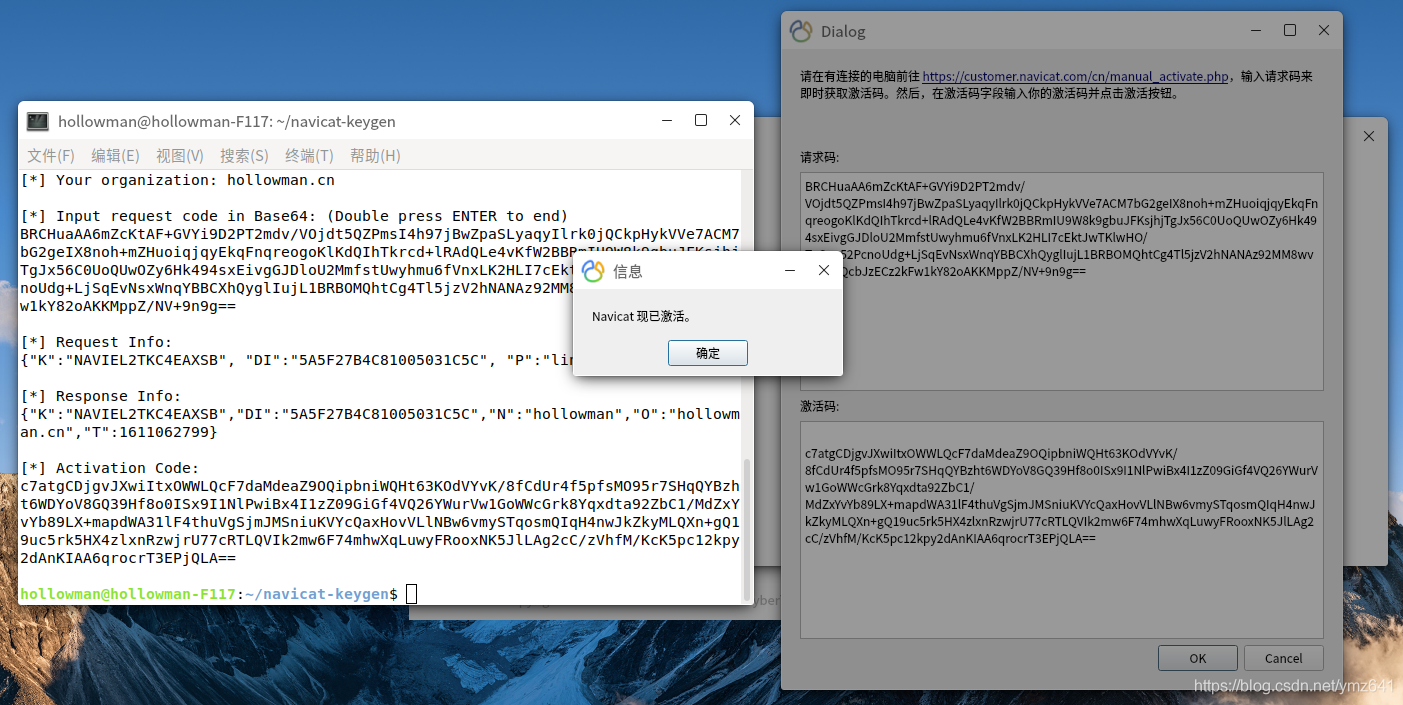
BRCHuaAA6mZcKtAF+GVYi9D2PT2mdv/VOjdt5QZPmsI4h97jBwZpaSLyaqyIlrk0jQCkpHykVVe7ACM7bG2geIX8noh+mZHuoiqjqyEkqFnqreogoKlKdQIhTkrcd+lRAdQLe4vKfW2BBRmIU9W8k9gbuJFKsjhjTgJx56C0UoQUwOZy6Hk494sxEivgGJDloU2MmfstUwyhmu6fVnxLK2HLI7cEktJwTKlwHO/TpSan52PcnoUdg+LjSqEvNsxWnqYBBCXhQyglIujL1BRBOMQhtCg4Tl5jzV2hNANAz92MM8wvuX+E2QcbJzECz2kFw1kY82oAKKMppZ/NV+9n9g==
[回车][回车]
[*] Request Info:
{"K":"NAVIEL2TKC4EAXSB", "DI":"5A5F27B4C81005031C5C", "P":"linux"}
[*] Response Info:
{"K":"NAVIEL2TKC4EAXSB","DI":"5A5F27B4C81005031C5C","N":"hollowman","O":"hollowman.cn","T":1611062799}
[*] Activation Code: #将以下代码复制到第八步手动JH窗口的JH码中
c7atgCDjgvJXwiItxOWWLQcF7daMdeaZ9OQipbniWQHt63KOdVYvK/8fCdUr4f5pfsMO95r7SHqQYBzht6WDYoV8GQ39Hf8o0ISx9I1NlPwiBx4I1zZ09GiGf4VQ26YWurVw1GoWWcGrk8Yqxdta92ZbC1/MdZxYvYb89LX+mapdWA31lF4thuVgSjmJMSniuKVYcQaxHovVLlNBw6vmySTqosmQIqH4nwJkZkyMLQXn+gQ19uc5rk5HX4zlxnRzwjrU77cRTLQVIk2mw6F74mhwXqLuwyFRooxNK5JlLAg2cC/zVhfM/KcK5pc12kpy2dAnKIAA6qrocrT3EPjQLA==
八、输入序列号注册(会提示注册失败)并转入手动JH
1.断开网络. 找到第六步未关闭的注册窗口,填写keygen给你的 序列号。
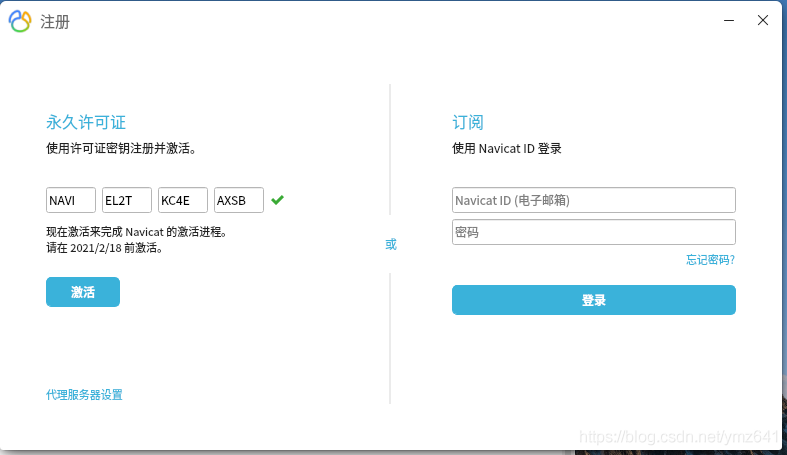
2.一般会提示失败,在弹出的提示中选择手动,弹出如下窗口。
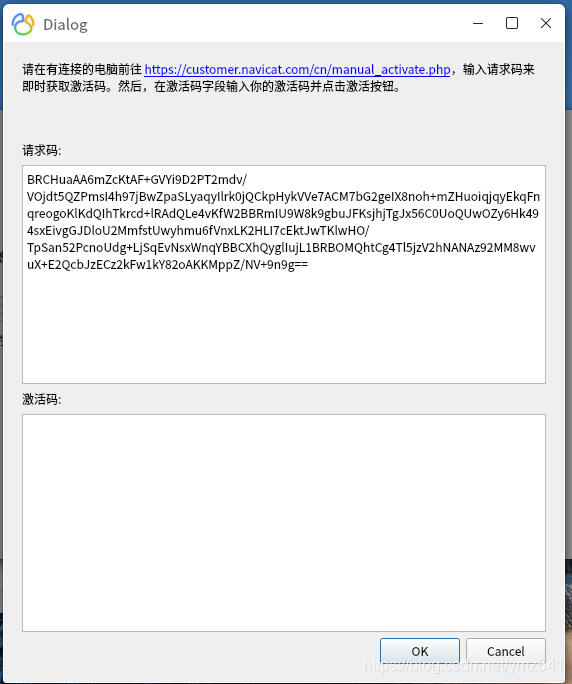
3.复制请求码中的字符串到第七步中新建的终端,也就是Input request code in Base64: (Double press ENTER to end)下面,连续2次回车
4.回车后,终端中将生成一串JH码,复制粘贴到手动JH窗口,点击OK
九、使用
至此,只要切换到navicat15-premium-cs-2.AppImage所在目录,并运行它,就可以正常使用了。
当然,你也可以将该应用程序移动或复制到你想要保存的目录。一个打包的文件完成一个应用程序的工作,只能再次用“惊喜”来形容。
hollowman@hollowman-F117:~$ ./navicat15-premium-cs-2.AppImage
效果图1张:

参考资源:
https://gitee.com/andisolo/navicat-keygen
https://appimage.org/
原文链接:https://blog.csdn.net/ymz641/article/details/112853932