一、官方kubernetes-dashboard.yaml简介###
①首先认识一下官方的kubernetes-dashboard.yaml,我们先下载:
https://github.com/kubernetes/dashboard/blob/v1.10.0/src/deploy/recommended/kubernetes-dashboard.yaml
[root@K8s-Master test]# wget https://raw.githubusercontent.com/kubernetes/dashboard/v1.10.1/src/deploy/recommended/kubernetes-dashboard.yaml
该文件分为以下几部分:
Dashboard Secret
Dashboard Service Account
Dashboard Role & Role Binding
Dashboard Deployment
Dashboard Service
这里,我们简单的对各个部分的功能进行介绍:
# ------------------- Dashboard Secret ------------------- #
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-certs
namespace: kube-system
type: Opaque
---
# ------------------- Dashboard Service Account ------------------- #
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
---
如上定义了Dashboard的用户,其类型为ServiceAccount,名称为kubernetes-dashboard。
# ------------------- Dashboard Role & Role Binding ------------------- #
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
# Allow Dashboard to create 'kubernetes-dashboard-key-holder' secret.
- apiGroups: [""]
resources: ["secrets"]
verbs: ["create"]
# Allow Dashboard to create 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["create"]
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics from heapster.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard-minimal
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
---
如上定义了Dashboard 的角色,其角色名称为kubernetes-dashboard-minimal,rules中清晰的列出了其拥有的多个权限。通过名称我们可以猜到,这个权限级别是比较低的。
如上定义了Dashboard的角色绑定,其名称为kubernetes-dashboard-minimal,roleRef中为被绑定的角色,也叫kubernetes-dashboard-minimal,subjects中为绑定的用户:kubernetes-dashboard。
# ------------------- Dashboard Deployment ------------------- #
kind: Deployment
apiVersion: apps/v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
spec:
containers:
- name: kubernetes-dashboard
image: k8s.gcr.io/kubernetes-dashboard-amd64:v1.10.1
ports:
- containerPort: 8443
protocol: TCP
args:
- --auto-generate-certificates
# Uncomment the following line to manually specify Kubernetes API server Host
# If not specified, Dashboard will attempt to auto discover the API server and connect
# to it. Uncomment only if the default does not work.
# - --apiserver-host=http://my-address:port
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
# Create on-disk volume to store exec logs
- mountPath: /tmp
name: tmp-volume
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {}
serviceAccountName: kubernetes-dashboard
# Comment the following tolerations if Dashboard must not be deployed on master
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
---
将其中的镜像替换成国内的镜像:
k8s.gcr.io/kubernetes-dashboard-amd64 替换成
image: registry.cn-hangzhou.aliyuncs.com/google_containers/kubernetes-dashboard-amd64:v1.10.0
如上可以看到,Dashboard的Deployment指定了其使用的ServiceAccount是kubernetes-dashboard。并且还将Secret kubernetes-dashboard-certs通过volumes挂在到pod内部的/certs路径。为何要挂载Secret ?原因是创建Secret 时会自动生成token。请注意参数--auto-generate-certificates,其表示Dashboard会自动生成证书。
# ------------------- Dashboard Service ------------------- #
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
ports:
- port: 443
targetPort: 8443
selector:
k8s-app: kubernetes-dashboard
二、部署Dashboard###
kubectl create -f kubernetes-dashboard.yaml
重新安装dashboard
kubectl delete -f kubernetes-dashboard.yaml
kubectl create -f kubernetes-dashboard.yaml
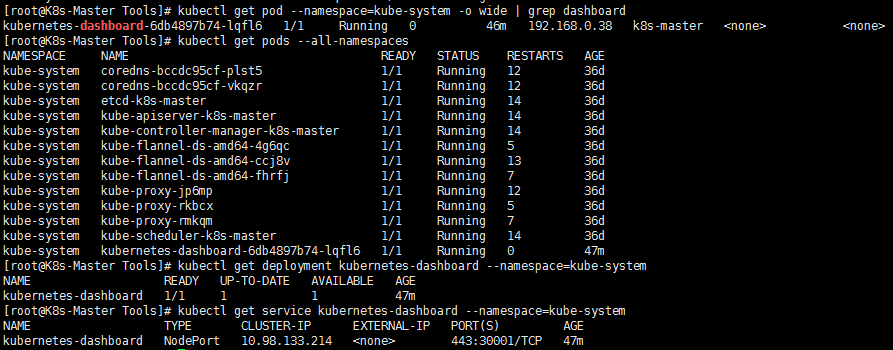
查看Pod 的状态为running说明dashboard已经部署成功:
kubectl get pod --namespace=kube-system -o wide | grep dashboard
kubectl get pods --all-namespaces
Dashboard 会在 kube-system namespace 中创建自己的 Deployment 和 Service:
kubectl get deployment kubernetes-dashboard --namespace=kube-system
kubectl get service kubernetes-dashboard --namespace=kube-system
遇到的错误:###
完成了上述操作却发现还是CrashLoopBackOff的错误

使用命令查看错误原因:
kubectl --namespace=kube-system describe pod <pod_name>
发现pod运行在副节点k8s-node1上,需要将dashboard调度到master节点上去。
输入命令,为master节点添加label
kubectl label node k8s-master type=master
在kubernetes-dashboard.yaml中添加nodeSelecor定义:
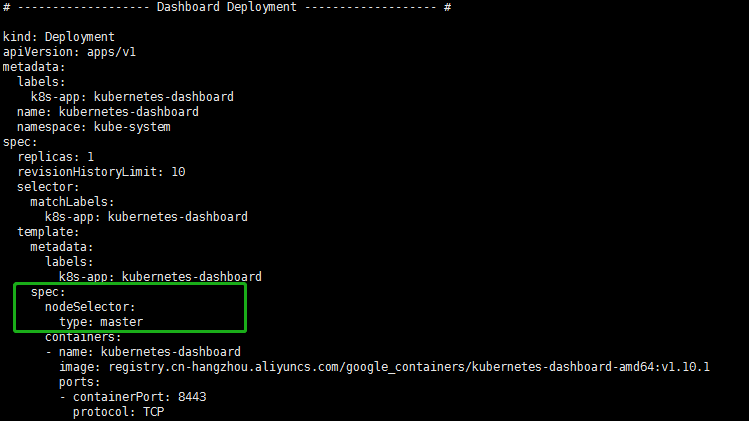
配置完成之后,再重新安装dashboard,发现问题得到了解决。
三、访问Dashboard###
根据官方文档,目前访问Dashboard有四种方式:
①NodePort
②kubectl proxy
③API Server
④Ingress
以上四种方式,我测试了前两种,目前NodePort和kubectl proxy可用。
①使用NodePort
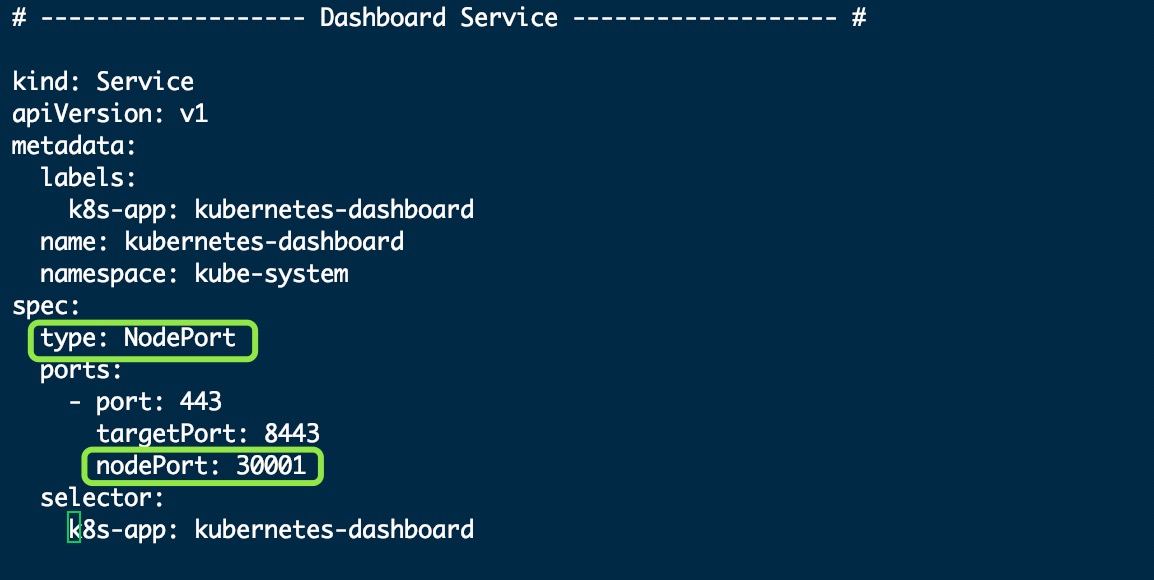
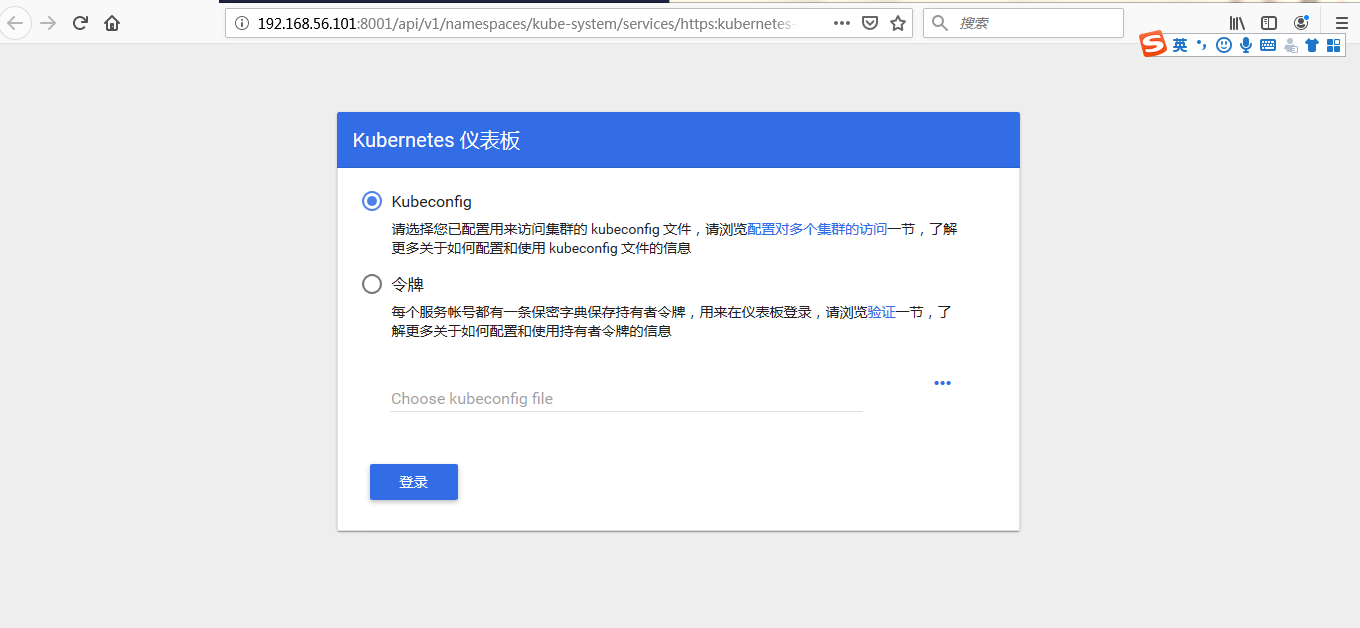
为kubernetes-dashboard.yaml添加Service后,就可以使用NodePort访问Dashboard。在我们的物理机上,使用Firefox访问https://192.168.56.101:30001/,结果如下图所示:

选择令牌方式获取token登录:
kubectl -n kube-system describe secret $(kubectl -n kube-system get secret | grep kubernetes-dashboard | awk '{print $1}')

②使用kubectl proxy
这里,我主要介绍一下最便捷的kubectl proxy方式。在Master上执行kubecll proxy,然后使用如下地址访问Dashboard:
http://localhost:8001/api/v1/namespaces/kube-system/services/https:kubernetes-dashboard:/proxy
但限制就是必须在Master上访问,这显然是个坑,我们的目标是在我们真实的物理机上去访问Master的Dashboard。
所以,在主节点上,我们执行kubectl proxy --address=192.168.56.101 --disable-filter=true开启代理。
其中:
address表示外界可以使用192.168.56.101来访问Dashboard,我们也可以使用0.0.0.0
disable-filter=true表示禁用请求过滤功能,否则我们的请求会被拒绝,并提示 Forbidden (403) Unauthorized。
我们也可以指定端口,具体请查看kubectl proxy --help
如下图所示,proxy默认对Master的8001端口进行监听:
这样,我们就可以使用如下地址访问登录界面:
http://192.168.56.101:8001/api/v1/namespaces/kube-system/services/https:kubernetes-dashboard:/proxy/#!/login
遇到的问题:获取的token值登录无效###
我们回想本文第三小节对kubernetes-dashboard.yaml的介绍,现在就理解了为什么其角色的名称为kubernetes-dashboard-minimal。一句话,这个Role的权限不够!
这个报错的原因是因为我们没有权限去访问Kubernetes仪表盘。
1⃣️我们可以在Bash中运行如下命令来解决上述问题:
kubectl create clusterrolebinding kubernetes-dashboard --clusterrole=cluster-admin --serviceaccount=kube-system:kubernetes-dashboard
或者
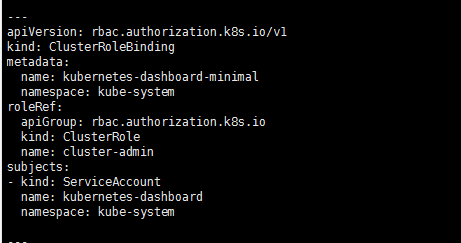
2⃣️我们可以更改RoleBinding修改为ClusterRoleBinding,并且修改roleRef中的kind和name,使用cluster-admin这个非常牛逼的CusterRole(超级用户权限,其拥有访问kube-apiserver的所有权限)。如下:
修改后,重新安装kubernetes-dashboard.yaml,Dashboard就可以拥有访问整个K8S 集群API的权限。
3⃣️kubernetes-dashboard卸载
kubectl delete deployment kubernetes-dashboard --namespace=kube-system
kubectl delete service kubernetes-dashboard --namespace=kube-system
kubectl delete role kubernetes-dashboard-minimal --namespace=kube-system
kubectl delete rolebinding kubernetes-dashboard-minimal --namespace=kube-system
kubectl delete sa kubernetes-dashboard --namespace=kube-system
kubectl delete secret kubernetes-dashboard-certs --namespace=kube-system
kubectl delete secret kubernetes-dashboard-csrf --namespace=kube-system
kubectl delete secret kubernetes-dashboard-key-holder --namespace=kube-system
参考链接:
kubernetes部署dashboard可视化插件.
kubernetes安装dashboard步骤.
Centos7 单节点上安装kubernetes-dashboard过程.
kubeadm部署kubernetes 1.13.1集群.
dashboard-ui.
kubernetes github.