杂烩/Misc Chowder
题目附件:
链接:https://pan.baidu.com/s/1Wb6cCIUundA-rCmQ-eJNLw
提取码:tk2t
比赛放的hint:
1、流量包中的网络连接对解题没有帮助 The network connection in pcap is not helping to the challenge
2、不需要访问流量里任何一个的服务器地址,所有数据都可以从流量包里直接提取 Do not need to connect the network, every data can be extracted from the pcap
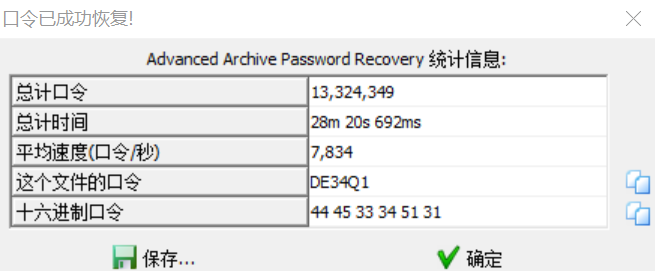
3、In the burst test point of compressed packet password, the length of the password is 6, and the first two characters are “D” and “E”. 压缩包密码暴破考点中,密码的长度为6位,前两位为DE
1、用foremosr分离出6张模模糊糊的jpg
2、导出http对象,扒出6张jpg和1张链接png
png图片中的链接如下:
https://drive.google.com/file/d/1JBdPj7eRaXuLCTFGn7AluAxmxQ4k1jvX/view
下载后得到readme.docx,binwalk分离出一个加密的You_found_me_Orz.zip
根据后来放的hint,掩码爆破,睡一觉,爆出来了
从You_found_me_Orz.zip中的jpg分离出rar
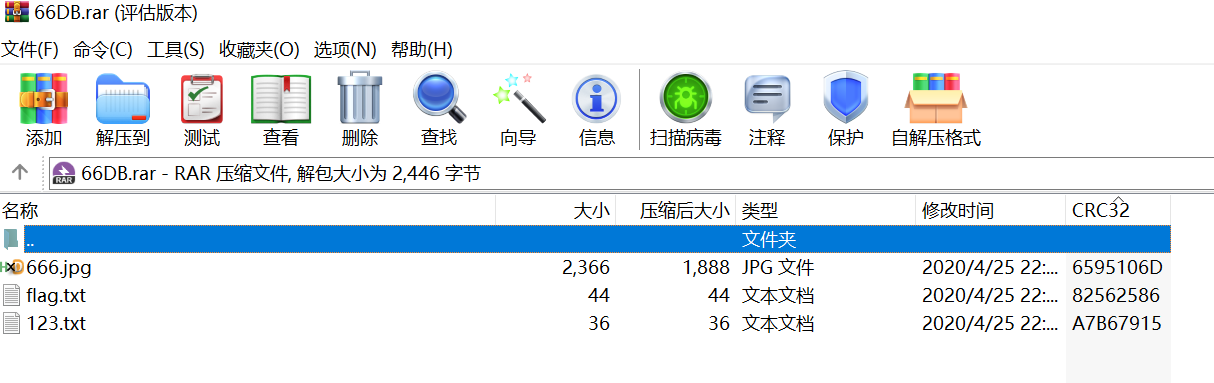
但是666.jpg在ubuntu打不开,用file命令得知是png(也能用HxD看出)
3、666.png是ADS隐写,用ntfsstreamseditor.exe能看到
life
链接:https://pan.baidu.com/s/14S_ddf1i6u1LWmrlC43-Lg
提取码:j52i
题目描述:No Game No Life!
1、在game.jpg中分离出一个加密的flag.zip和passphare.png
2、这个png是27*27的,确定不是二维码
赛后知道有个生命游戏模拟器
手动填充点点
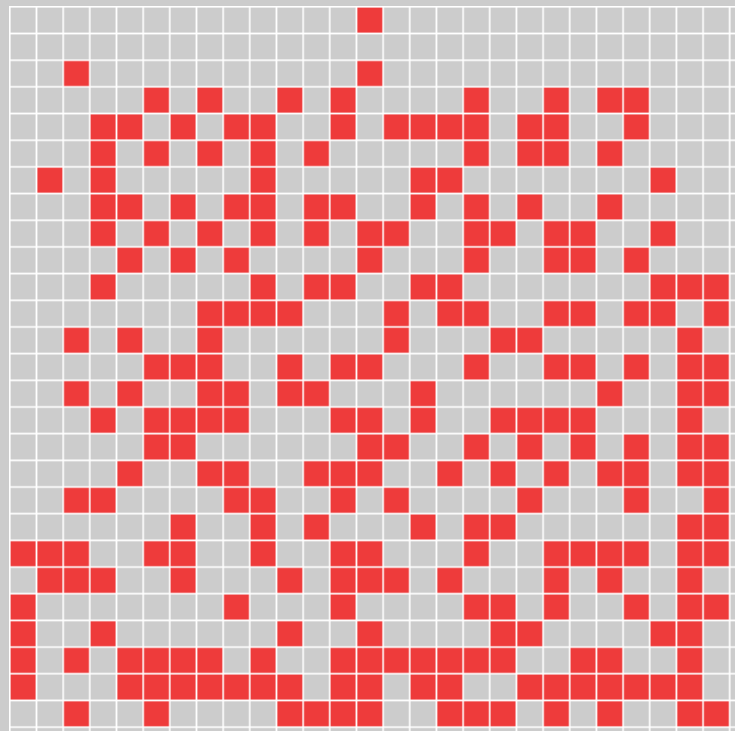
点击单步,得到:
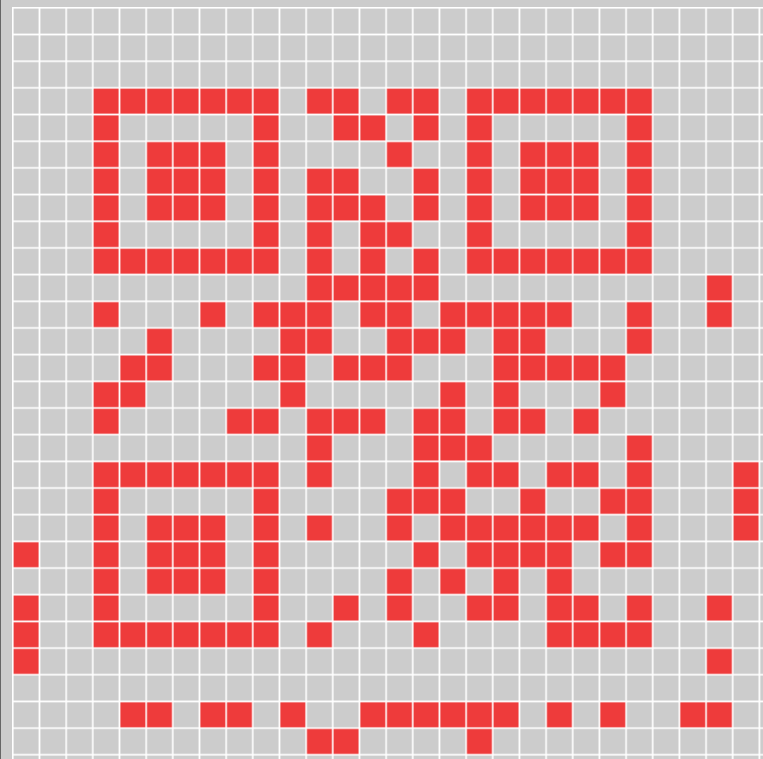
扫出:AJTC8ADEVRA13AR,能解开flag.zip
3、解开是txt.pilf.txt,flip意为翻转
0QjN1MTM0MTN0QjN3ImNjNzM3QTNmdTN3MTNmdzMzcjNxcjM3QTNmdDN2gzMzUjZ2czM0YDZzMjMxcDZ
str = "0QjN1MTM0MTN0QjN3ImNjNzM3QTNmdTN3MTNmdzMzcjNxcjM3QTNmdDN2gzMzUjZ2czM0YDZzMjMxcDZ"
print(str[::-1])
ZDcxMjMzZDY0Mzc2ZjUzMzg2NDdmNTQ3MjcxNjczMzdmNTM3NTdmNTQ3MzNjNmI3NjQ0NTM0MTM1NjQ0
base64 decode得到:d71233d64376f5338647f54727167337f53757f54733c6b7644534135644
再翻转,得到:4465314354467b6c33745f75735f73376172745f7468335f67346d33217d
hex转ascii。
Easy Protocol
这道题俺一点思路都没有,有一些内网的东西
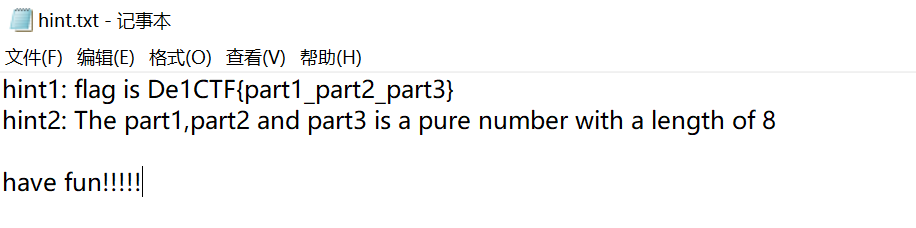
hint.txt的意思就是flag的3部分都是8位纯数字
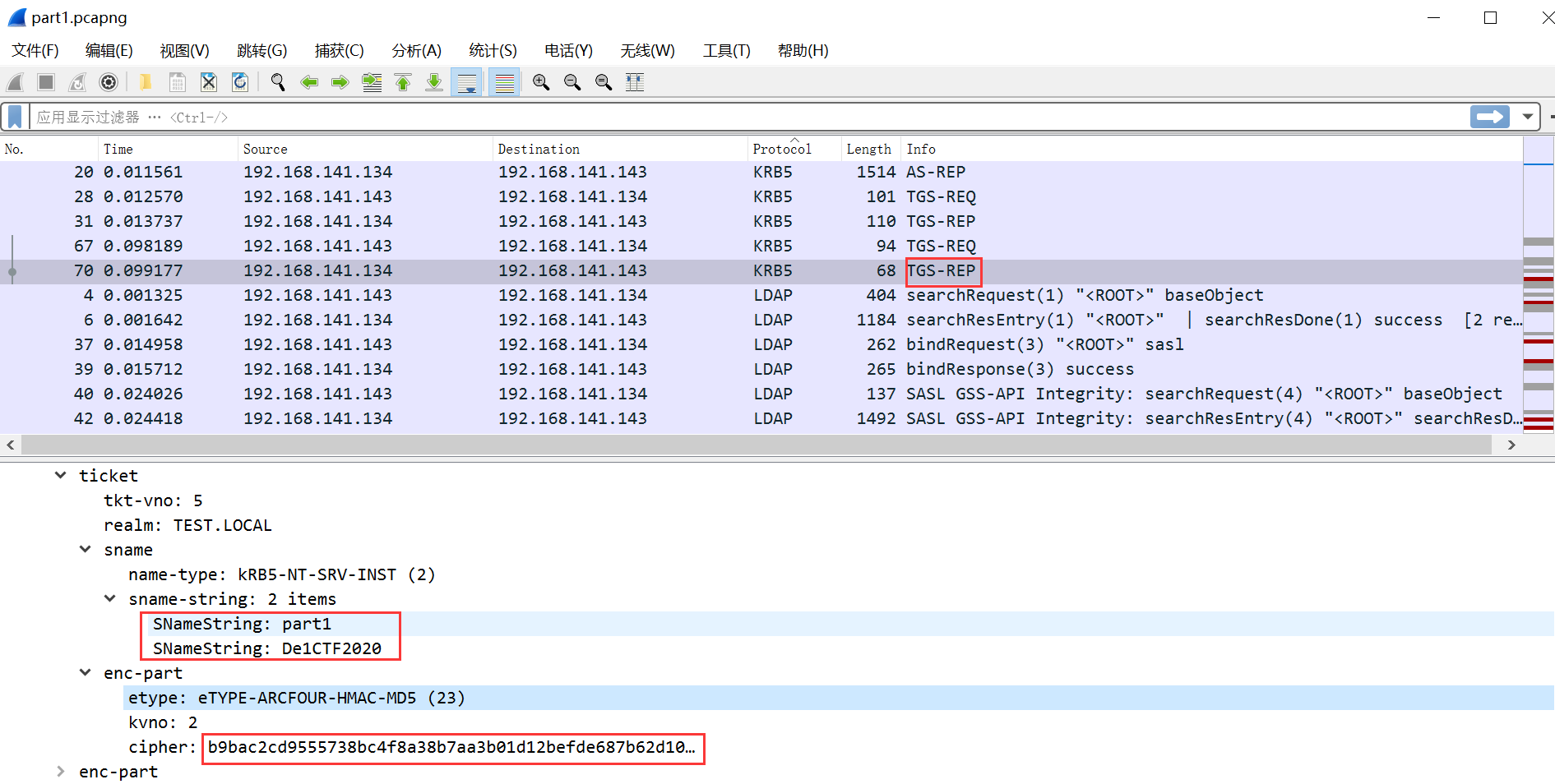
part1.pcapng
1、par1.pcapng中出现了tcp、ldap、krb5协议,Ctrl+F,看到67和70帧都有De1ctf关键字,将protocol排序
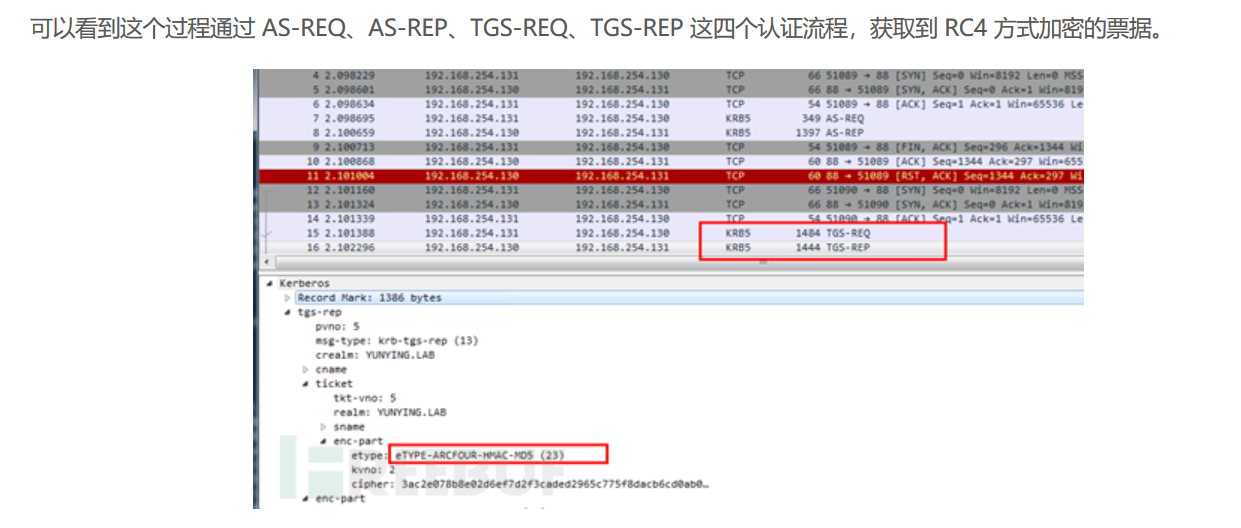
搜一下这个kerberos协议
kerberos协议参考:
Kerberos协议探索系列之扫描与爆破篇
Windows内网协议学习Kerberos篇之TGSREQ& TGSREP
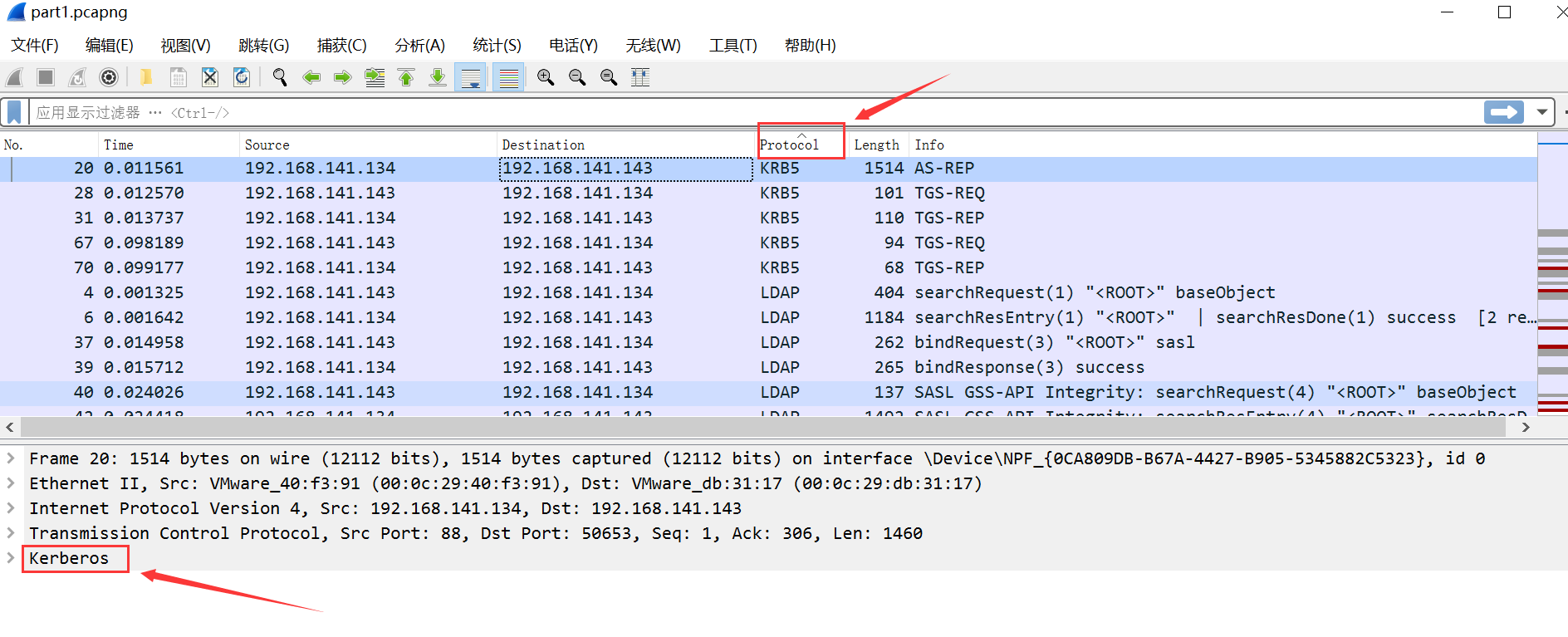
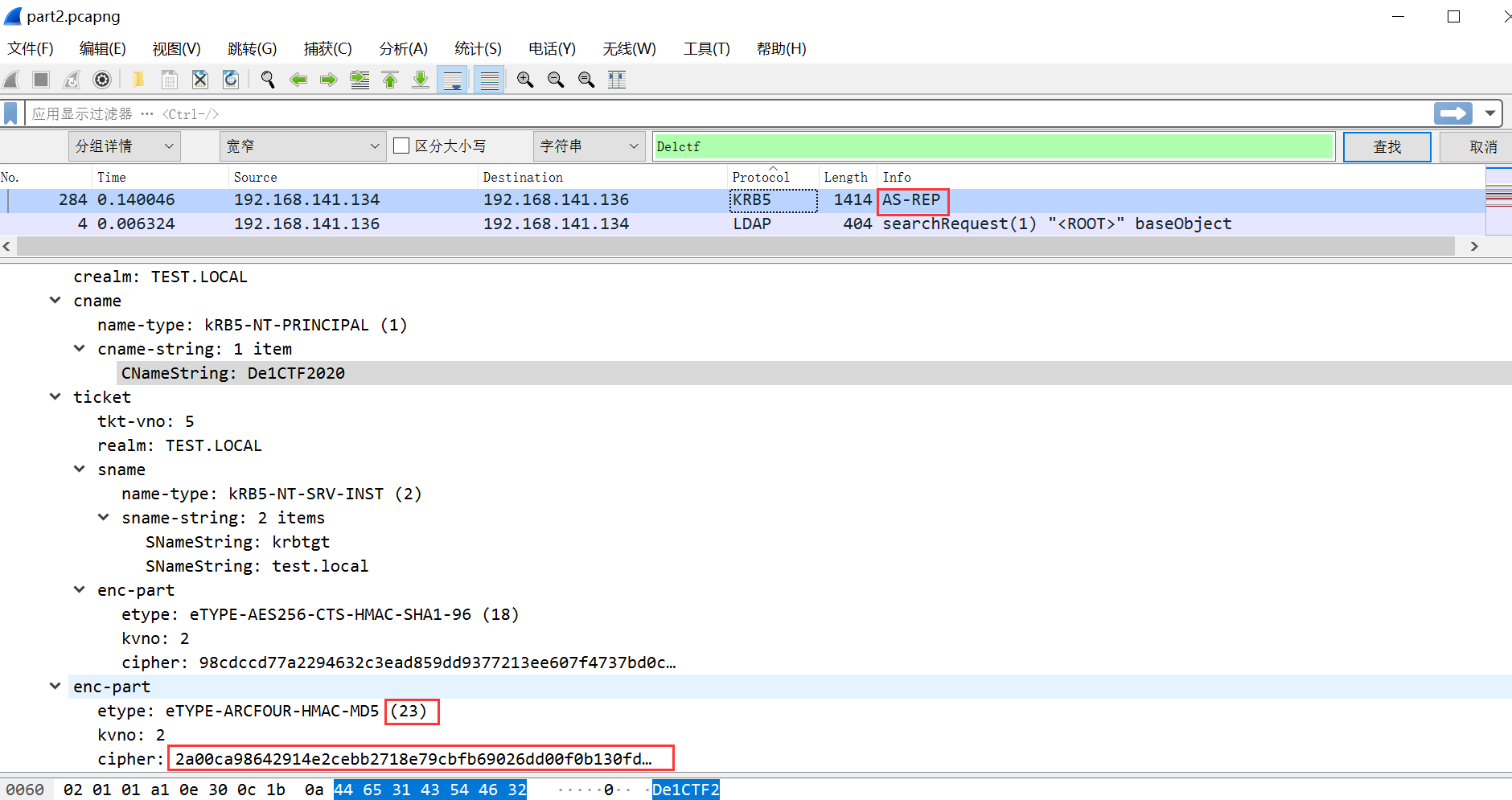
hashcat爆破参考:https://www.freebuf.com/sectool/164507.html
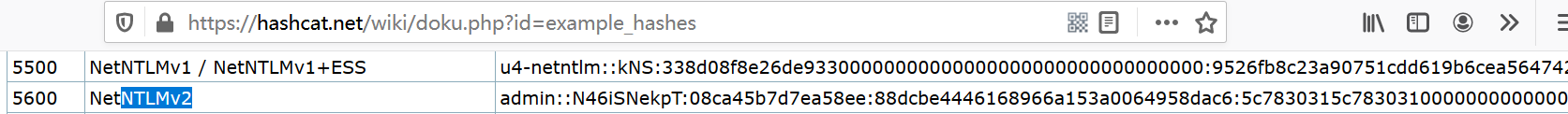
在hashcat wiki找到kerberos 5的格式:
构造好hashcat支持的hash值,part1:
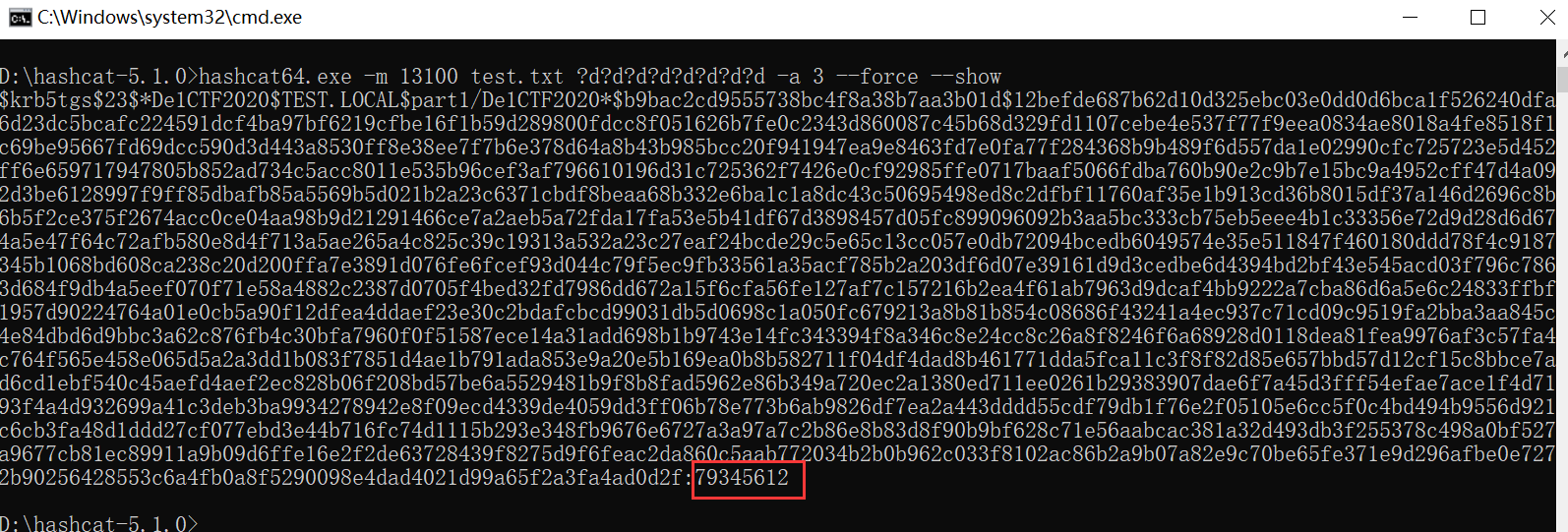
$krb5tgs(23)De1CTF2020(TEST.LOCAL)part1/De1CTF2020$b9bac2cd9555738bc4f8a38b7aa3b01d12befde687b62d10d325ebc03e0dd0d6bca1f526240dfa6d23dc5bcafc224591dcf4ba97bf6219cfbe16f1b59d289800fdcc8f051626b7fe0c2343d860087c45b68d329fd1107cebe4e537f77f9eea0834ae8018a4fe8518f1c69be95667fd69dcc590d3d443a8530ff8e38ee7f7b6e378d64a8b43b985bcc20f941947ea9e8463fd7e0fa77f284368b9b489f6d557da1e02990cfc725723e5d452ff6e659717947805b852ad734c5acc8011e535b96cef3af796610196d31c725362f7426e0cf92985ffe0717baaf5066fdba760b90e2c9b7e15bc9a4952cff47d4a092d3be6128997f9ff85dbafb85a5569b5d021b2a23c6371cbdf8beaa68b332e6ba1c1a8dc43c50695498ed8c2dfbf11760af35e1b913cd36b8015df37a146d2696c8b6b5f2ce375f2674acc0ce04aa98b9d21291466ce7a2aeb5a72fda17fa53e5b41df67d3898457d05fc899096092b3aa5bc333cb75eb5eee4b1c33356e72d9d28d6d674a5e47f64c72afb580e8d4f713a5ae265a4c825c39c19313a532a23c27eaf24bcde29c5e65c13cc057e0db72094bcedb6049574e35e511847f460180ddd78f4c9187345b1068bd608ca238c20d200ffa7e3891d076fe6fcef93d044c79f5ec9fb33561a35acf785b2a203df6d07e39161d9d3cedbe6d4394bd2bf43e545acd03f796c7863d684f9db4a5eef070f71e58a4882c2387d0705f4bed32fd7986dd672a15f6cfa56fe127af7c157216b2ea4f61ab7963d9dcaf4bb9222a7cba86d6a5e6c24833ffbf1957d90224764a01e0cb5a90f12dfea4ddaef23e30c2bdafcbcd99031db5d0698c1a050fc679213a8b81b854c08686f43241a4ec937c71cd09c9519fa2bba3aa845c4e84dbd6d9bbc3a62c876fb4c30bfa7960f0f51587ece14a31add698b1b9743e14fc343394f8a346c8e24cc8c26a8f8246f6a68928d0118dea81fea9976af3c57fa4c764f565e458e065d5a2a3dd1b083f7851d4ae1b791ada853e9a20e5b169ea0b8b582711f04df4dad8b461771dda5fca11c3f8f82d85e657bbd57d12cf15c8bbce7ad6cd1ebf540c45aefd4aef2ec828b06f208bd57be6a5529481b9f8b8fad5962e86b349a720ec2a1380ed711ee0261b29383907dae6f7a45d3fff54efae7ace1f4d7193f4a4d932699a41c3deb3ba9934278942e8f09ecd4339de4059dd3ff06b78e773b6ab9826df7ea2a443dddd55cdf79db1f76e2f05105e6cc5f0c4bd494b9556d921c6cb3fa48d1ddd27cf077ebd3e44b716fc74d1115b293e348fb9676e6727a3a97a7c2b86e8b83d8f90b9bf628c71e56aabcac381a32d493db3f255378c498a0bf527a9677cb81ec89911a9b09d6ffe16e2f2de63728439f8275d9f6feac2da860c5aab772034b2b0b962c033f8102ac86b2a9b07a82e9c70be65fe371e9d296afbe0e7272b90256428553c6a4fb0a8f5290098e4dad4021d99a65f2a3fa4ad0d2f
hashcat64.exe -m 13100 test1.txt ?d?d?d?d?d?d?d?d -a 3 --force --show
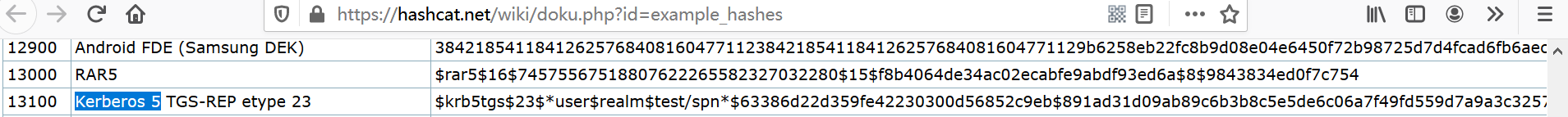
part2.pcapng
Ctrl+F,搜索关键字De1ctf
有关kerberos协议的ASREQ & ASREP认证模块,参考:Windows内网协议学习Kerberos篇之ASREQ& ASREP
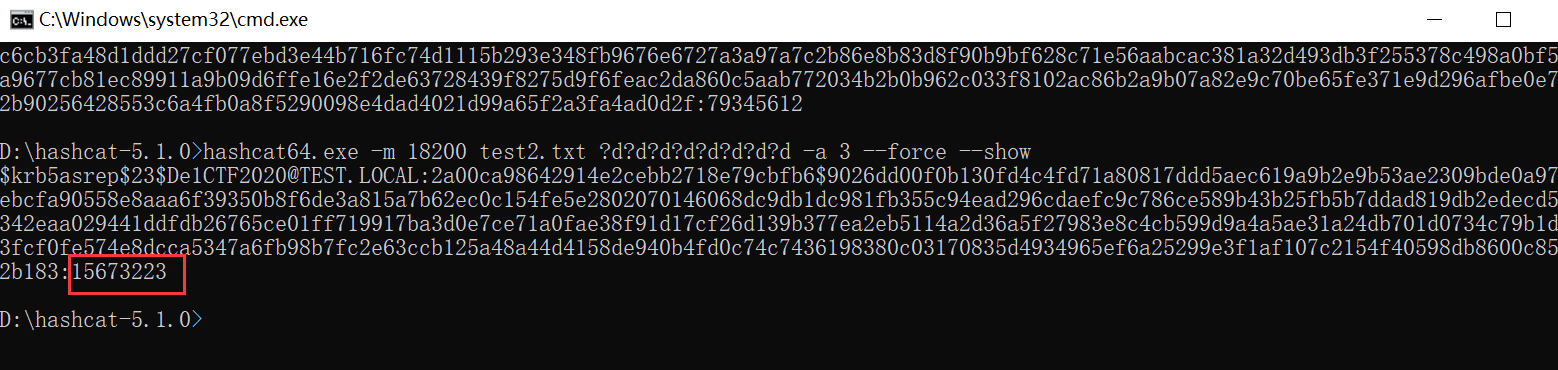
part2:$krb5asrep(23)De1CTF2020@TEST.LOCAL:2a00ca98642914e2cebb2718e79cbfb6$9026dd00f0b130fd4c4fd71a80817ddd5aec619a9b2e9b53ae2309bde0a9796ebcfa90558e8aaa6f39350b8f6de3a815a7b62ec0c154fe5e2802070146068dc9db1dc981fb355c94ead296cdaefc9c786ce589b43b25fb5b7ddad819db2edecd573342eaa029441ddfdb26765ce01ff719917ba3d0e7ce71a0fae38f91d17cf26d139b377ea2eb5114a2d36a5f27983e8c4cb599d9a4a5ae31a24db701d0734c79b1d323fcf0fe574e8dcca5347a6fb98b7fc2e63ccb125a48a44d4158de940b4fd0c74c7436198380c03170835d4934965ef6a25299e3f1af107c2154f40598db8600c855b2b183
hashcat64.exe -m 18200 test2.txt ?d?d?d?d?d?d?d?d -a 3 --force --show
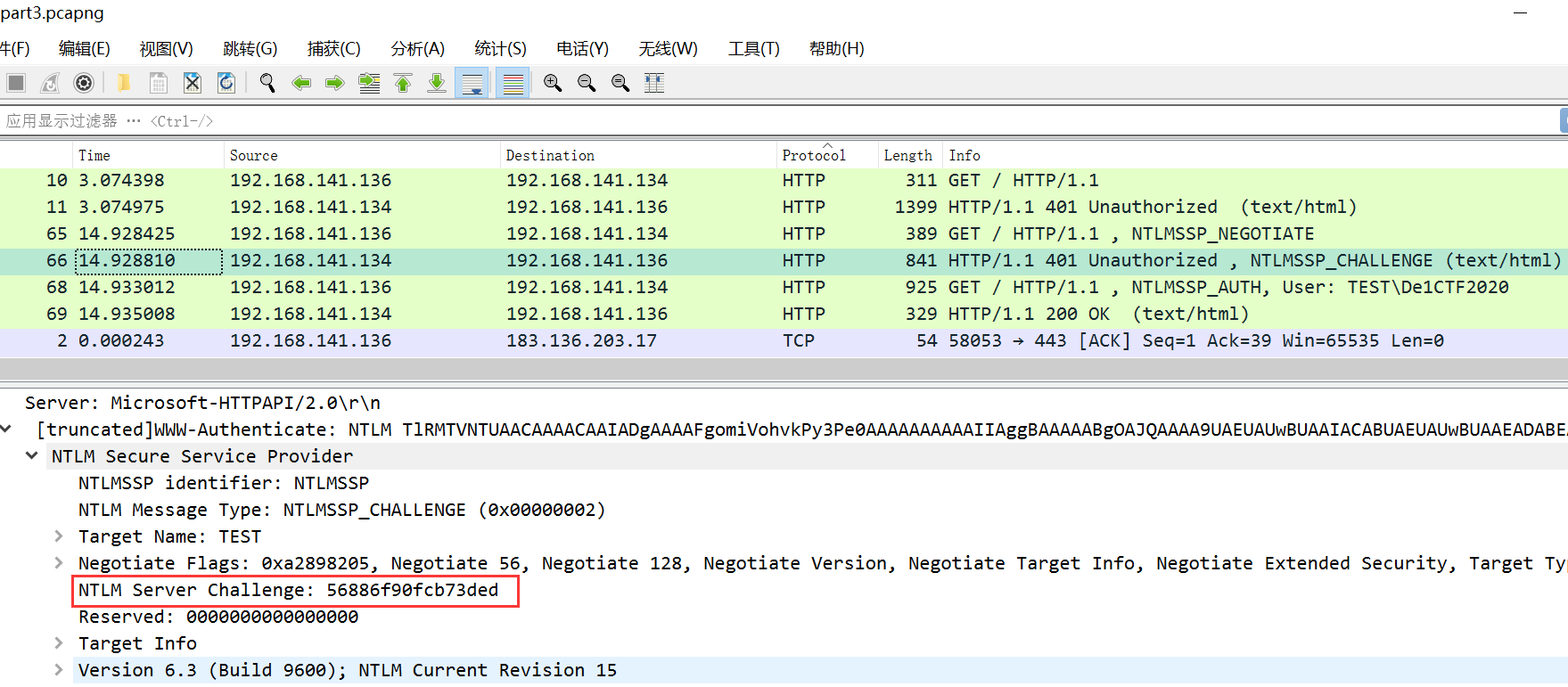
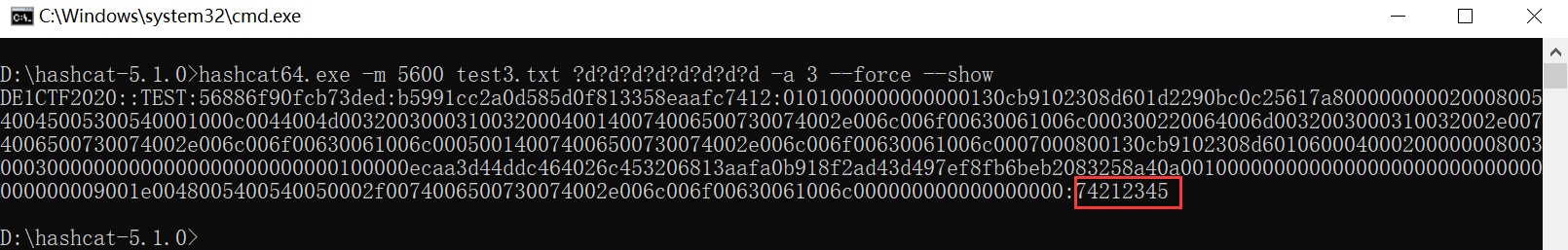
part3.pcapng
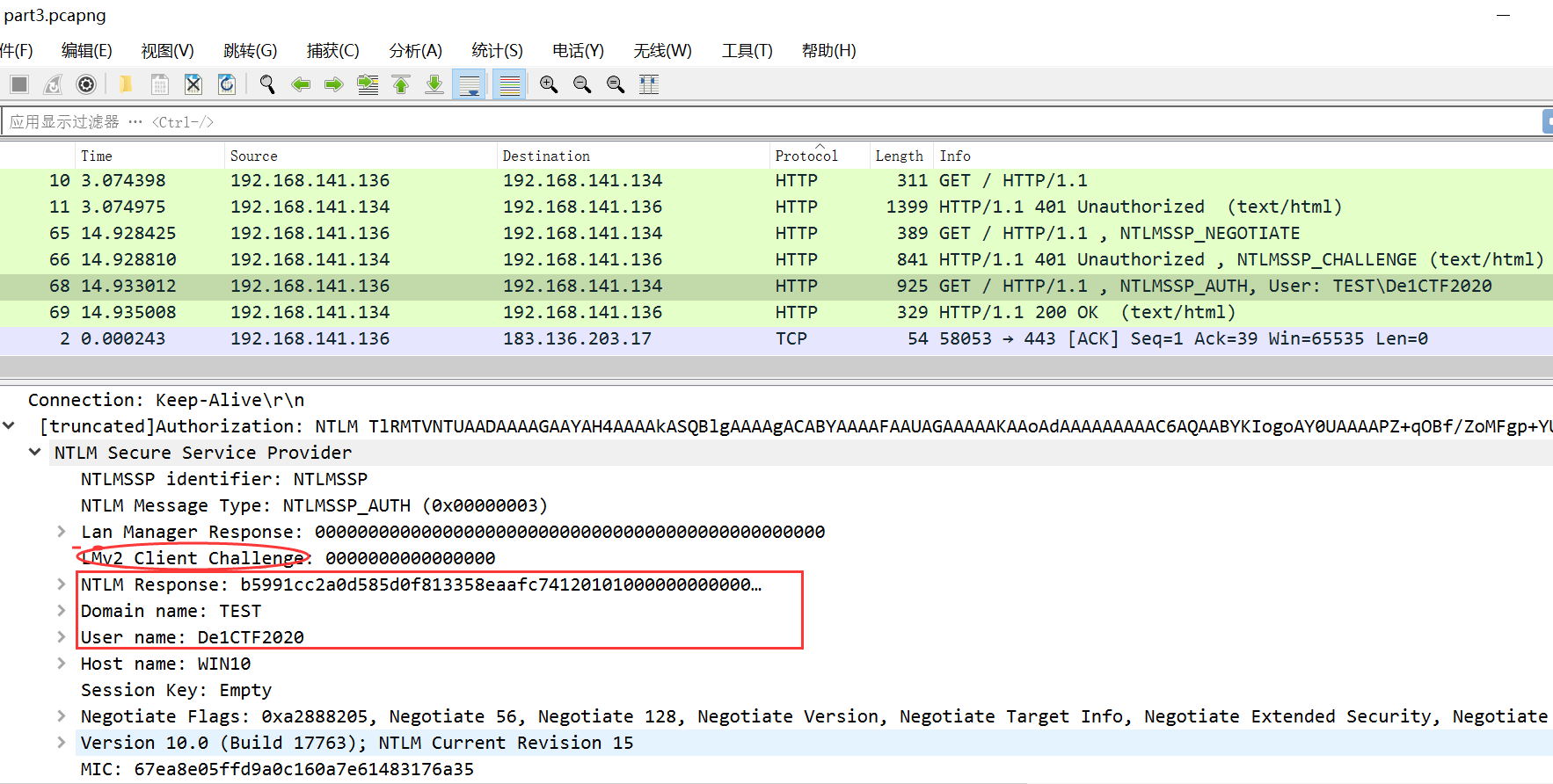
Ctrl+F,在第68,69帧找到De1ctf关键字,搜搜这个NTLM,存在NTML身份认证(参考:Windows身份认证及利用思路
Windows下的密码hash——NTLM hash和Net-NTLM hash介绍
Windows内网协议学习NTLM篇之NTLM基础介绍)
从第68帧看出这里是Net-NTLM v2

part3:De1CTF2020::TEST:56886f90fcb73ded:b5991cc2a0d585d0f813358eaafc7412:0101000000000000130cb9102308d601d2290bc0c25617a80000000002000800540045005300540001000c0044004d0032003000310032000400140074006500730074002e006c006f00630061006c000300220064006d0032003000310032002e0074006500730074002e006c006f00630061006c000500140074006500730074002e006c006f00630061006c0007000800130cb9102308d60106000400020000000800300030000000000000000000000000100000ecaa3d44ddc464026c453206813aafa0b918f2ad43d497ef8fb6beb2083258a40a0010000000000000000000000000000000000009001e0048005400540050002f0074006500730074002e006c006f00630061006c000000000000000000
hashcat64.exe -m 5600 test3.txt ?d?d?d?d?d?d?d?d -a 3 --force --show