Problem:
If you had to pick one aspect of cleanroom software engineering that makes it radically different from conventional or object-oriented software engineering approaches, what would it be?
Answer:
592-29-1P SA Code: 4478
SR Code: 4578
The Clean room process is a theory-based, team-oriented process for the development and certification of high-reliability software systems under statistical quality control. Its principal objective is to develop software that exhibits zero failures in use. For this purpose the life cycle is different from conventional software development techniques.
The approach combines mathematical-based methods of software specification, design and correctness verification with statistical, usage-based testing to certify software fitness for use.
The clean room software engineering differs from the conventional software engineering because
1. It makes explicit use of statistical quality control,
2. It verifies design specifications using a mathematically based proof of correctness, and
3. it implements testing techniques that have a high likelihood of uncovering high impact errors.
Cleanroom engineering diverges from conventional software practices by deemphasizing the role of unit testing and debugging and dramatically reducing the amount of testing performed by the developer of the software.
In conventional software development, errors are accepted as a fact of life. Because errors are deemed top be inevitable, each program component should be unit tested and then debugged. When the software is finally released, field use uncovers still more defects and another test and debug cycle begins. The rework associated with these activities is costly and time consuming. It can be degenerative error correction can lead to the introduction of still more errors.
In clean room software engineering, unit testing and debugging are replaced by correctness verification and statistically based testing. These activities, coupled with the record keeping necessary for continuous improvement, make the cleanroom approach unique.
.
Problem:
How do an incremental process model and certification work together to produce high-quality software?
Answer:
592-29-2P SA Code: 4478
SR Code: 4578
The Cleanroom process embeds software development and testing within a statistical quality control framework. Mathematically-based software development processes are employed to create software that is correct by design and statistical usage testing processes are employed to provide inferences about software reliability. This systematic process of assessing and controlling software quality during development permits certification of software fitness for use at delivery.
The value of a process under statistical quality control is well illustrated by modern manufacturing processes where the sampling of output is directly feedback into the processes to control quality. Once the discipline of statistical quality control is in place, management has objective visibility into the software development process and can control process changes to control product quality.
The characteristics of the Cleanroom process are an incremental development life cycle and independent quality assessment through statistical testing. The development life cycle starts with a specification that not only defines function and performance requirements, but also identifies operational usage of the software and a nested sequence of user-function subsets that can be developed and tested as increments which accumulate into the final system. Disciplined software engineering methods provide design and verification techniques required to create correct software. Correctness verification by development teams is used to identify and eliminate defects prior to any execution of the
Software.
Software execution is controlled by an independent certification team that uses statistical testing methods to evaluate software quality. Statistical testing results in objective quality certification of software at delivery and provides a scientific basis for generalizing reliability estimates to operational environments.
Problem:
Using box structure specification, develop “first-pass” analysis and design models for the SafeHome system.
Answer: Problem:
A bubble-sort algorithm is defined in the following manner:

Partition the design into subfunctions, and define a set of conditions that would enable you to prove that this algorithm is correct.
Answer:
Partition of Bubble sort algorithm
Supposed algorithm design is divided into two subparts. They are
1. Procedure bubble sort
2. Procedure swap
procedure bubblesort :
var i, t, integer;
begin
repeat until t = a[1]
t := a[1];
for j = 2 to n do
if (a[j-1]>a[j]) then
begin
swap (&a[j-1], &a[j])
end
end rep
end
procedure swap(*a, *b ) :
var t;
begin
t = *a;
*a = *b;
*b = t
end
Set of conditions for bubble sort process:
In first step, the list is separated into two subparts:
1. Sorted
2. Unsorted.
The smallest element in the list is bubbled from the unsorted list and moved to the sorted subsist. And moves one element ahead; increasing the number of sorted elements and decreasing the number of unsorted ones.
At each time, an element moves from unsorted part to the sorted part, until one sort pass is completed. In a list of n elements, bubble sort requires up to (n-1) passes to sort the data.
Problem:
Document a correctness verification proof for the bubble sort discussed in Problem 28.4.
Answer:
592-29-6P SA Code: 4478
SR Code: 4578
Correctness proof for the bubble sort by program verification:
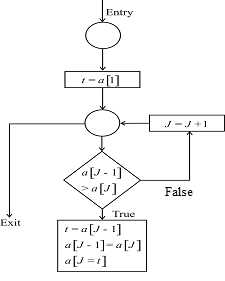
1) Initially the entry conditions are correct and the loop repeats until  and then the variable initialized to L and loop repeats until 10.
and then the variable initialized to L and loop repeats until 10.
2) If checks the condition  is greater then a
is greater then a  then the situations followed by it exchange both values.
then the situations followed by it exchange both values.
3) If the condition fails, then increments the loop variable by 1.
4) The exit condition determines whether  if it fails then it exists the block.
if it fails then it exists the block.
Problem:
Select a program that you use regularly (e.g., an e-mail handler, a word processor, a spreadsheet program). Create a set of usage scenarios for the program. Define the probability of use for each scenario, and then develop a program stimuli and probability distribution table similar to the one shown in Section 28.4.1.
Answer:
592-29-8P SA Code: 4478
SR Code: 4578
Consider an e-mail handler, the e-mail contain the inbox, sent items, unread mails, delete items etc. These all are regularly usage scenarios for this program.cleanroom testing teams must determine a usage probability distribution for the e-mail handler. The specification for each increment of the e-mail handler is analyzed to define set of stimuli (inputs or events) that cause the handler to change its behavior.
Probability distribution table for E-mail handler are
Program stimulus probability interval
Inbox 60% 1-60
Sent items 30% 61-90
Delete mails 5% 91-95
Unread mails 3% 96-98
Junk E-mails 2% 99-100
Problem:
For the program stimuli and probability distribution table developed in Problem 28.6, use a random-number generator to develop a set of test cases for use in statistical use testing.
Answer:
Test cases are generated for each set of stimuli according to the usage probability.
To generate a sequence of usage test cases that conform to the usage probability distribution, random numbers between 1 and 99 are generated. Each random number corresponds to an interval on the preceding probability distribution
Random number sequences are generated
We cases are derived as
The testing team executes there use cases and verifies software behavior against the specification for the system.
Problem:
In your own words, describe the intent of certification in the cleanroom software engineering context.
Answer:
591-29-10P SA Code: 4478
SR Code: 4578
________________________________________________________________________
Certification (the Cleanroom term for testing) is performed to certify the software reliability, not test the software in the classical sense. The methods used are statistical quality control (SQC) and statistical usage testing.
Clean room certification and, specifically, statistical usage based testing, does not measure quality in defects per line of code. Instead, quality is measured in sigma units.
Cleanroom certification can reduce time to market because you are not spending time testing and fixing when you need not be. When you reach the quality level desired, you can ship, even if complete path coverage is not achieved. Cleanroom certification can tell you when testing is complete and the product can be released.
Problem:
You have been assigned to a team that is developing software for a fax modem. Your job is to develop the “phone book” portion of the application. The phone book function enables up to MaxNames people to be stored along with associated company names, fax numbers, and other related information. Using natural language, define
a. The data invariant.
b. The state.
c. The operations that are likely.
Answer:
4633-21-9P SA: 4475
SR: 6376
If we consider the application “phone book”, the phone book function enables up to maxnames of people to be stored along with associated company names, fax names, and other related information without any duplication.
In a phone book, the entries can be as shown.
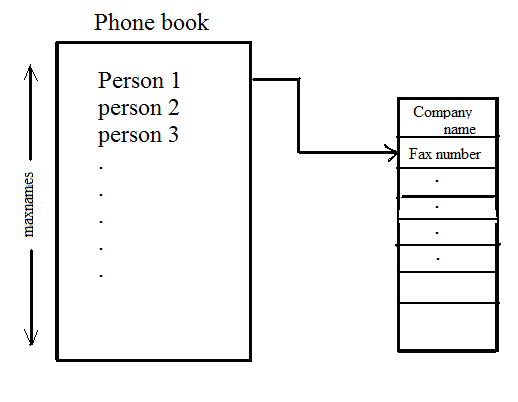
(a) The data invariant:
The data invariant is a condition that is true through out the execution of the system (phone book) that contains a collection of data.
The data invariant that holds for the phone book has the following components.
• There cannot be entries more than maxnames in the phone.
• There cannot be any duplicate entries in the phone book.
(b) The state:
A state is the stored data, which a system accesses and alters. It is a symbol table. In this phone book there are many states. A system can be in one of several states.
In a phone book there can be various states. They are
• Create contact
• Delete contact
• Create group,
• Speed dial
• Edit contact
(c) The operations those are likely:
An operation is an action that takes place within a system and reads or writes data.
If the phone book function is concerned with various actions like creating, editing, and deleting contacts, groups etc. So the operations that are likely are
• Create()
• Delete()
• Edit()
• Creategroup()
• Deletegroup()
Three types of operations that can be associated with operations are:
• Invariants
• Pre-condition.
• Post-condition.
•
An invariant defines what is guaranteed not to change. The phone book function has an invariant that states that the number of elements in the phone book is always less than or equal to the maxnames.
• A precondition defines the circumstances in which a particular operation is valid. The precondition for an operation that adds a name in the phone book is that, adding a new name/ number to the phone book is valid only if there do not exists a contact with the same name and also the number of contacts is less than maxnames.
• A post-condition operation states that what is guaranteed to be true upon completion of an operation. In the context of a phone book, if we consider a create() operation, the post condition would specify that the phone book is now added with a new contact.
Problem:
You have been assigned to a software team that is developing software called MemoryDoubler that provides greater apparent memory for a PC than physical memory. This is accomplished by identifying, collecting, and reassigning blocks of memory that have been assigned to an existing application but are not being used. The unused blocks are reassigned to applications that require additional memory. Making appropriate assumptions and using natural language, define
a. The data invariant.
b. The state.
c. The operations that are likely.
Answer:
4633-21-10P SA: 4475
SR: 6376
The software “MemoryDoubler” provides greater apparent memory for a PC than physical memory. It is accomplished by identifying, collecting, and reassigning blocks of memory.
(a)
The data invariant:
Data invariant is a condition that is true through out the execution of the system. In a memorydoubler system, the data invariants are
1. No memory block will be marked as both used and unused.
2. Set of memory blocks are in the queue and that will be subsets of the collection of currently used blocks.
3. Collection of used blocks and unused blocks should be maintained with no duplicates.
(b)
The state:
The state in a memorydoubler system is a collection of free memory blocks and collection of used memory block and returned blocks.
(c)
The operations those are likely:
An operation is an action within a system. And the operations associated with the memorydoubler system are
1. An operation that adds a collection of memory blocks to the older one.
2. An operation that removes a collection of used memory blocks from the front of the old memory and place them in the collection of unused block memory.
3. An operation that checks whether the additional memory block is empty.
In these operations, the first operation is a pre-condition. Blocks to be added must be in the collection of used memory block.
The post condition is the collection of blocks and must be added to end of another one.
The final operation checks whether another block of memory is empty or not. If another memory block is empty, then it delivers the post condition value as true.
Solution :Chapter28: FORMAL MODELING AND VERIFICATION
28.1. Proof of correctness applied as software is specified is probably the most significant departure from other approaches.
28.2. Each increment in the cleanroom process may be planned to produce one or more certified components. As the increments are completed, the software is integrated and because the components are certified, integration can occur with relatively little concern for error.
28.3. To some extent the black box specification is similar to a level 0 data flow diagram in that inputs and outputs are specified for the box. Therefore, the SafeHome black box would be similar to the level 0 DFD presented in Chapter 12. The state box is analogous to the state transition diagram. The clear box representation is analogous to procedural design and can be represented using a PDL.
28.4 and 28.5. A detailed solution to this problem and many other common algorithms can be found in [LIN79].
28.6. Answers will vary
28.7. Answers will vary
28.8. The intent of the certification process is to specify the reliability for each component, allowing them to be stored along with their usage scenarios, program stimuli, and probability distributions in a repository of potentially reusable software components. The software components are precisely specified and have been verified against their specifications.
28.9. Data invariant: the phone book will contain no more than maxnames names; there will be no duplicate names in the phone book. The state is the data that the software access, therefore, in this case, the state is the phone book itself. Operations are similar to the operations defined for objects in that they are capable of changing the state. Operations for this problem include: add, delete, edit, obtain.
28.10. The data invariant is the memory block list that contains the start and end address of the unused memory, along with appropriate assignment information; any given block can only be assigned to one program at a time. The state is the memory block table. Operations for this problem include: add, delete, assign, lookup.