(:」∠)_
- 此作业所属课程:2019-2020-2-1991&1993《网络攻防实践》
- 本次作业要求:实践一 网络攻防环境的搭建
- 课程目标:学习网络攻防实践
- 本次作业在哪个方面帮助我实现目标:第二章 网络攻防实验环境
攻防环境搭建过程
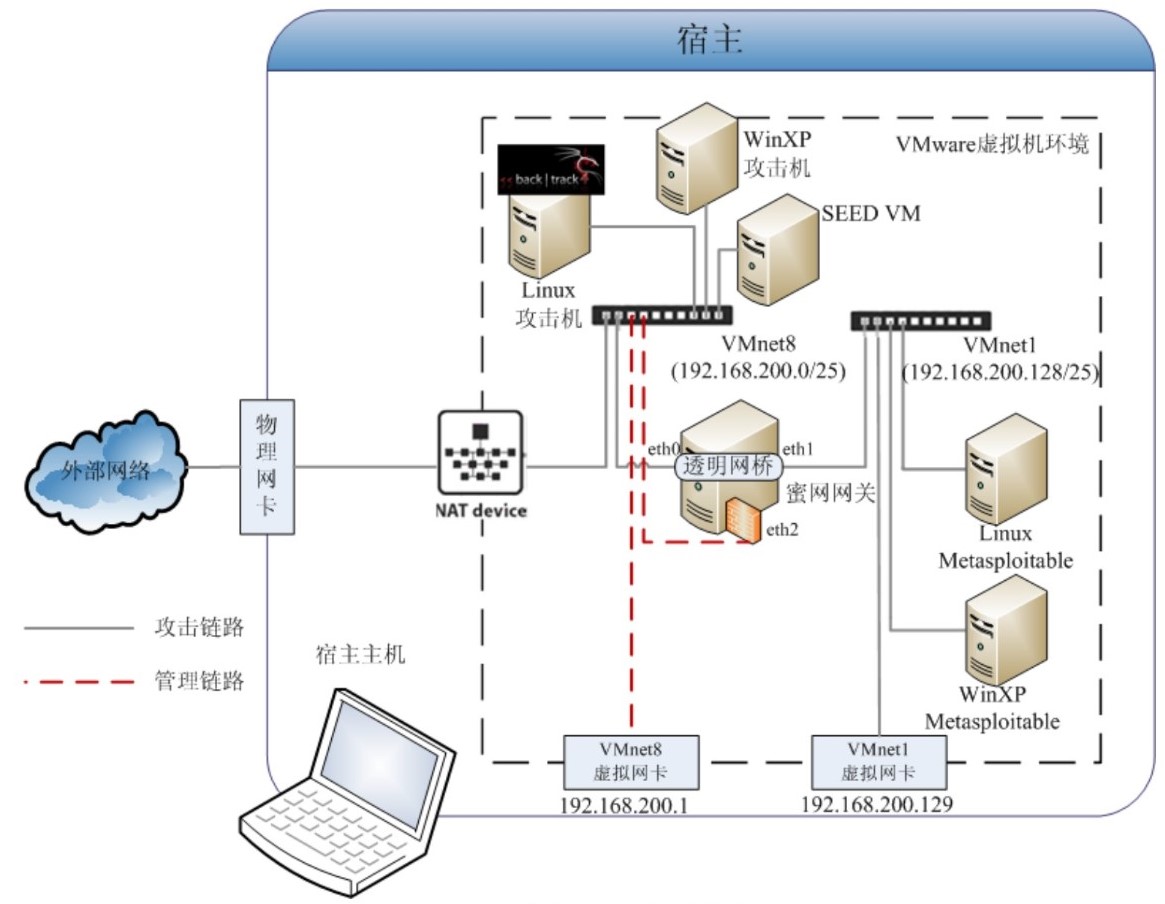
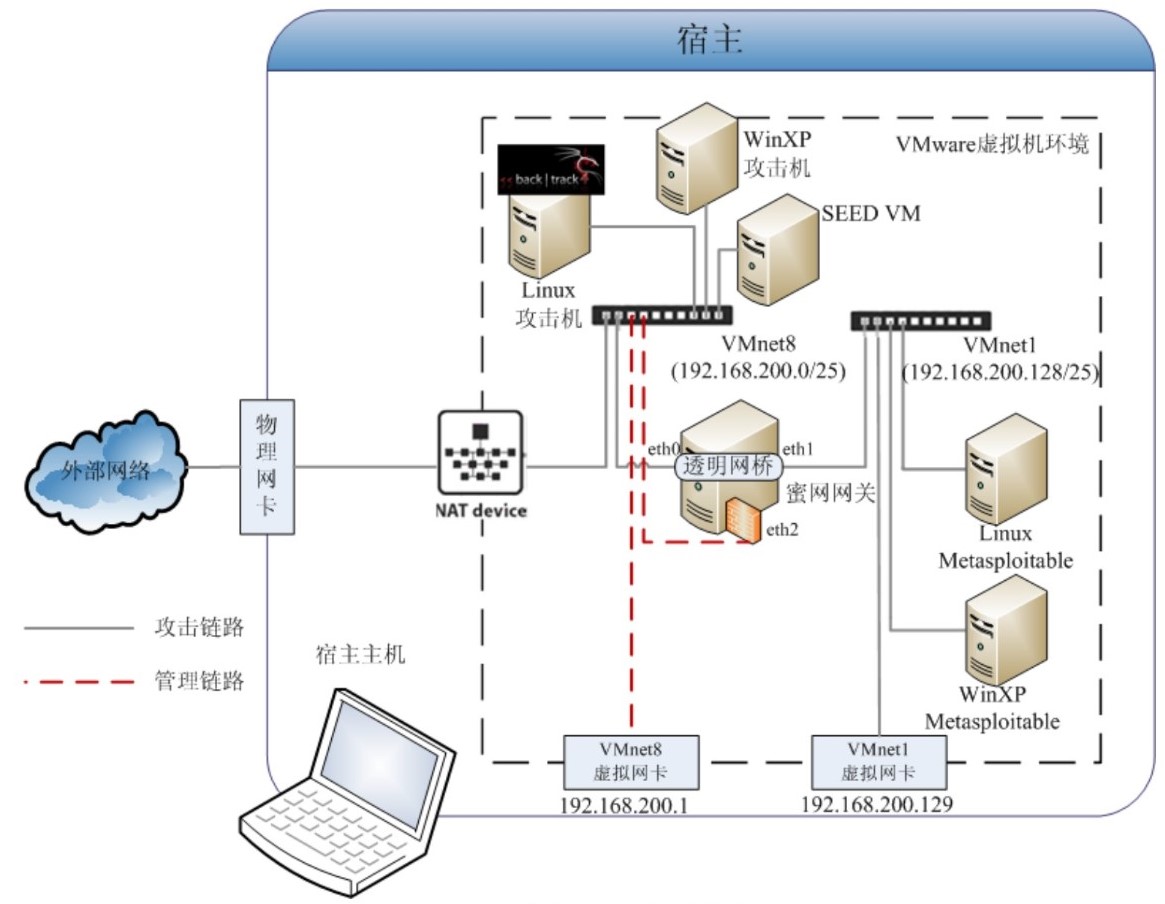
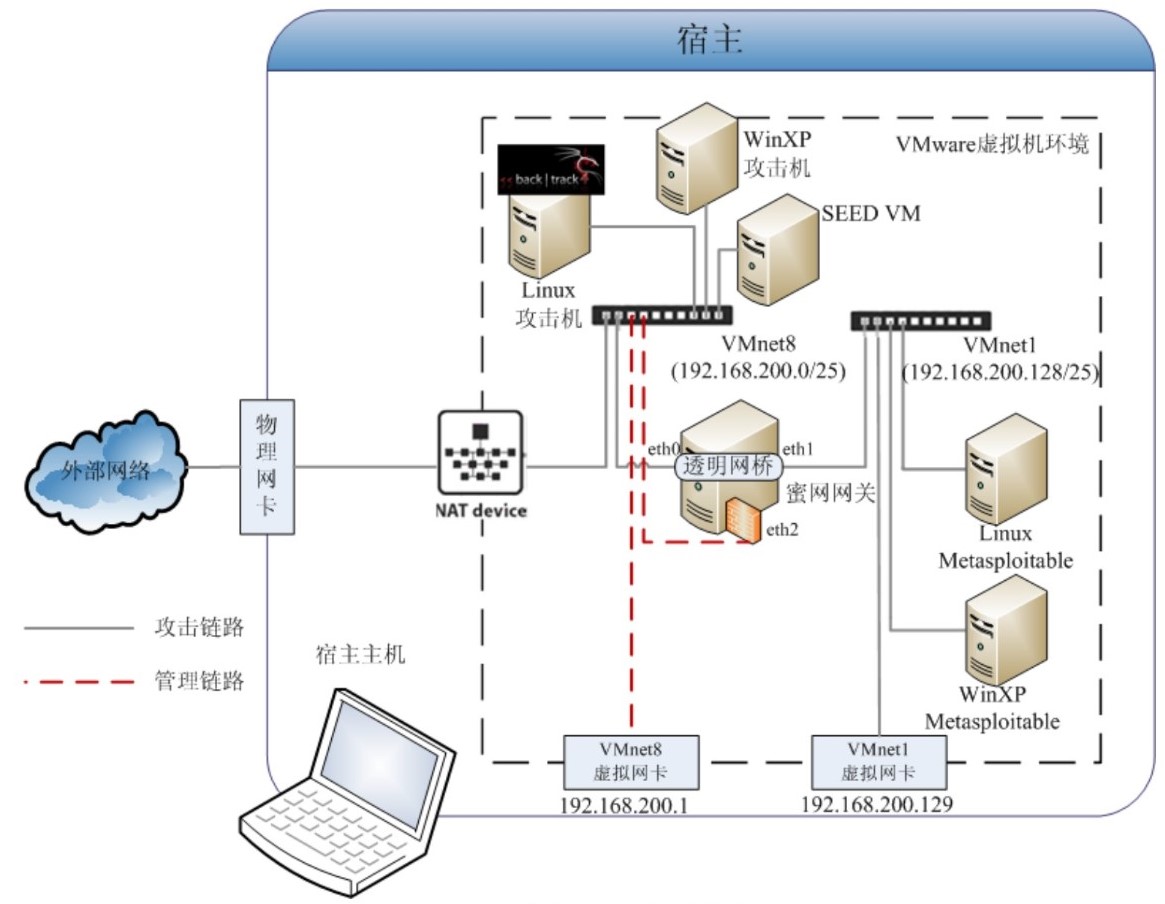
1、网络架构
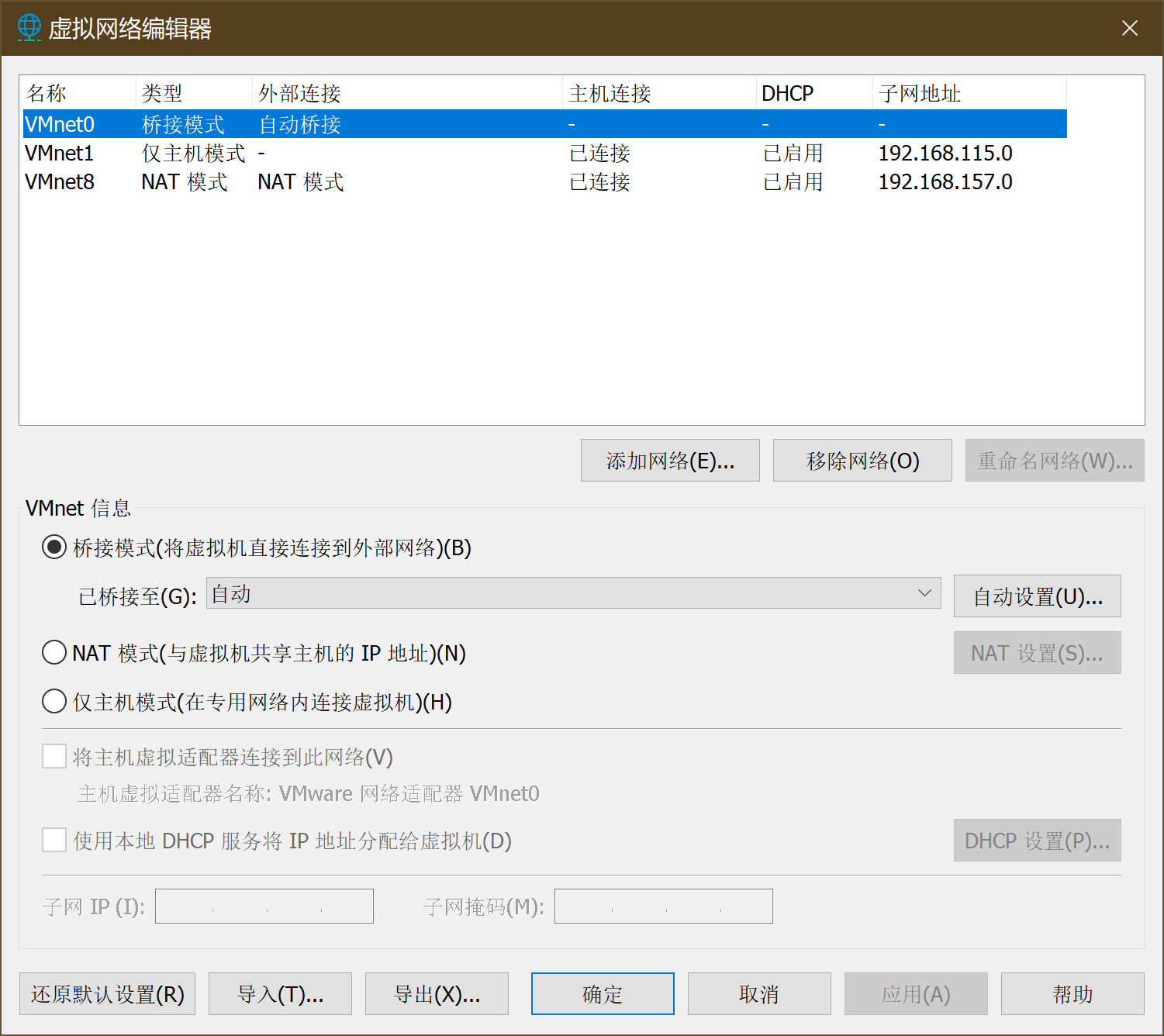
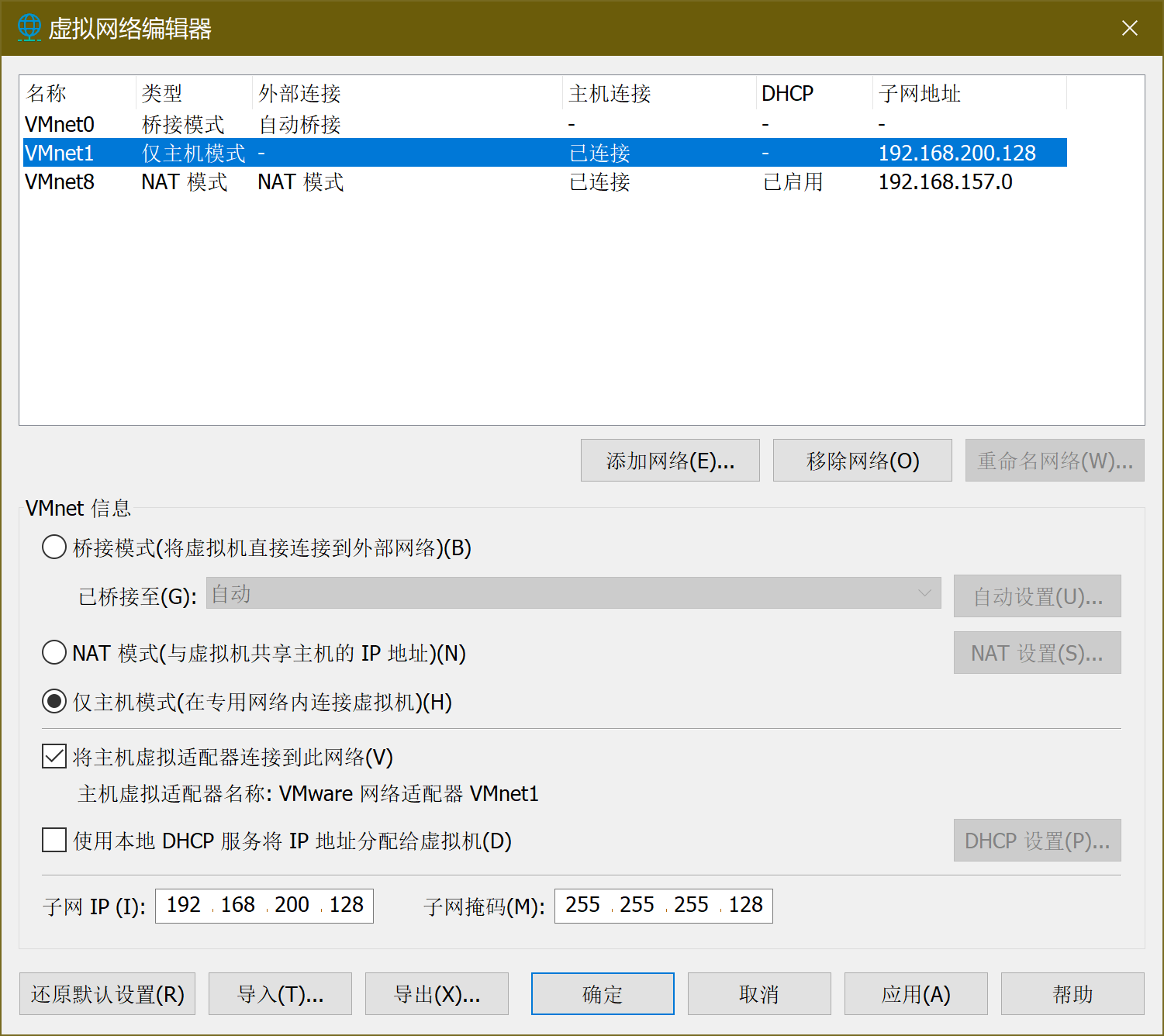
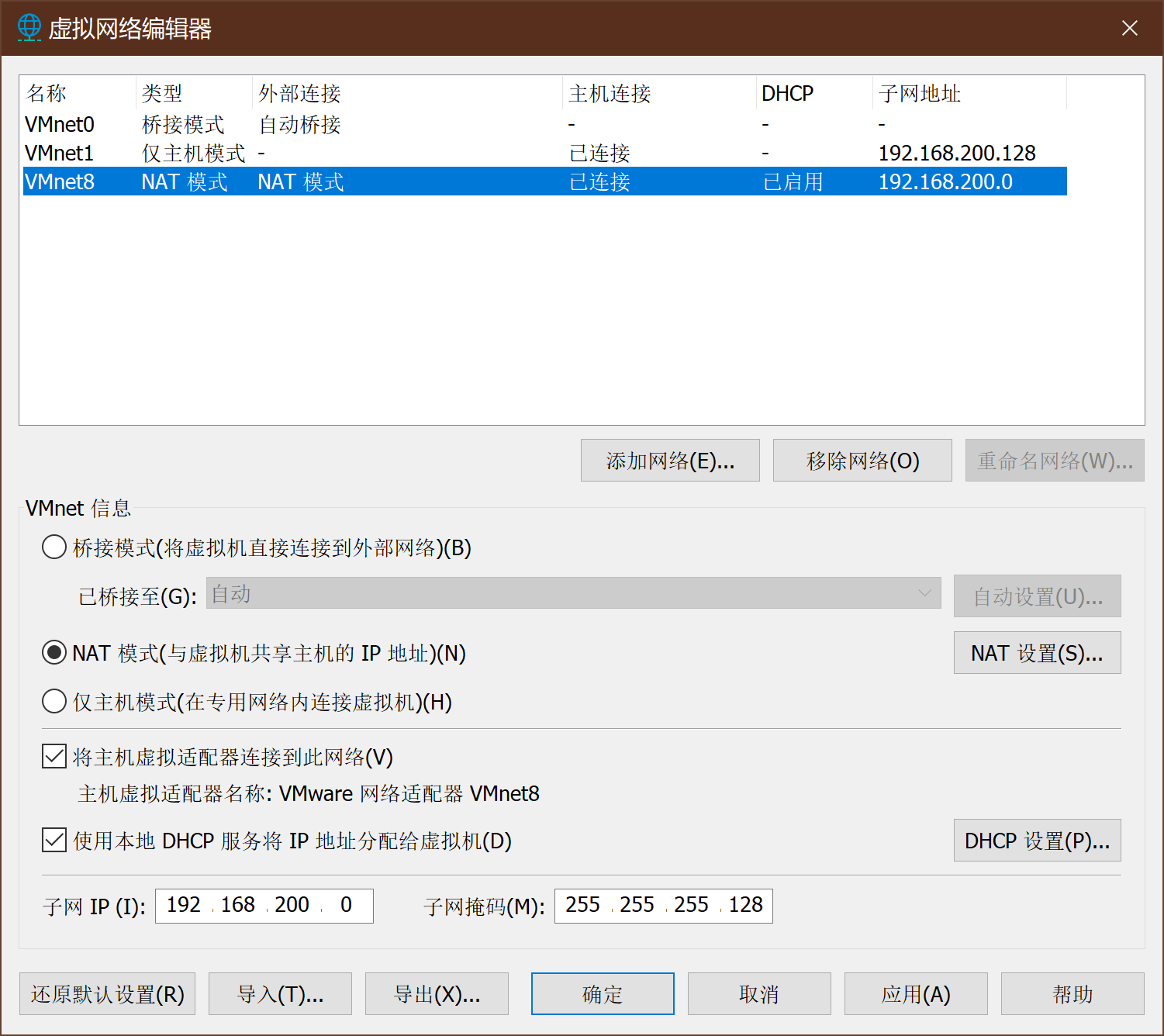
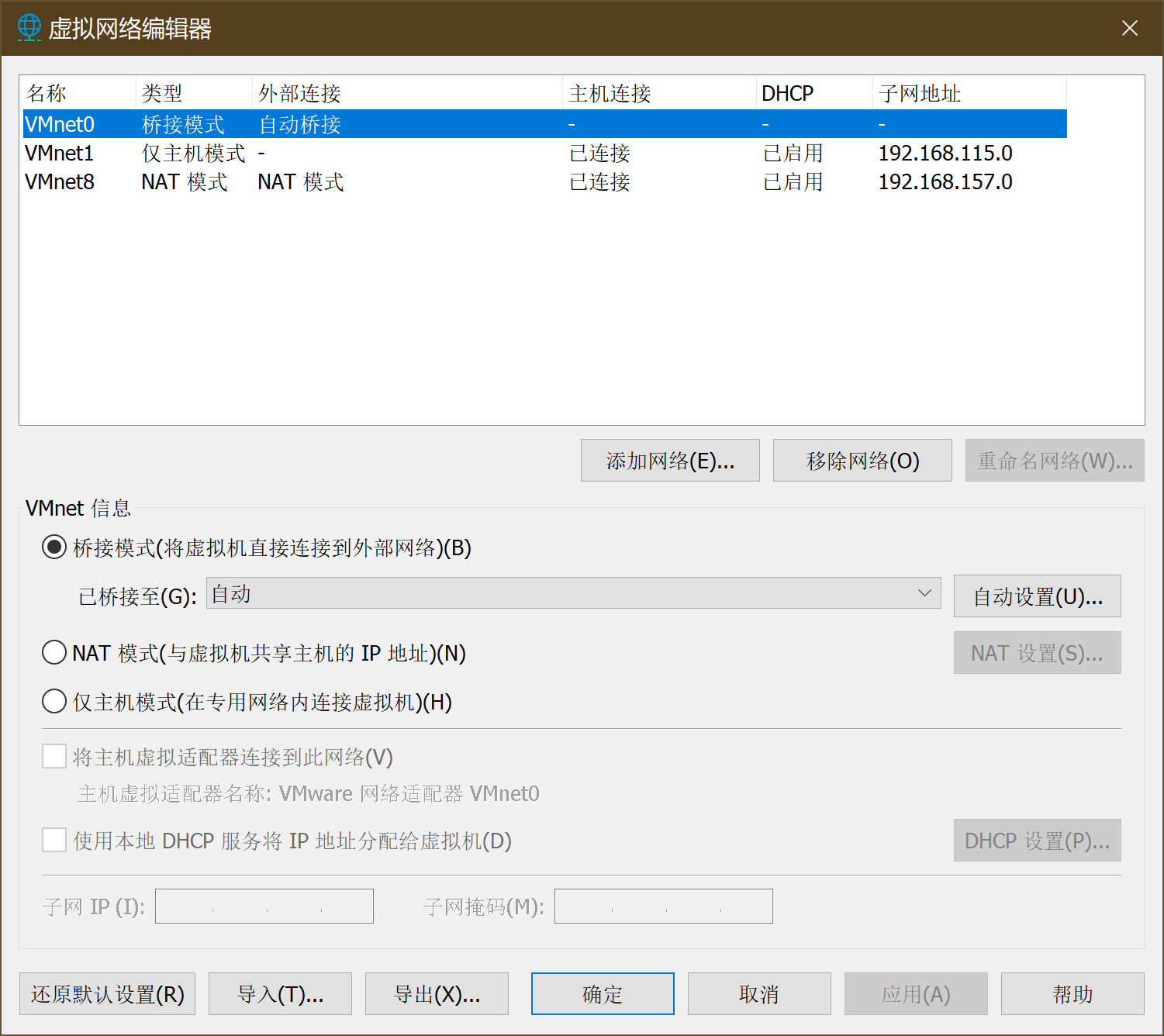
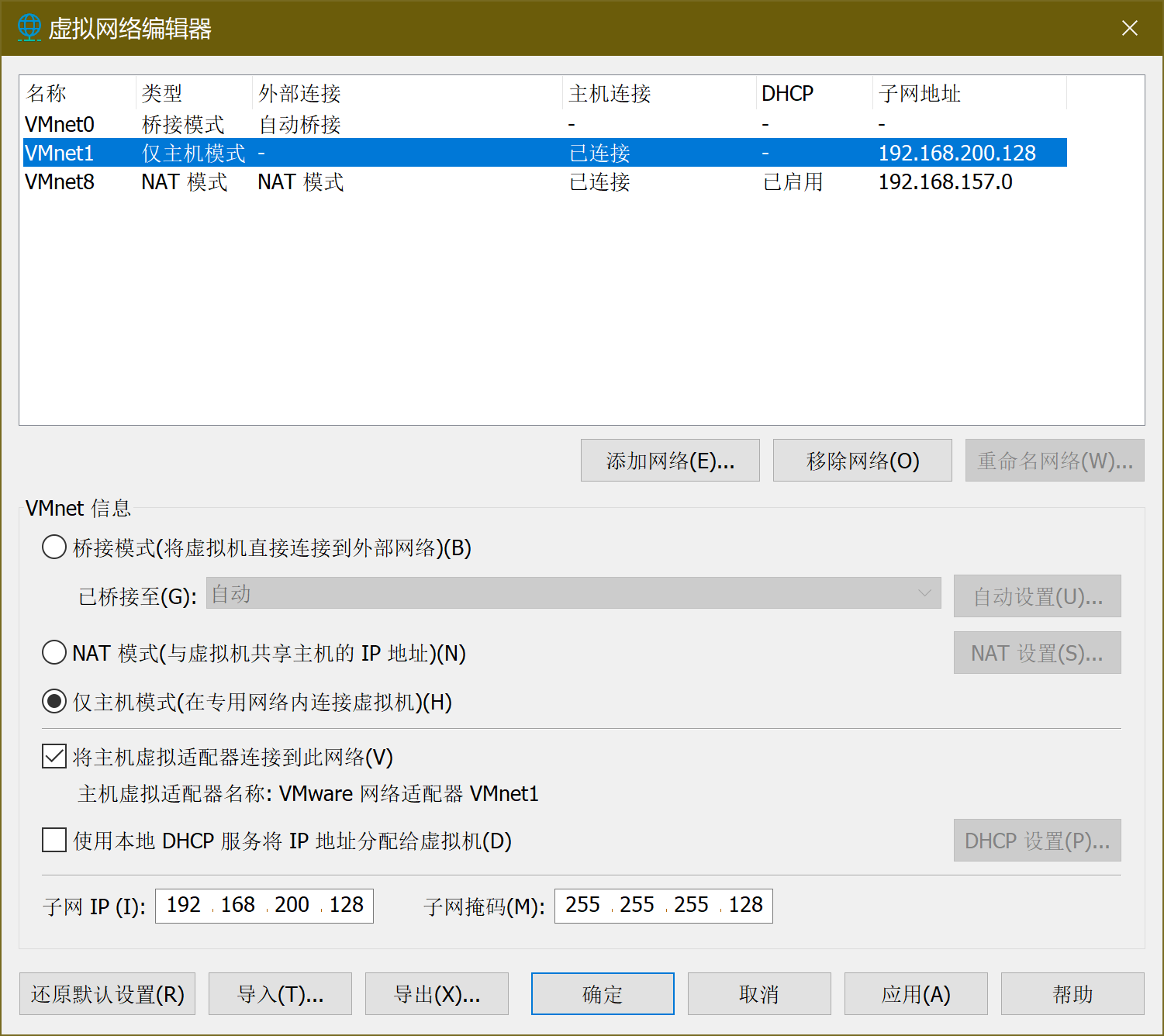
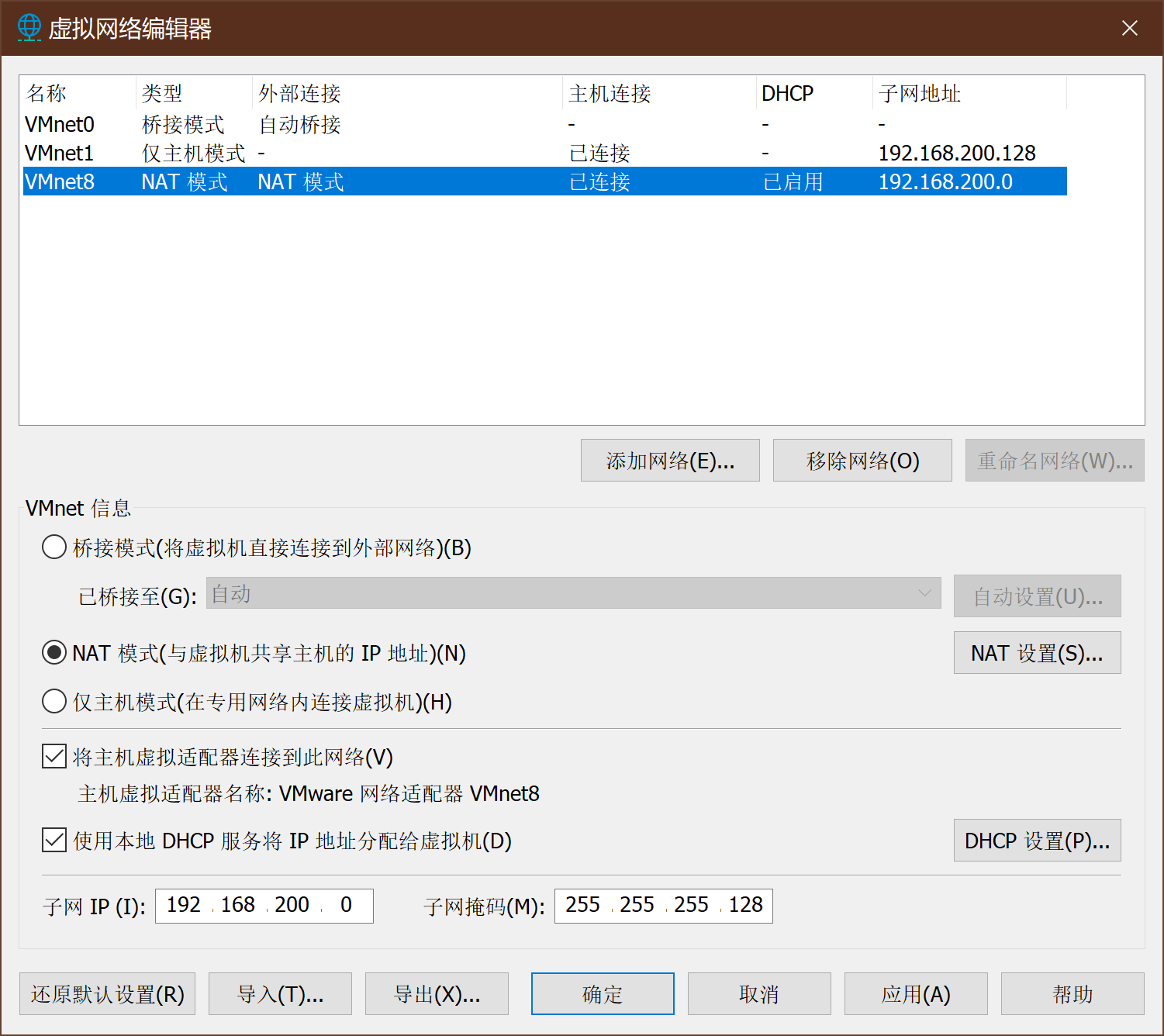
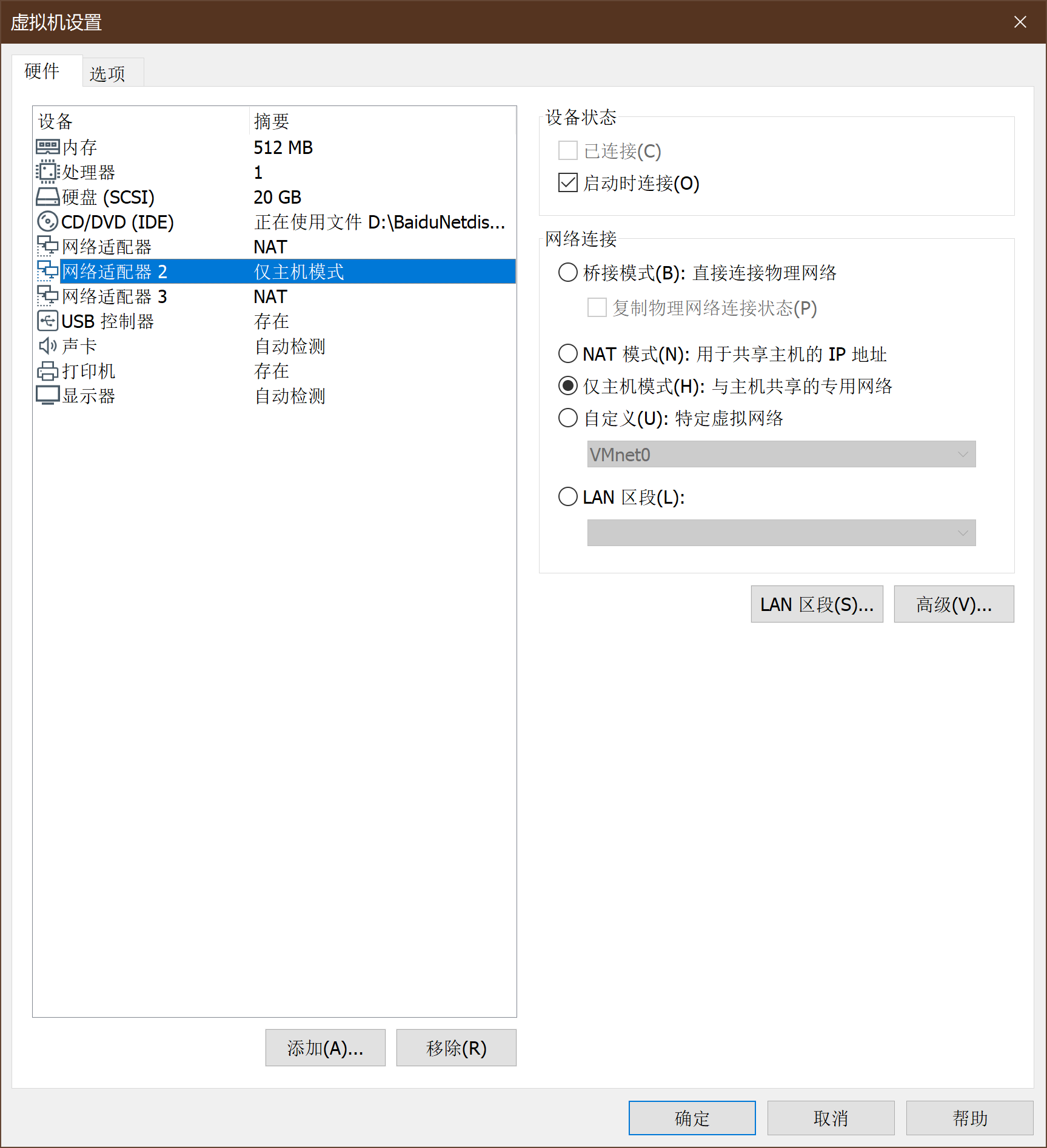
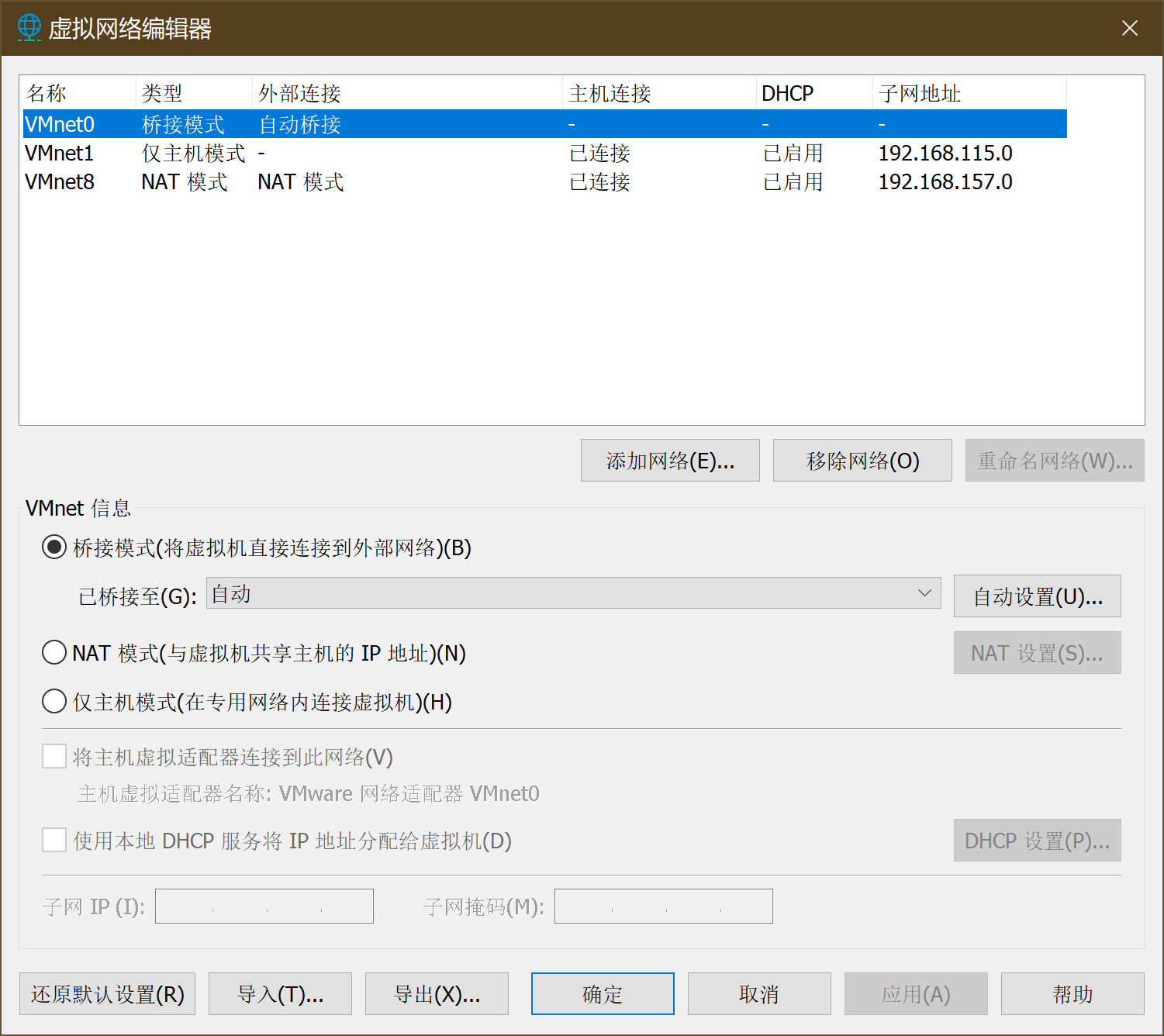
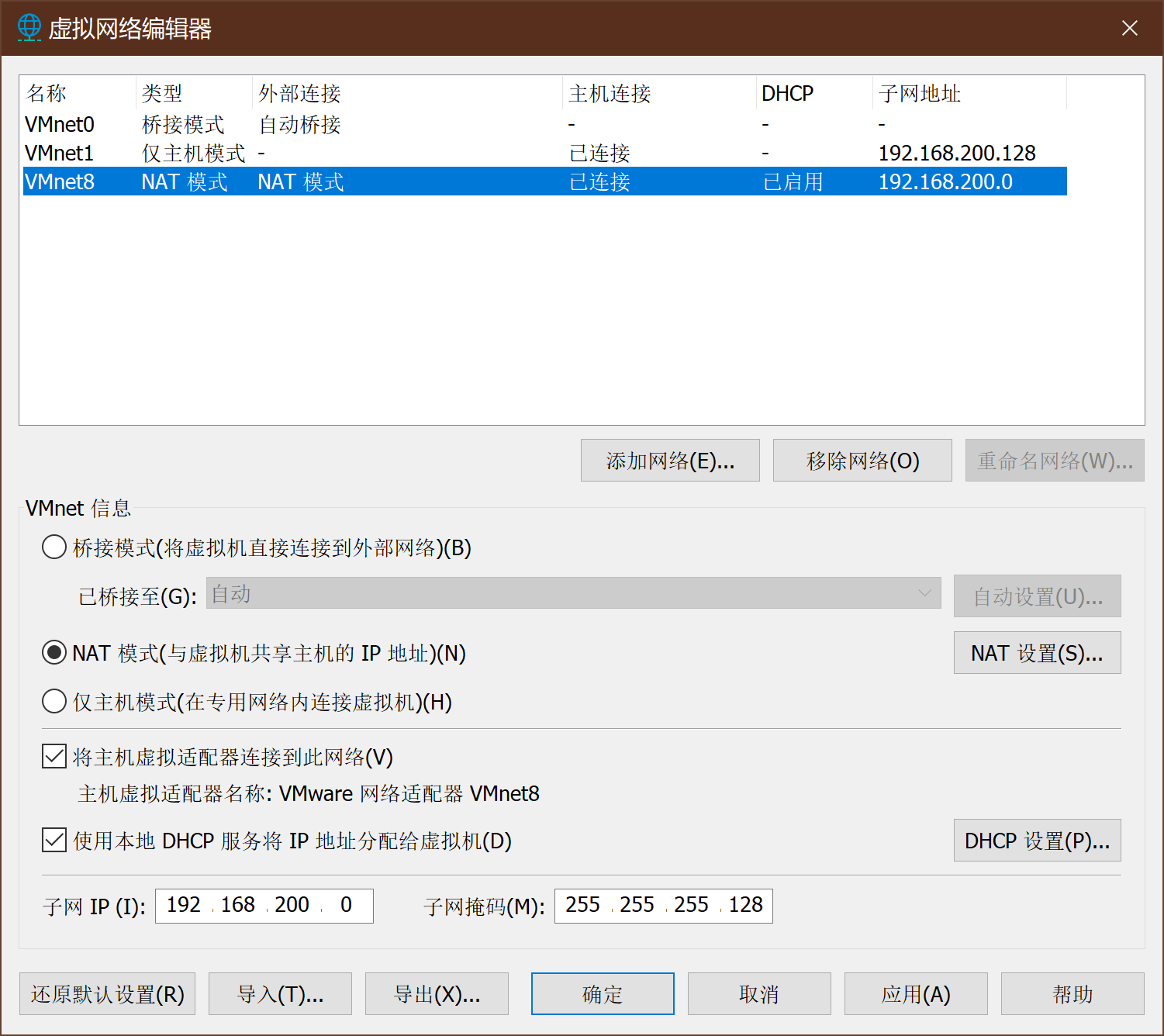
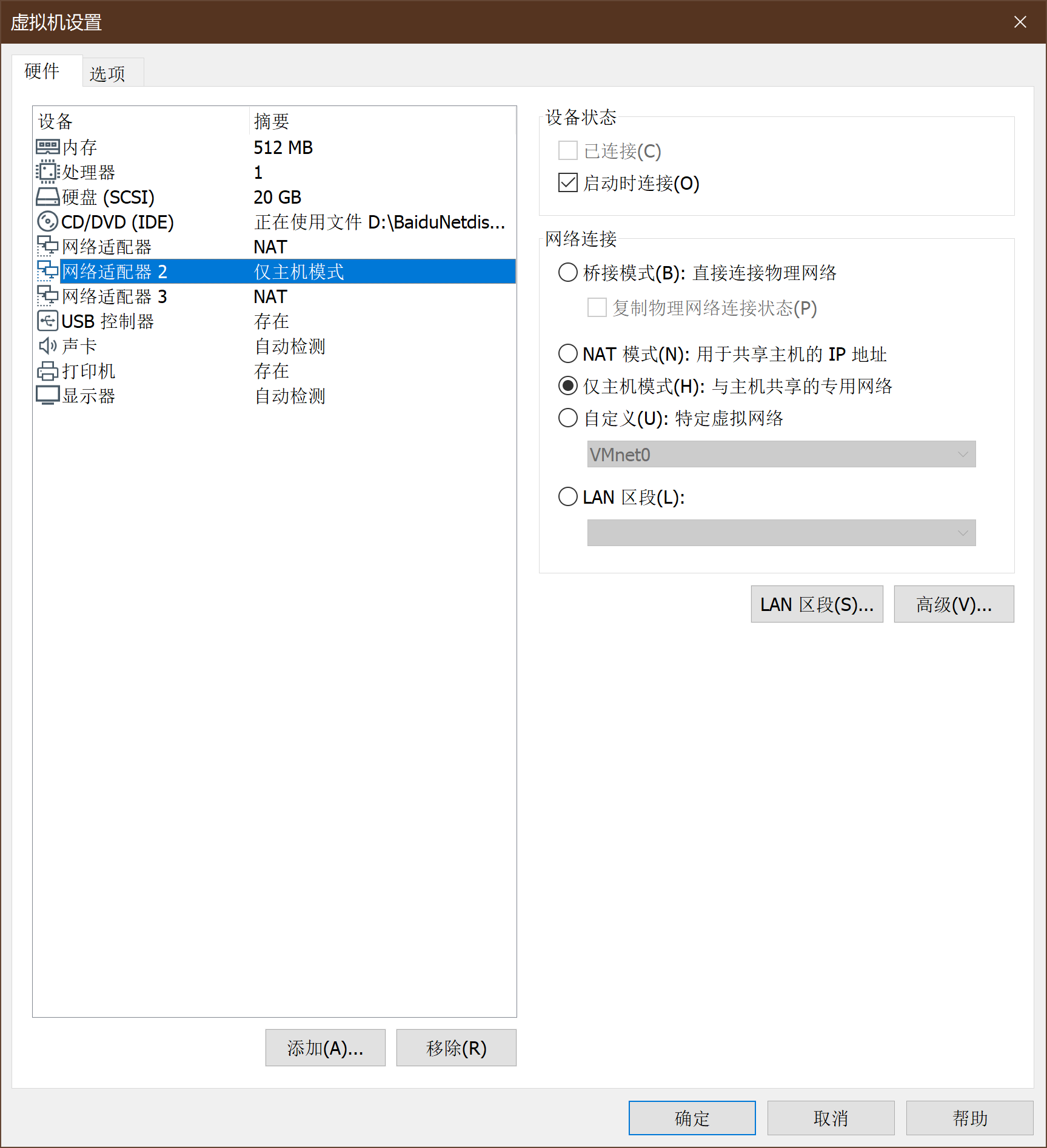
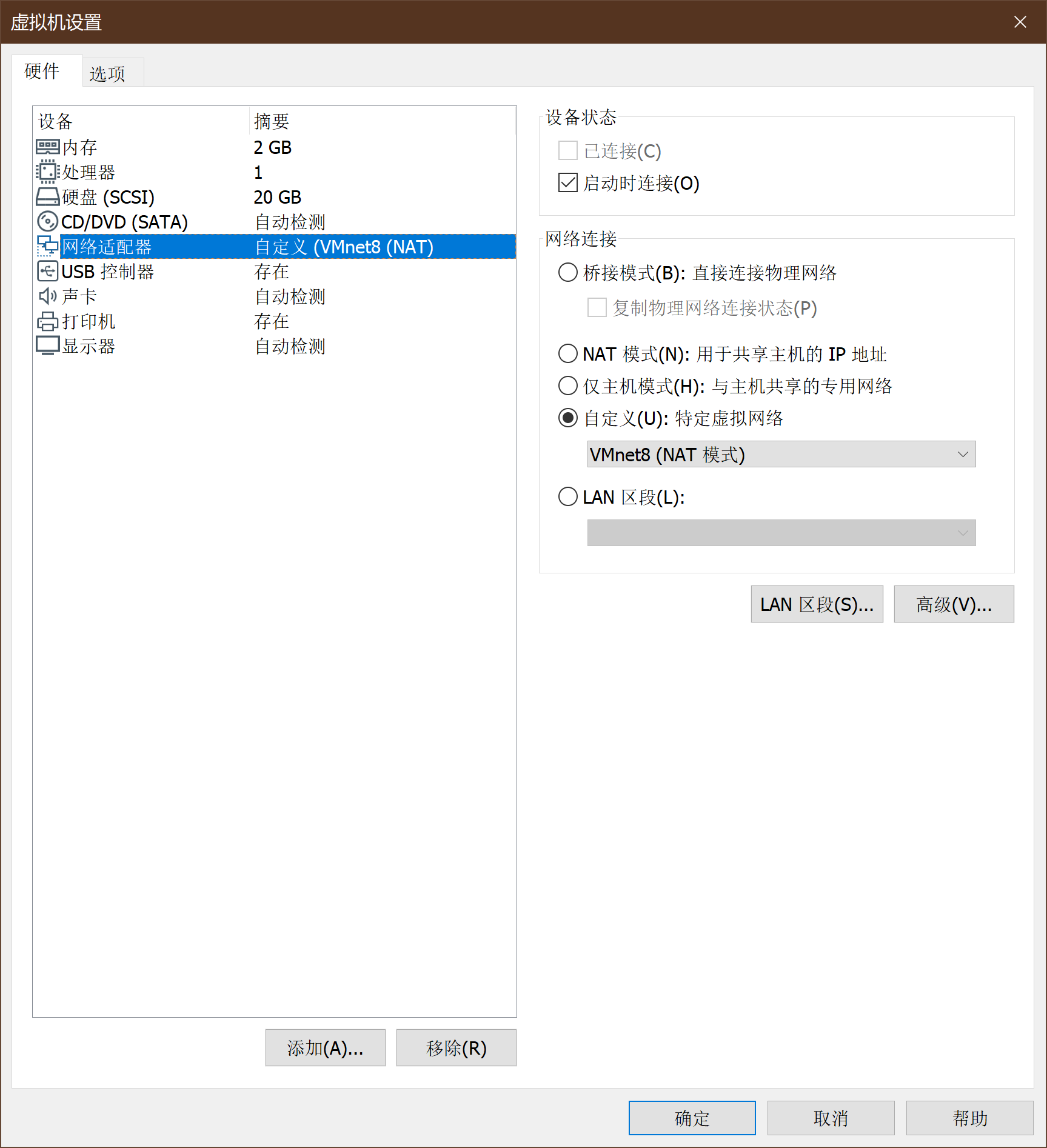
2、VM网络设置
-
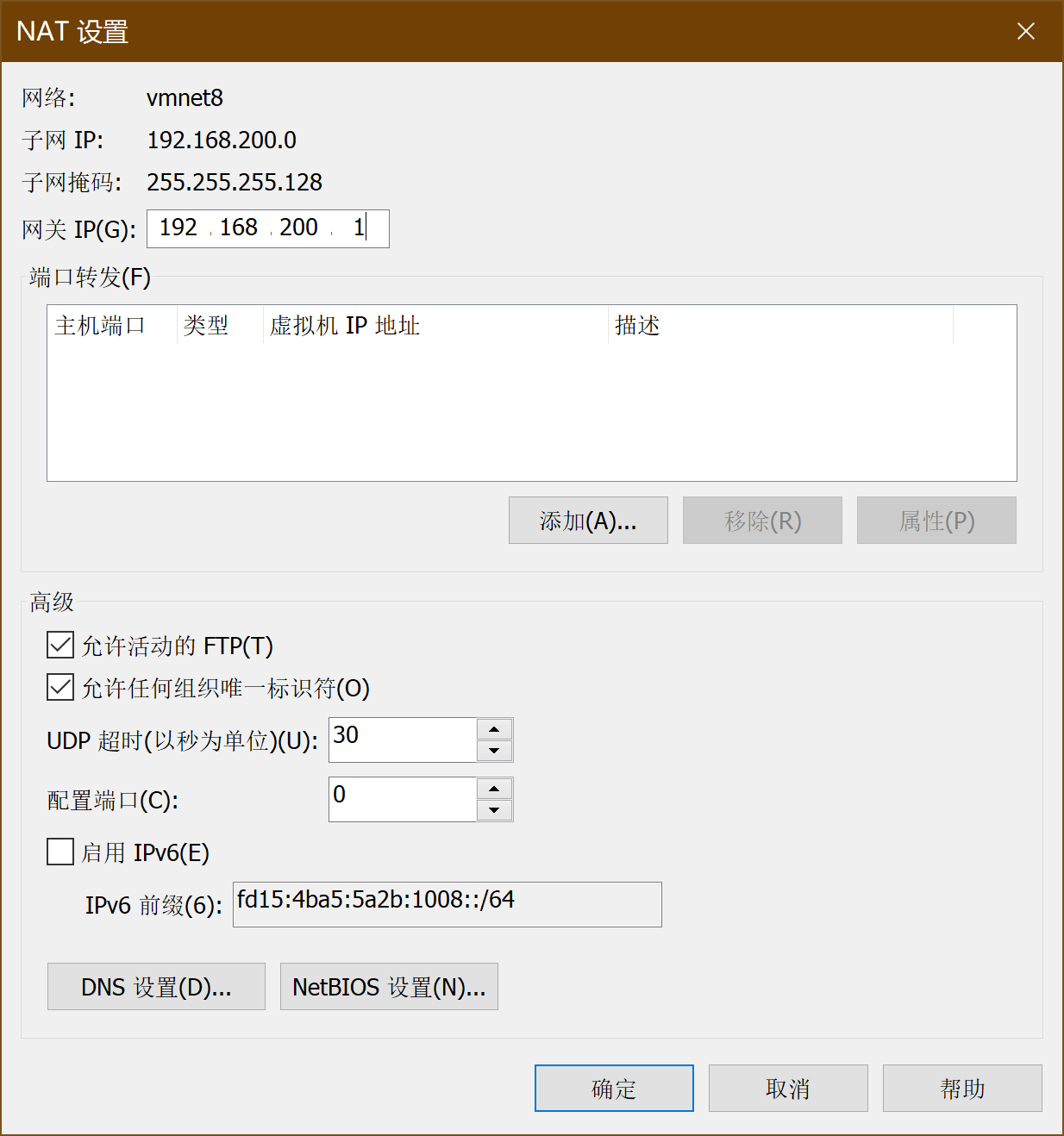
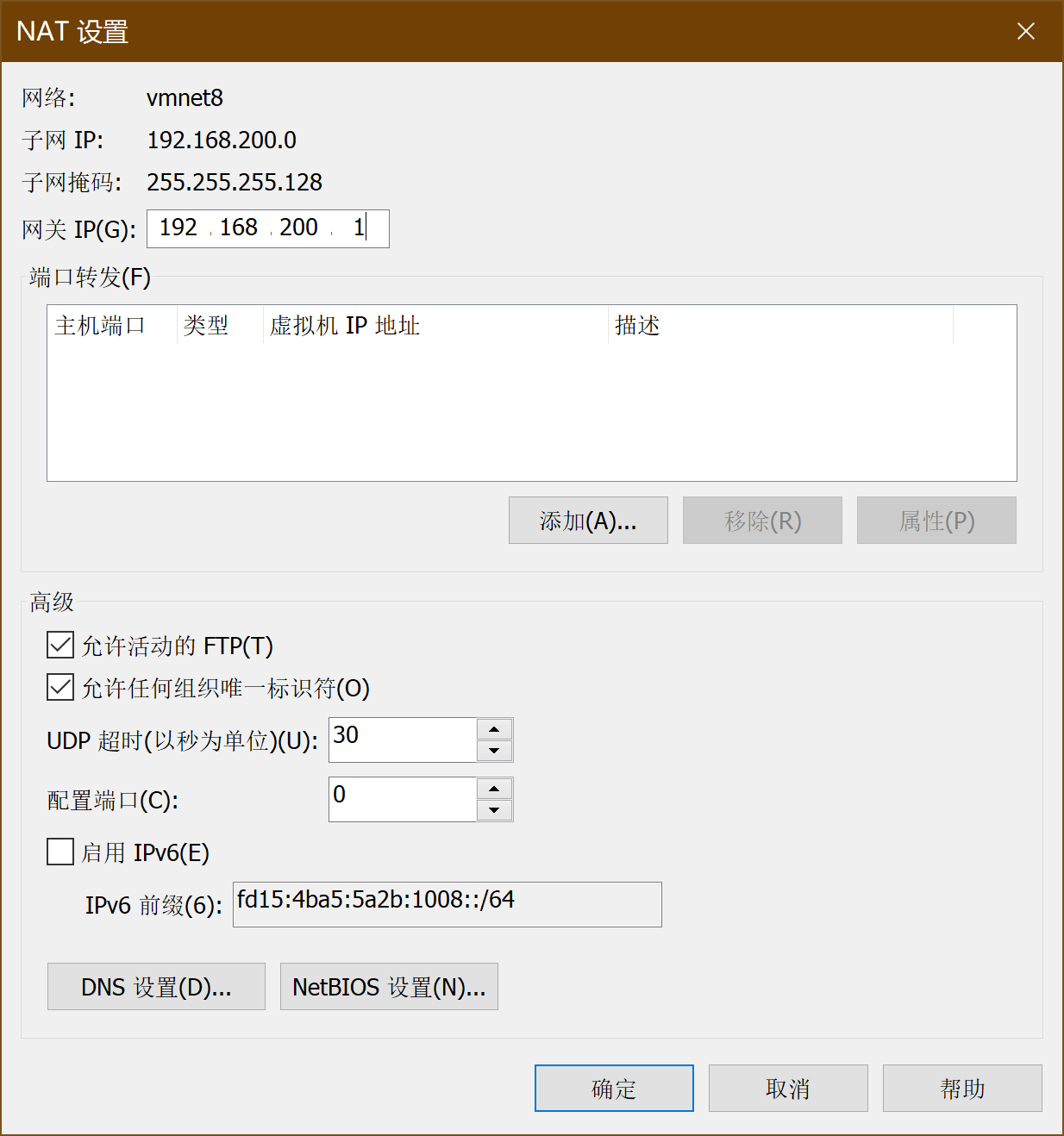
其中,VMnet8的NAT设置:
-
VMnet8的DHCP设置:
确定,网络适配器完成。
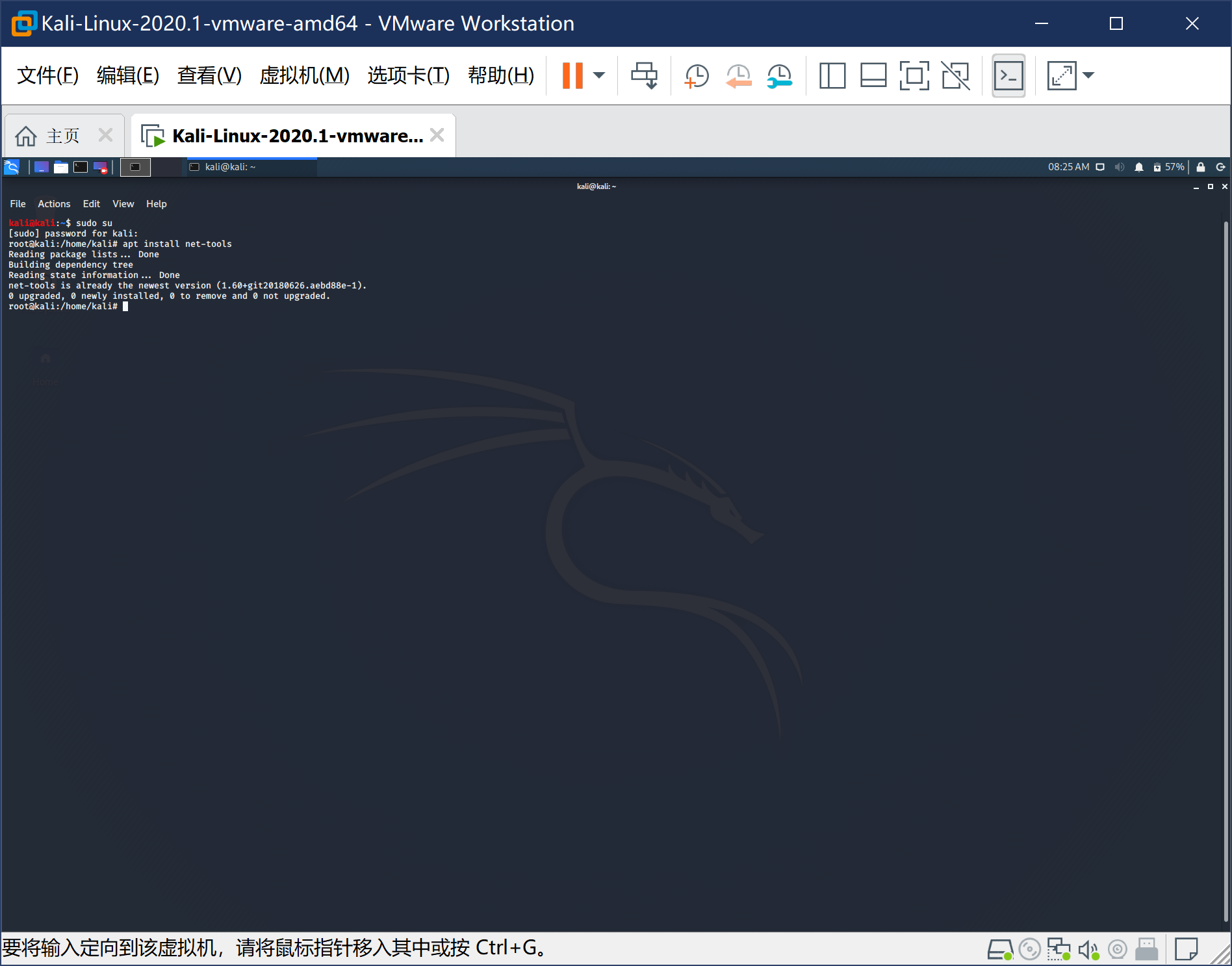
3、安装linux攻击机-Kail
-
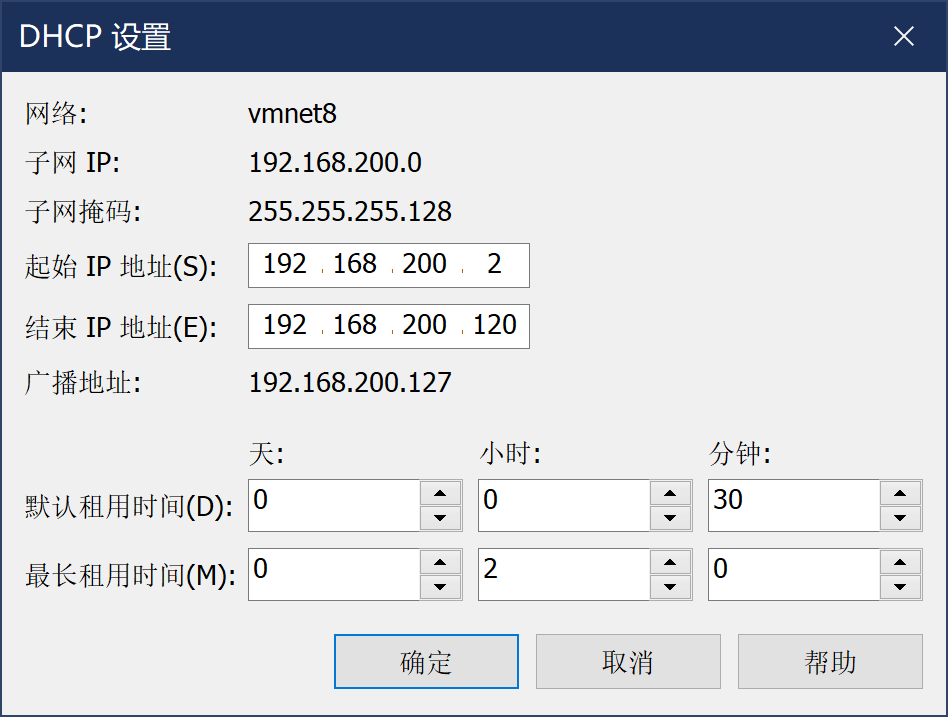
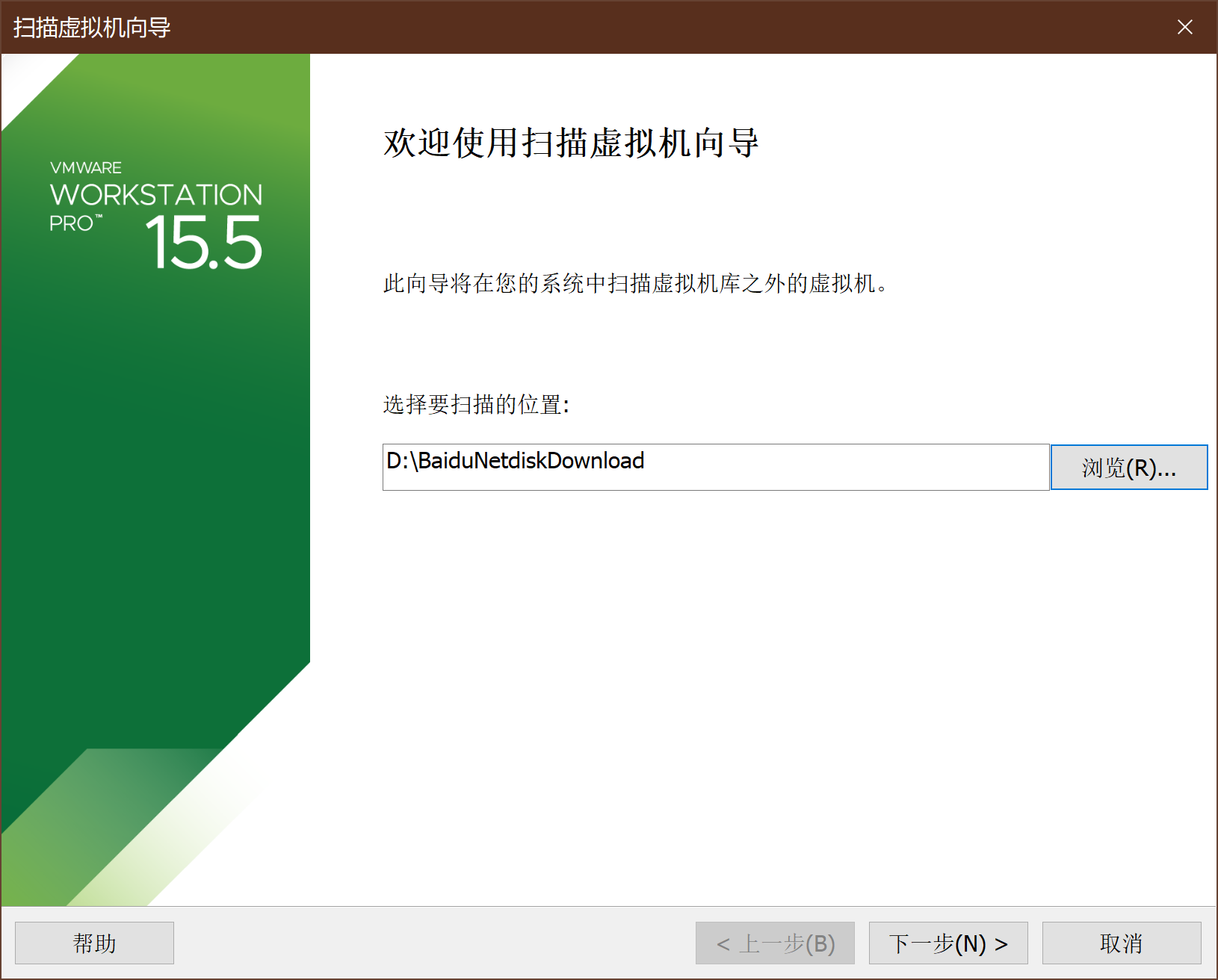
kail以VM虚拟机vmx文件的形式提供,通过扫描虚拟机可以直接导入,如下图
-
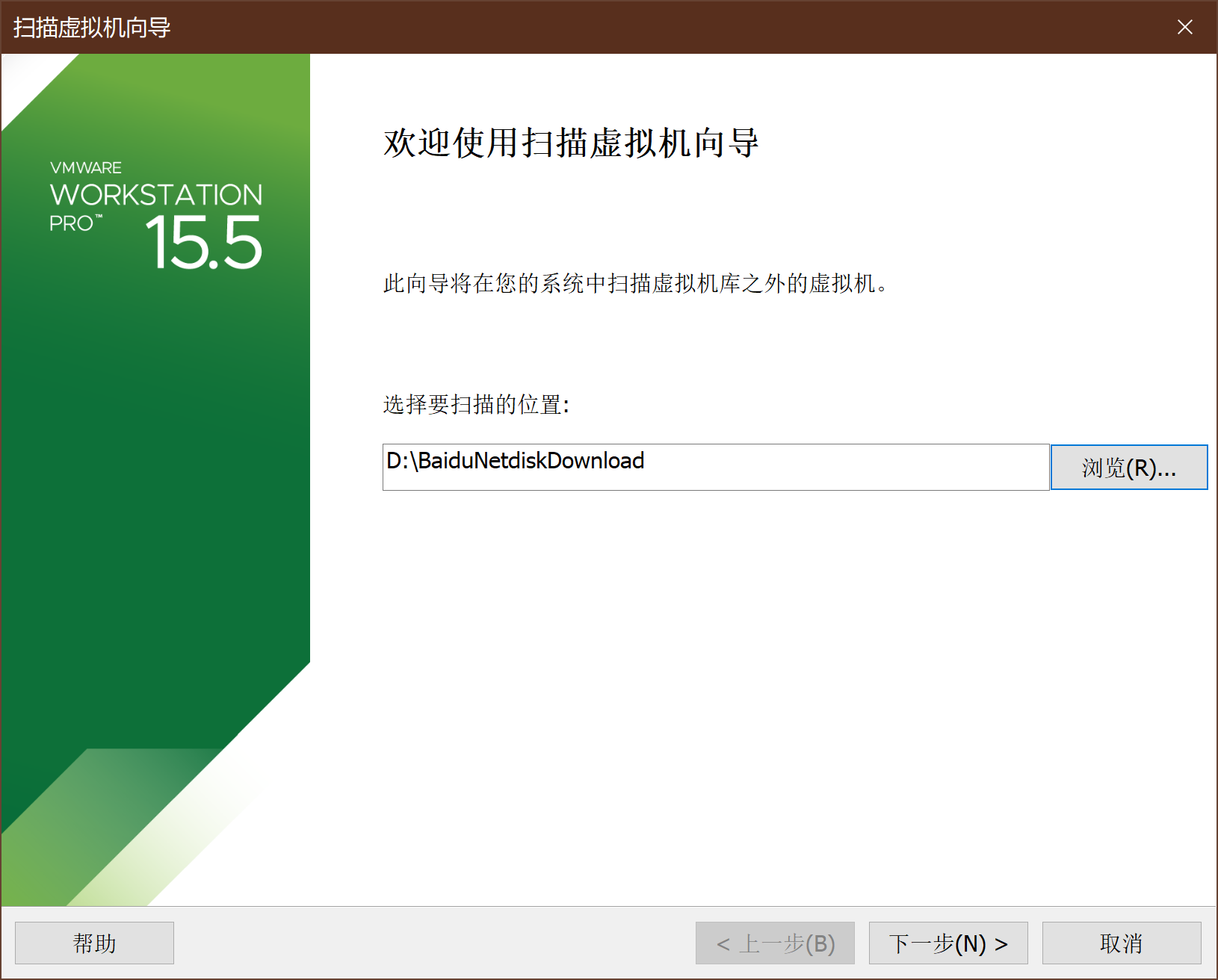
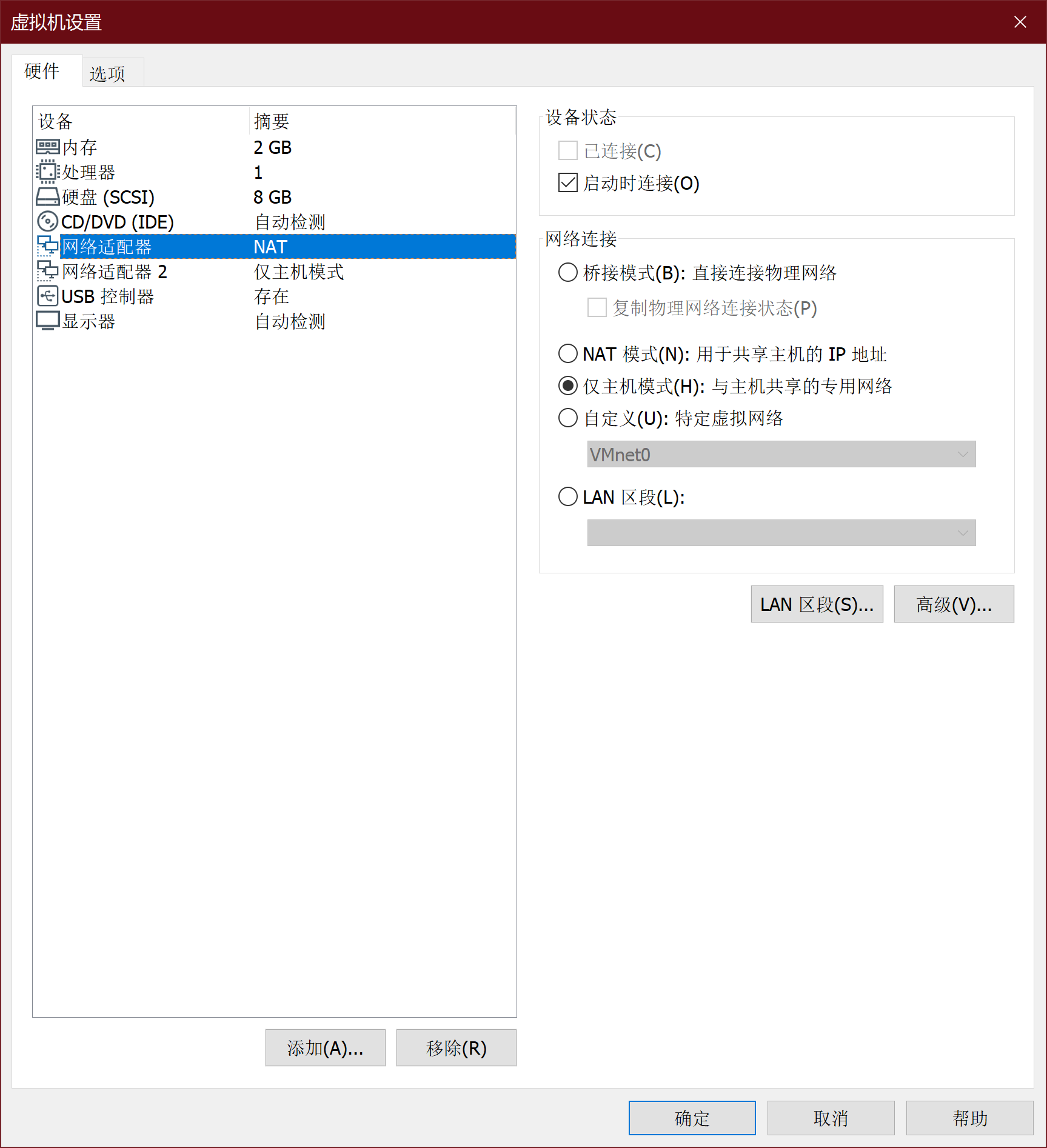
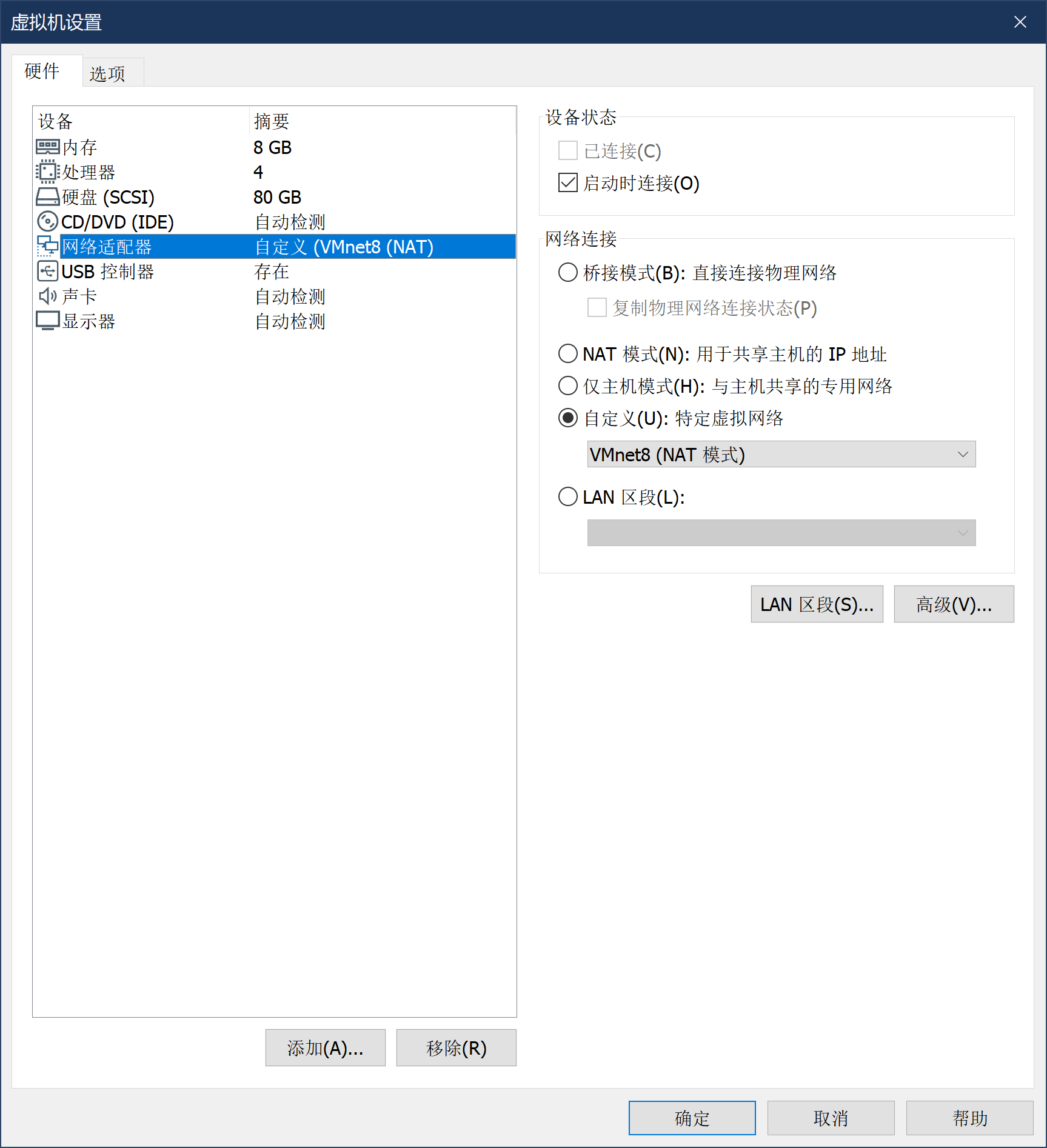
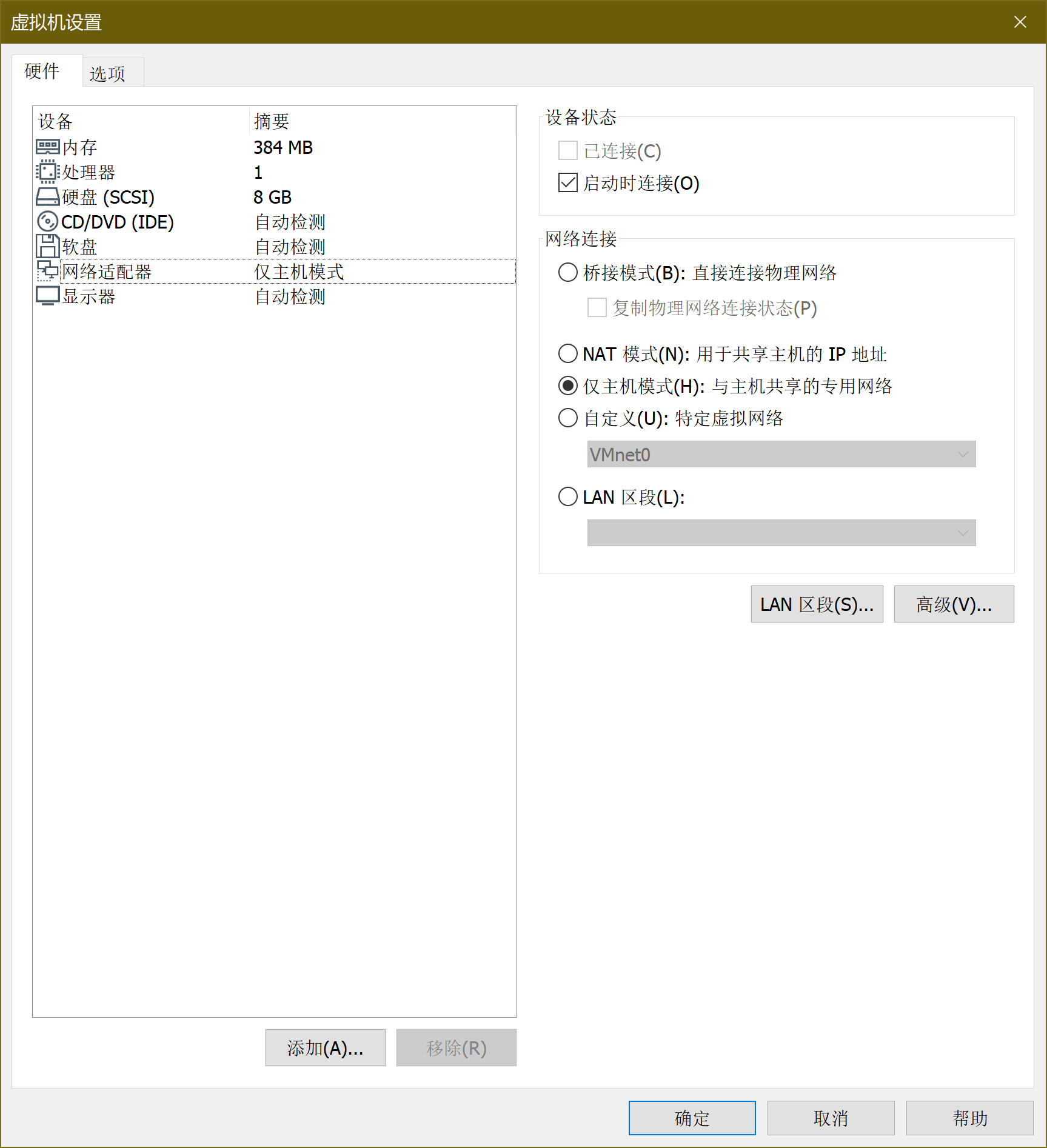
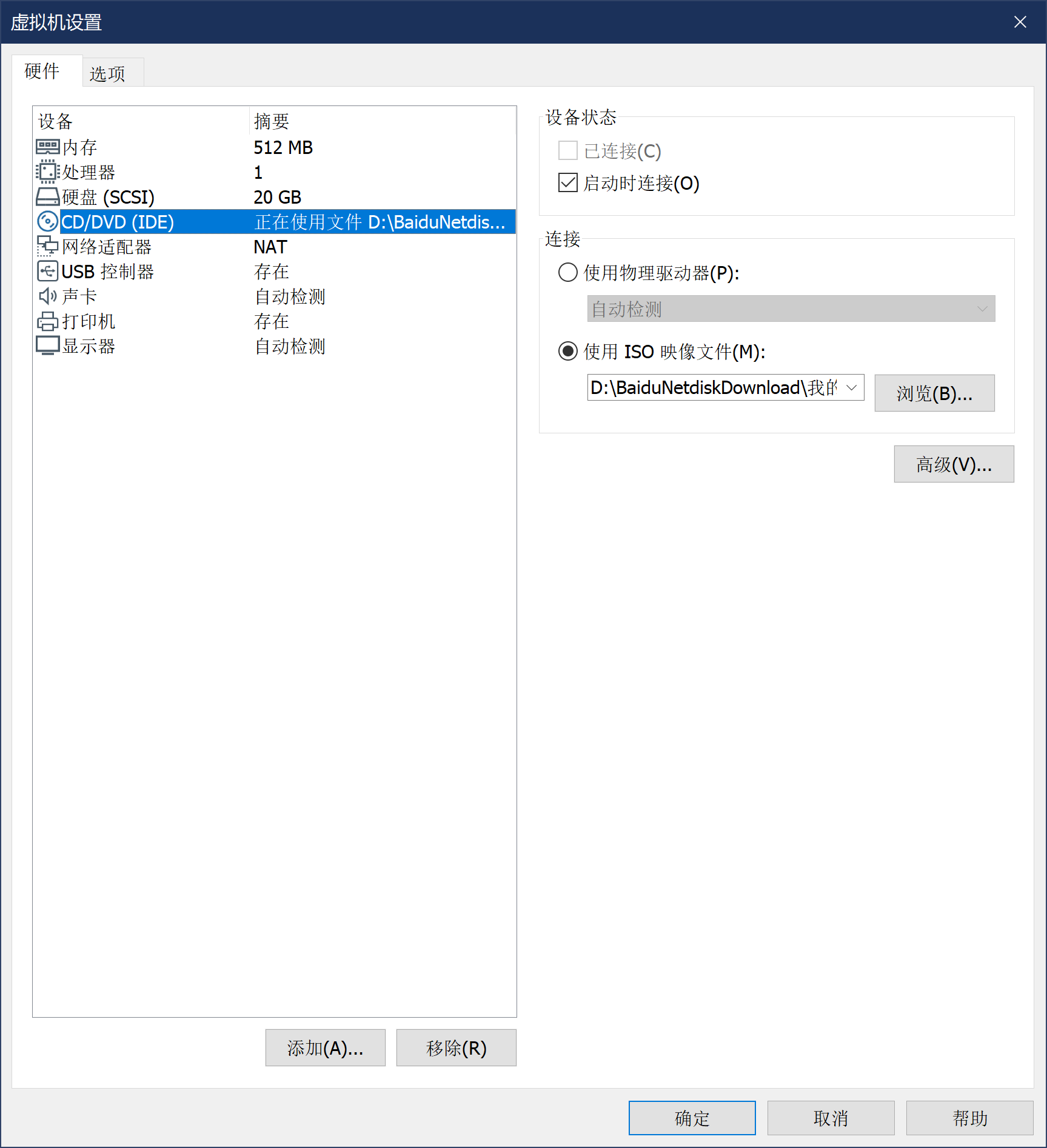
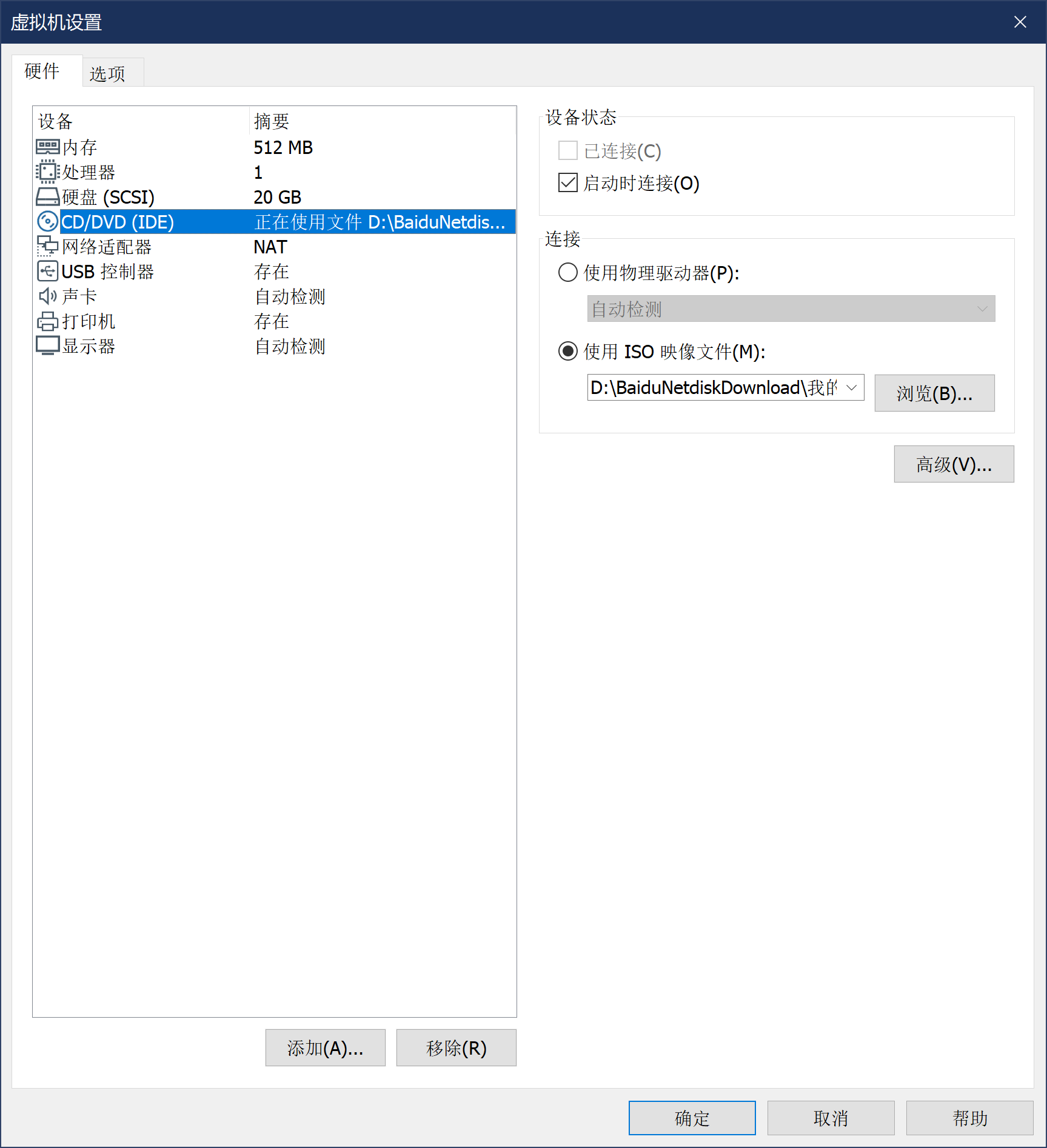
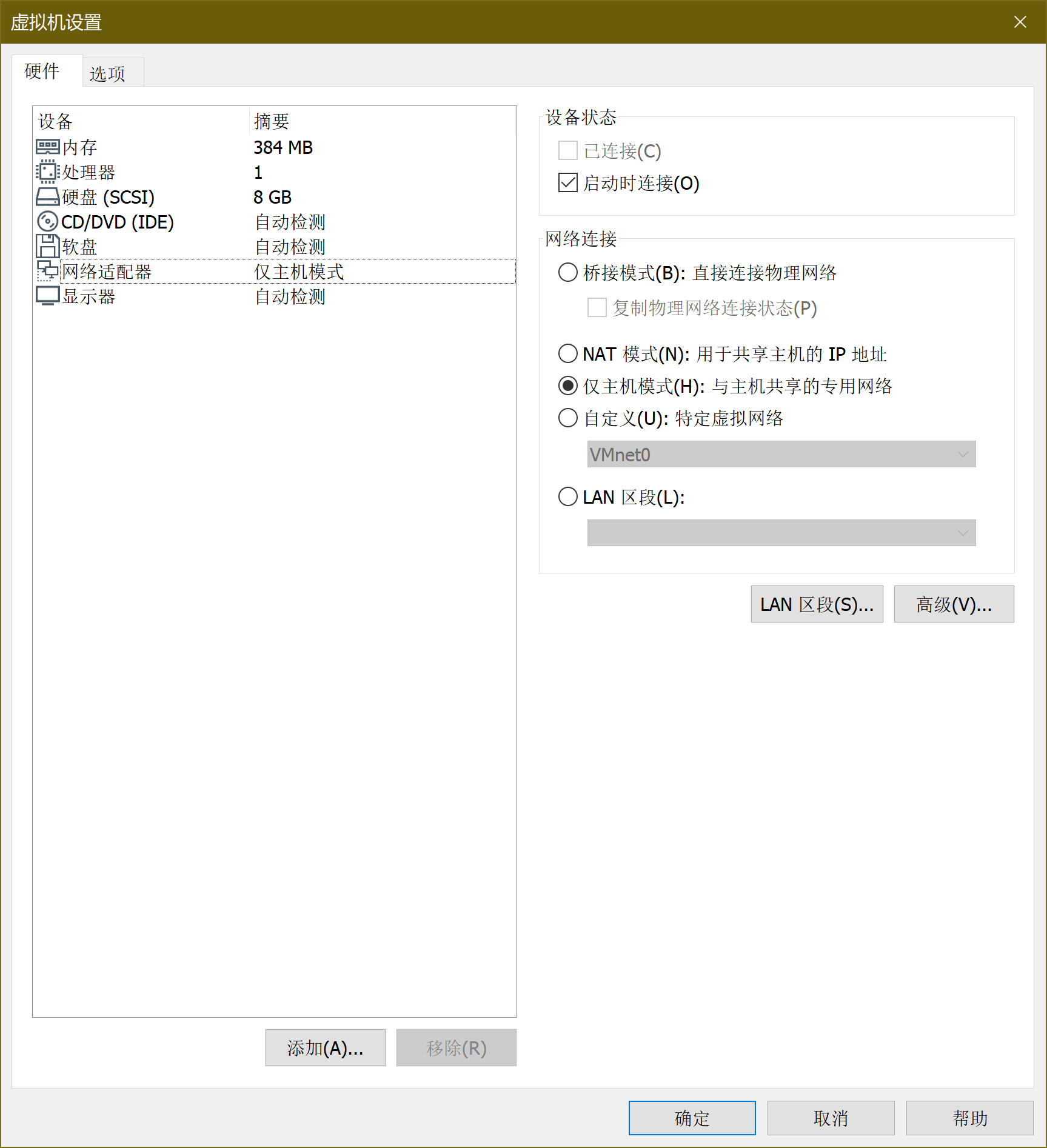
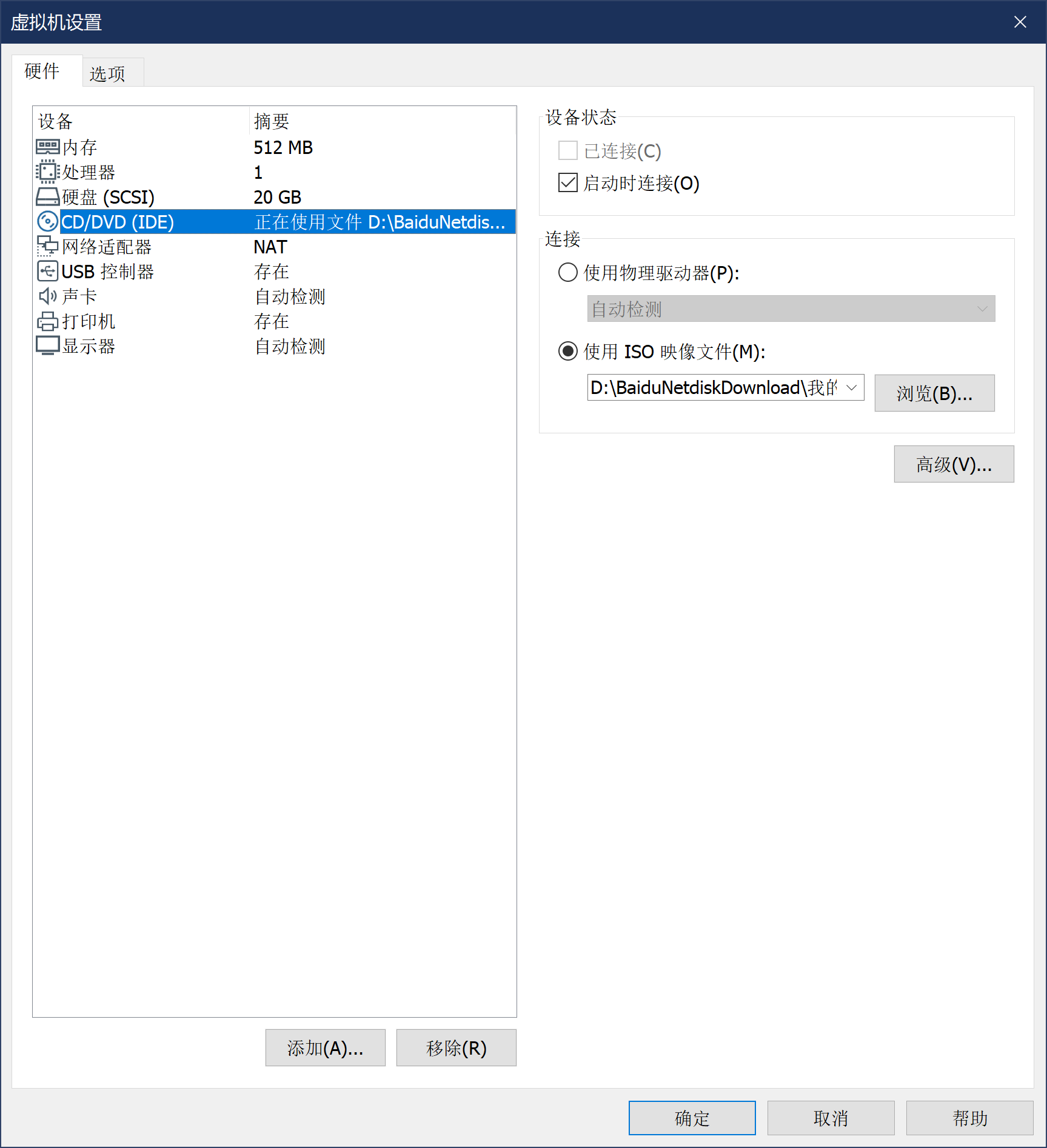
虚拟机设置
-
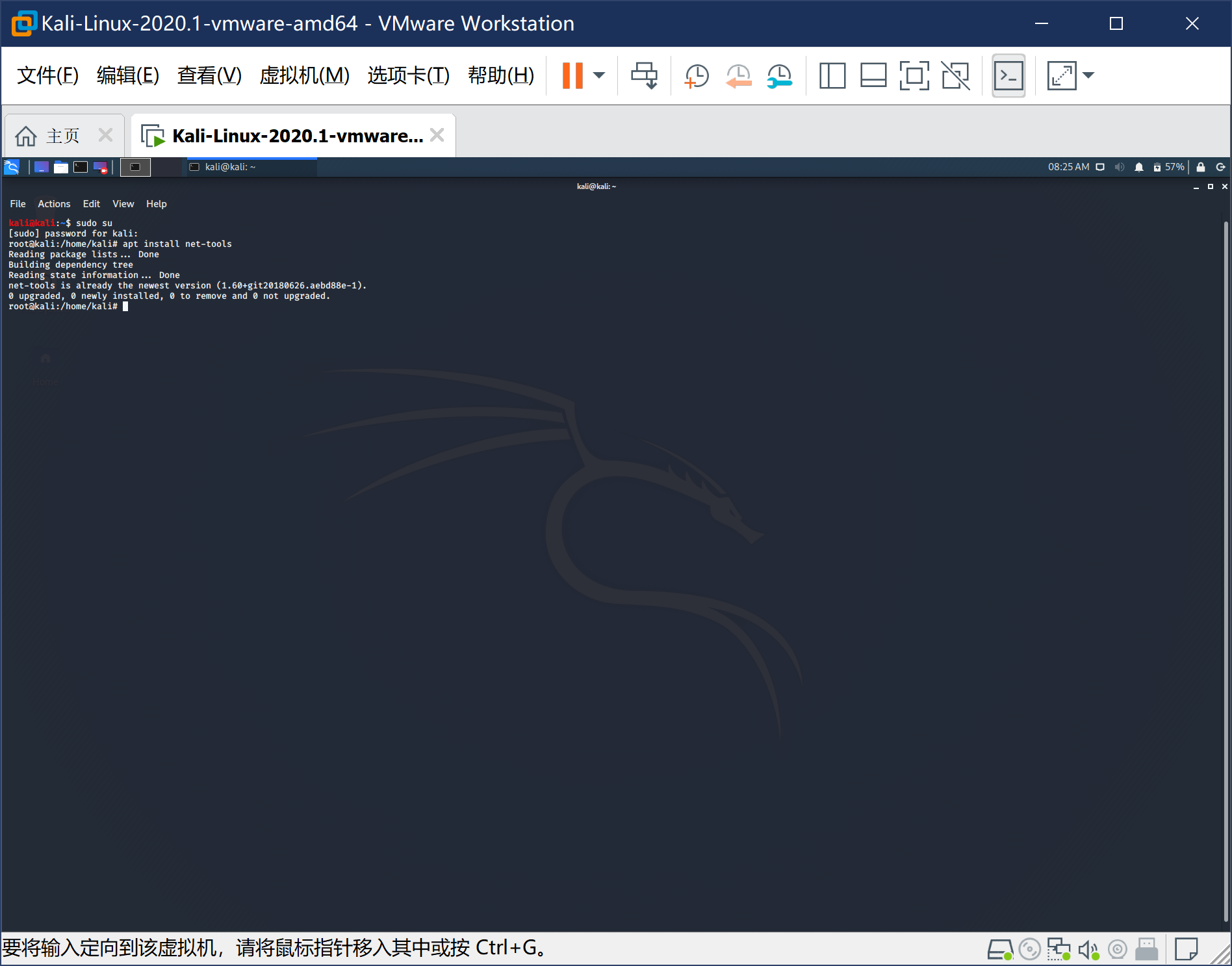
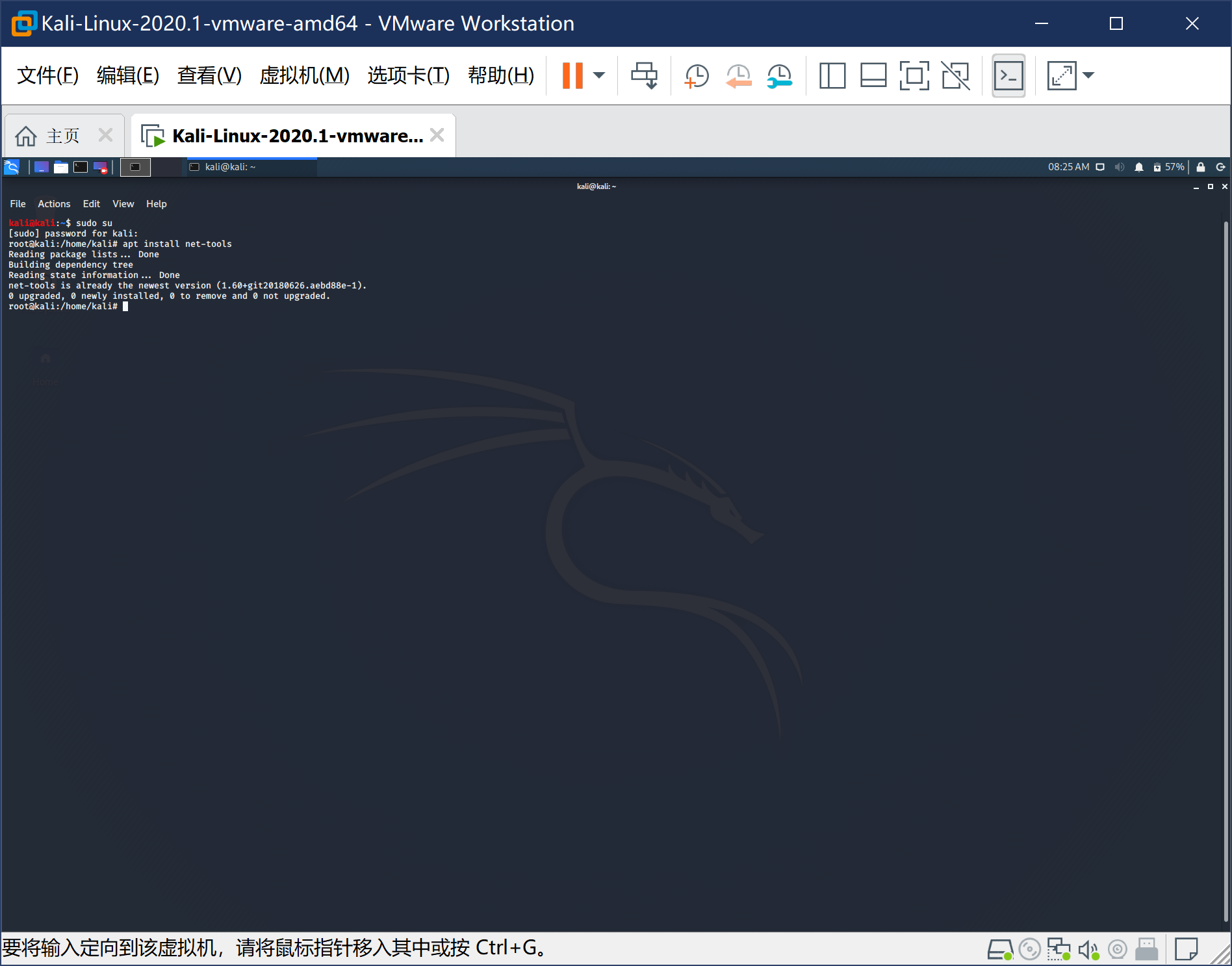
启动虚拟机,进行软件设置。Kali的默认用户名为kali,密码kali, root密码kali(先登录kali,后使用su进行提权,禁止直接root登录)

-
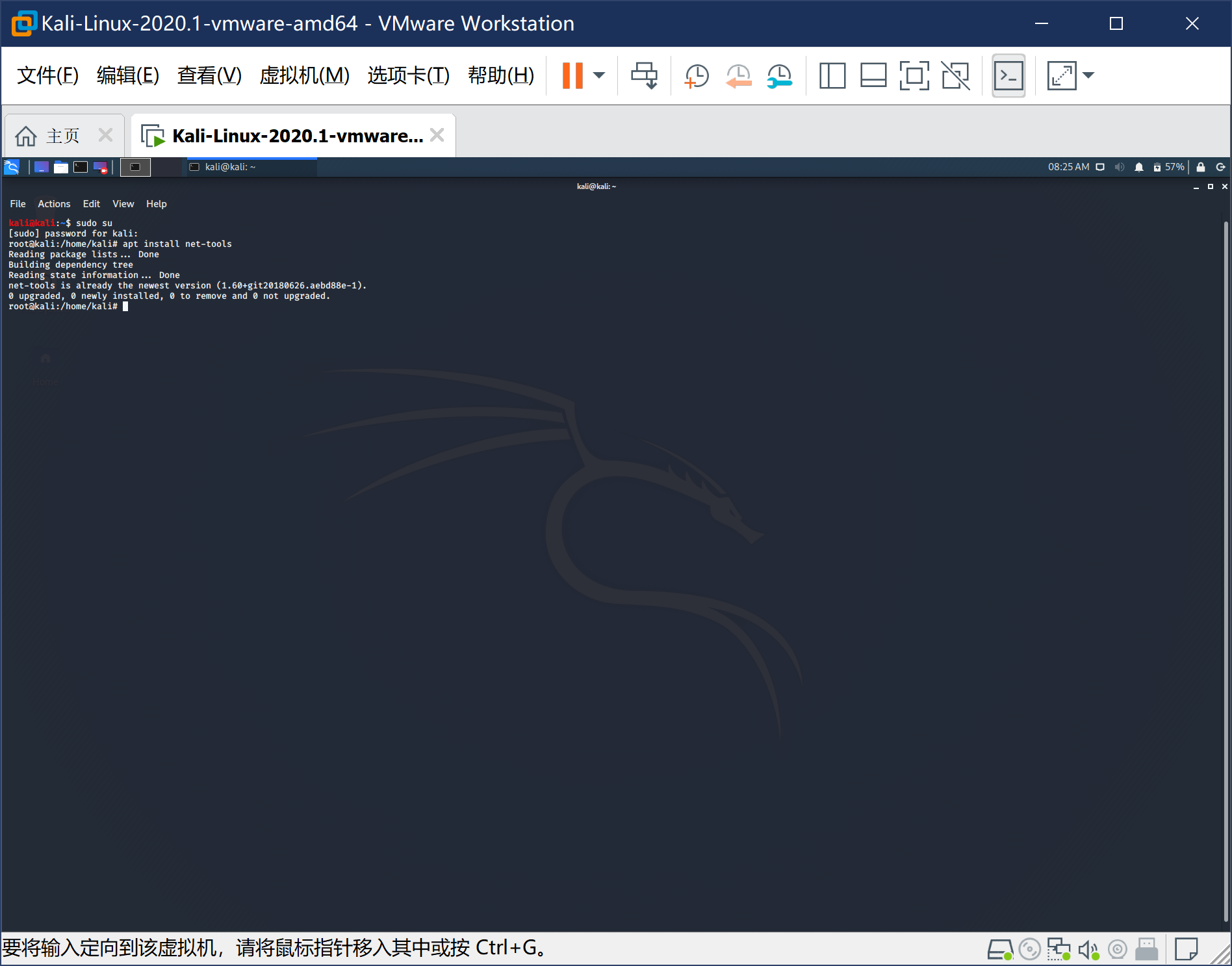
登录->提权->安装net-tools(ifconfig包)->查看网络信息。

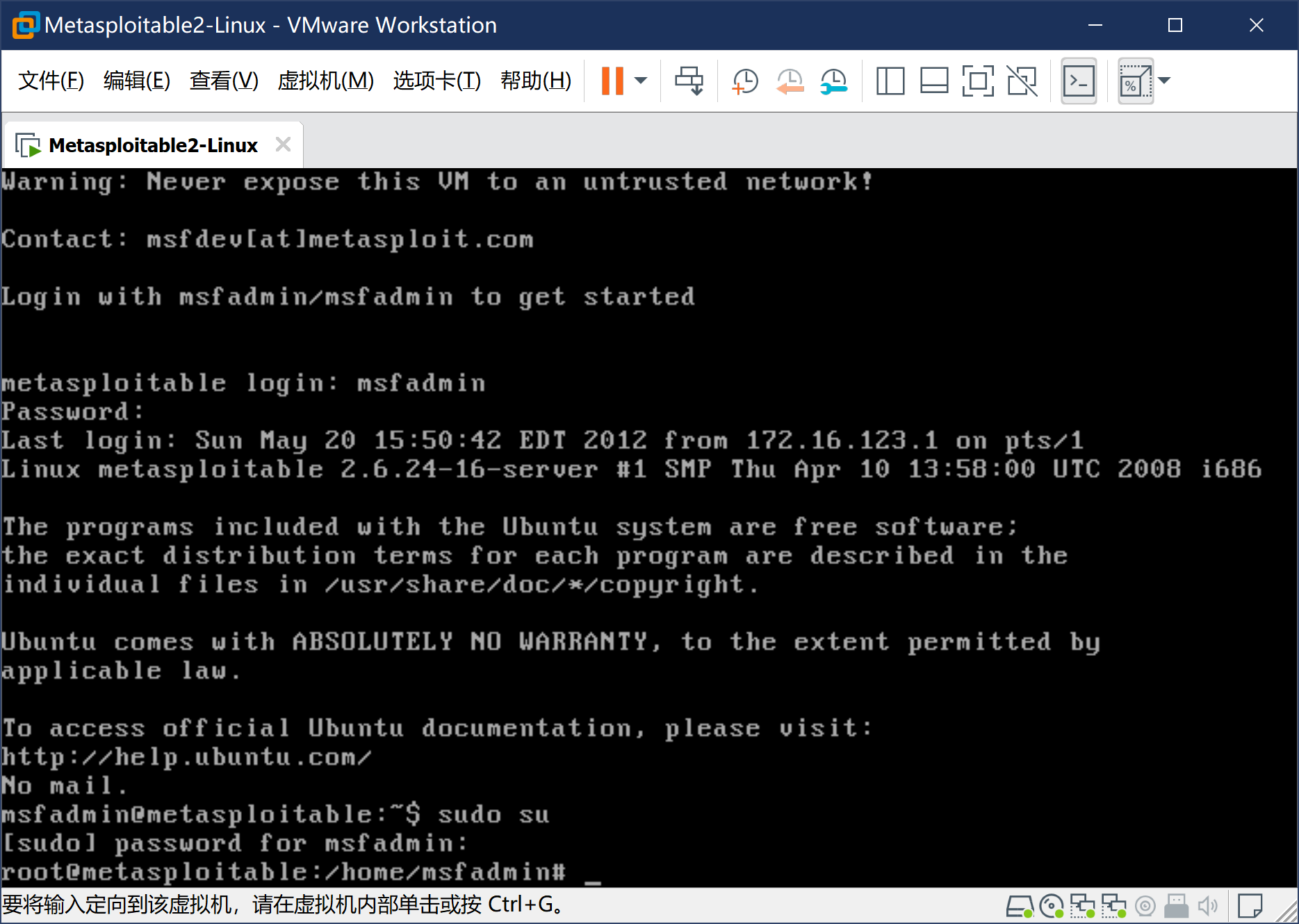
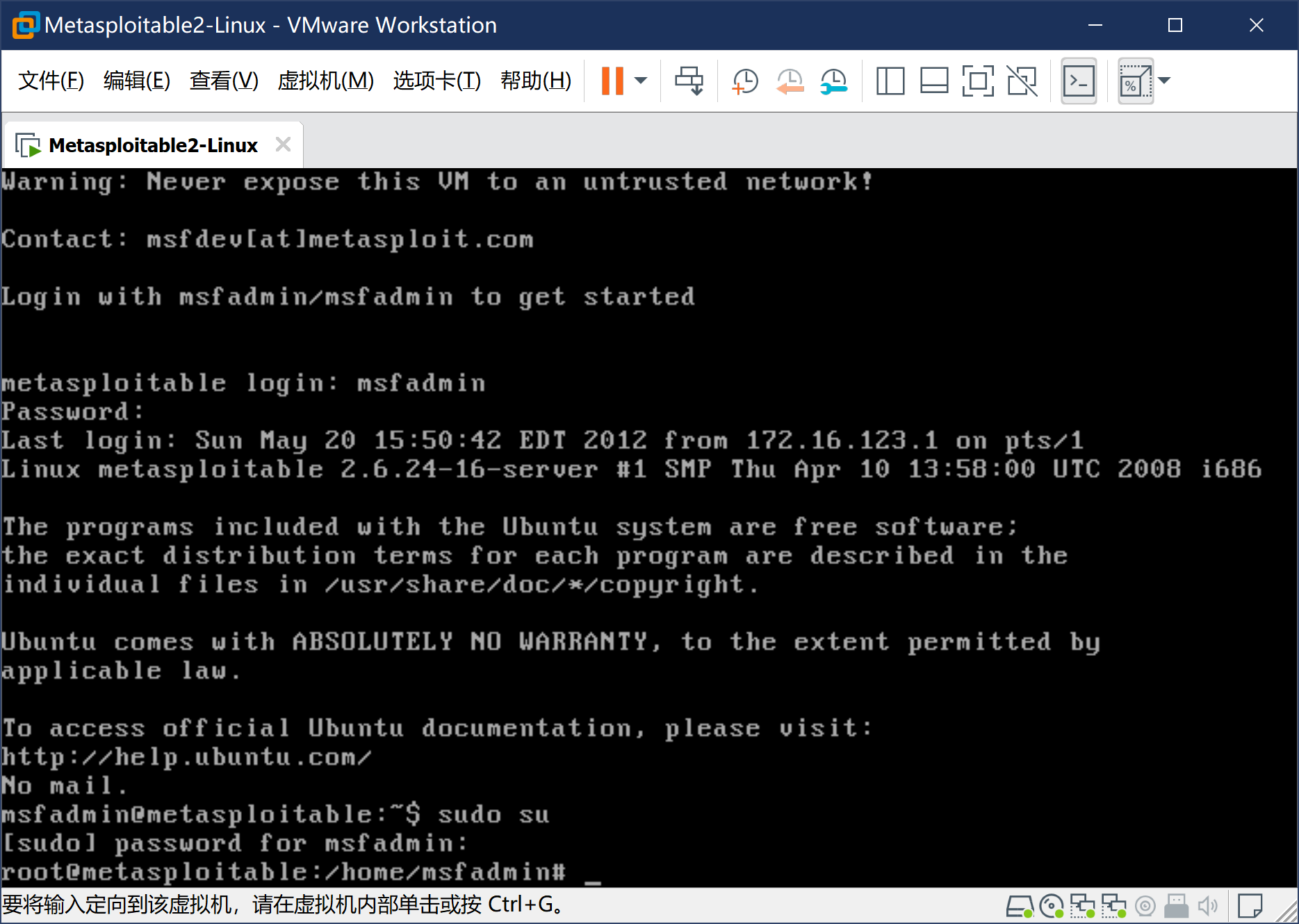
4、安装Metasploitable2-Linux
-
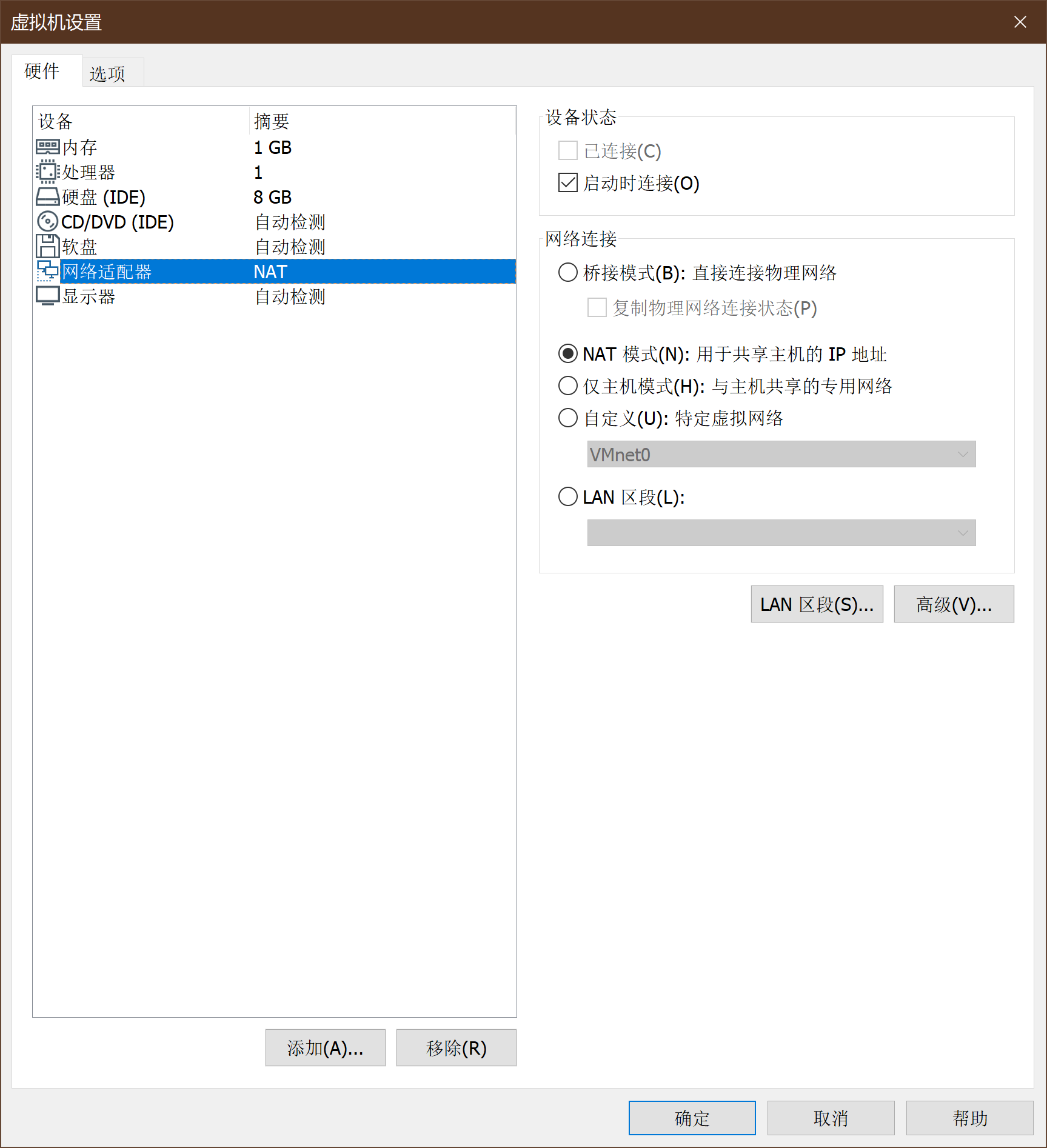
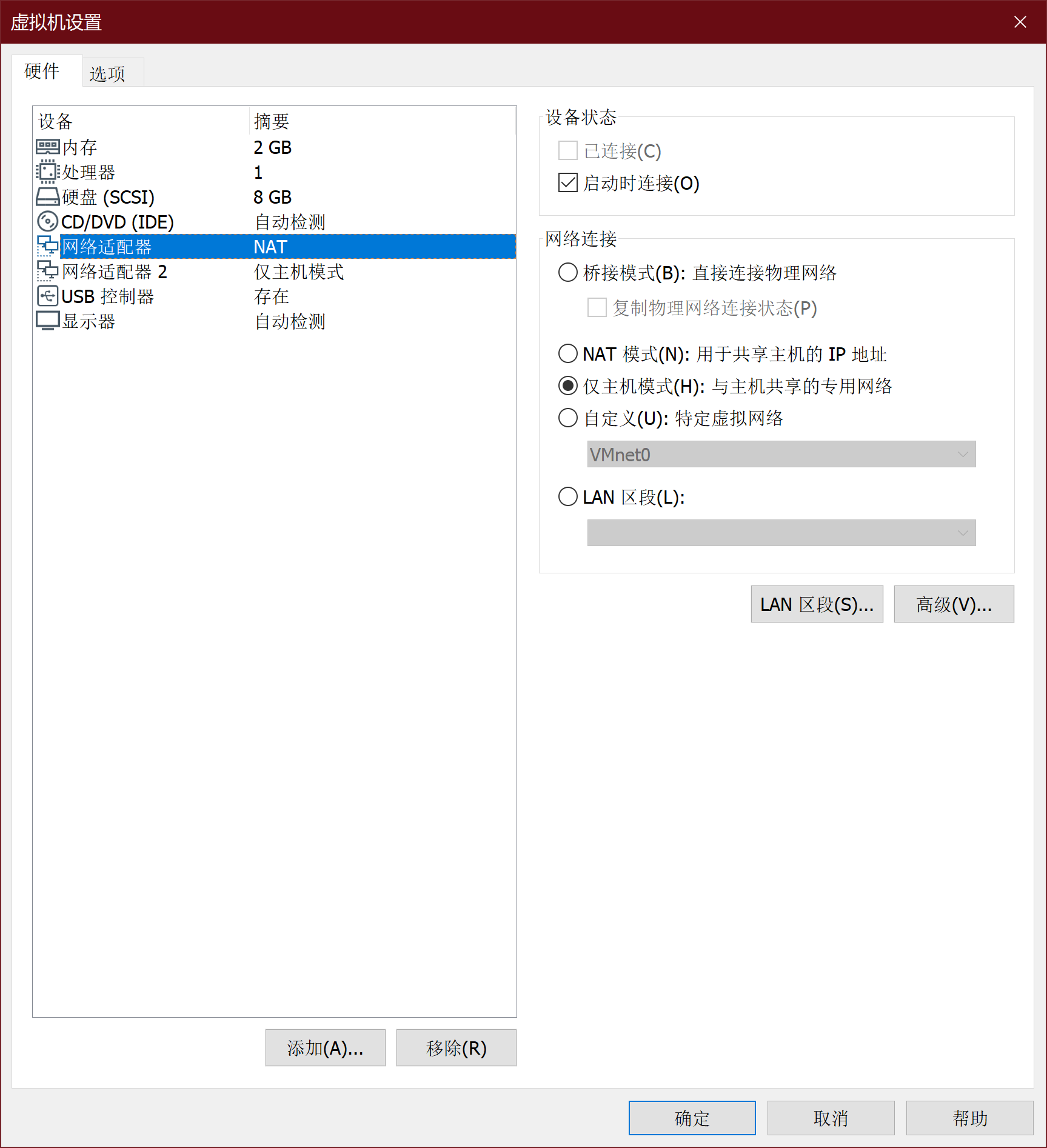
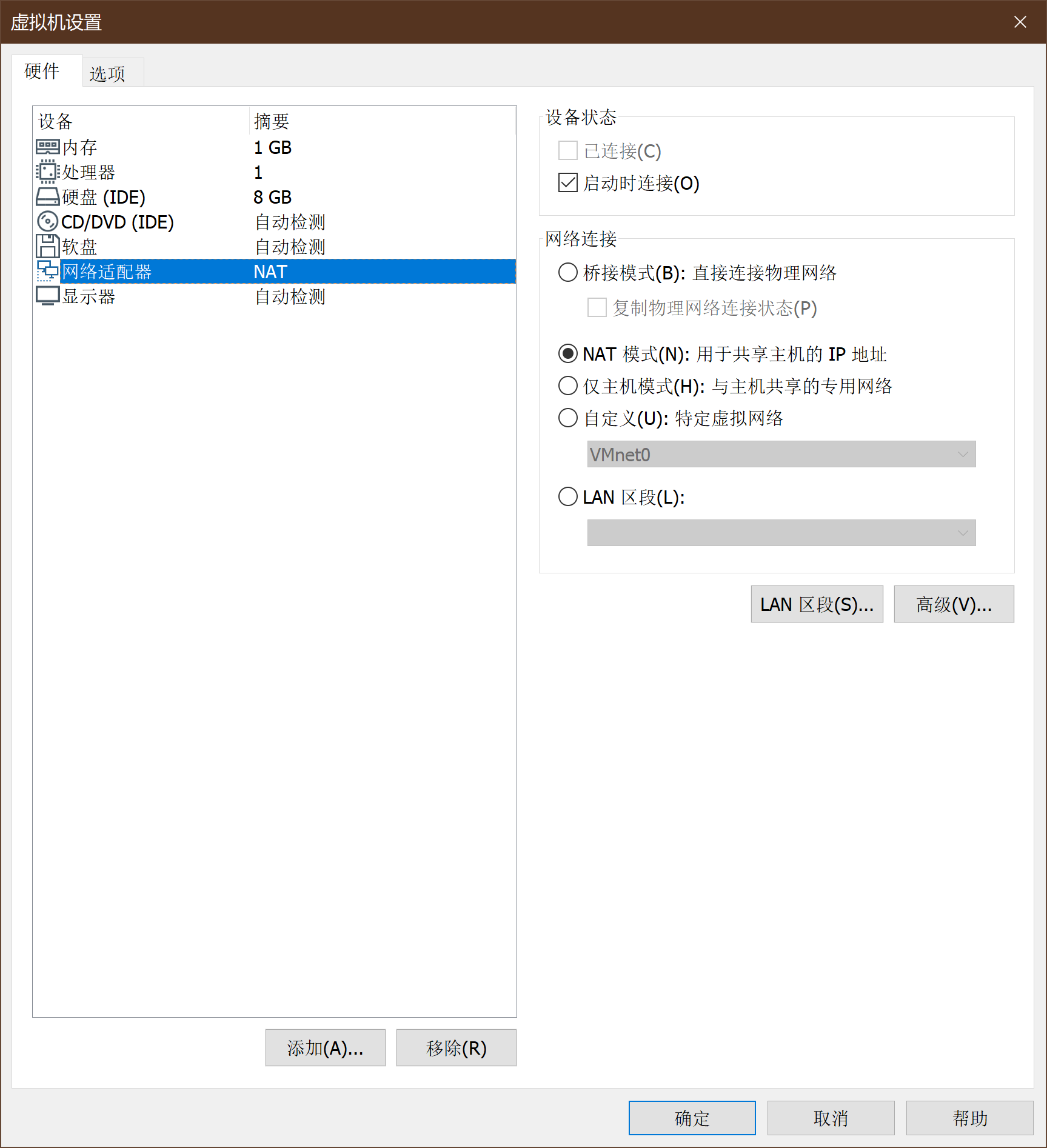
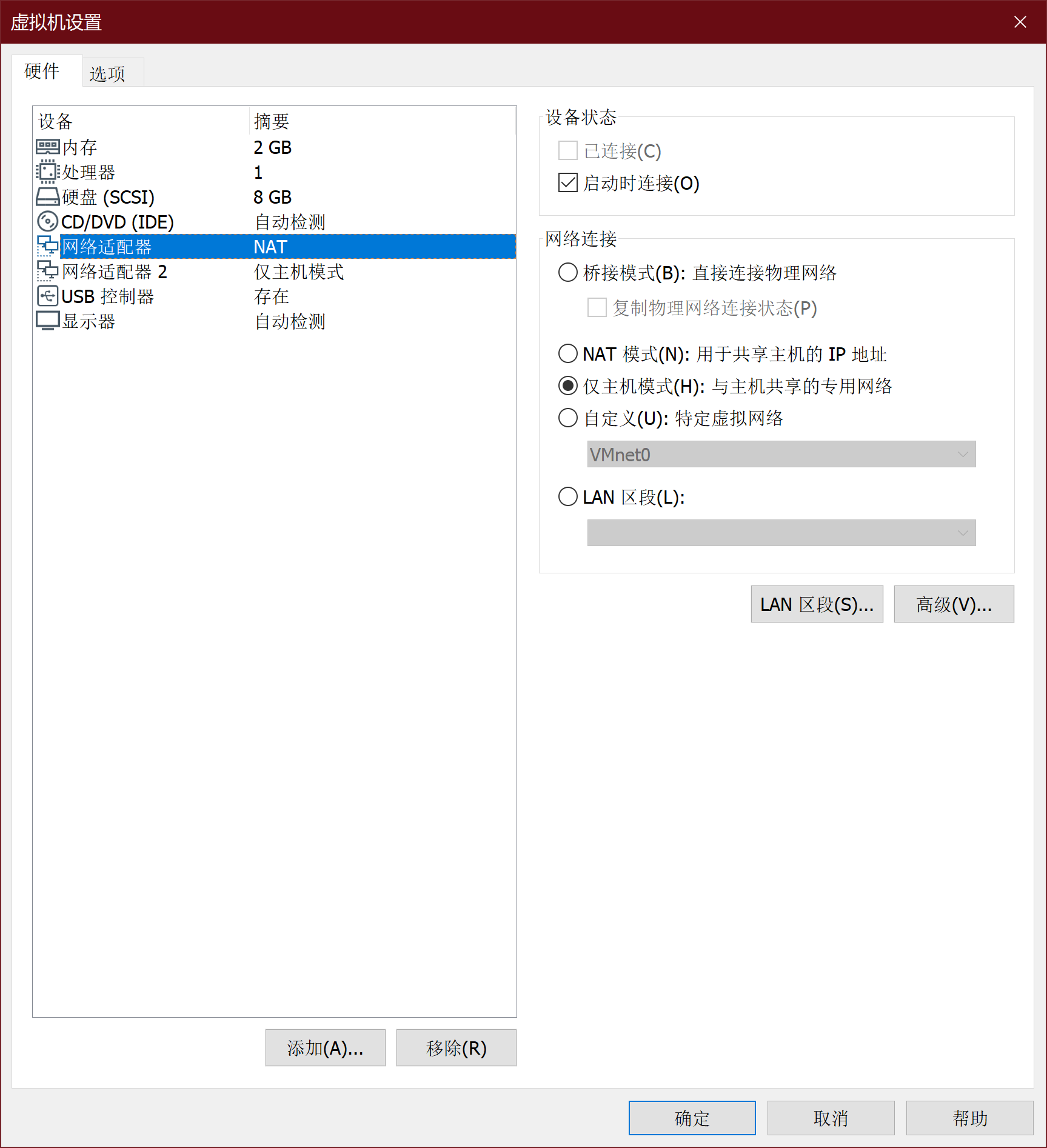
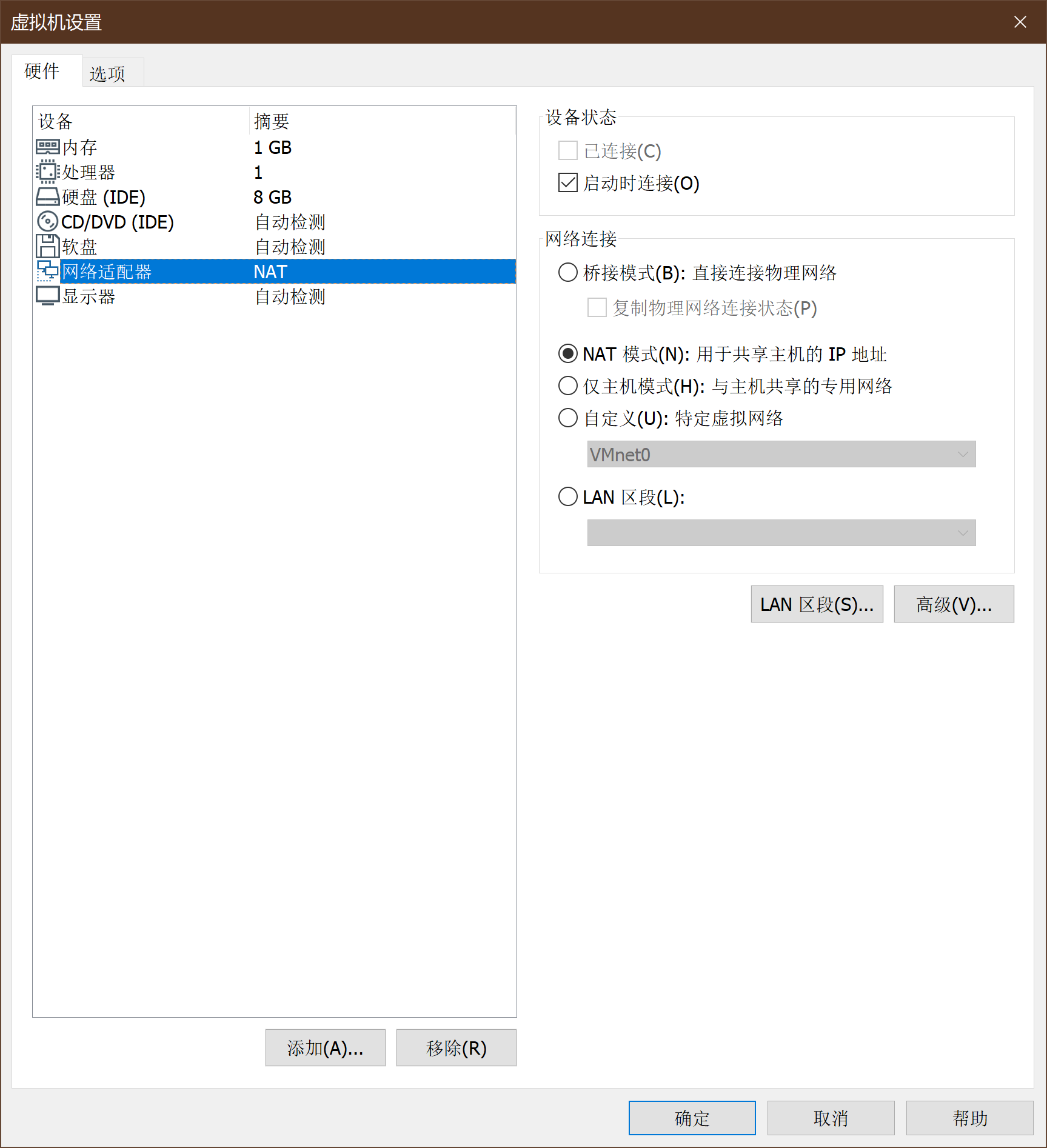
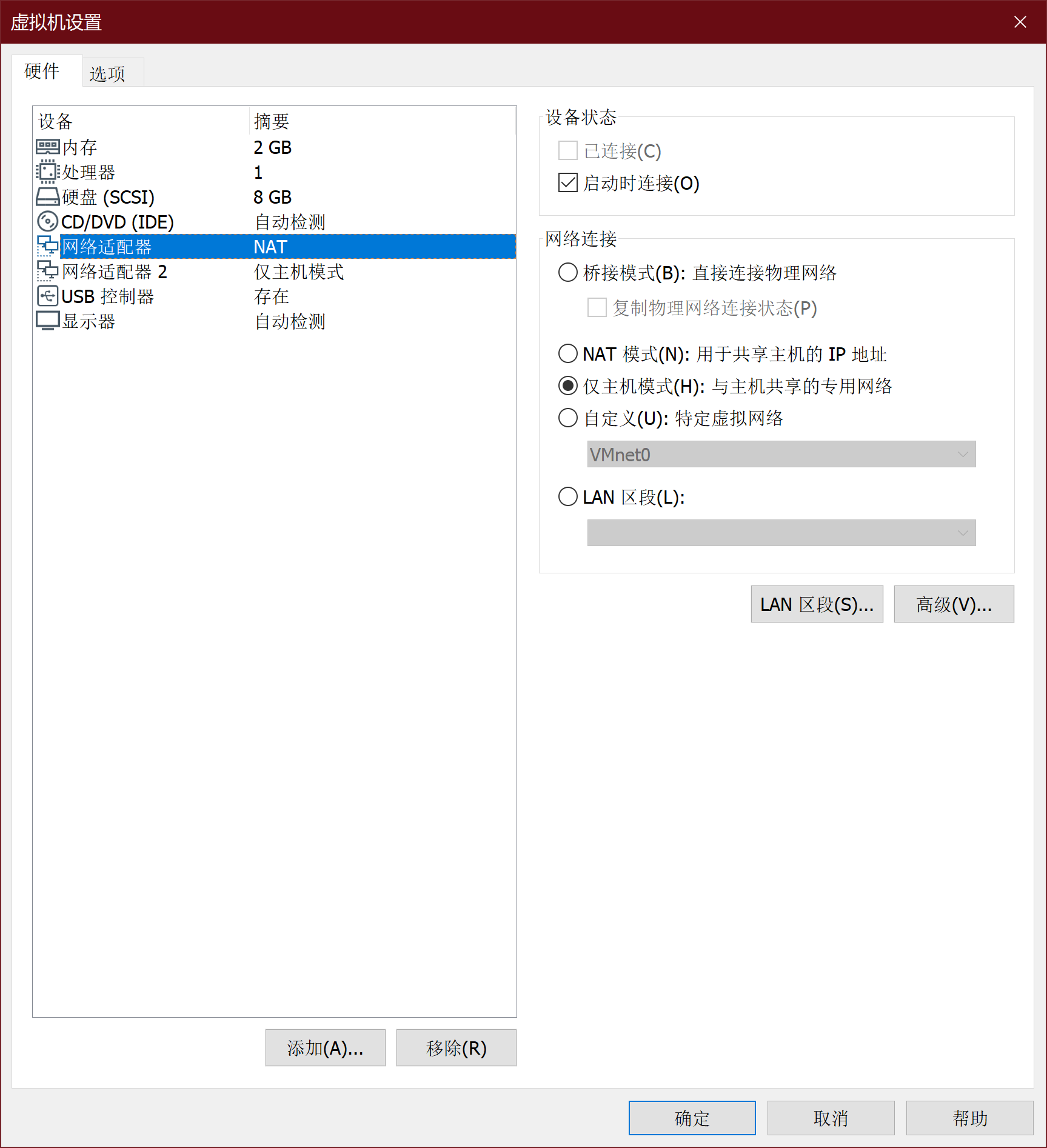
Metasploitable2-Linux通过VM虚拟机镜像给定,导入方式与Kali相同。Metasploitable2-Linux的网卡设置如下:
-
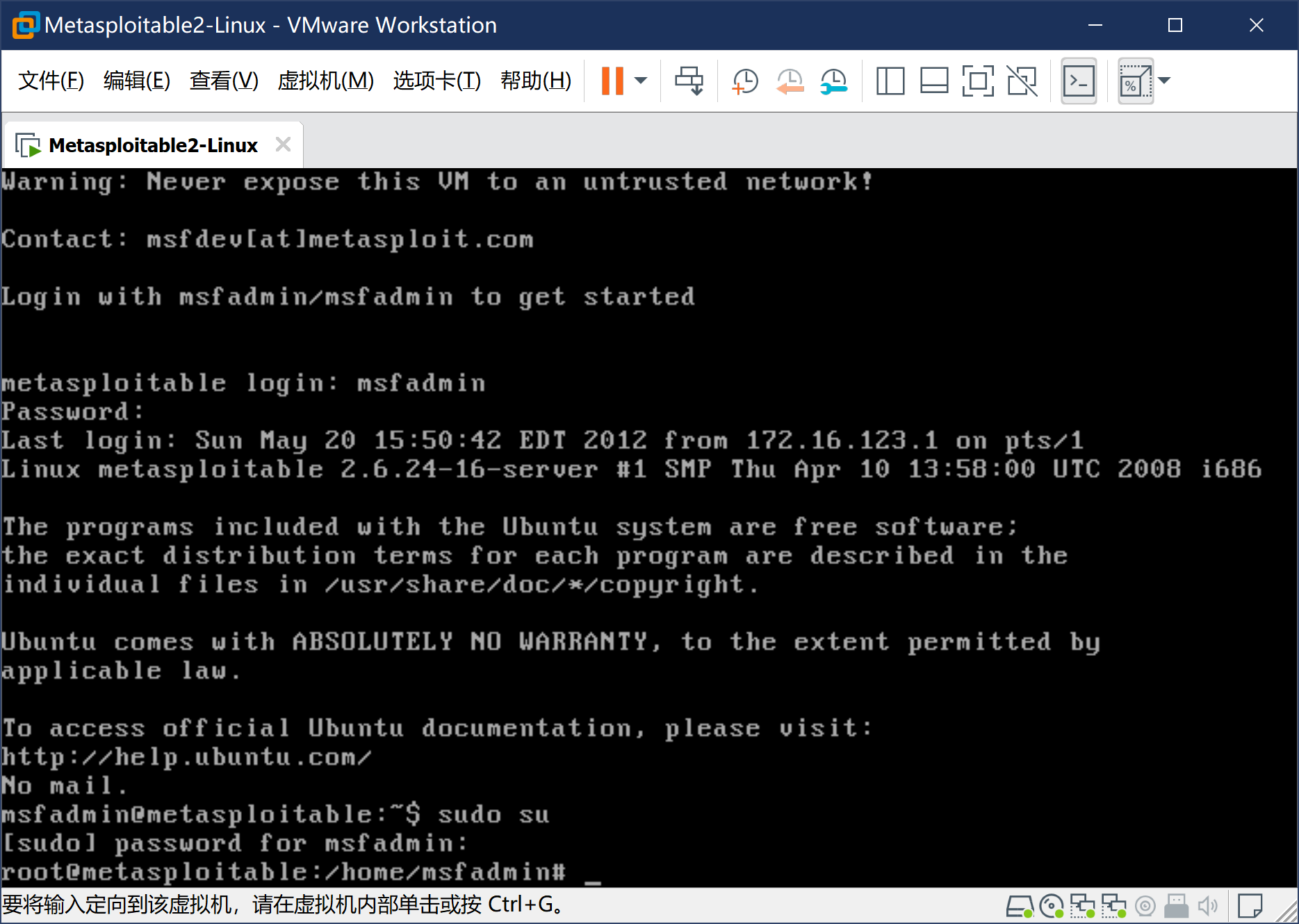
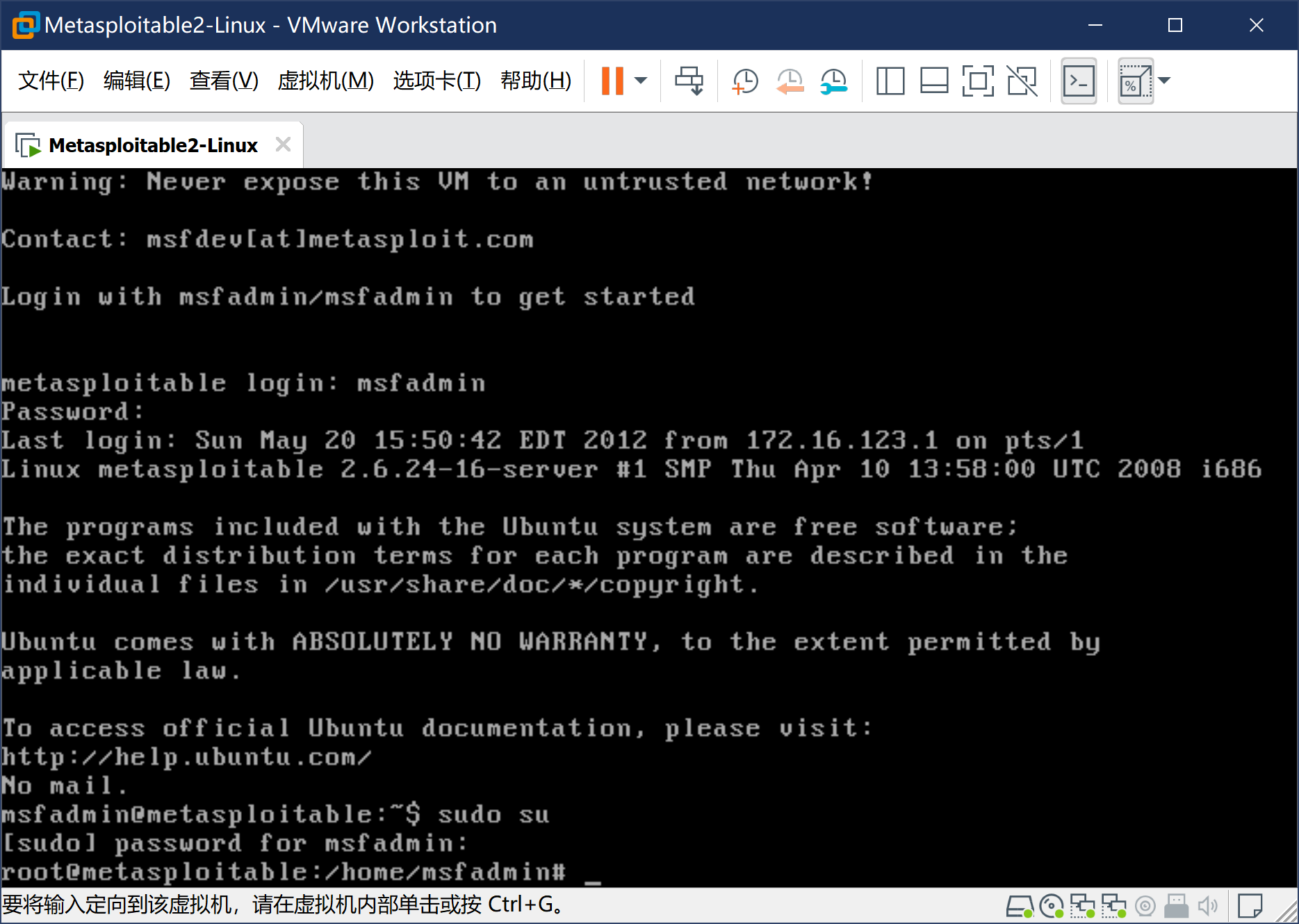
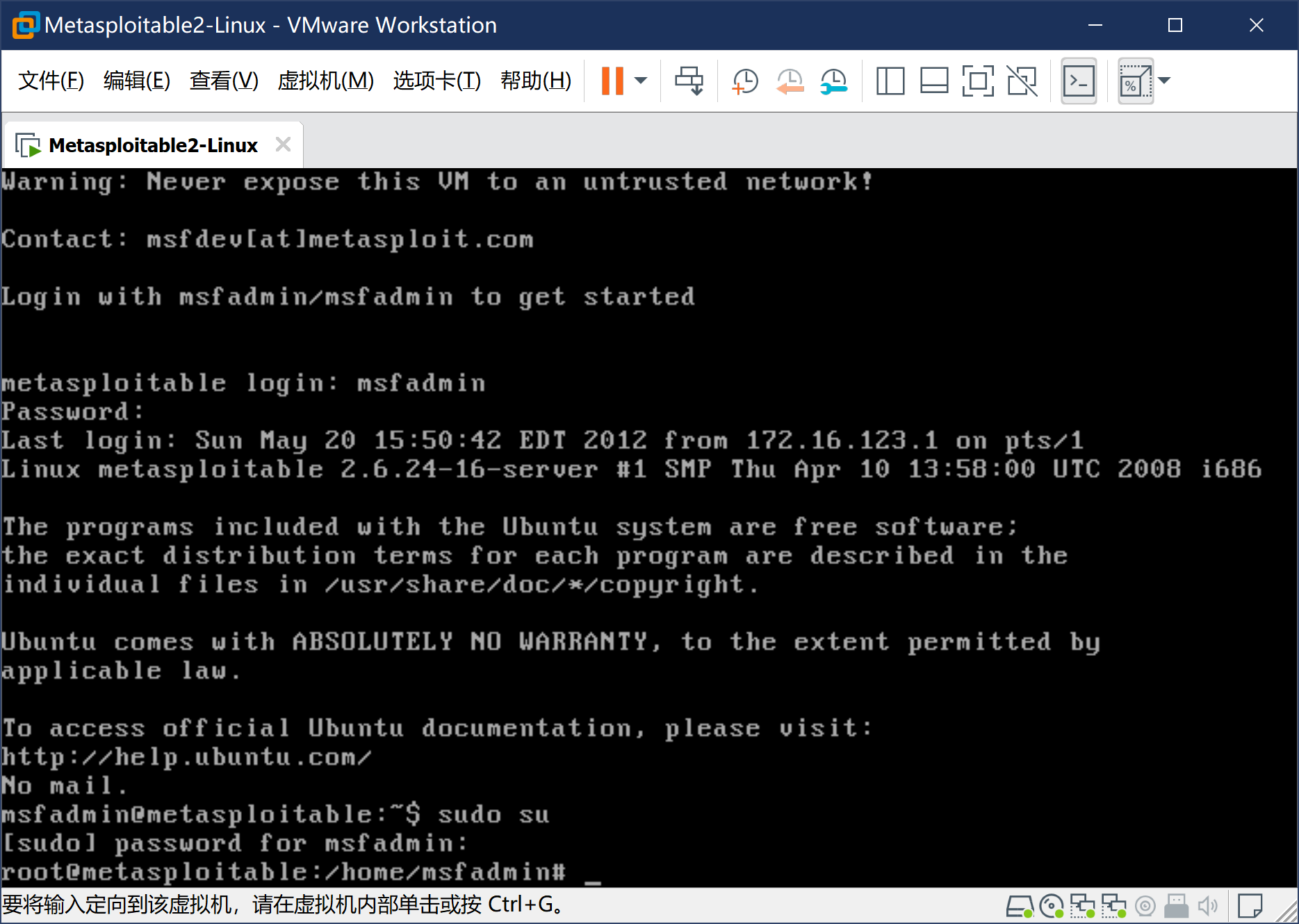
进入系统,账号msfadmin,密码msfadmin。此处需要手动设置IP地址,具体命令如下:先通过sudo su命令提升权限(密码msfadmin)
-
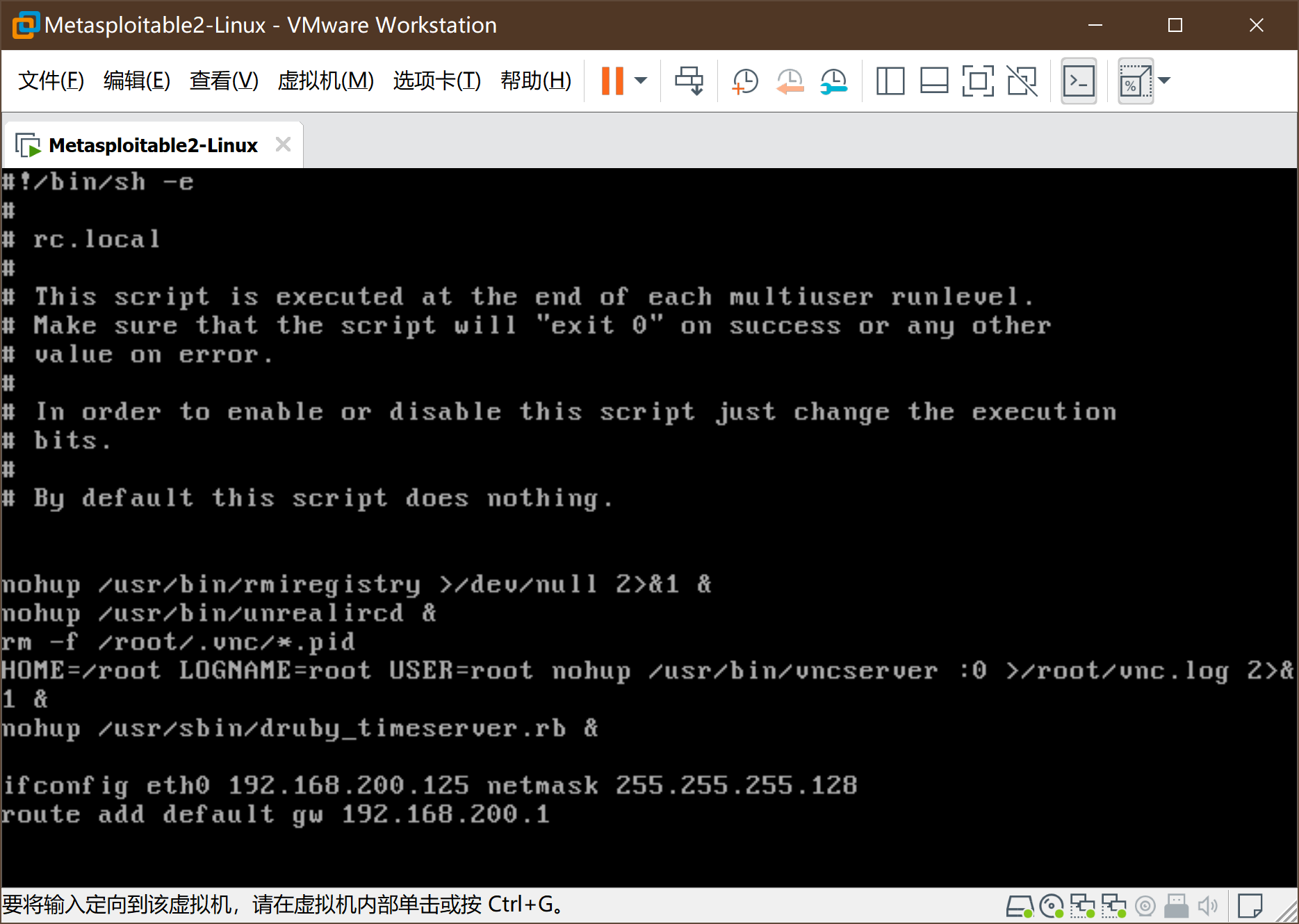
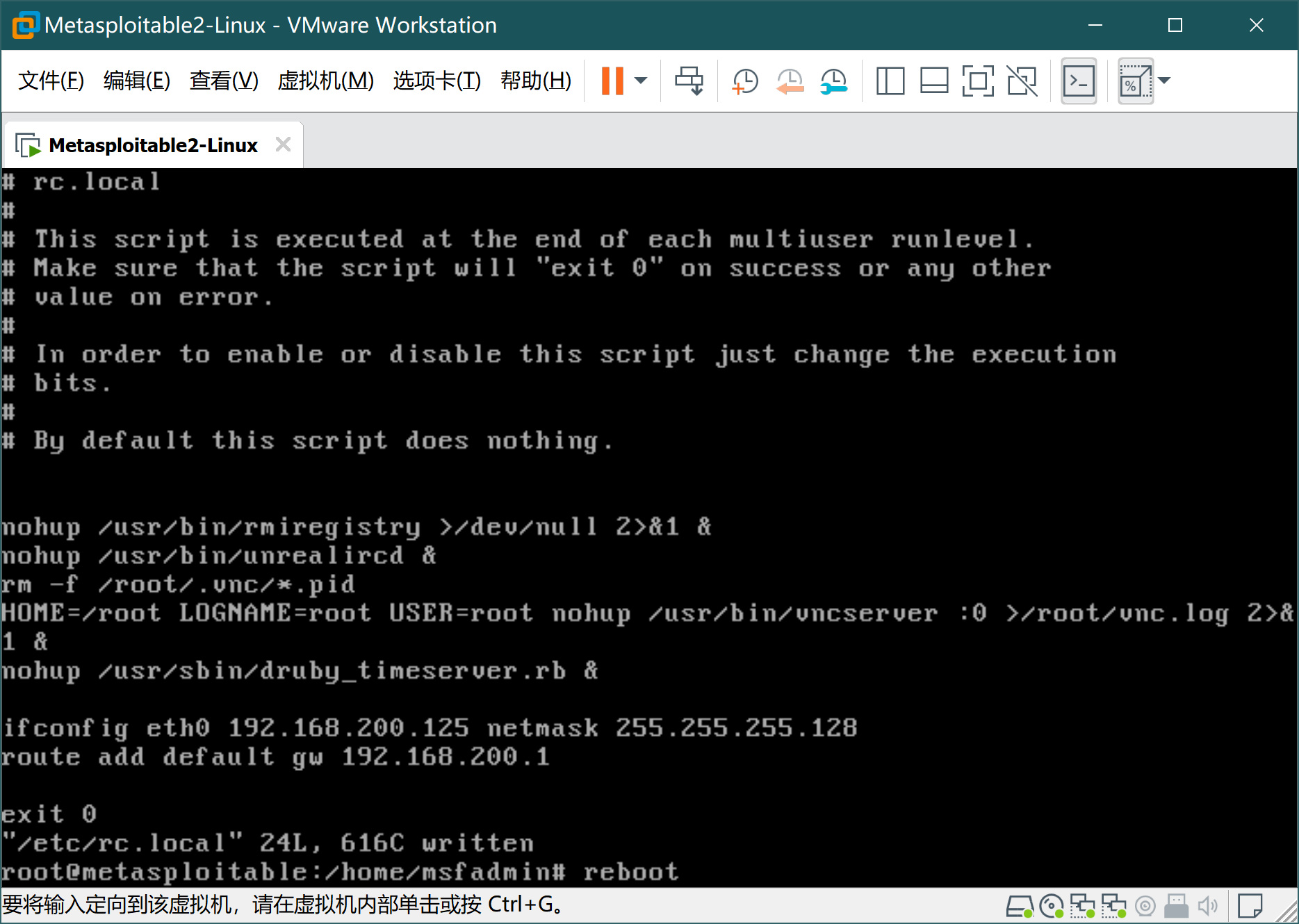
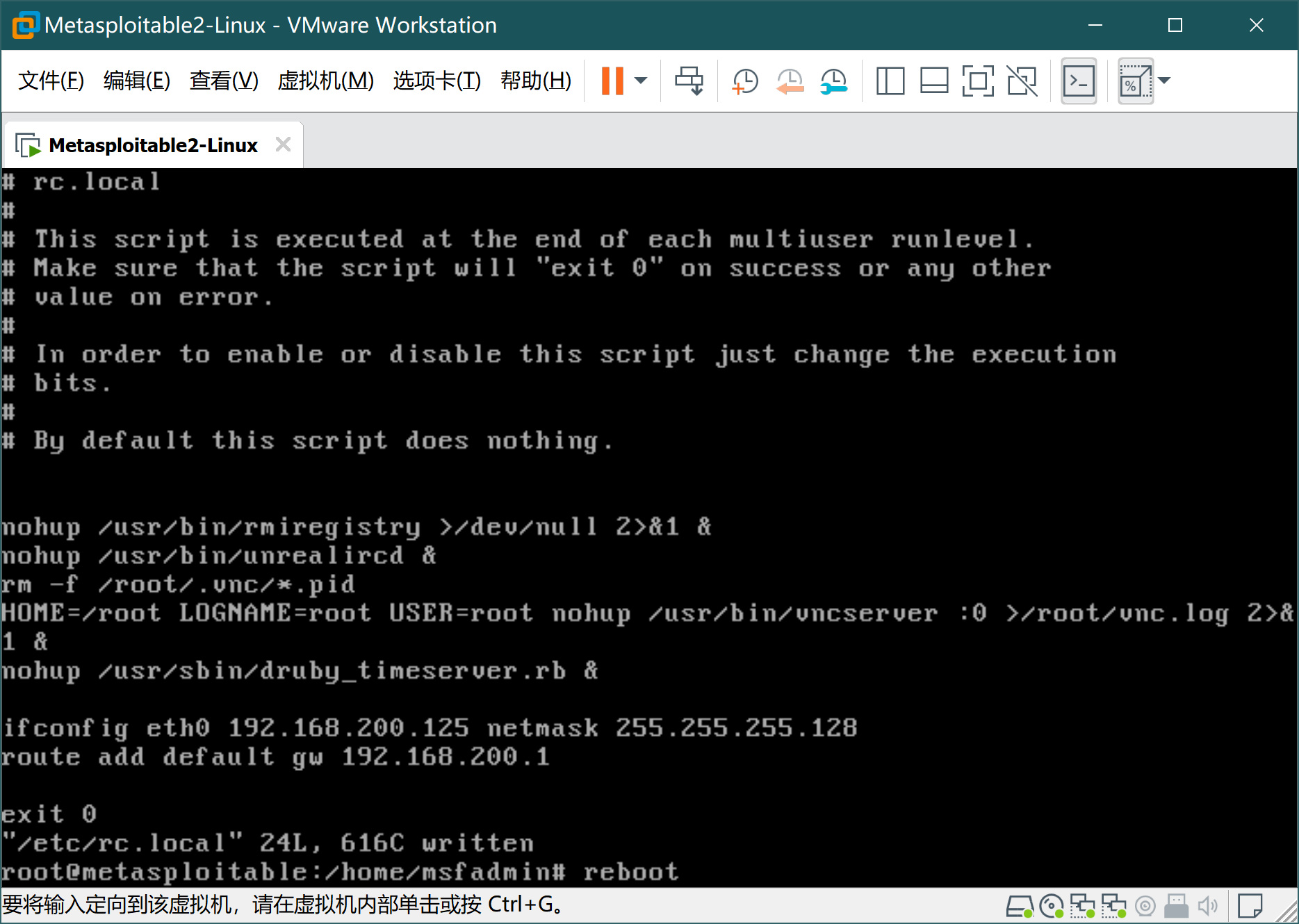
执行如下命令
vim /etc/rc.local
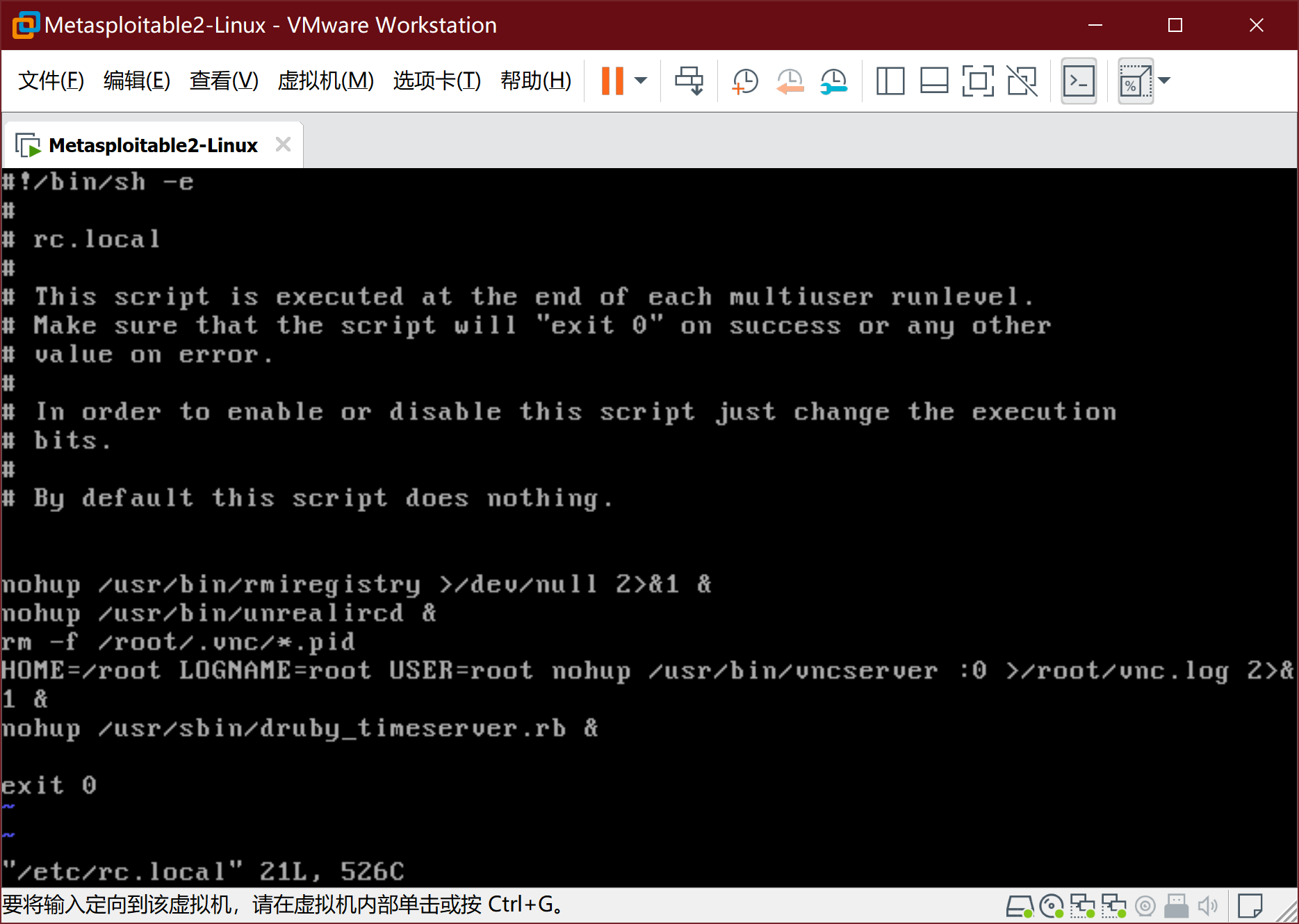
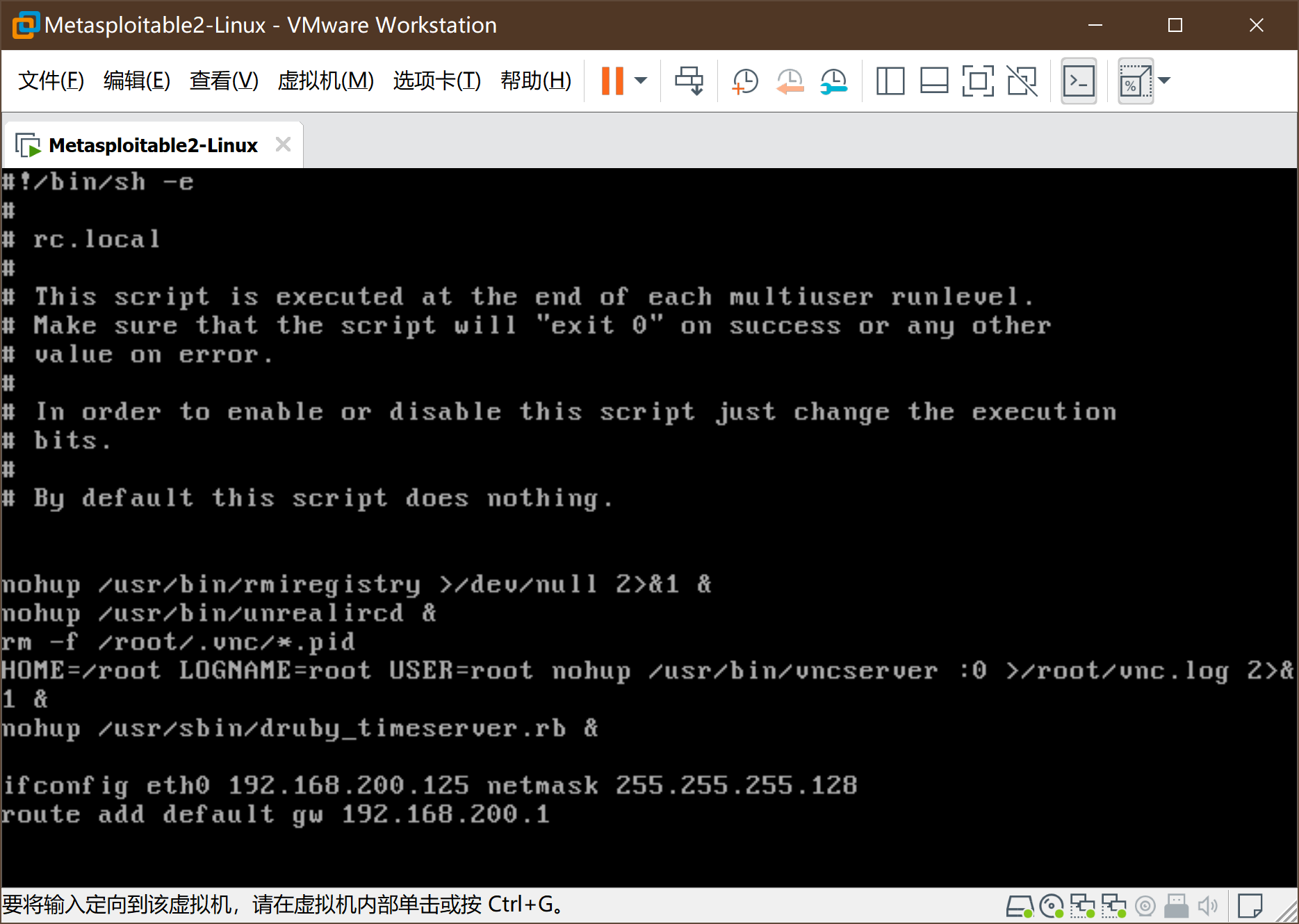
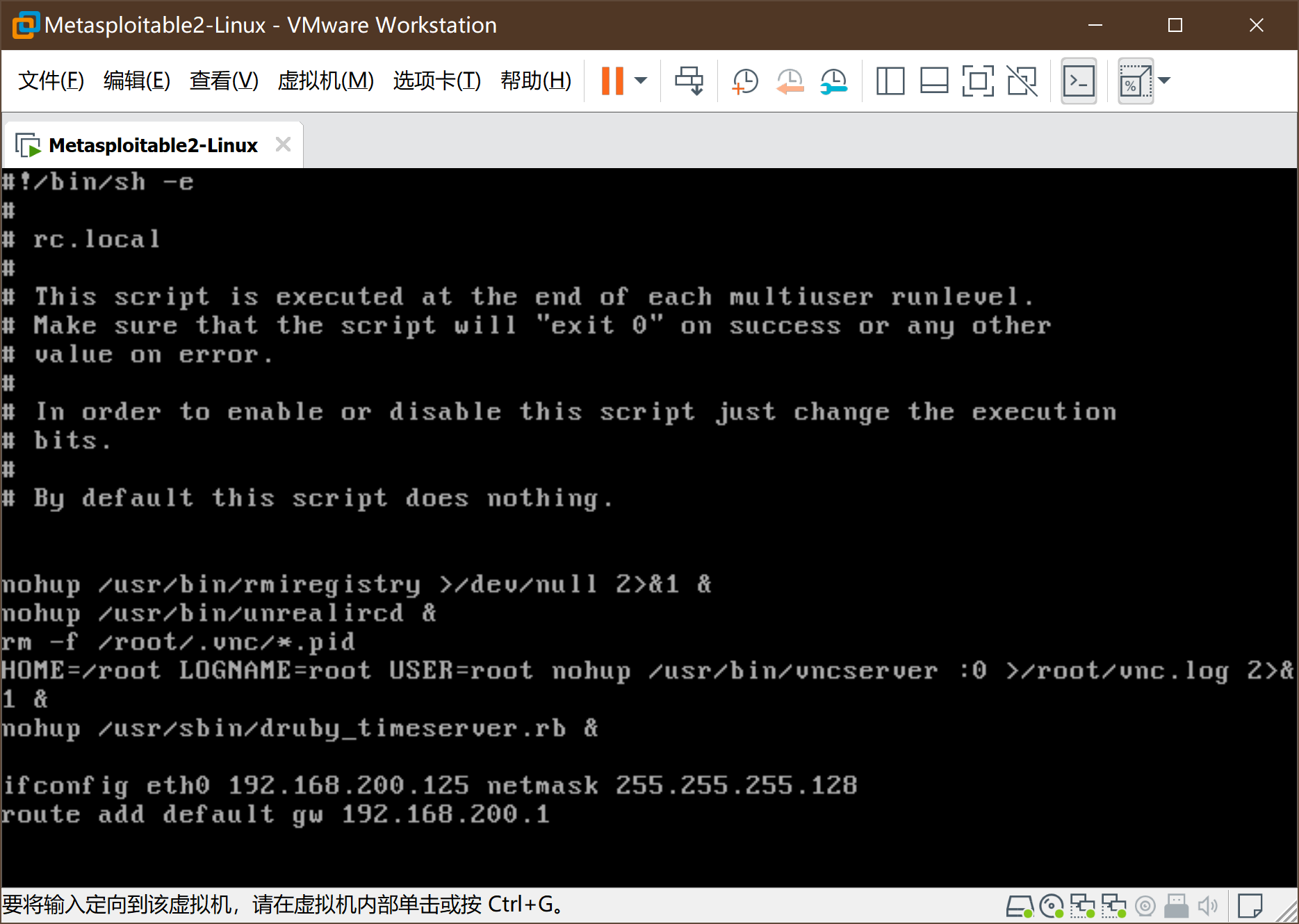
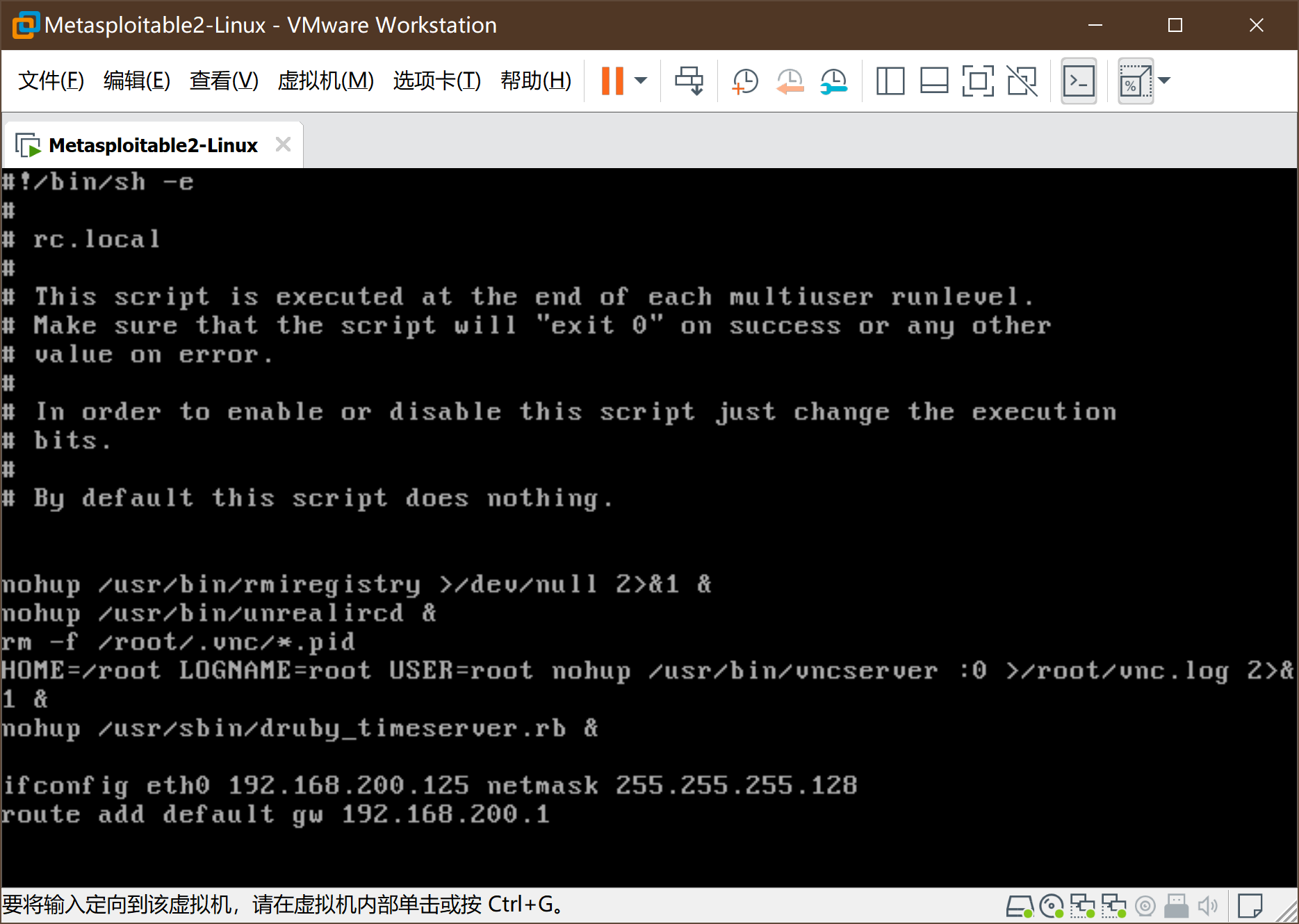
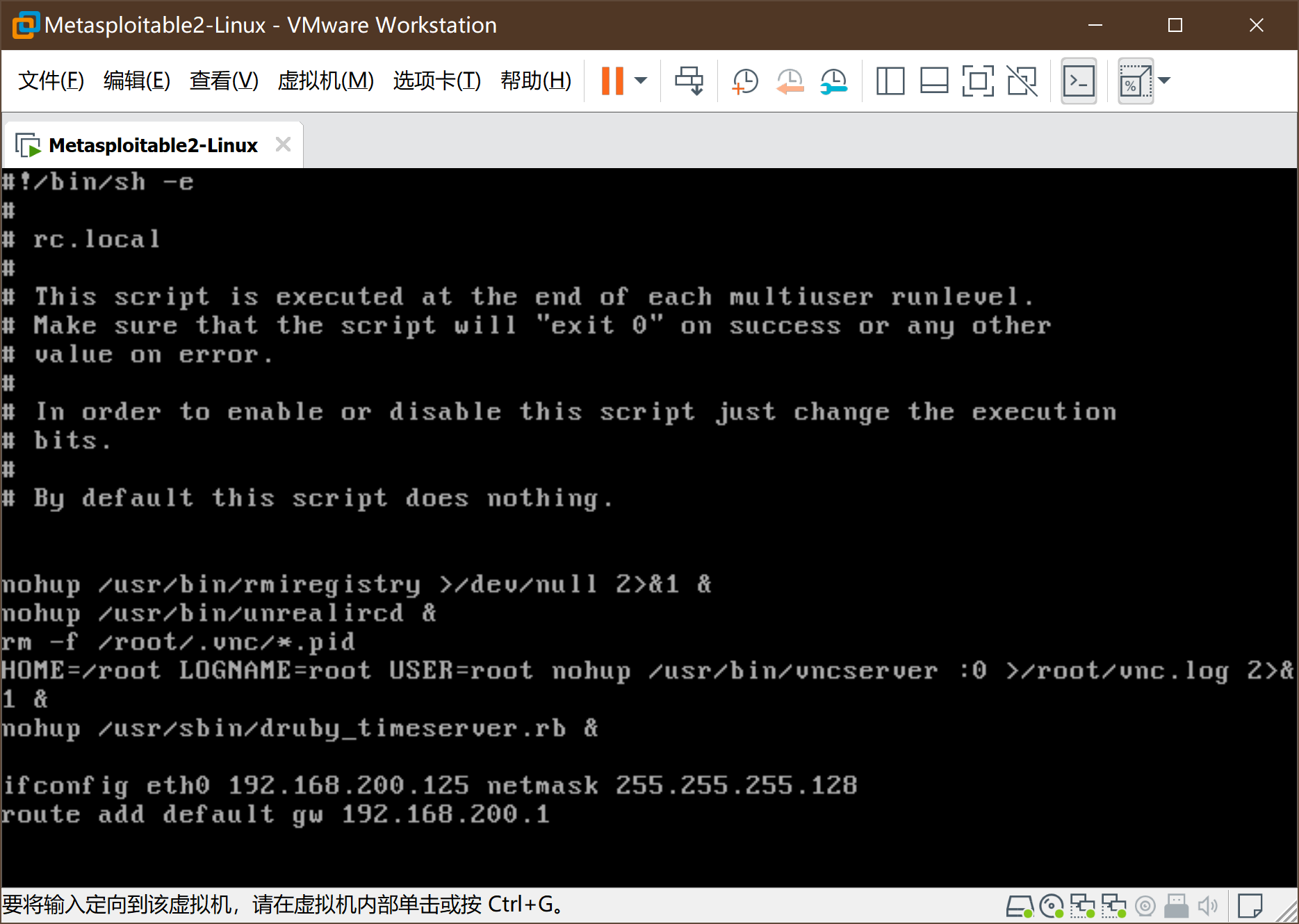
- 按i键进入编辑模式,在文件倒数第二行exit0之前, 插入以下两句
ifconfig eth0 192.168.200.125 netmask 255.255.255.128
route add default gw 192.168.200.1
-
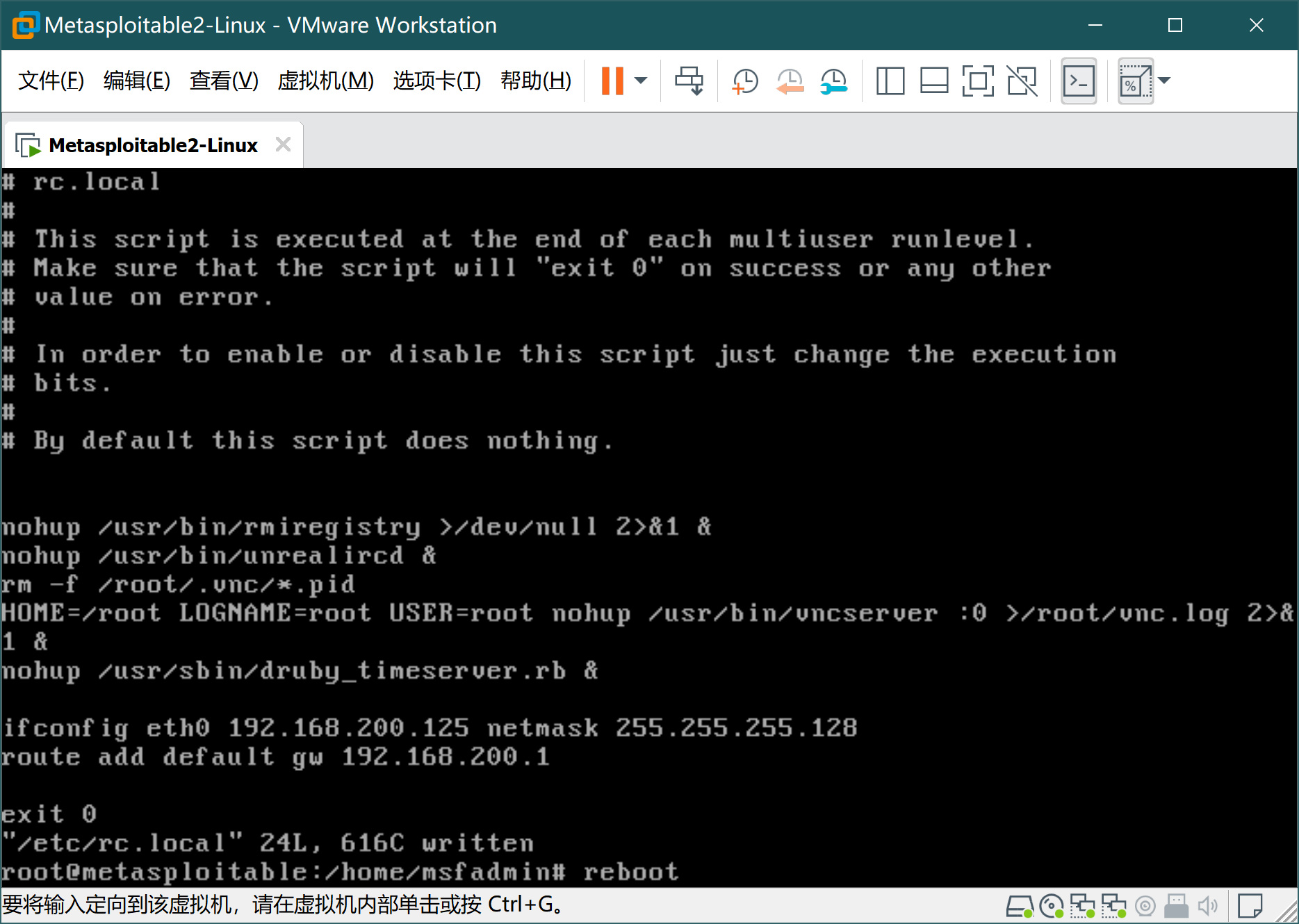
按ESC键,再用 :wq 后回车。之后reboot重启:
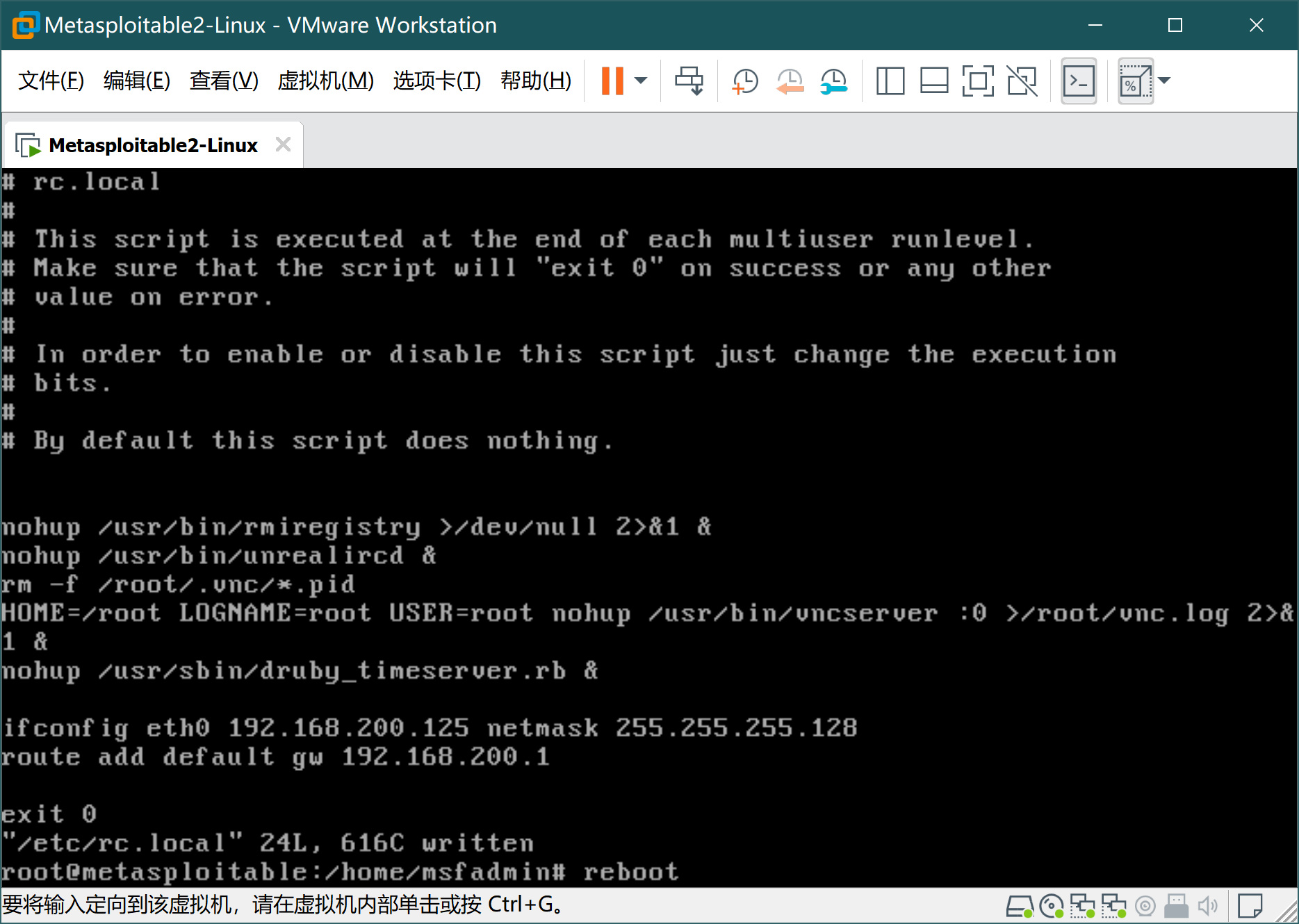
-
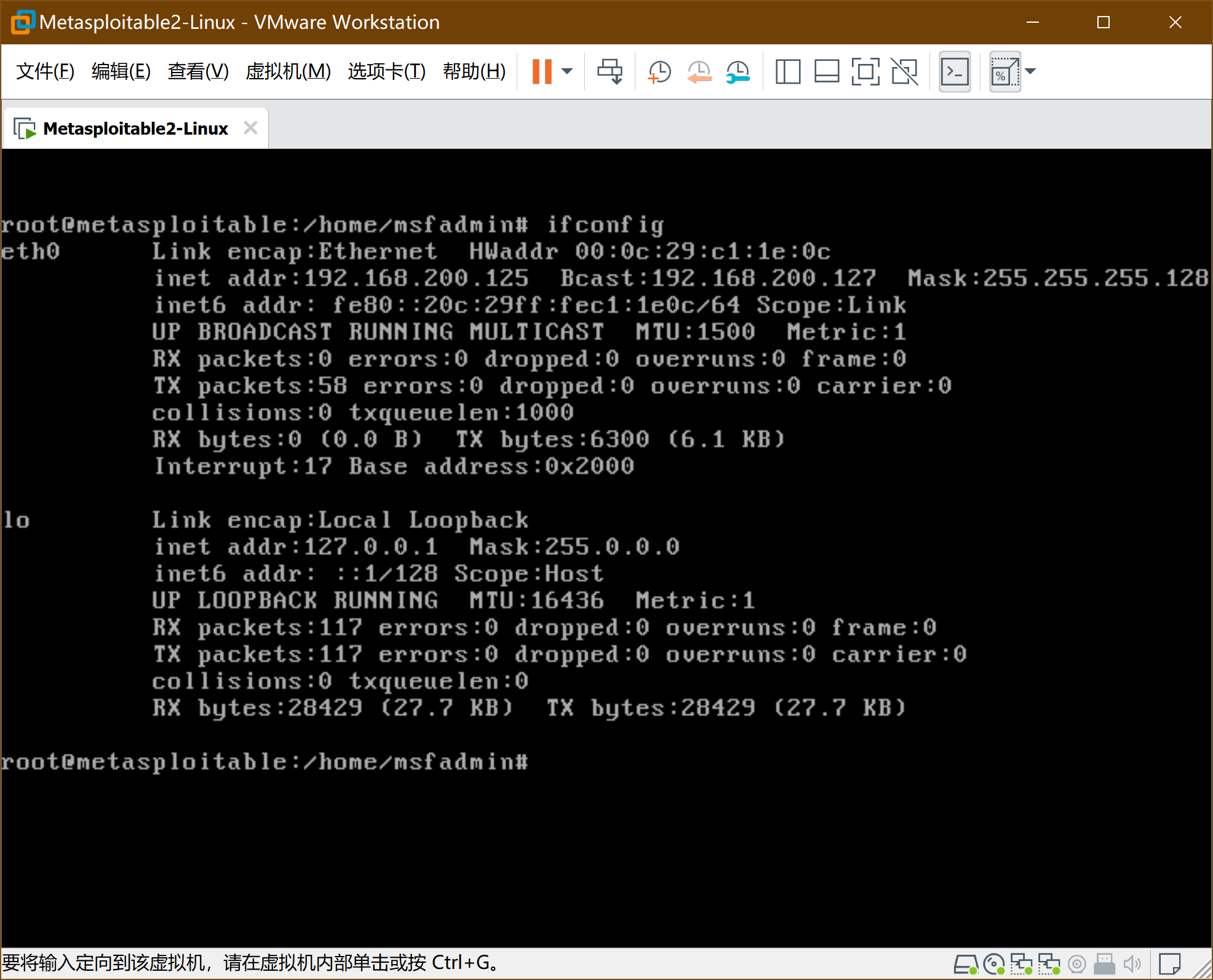
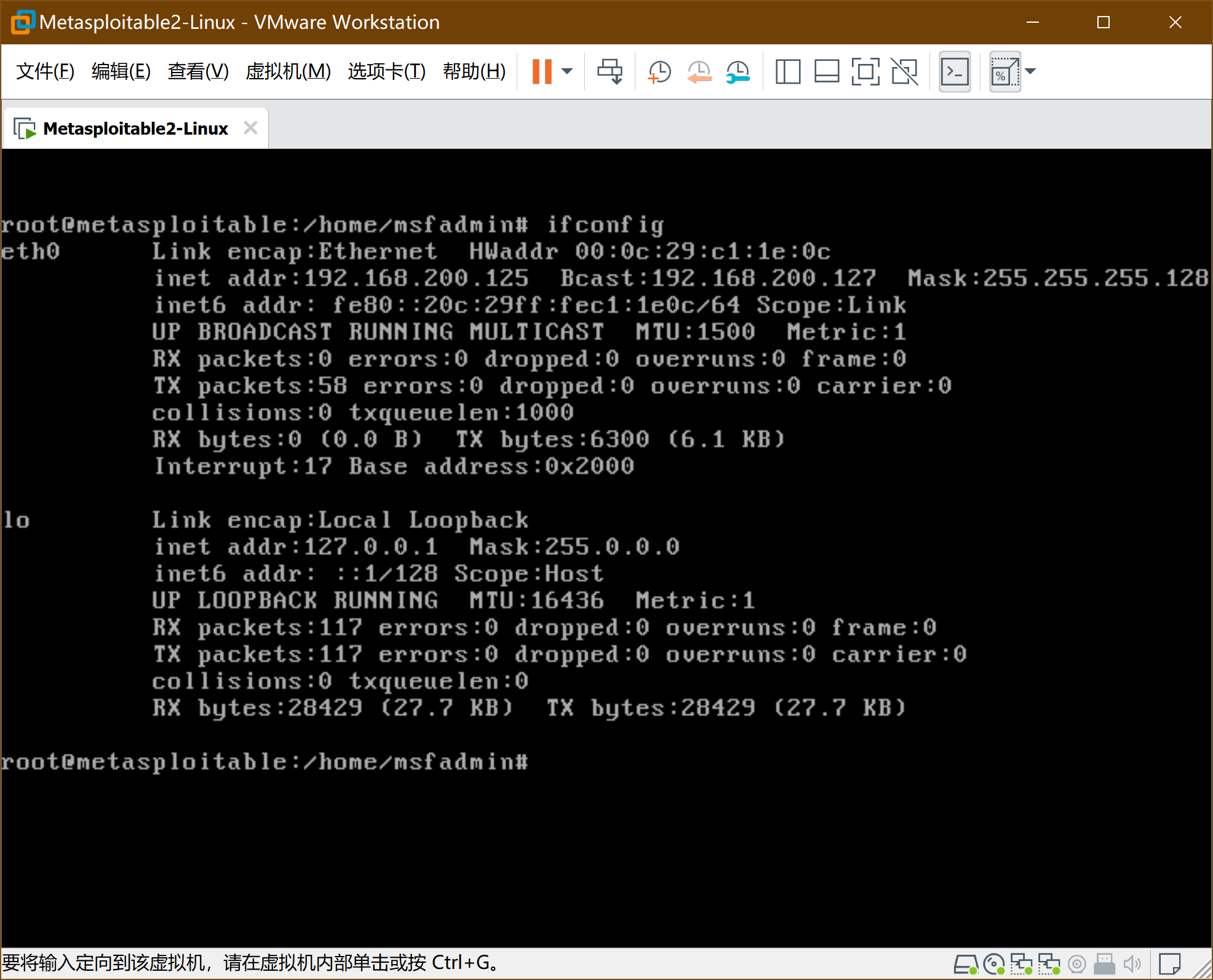
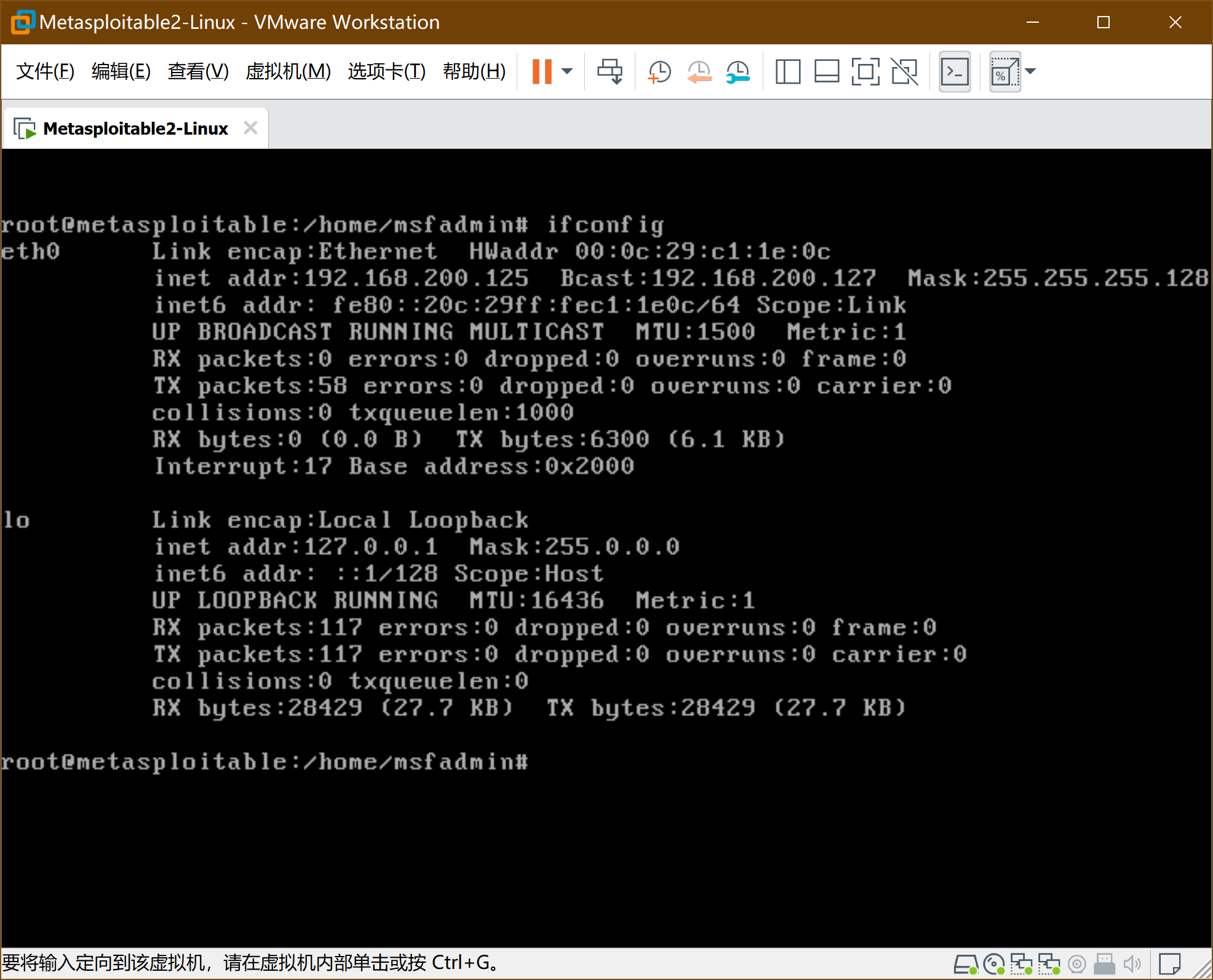
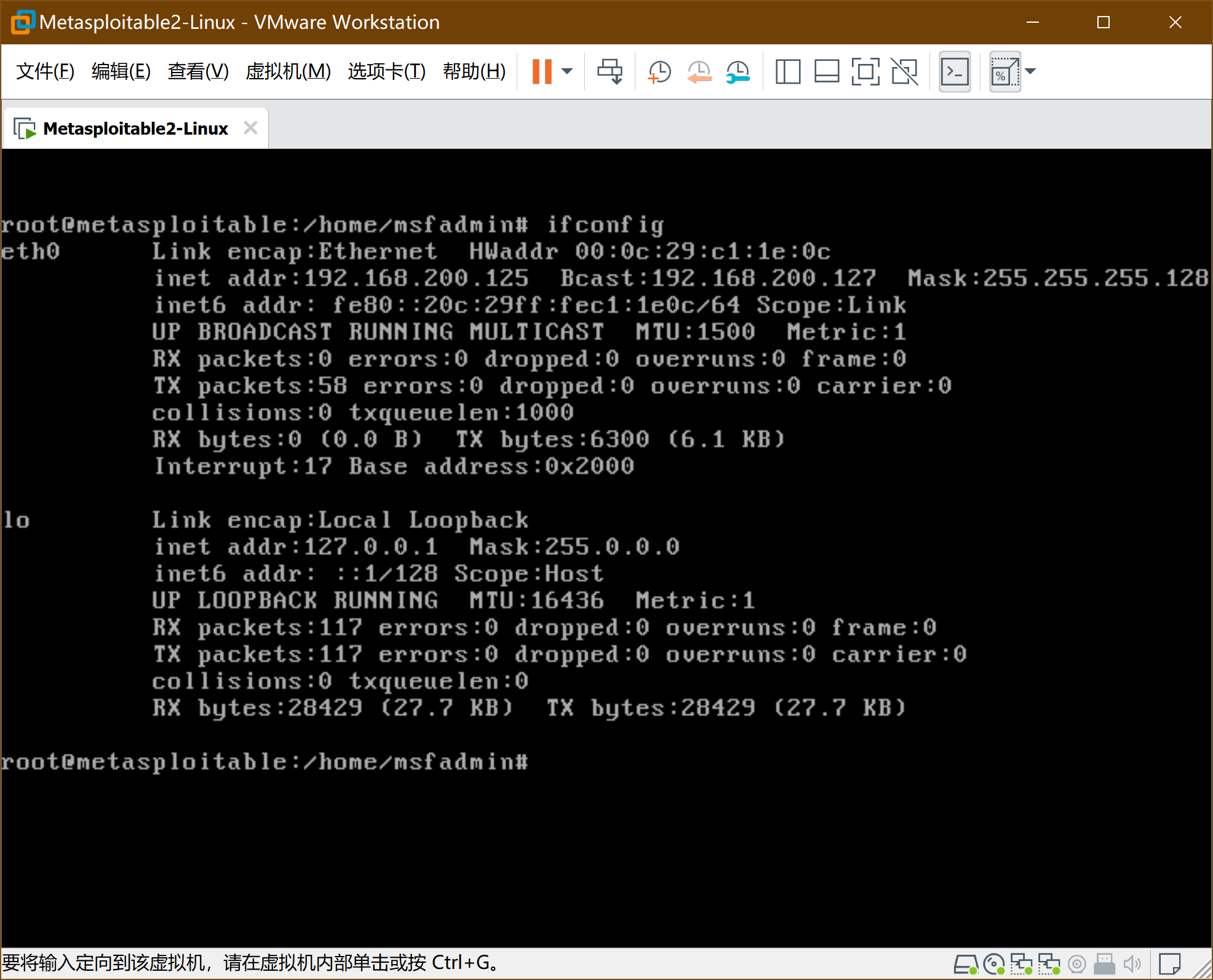
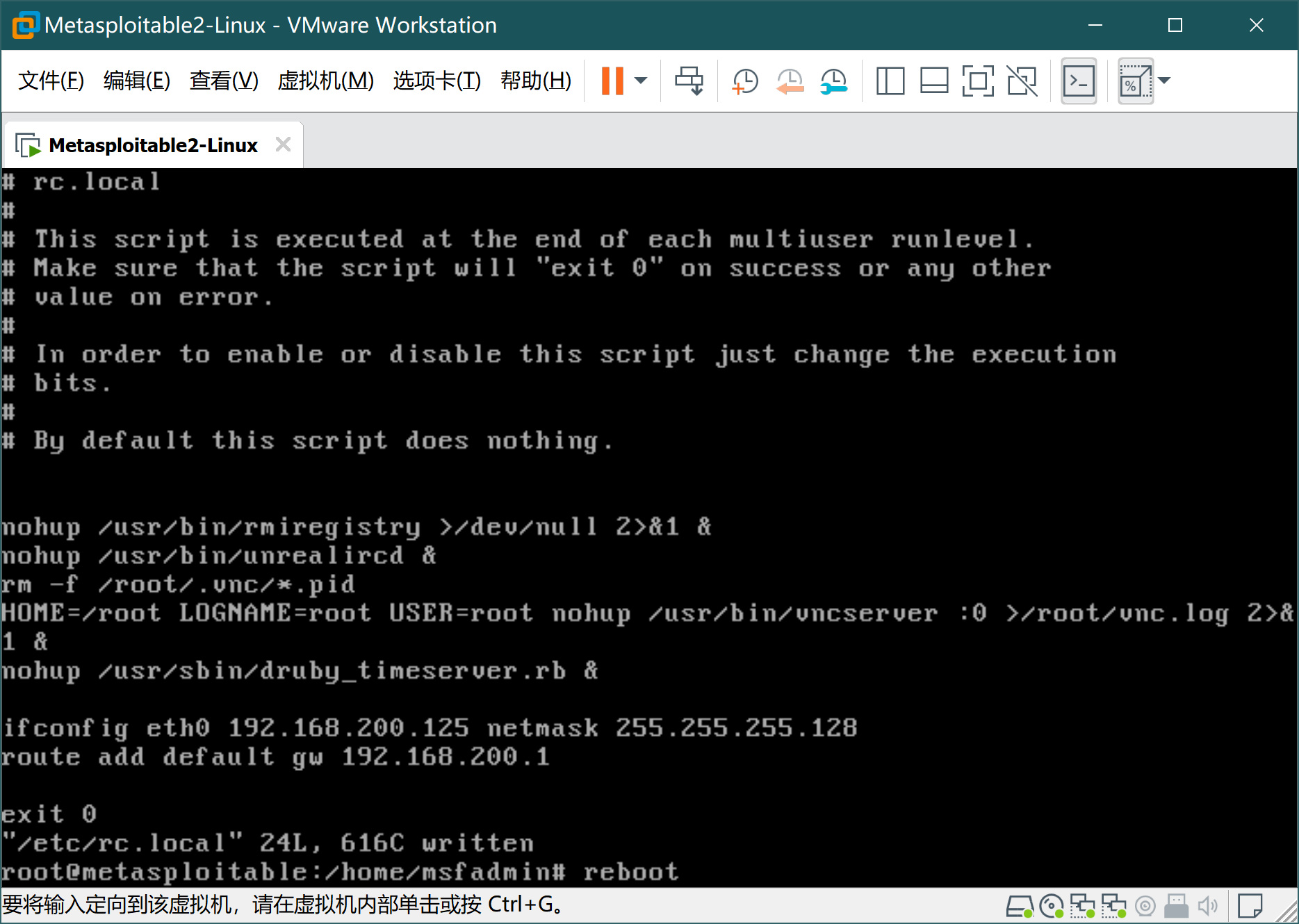
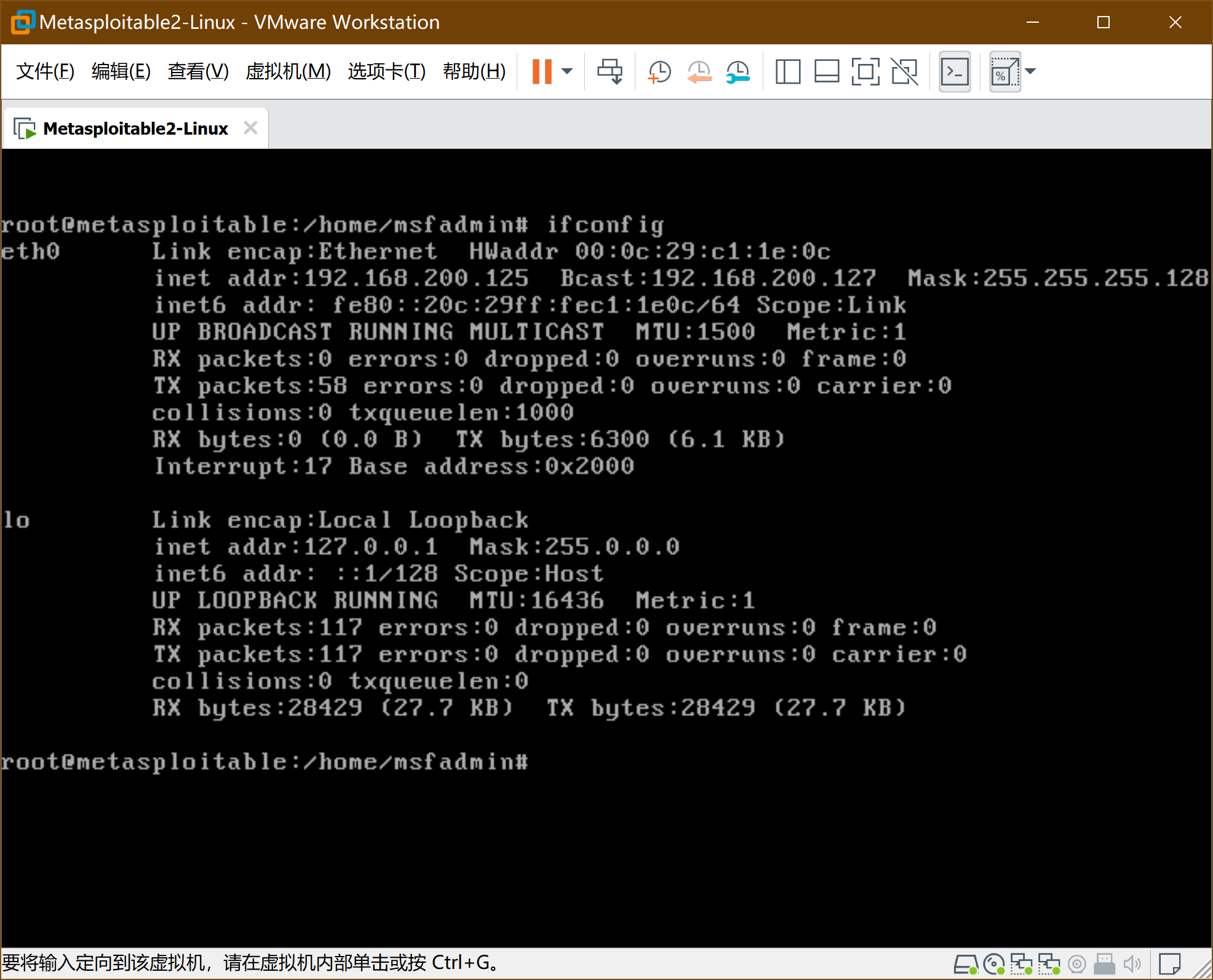
通过ifconfig查看结果
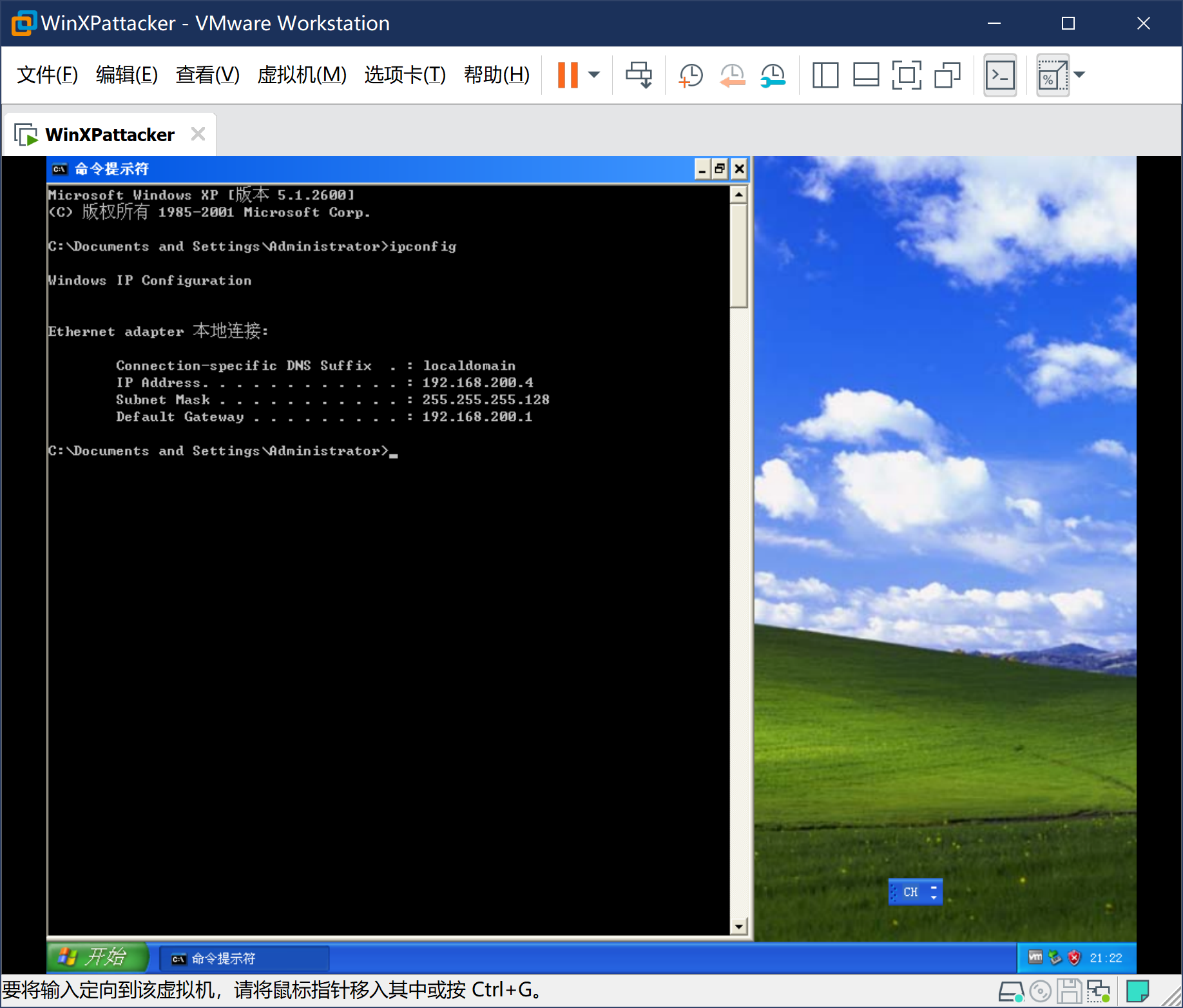
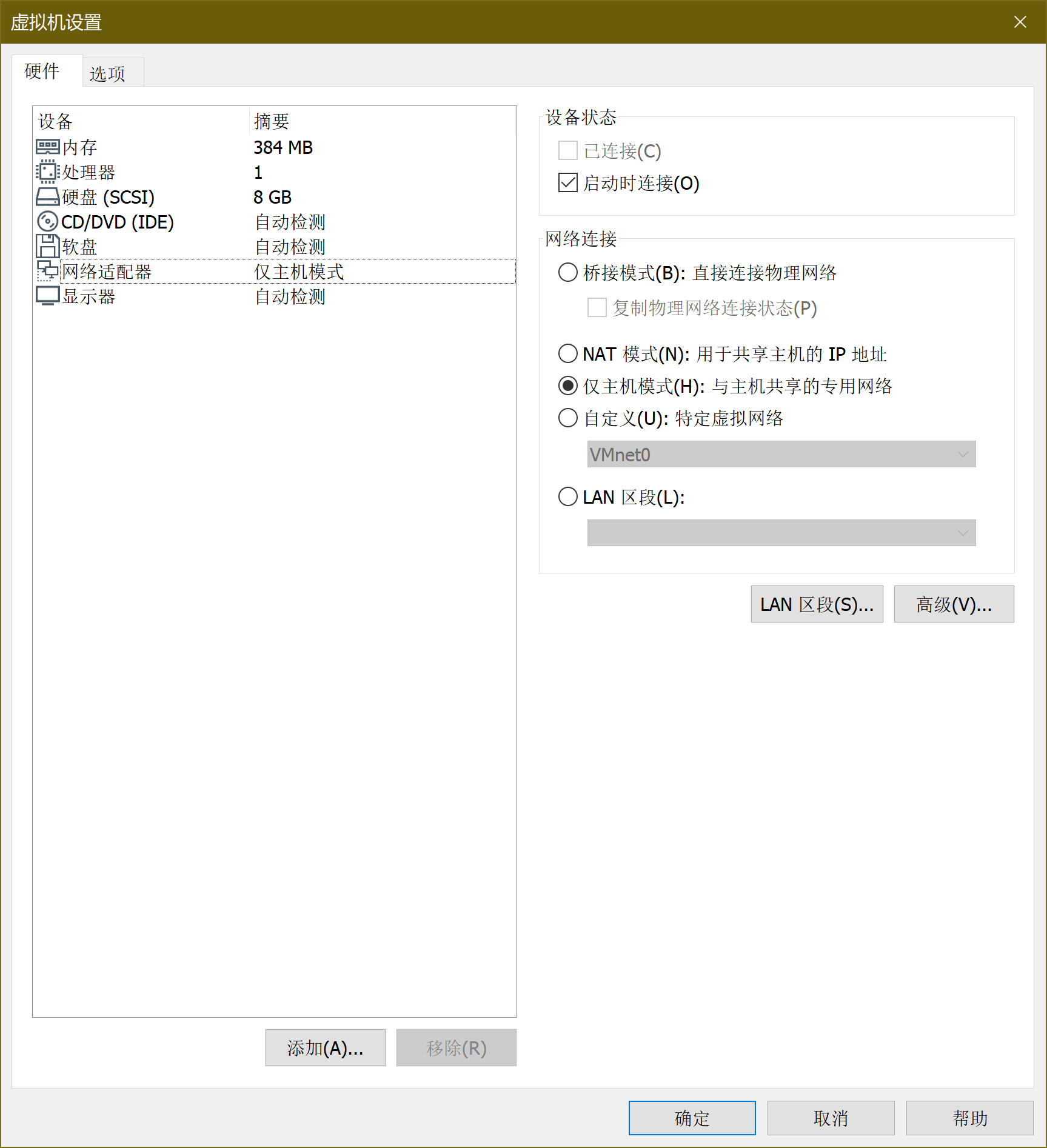
5、安装windows攻击机-windows Attacker
-
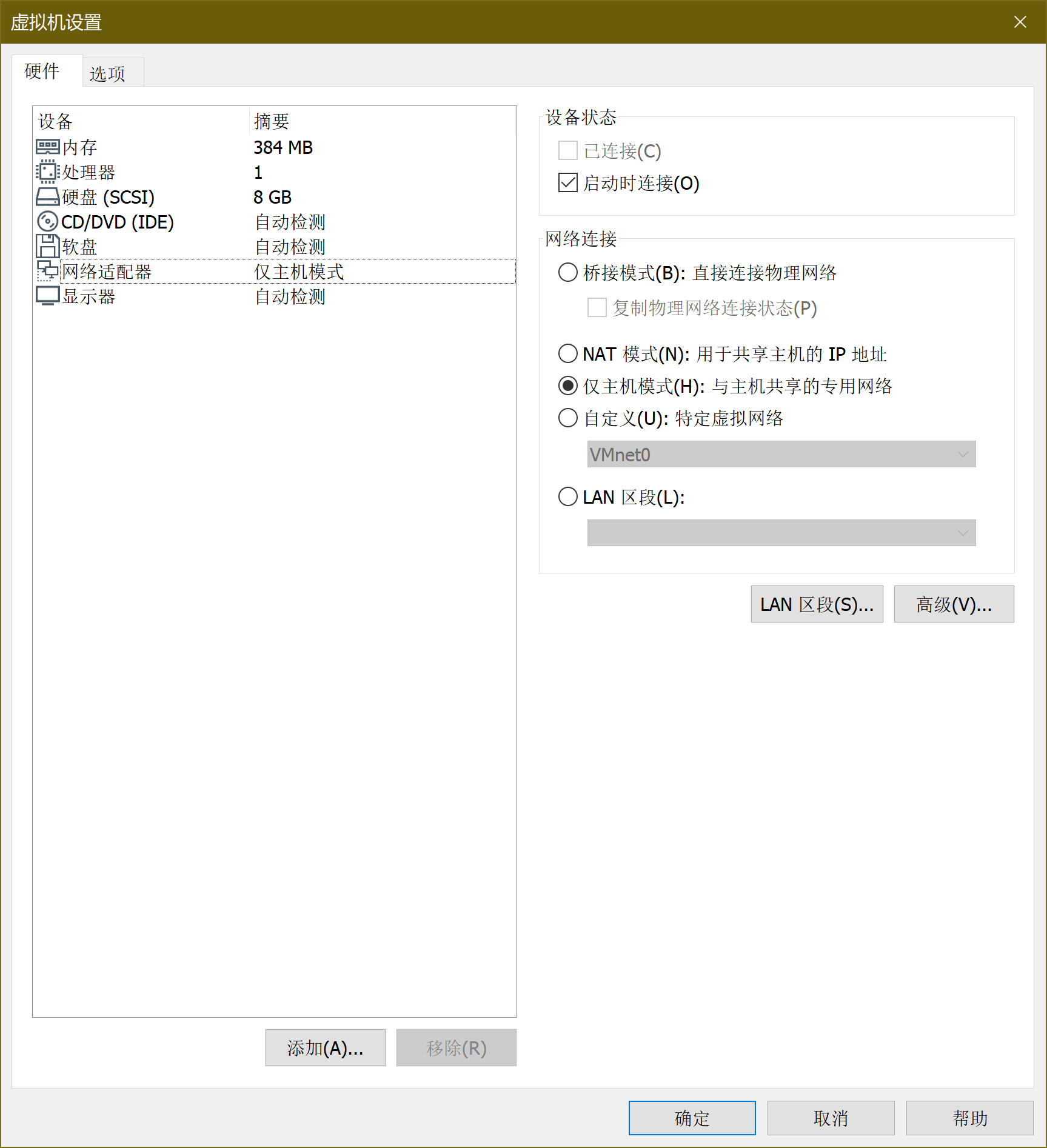
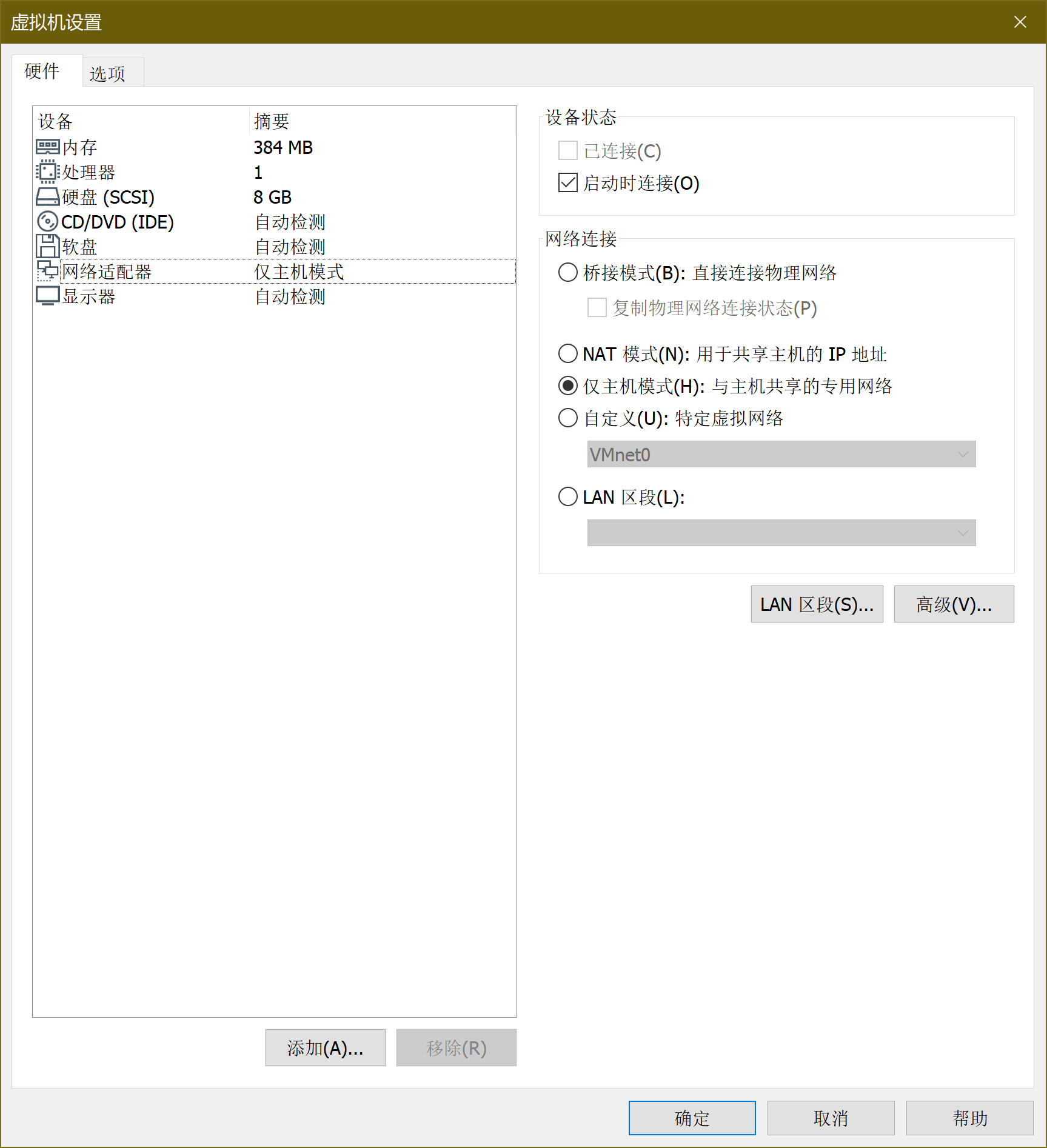
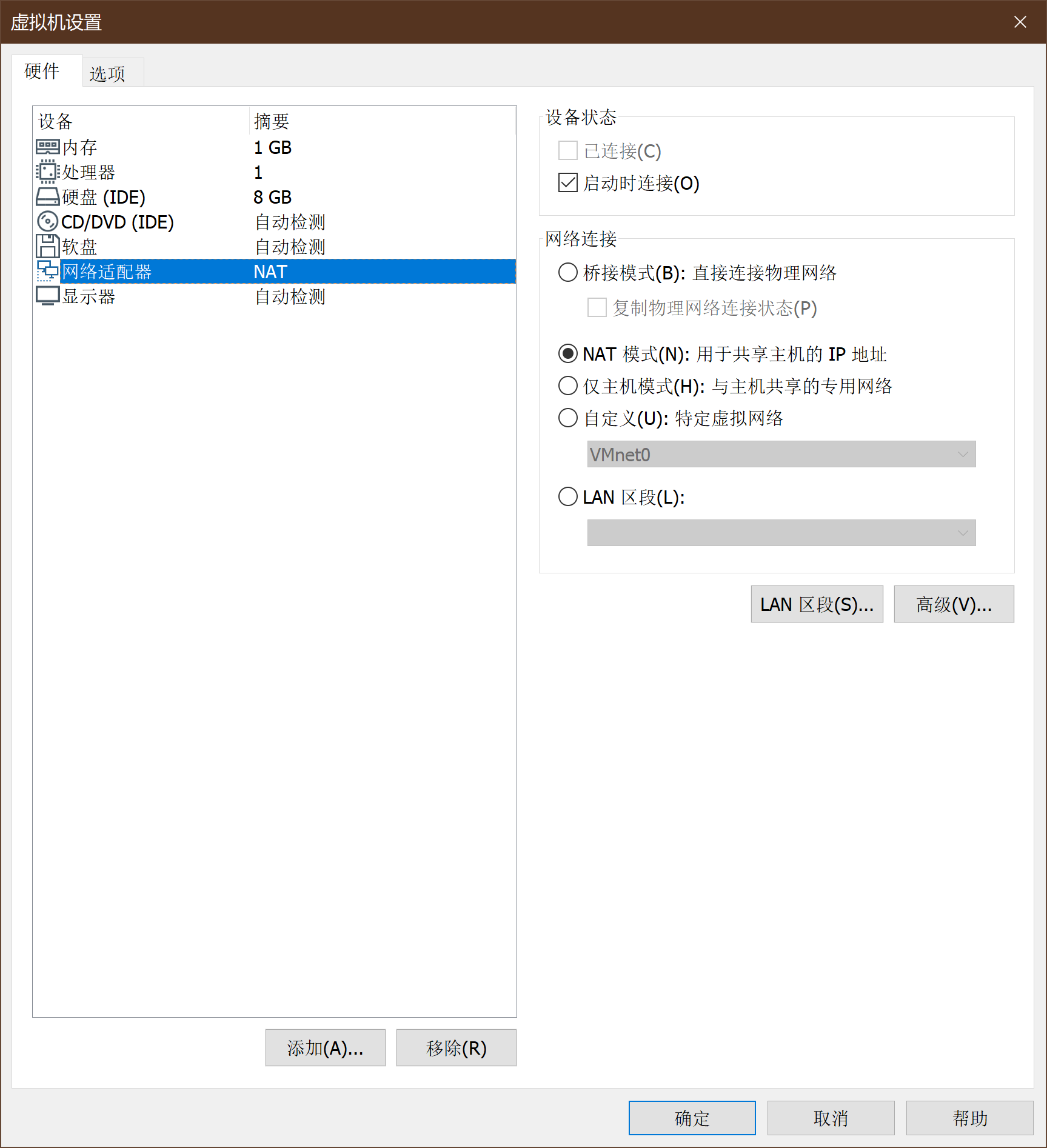
WinXPattacker通过VM虚拟机镜像给定,导入方式与Kali相同。WinXPattacker的网卡设置如下:
-
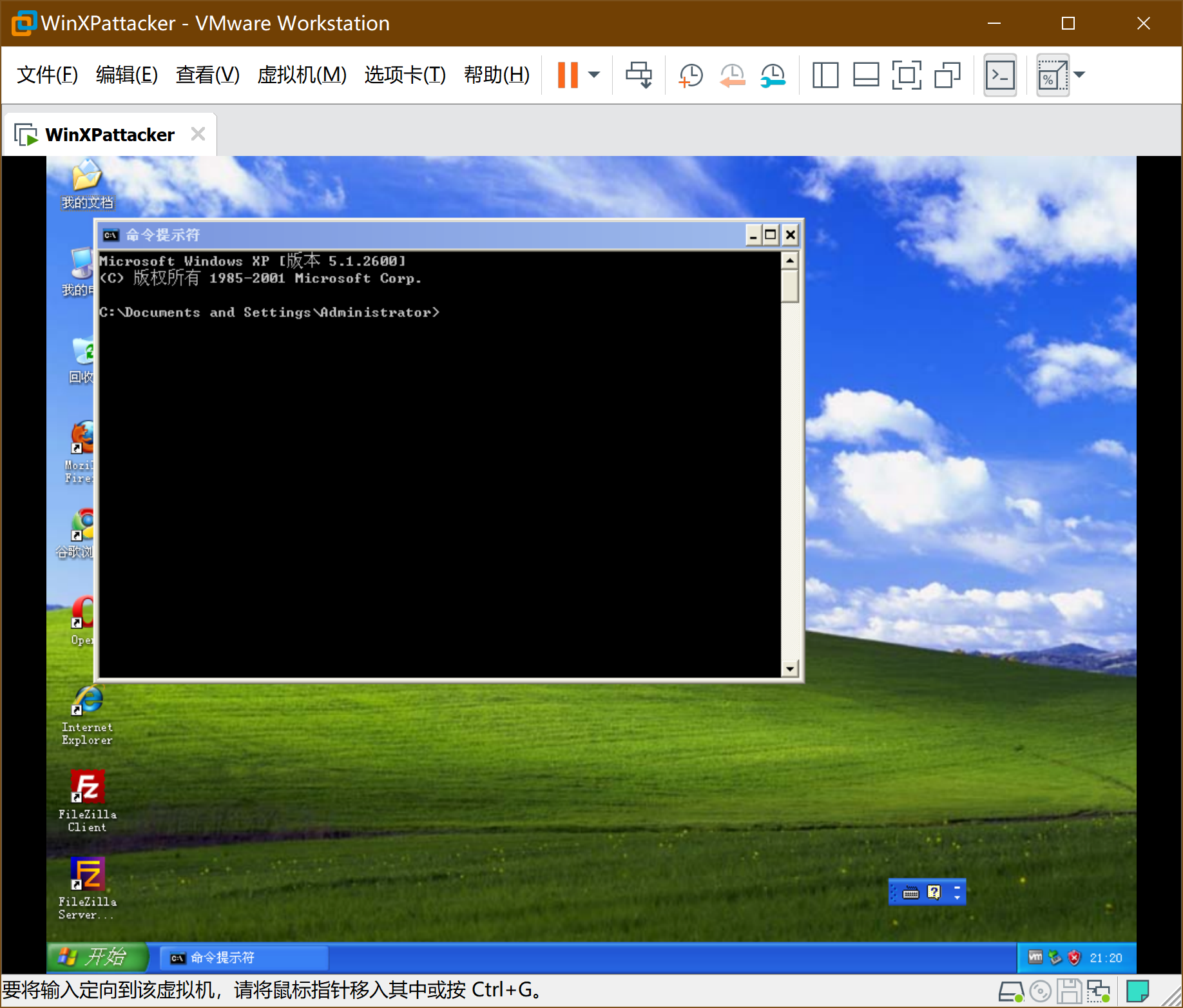
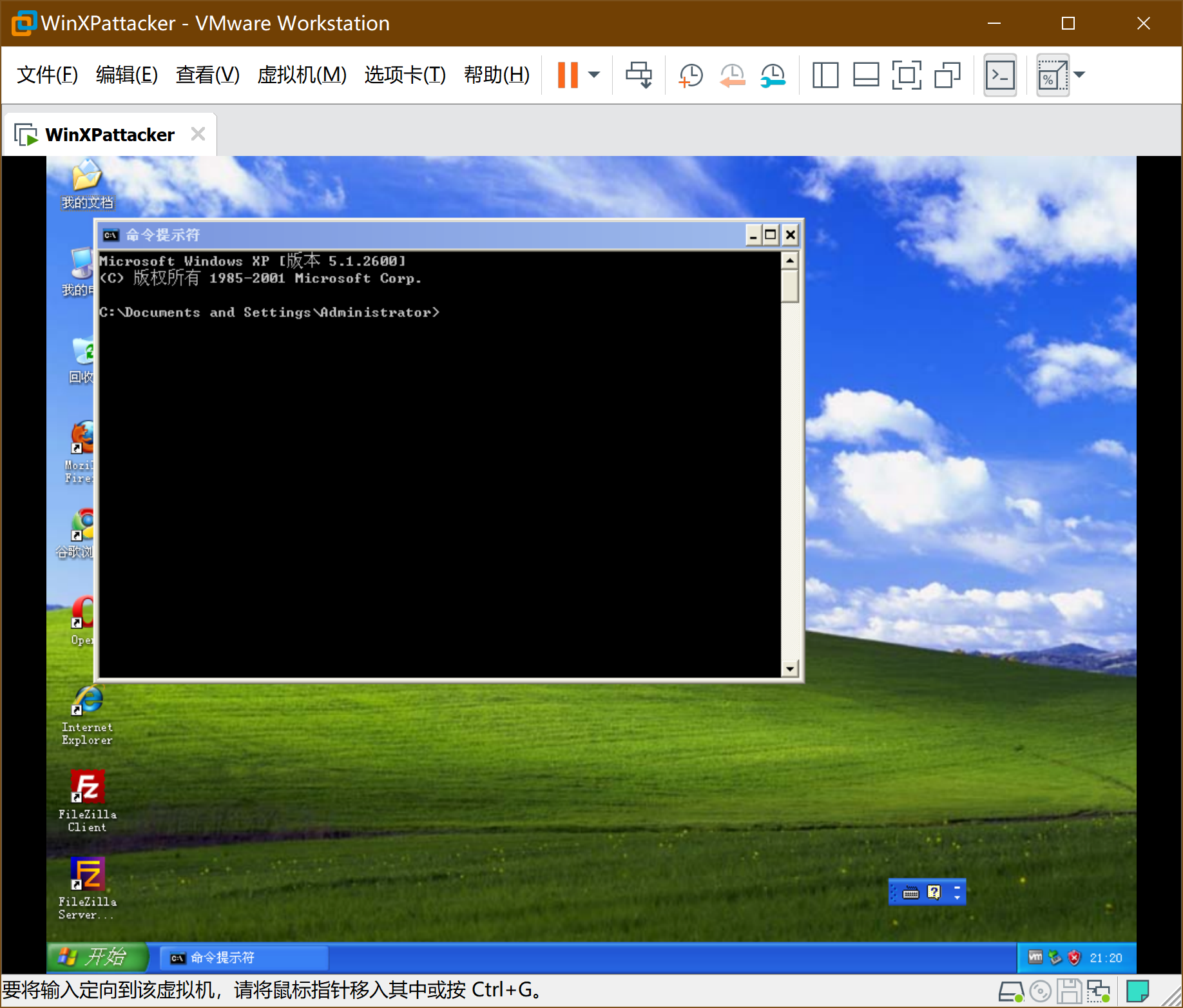
进入系统 密码mima1234
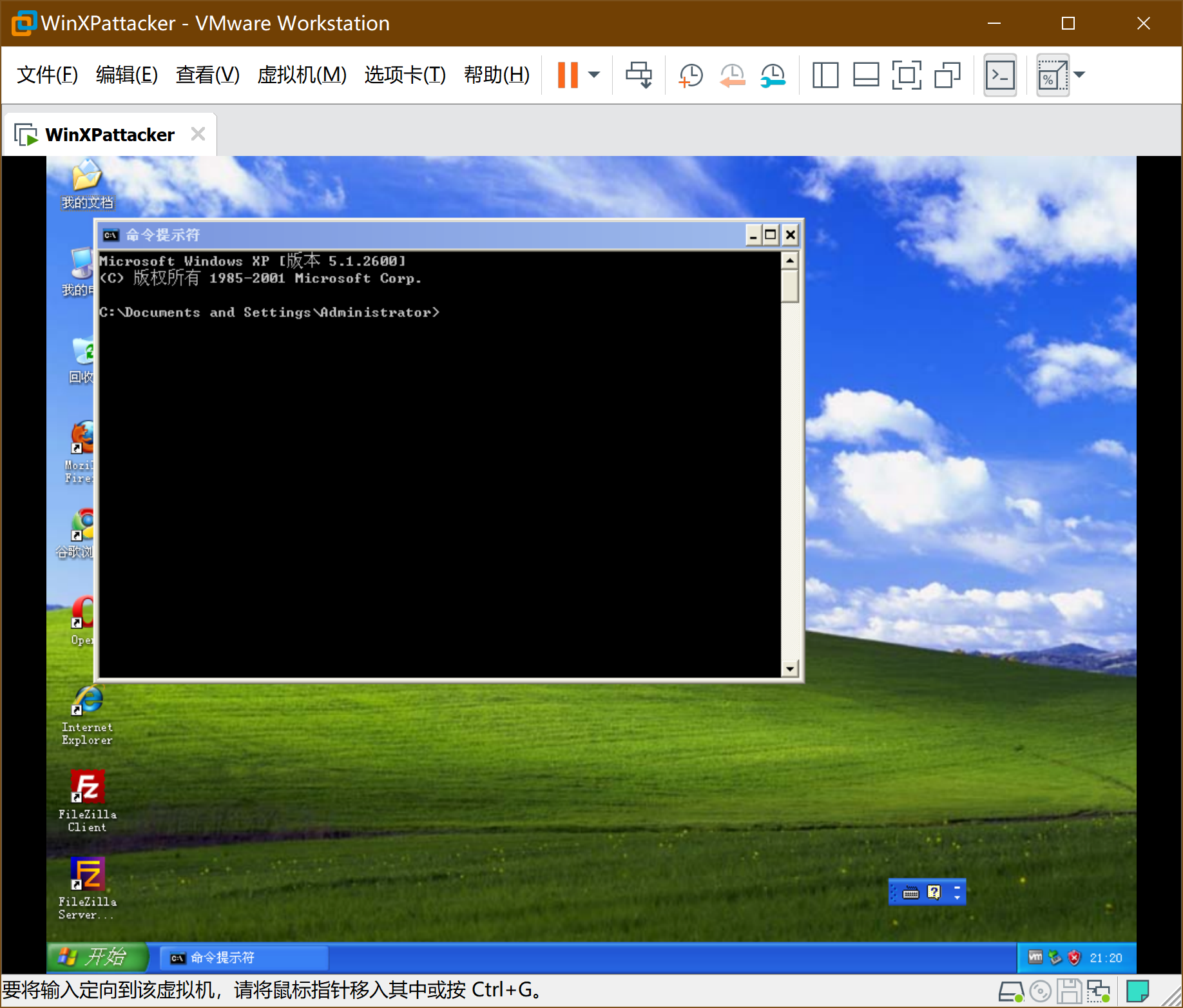
-
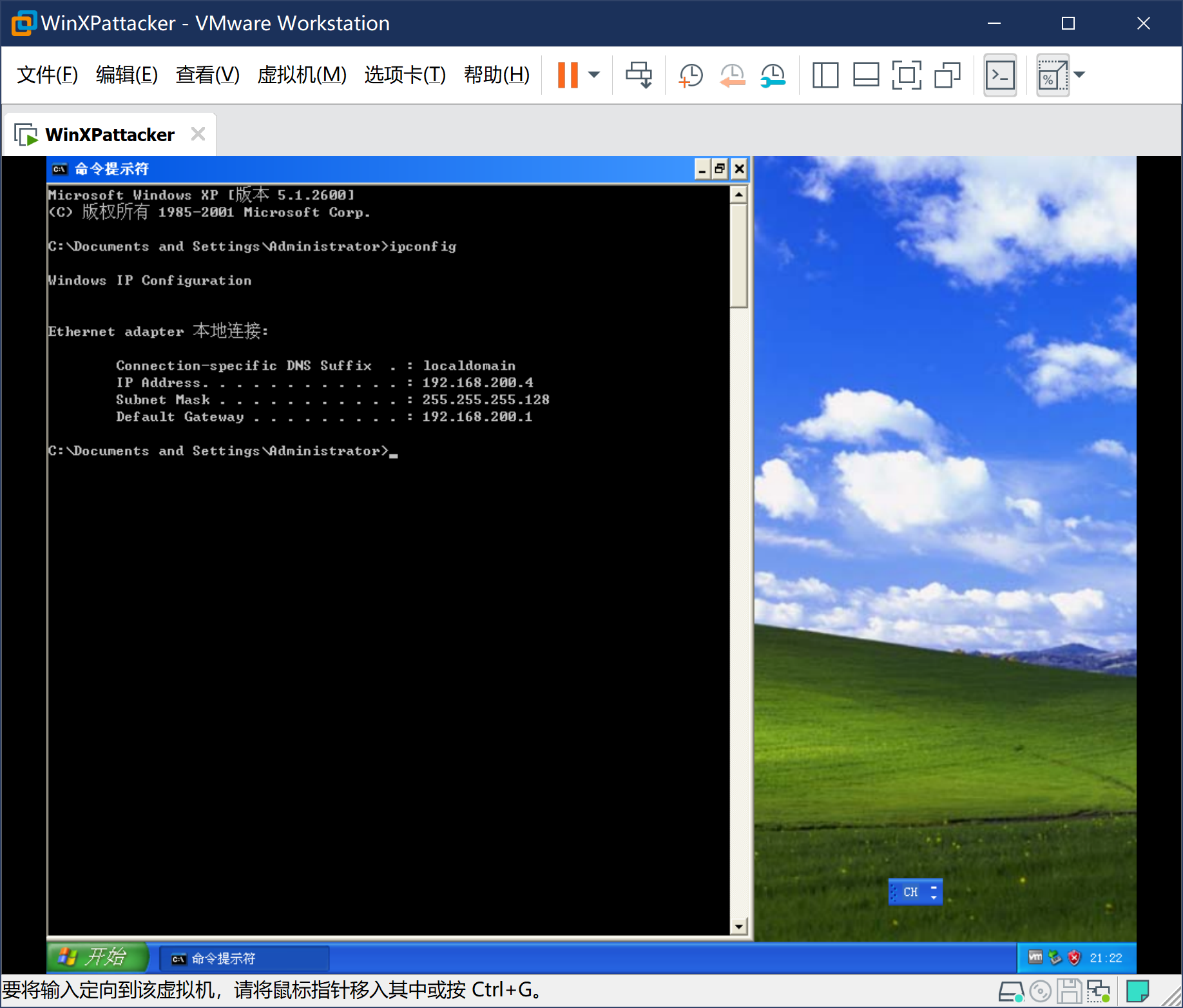
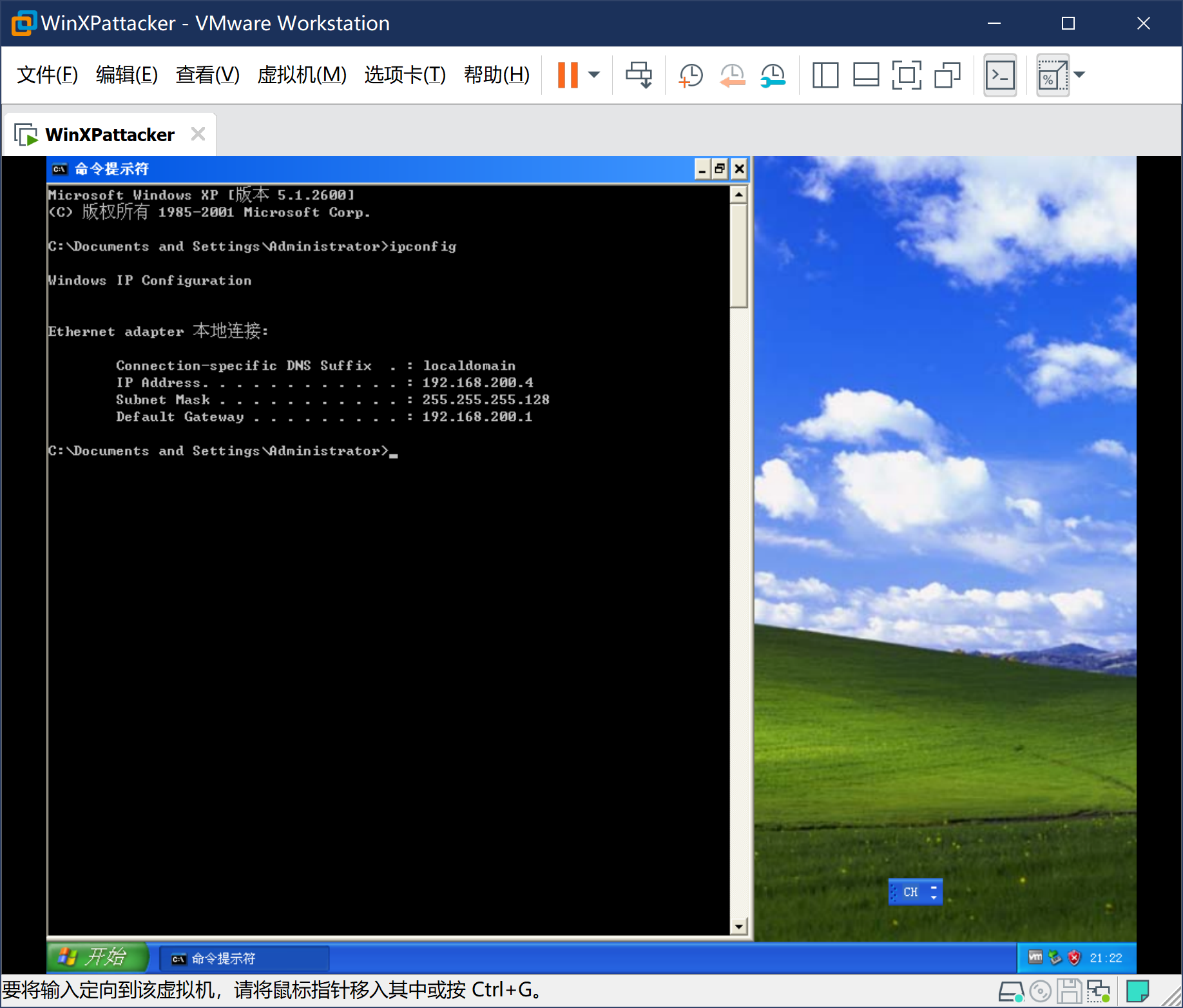
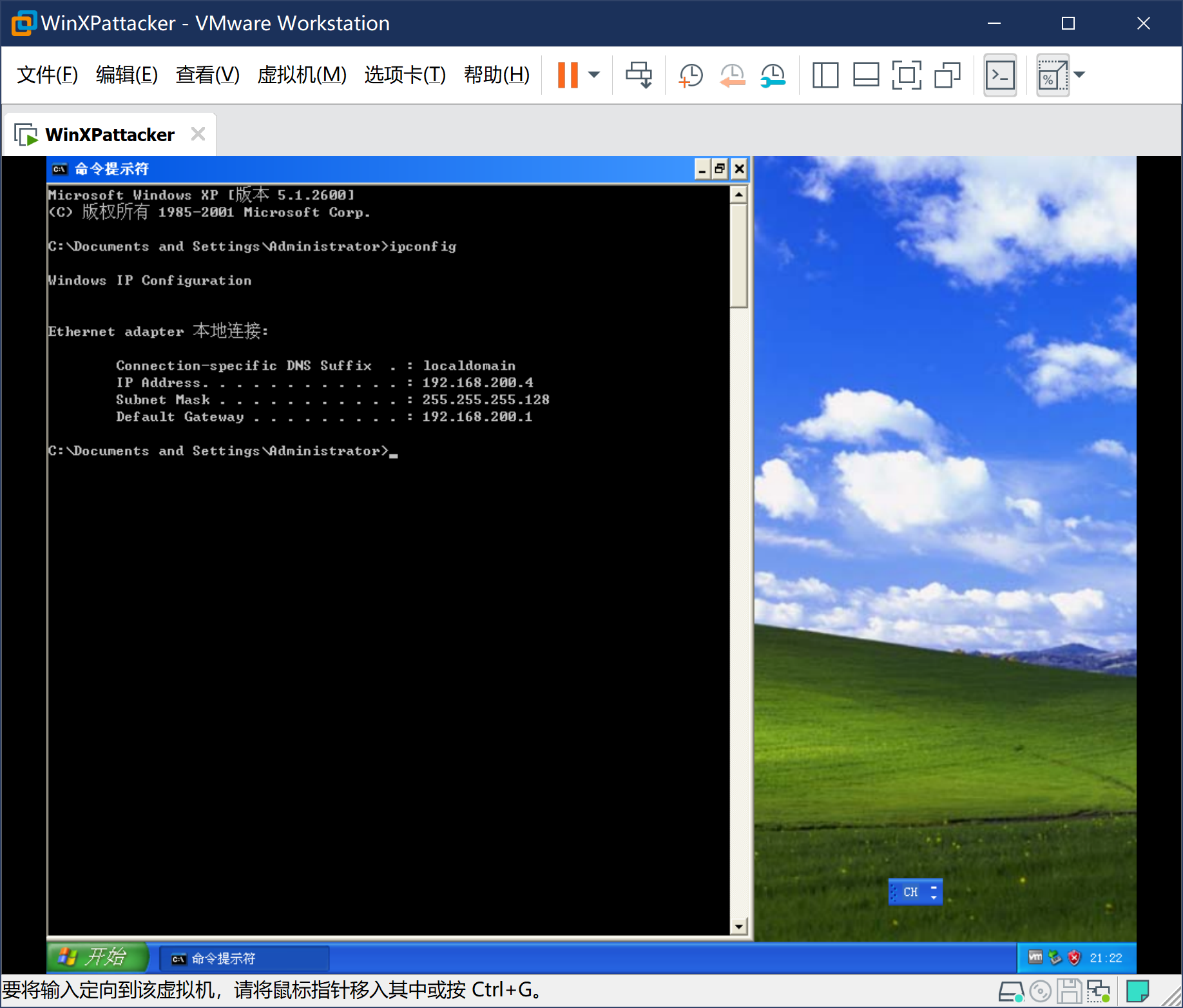
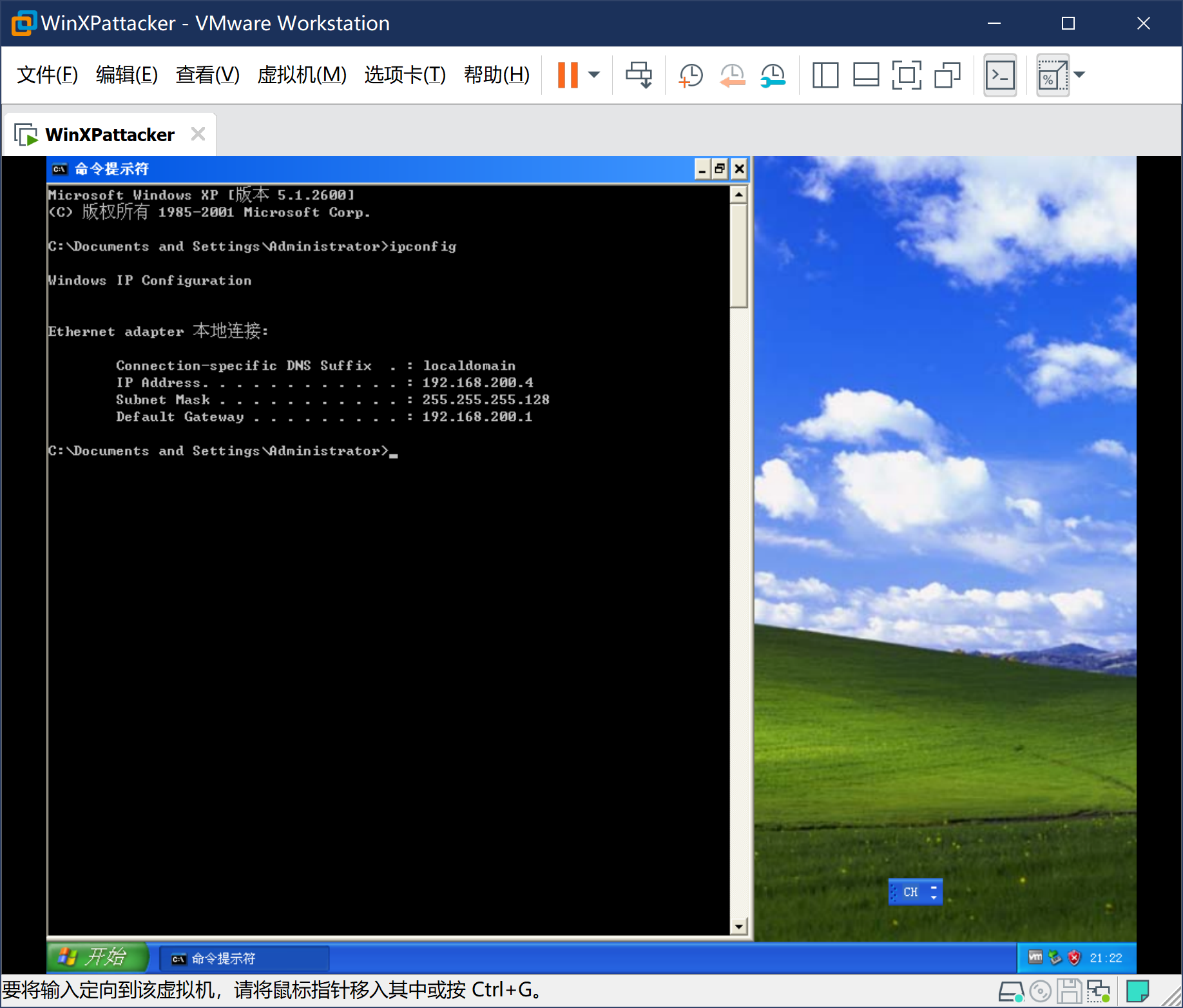
此时系统已经通过DHCP获得IP地址,不需要手动配置,但需要找到具体IP。通过ipconfig获得windowsattacker的ip地址:
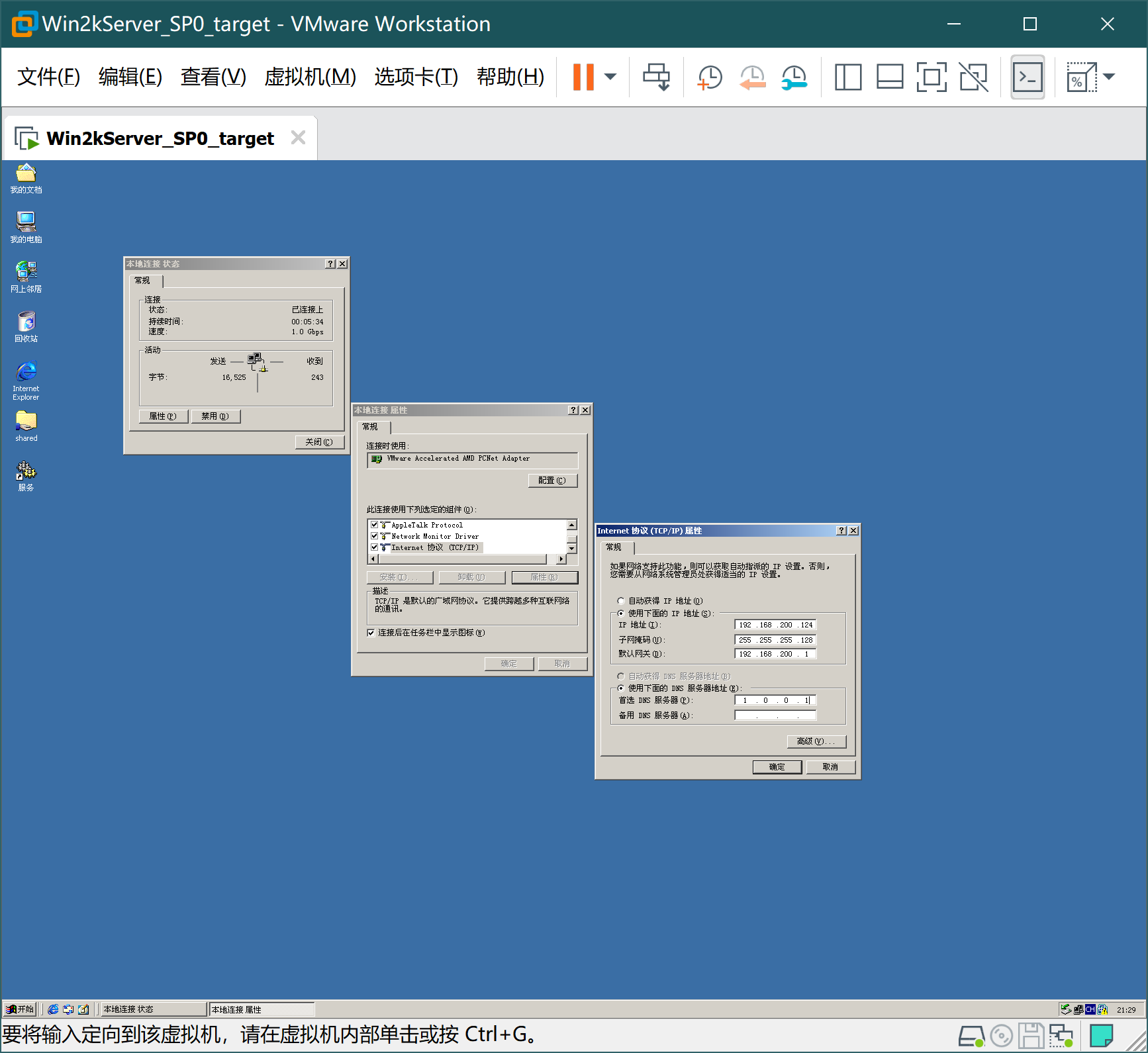
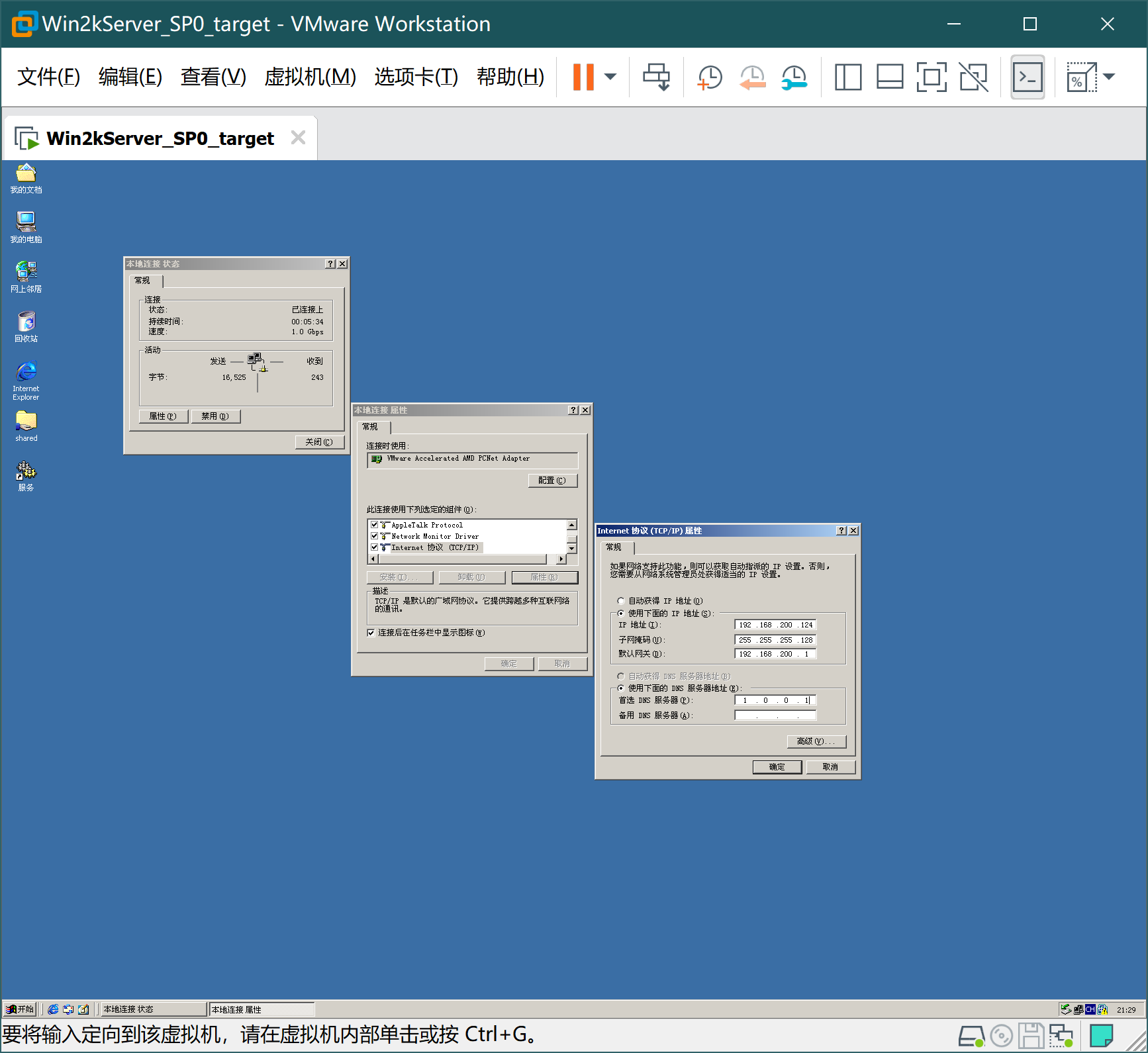
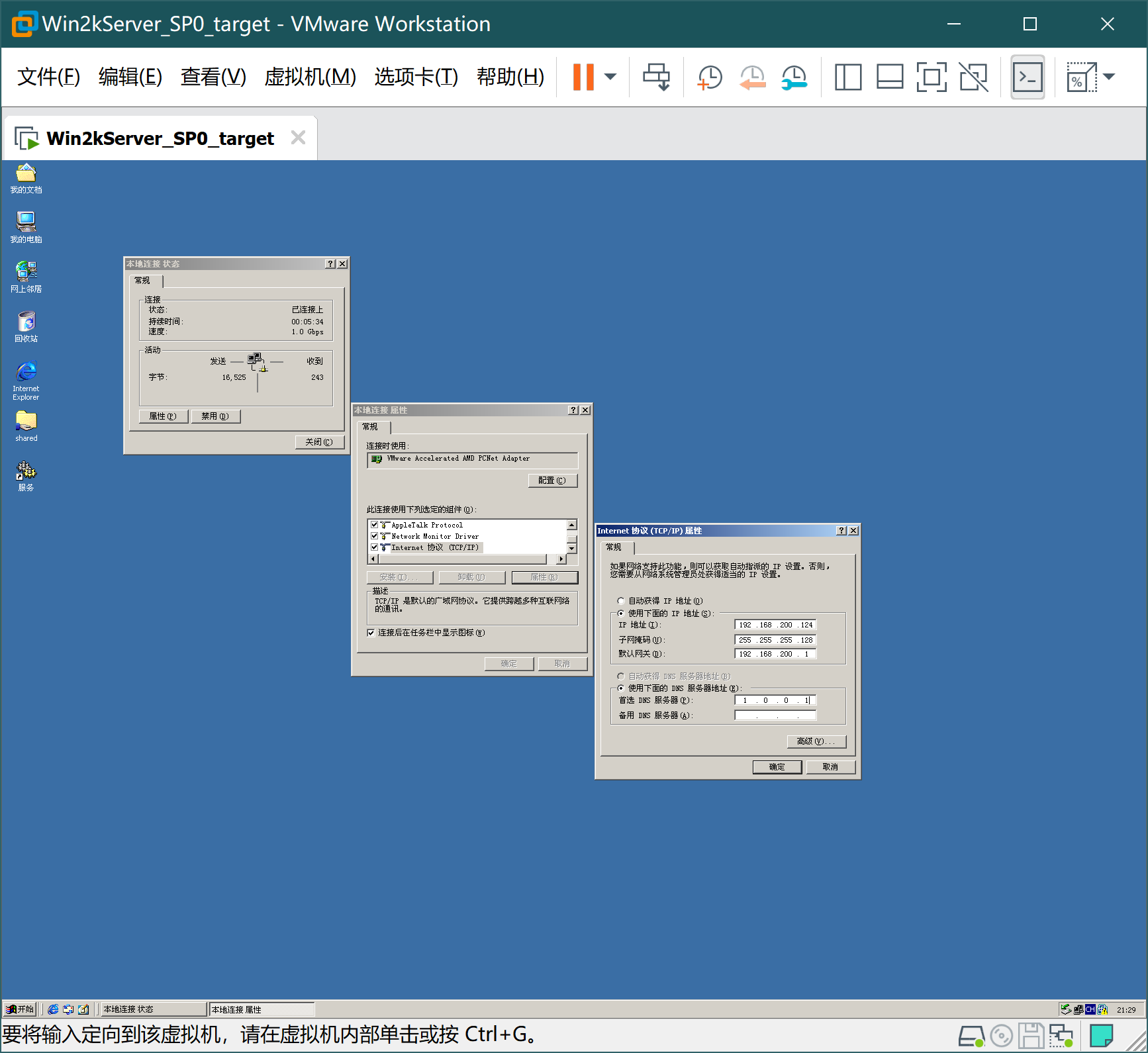
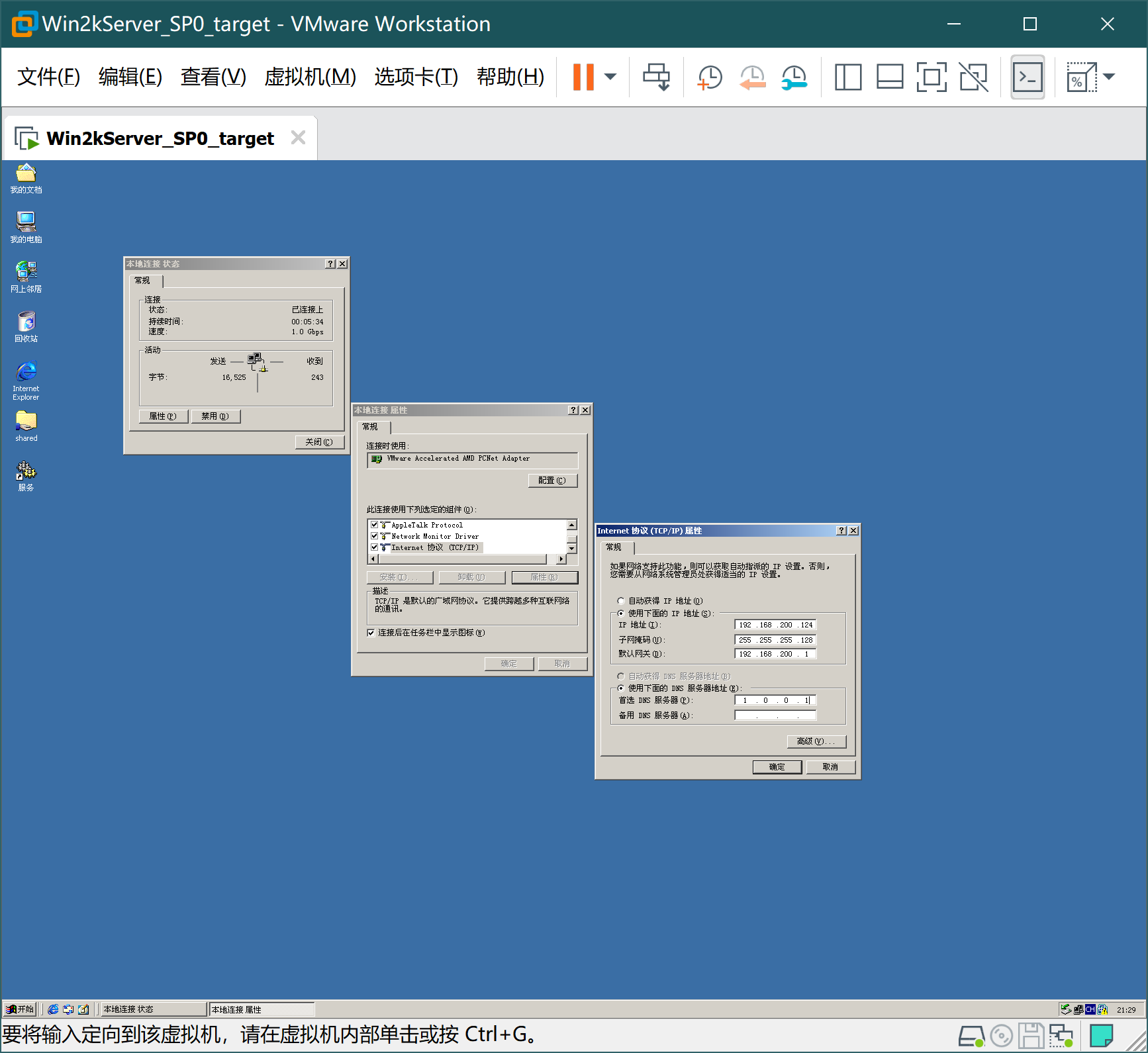
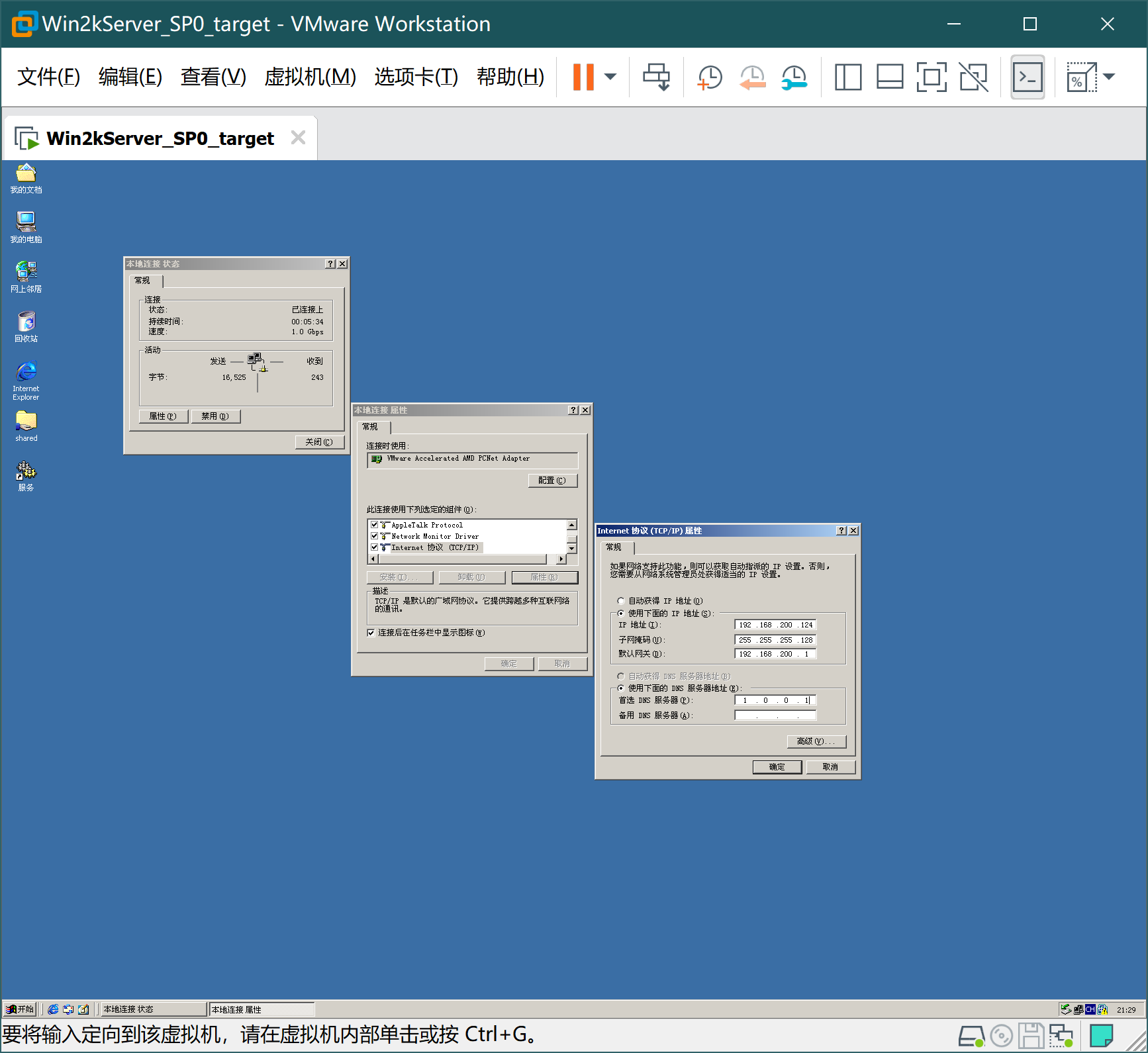
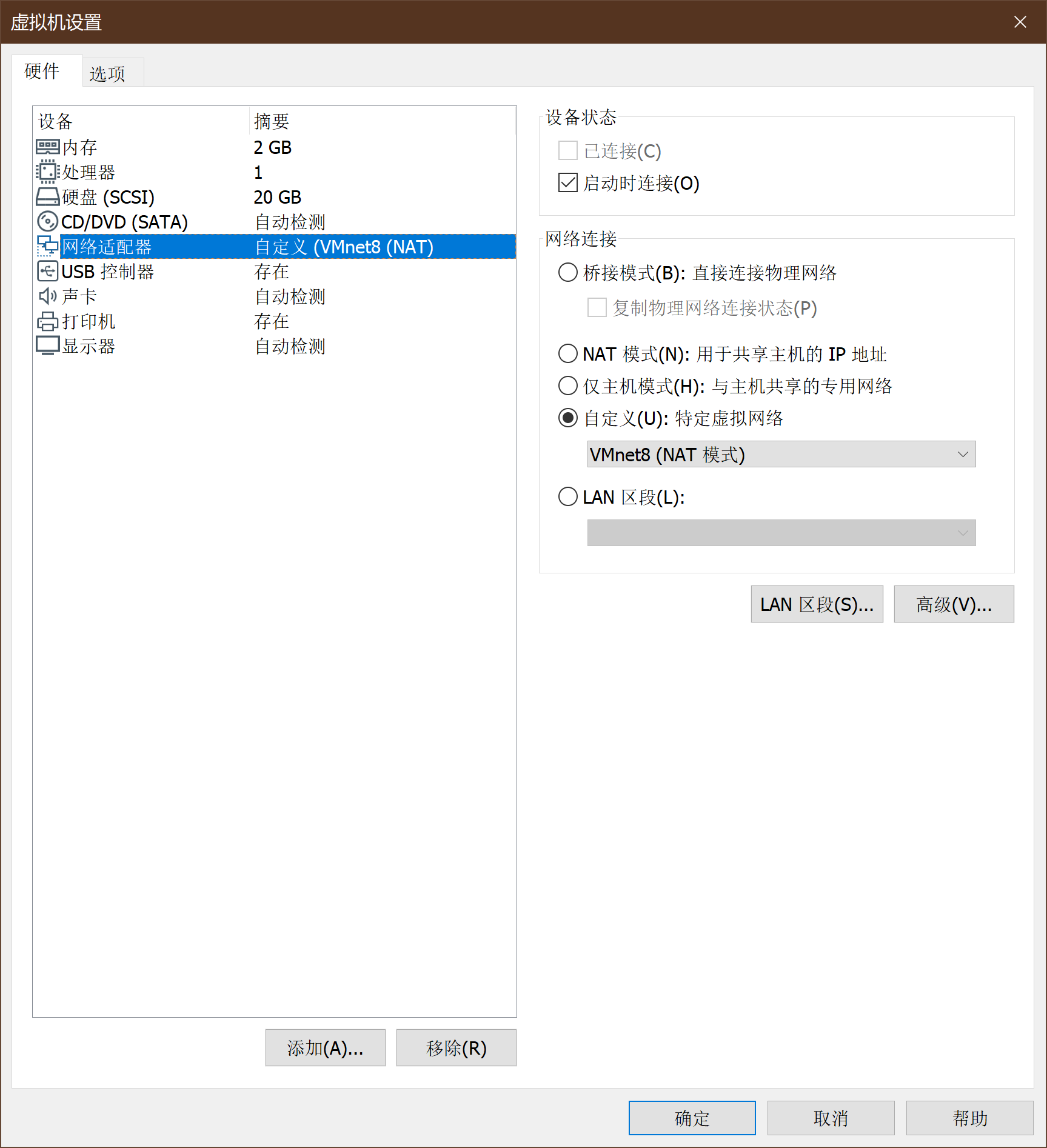
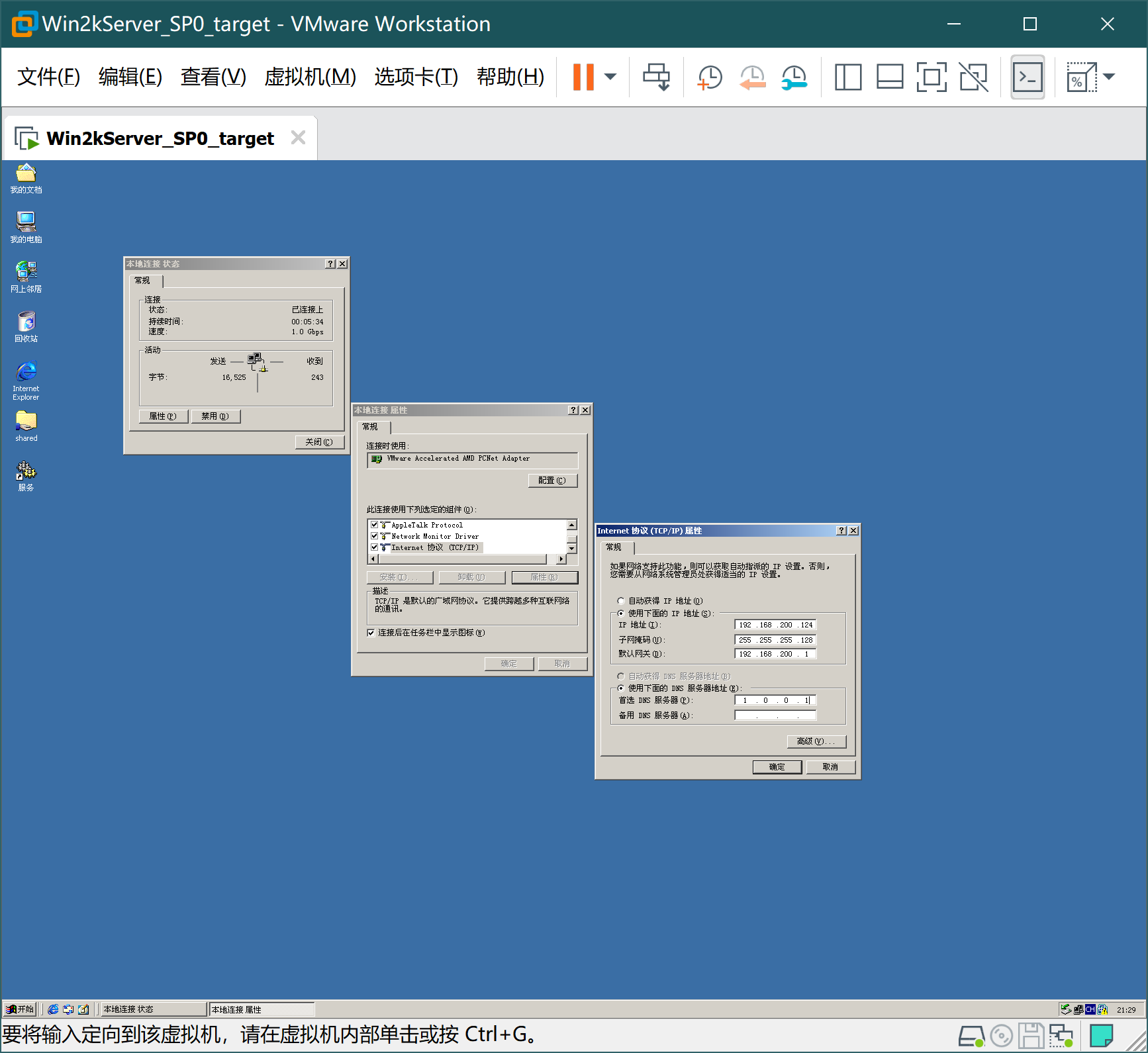
6、安装windows靶机-win2kServer
-
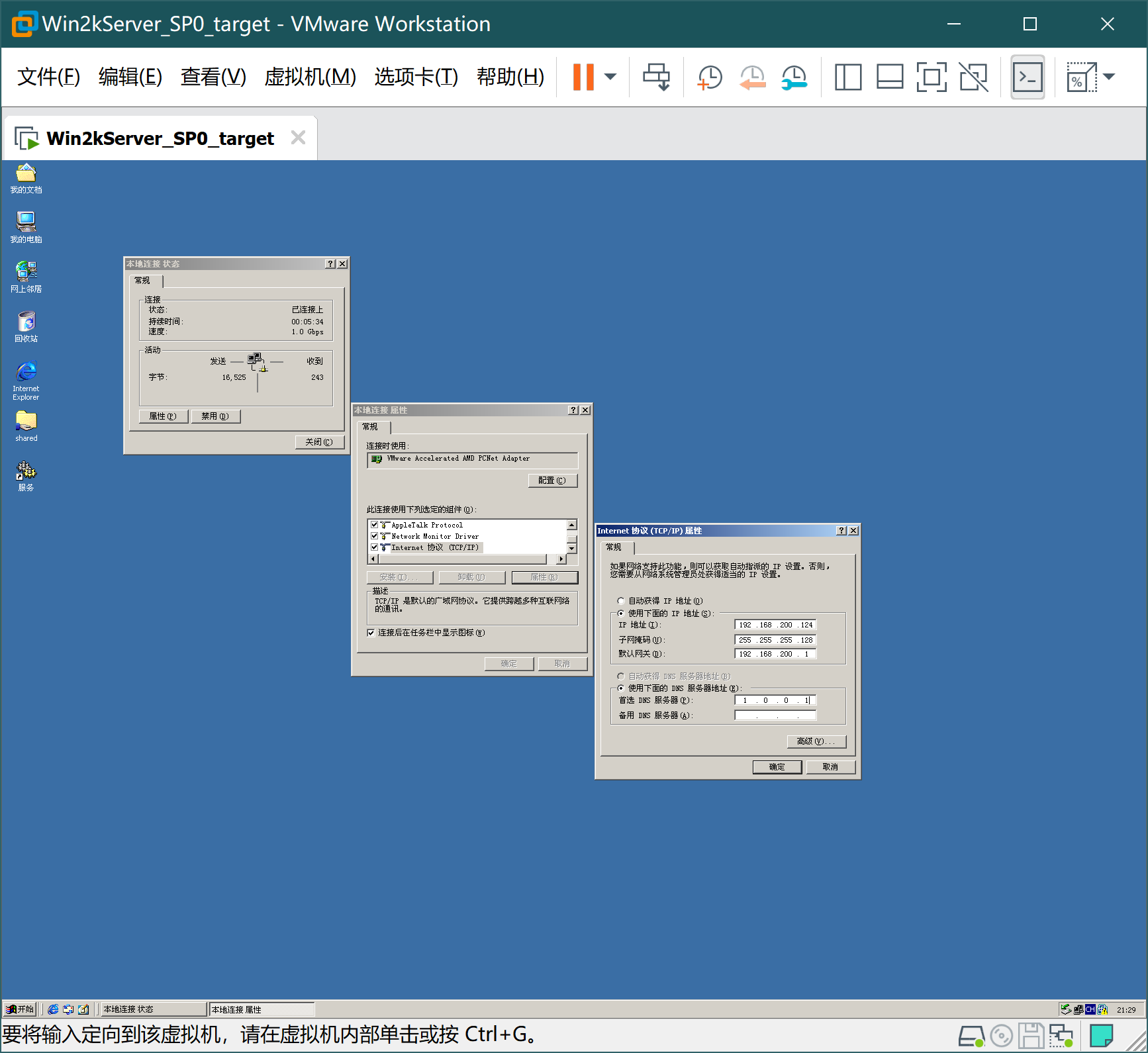
win2kServer通过虚拟机镜像给予,导入方式和上文的Kali相同。安装之后通过VM的快捷键ALT+CTRL+DEL进入系统(直接发送会被主机拦截),账号administrator,密码mima1234。网卡设置如下:
-
打开虚拟机
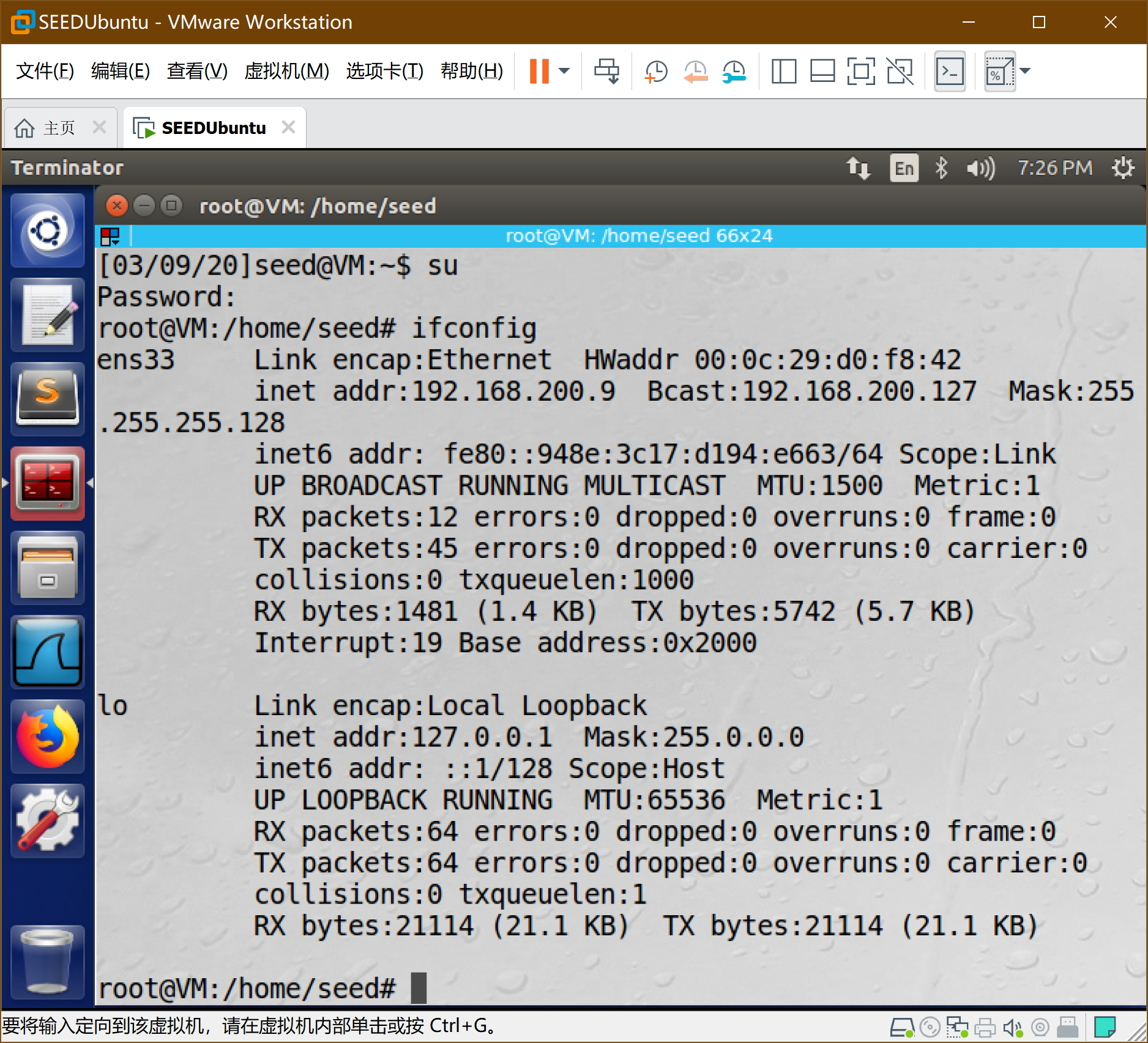
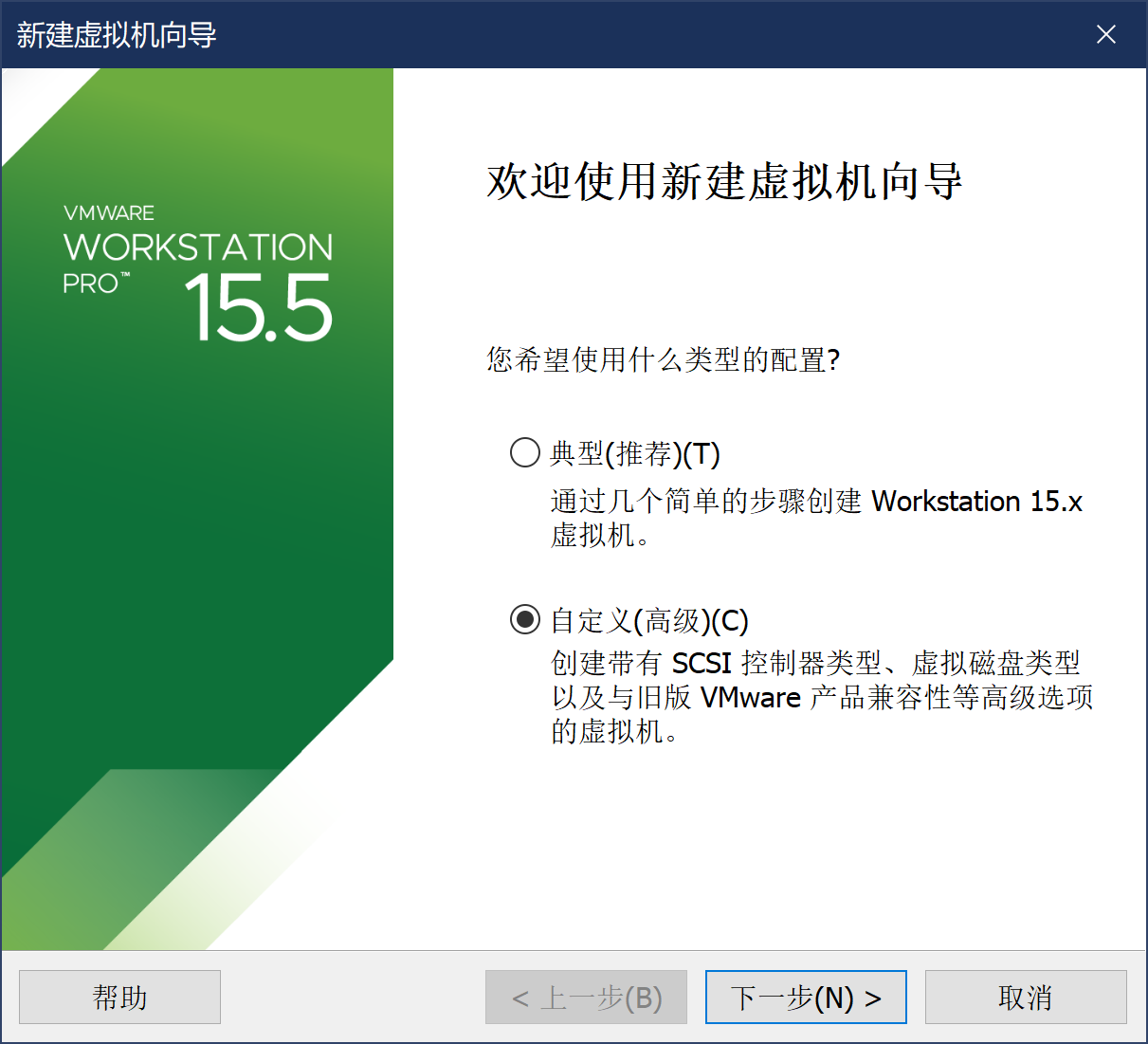
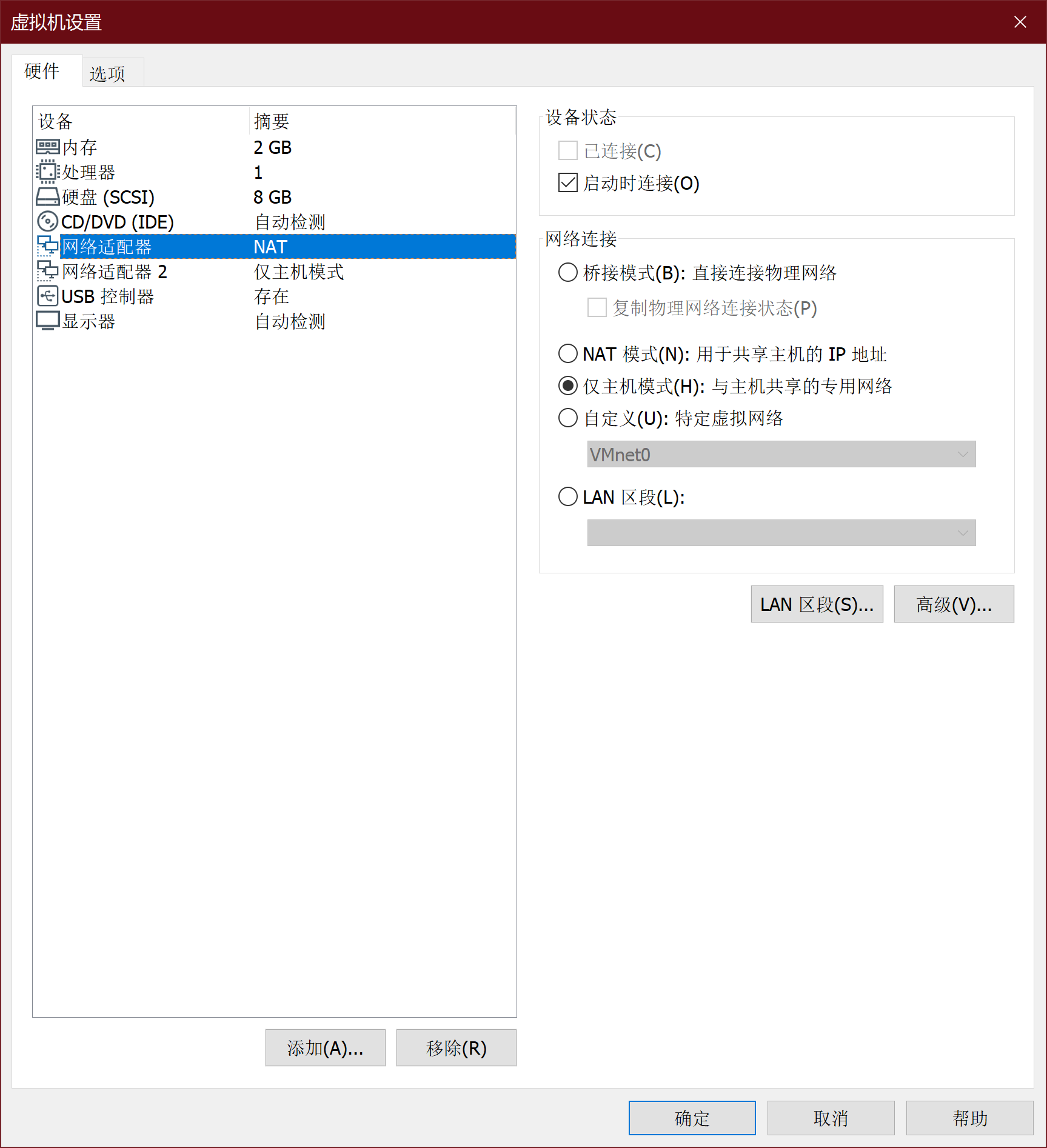
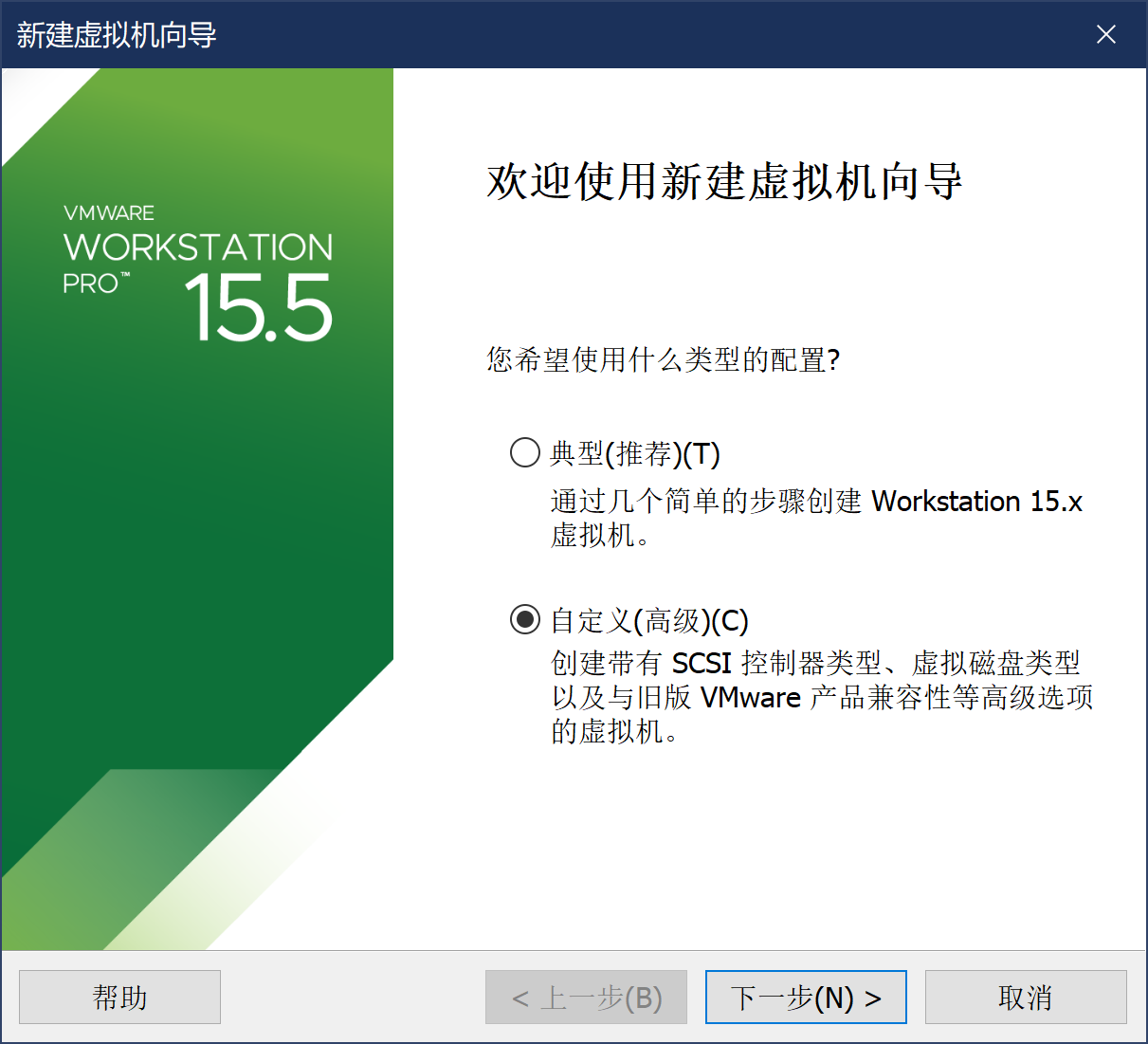
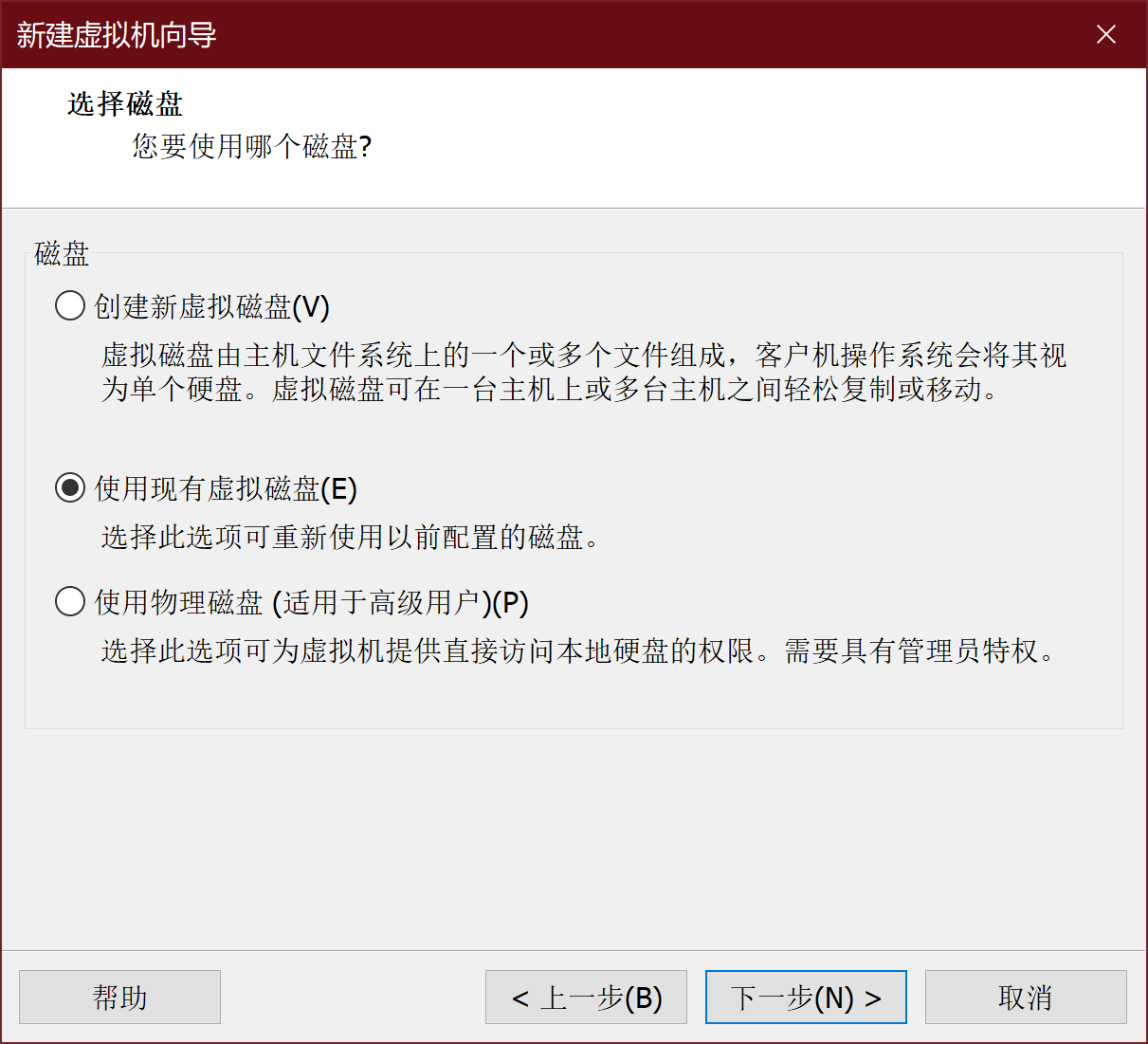
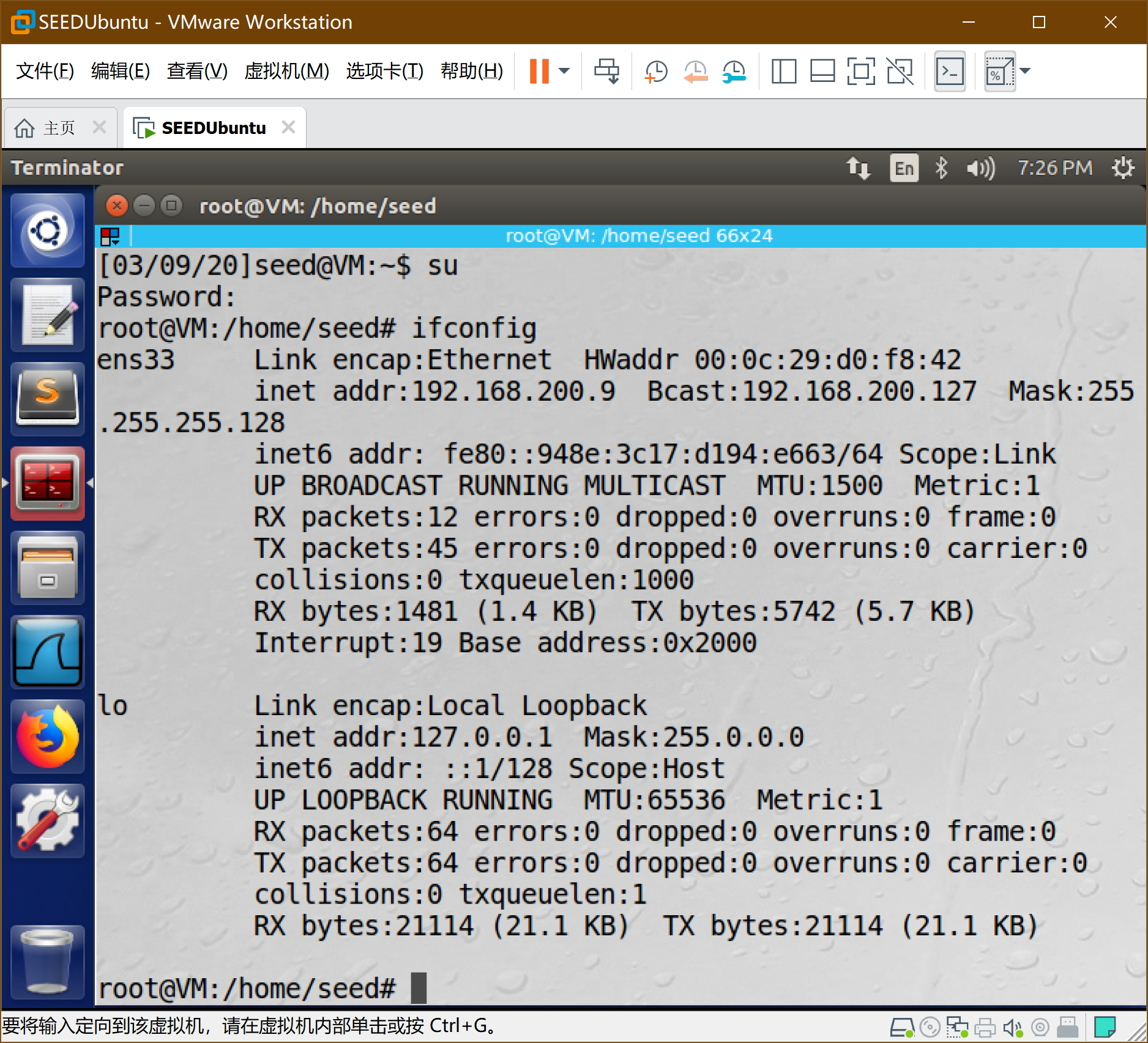
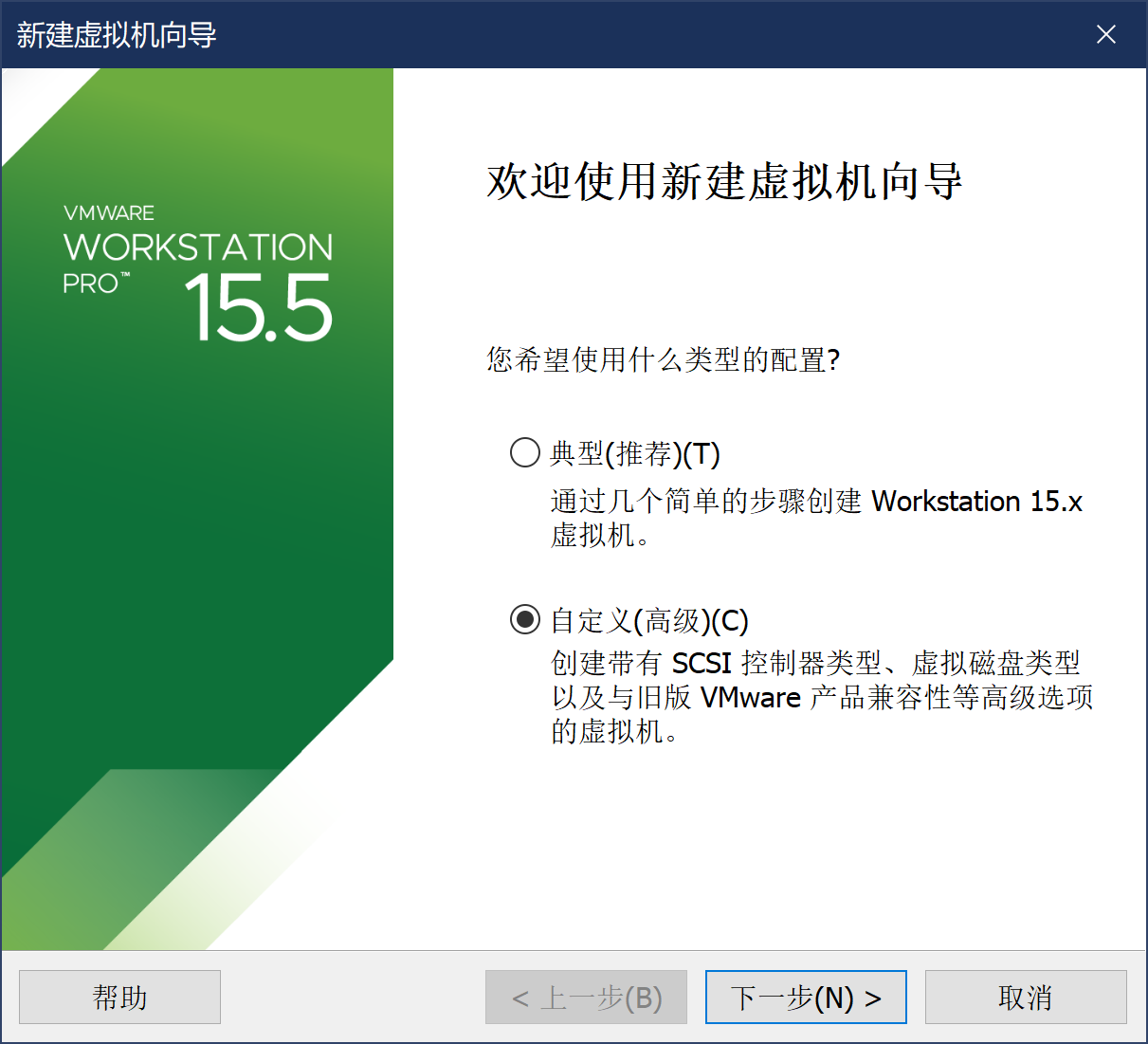
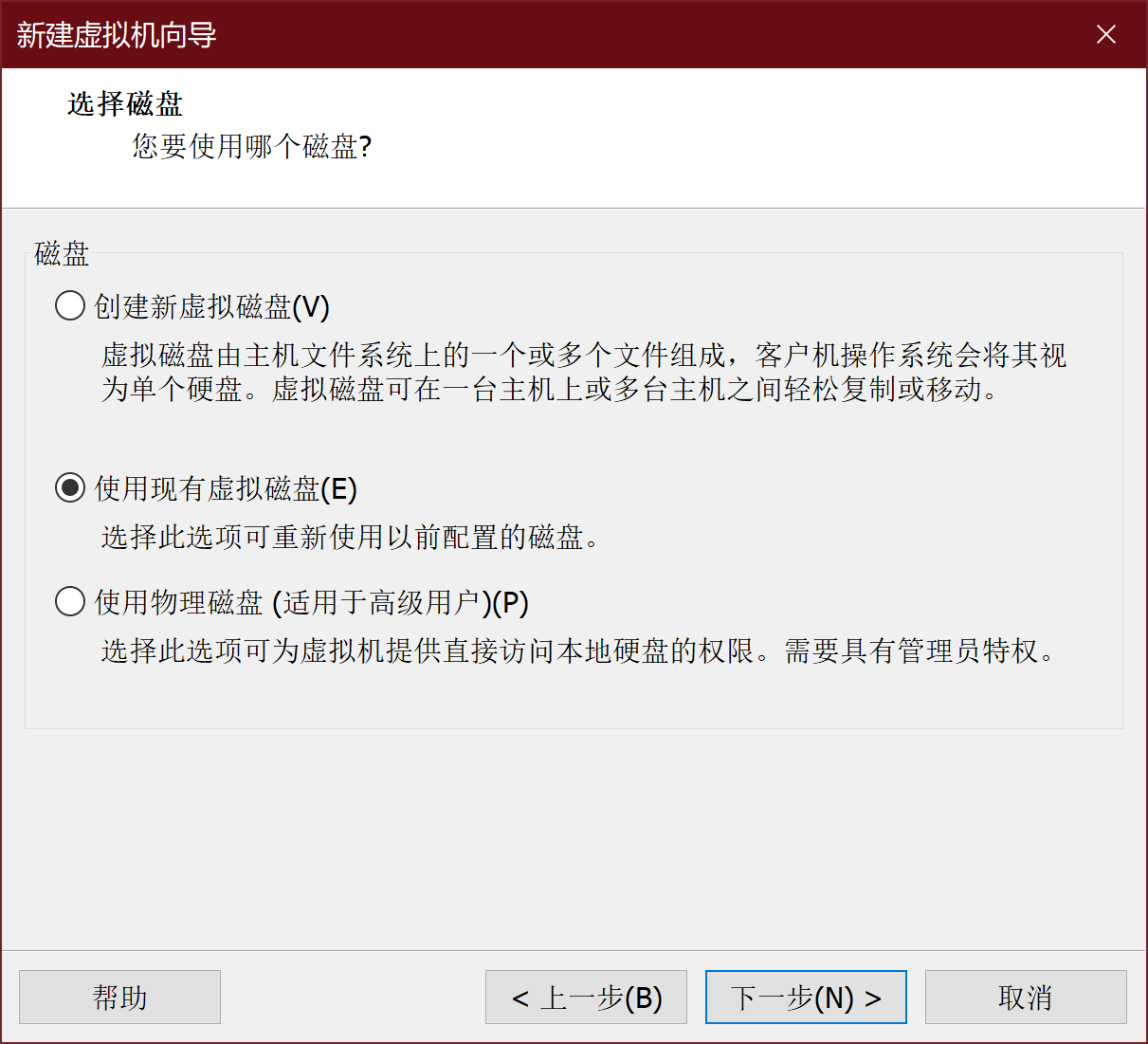
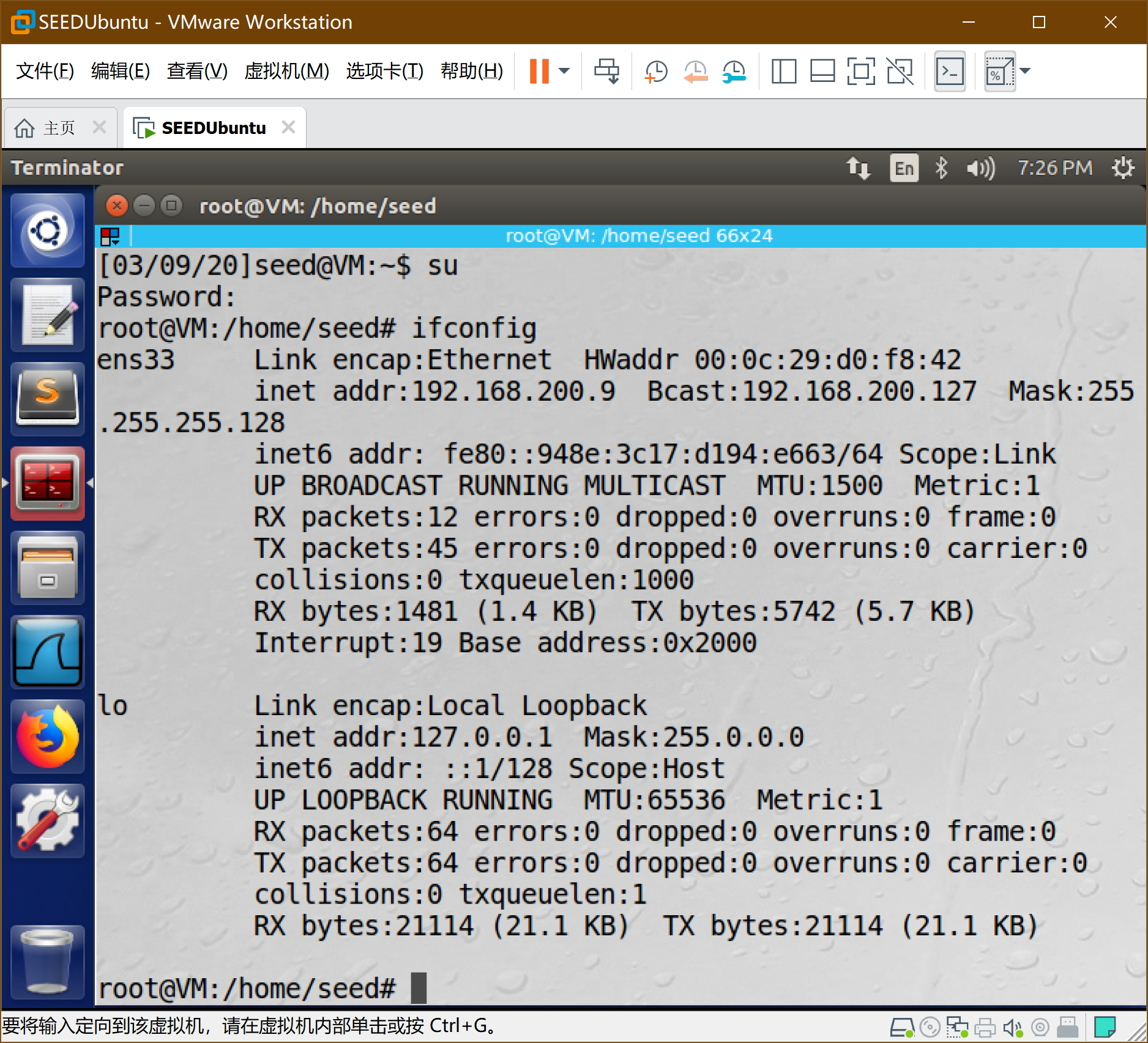
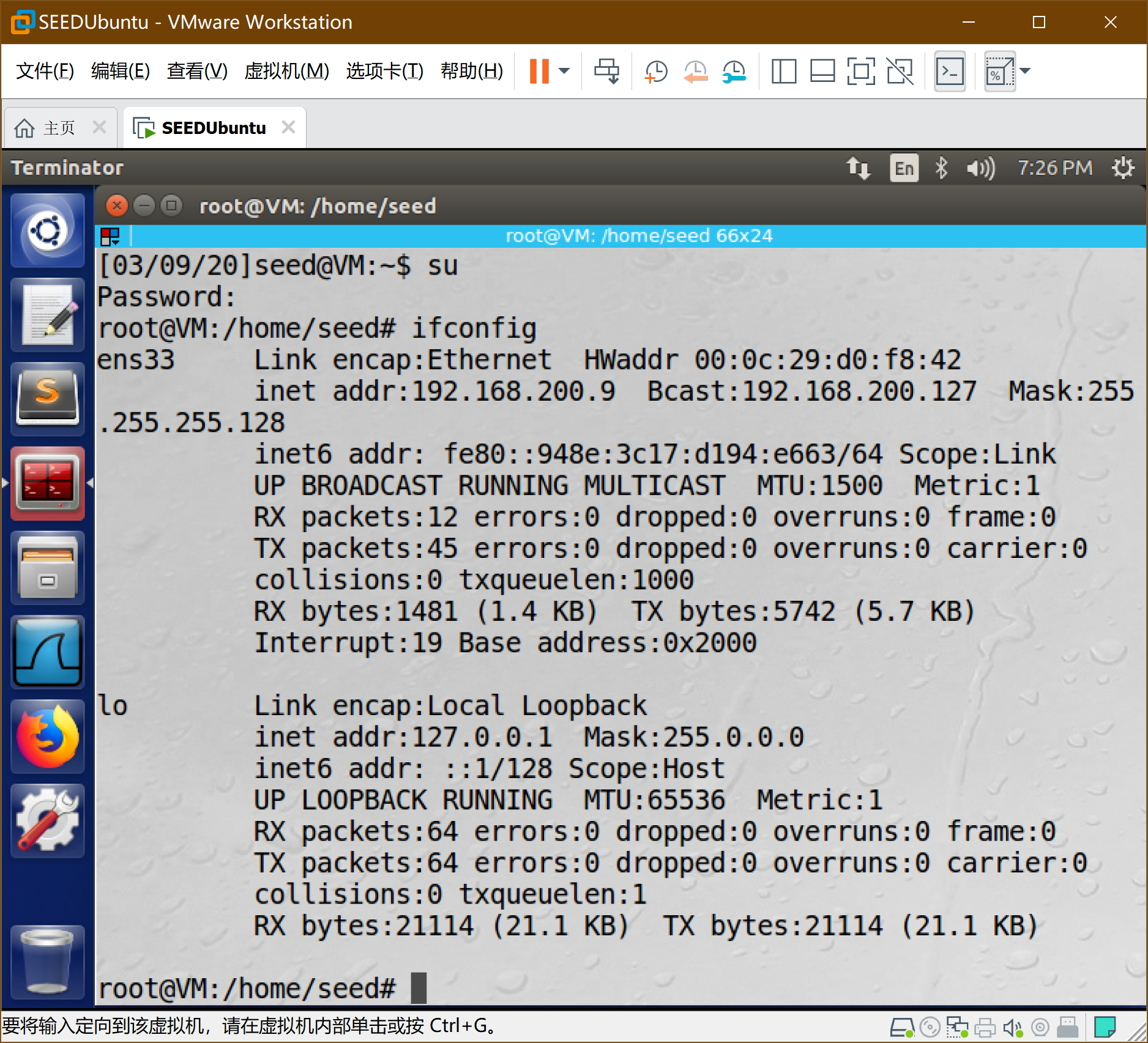
7、SEEDUbuntu安装配置
-
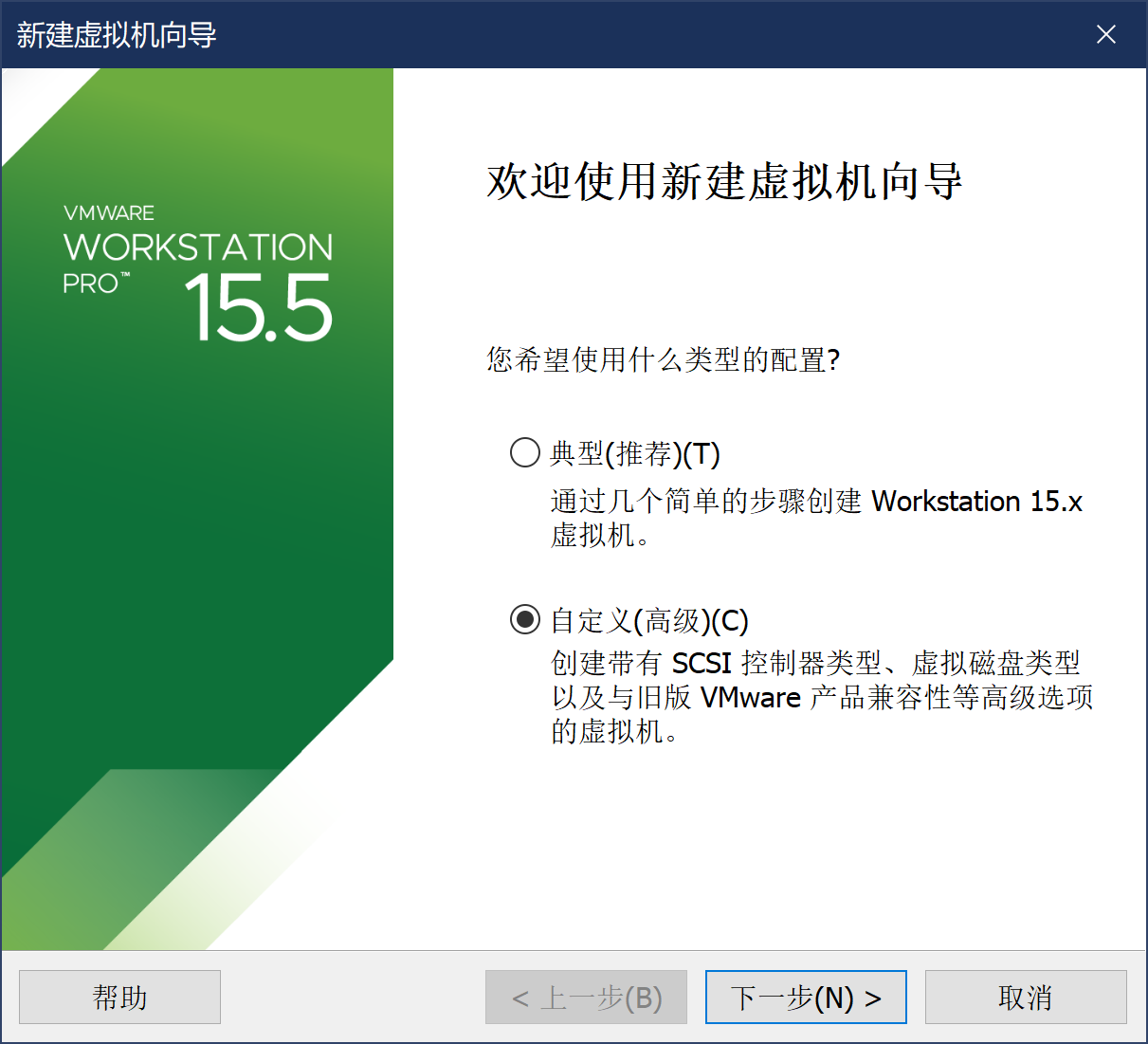
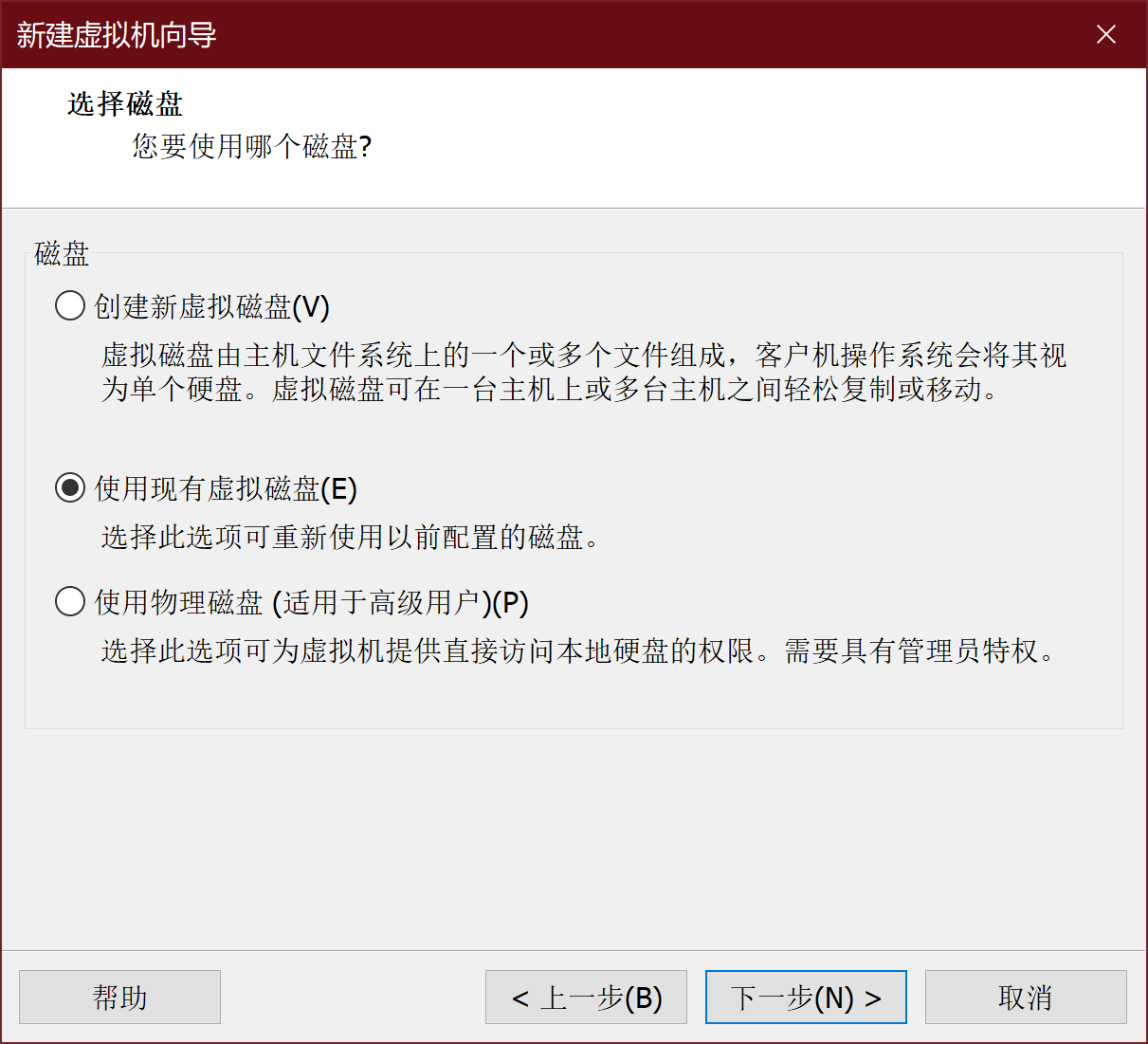
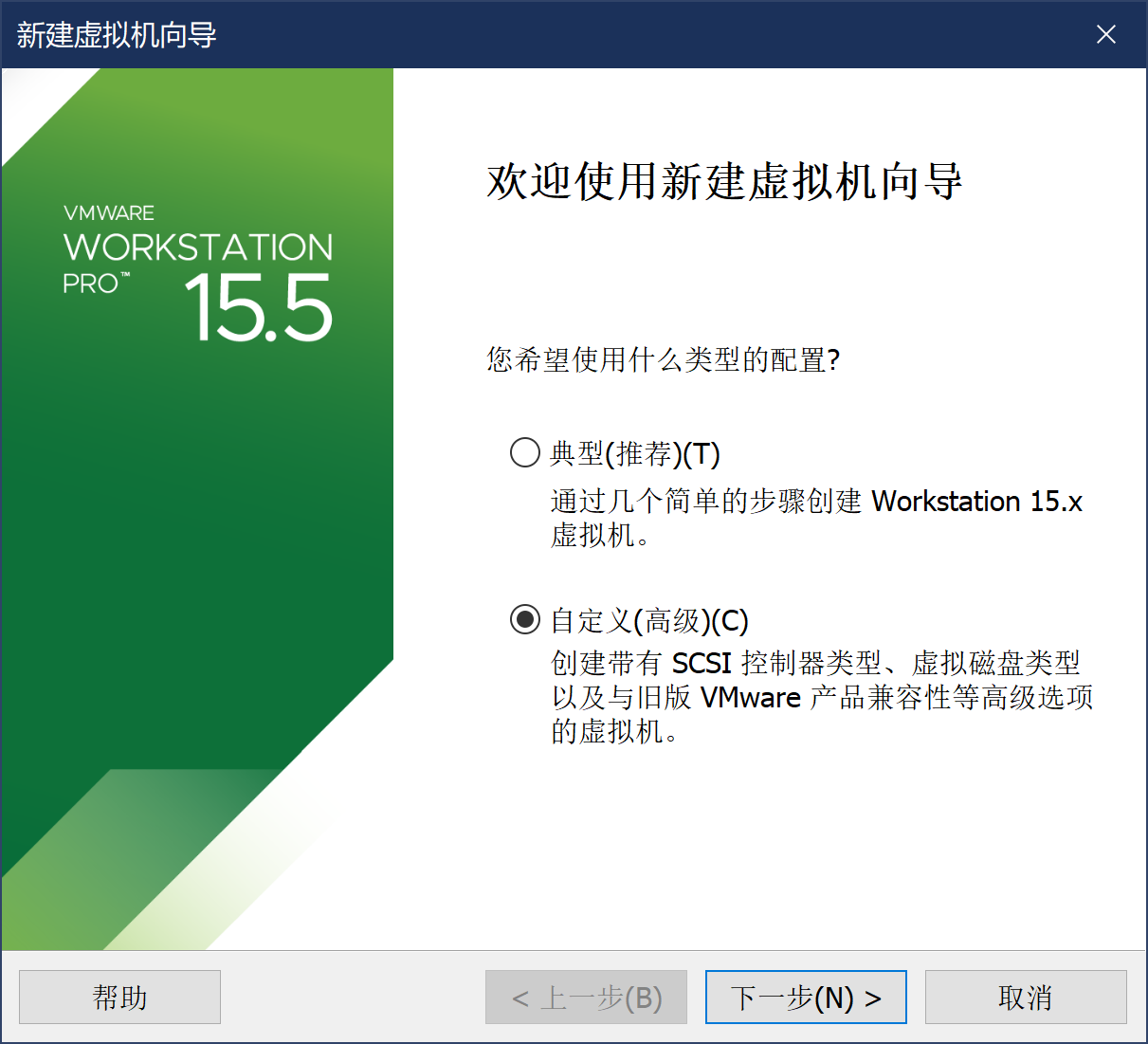
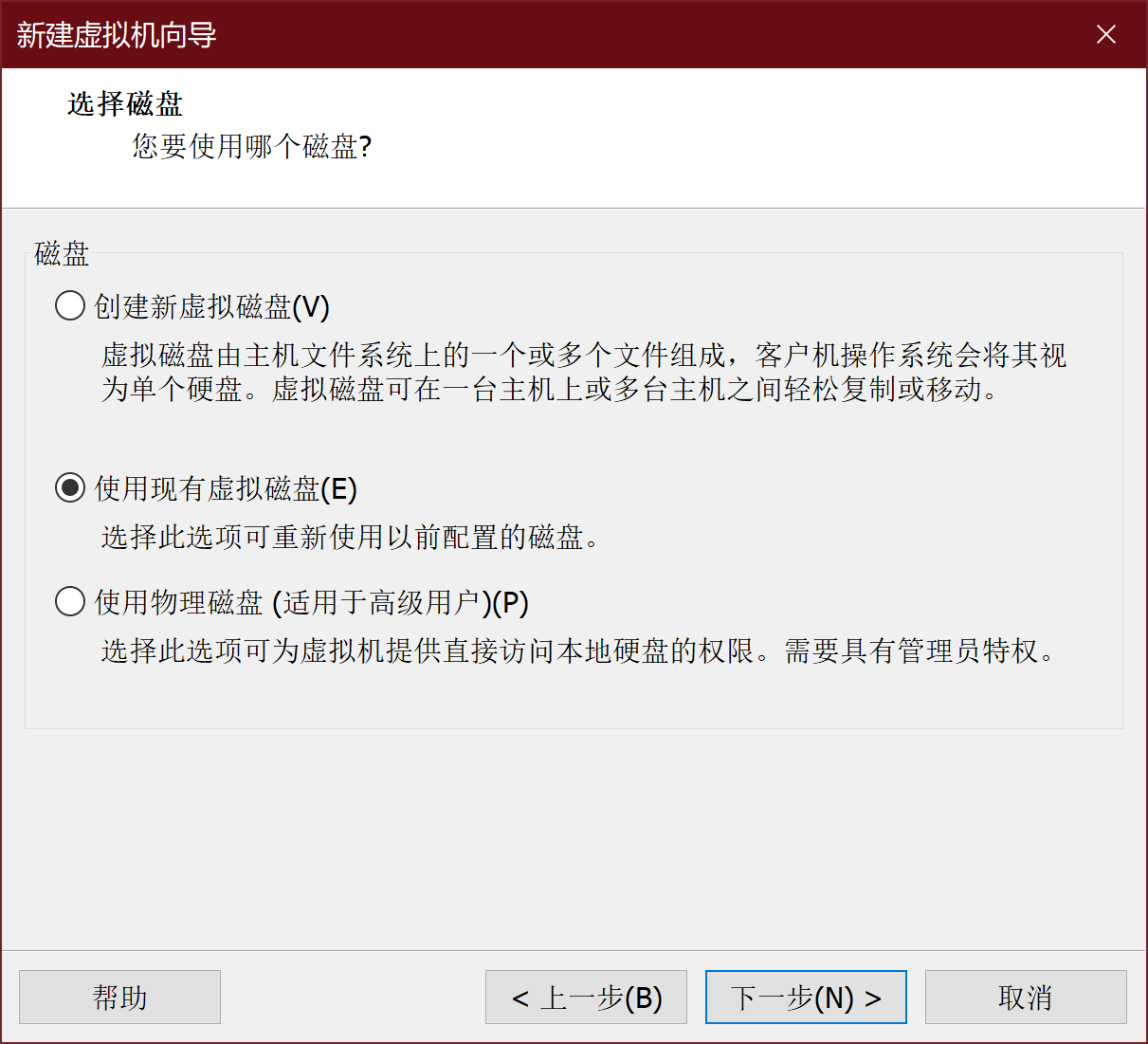
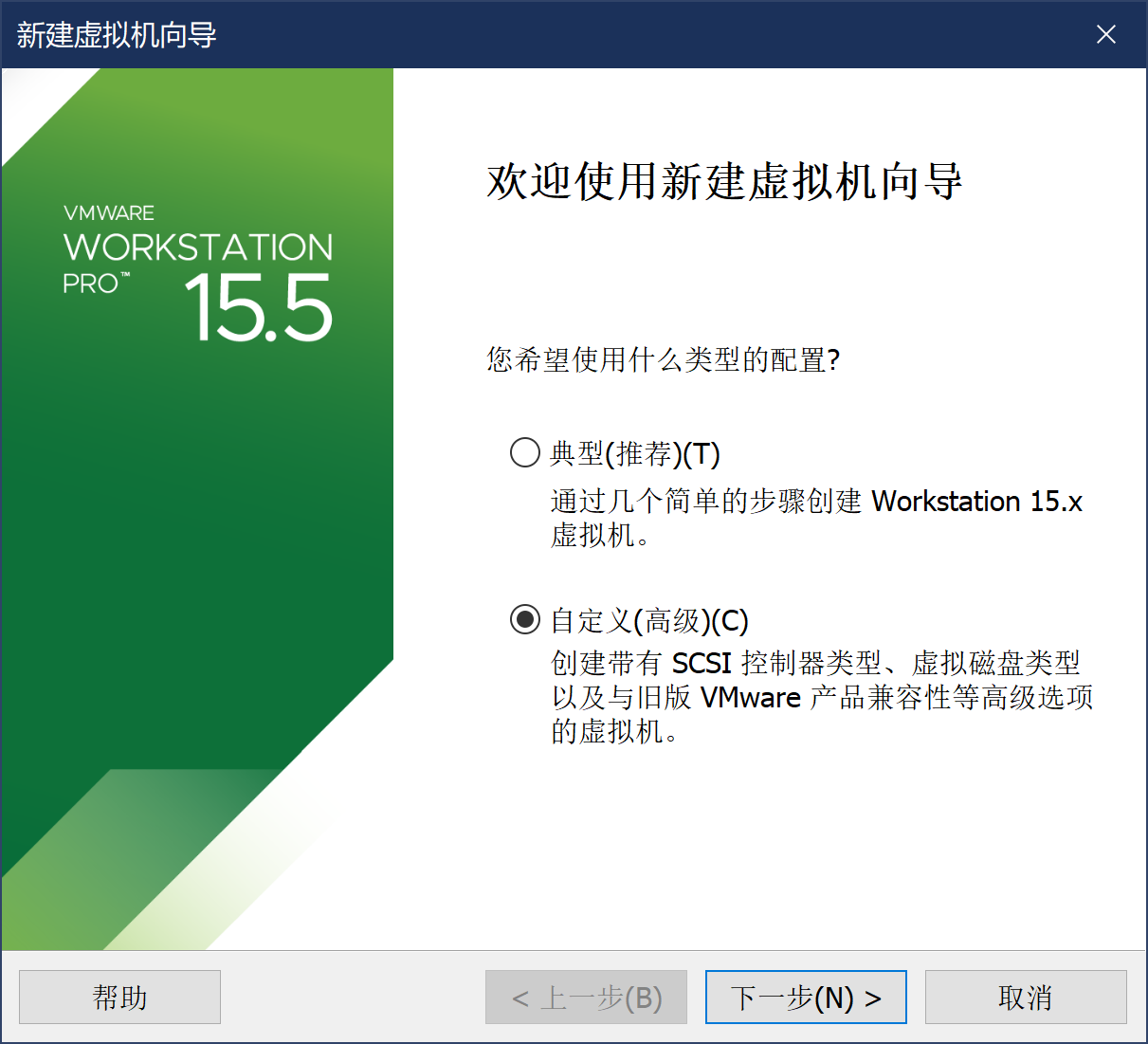
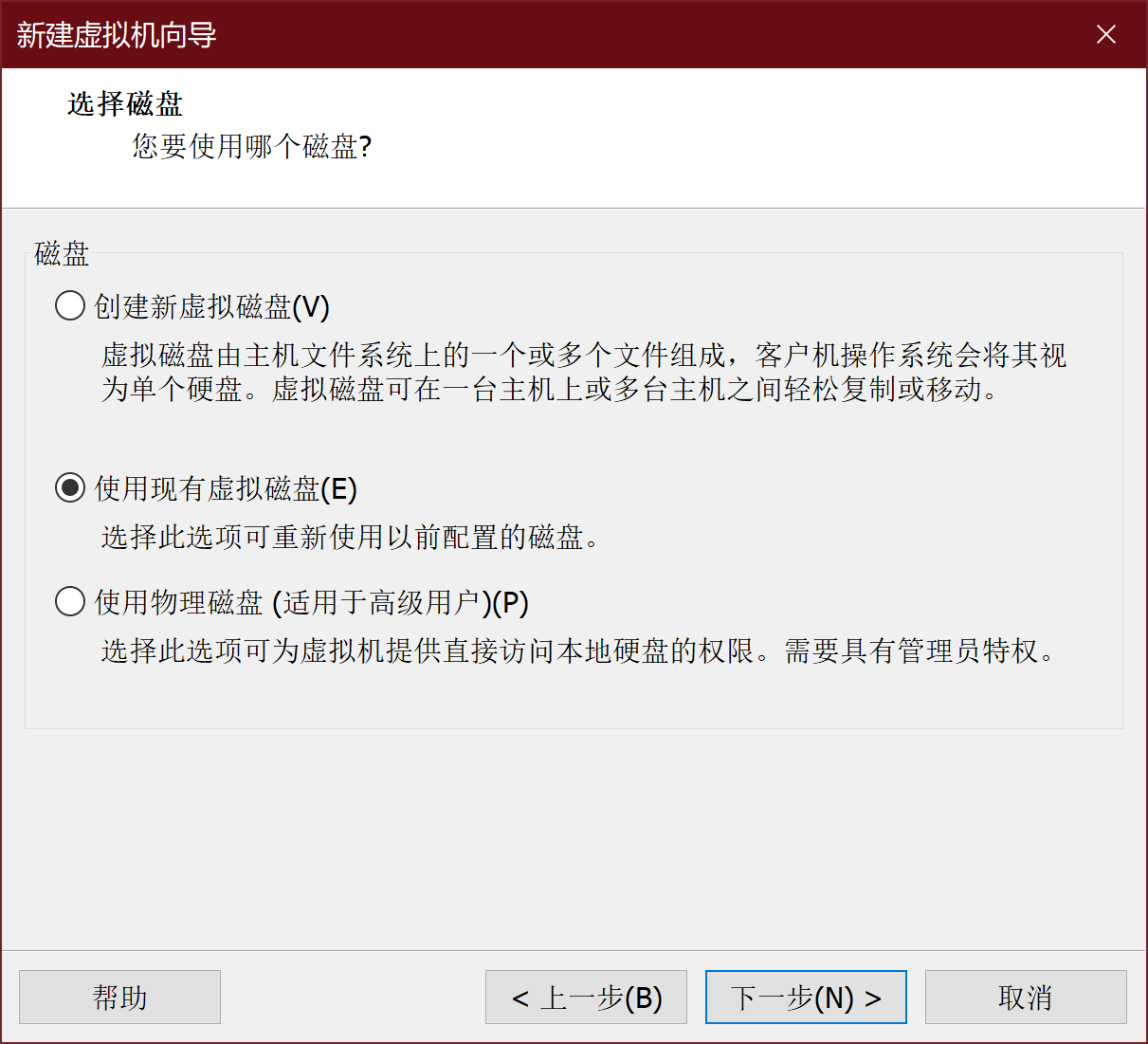
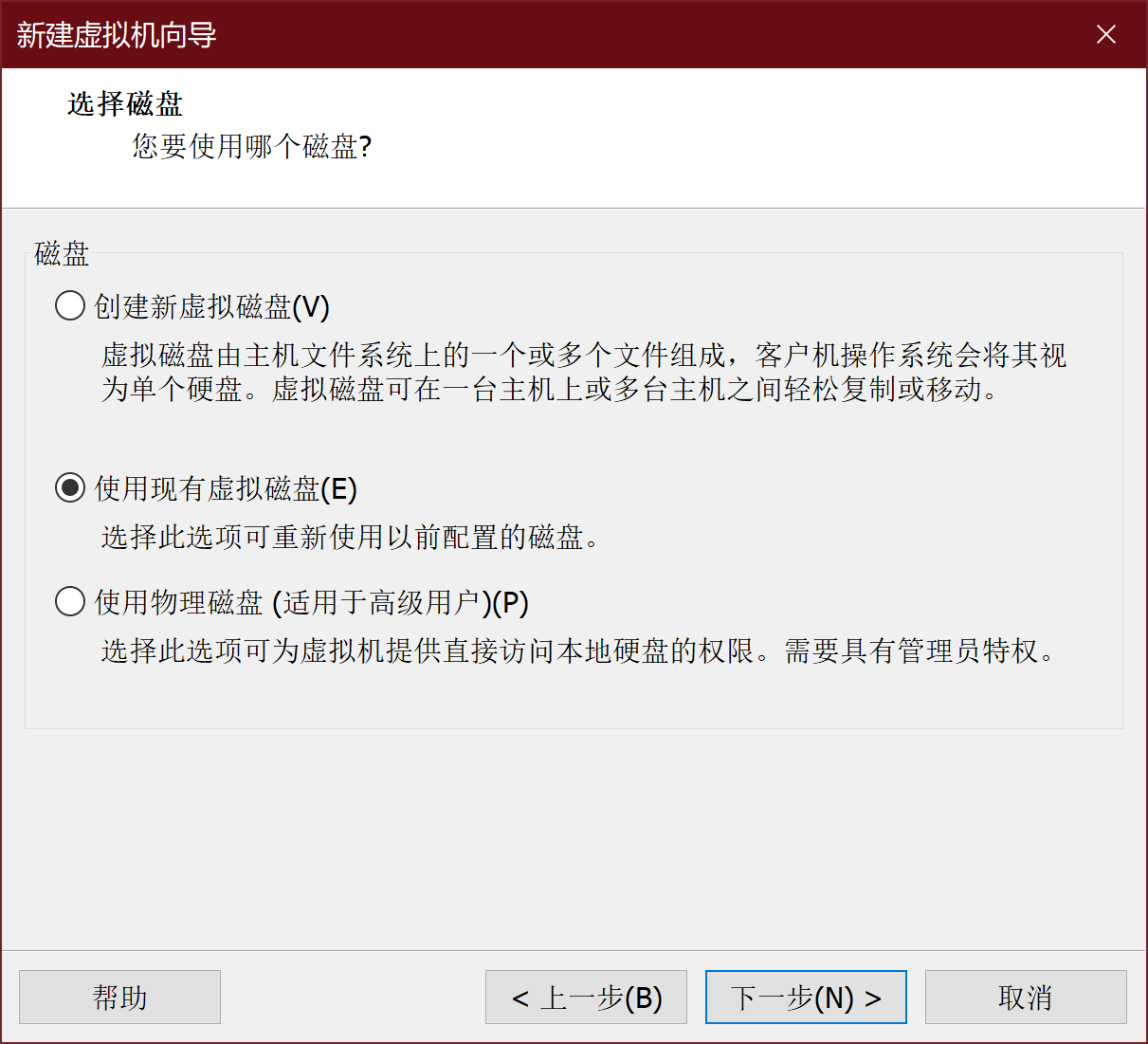
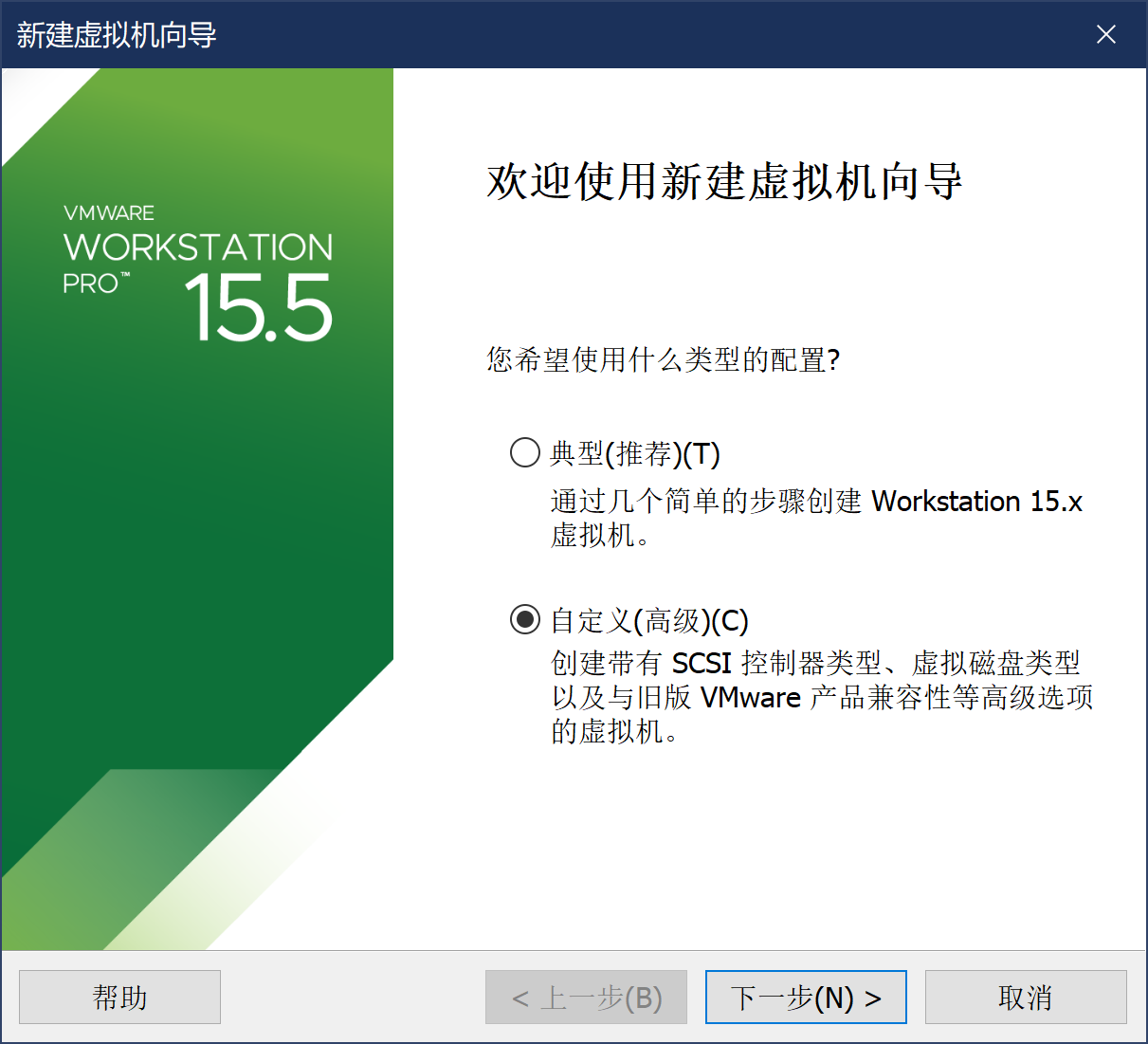
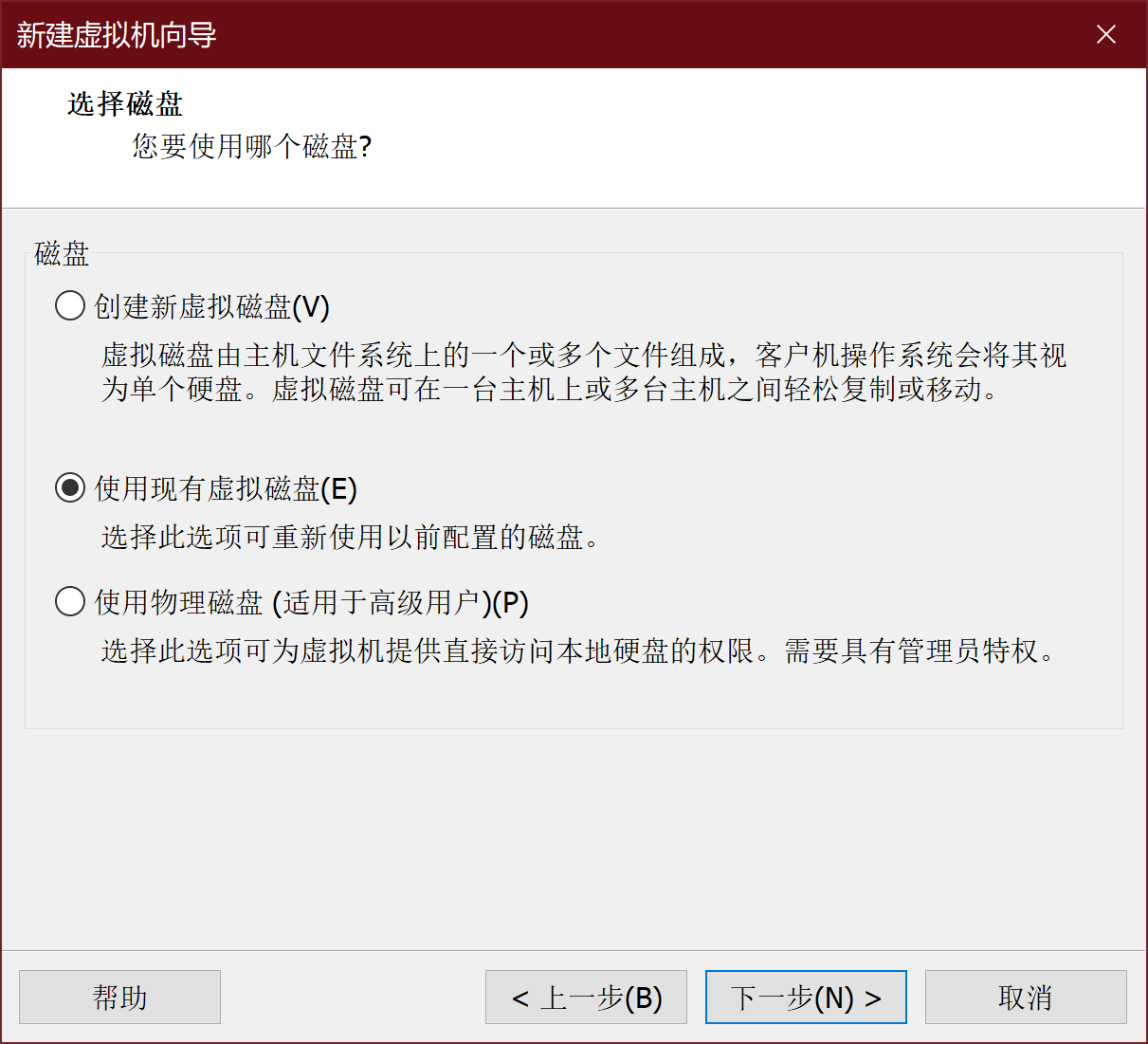
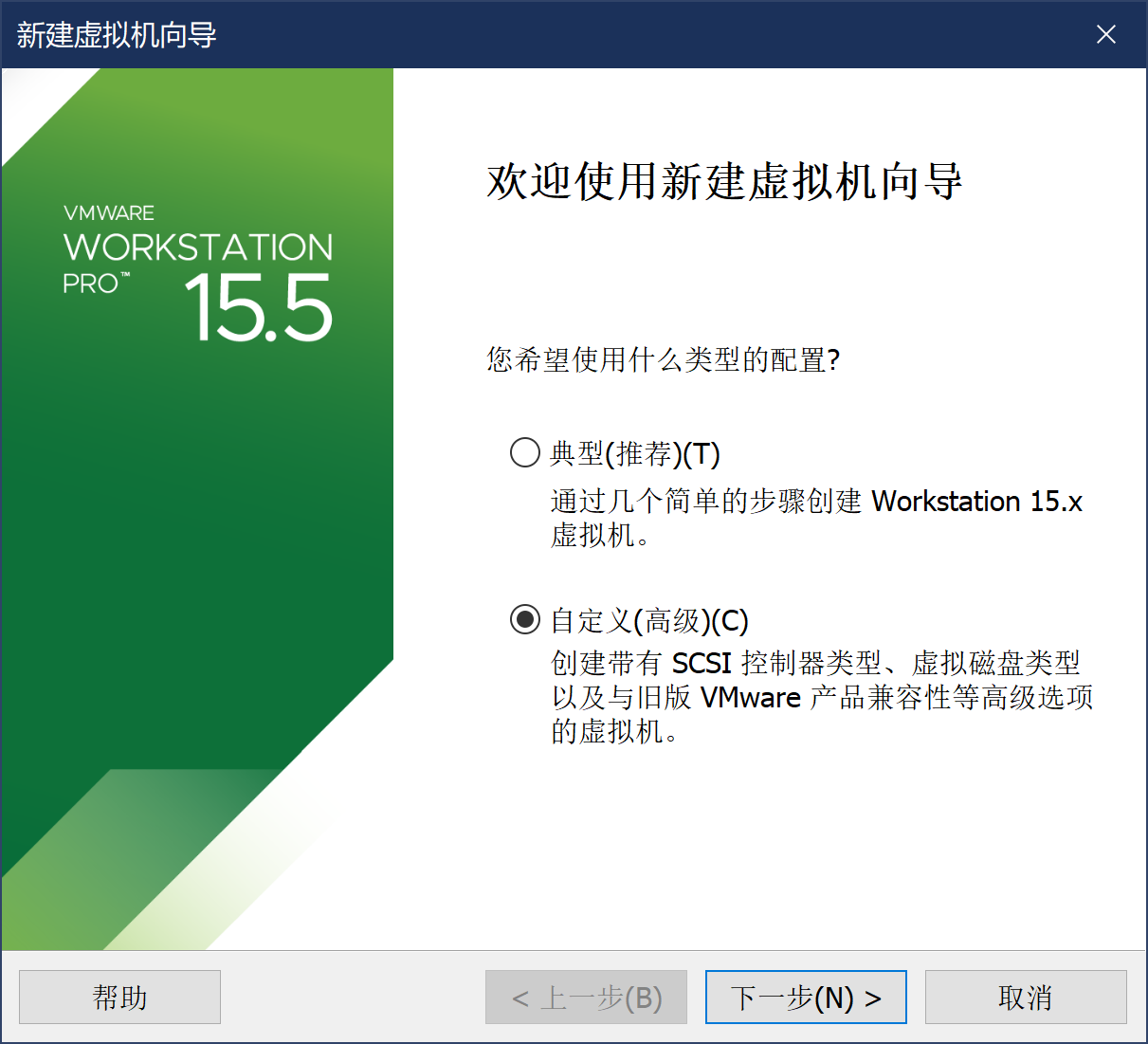
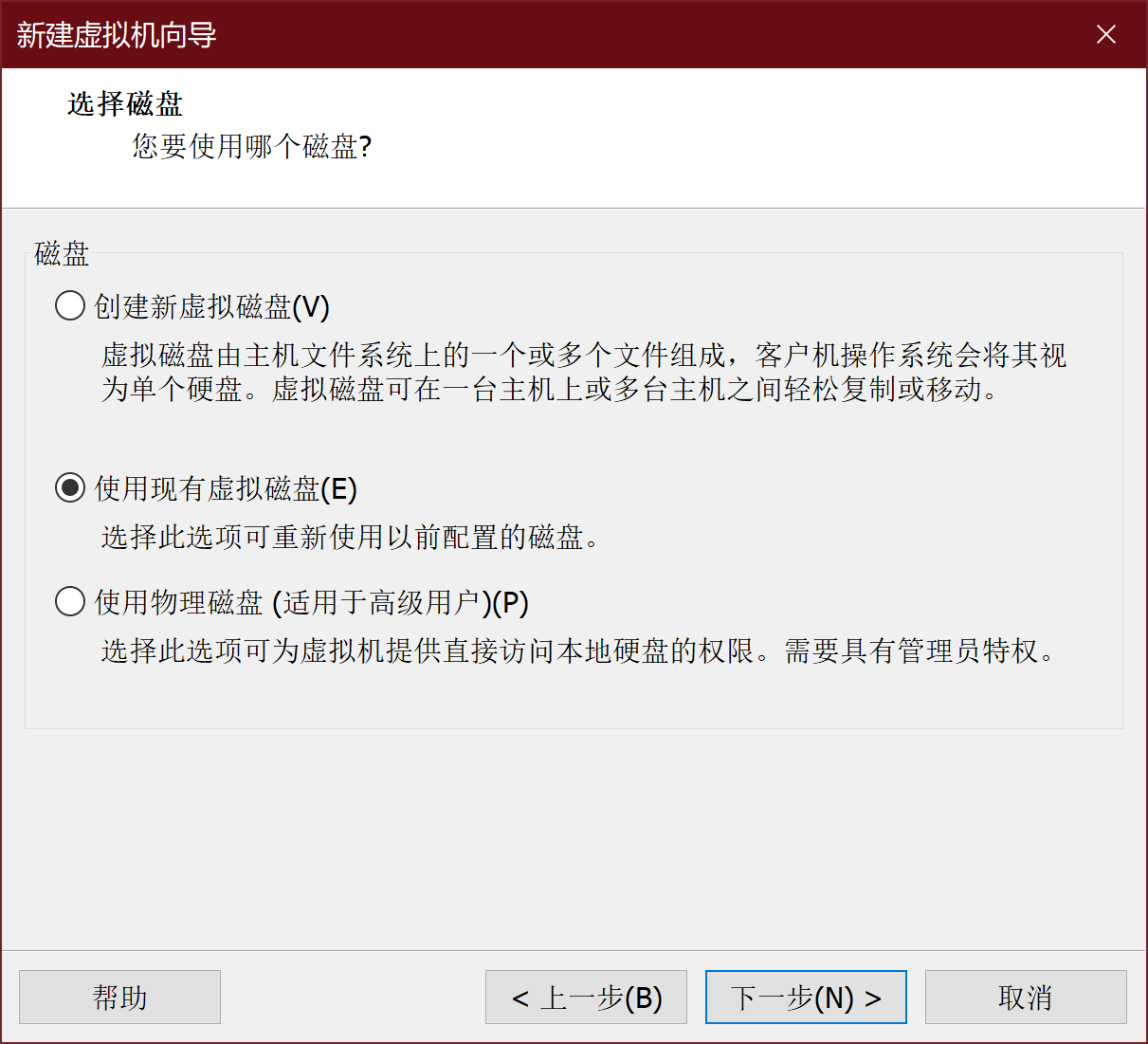
SEEDUbuntu通过VM虚拟机vmdk磁盘镜像给定,选择新建虚拟机->自定义安装->兼容XX随便选->稍后安装系统->选择linux、版本ubuntu->名称(SEEDUbuntu)位置(D盘)->下一步->使用现有虚拟磁盘!!!选择seedubuntu的vmdk文件(SEEDUbuntu-16.04-32bit.vmdk)->下一步->保持现有格式。
-
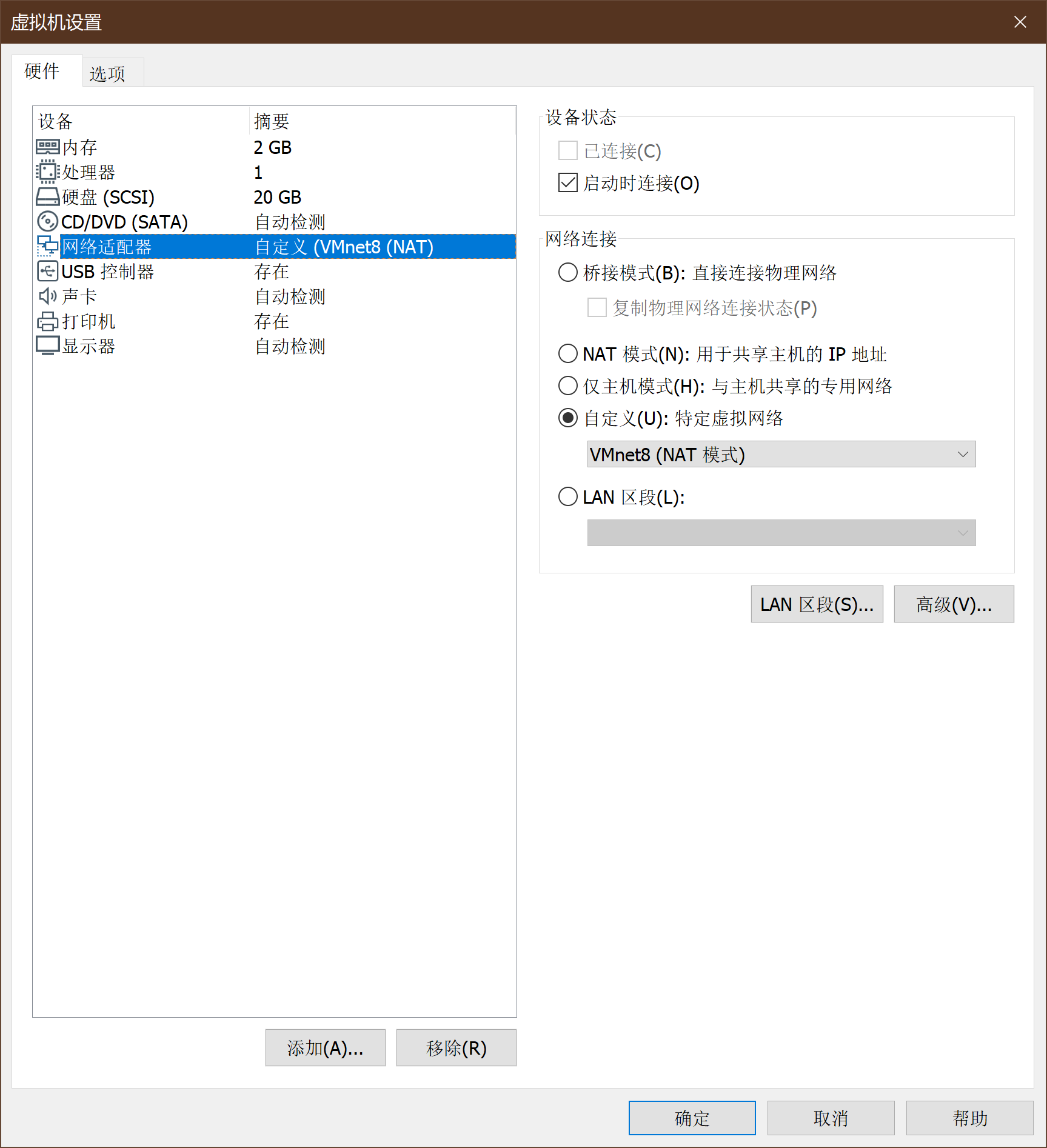
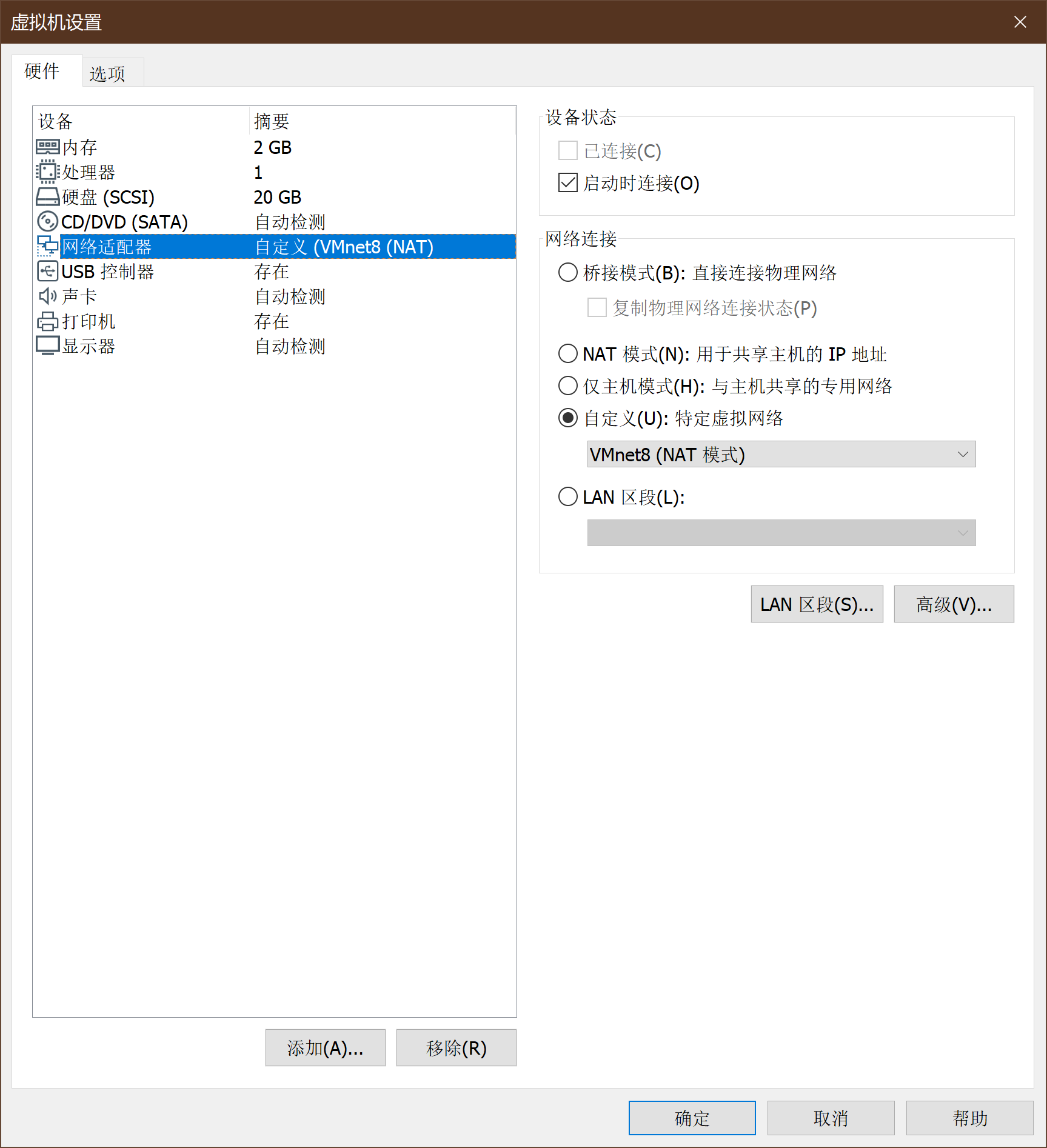
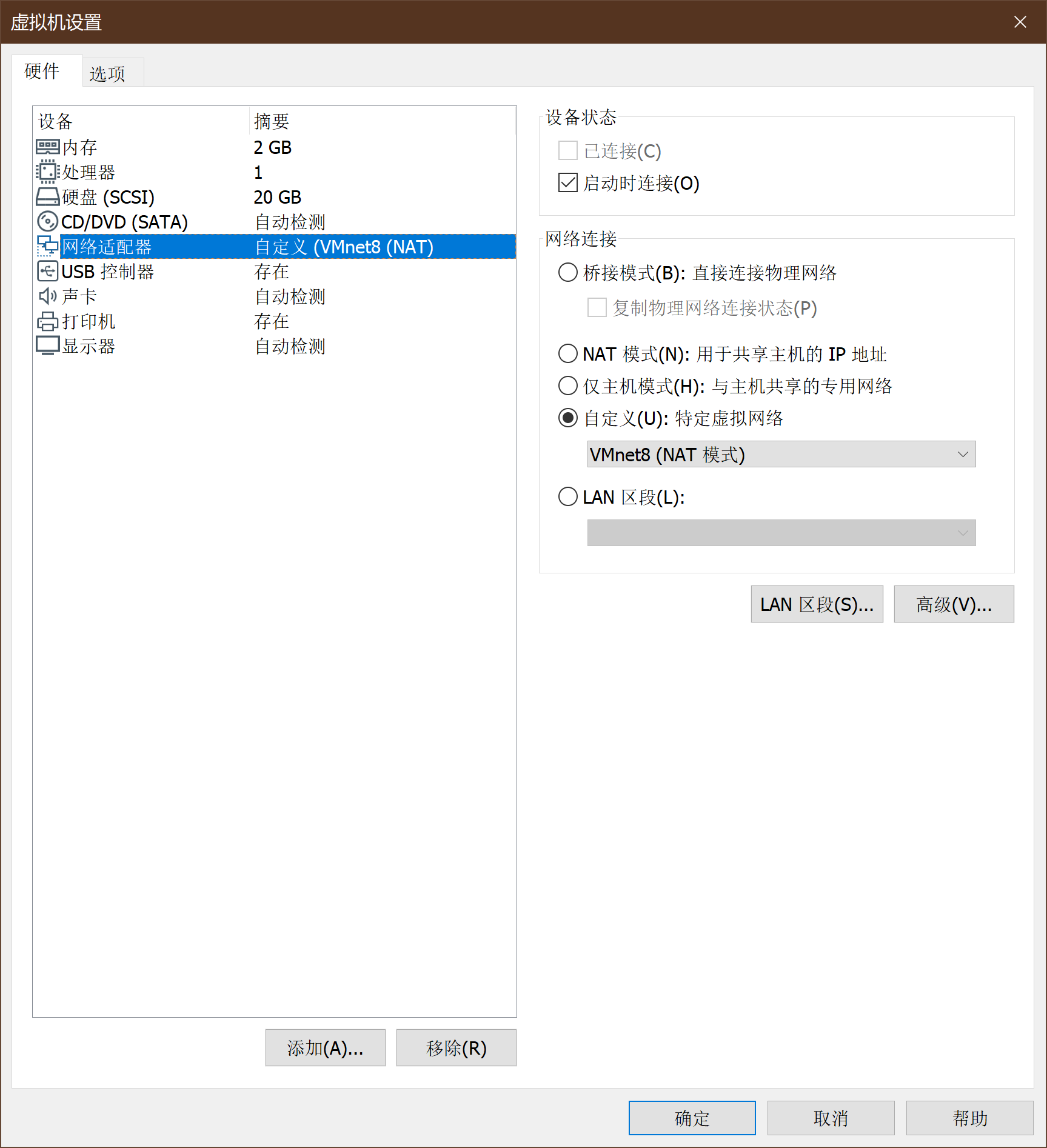
SEEDUbuntu的网卡设置如下:
-
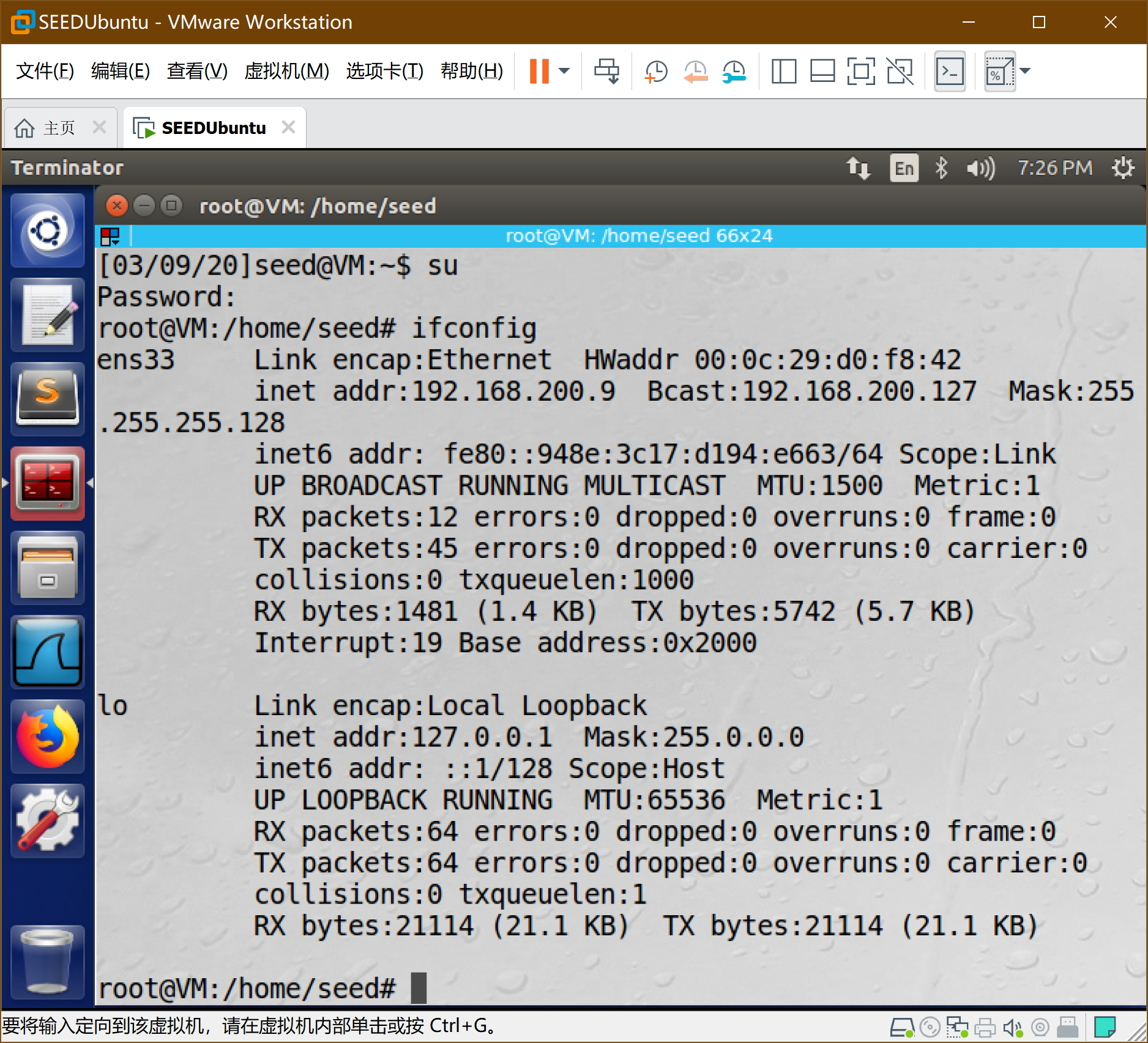
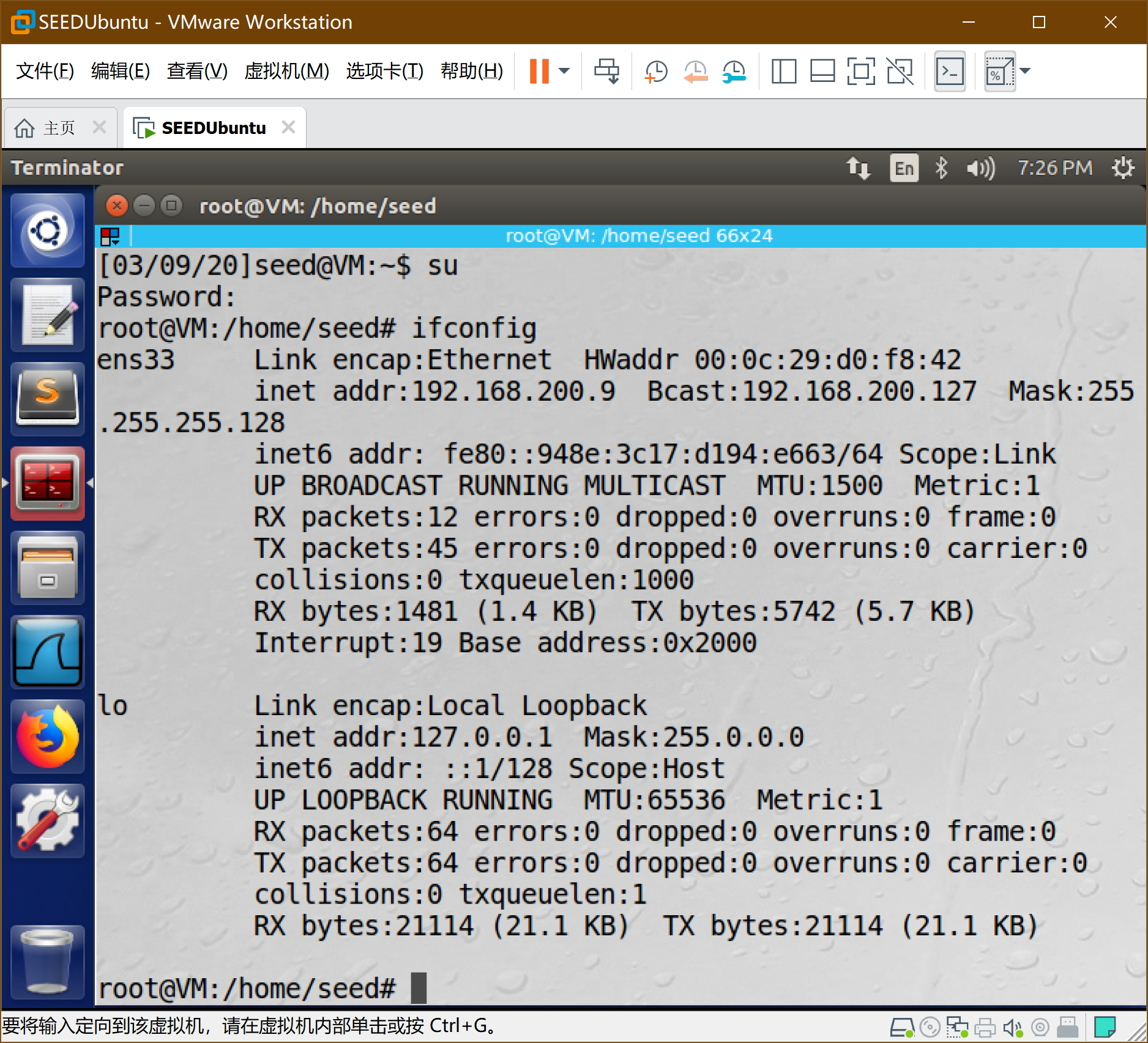
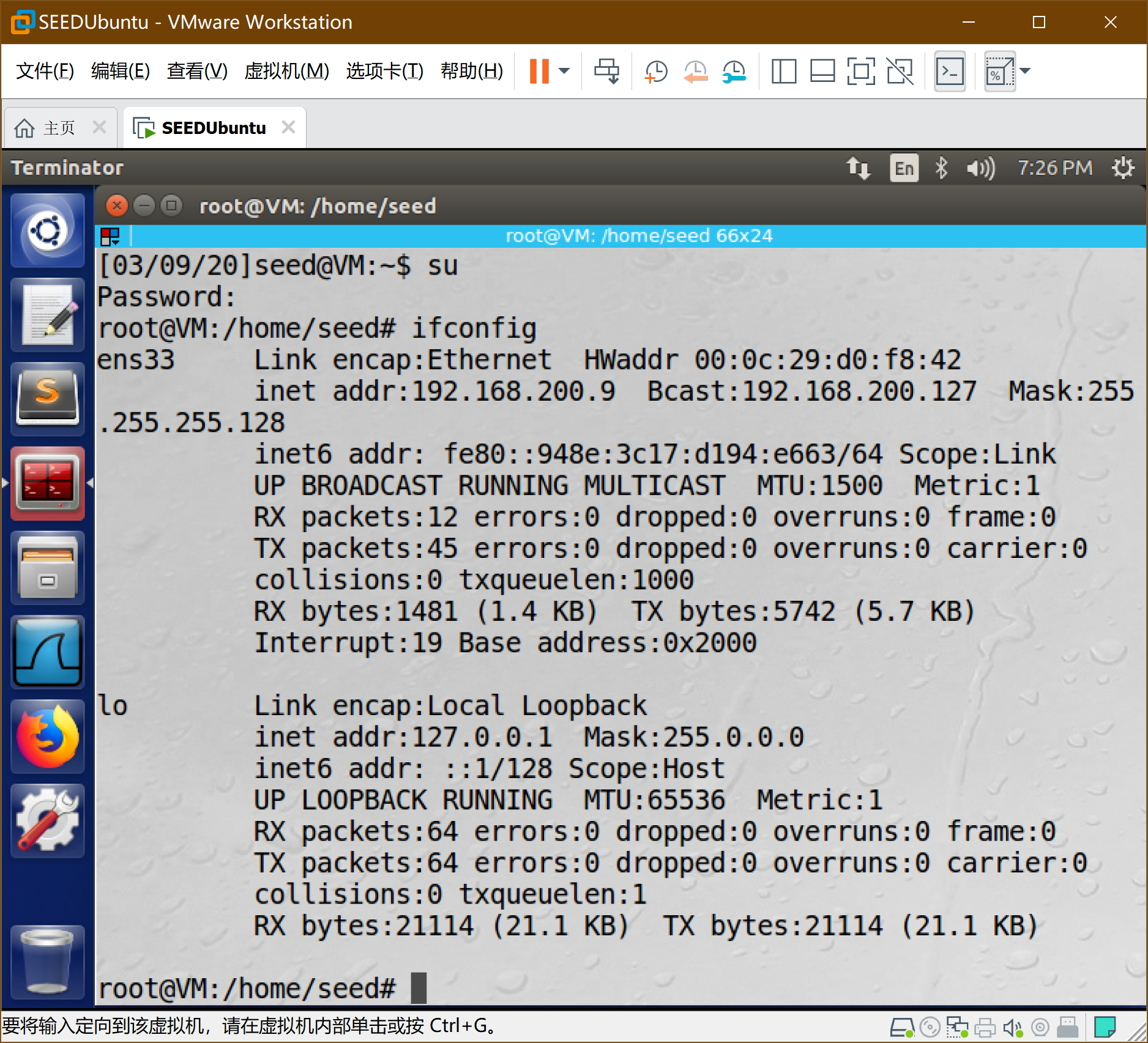
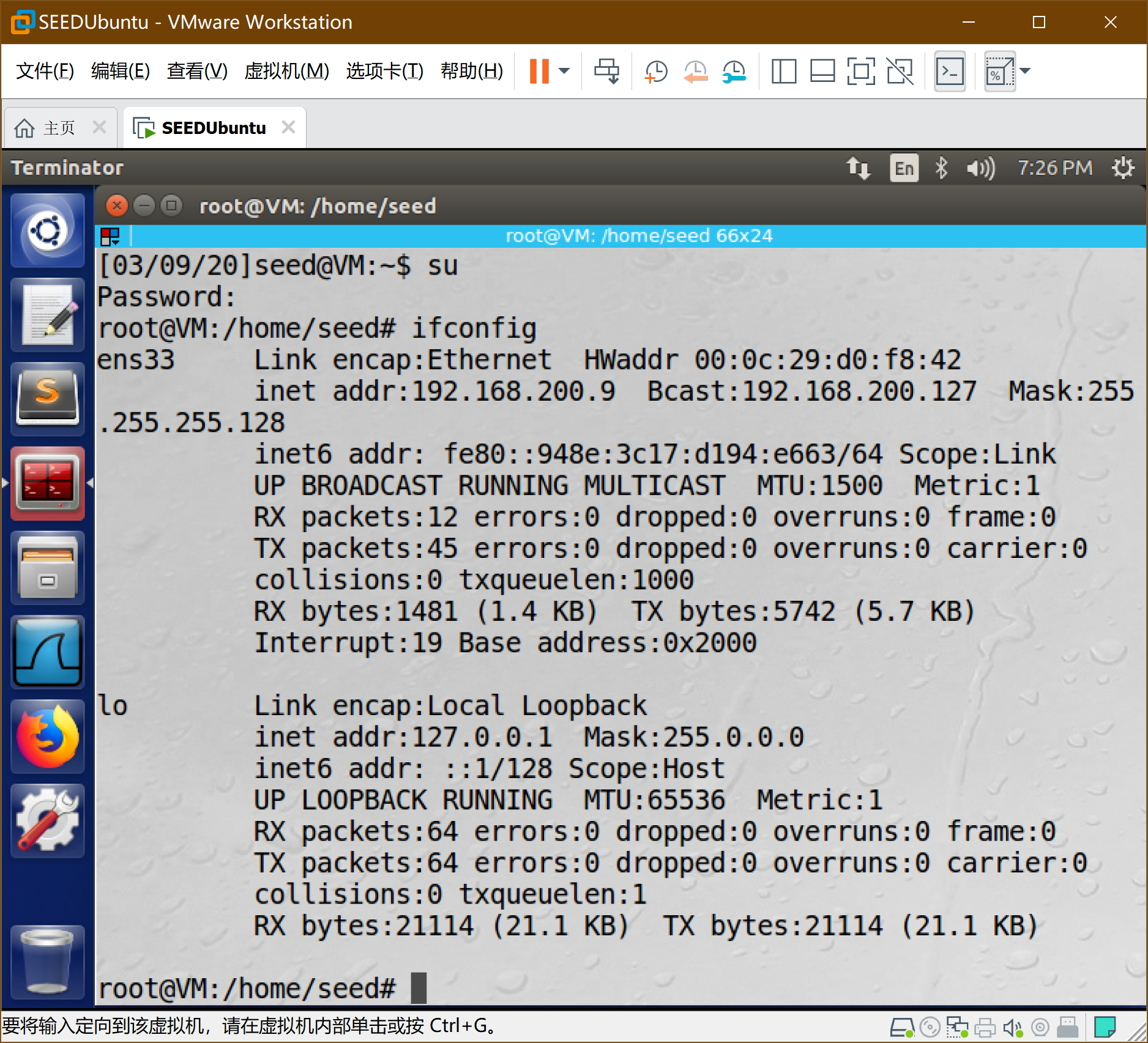
启动虚拟机,账户为seed 密码为dees,开机后通过su命令提权,密码为seedubuntu,ifconfig查看相关网络信息。
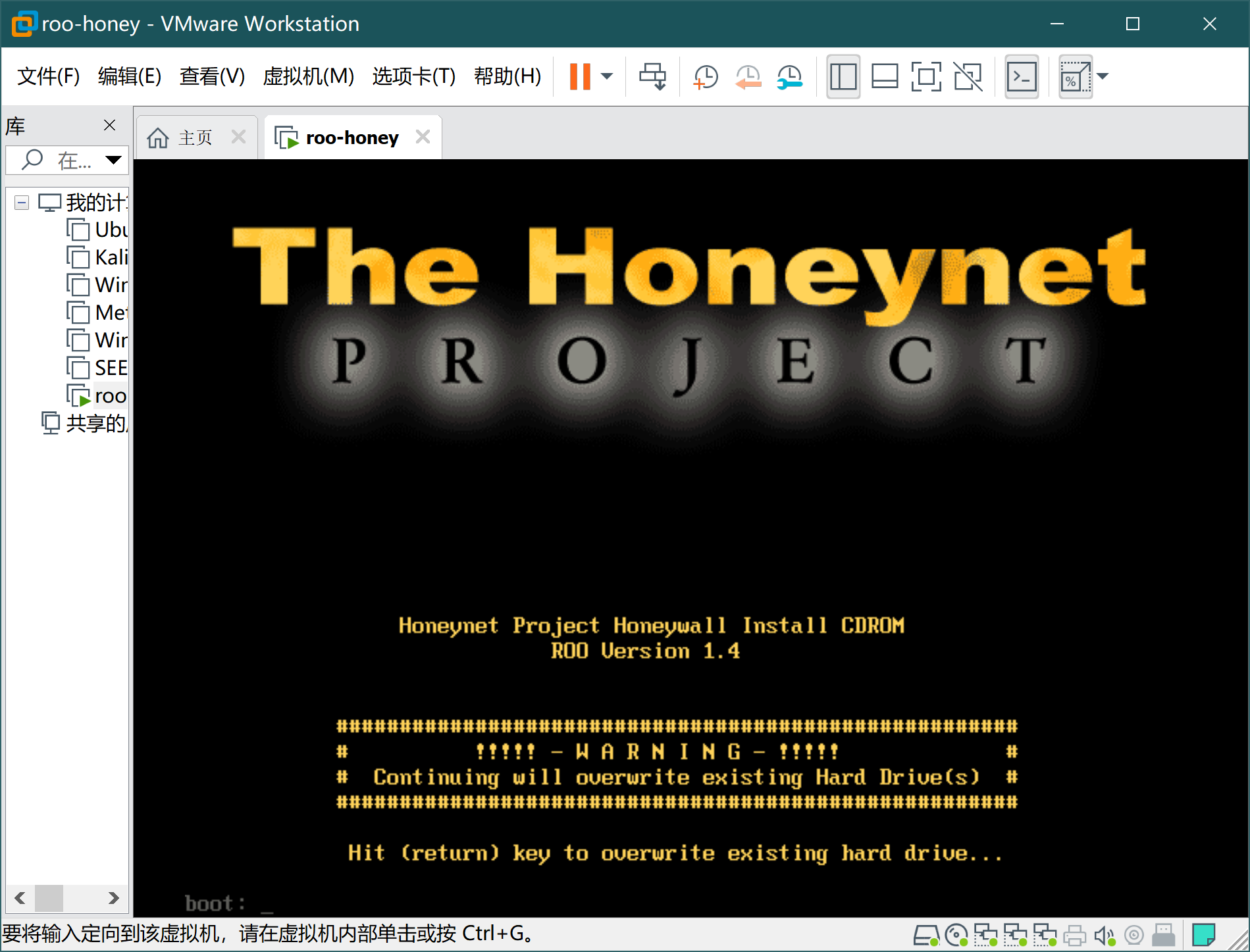
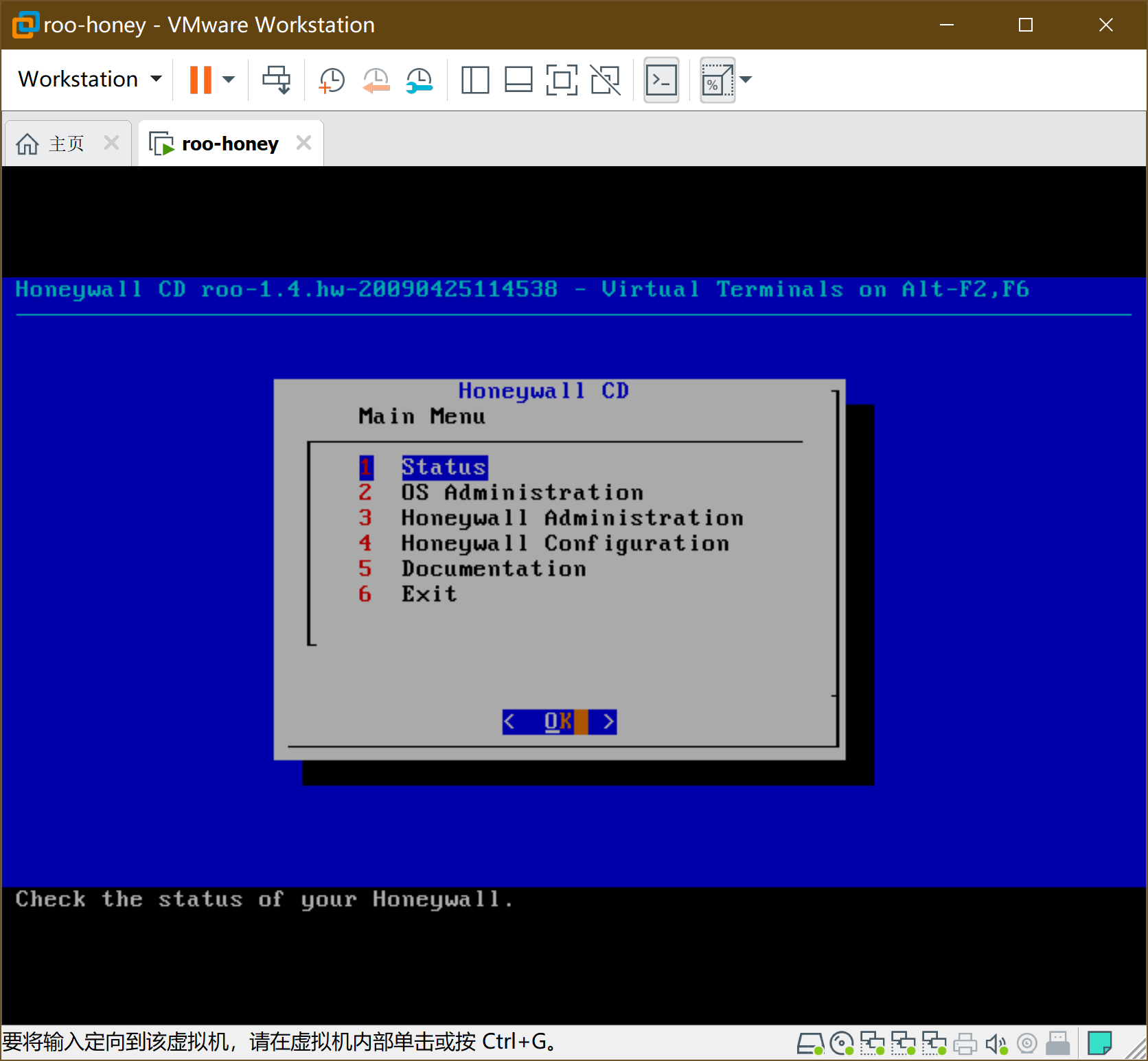
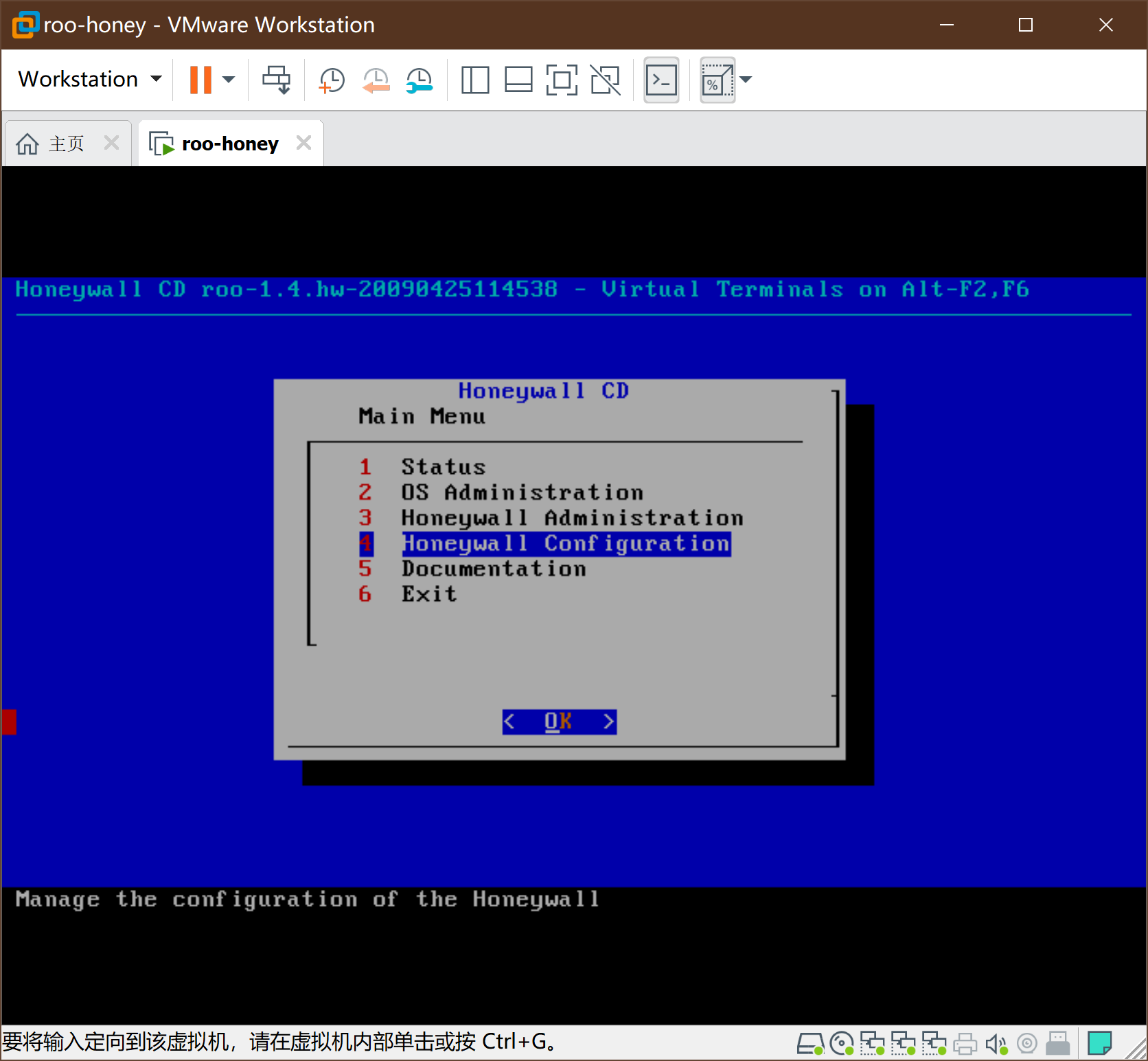
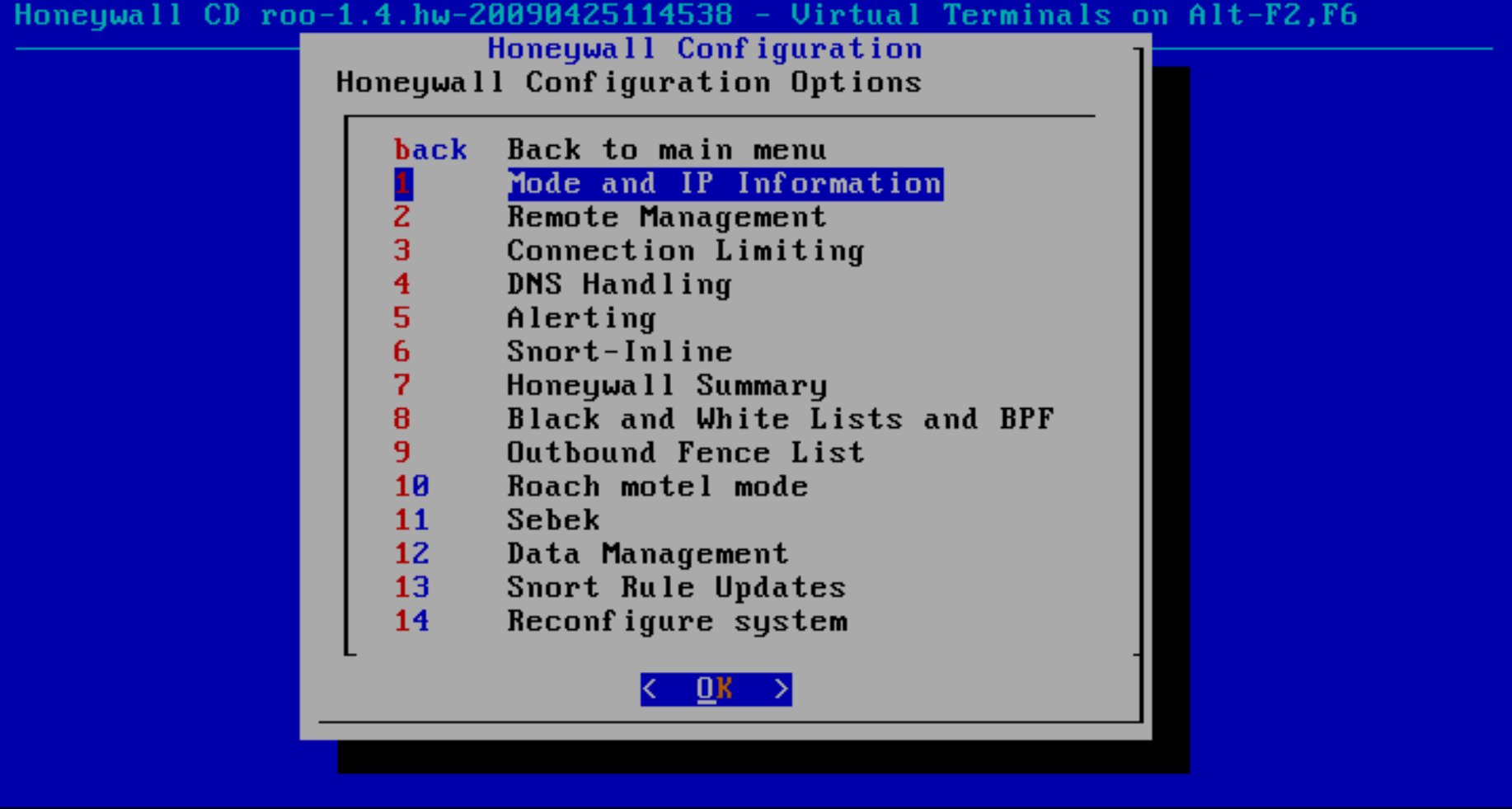
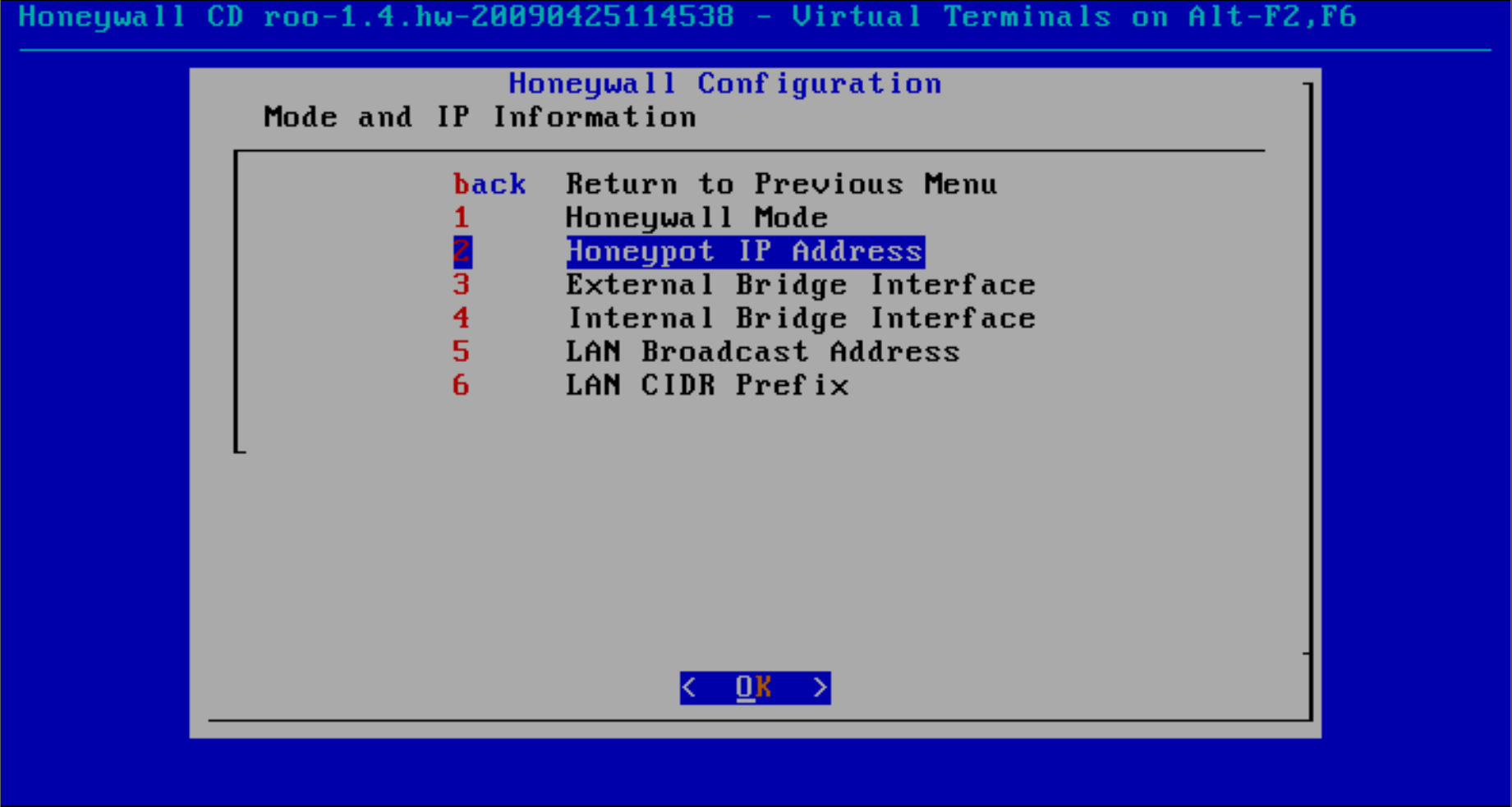
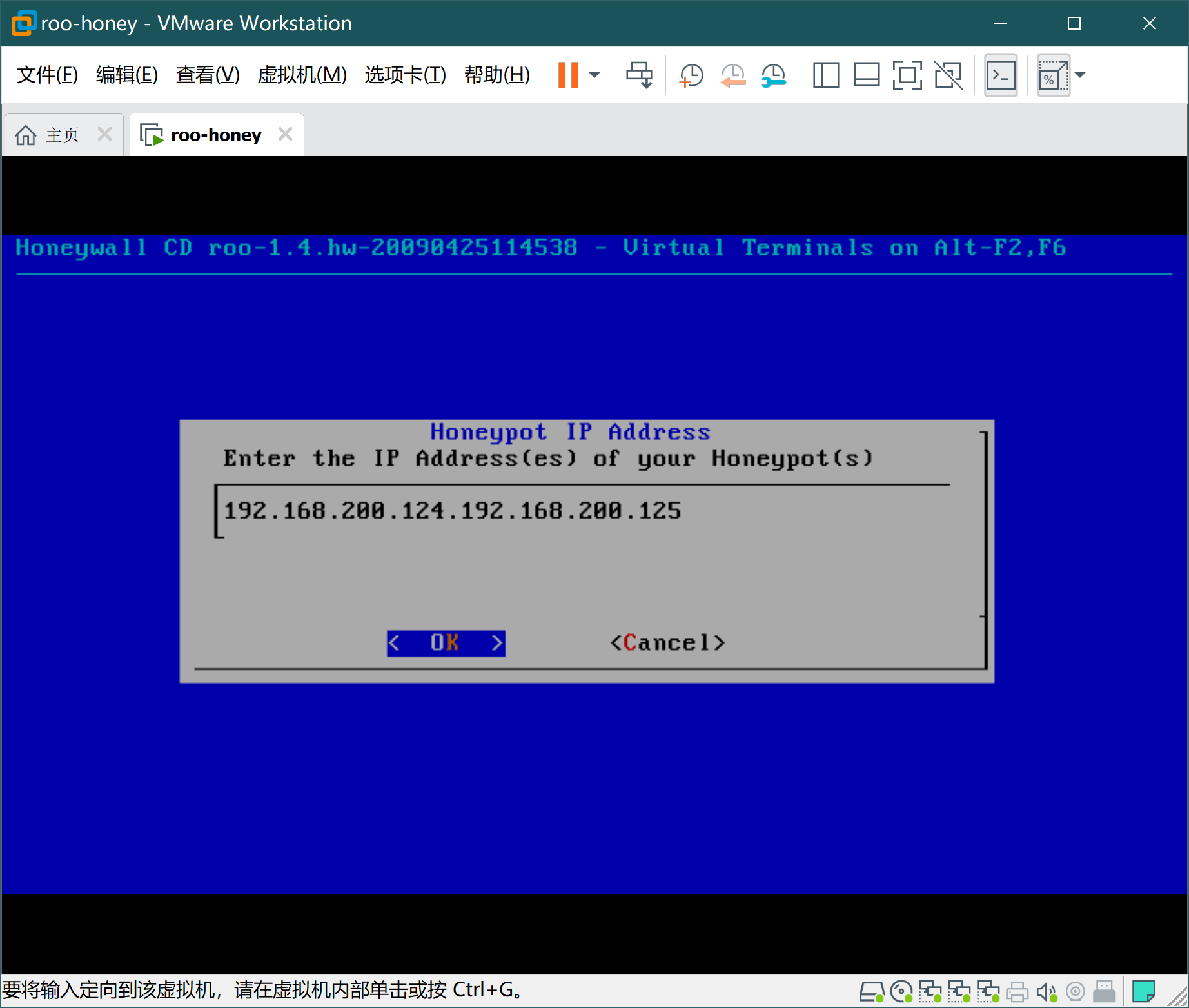
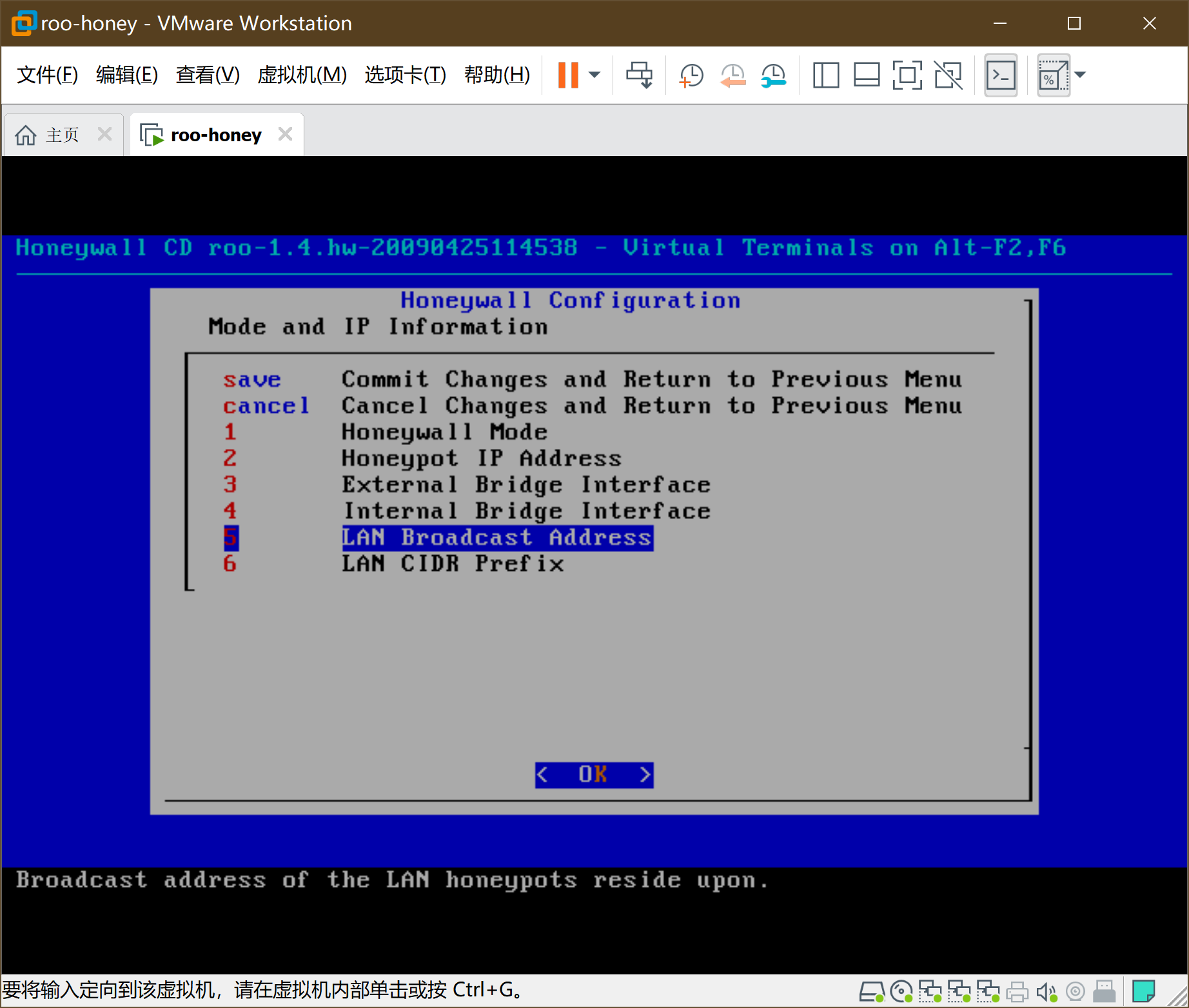
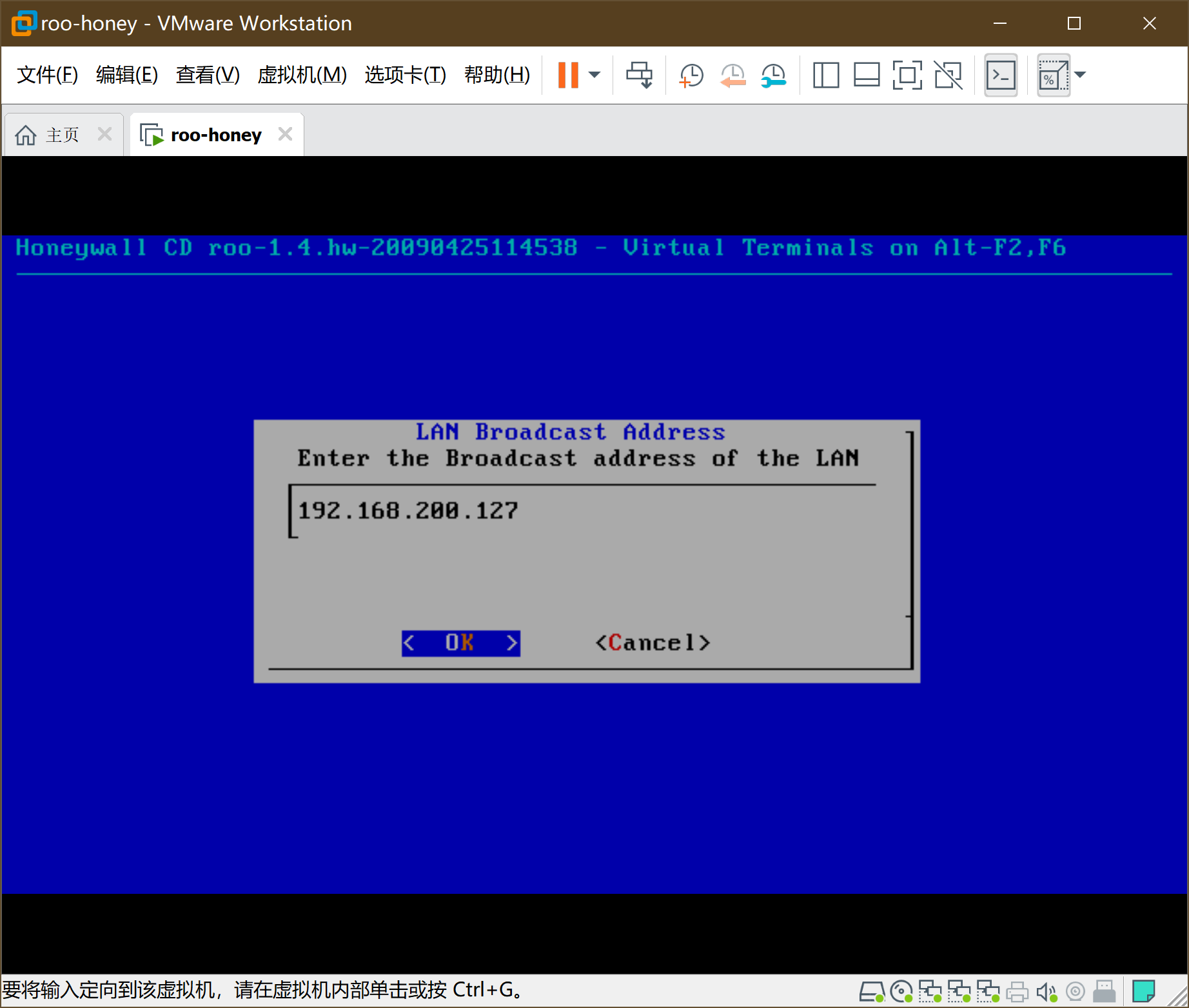
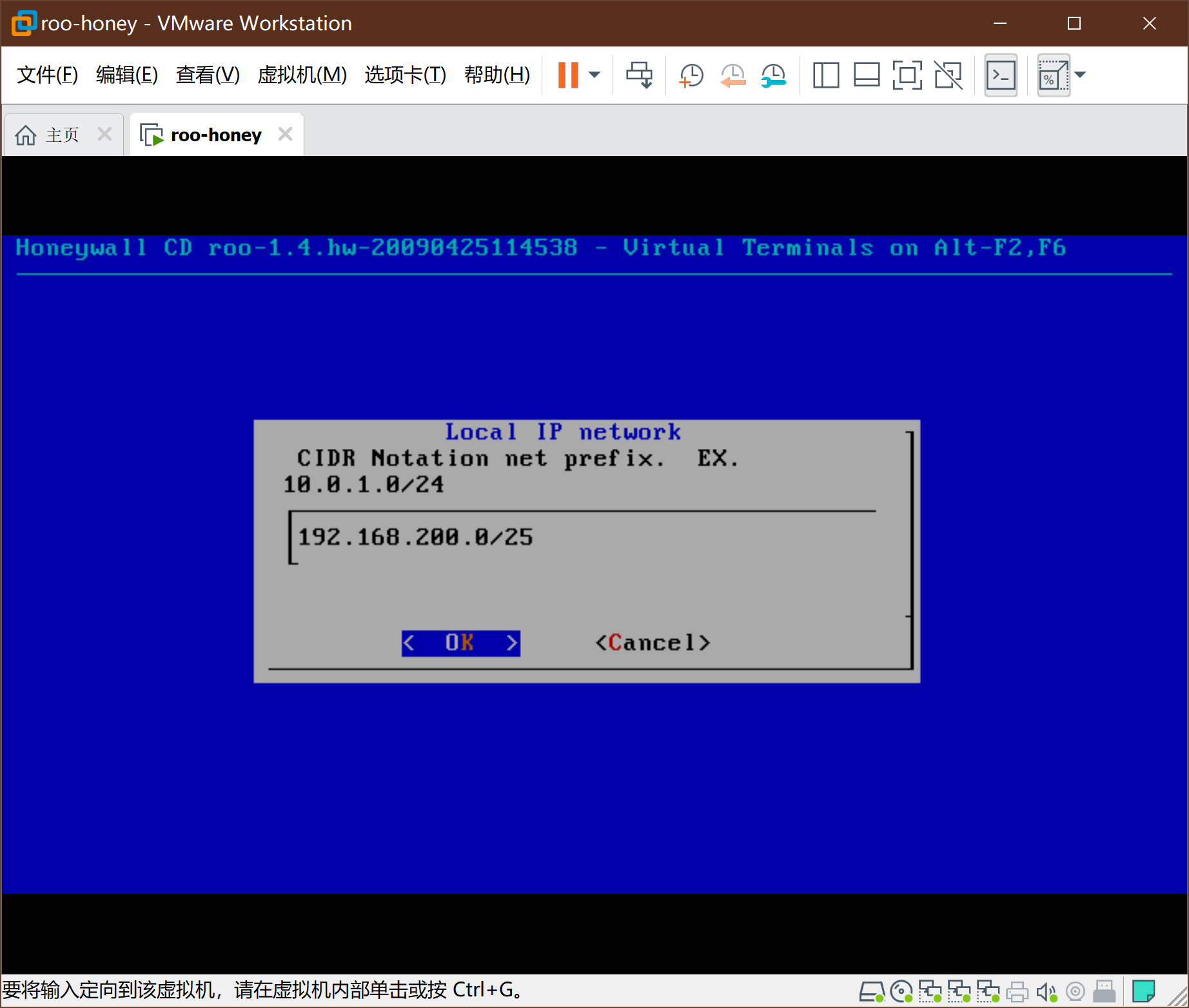
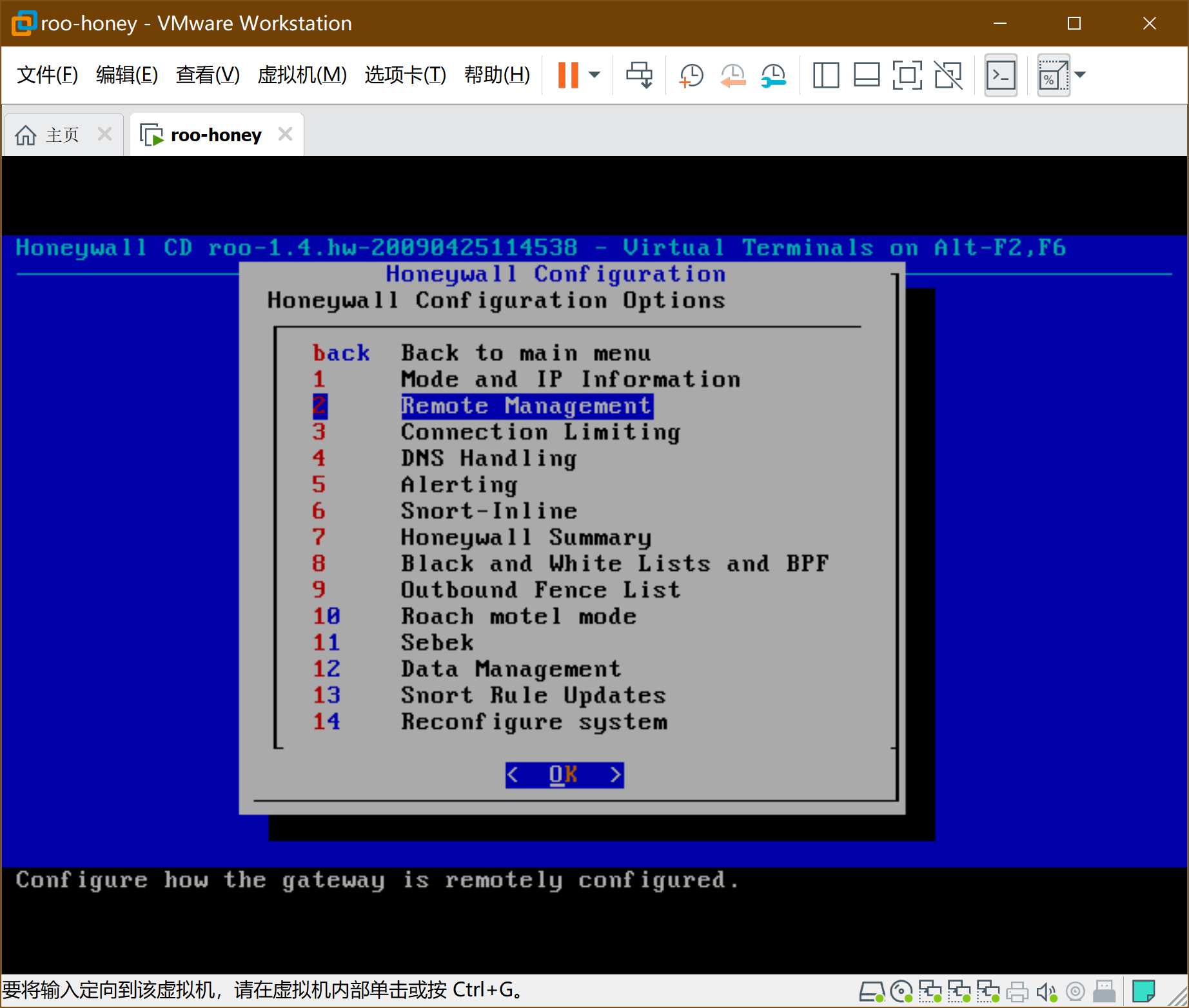
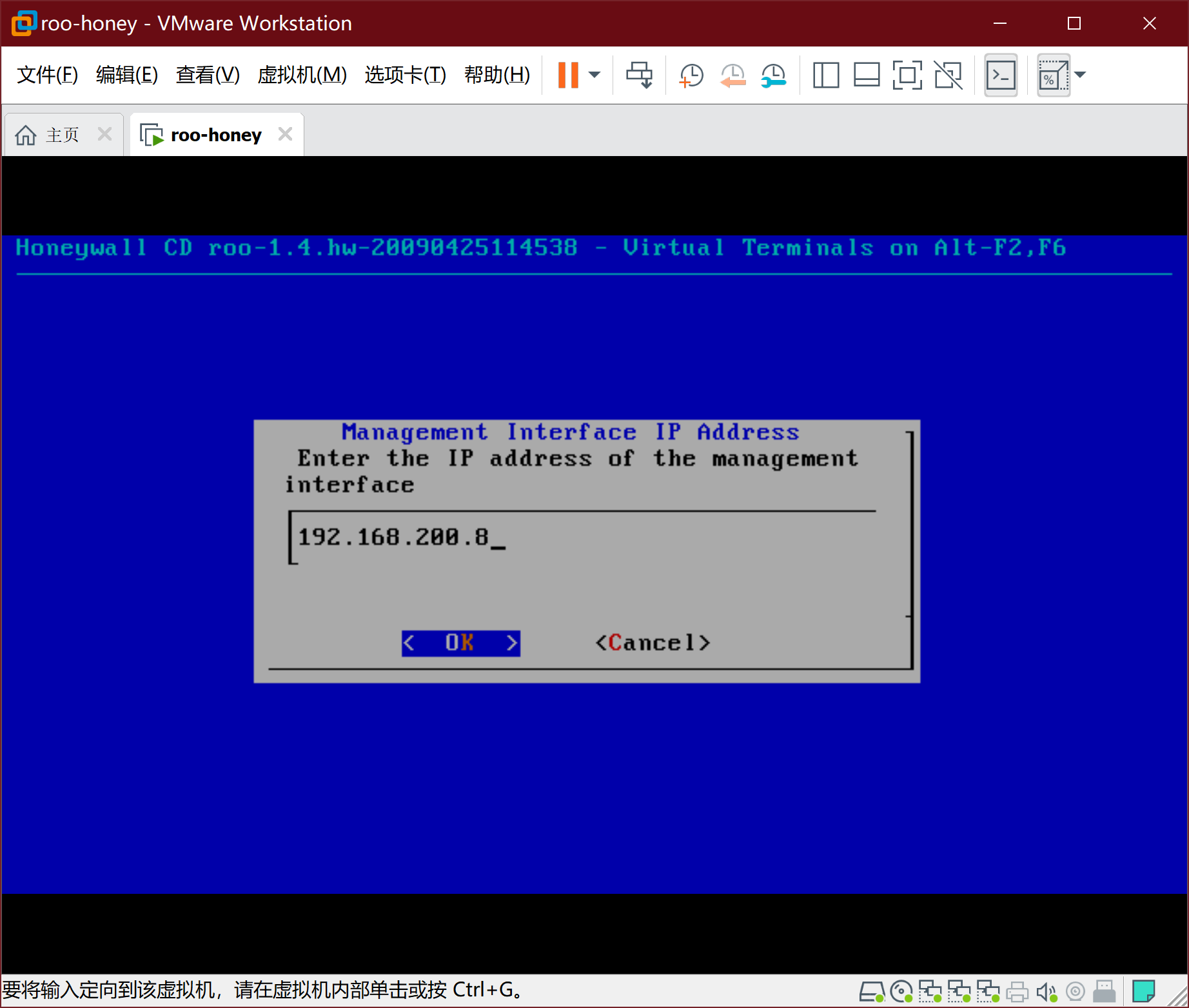
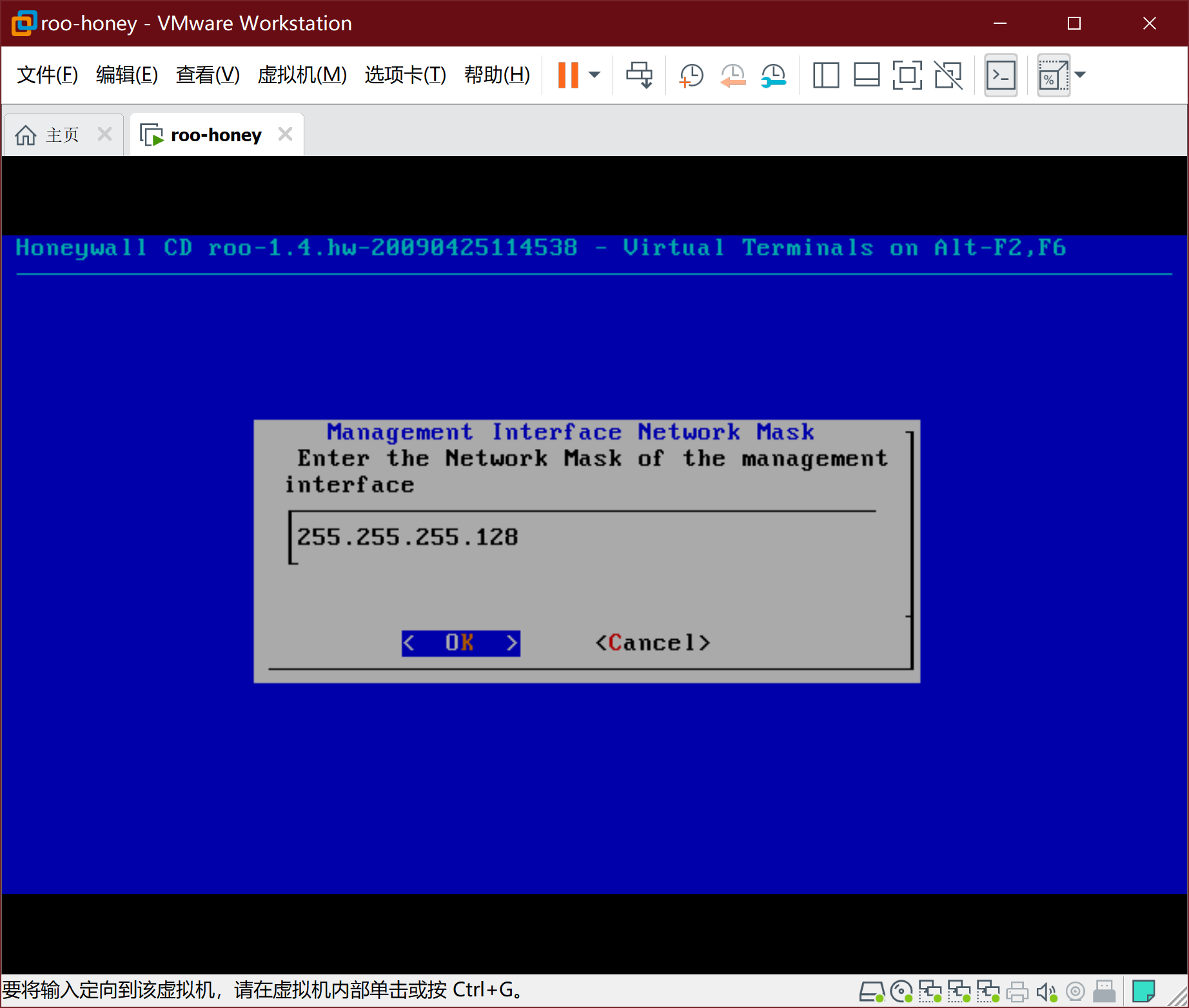
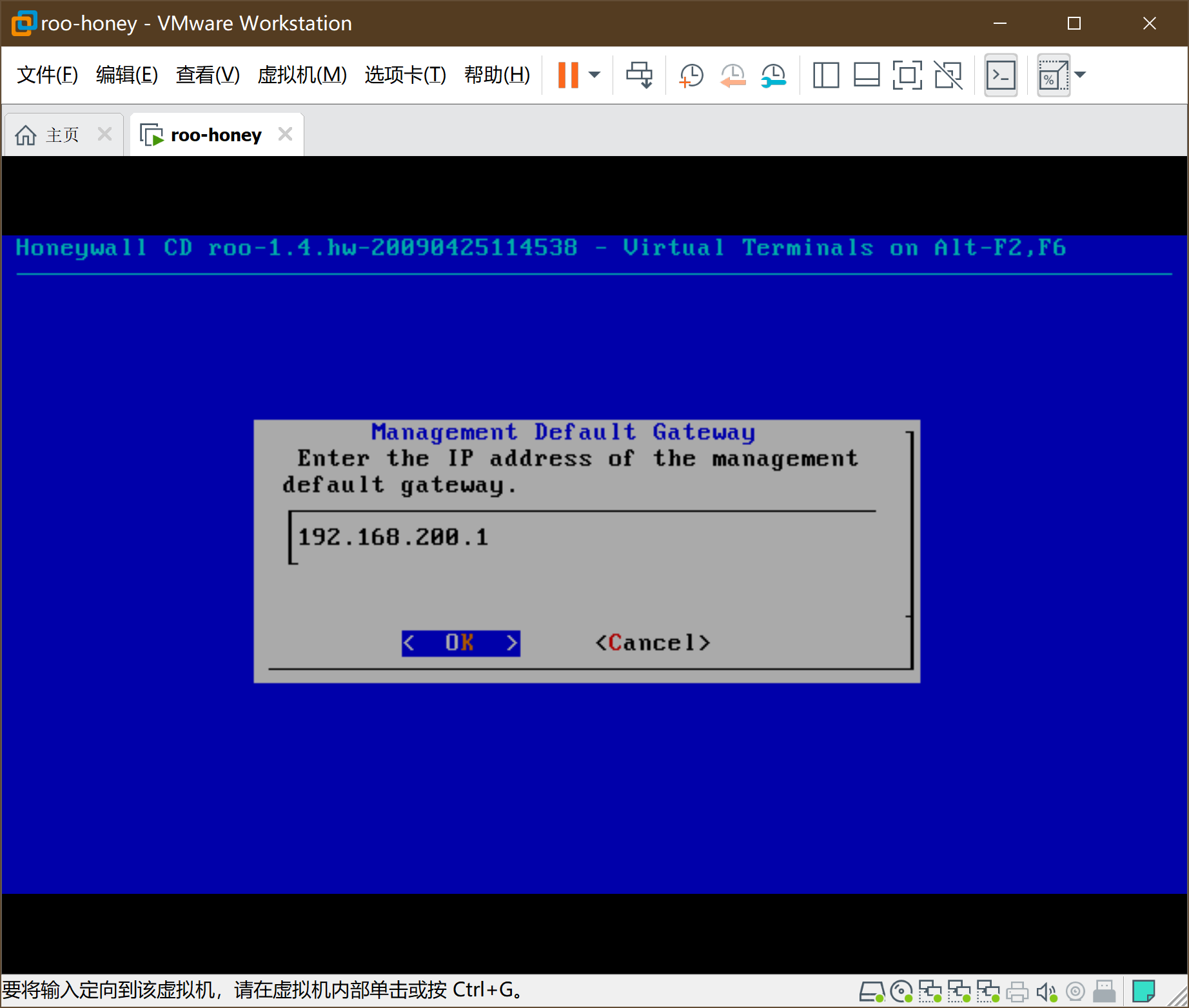
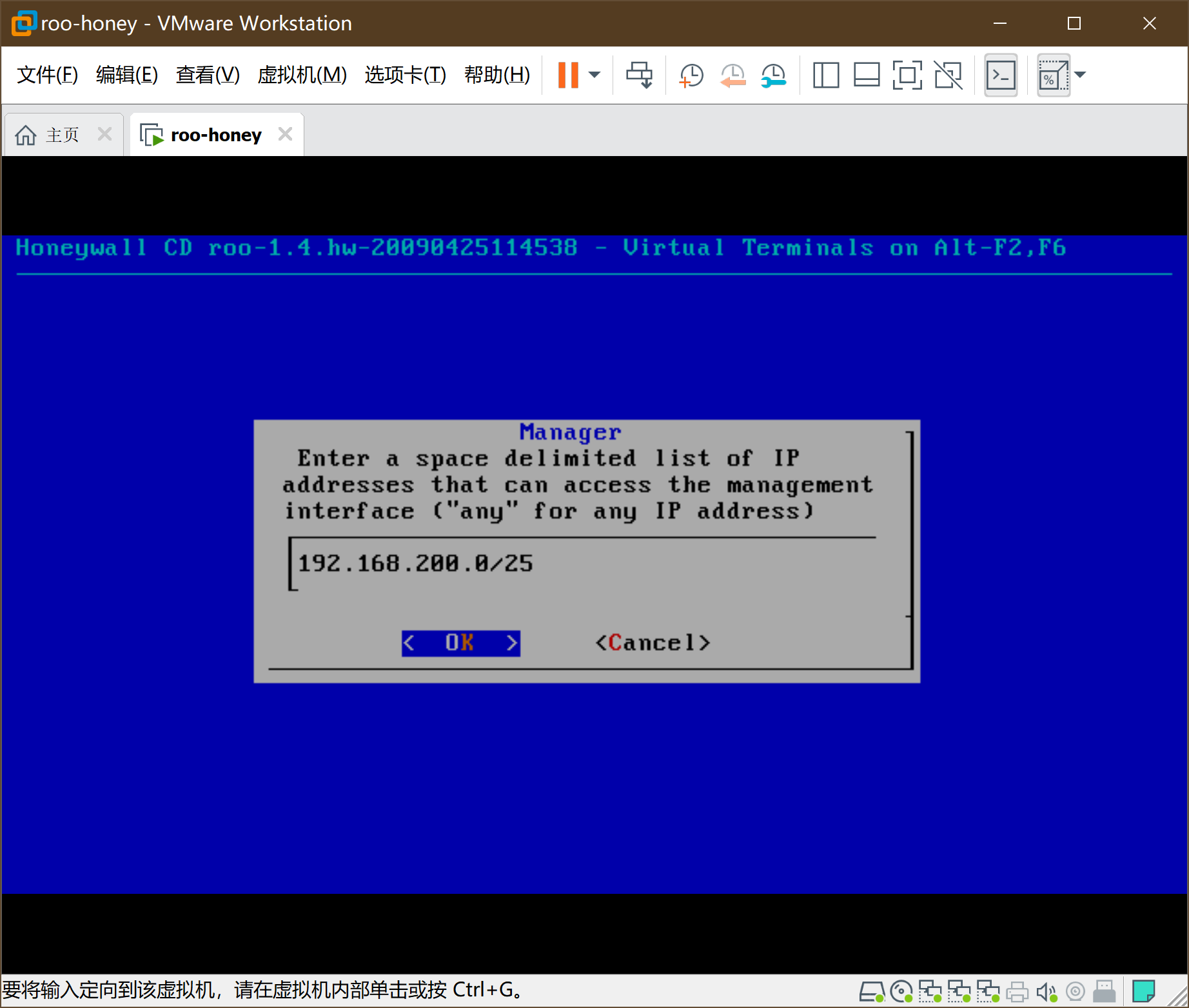
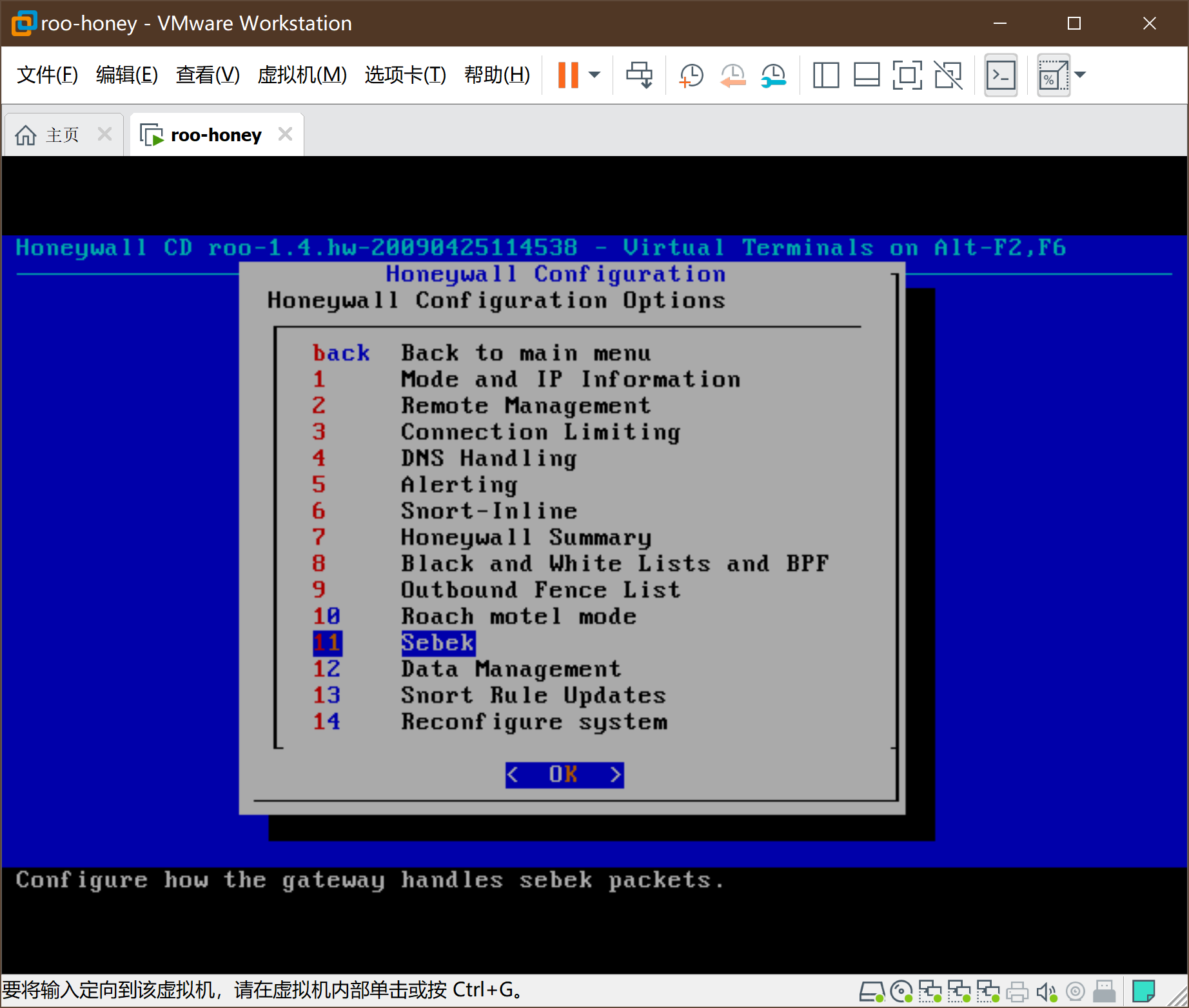
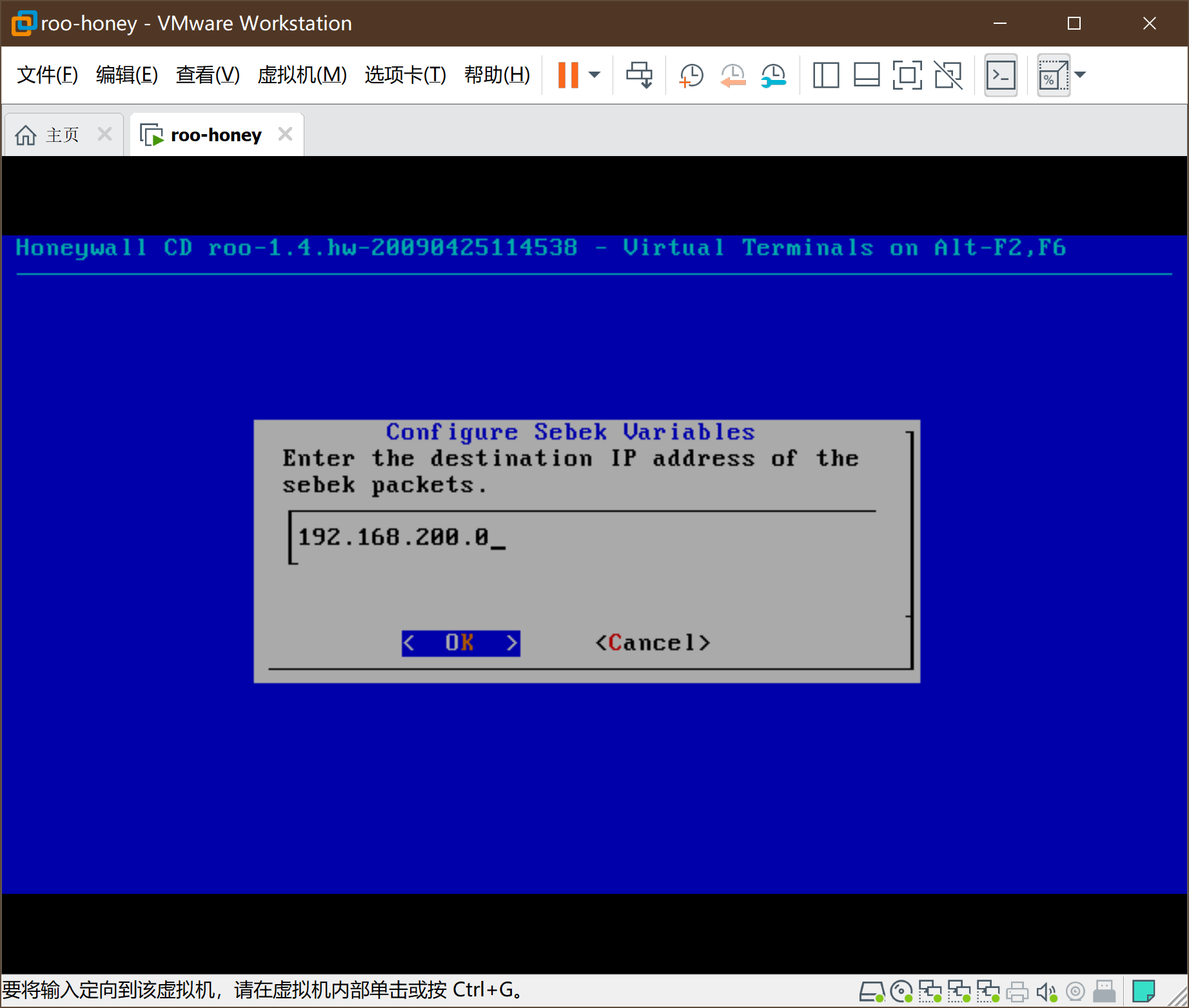
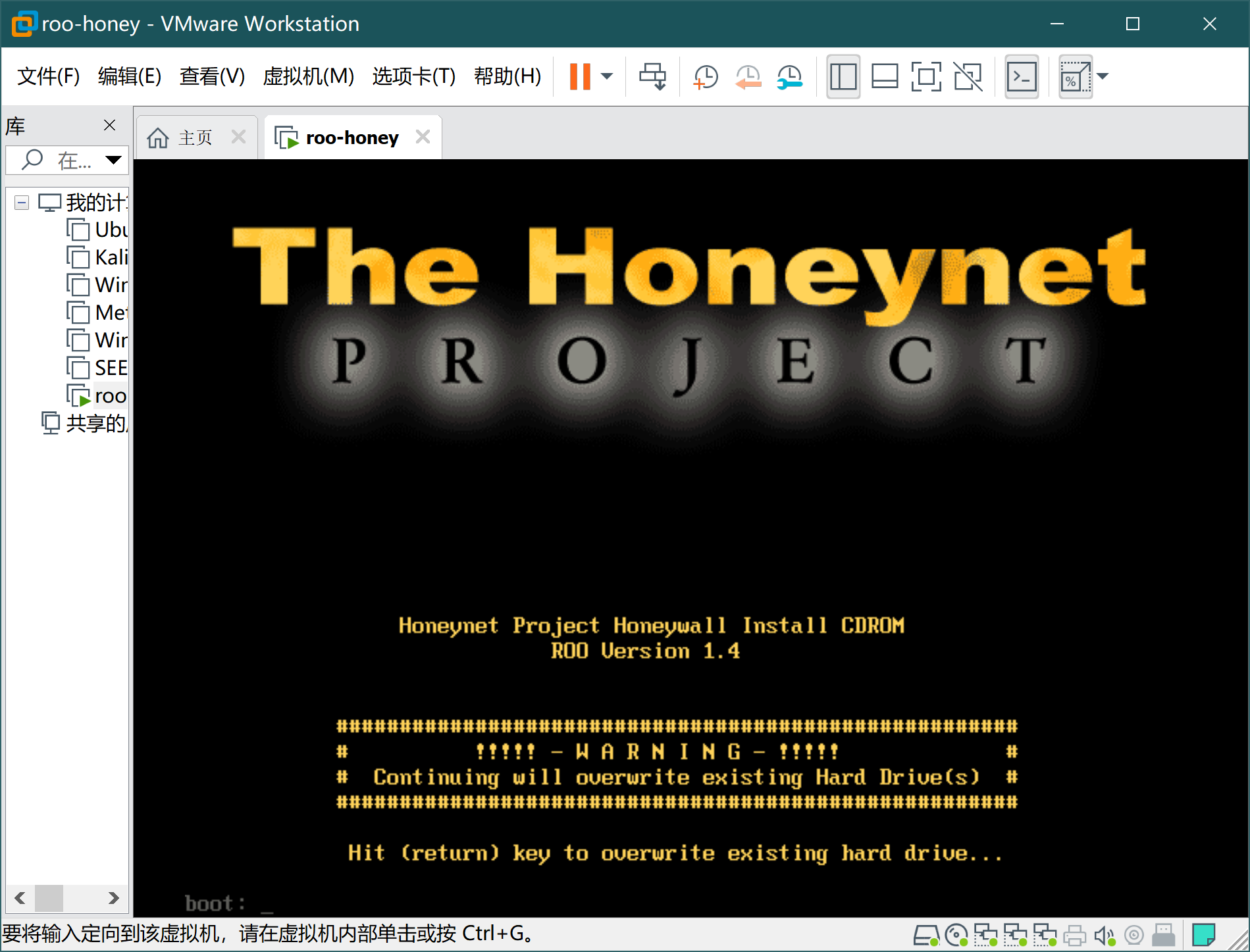
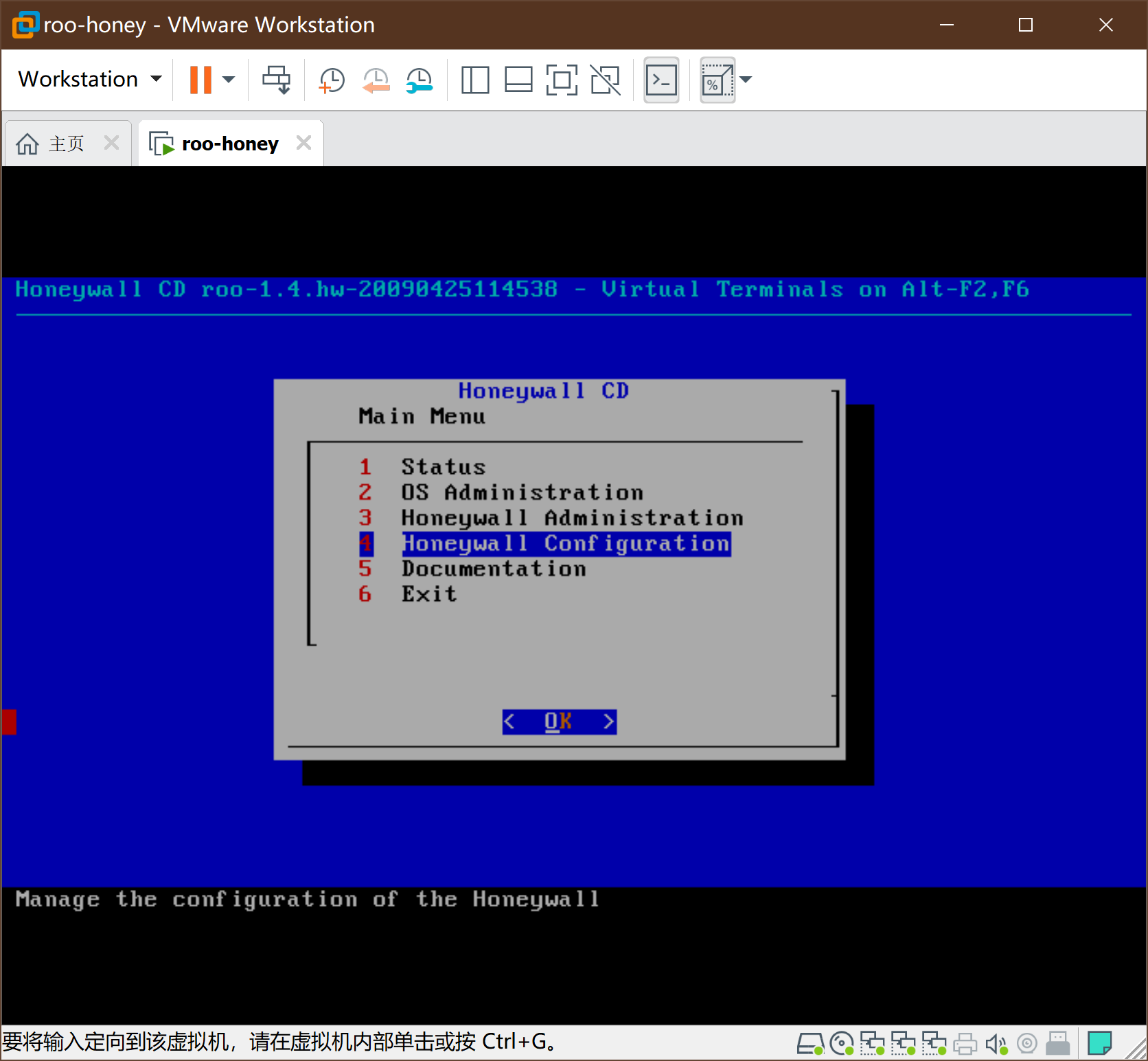
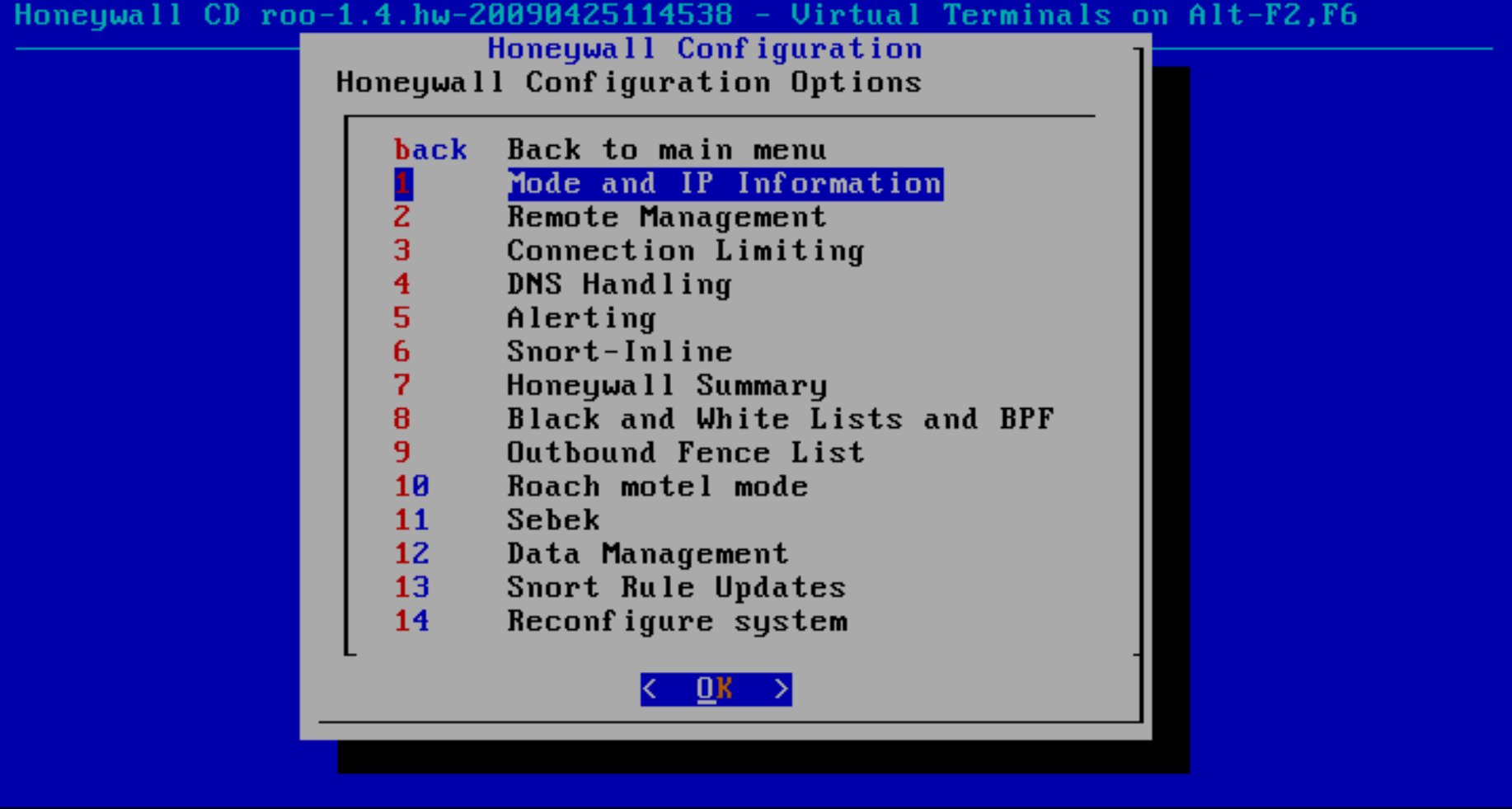
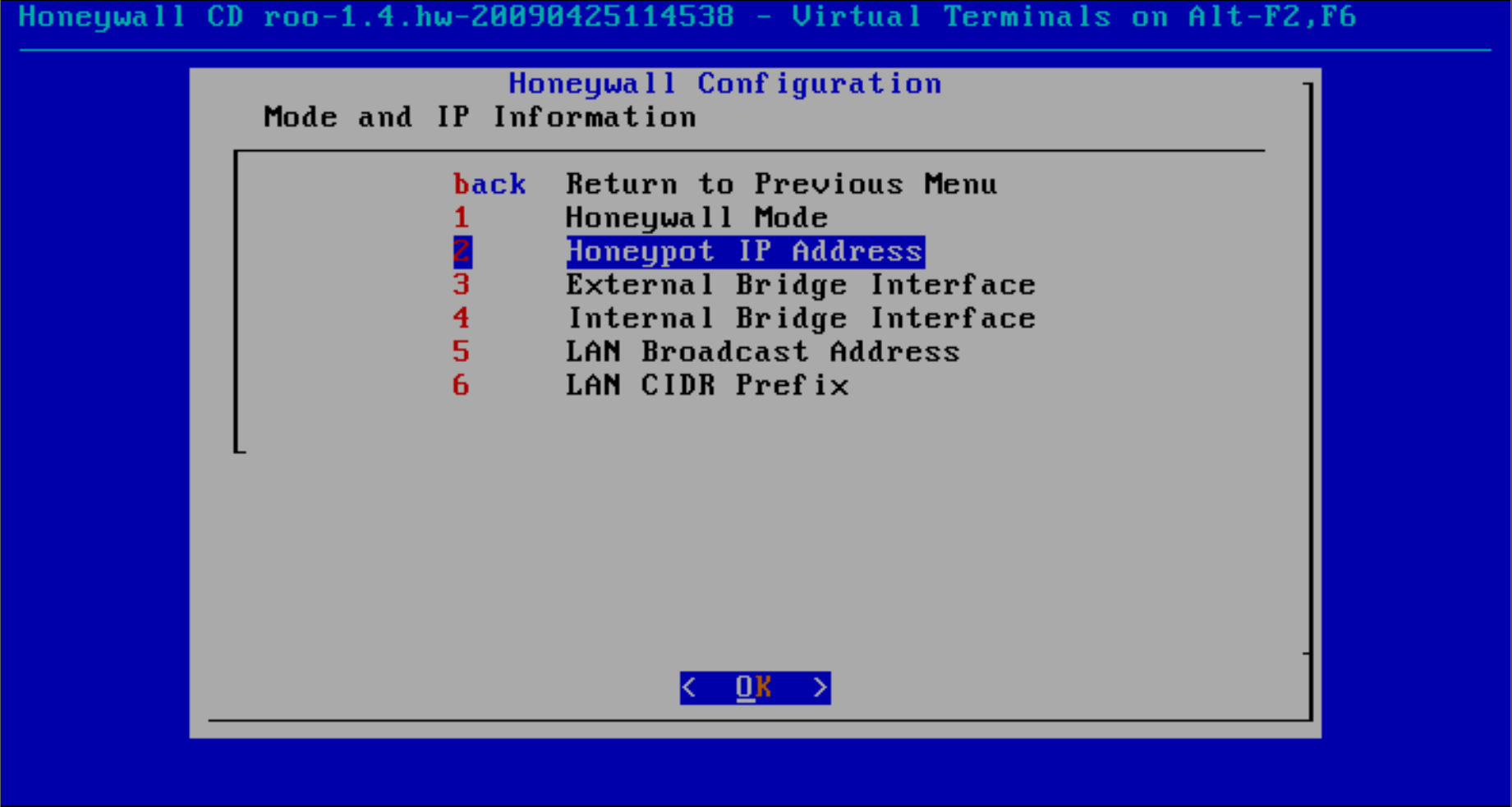
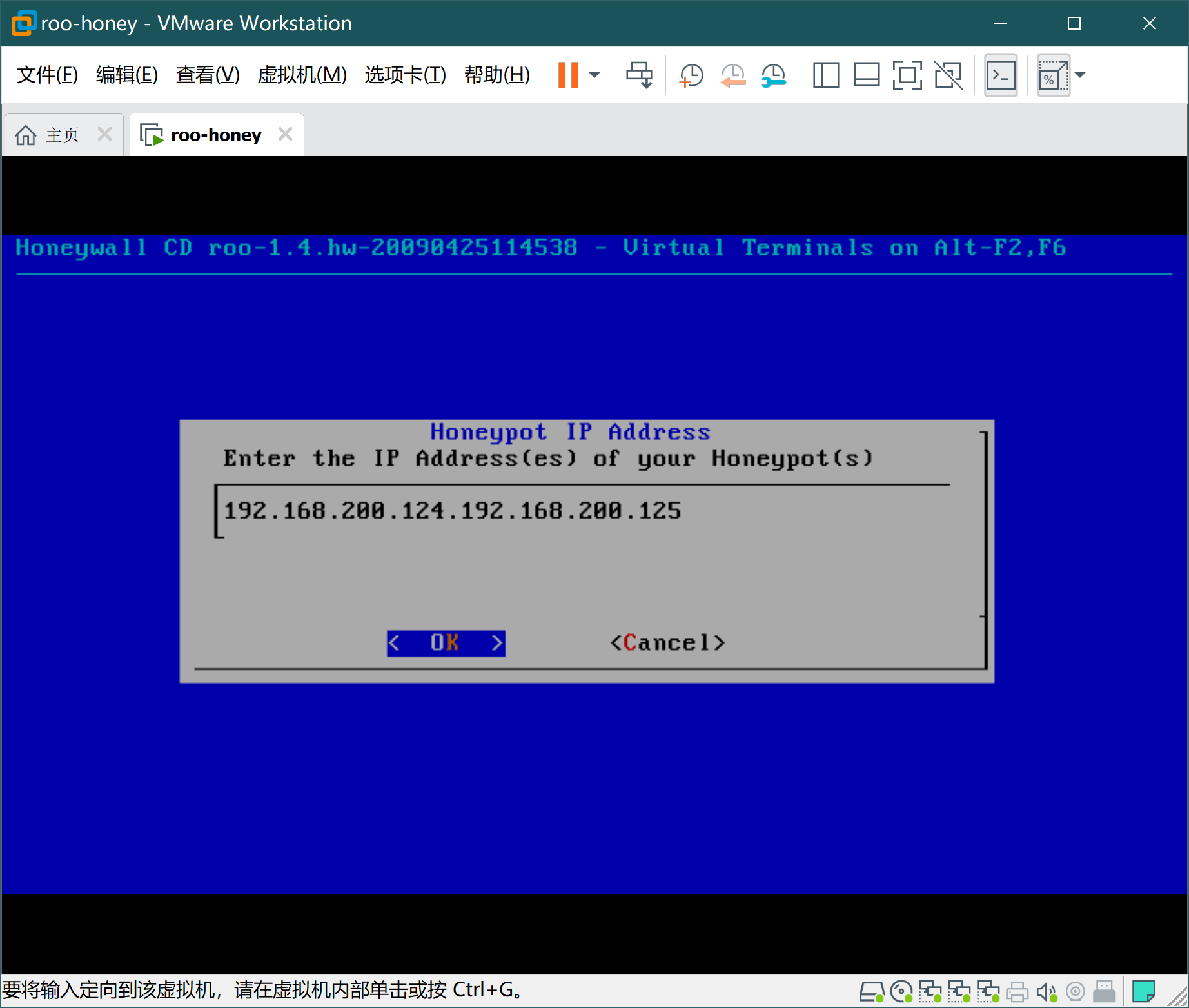
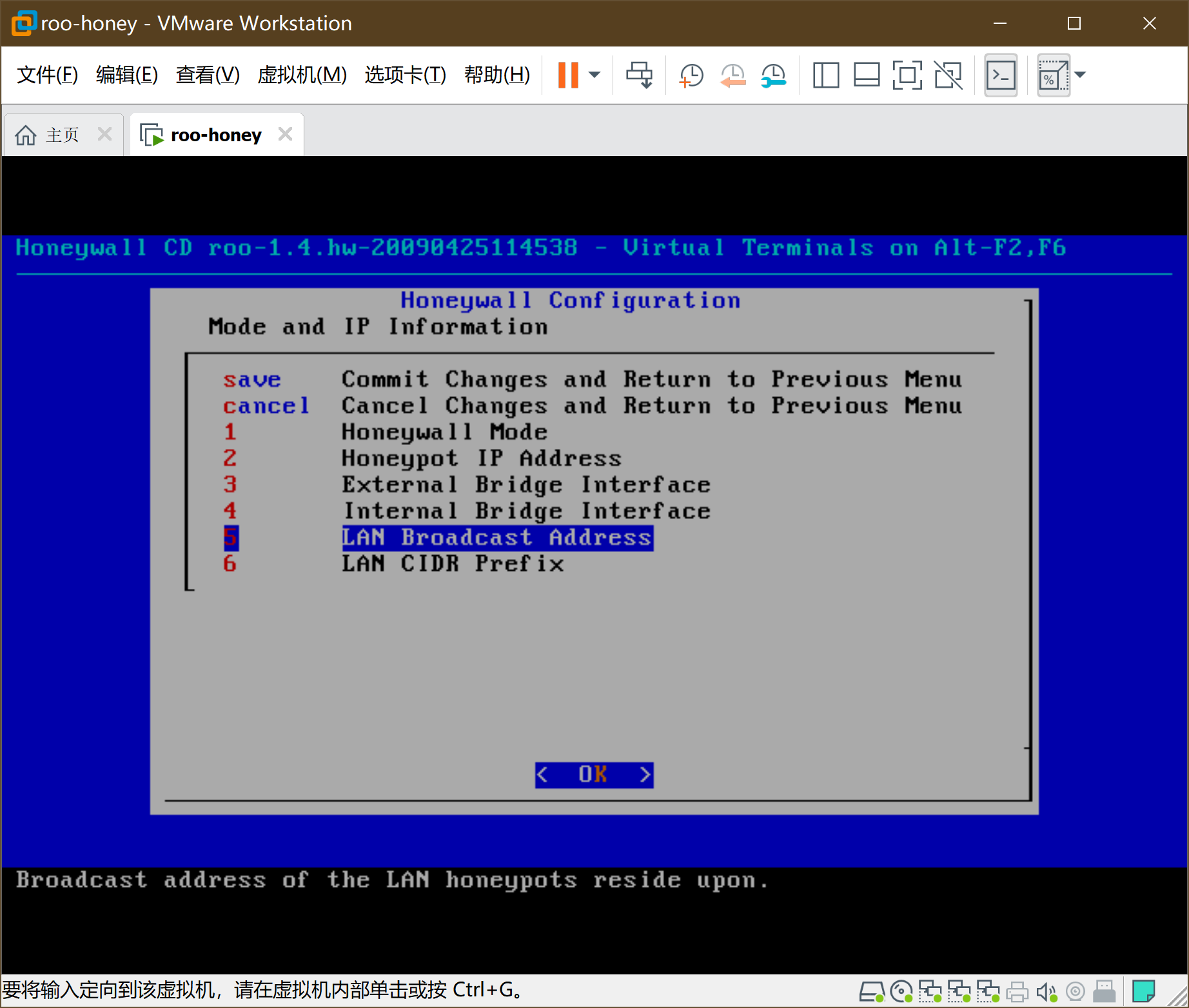
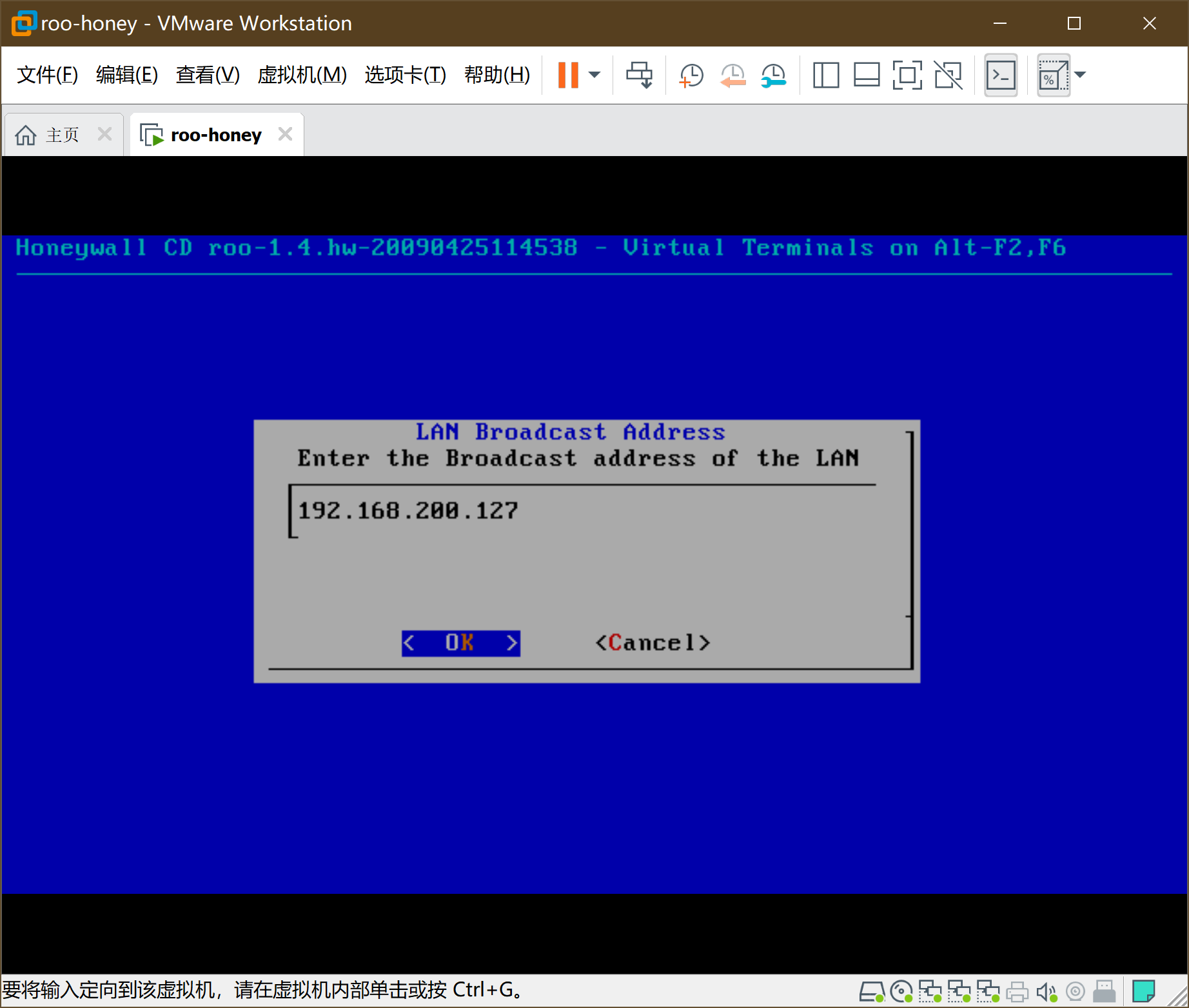
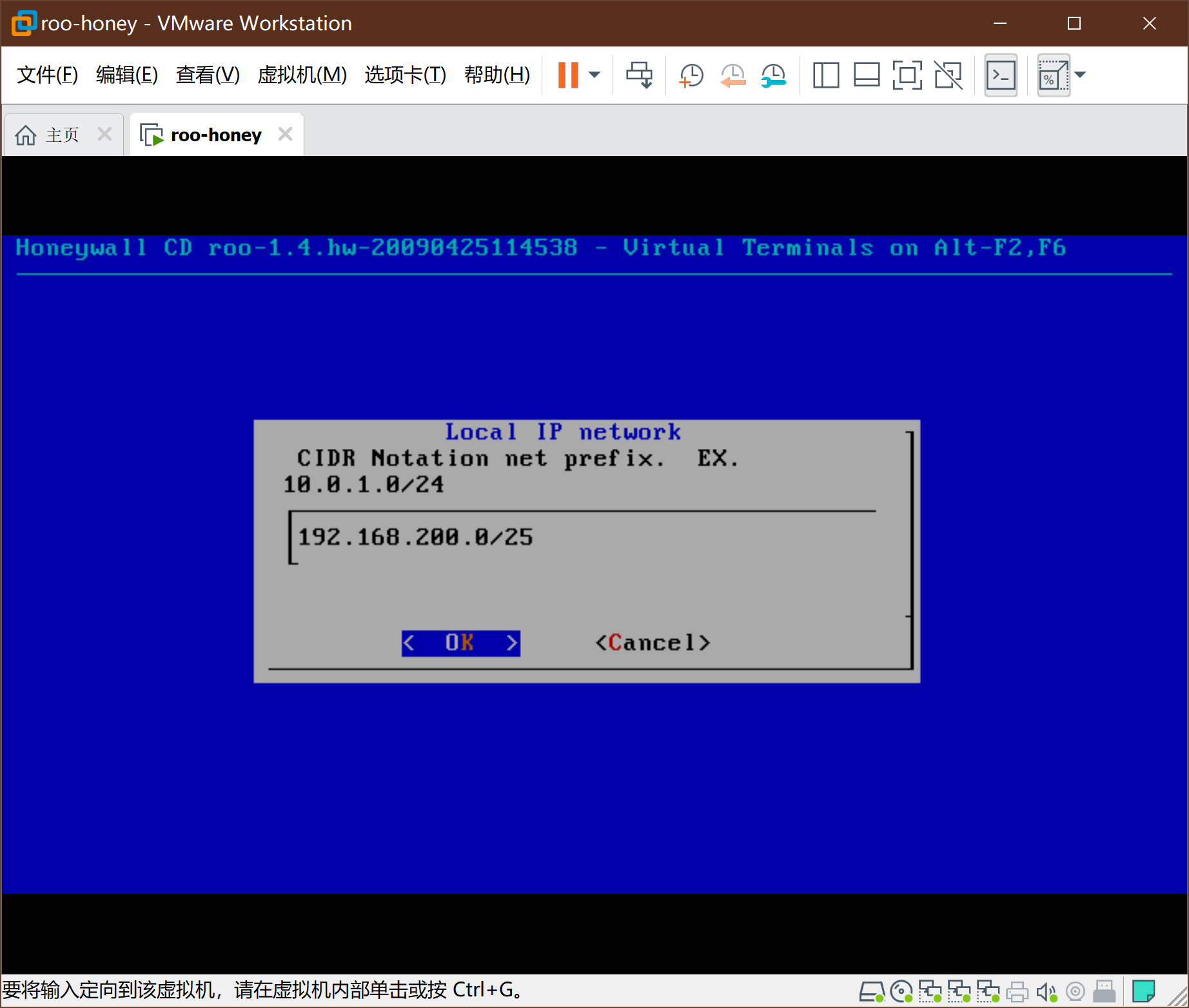
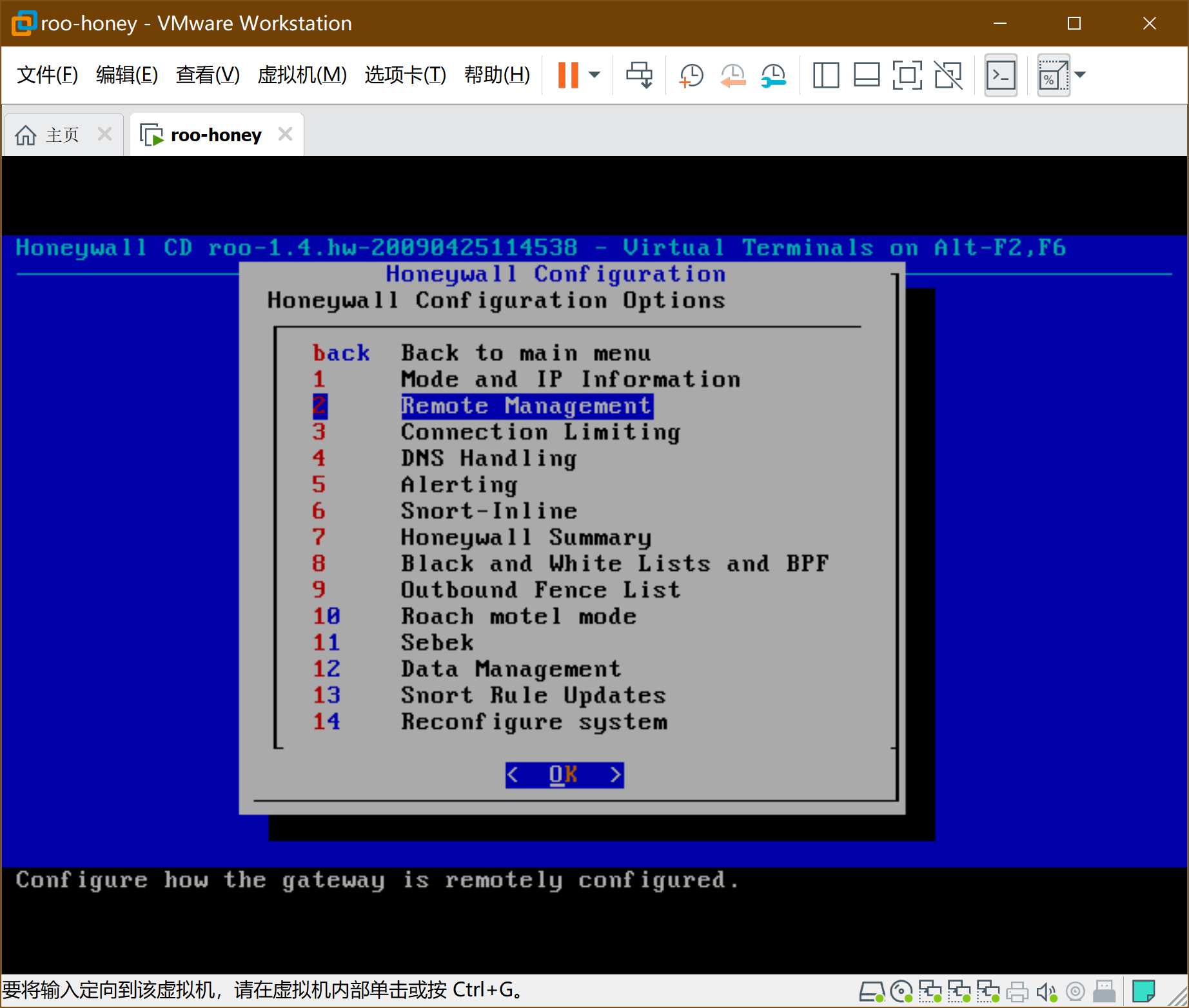
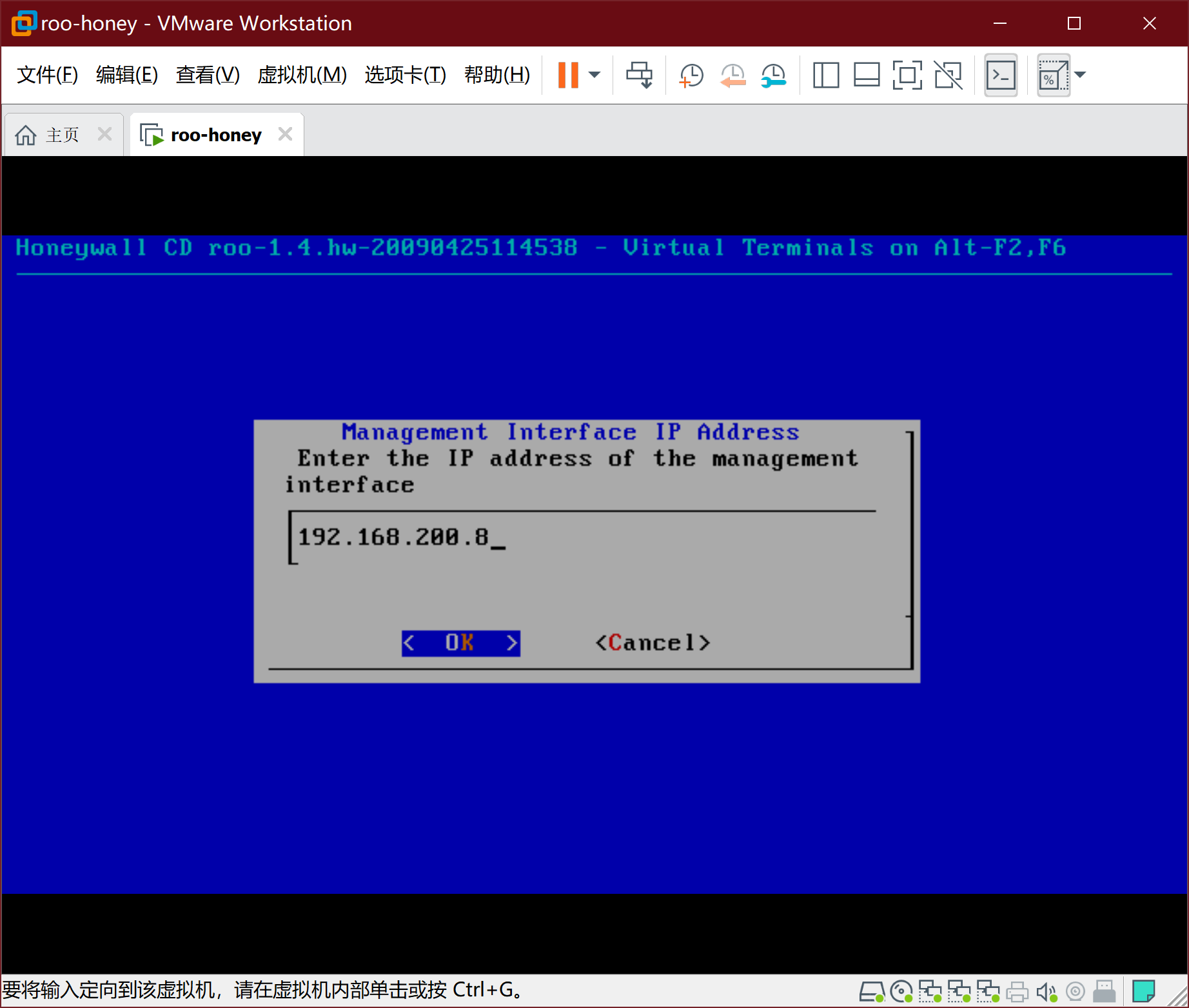
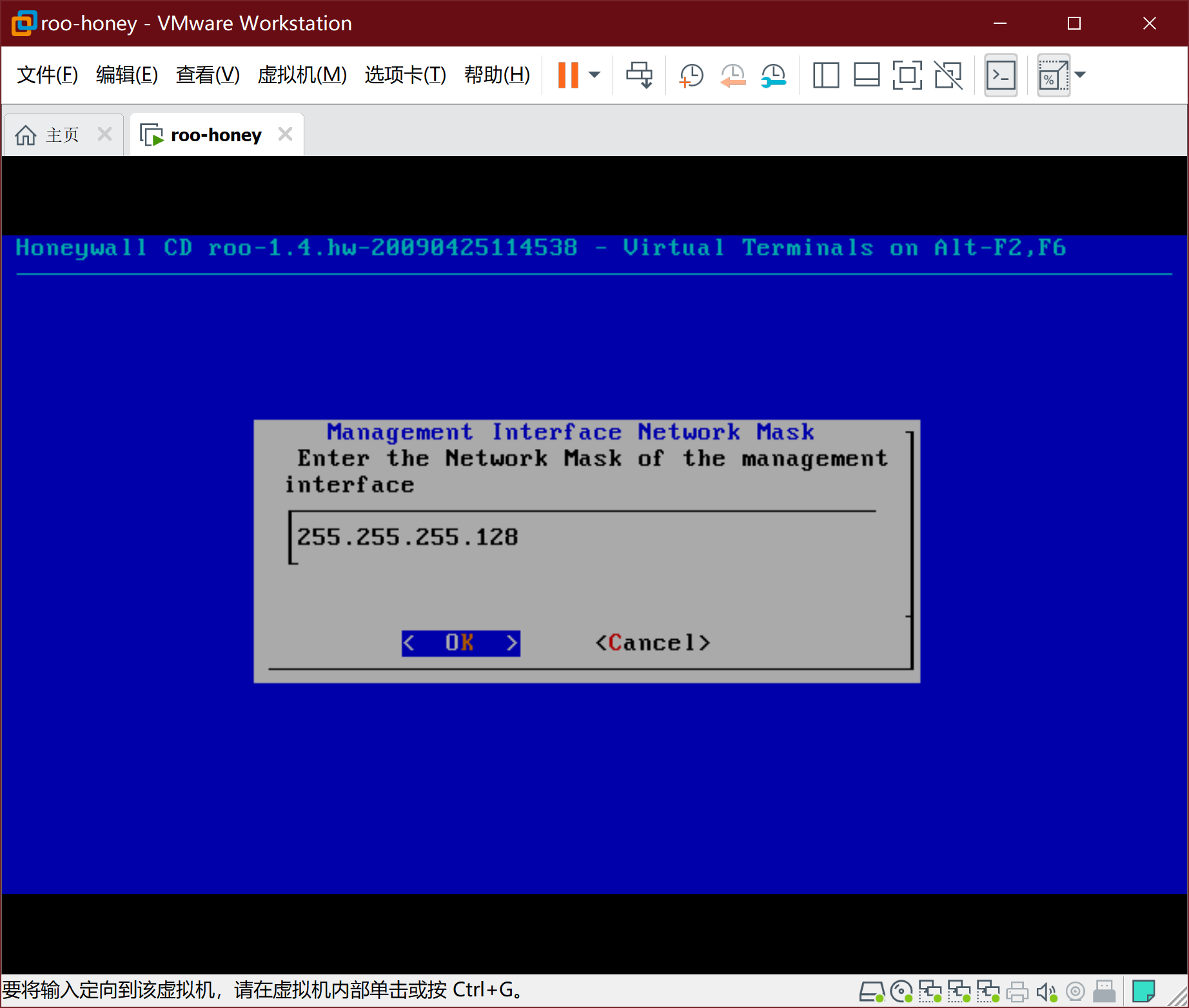
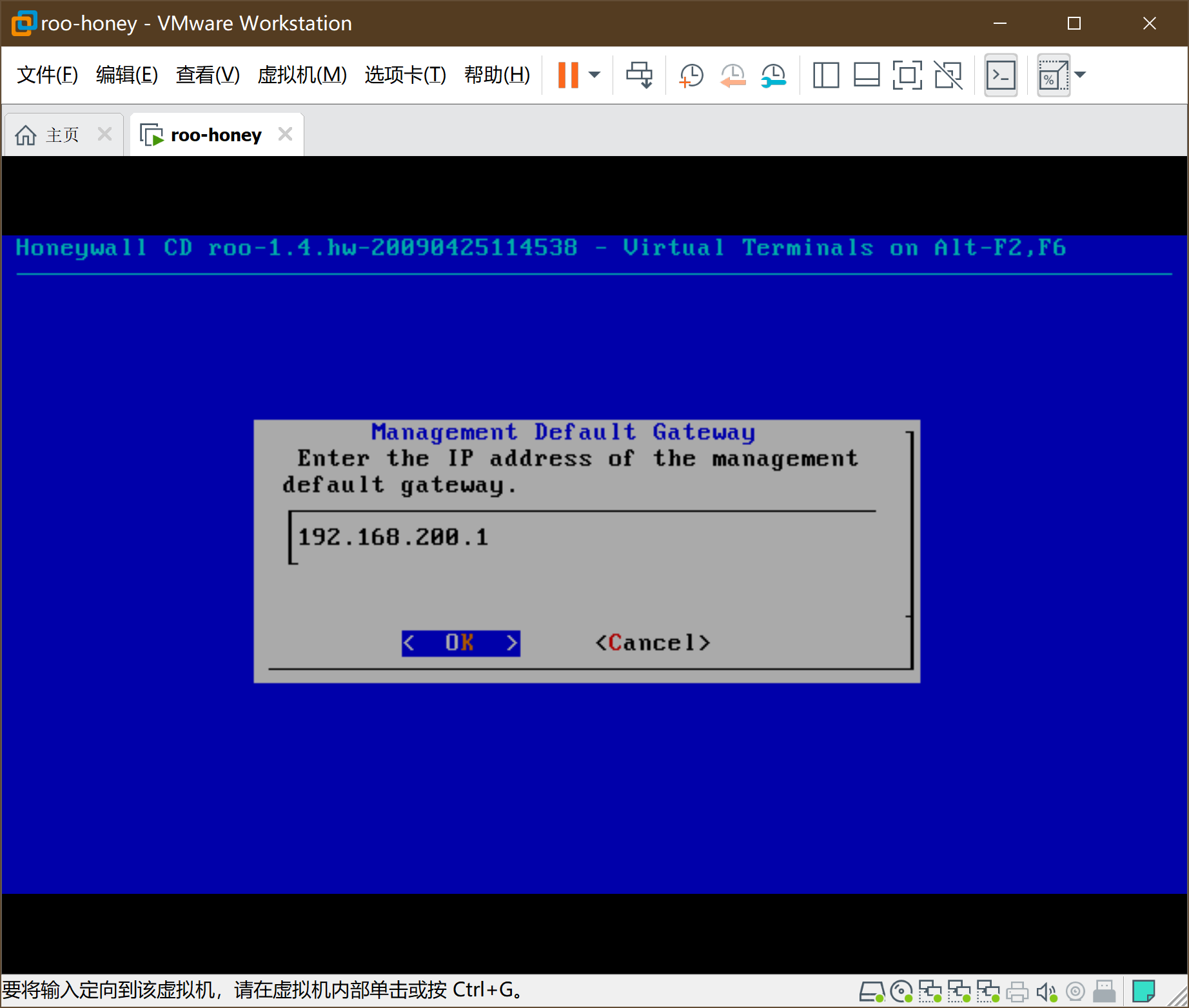
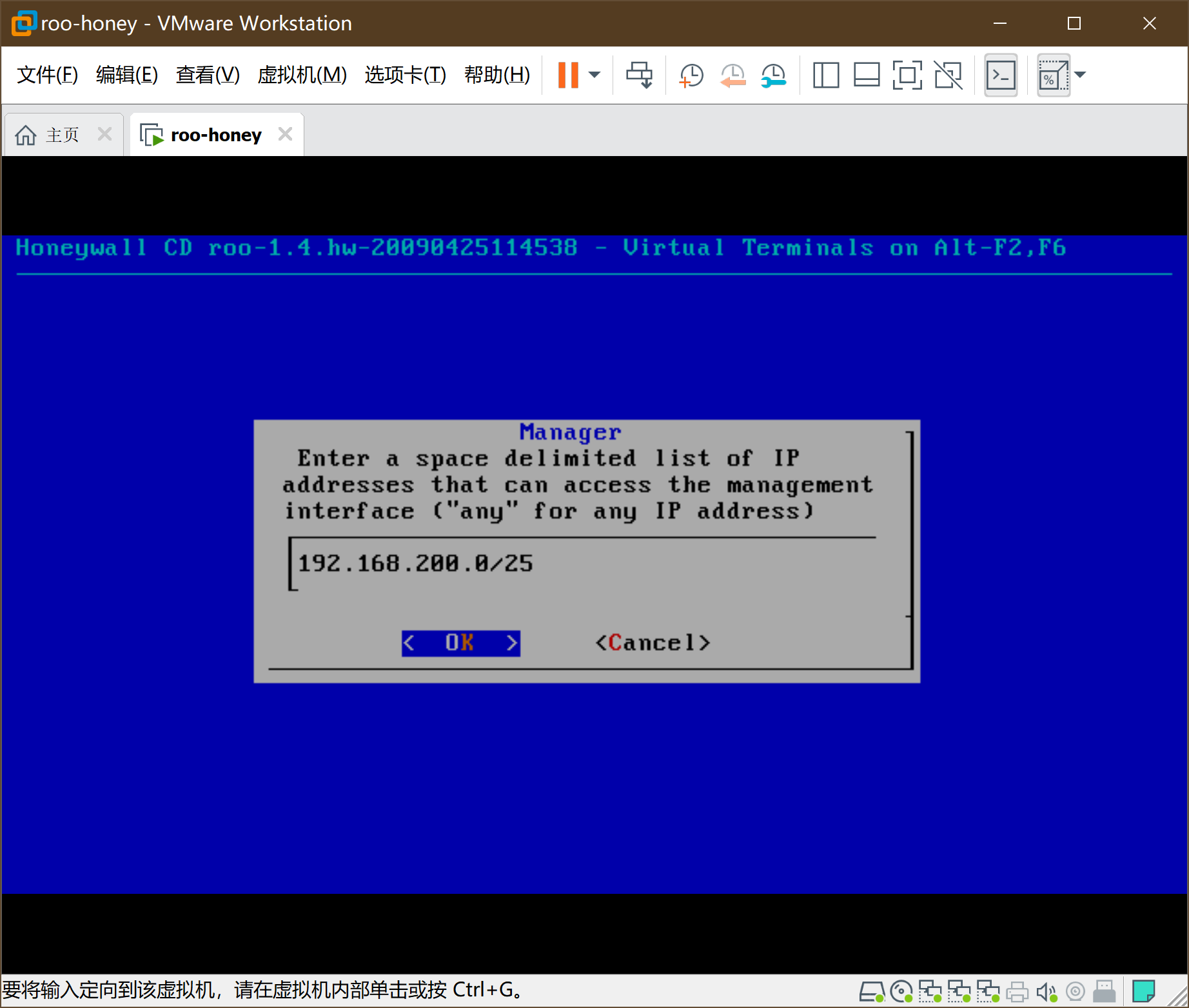
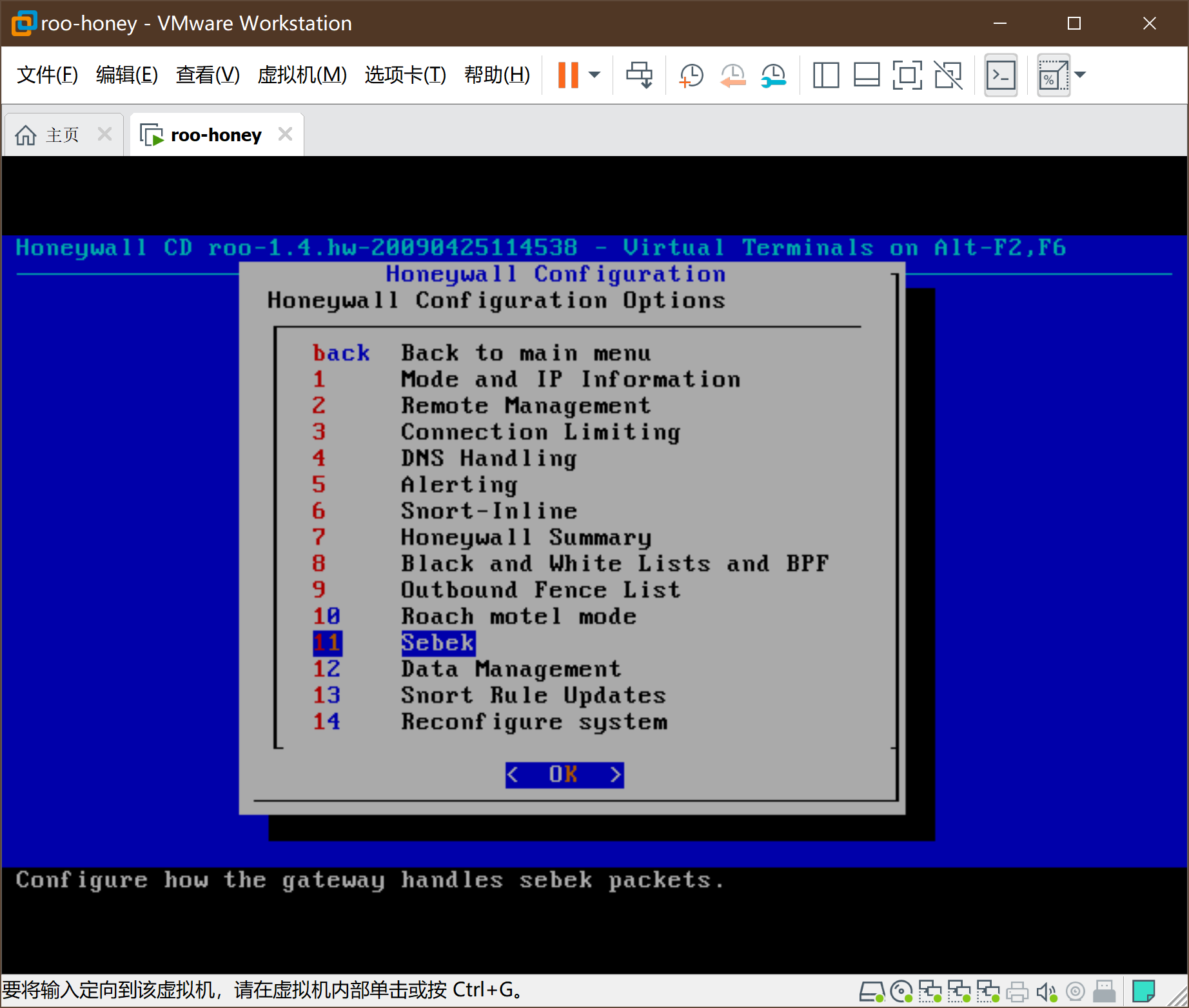
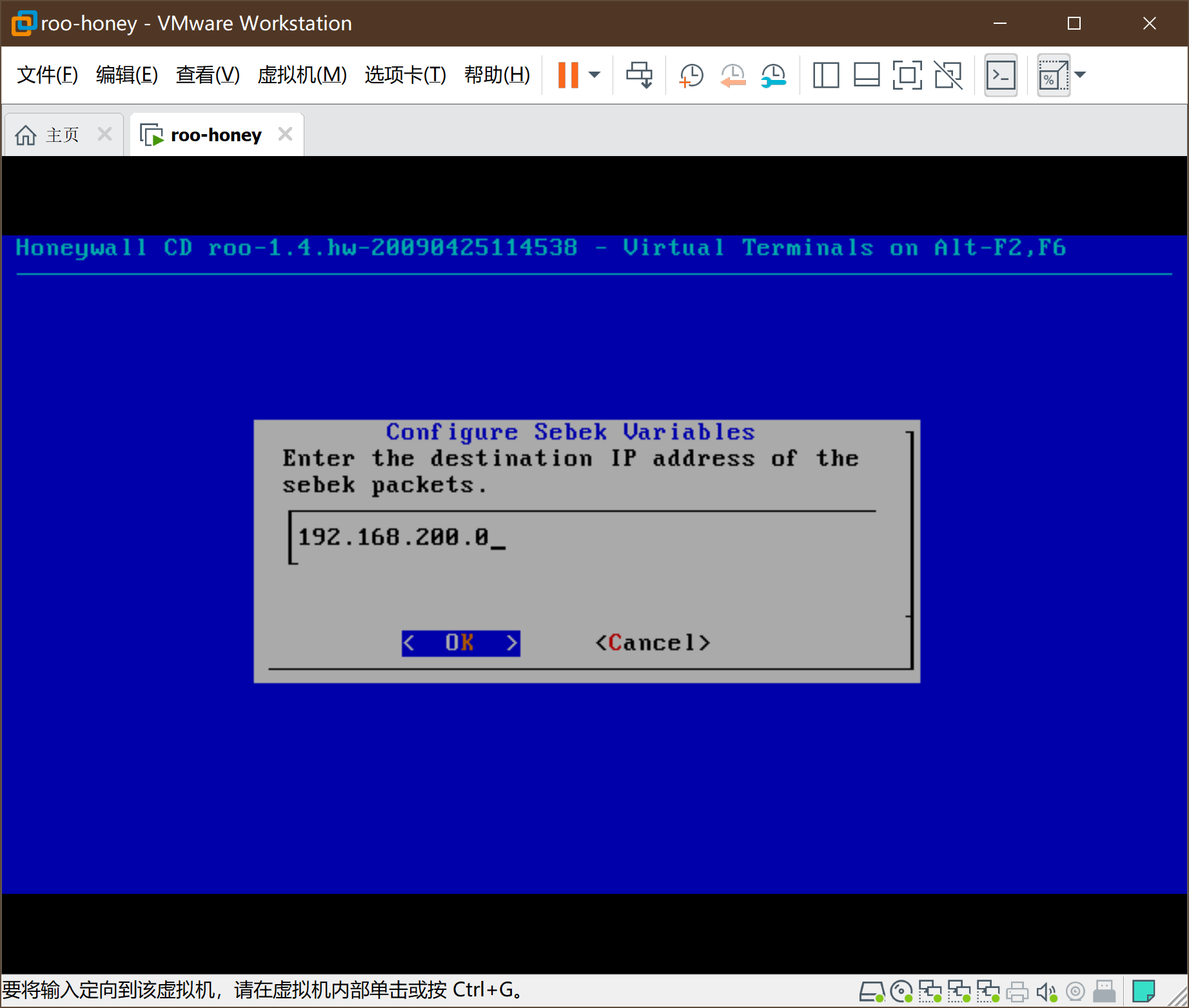
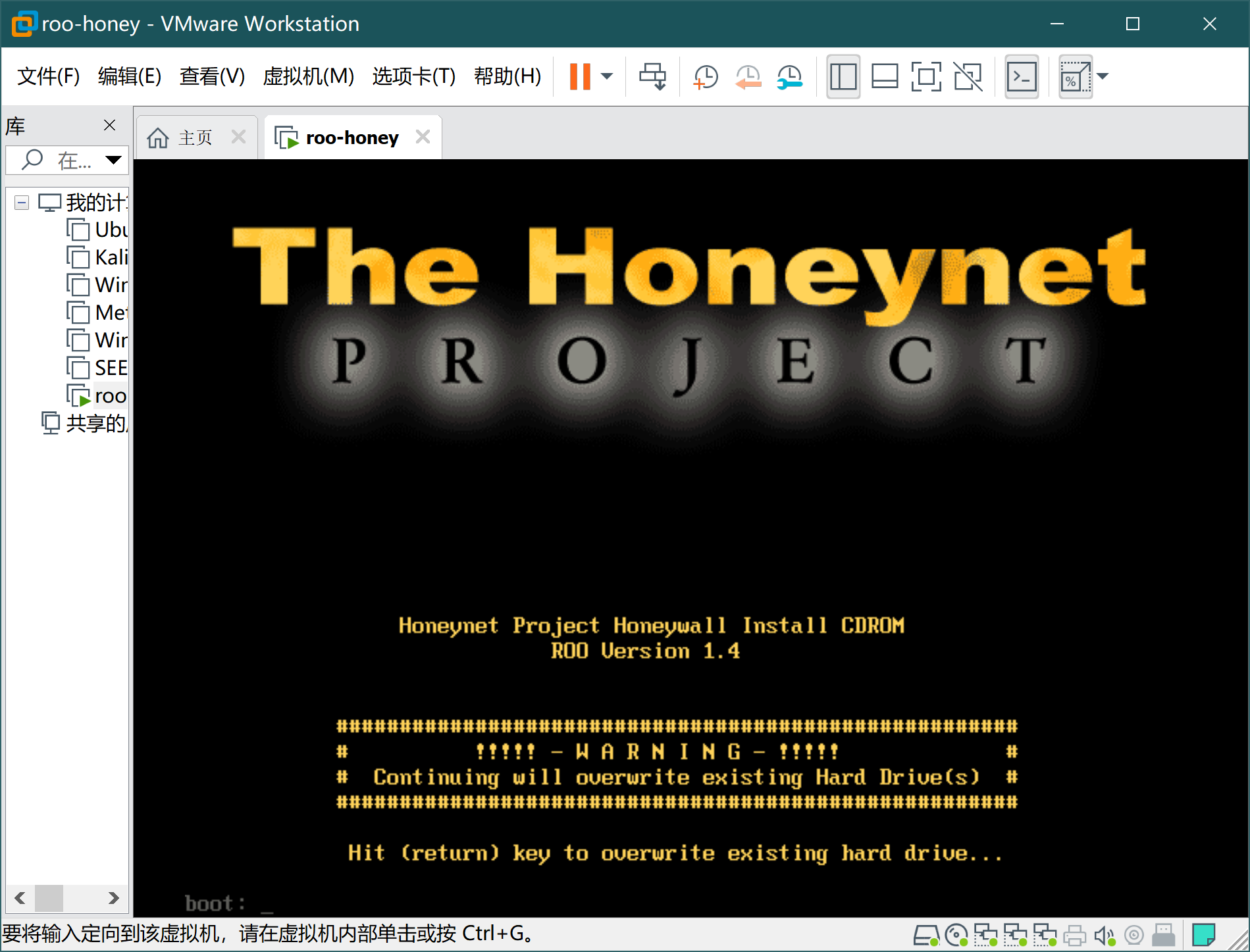
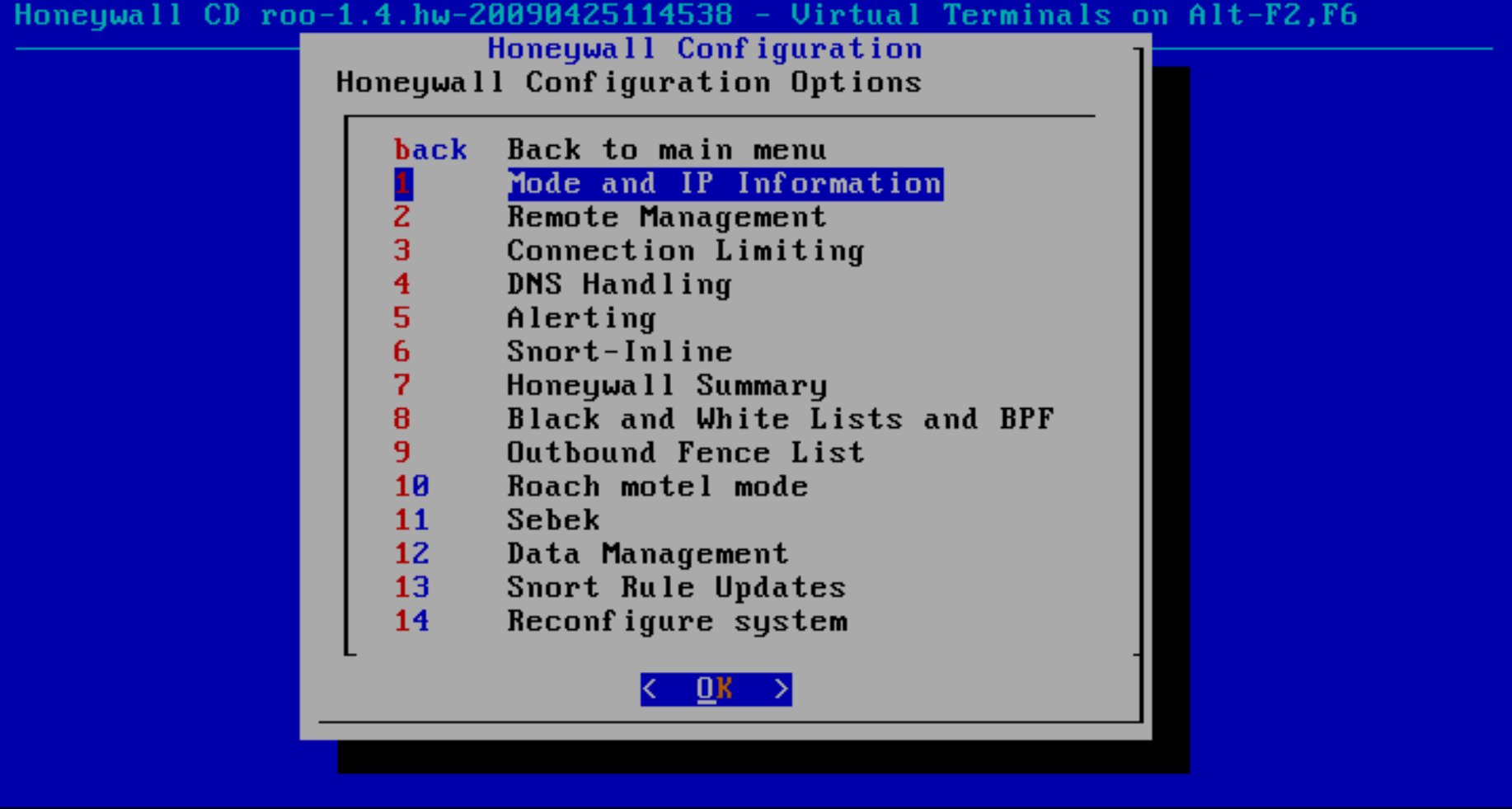
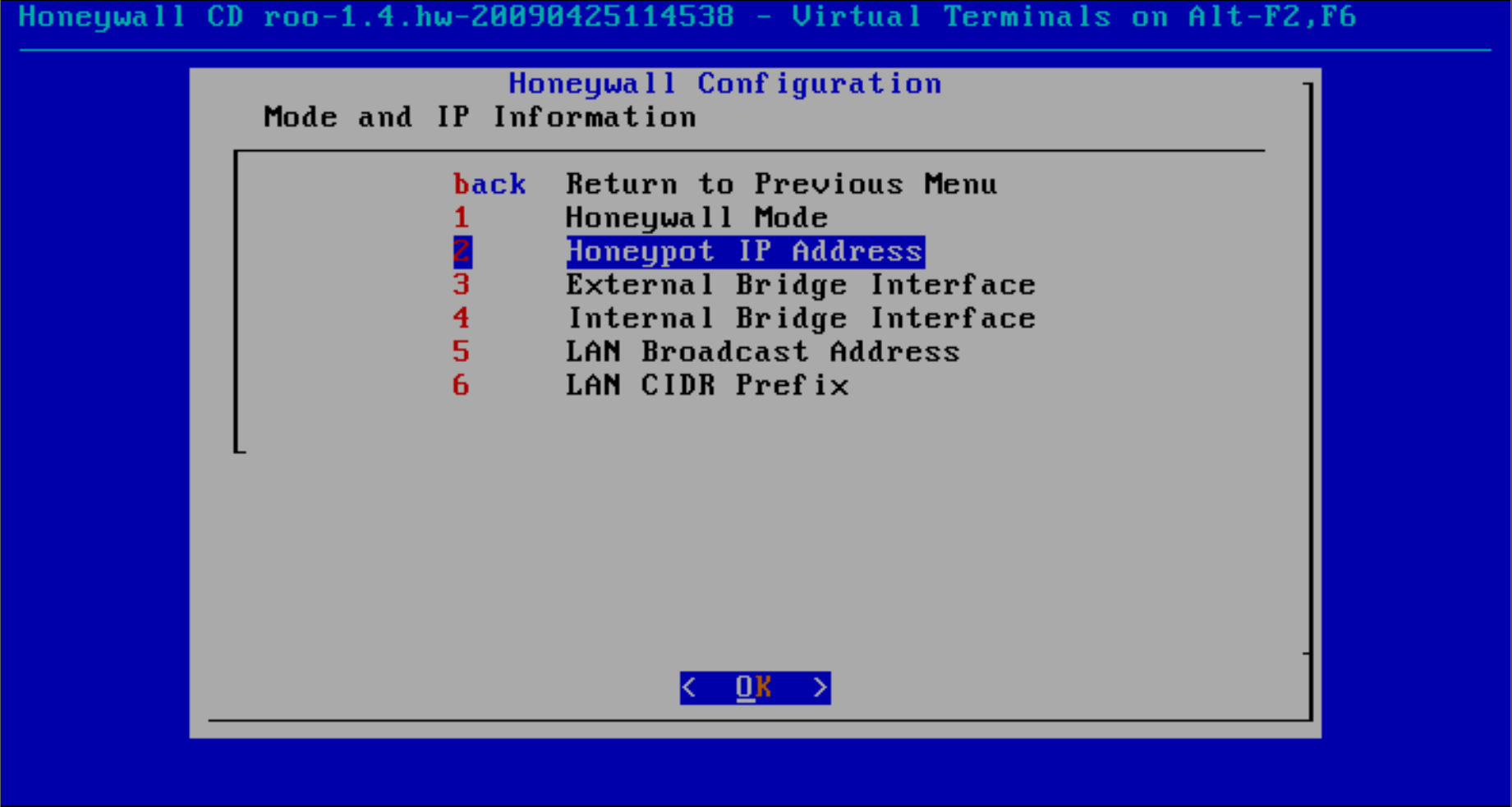
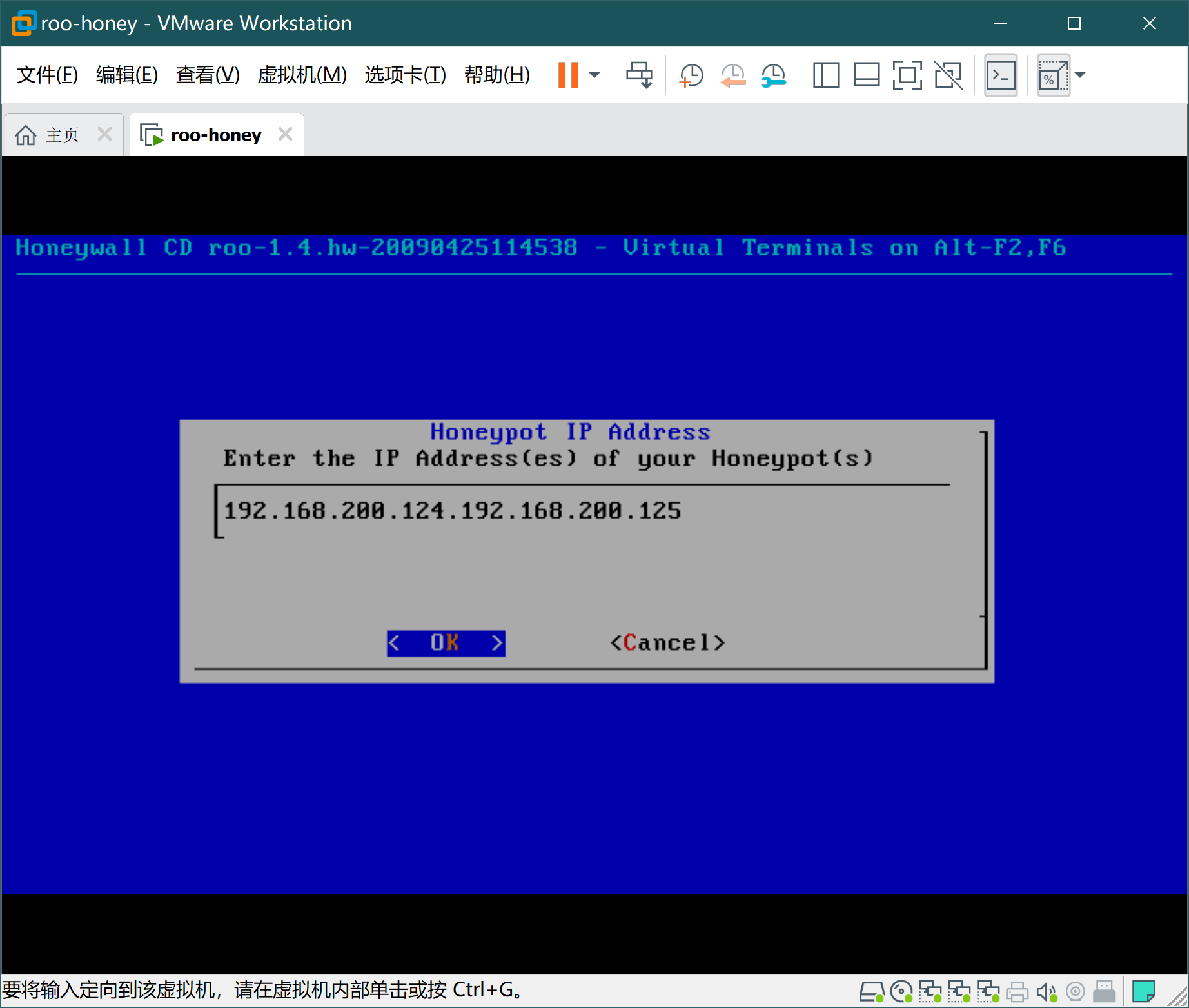
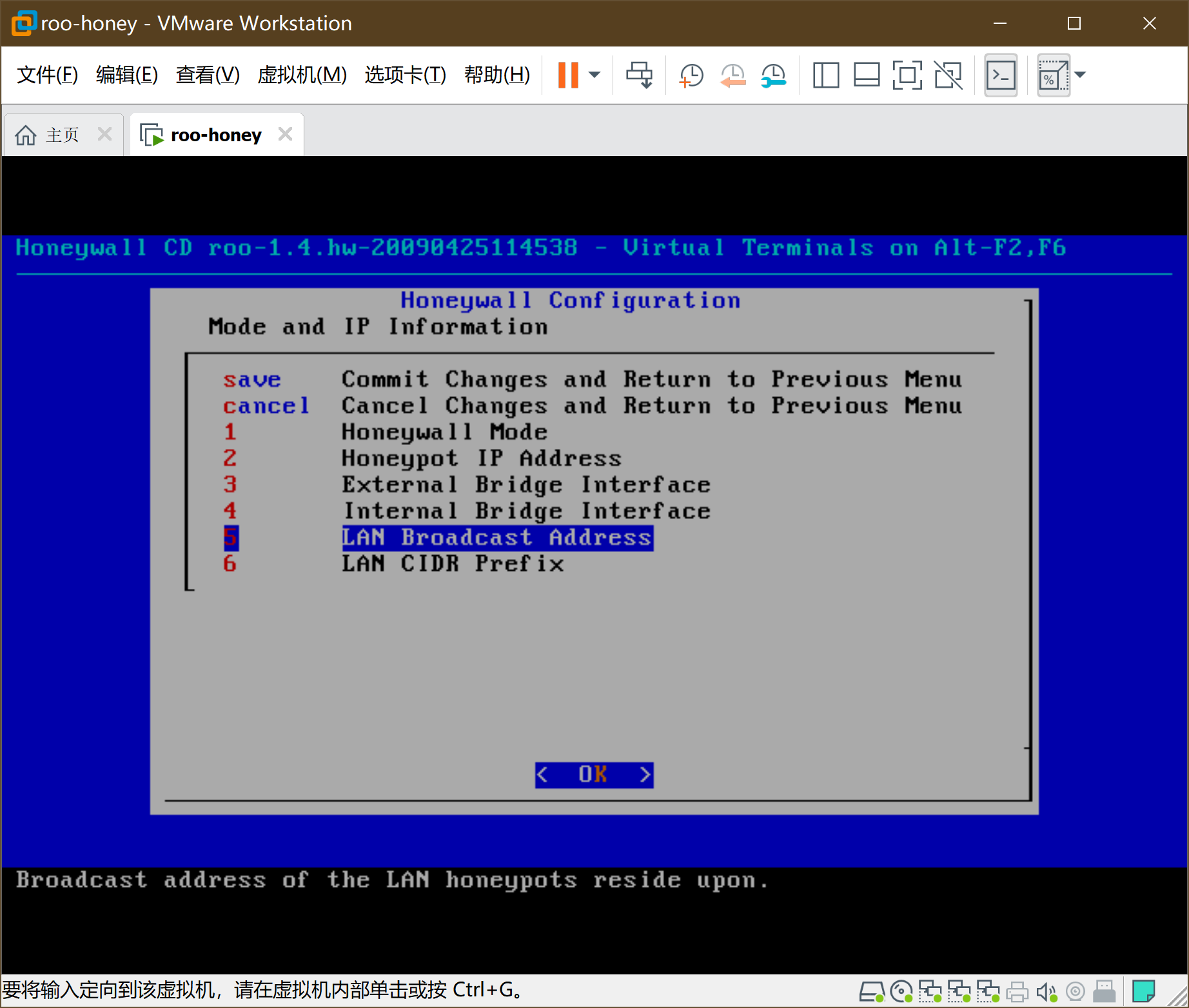
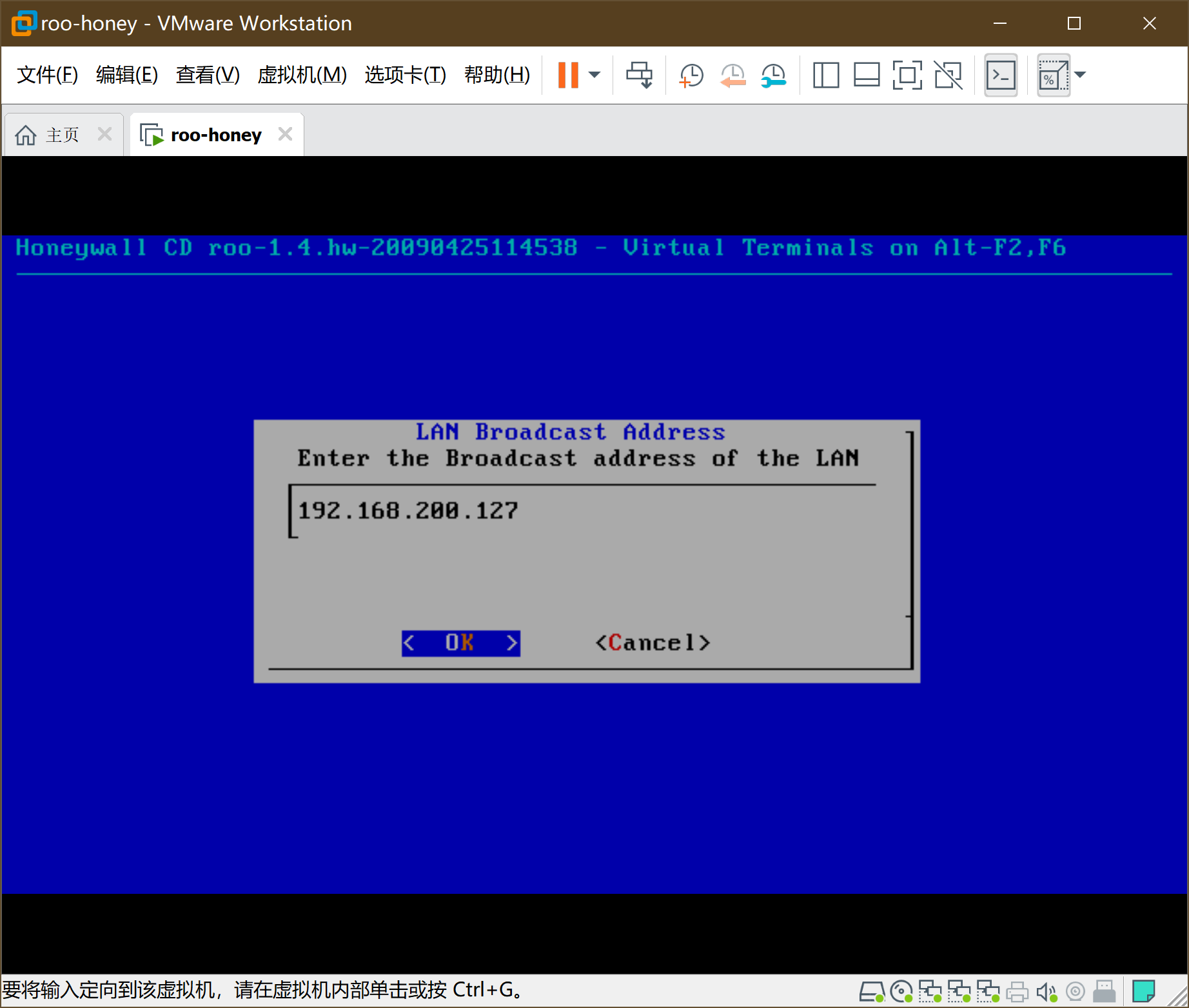
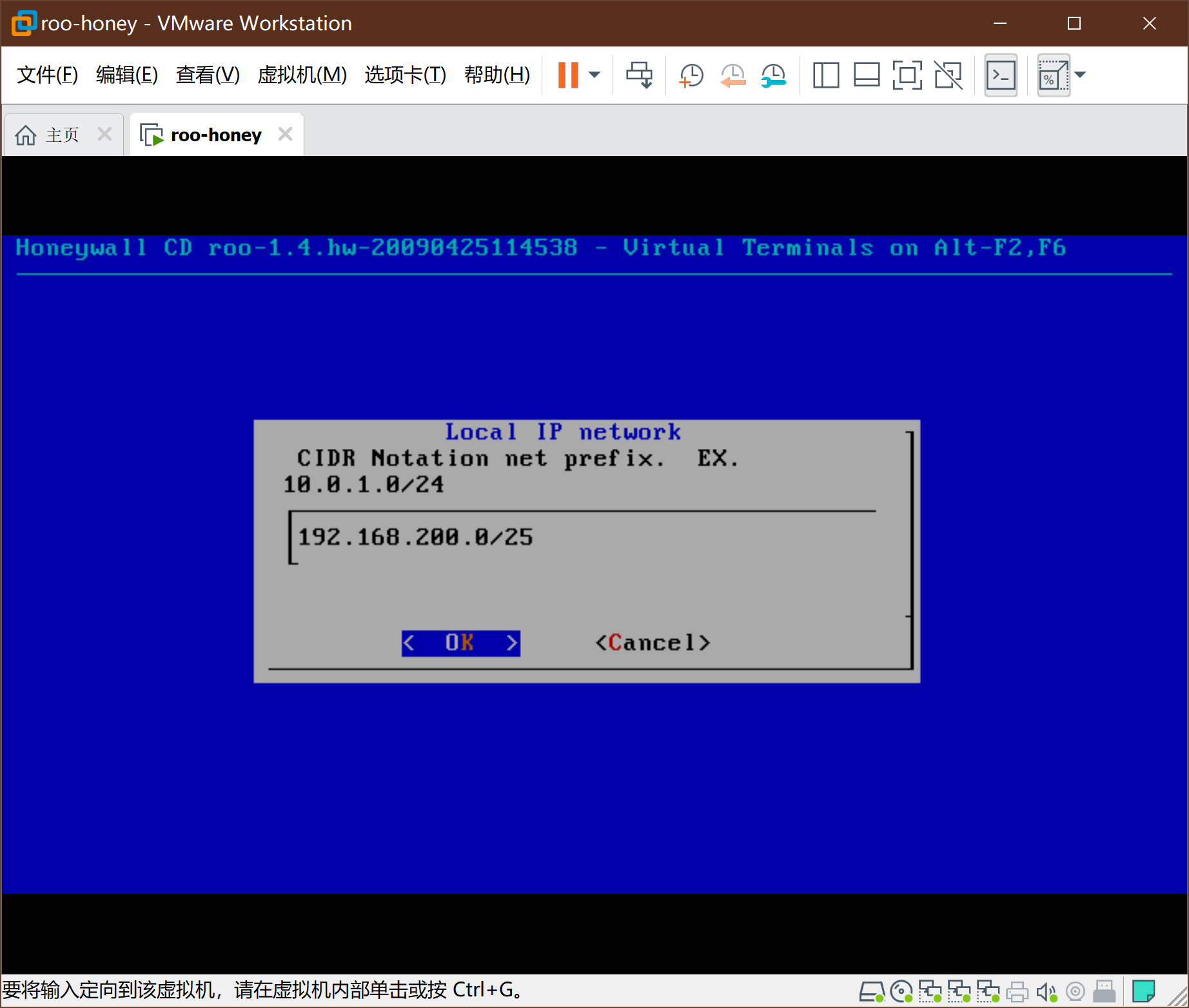
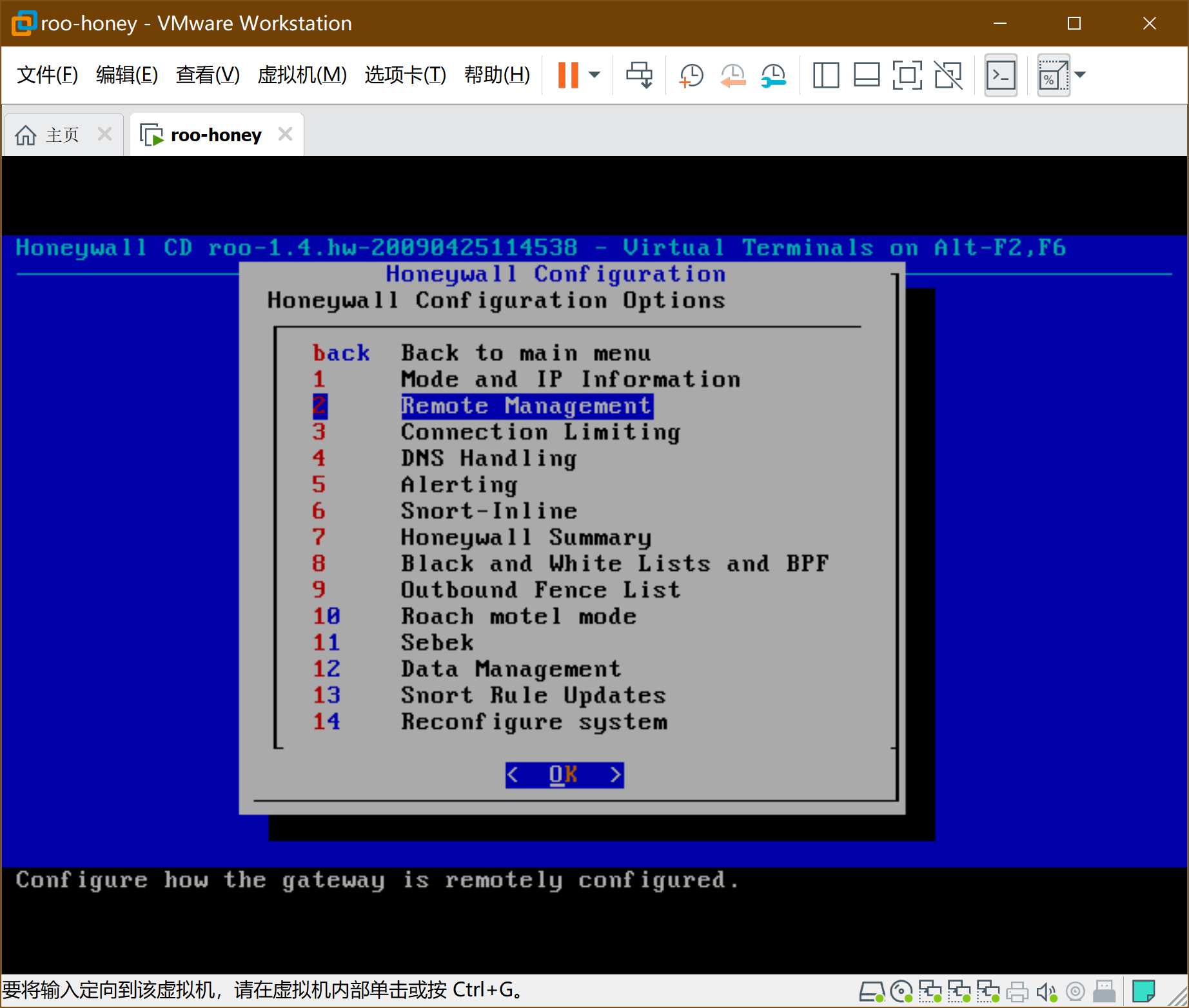
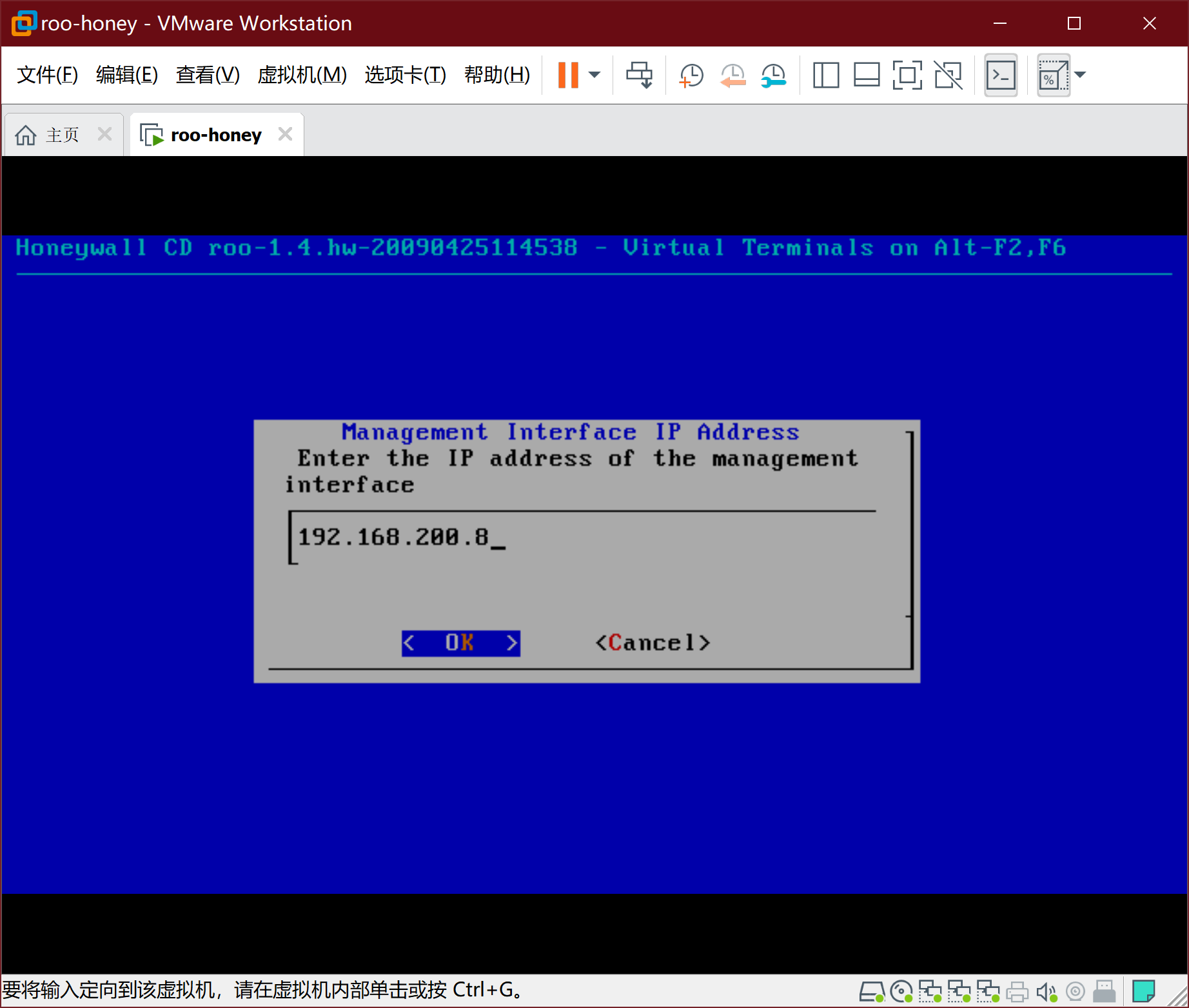
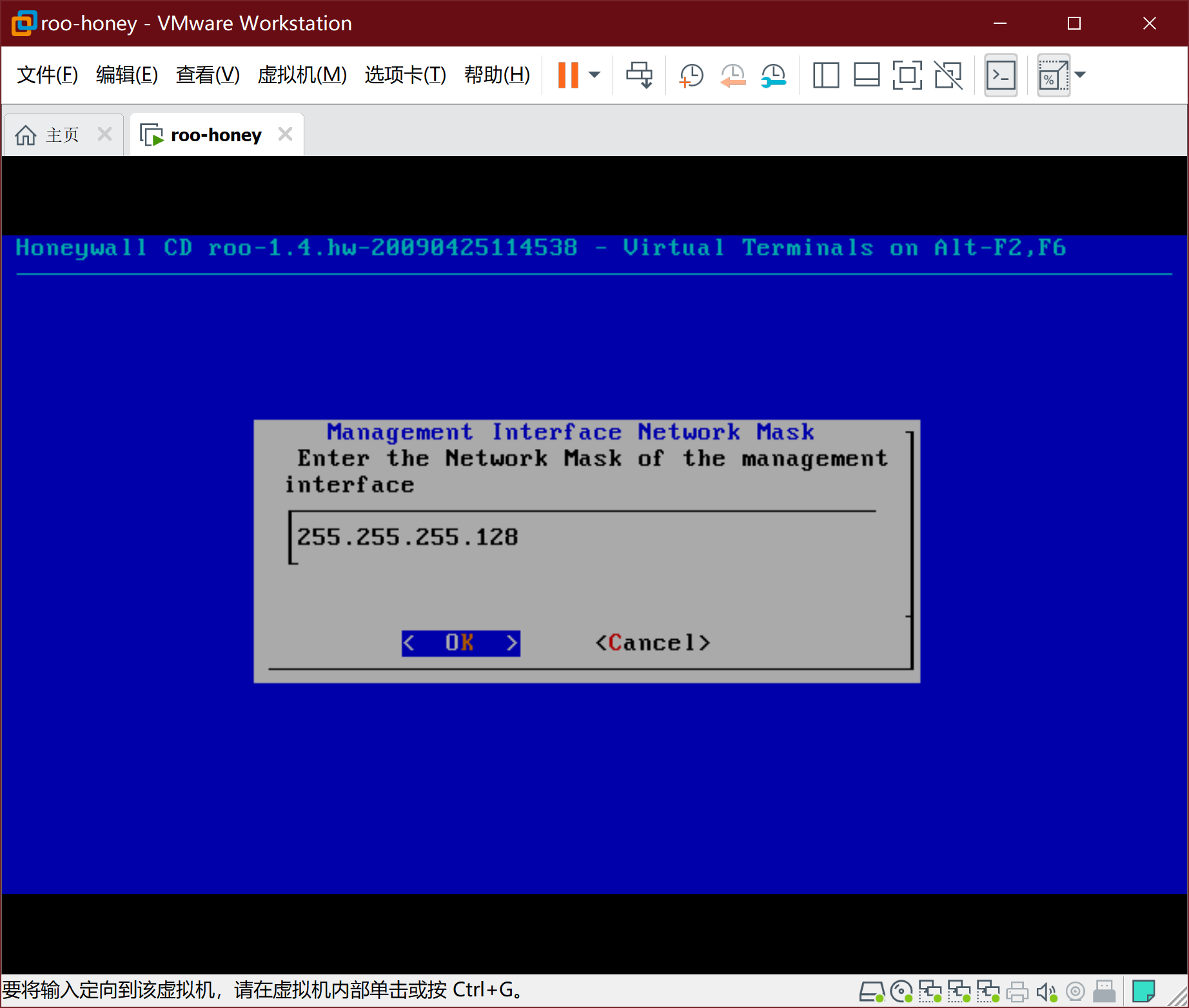
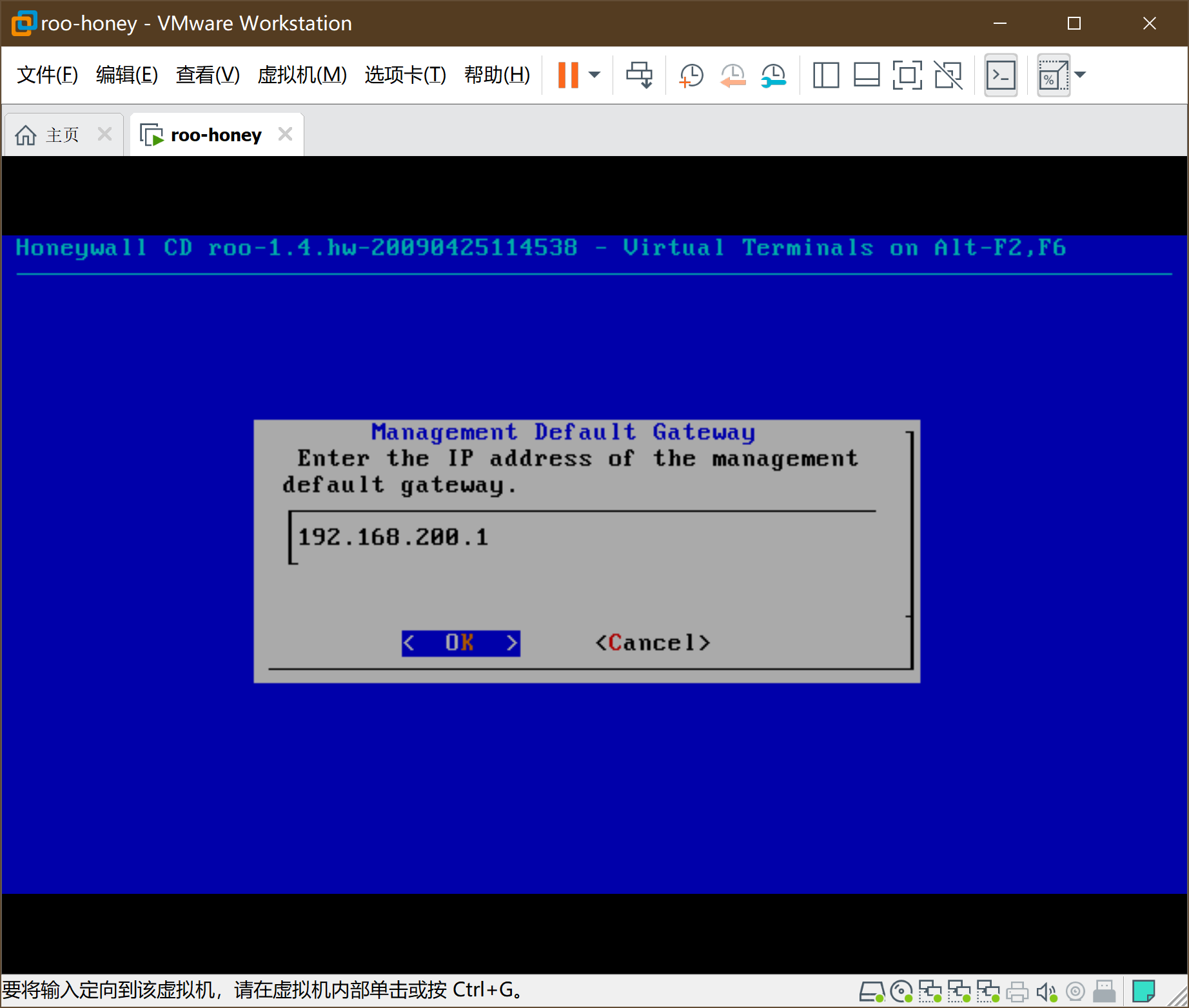
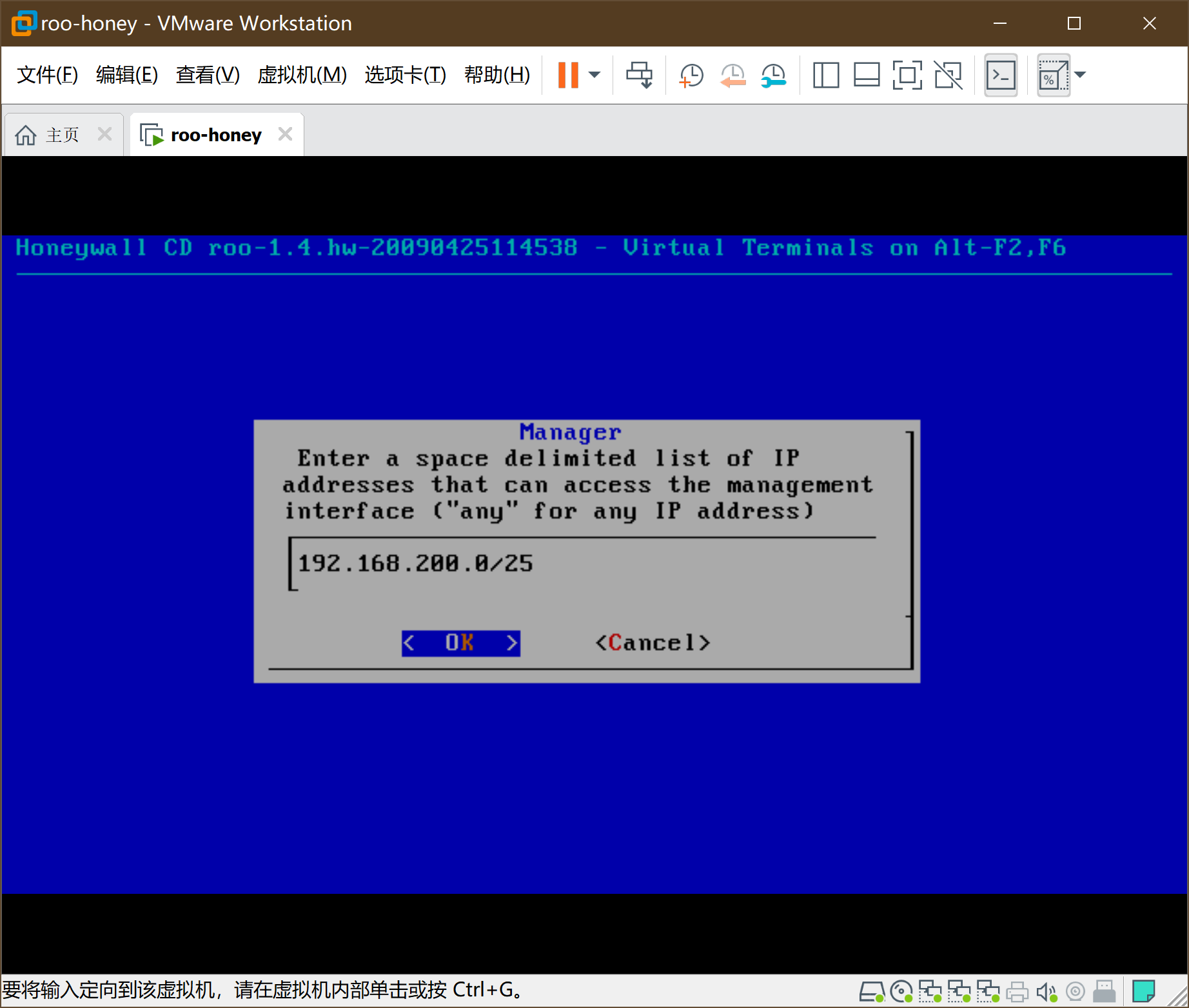
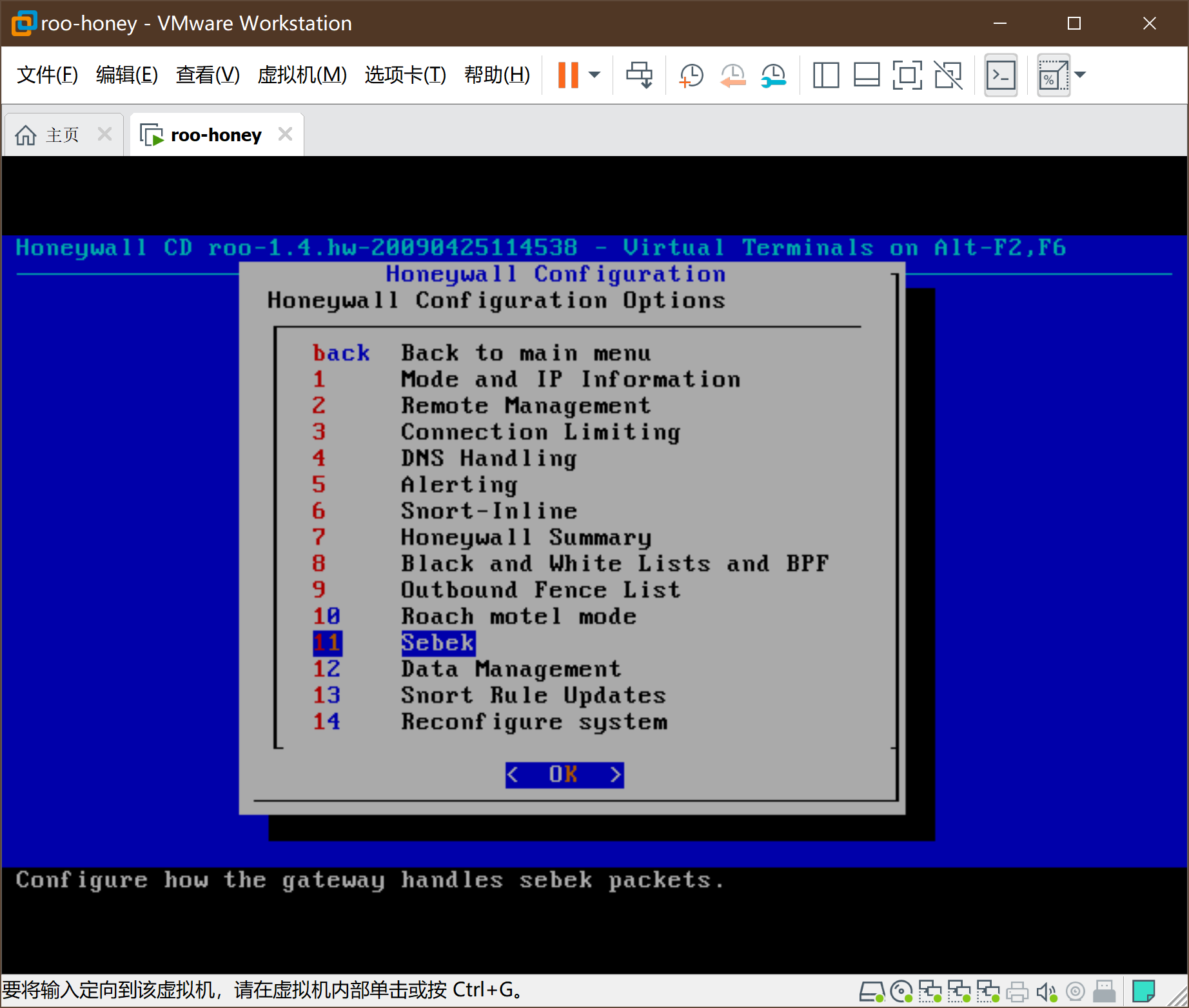
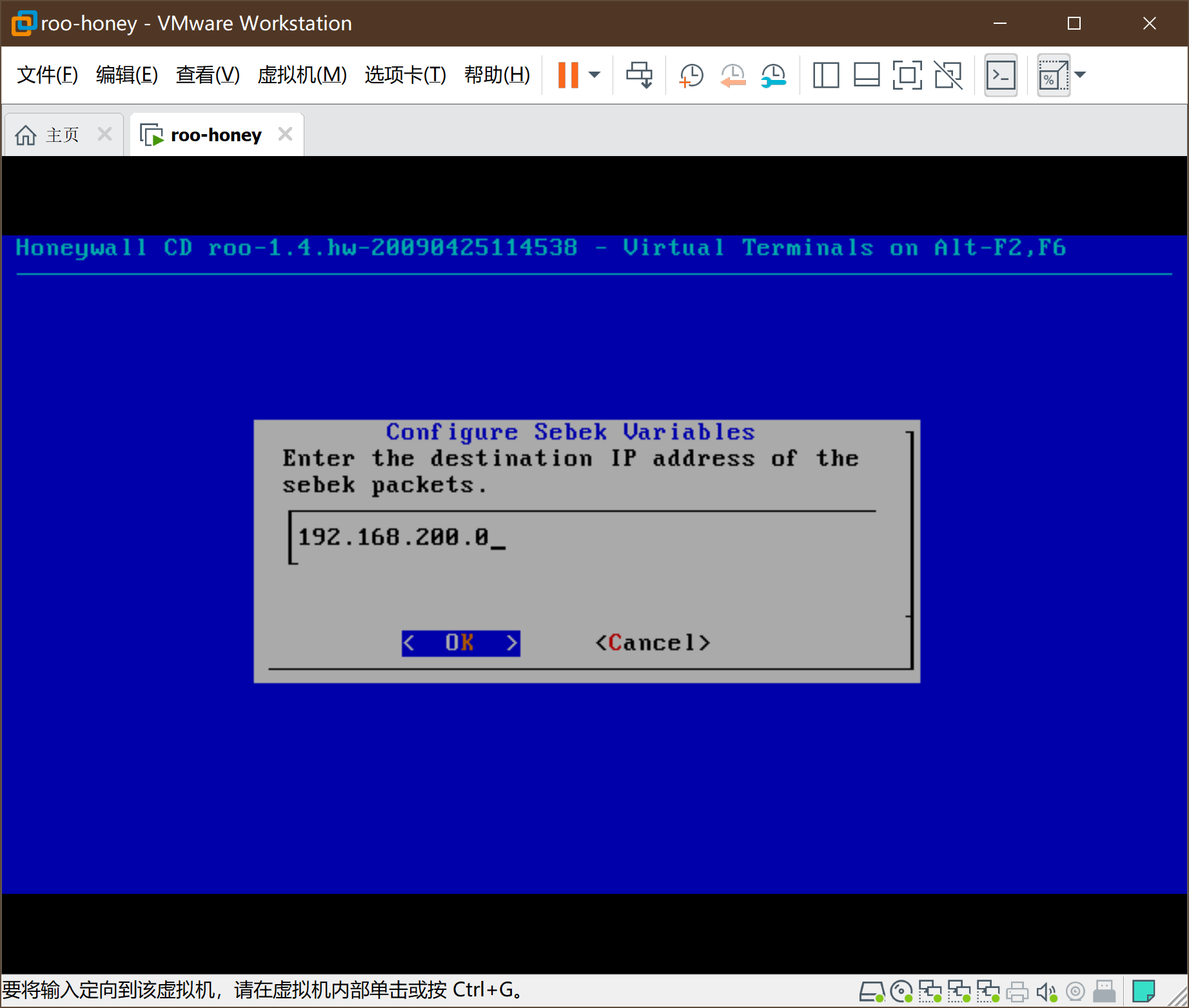
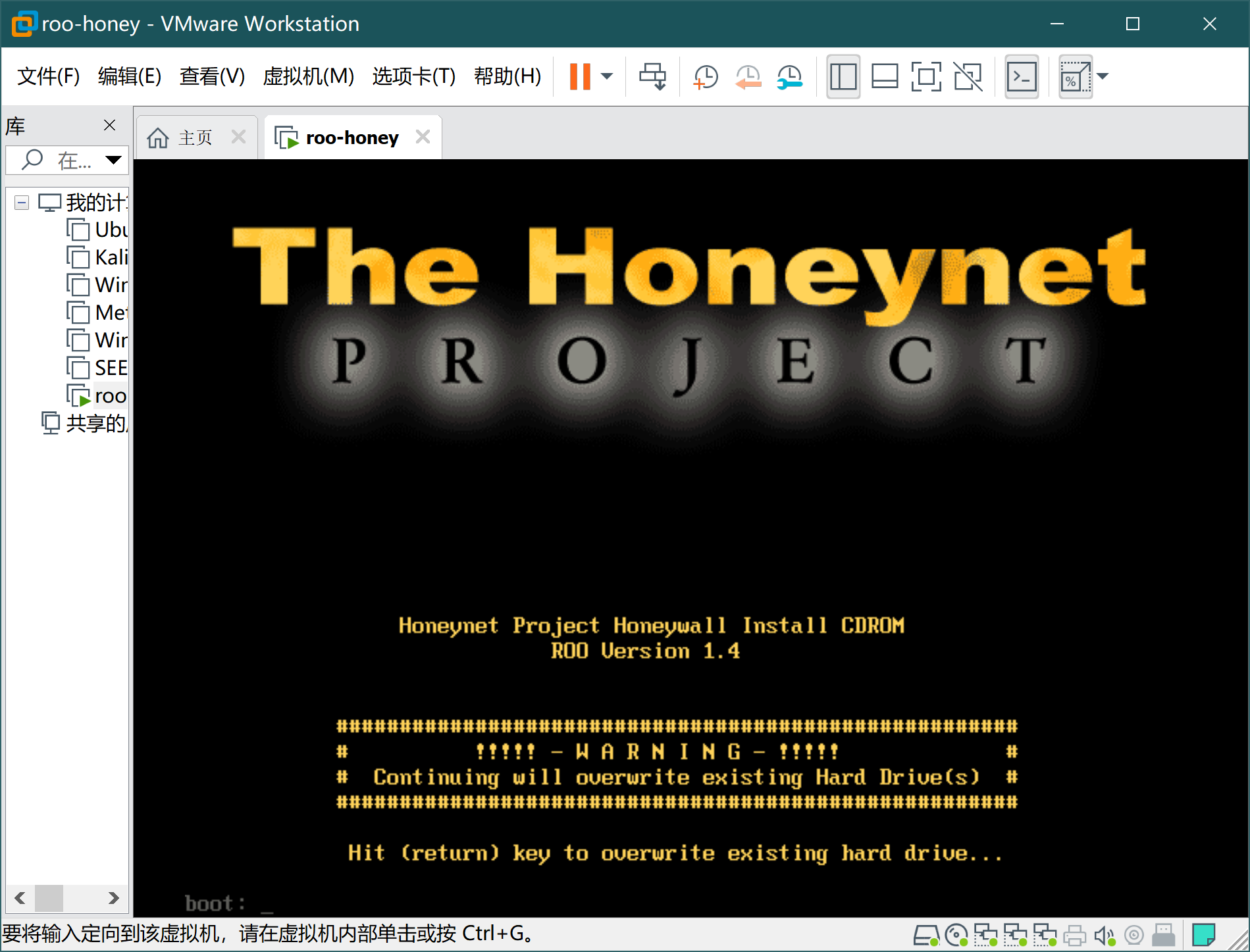
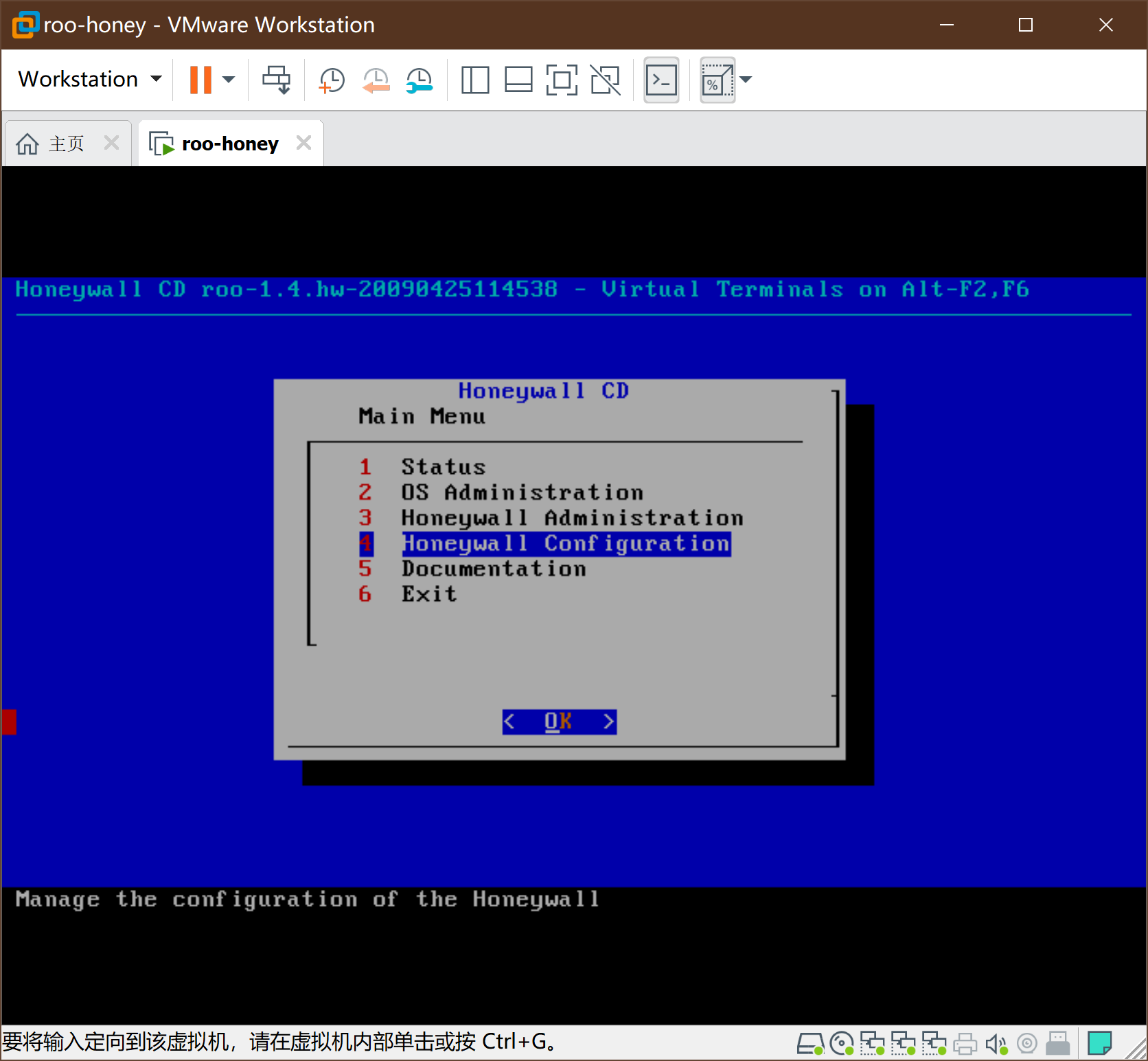
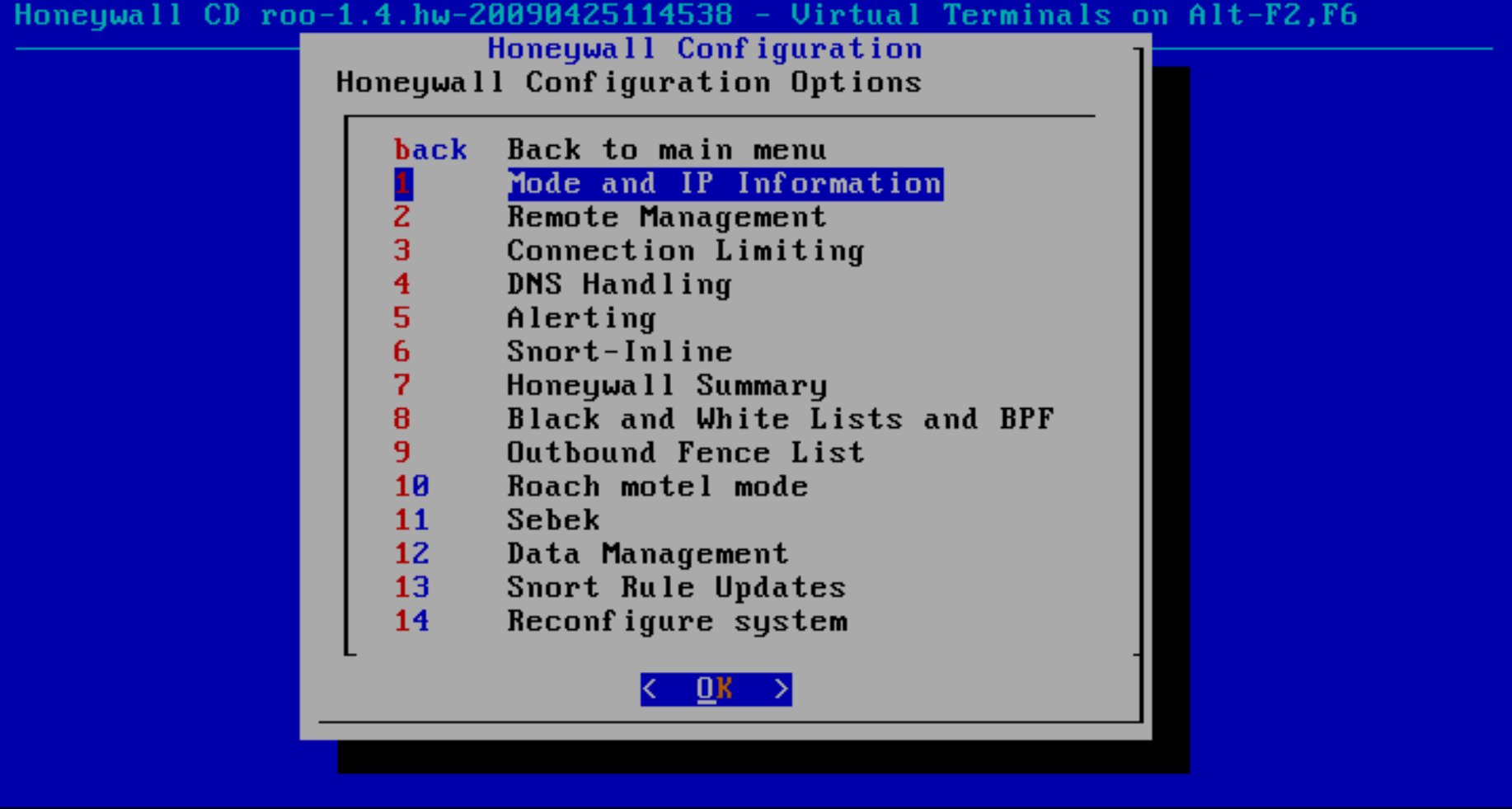
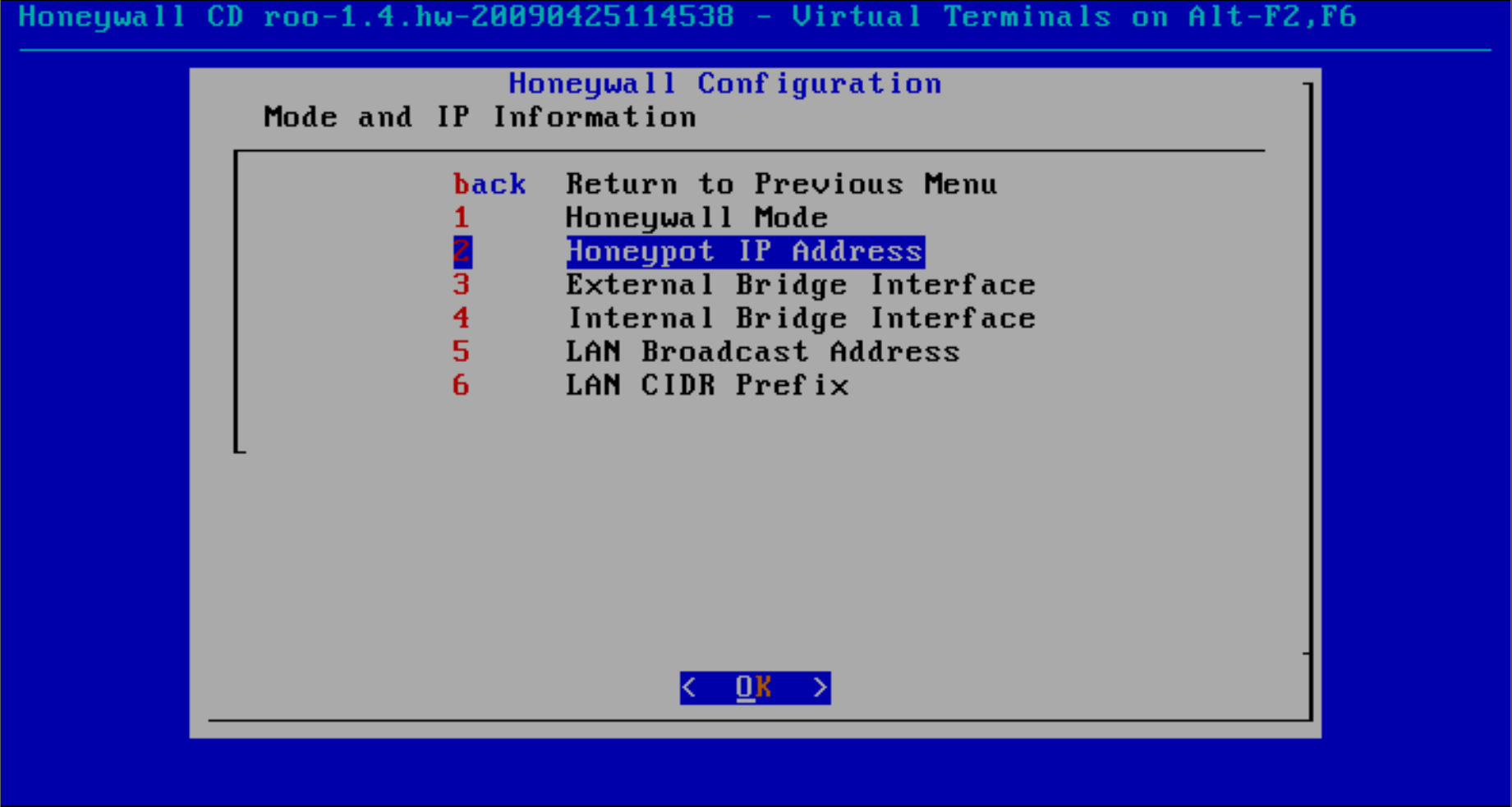
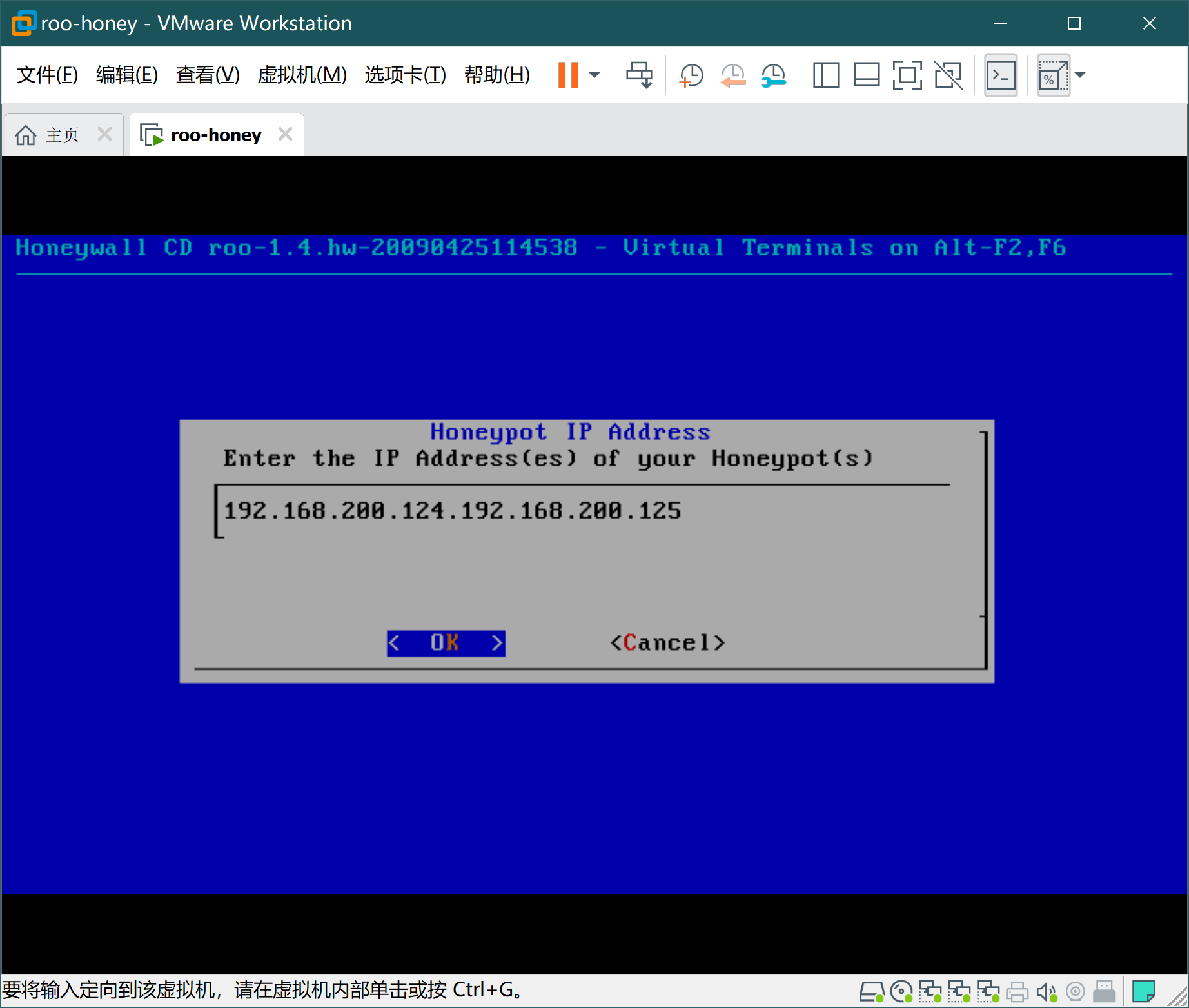
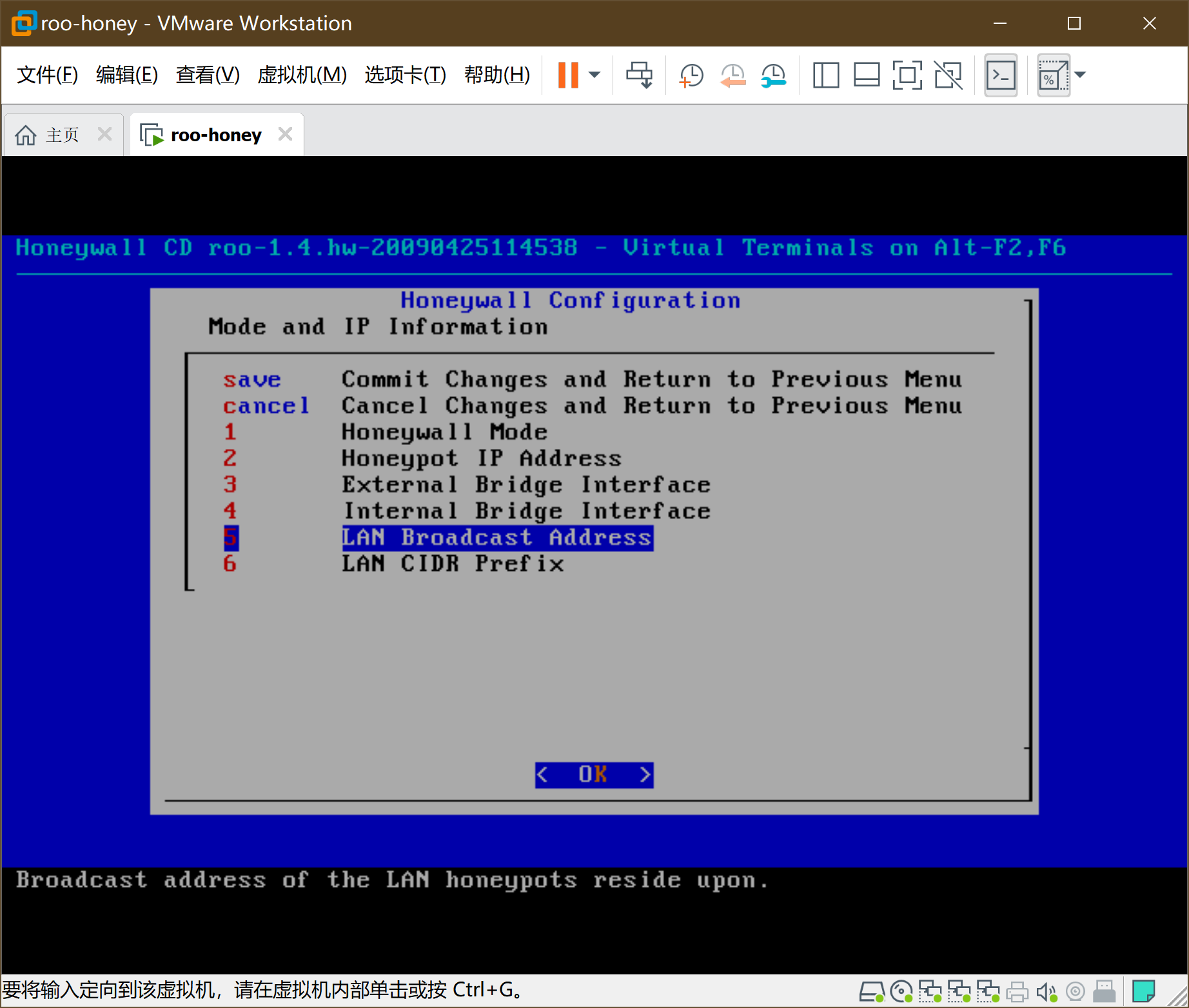
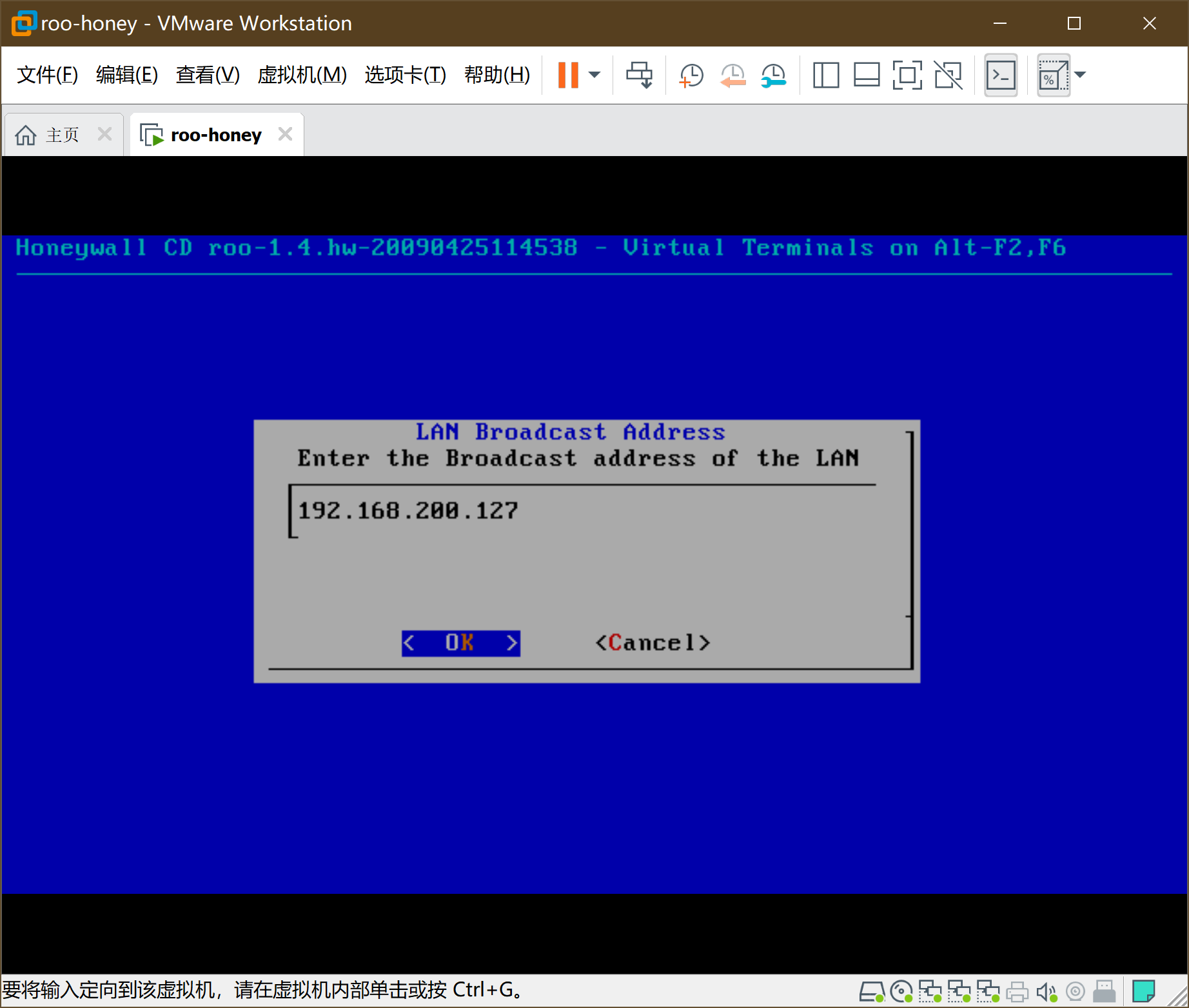
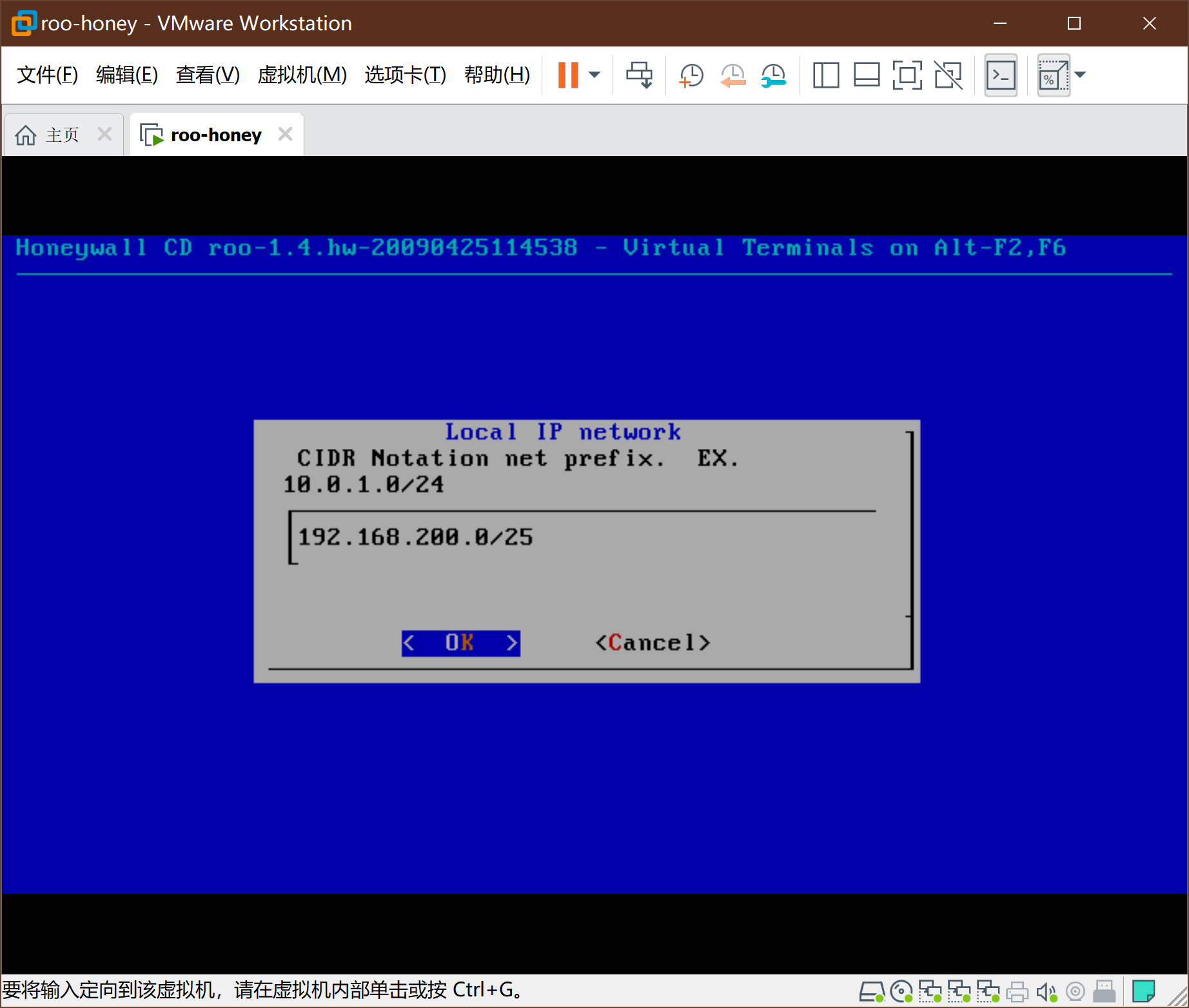
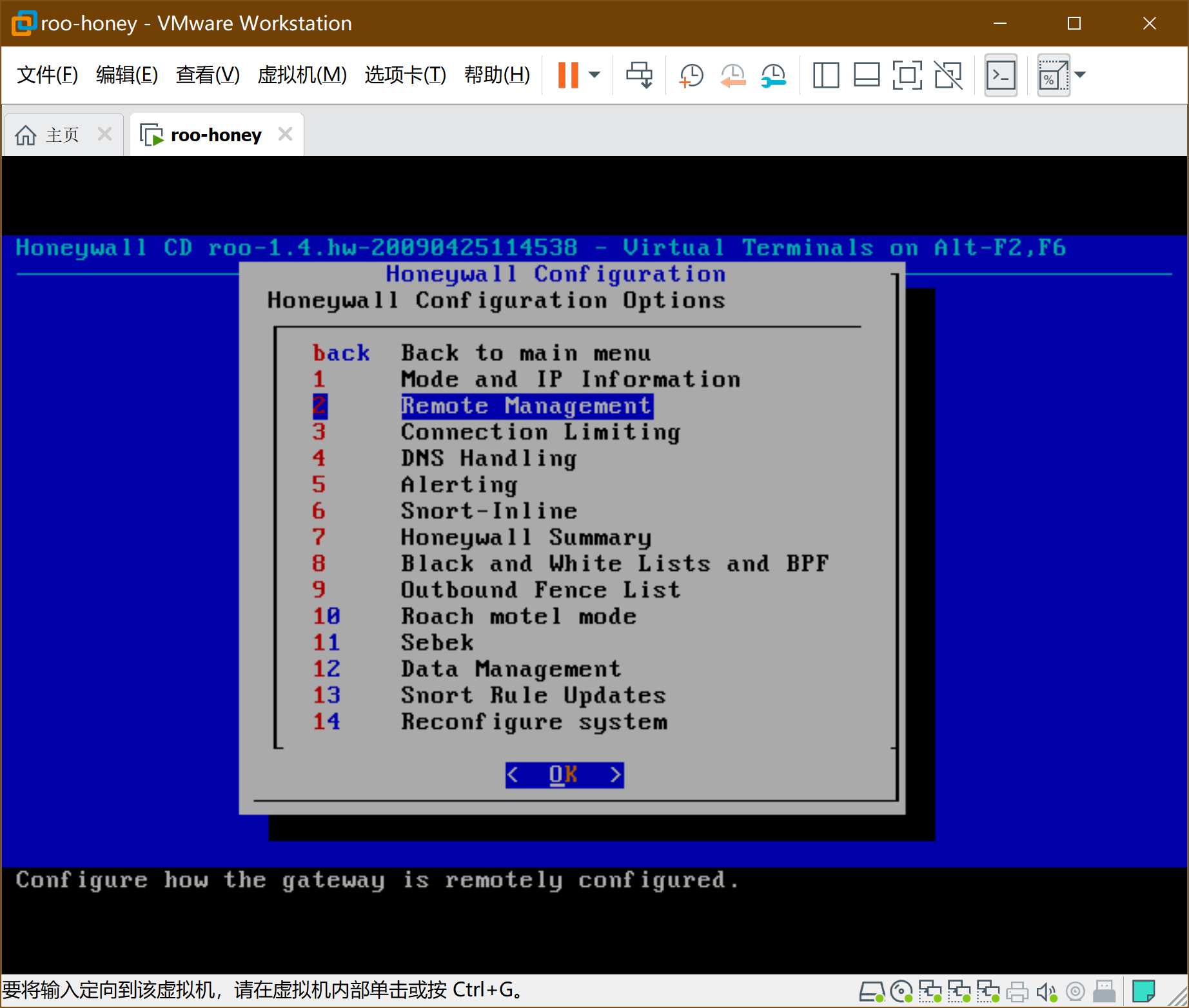
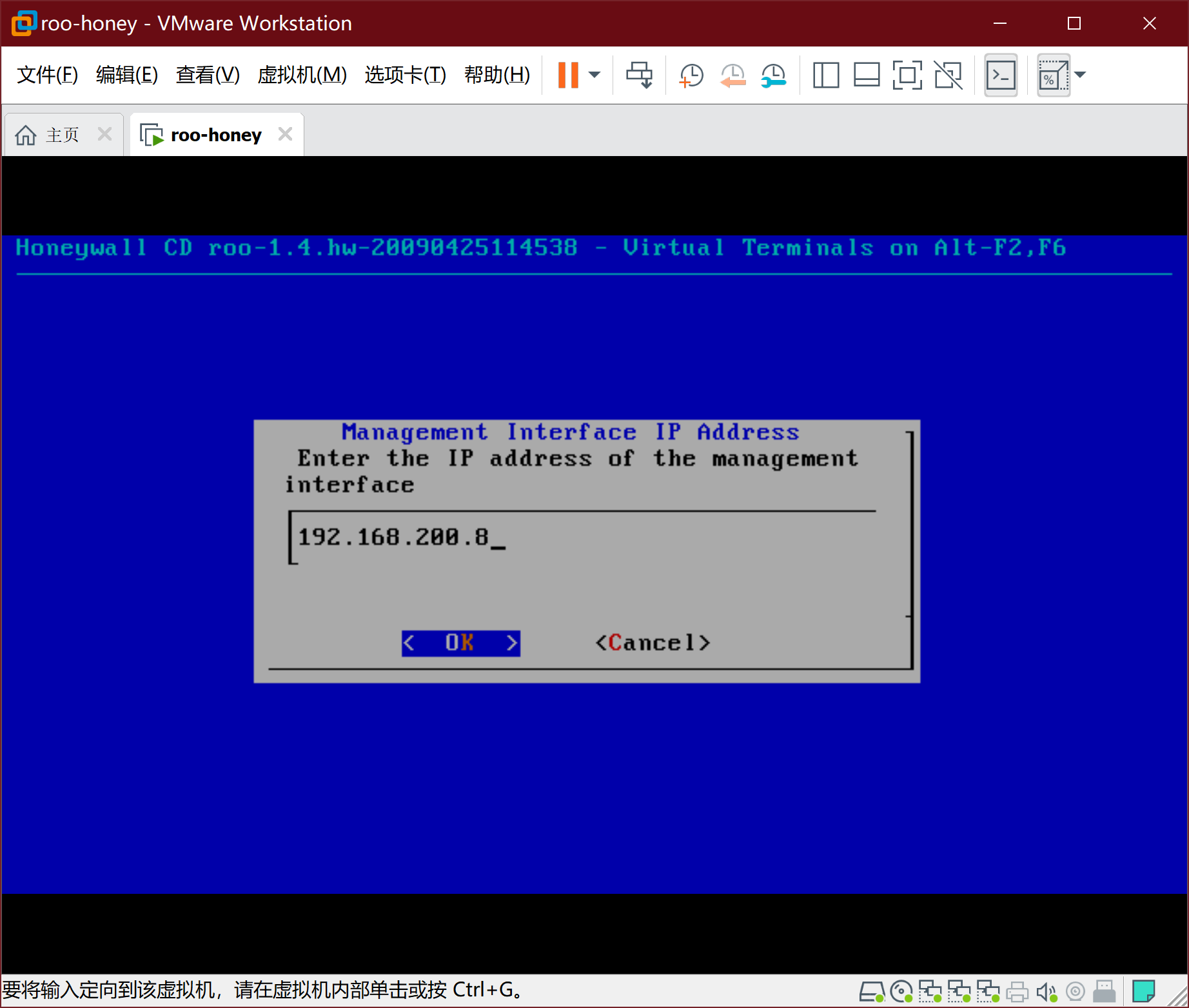
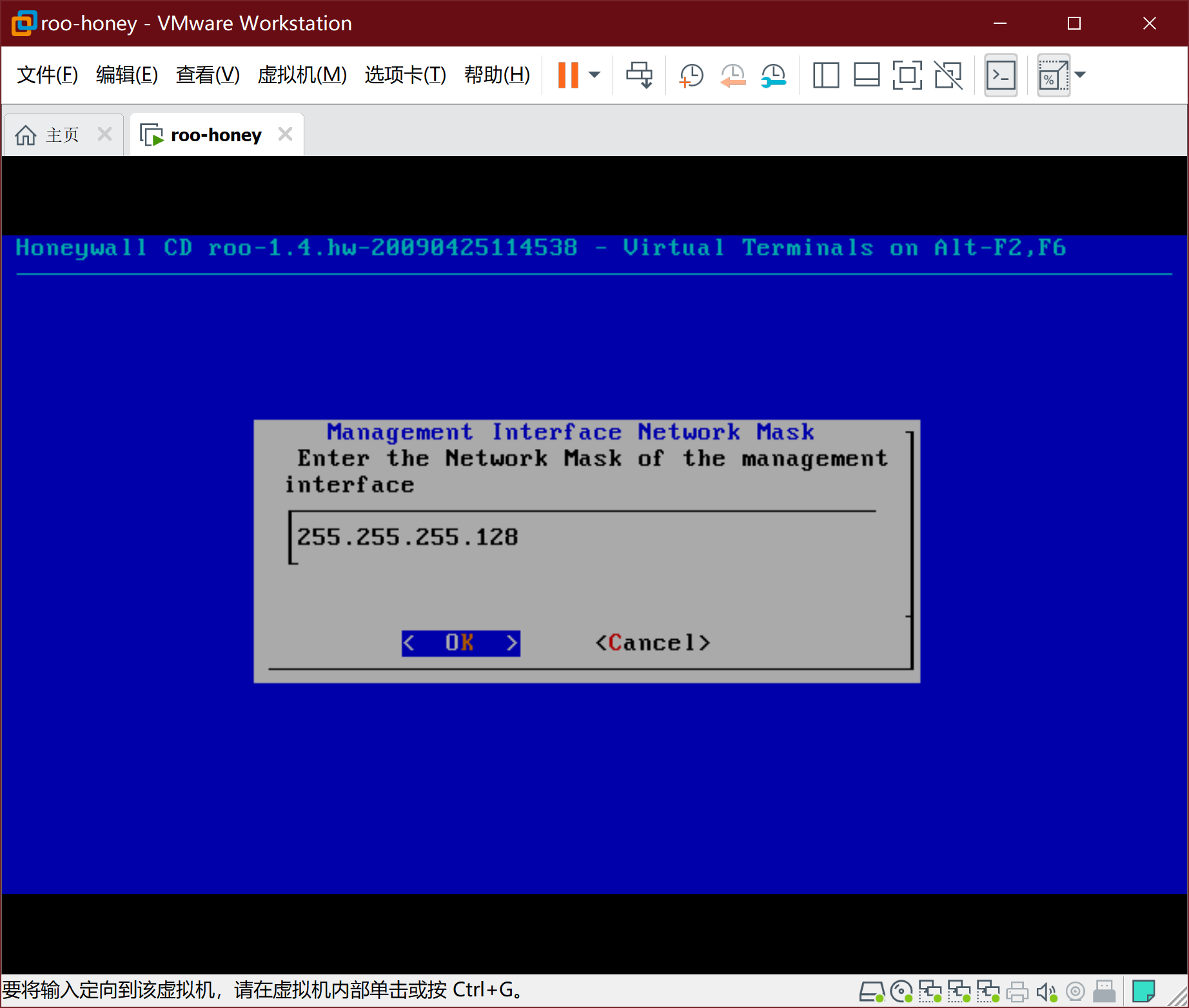
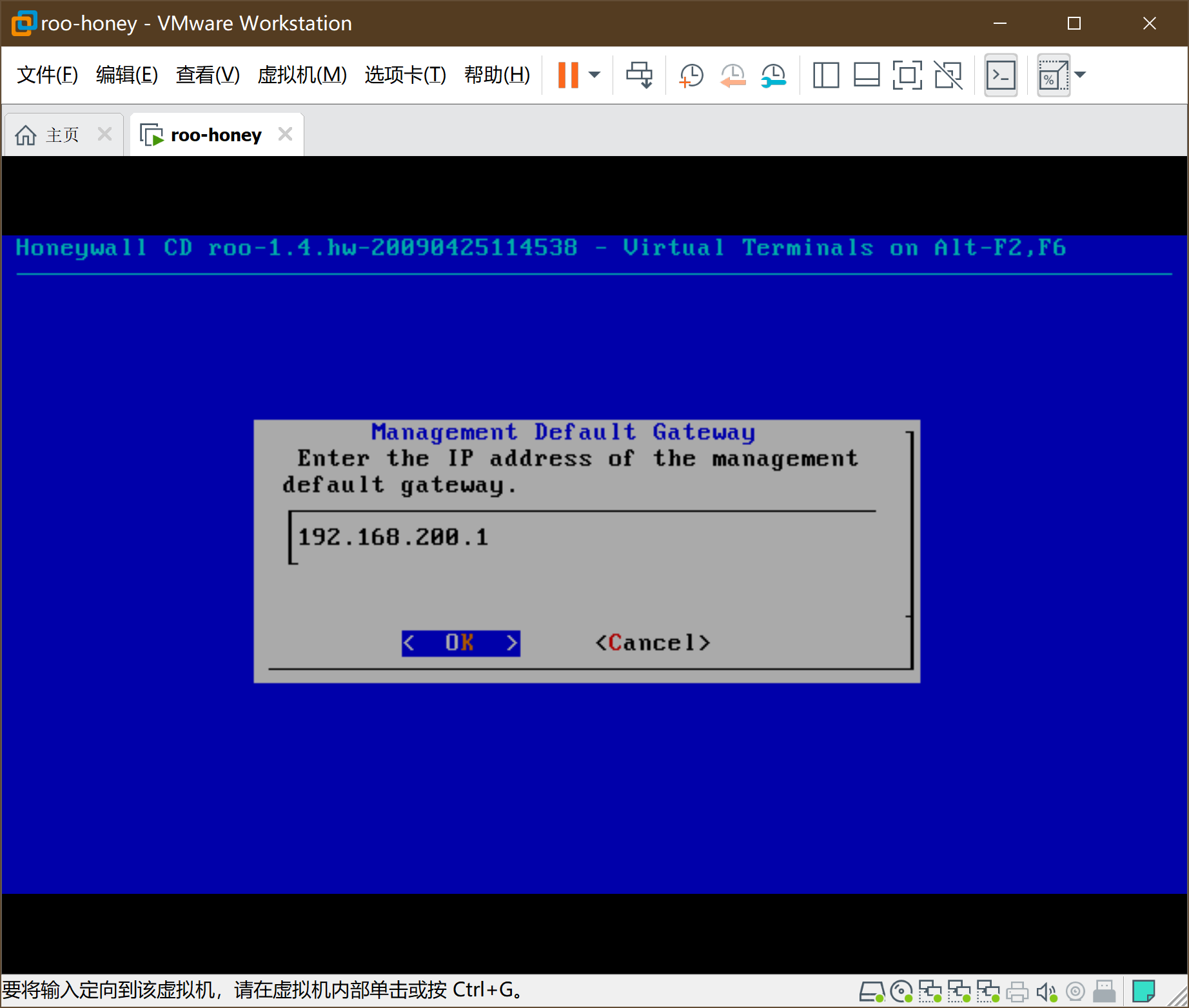
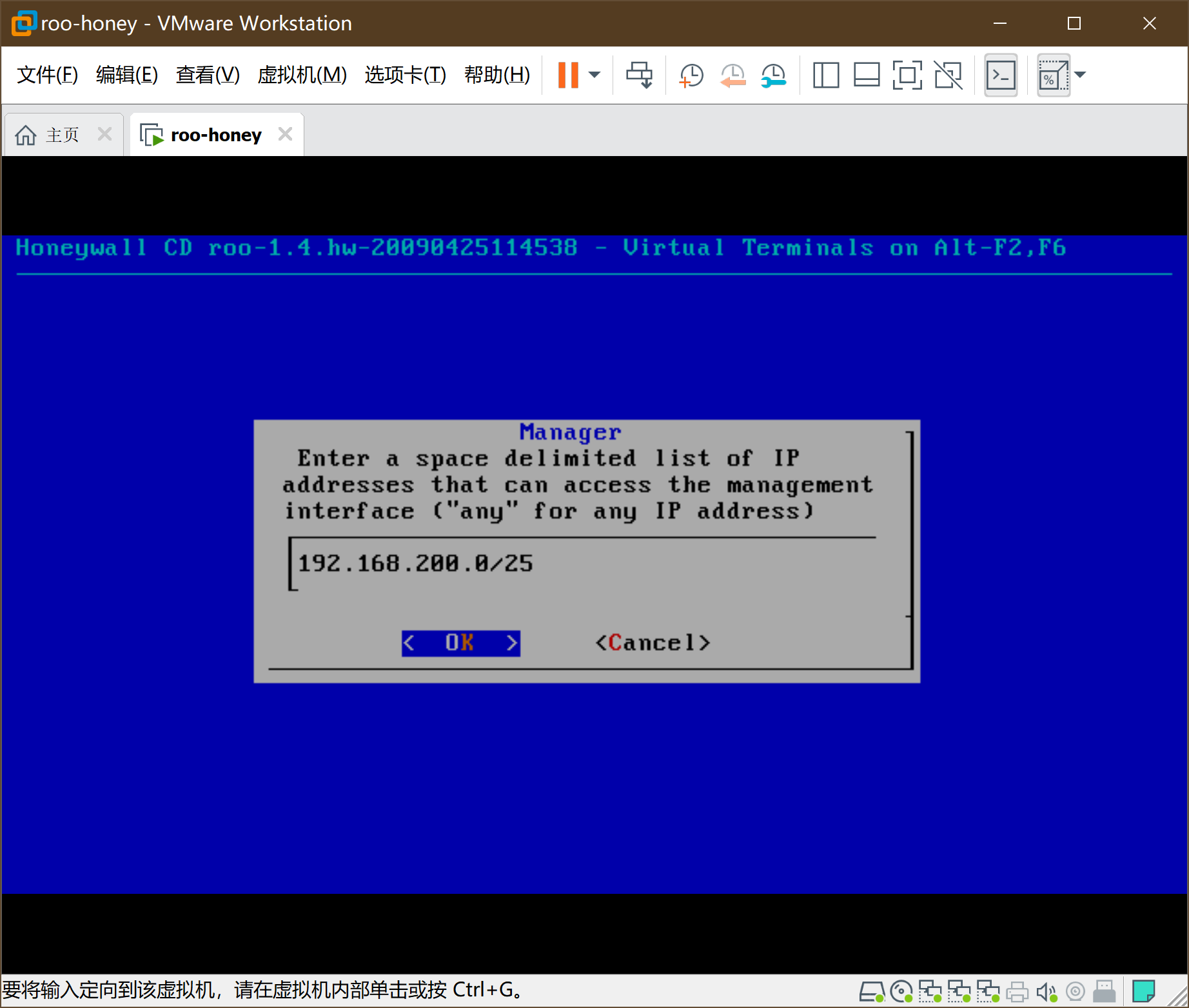
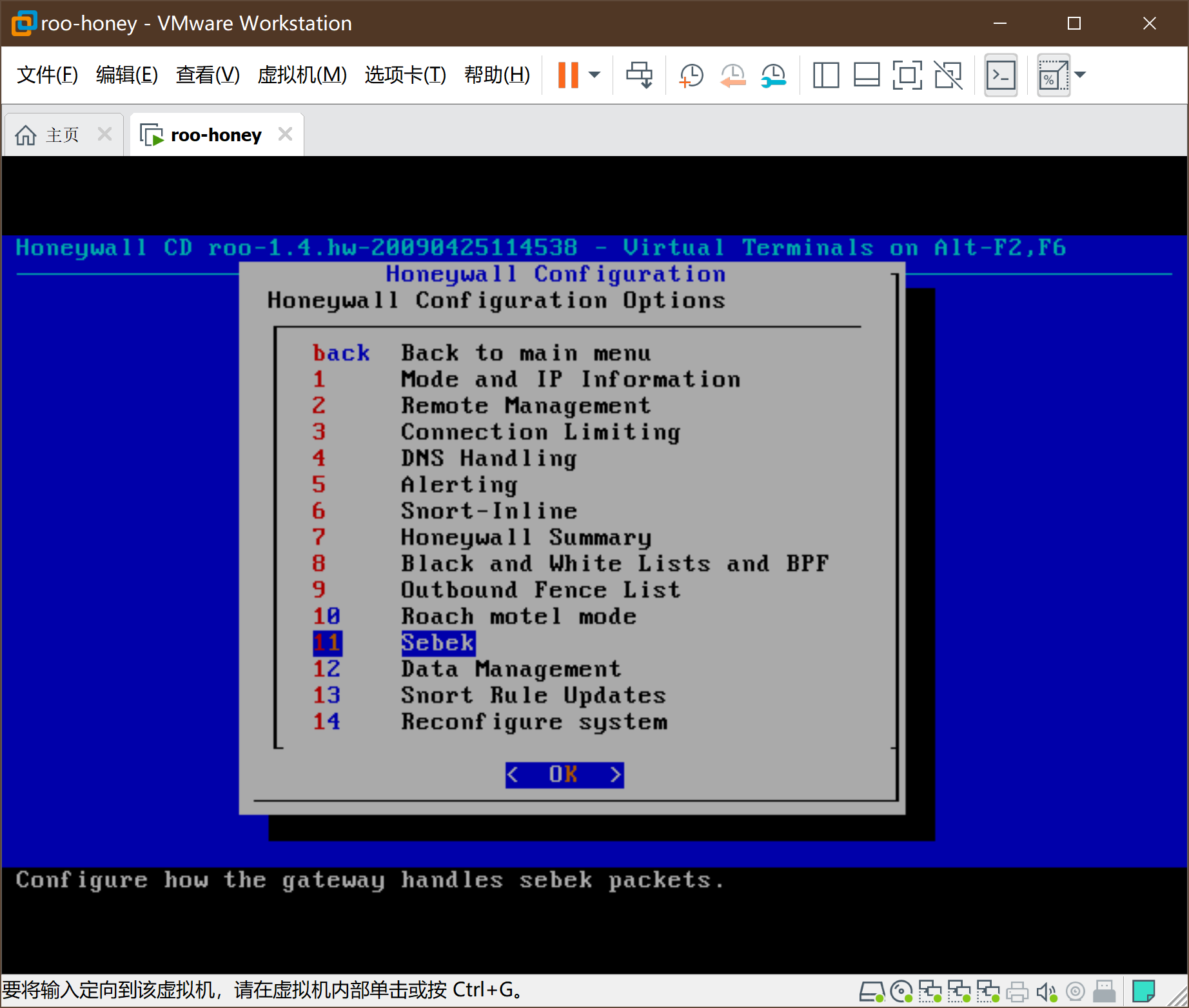
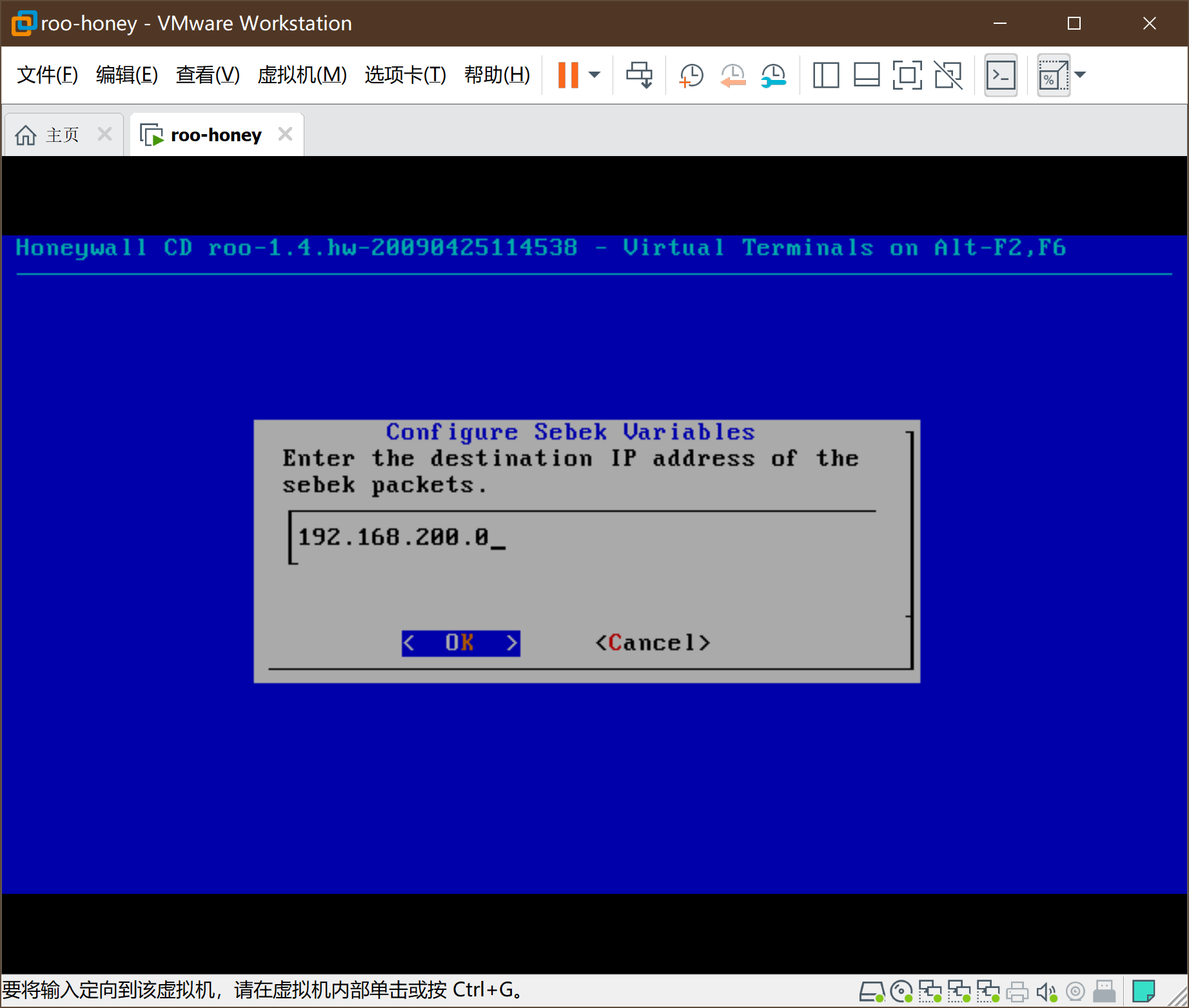
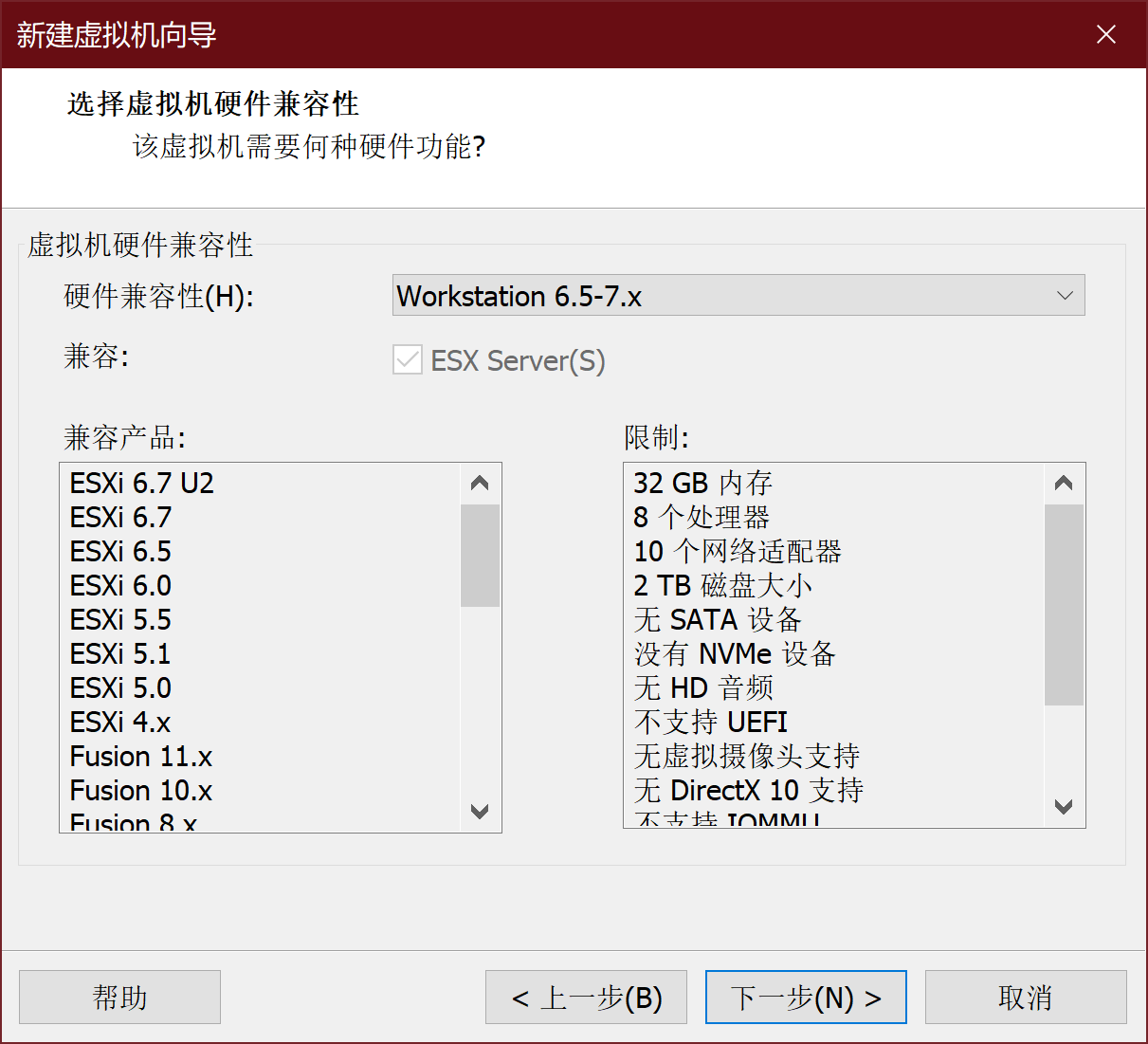
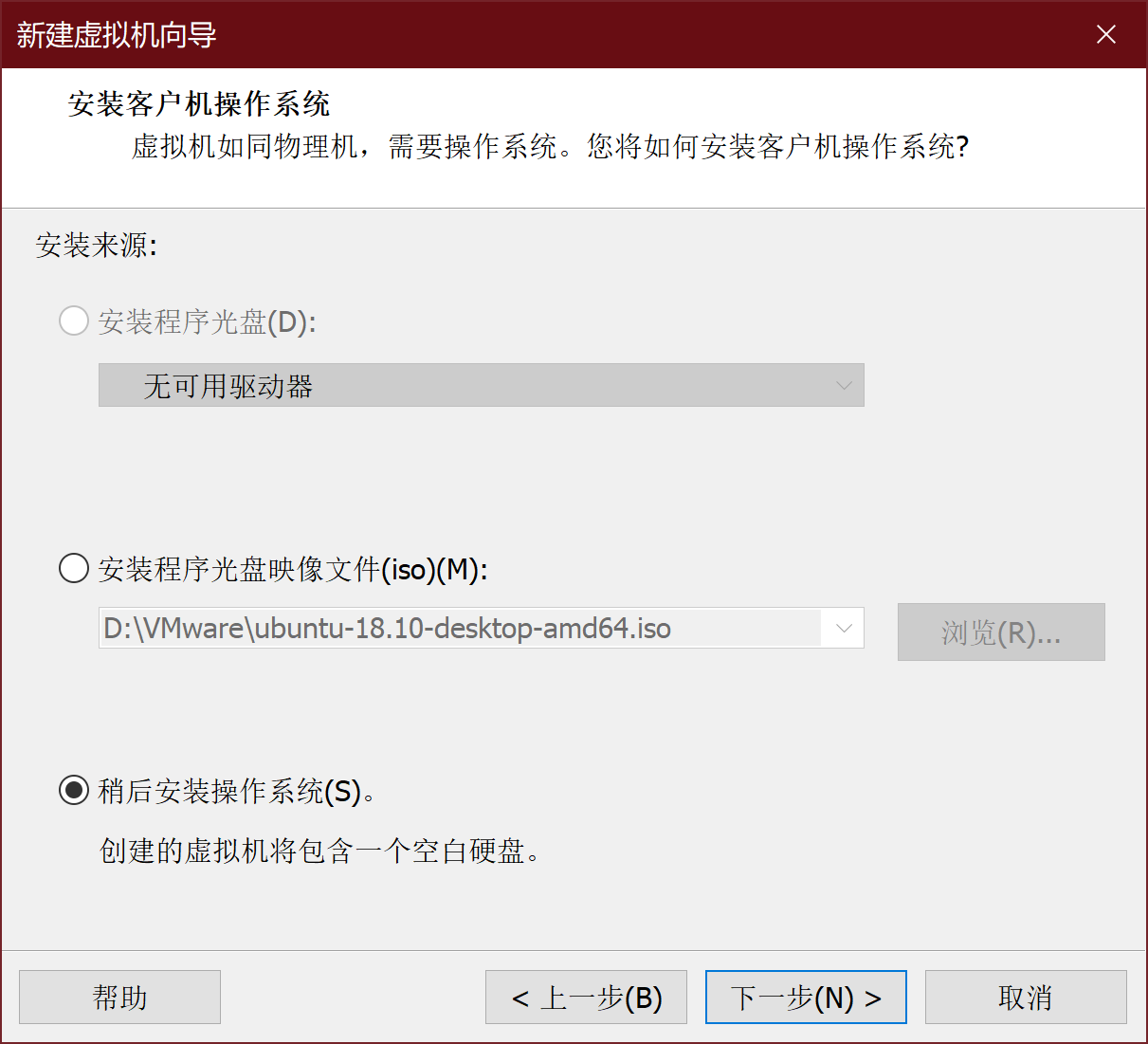
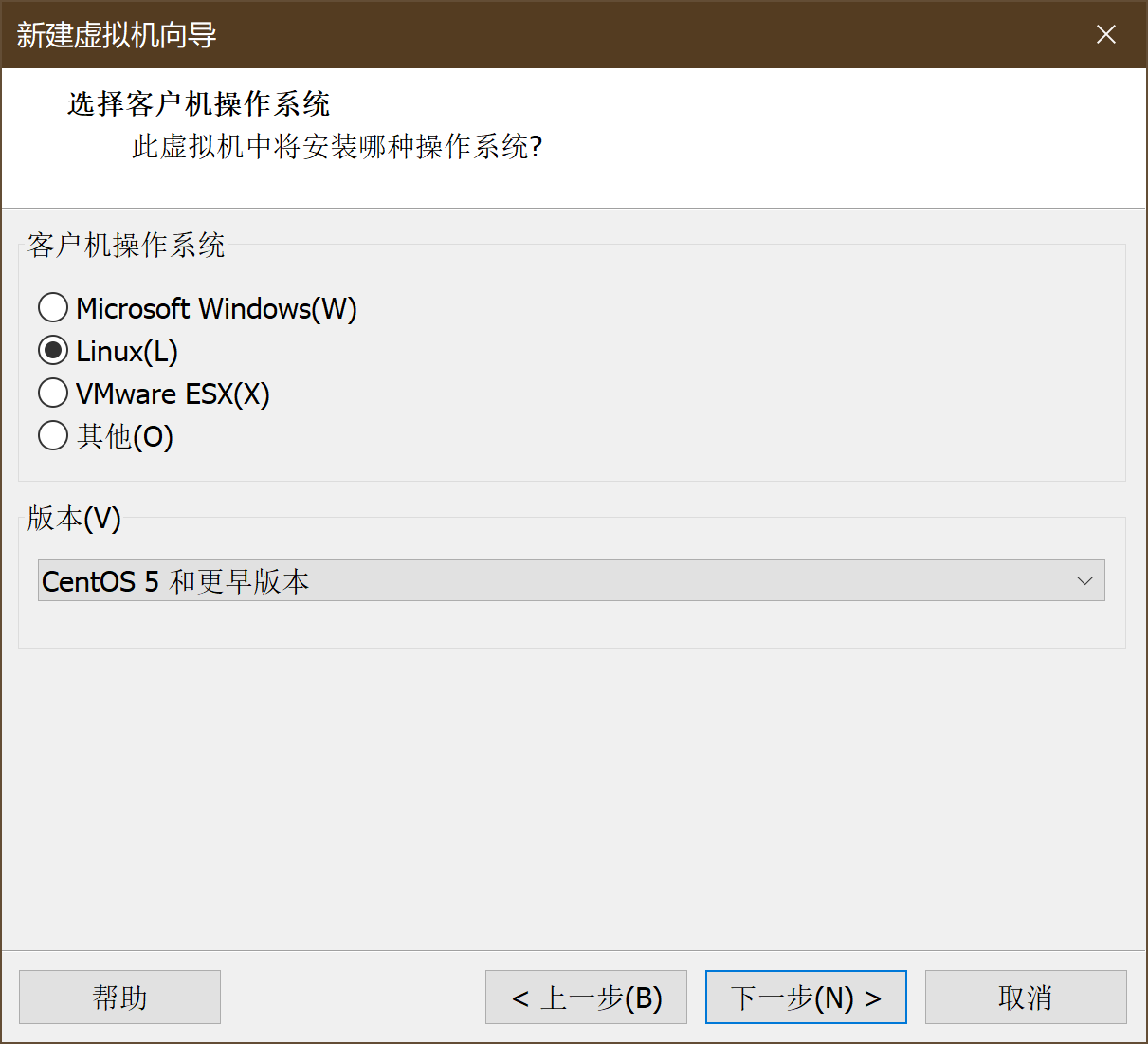
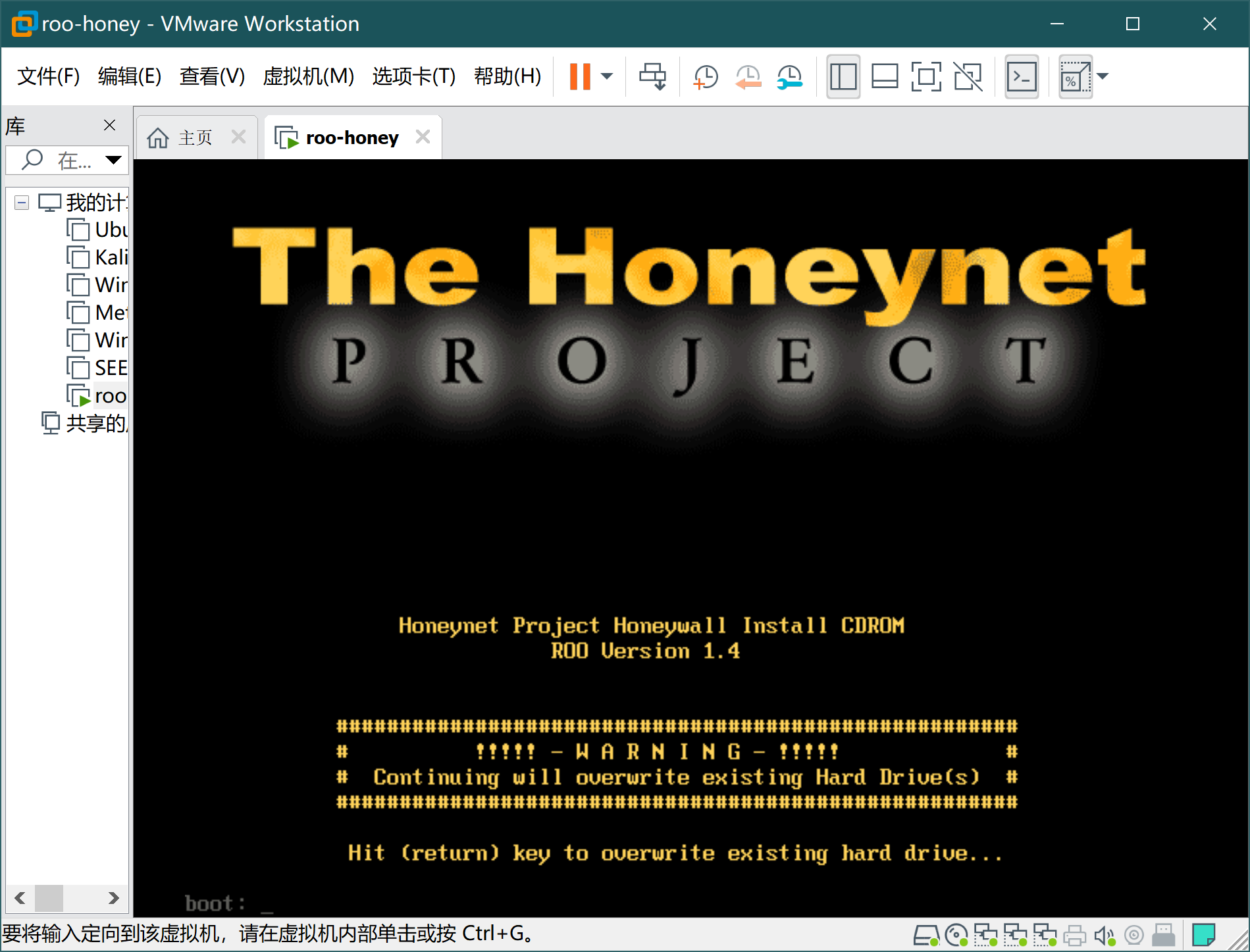
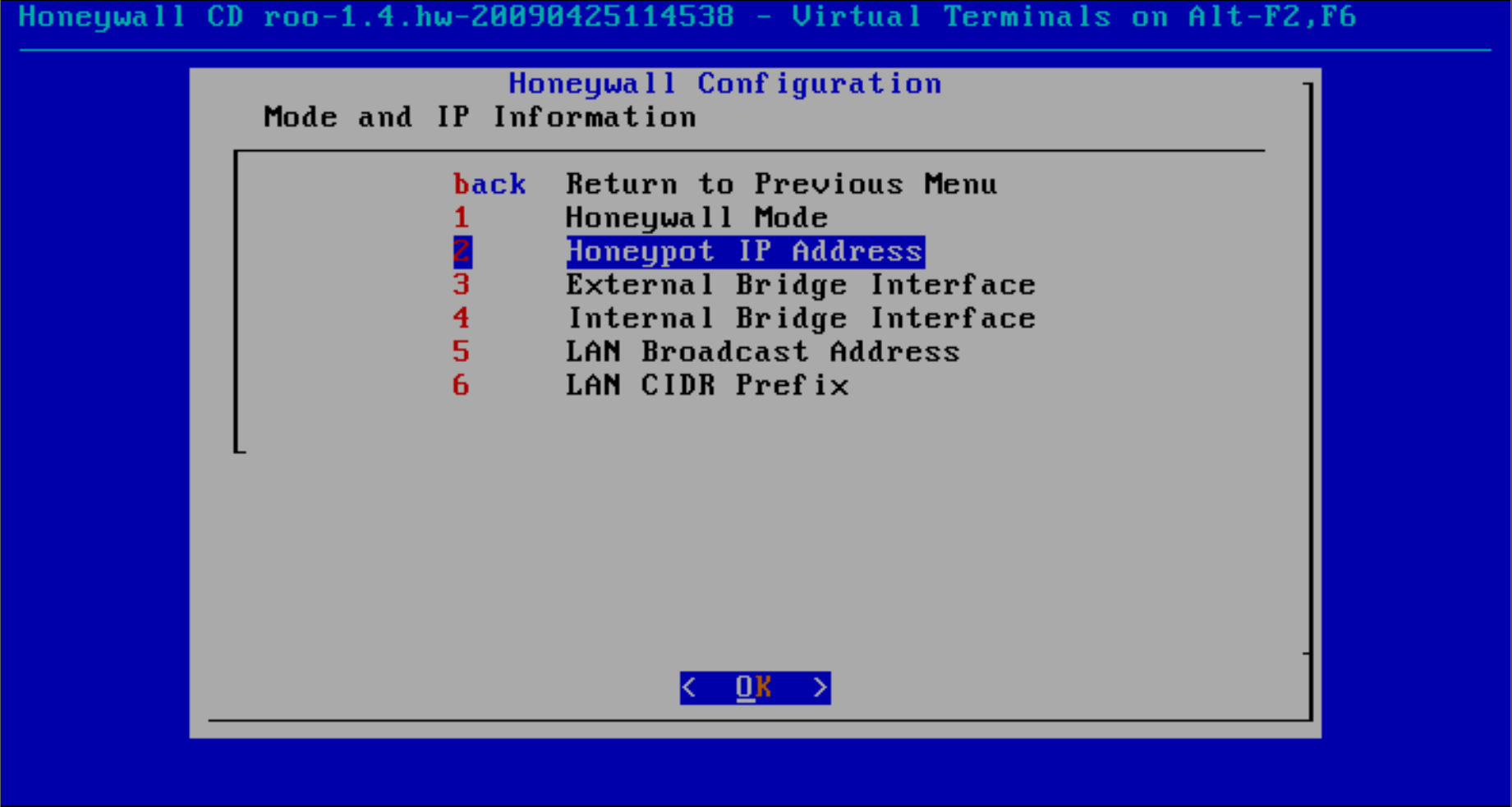
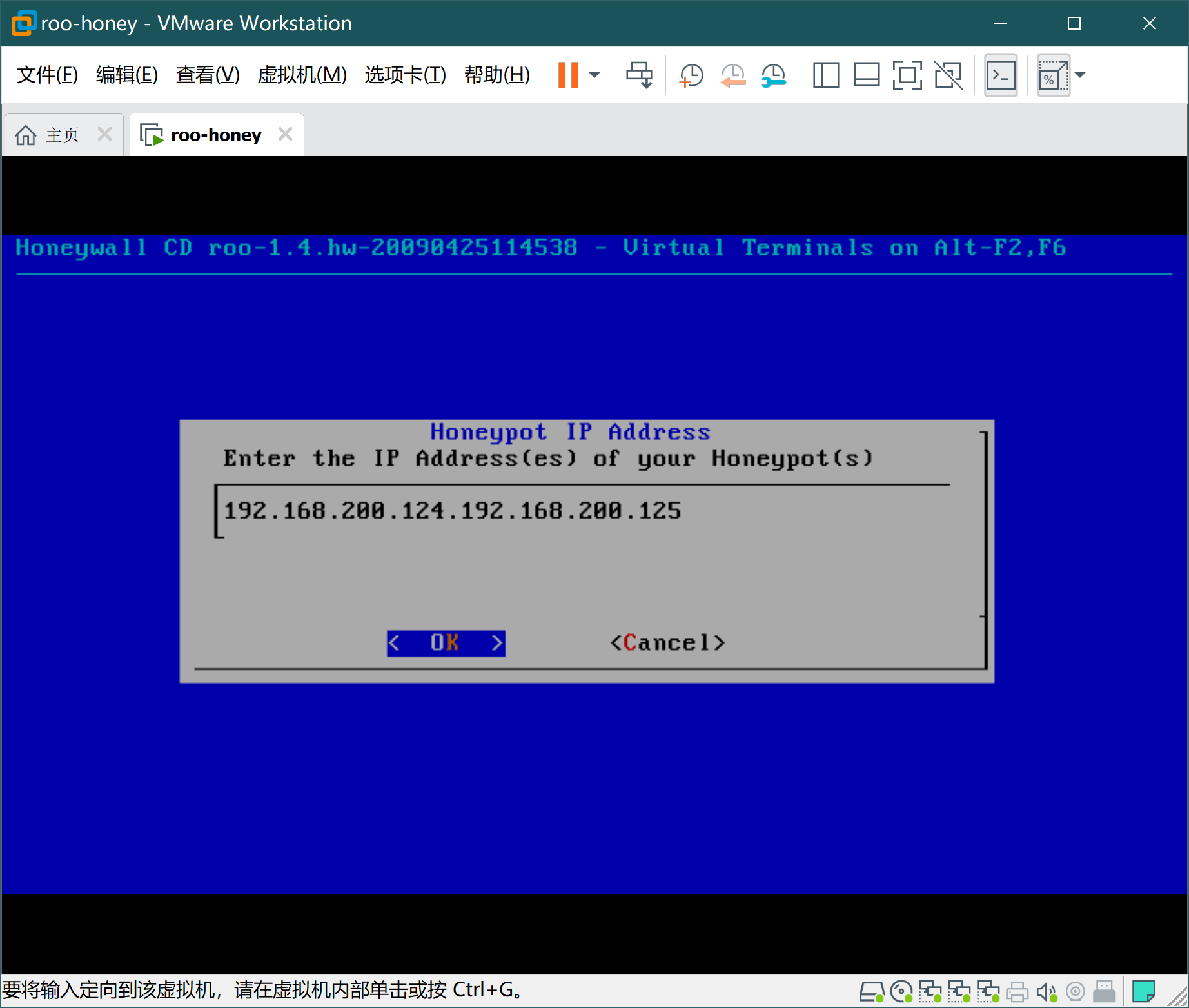
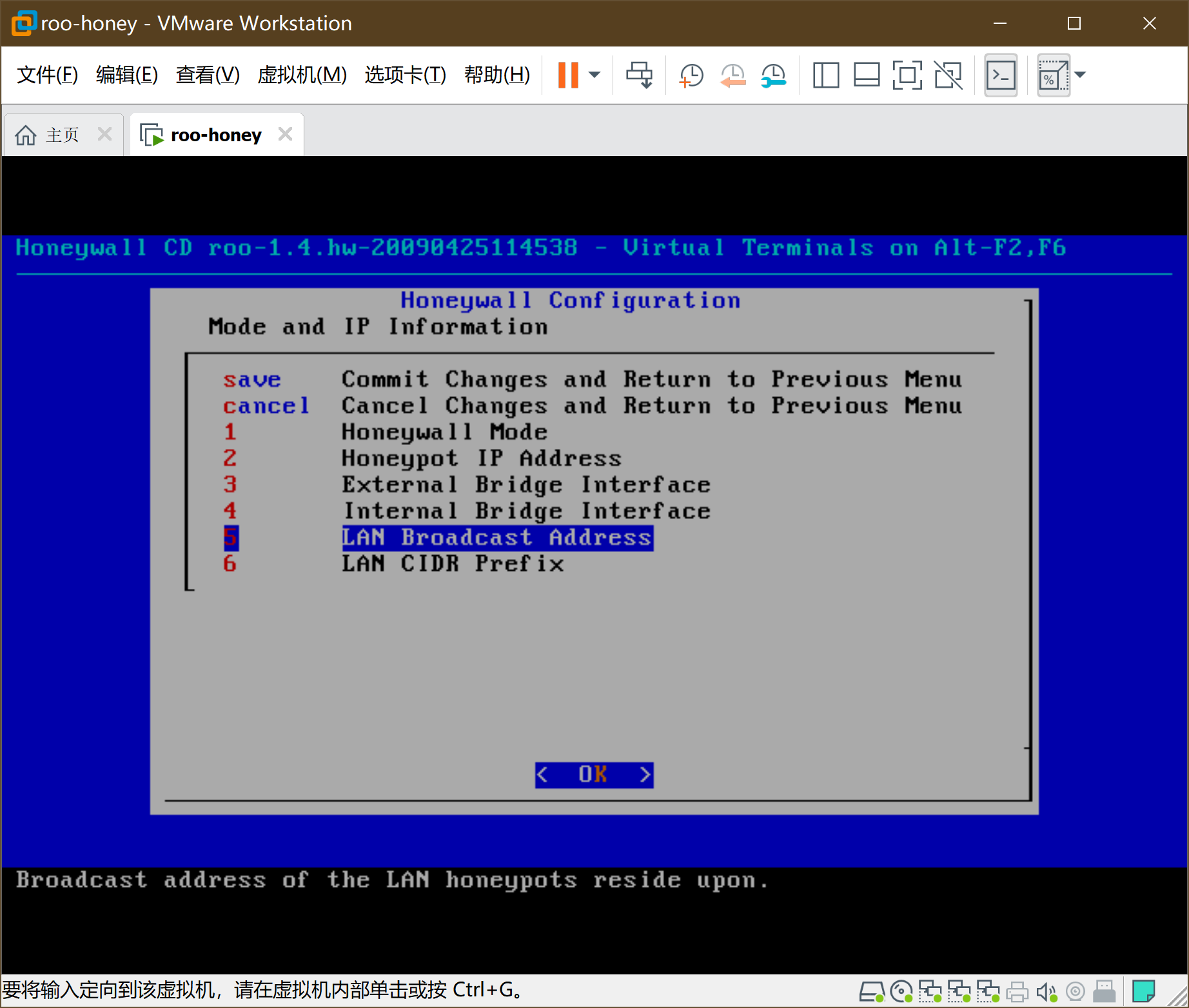
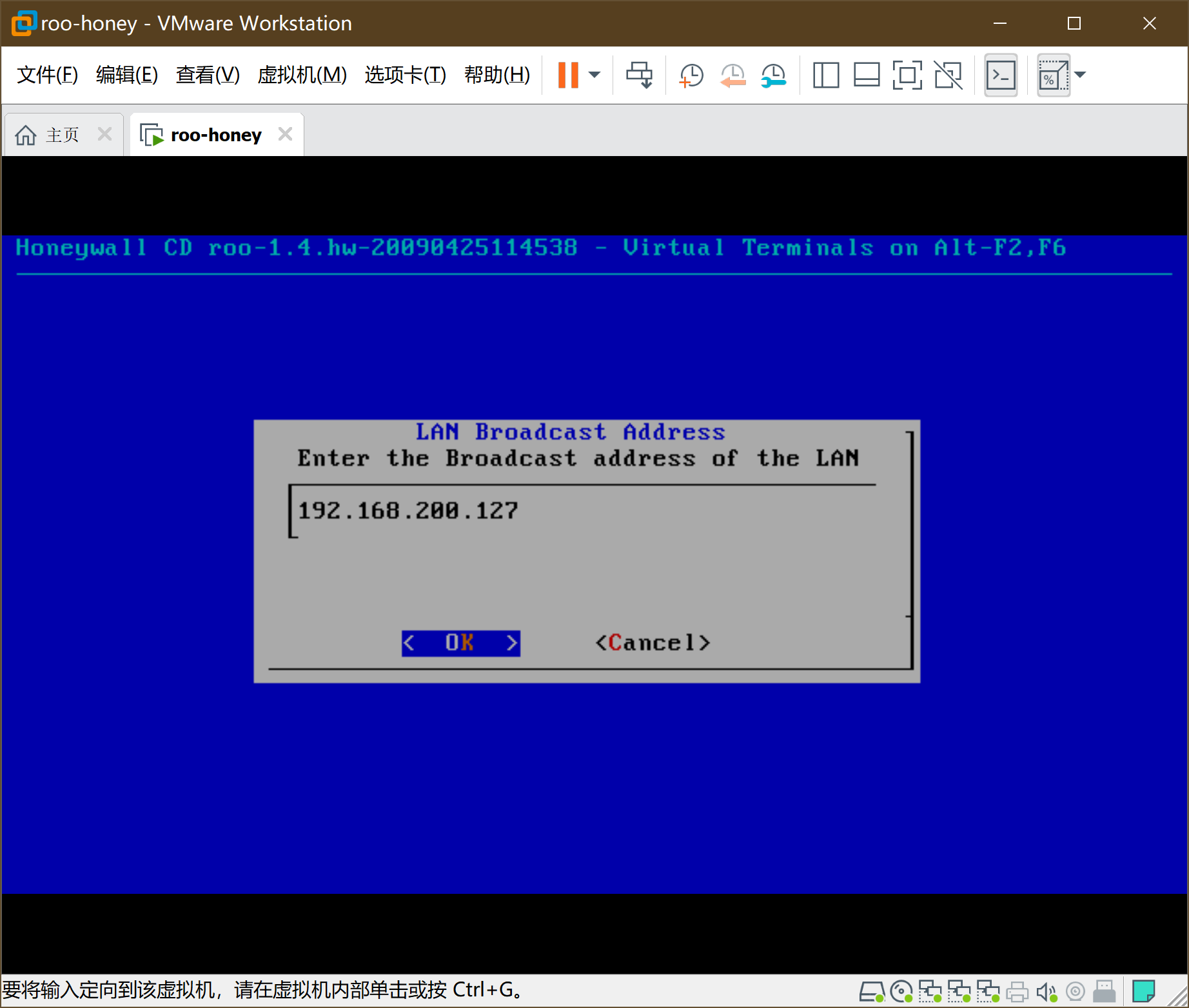
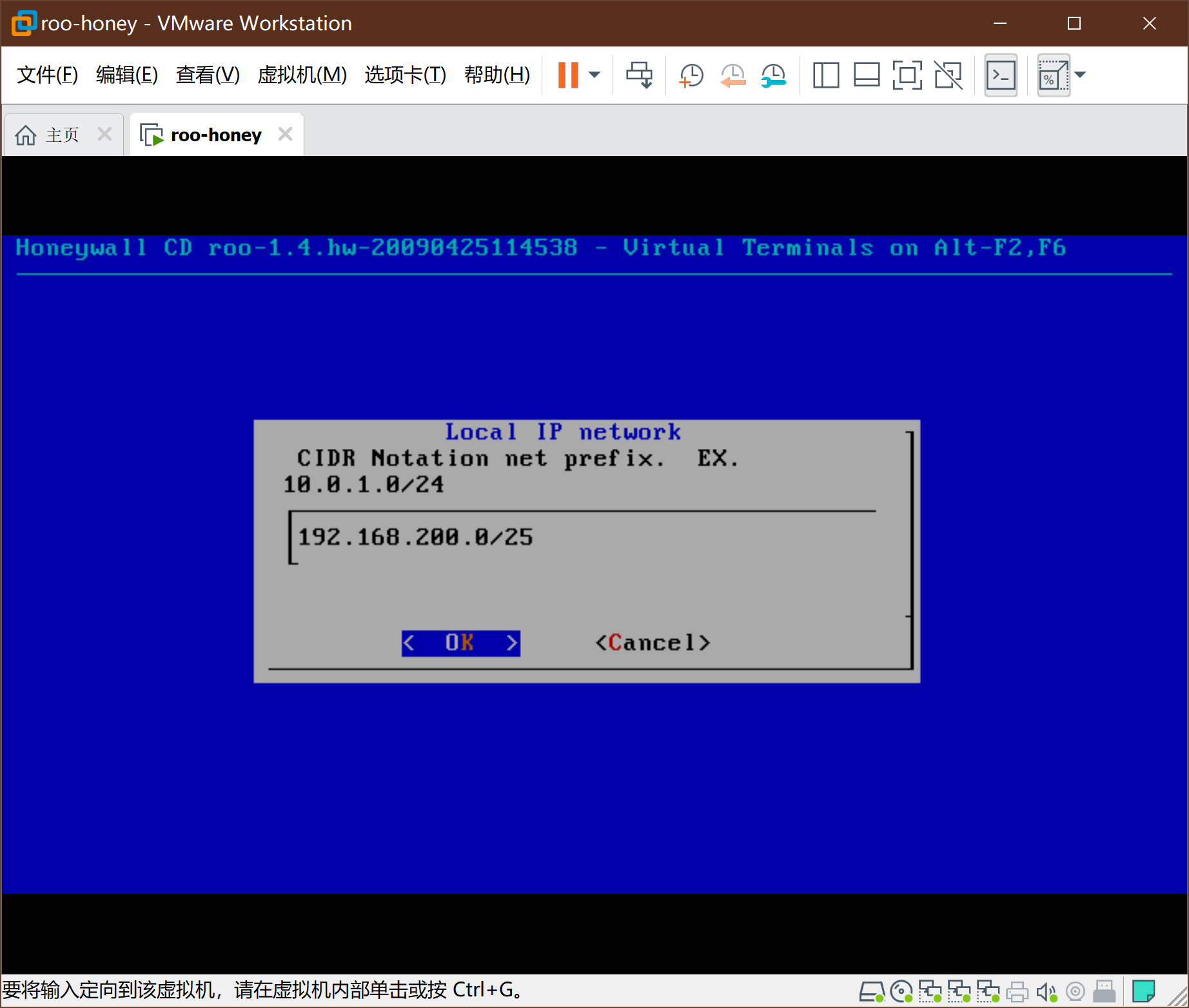
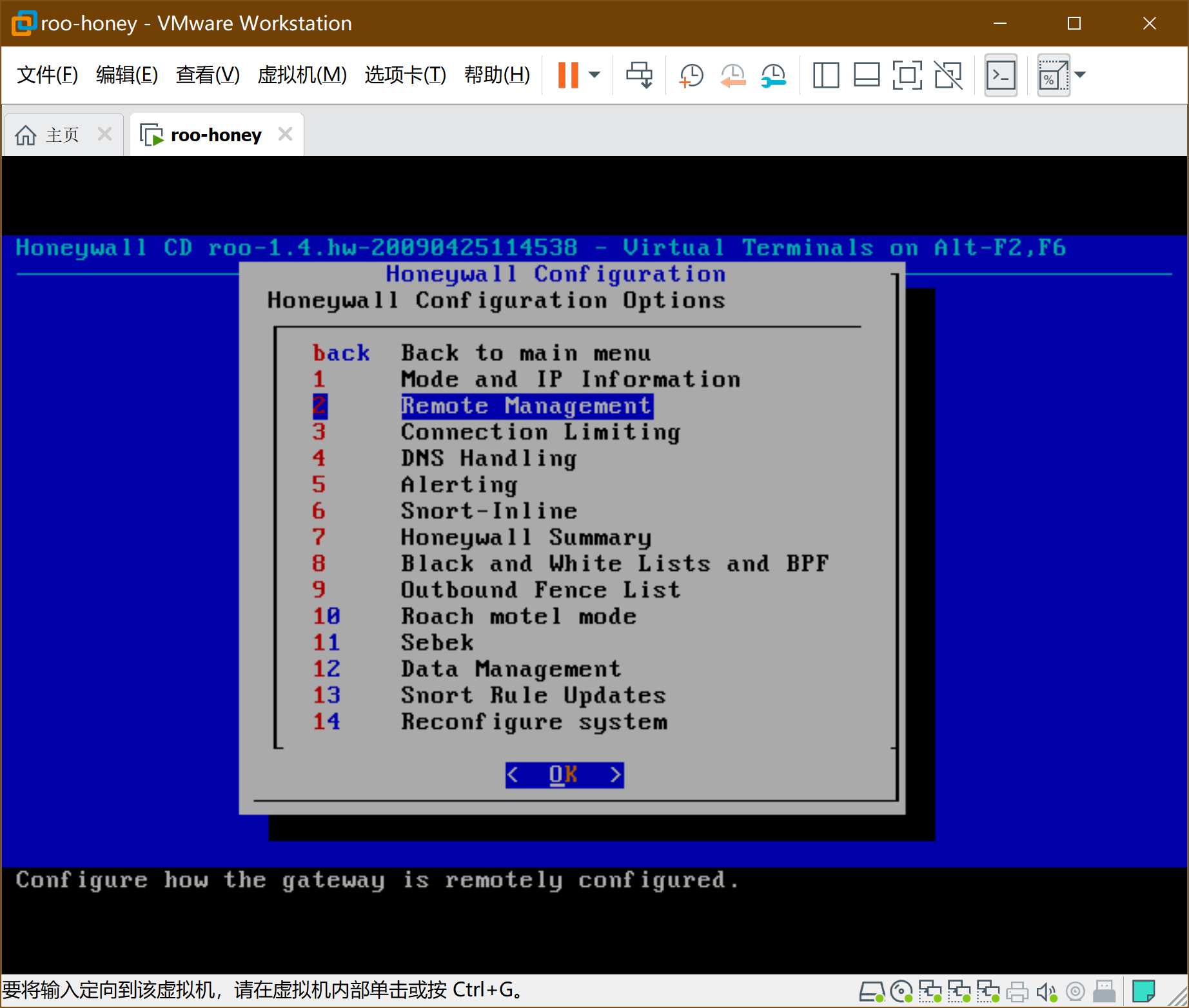
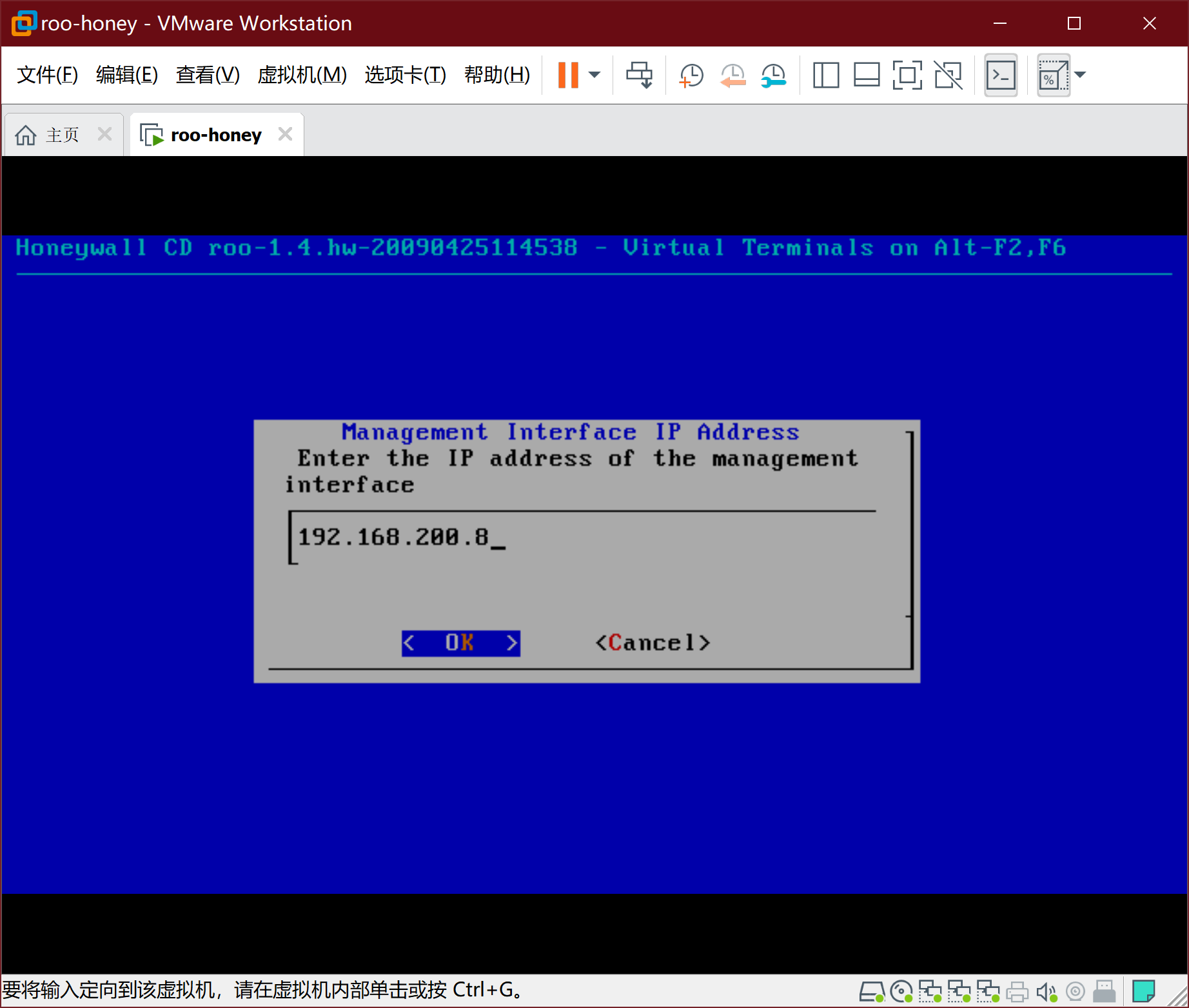
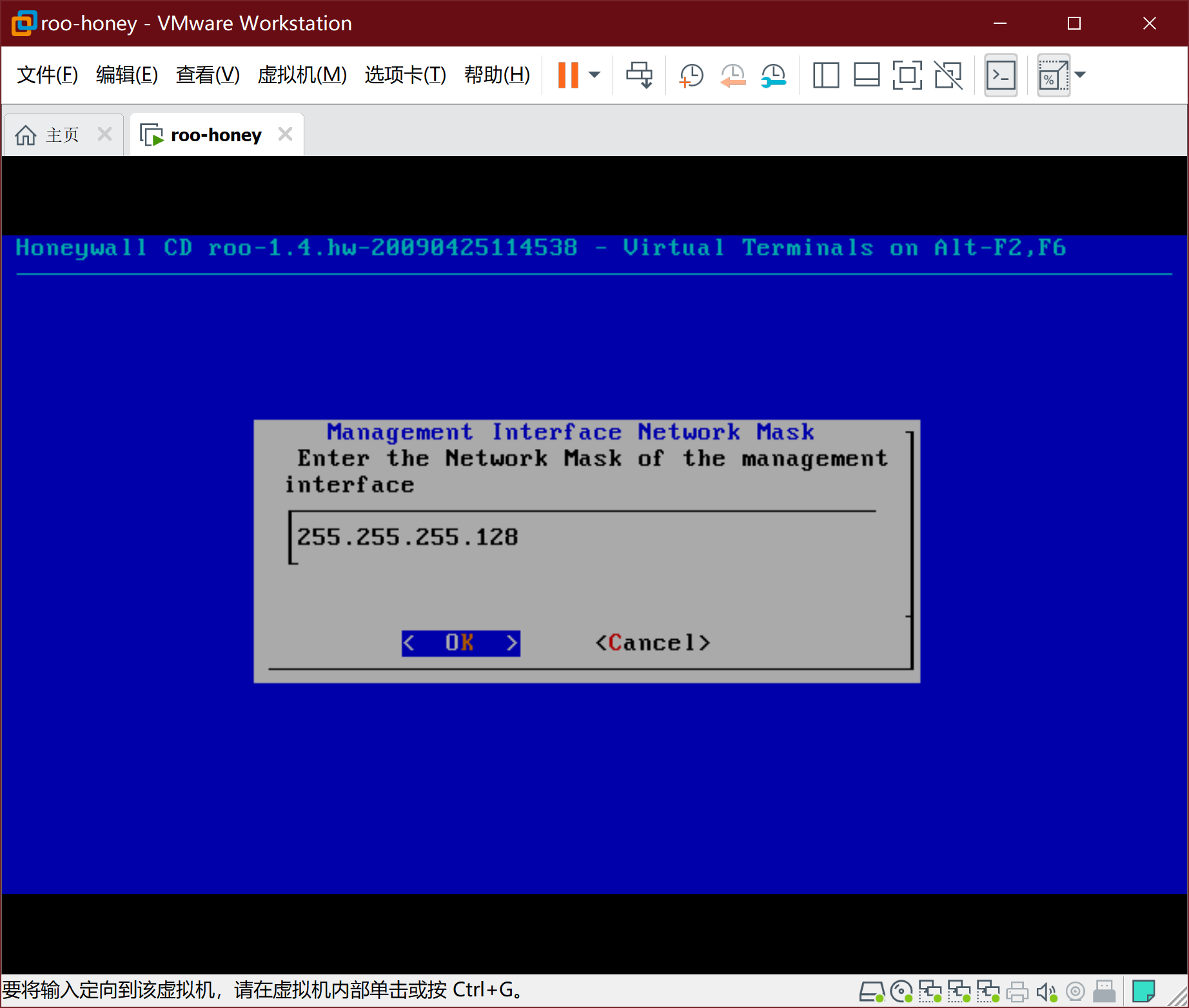
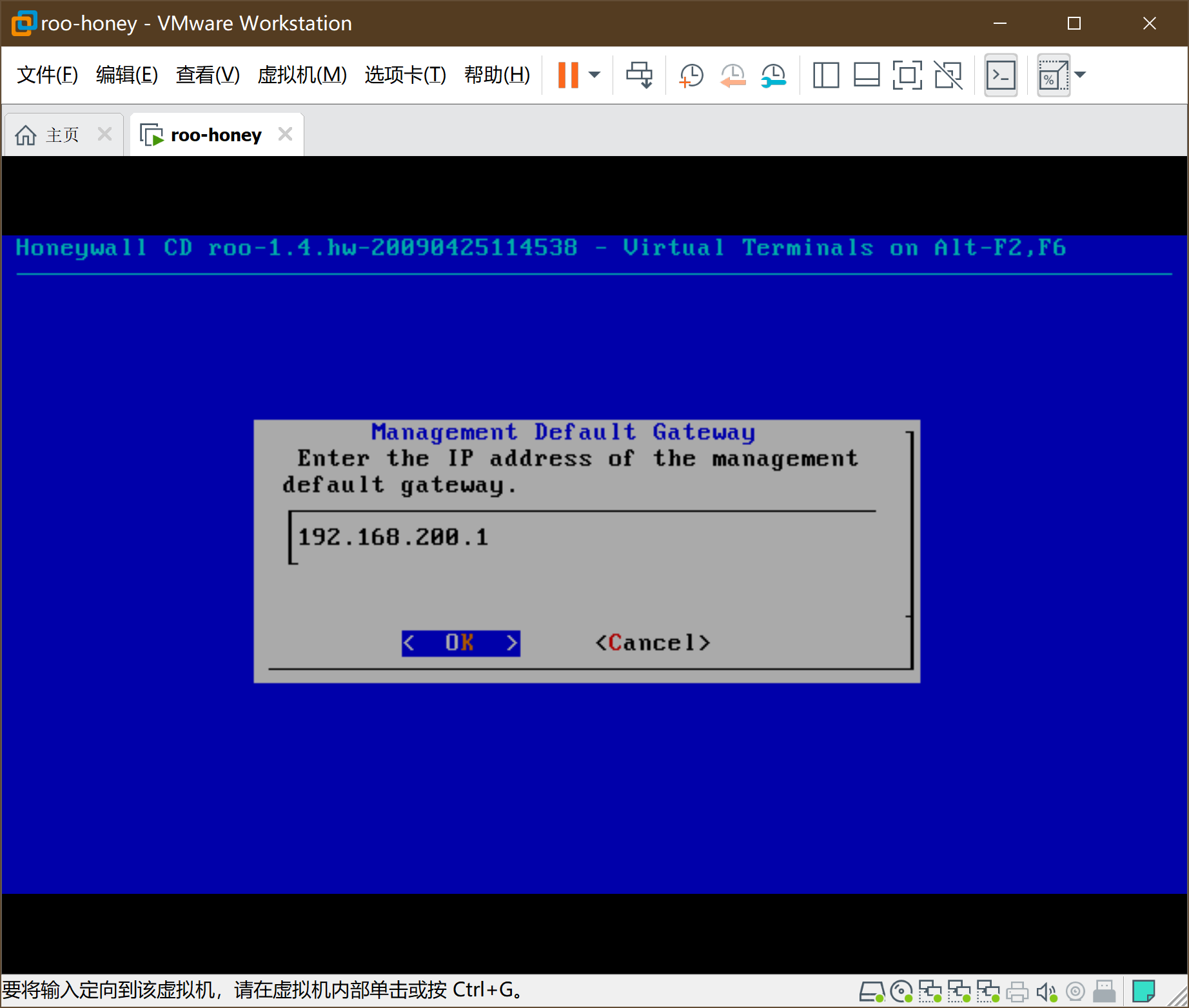
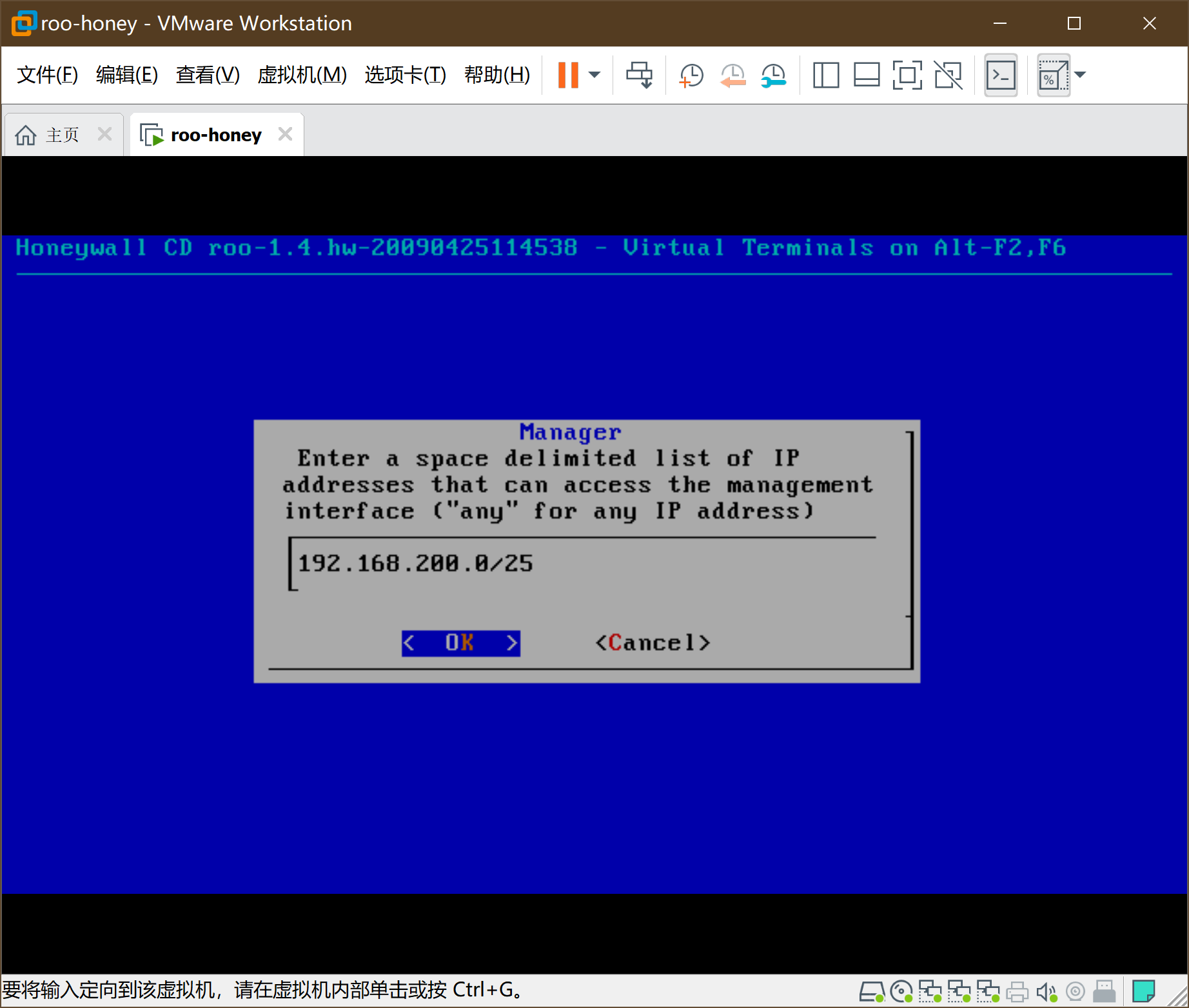
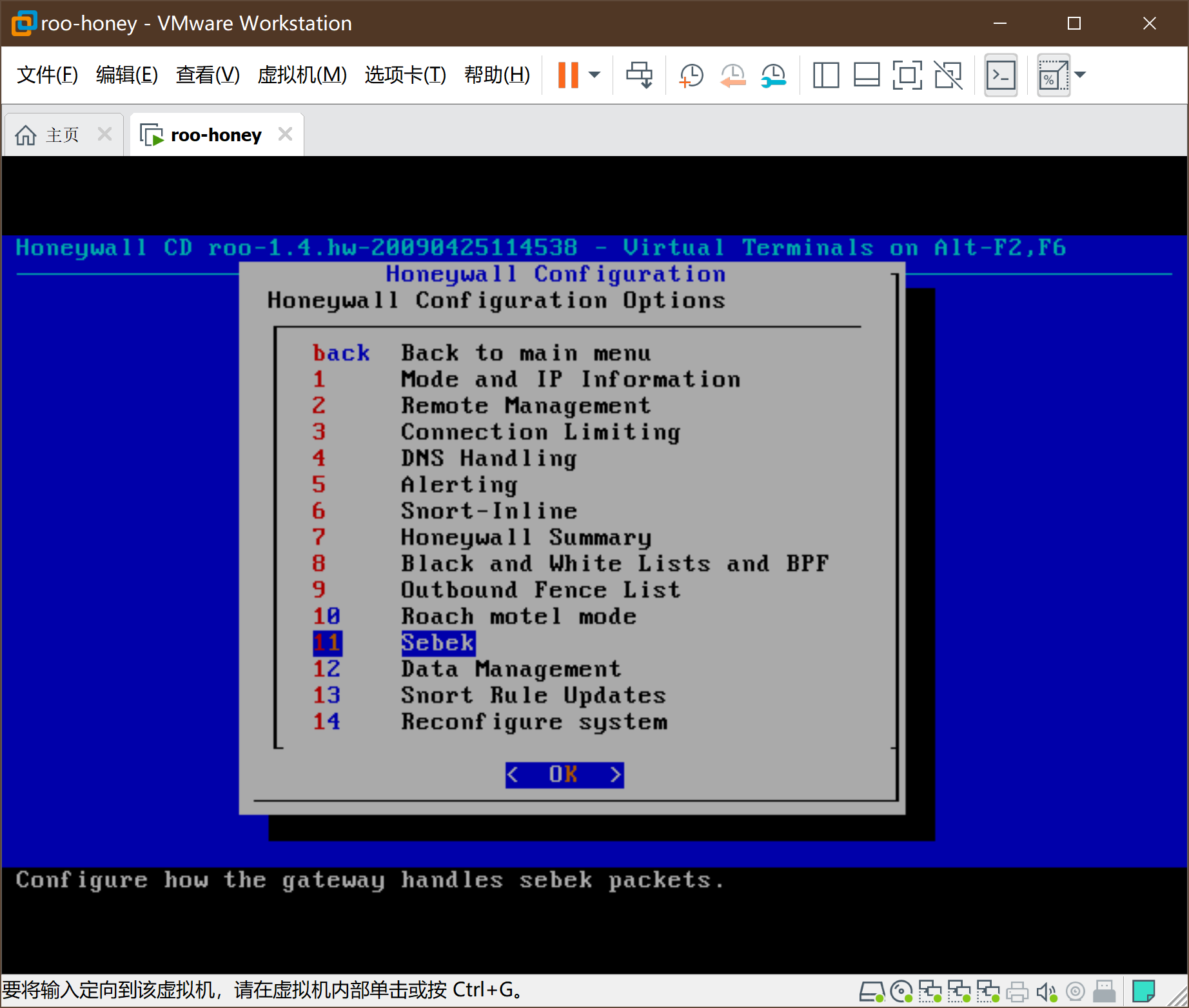
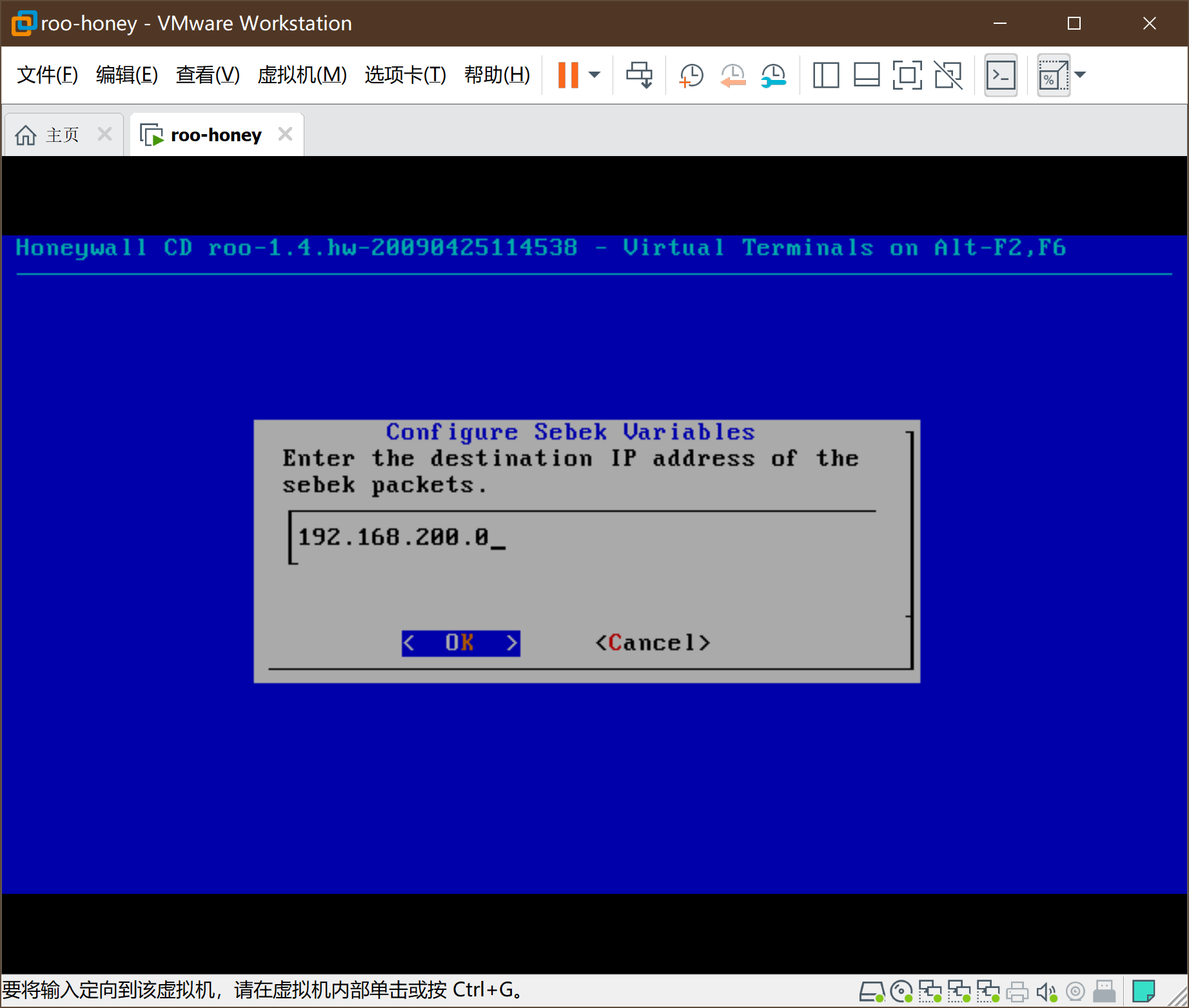
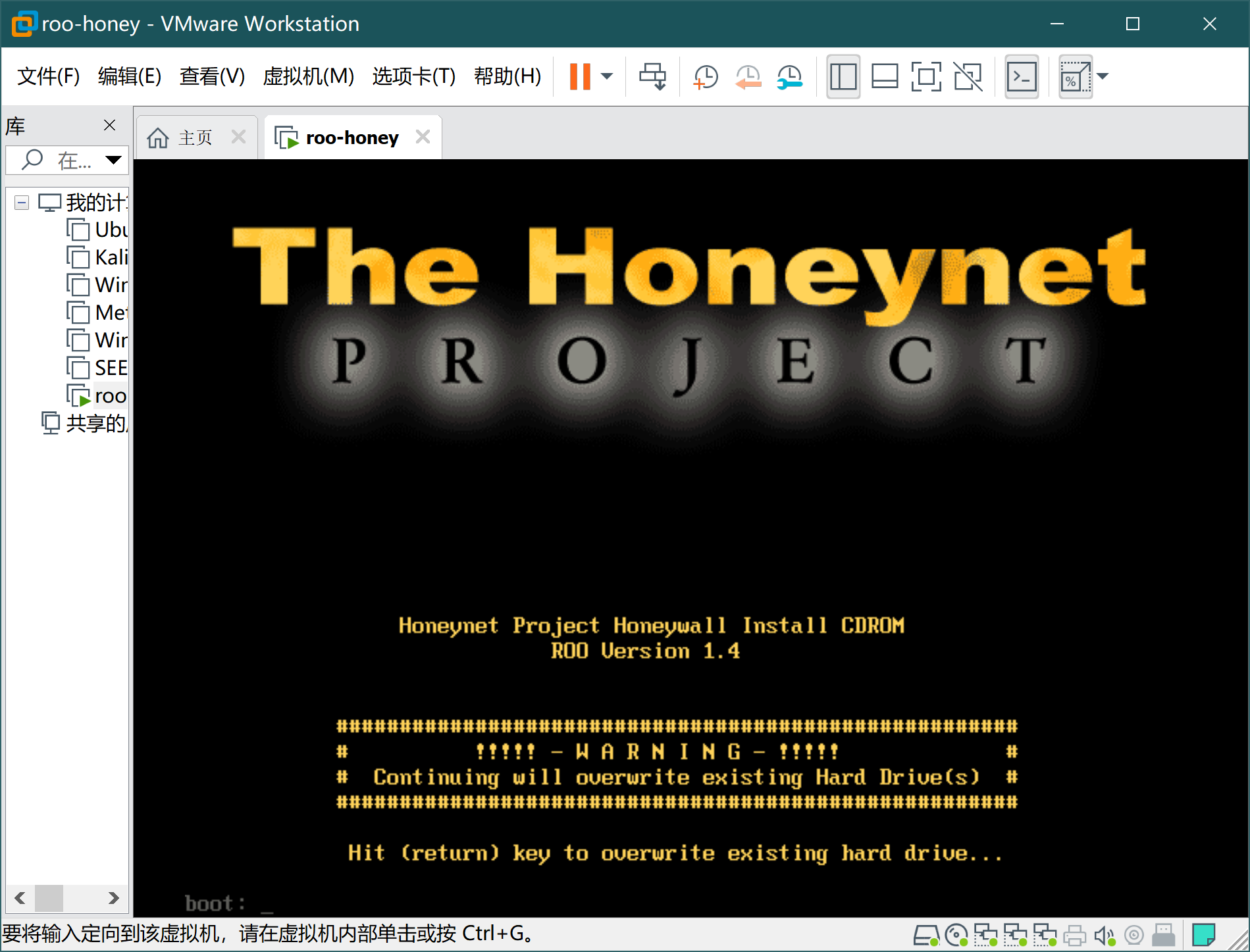
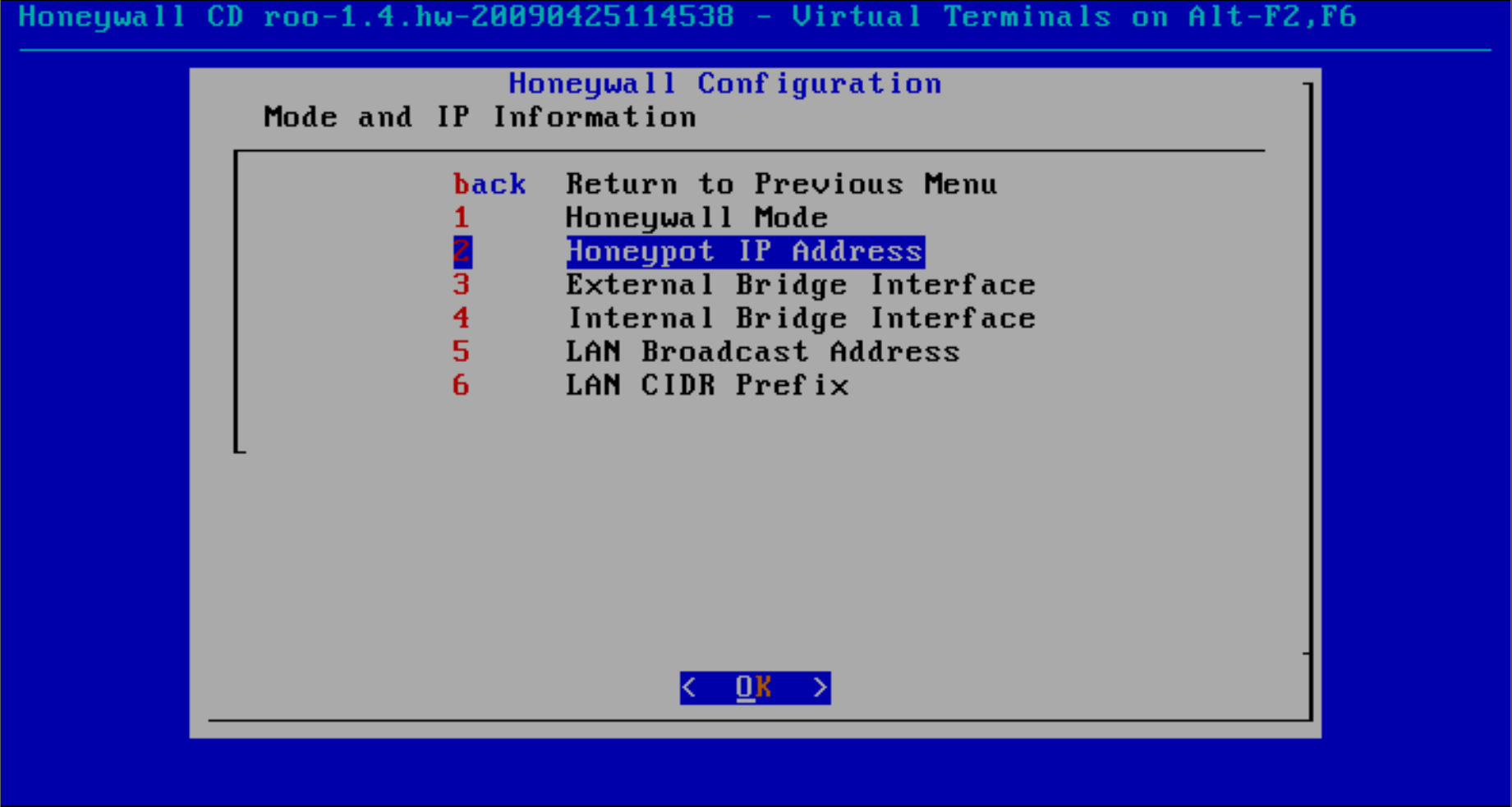
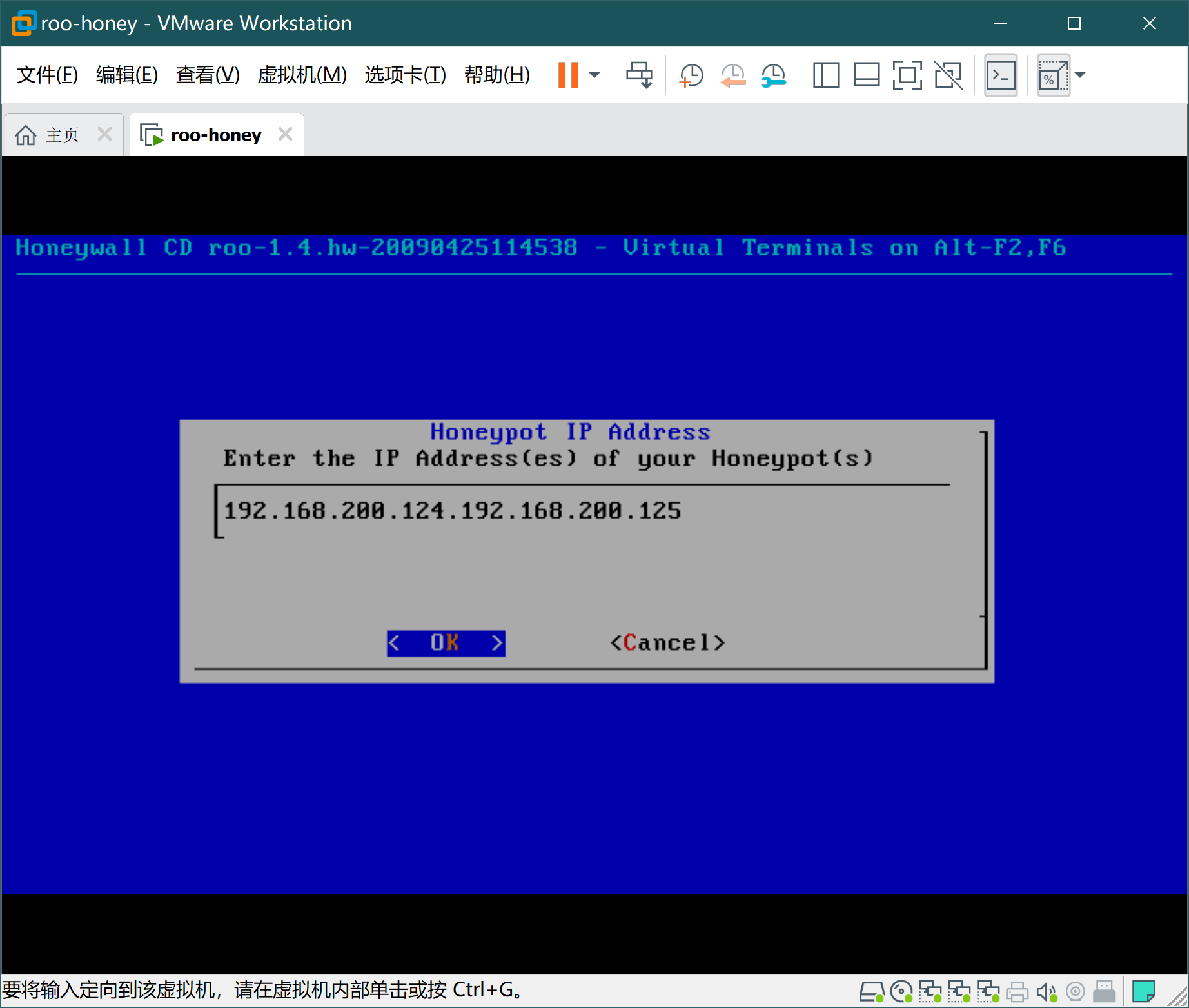
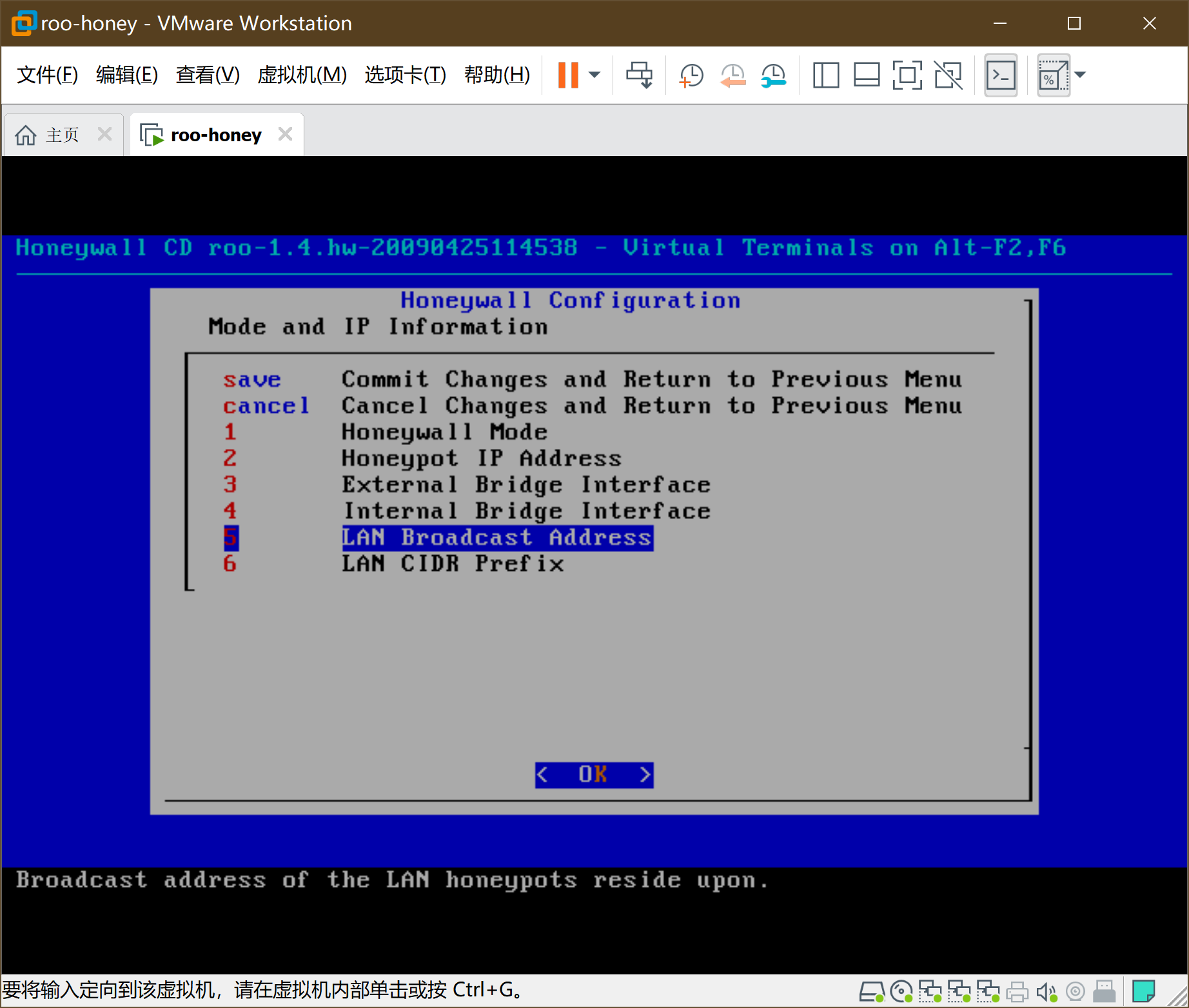
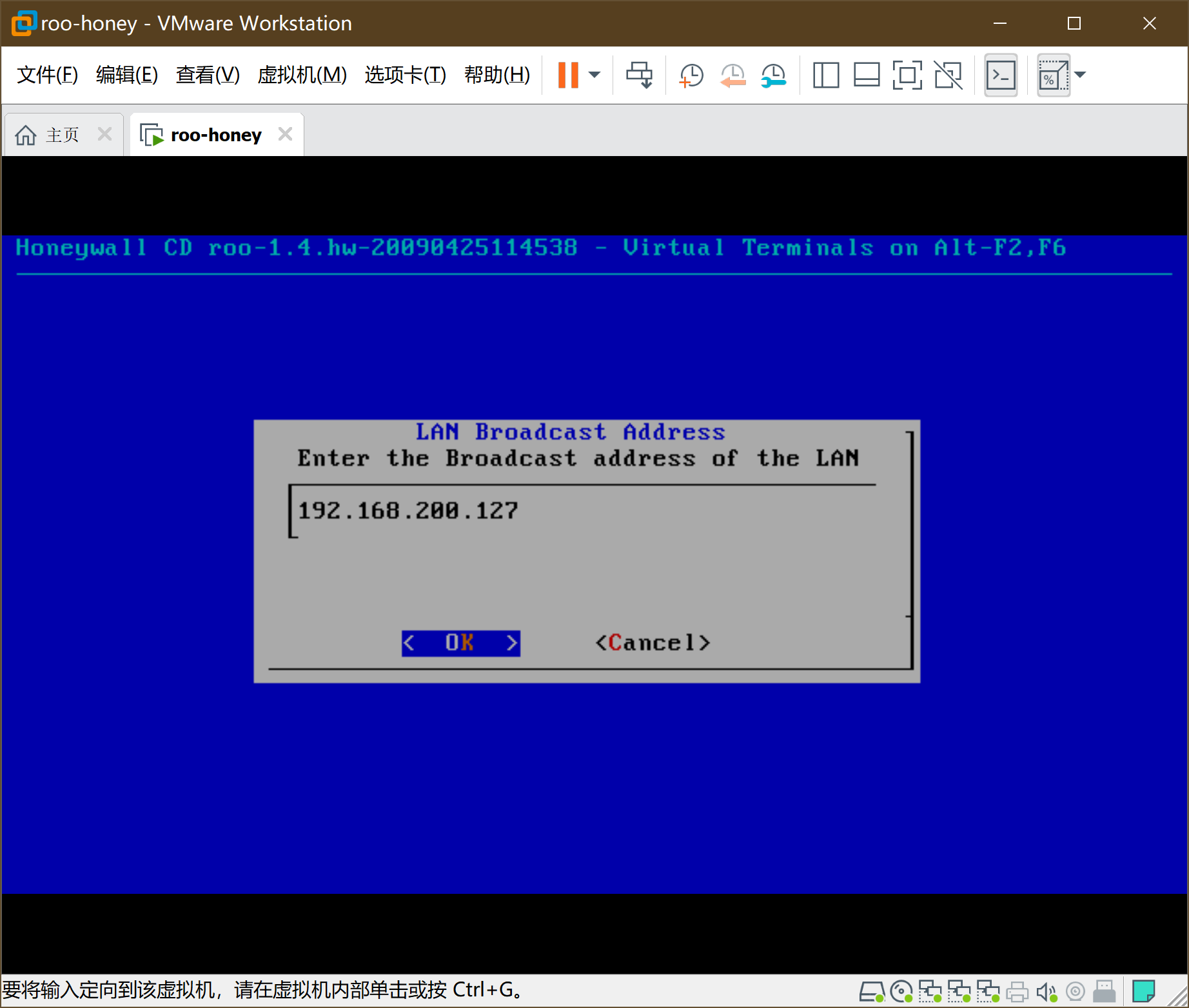
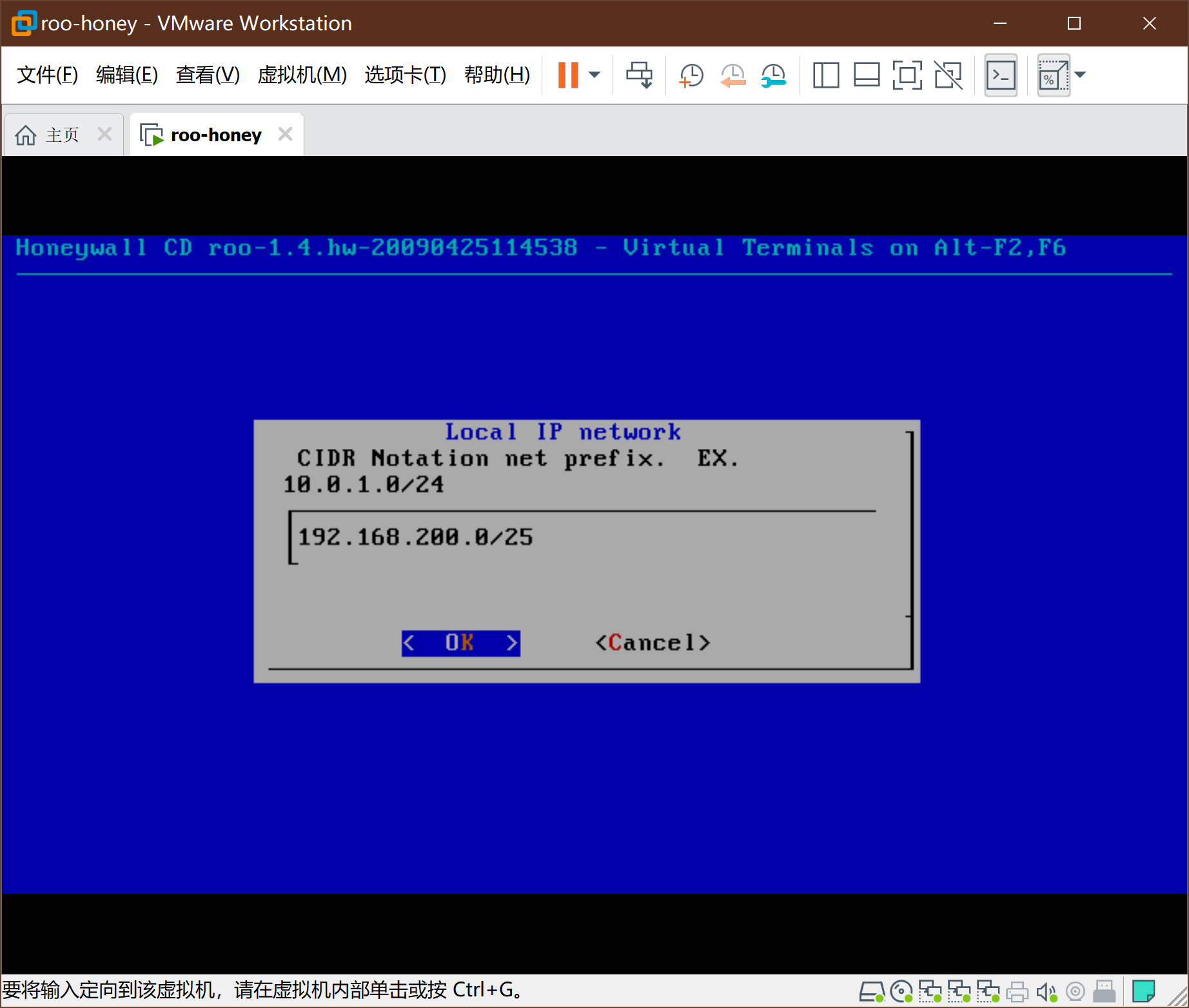
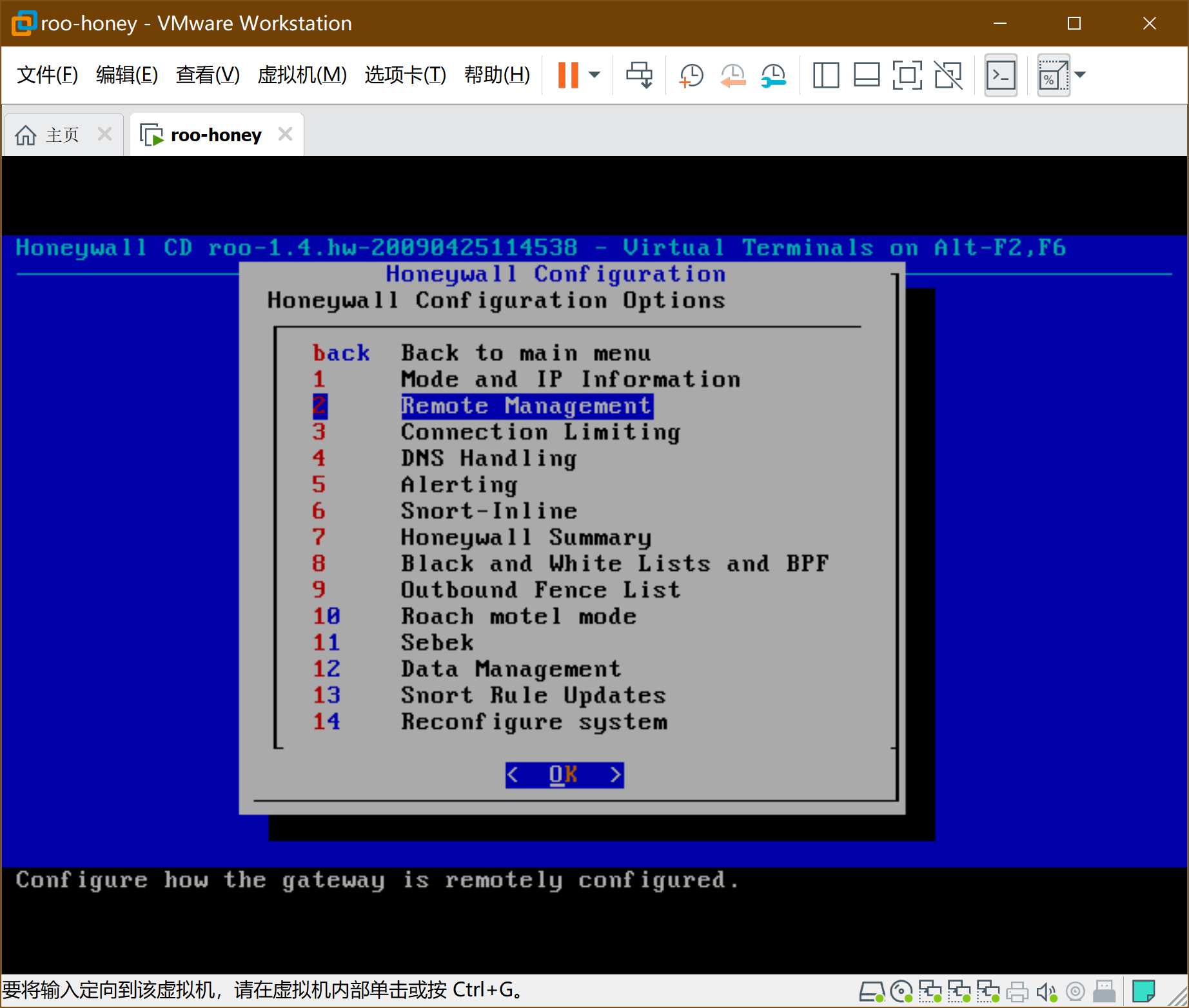
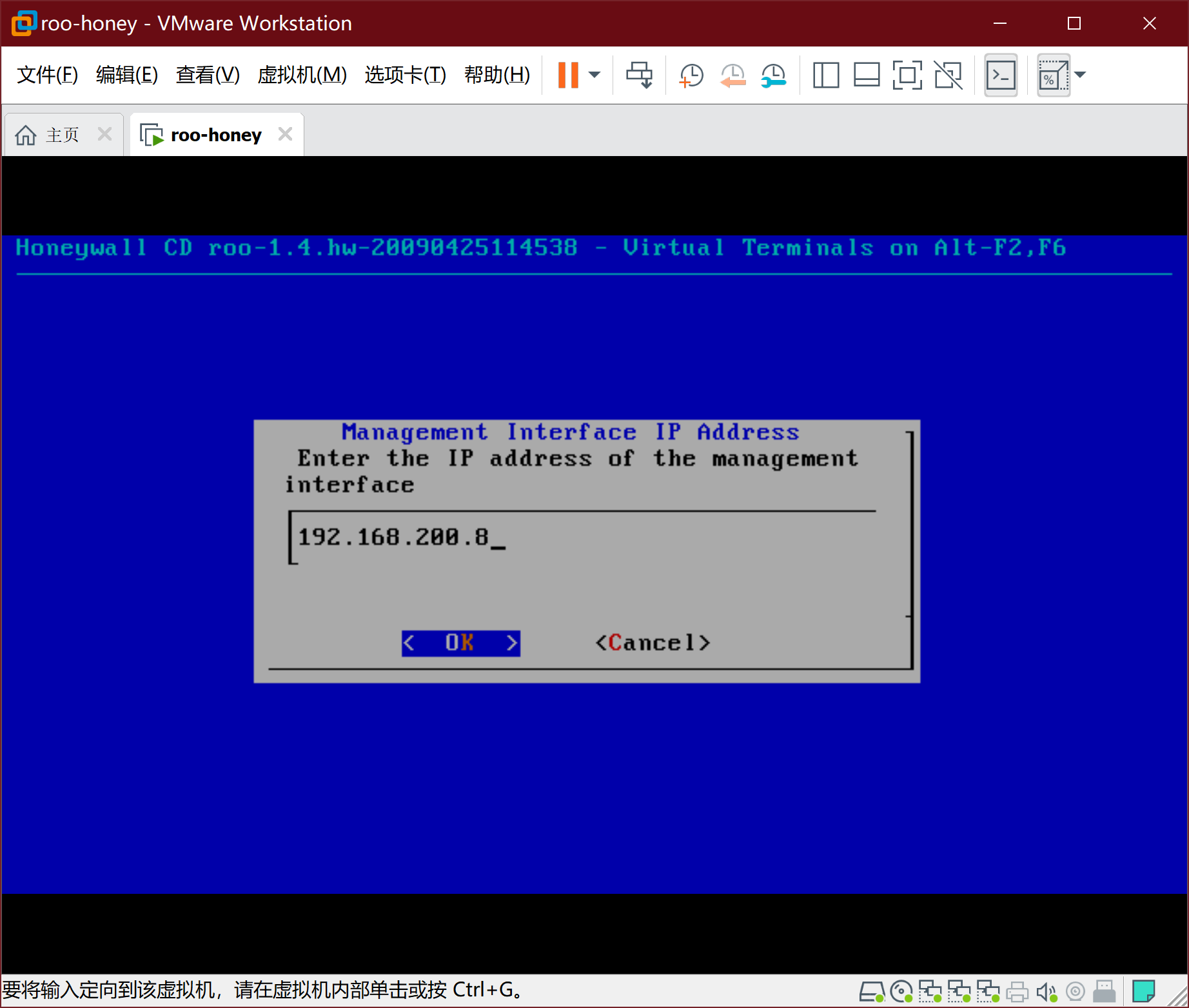
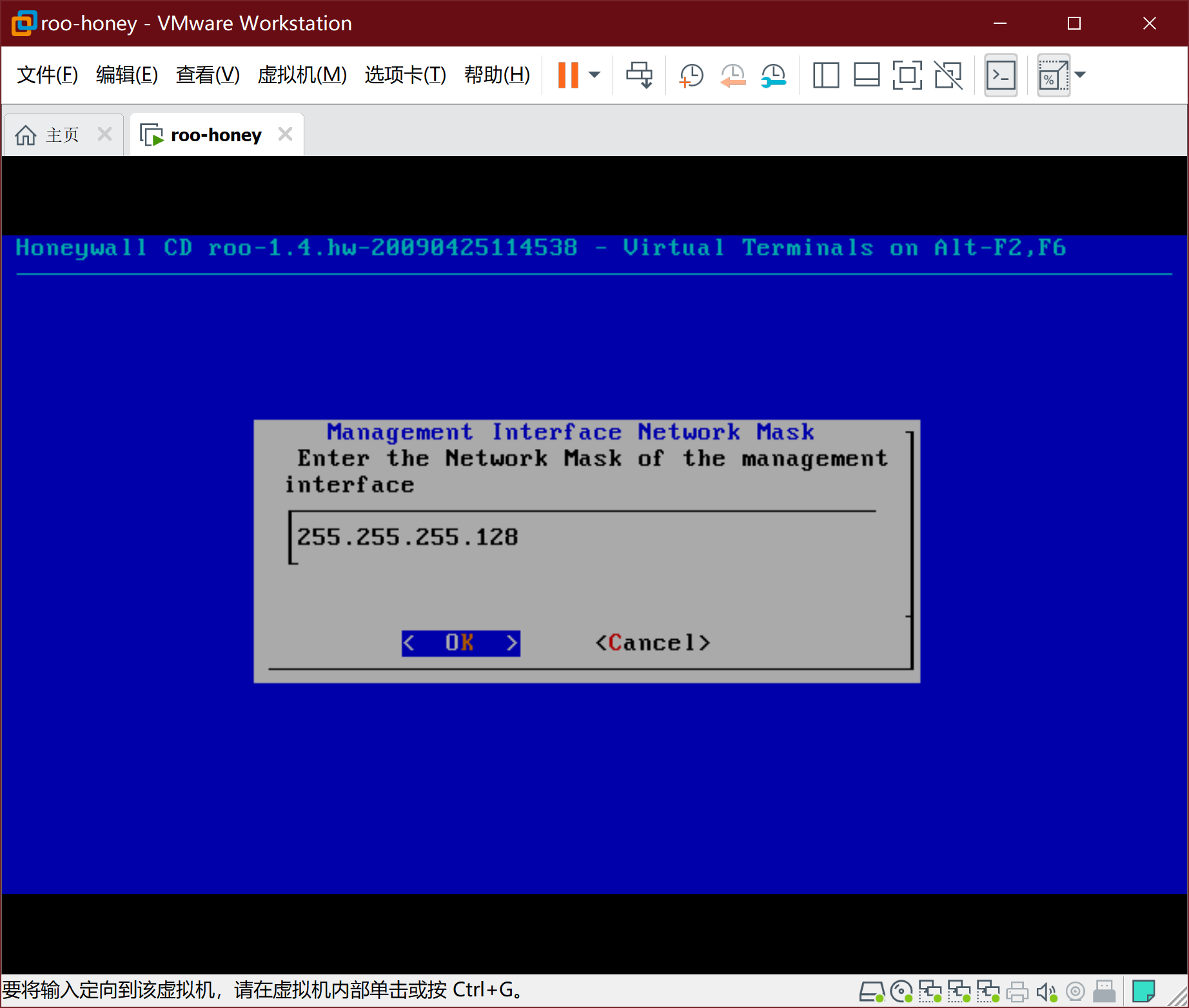
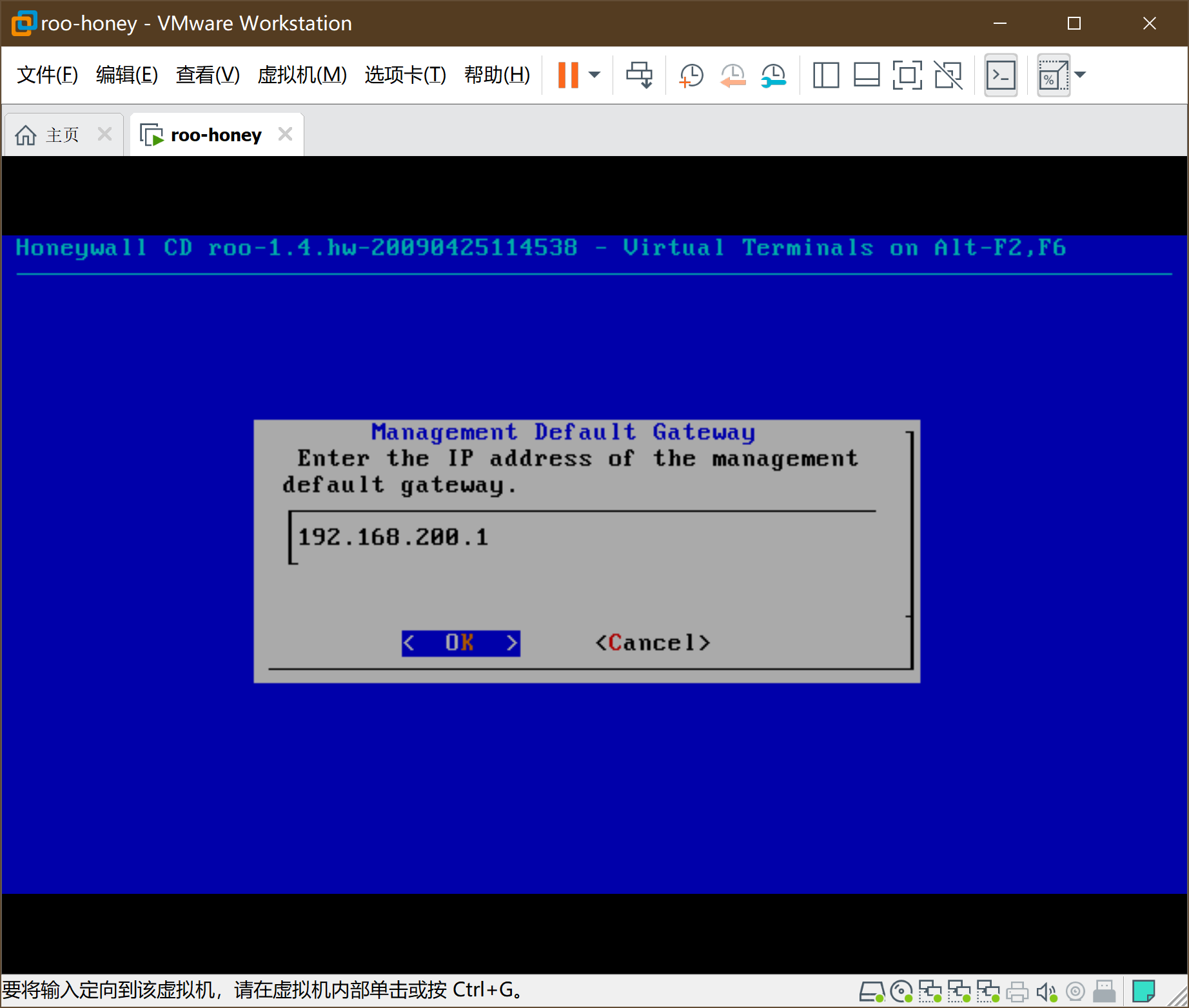
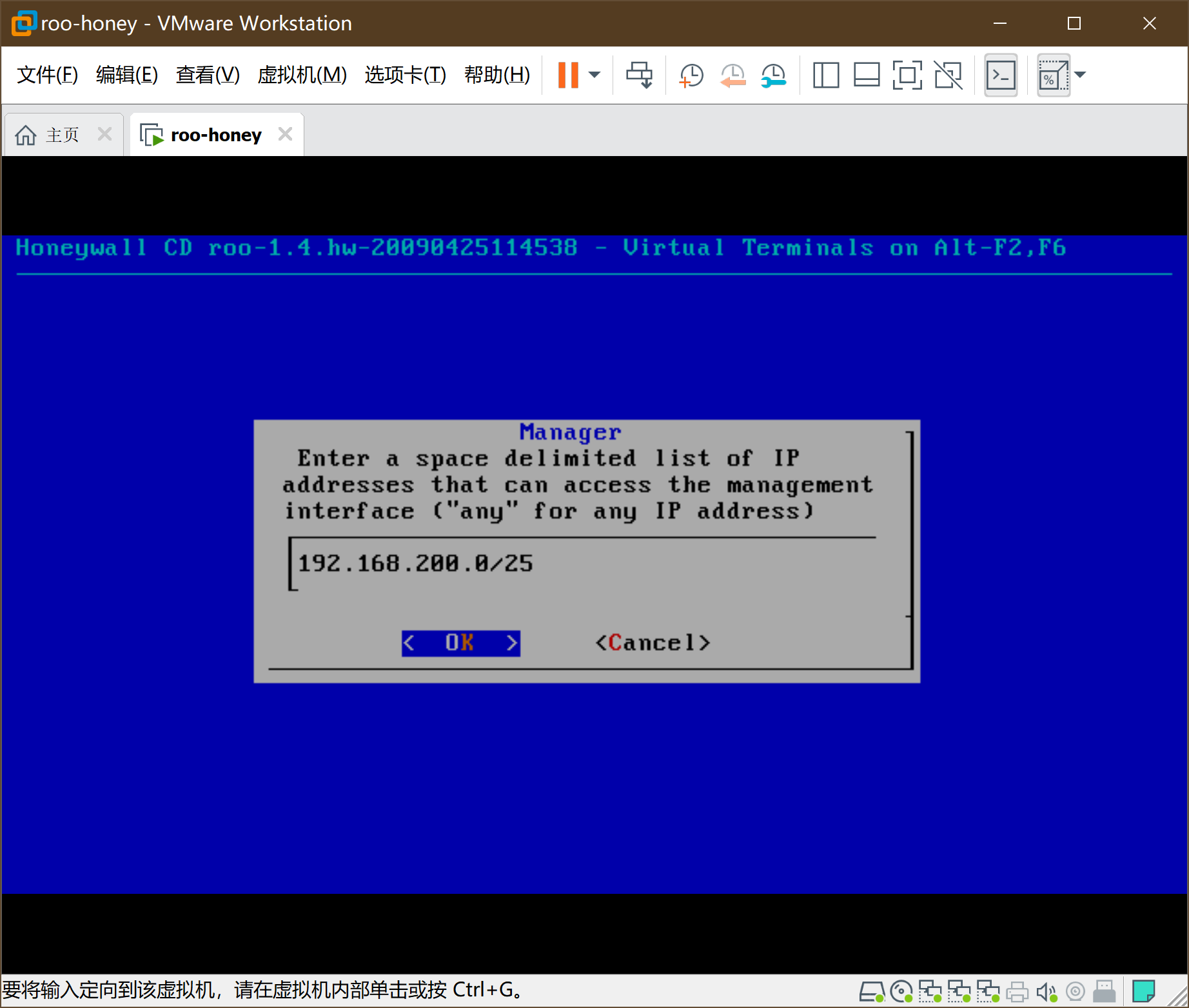
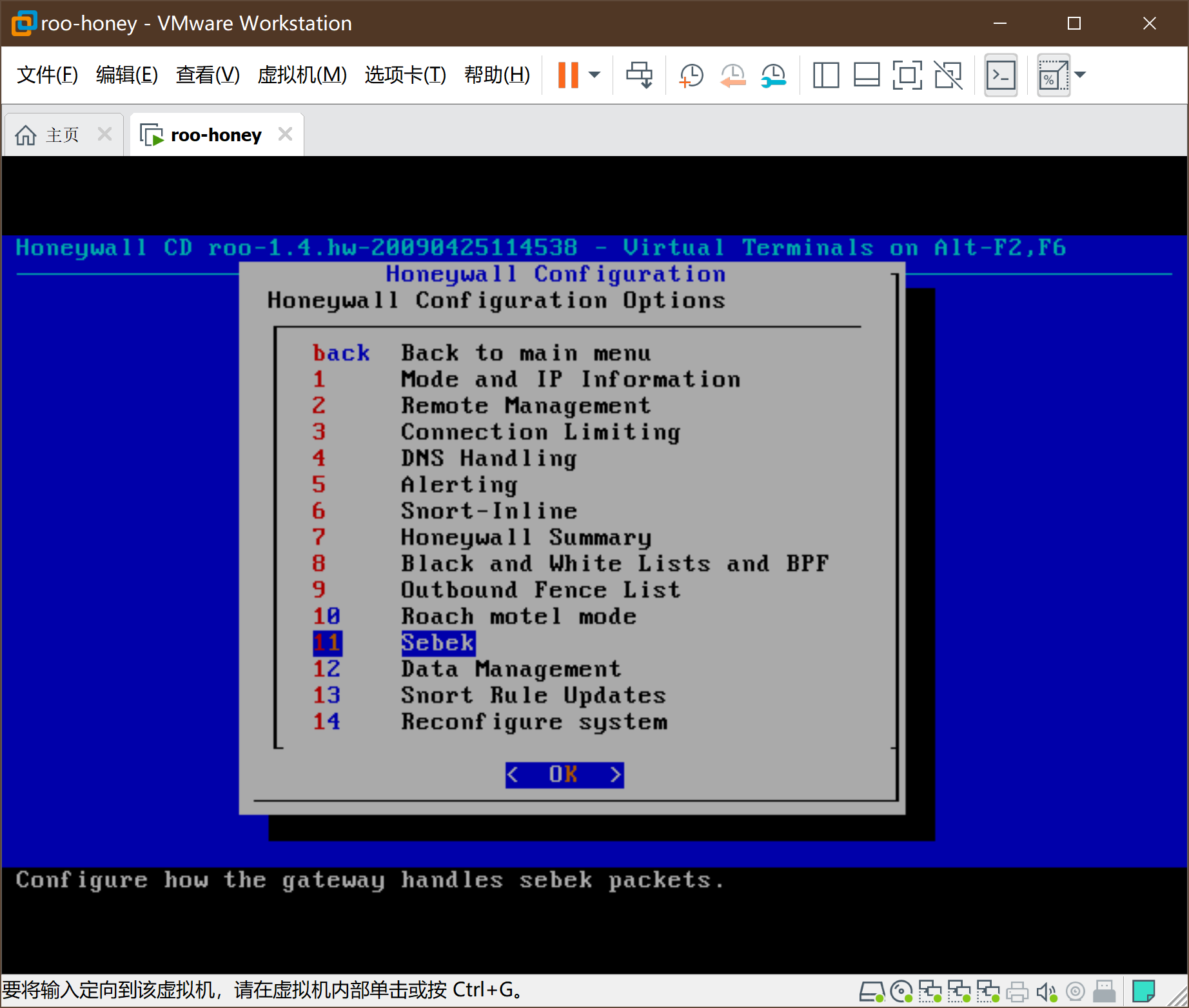
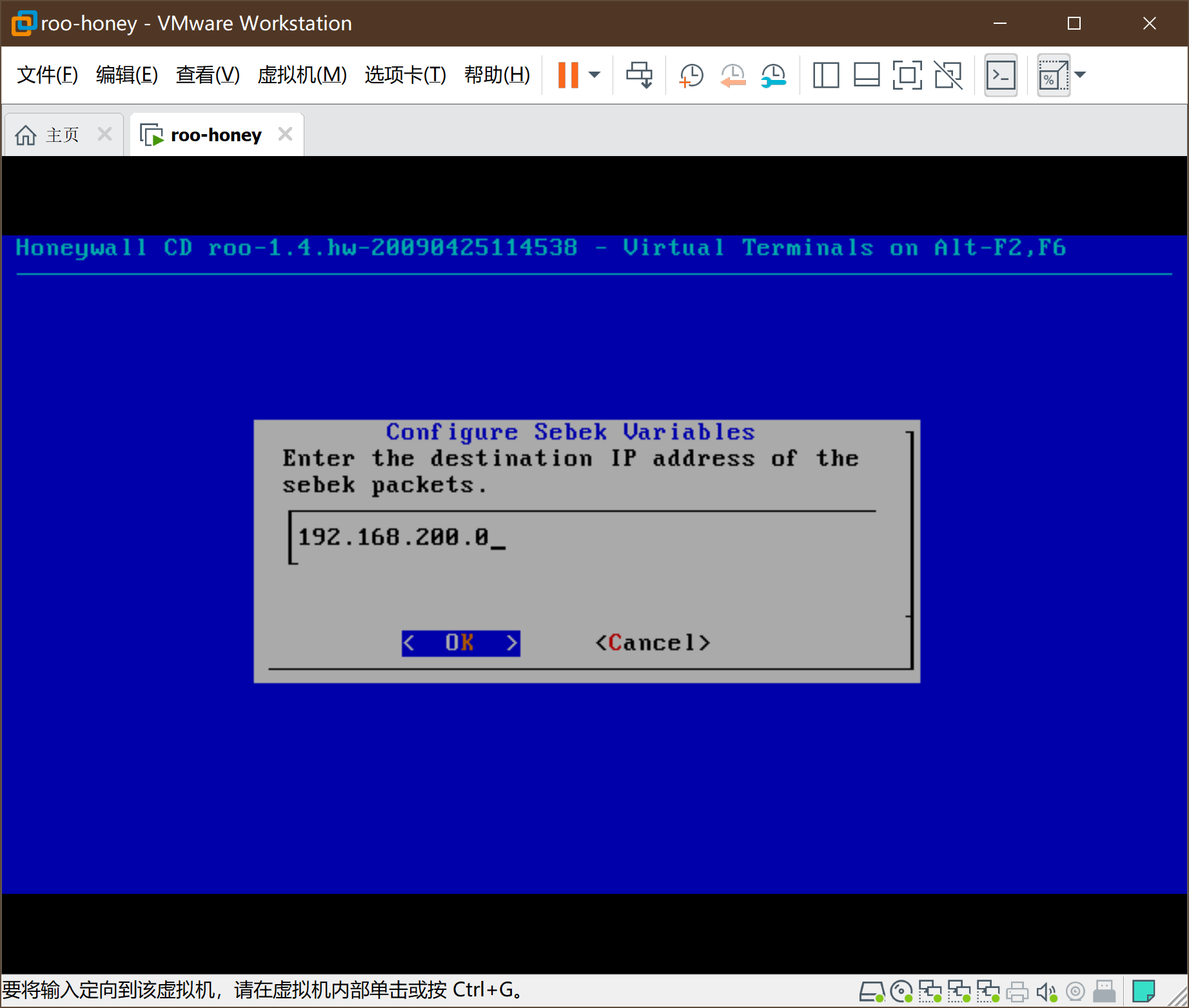
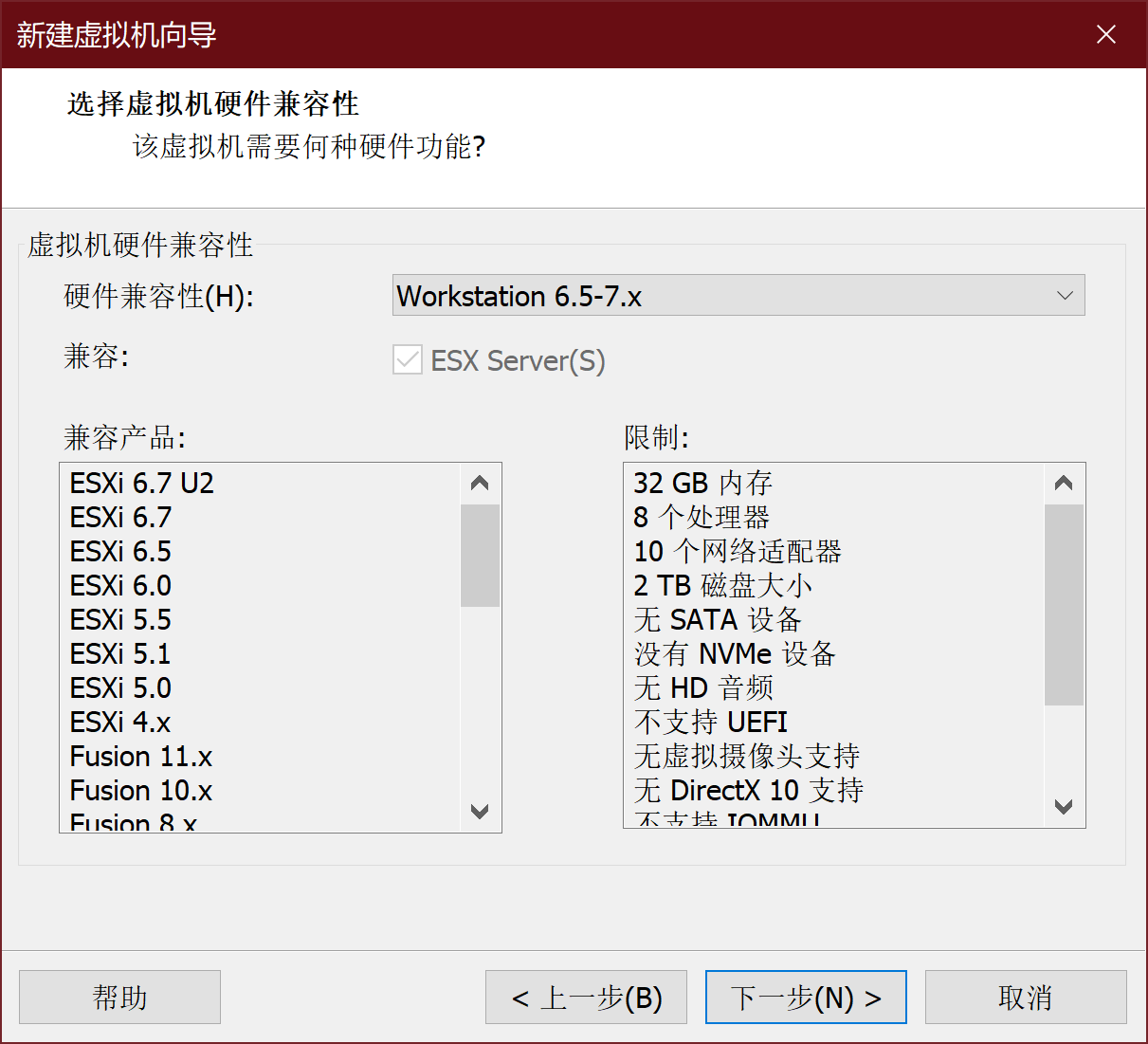
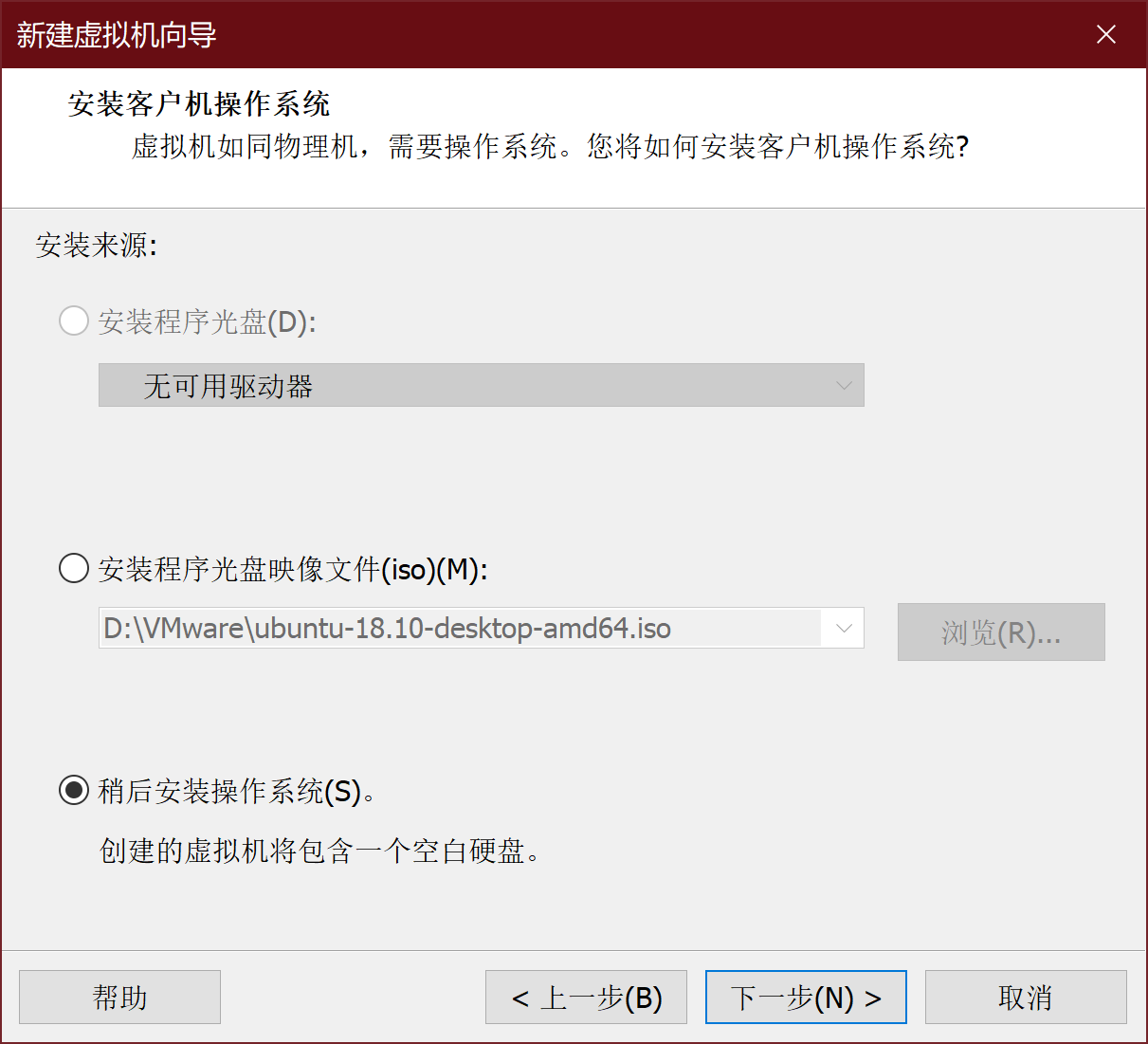
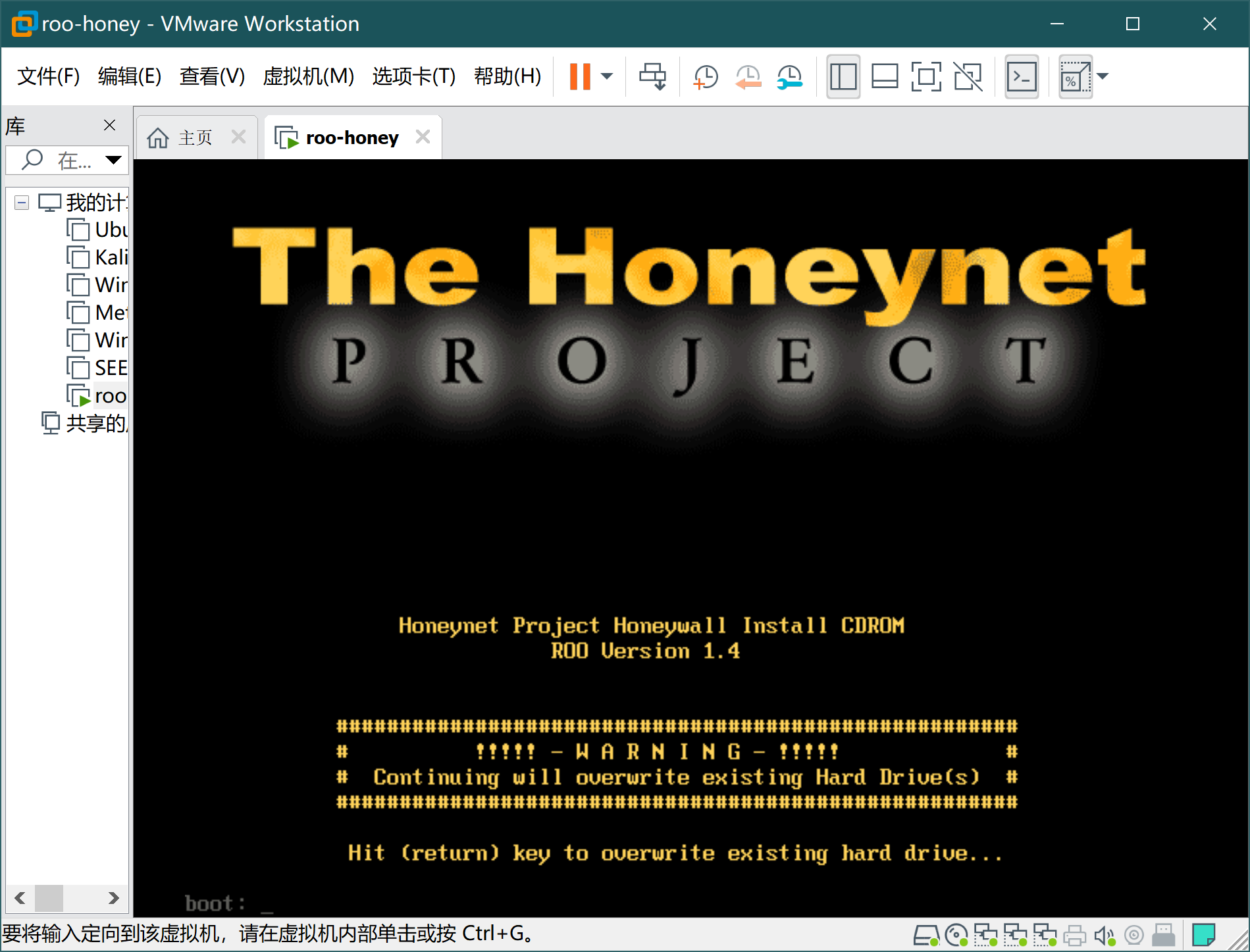
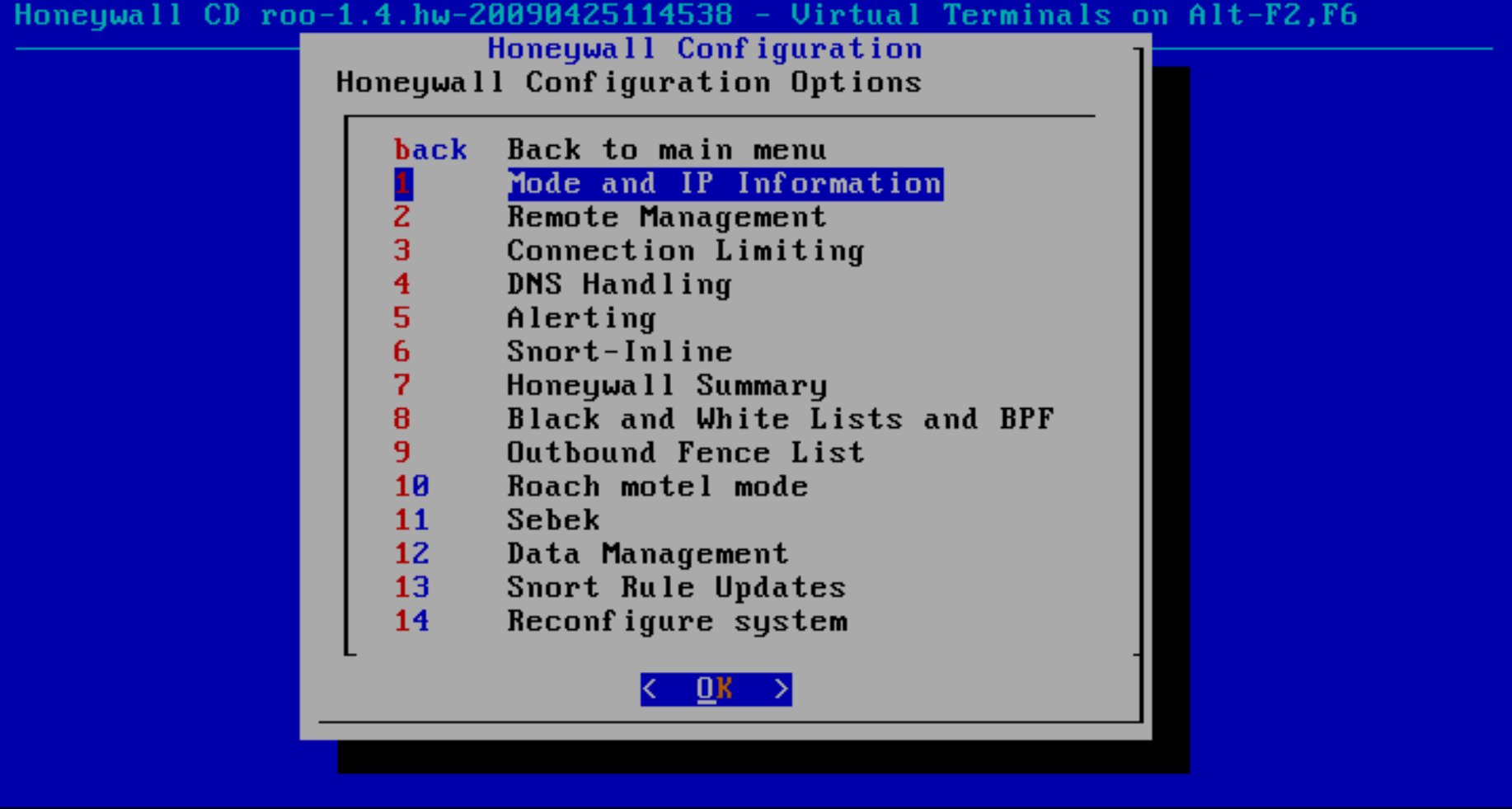
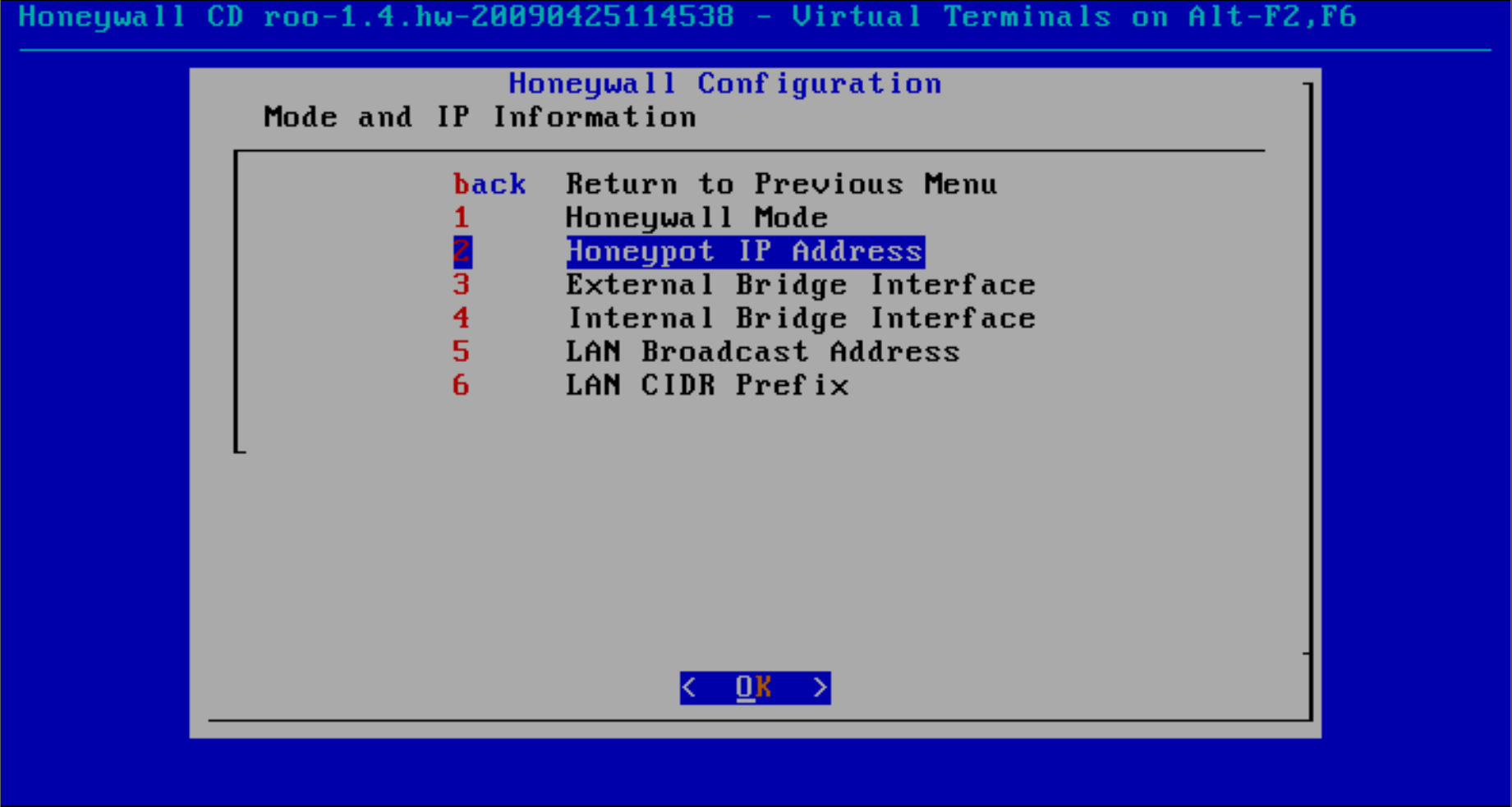
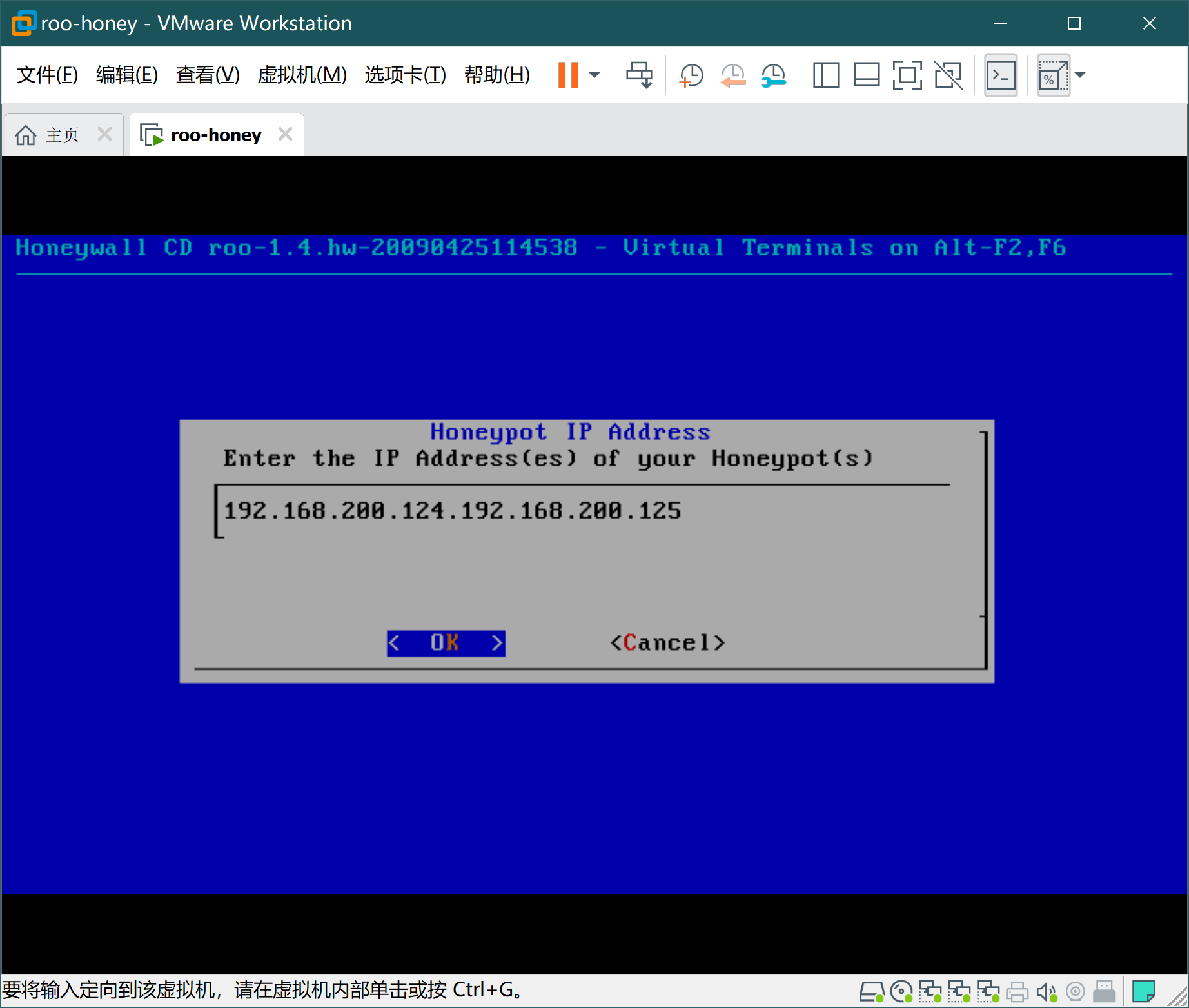
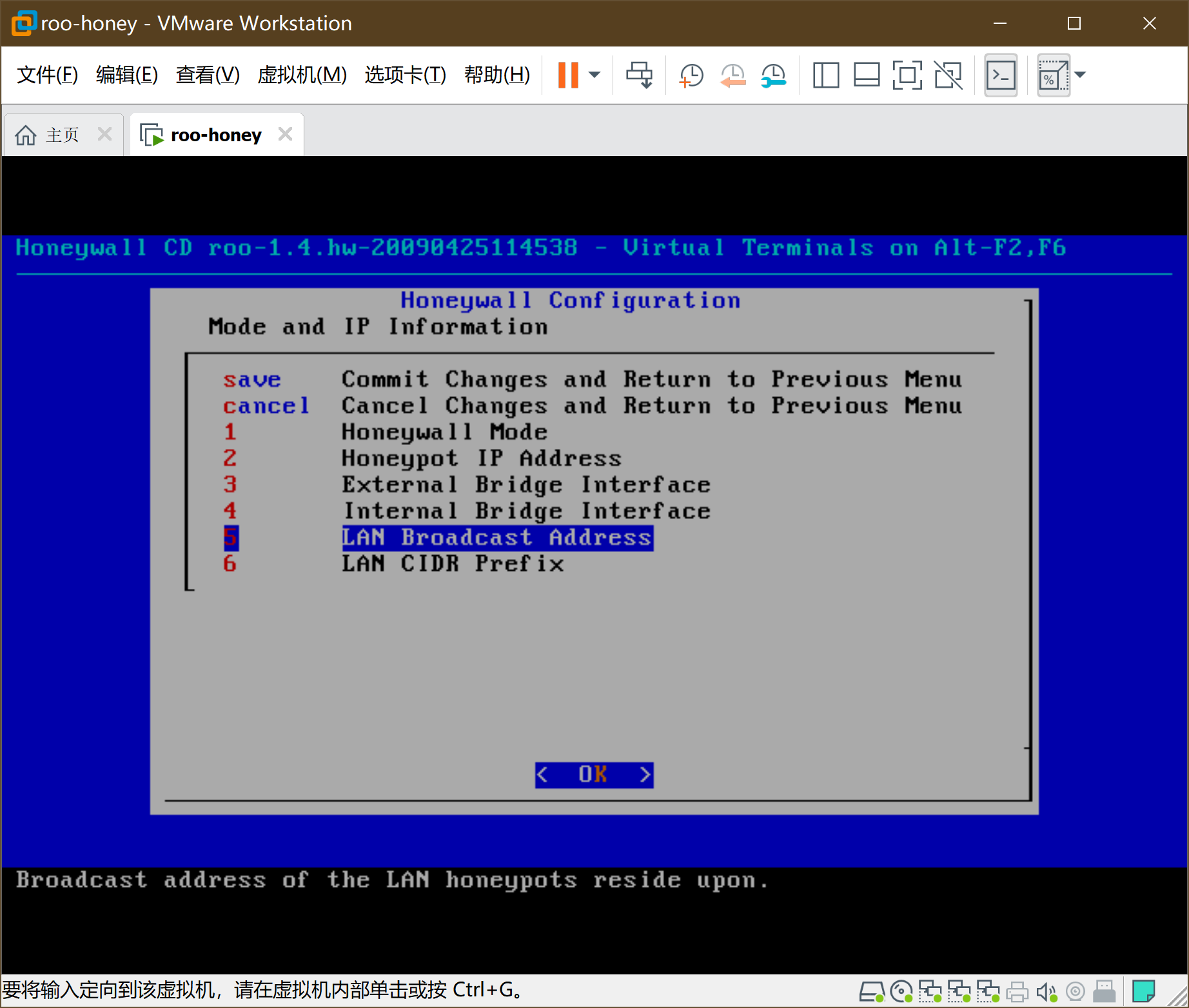
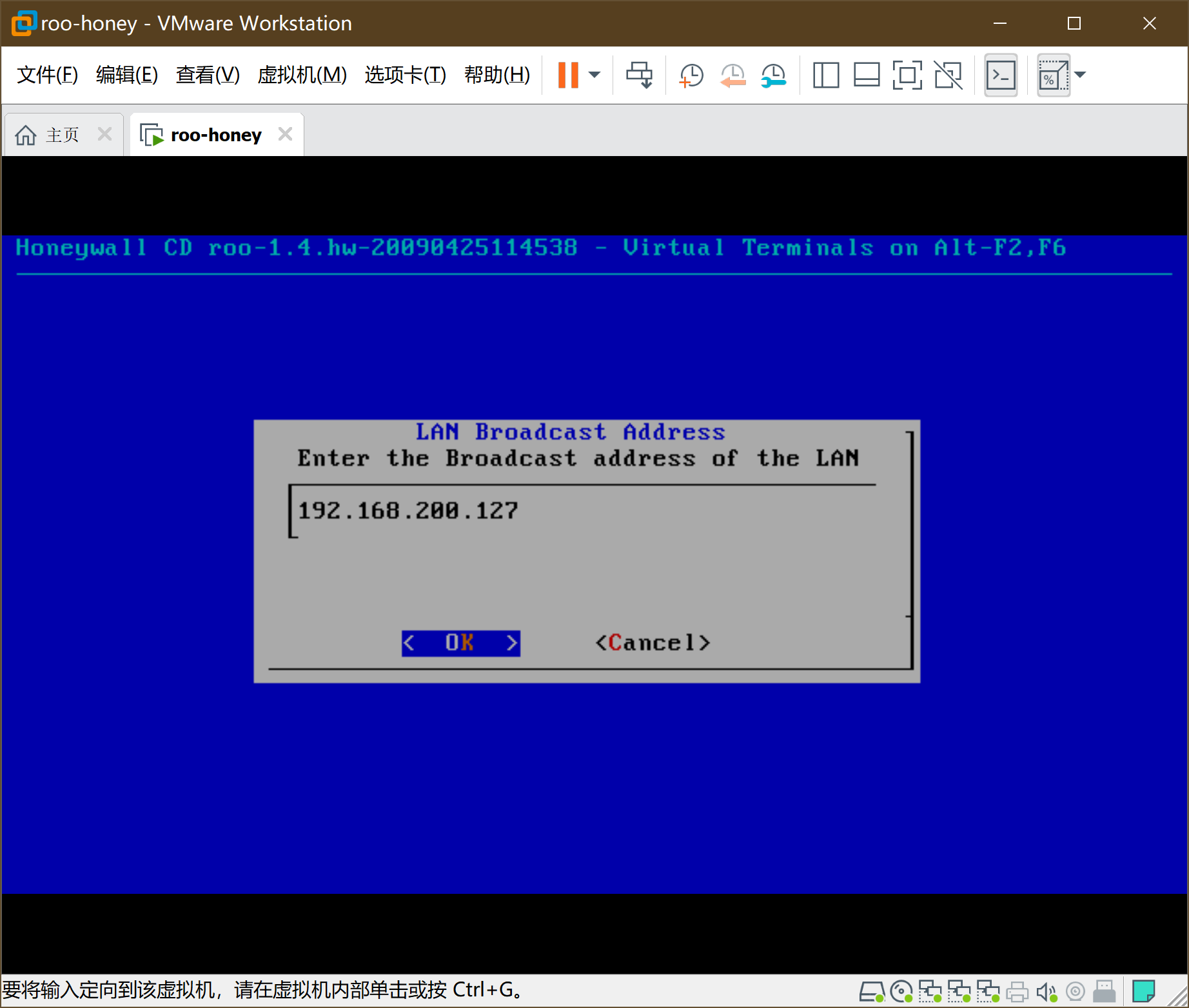
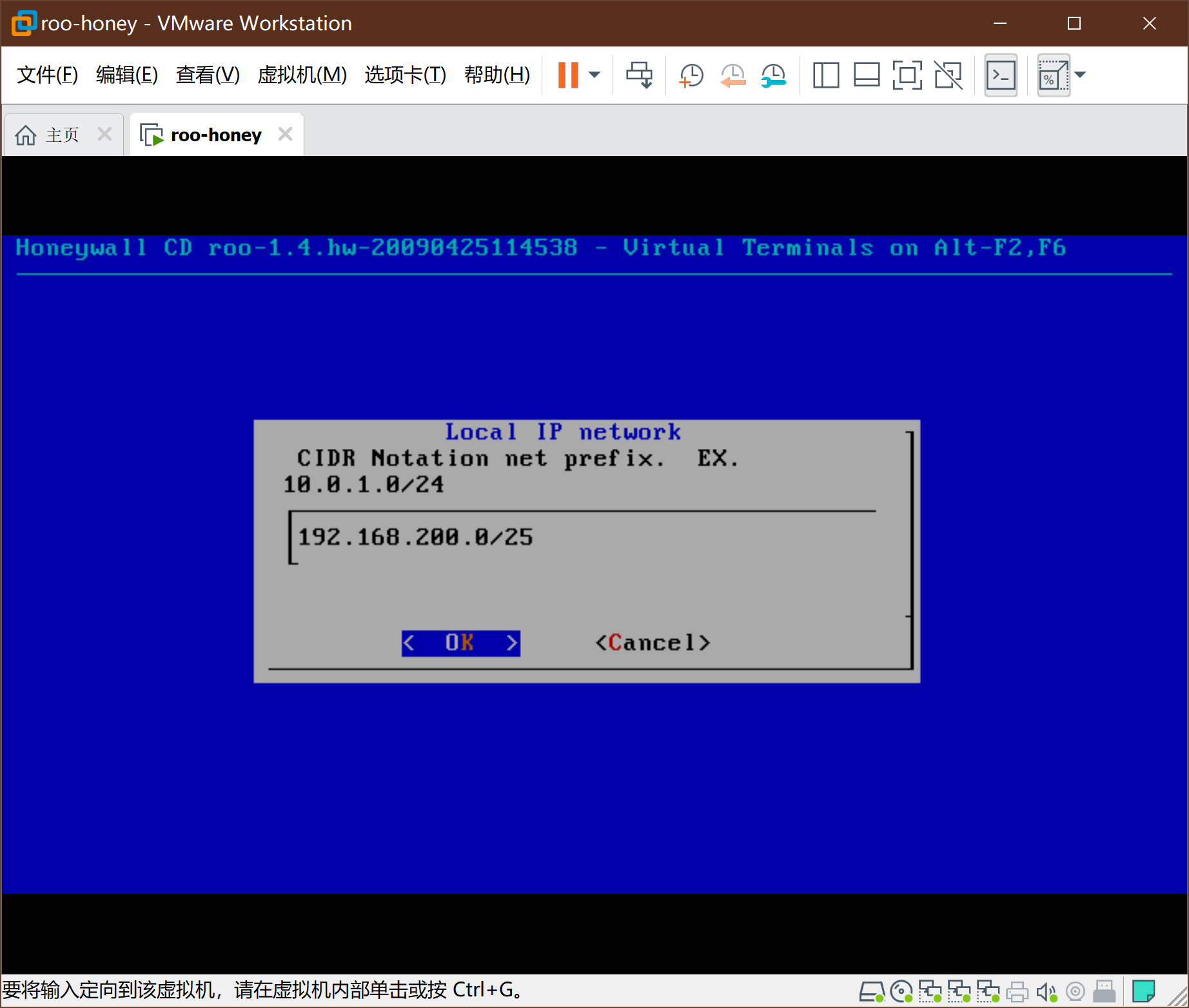
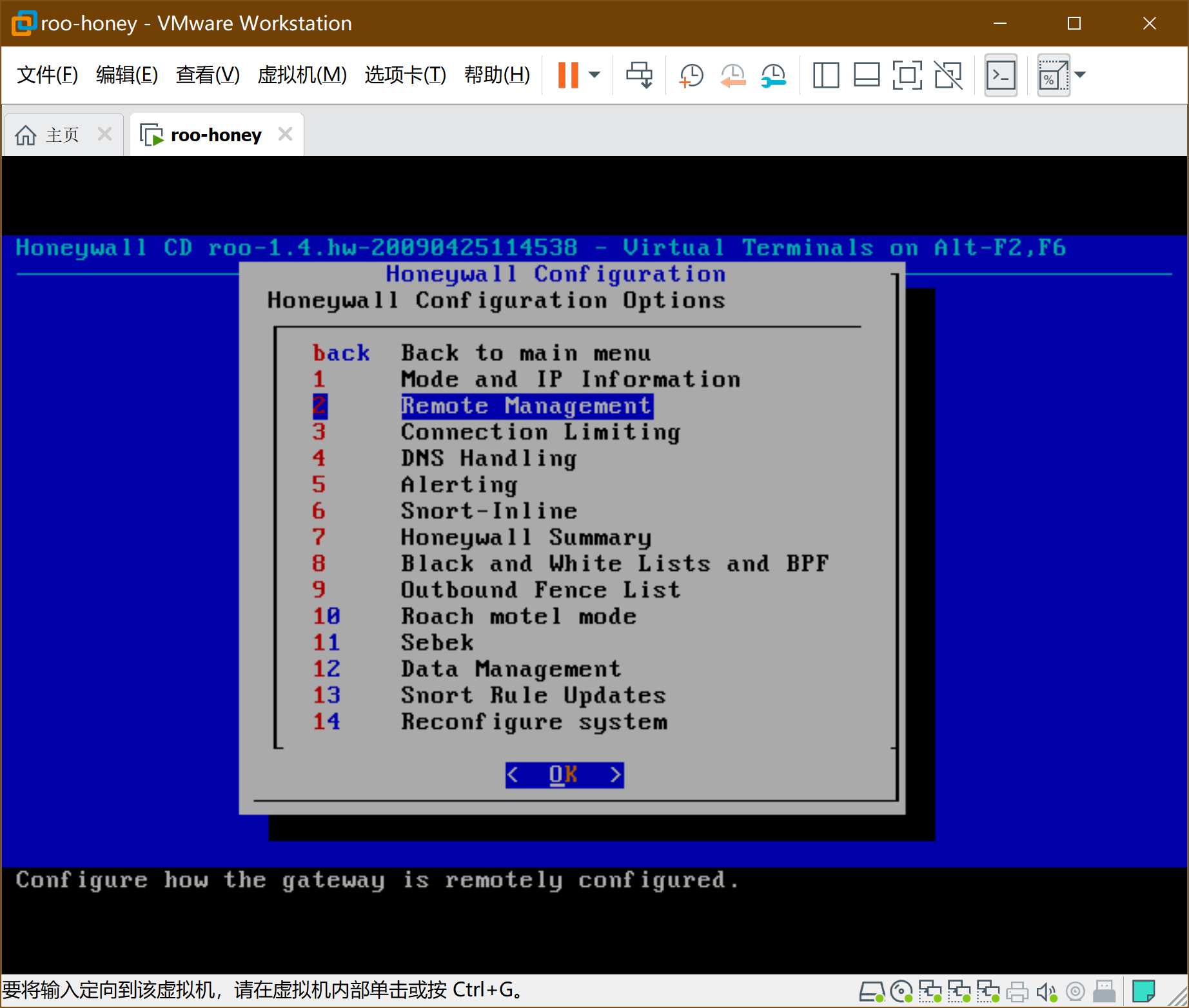
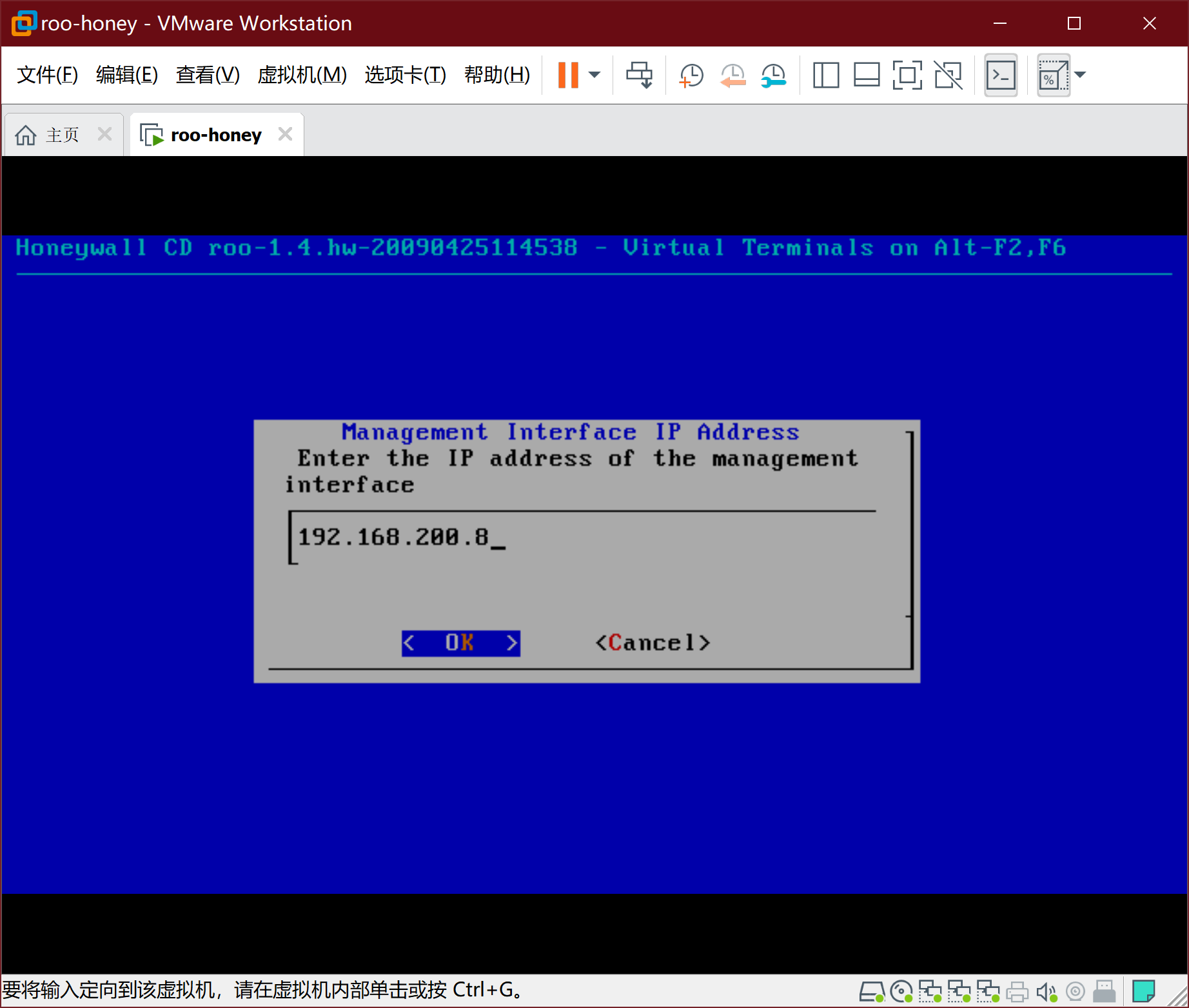
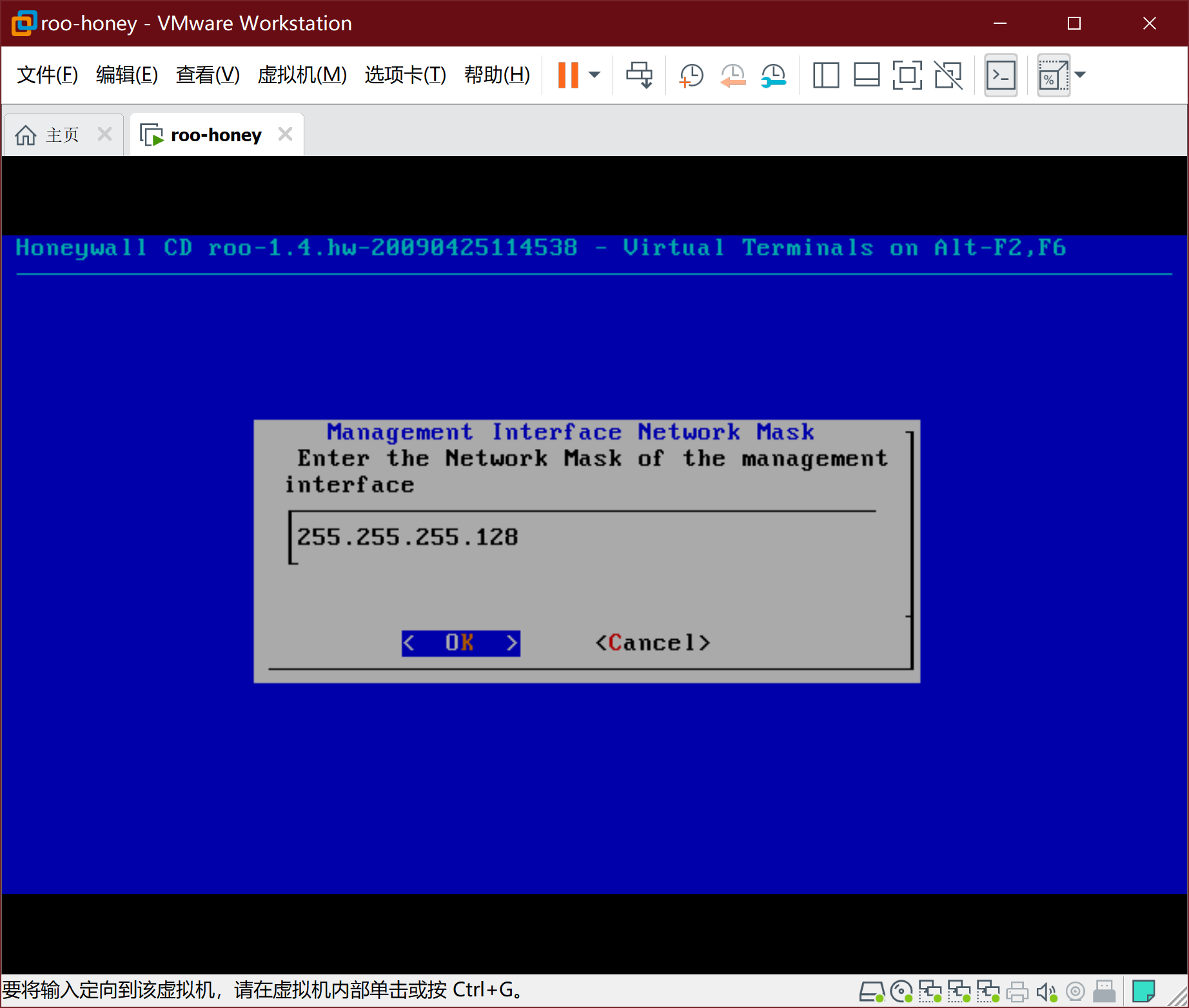
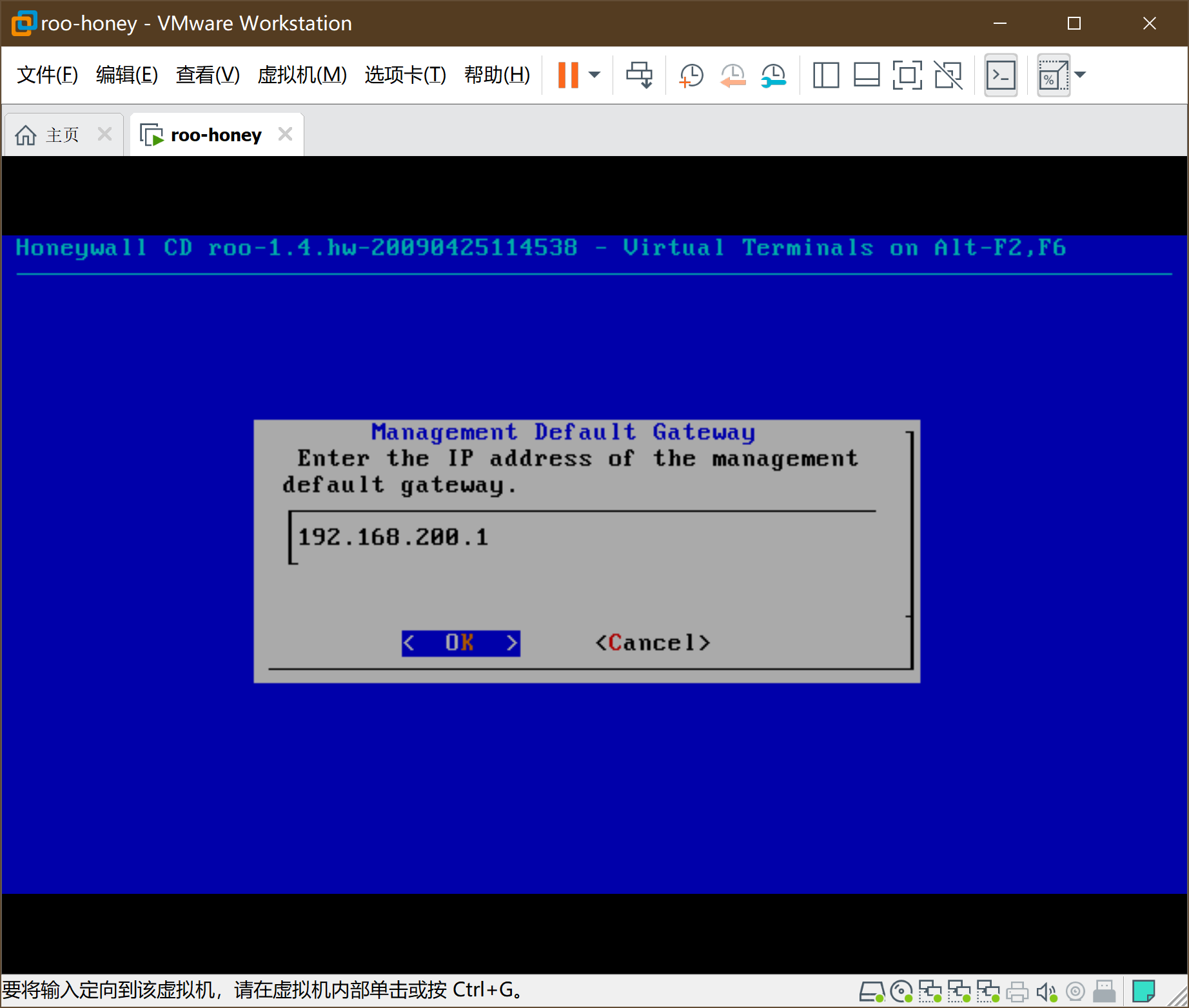
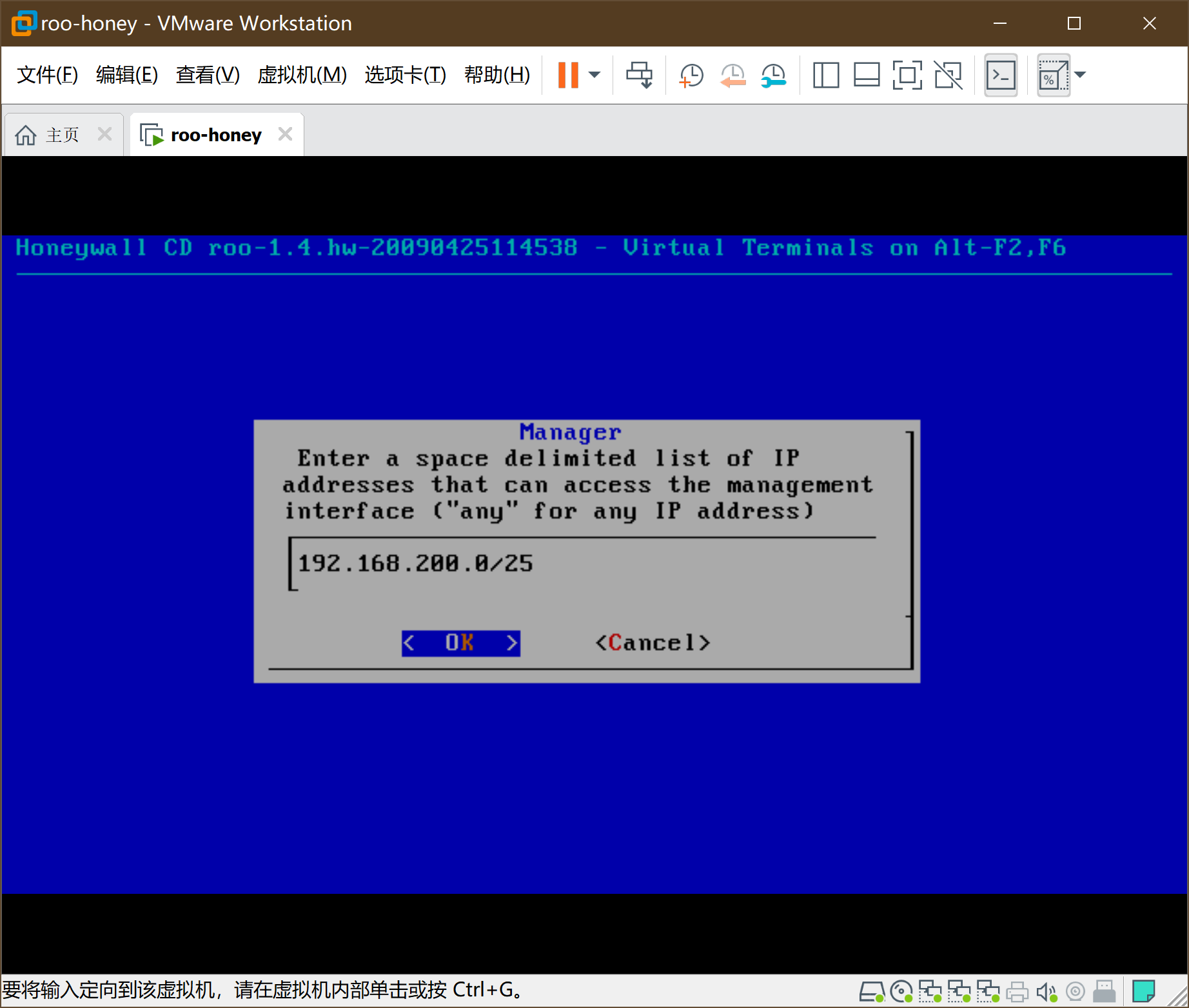
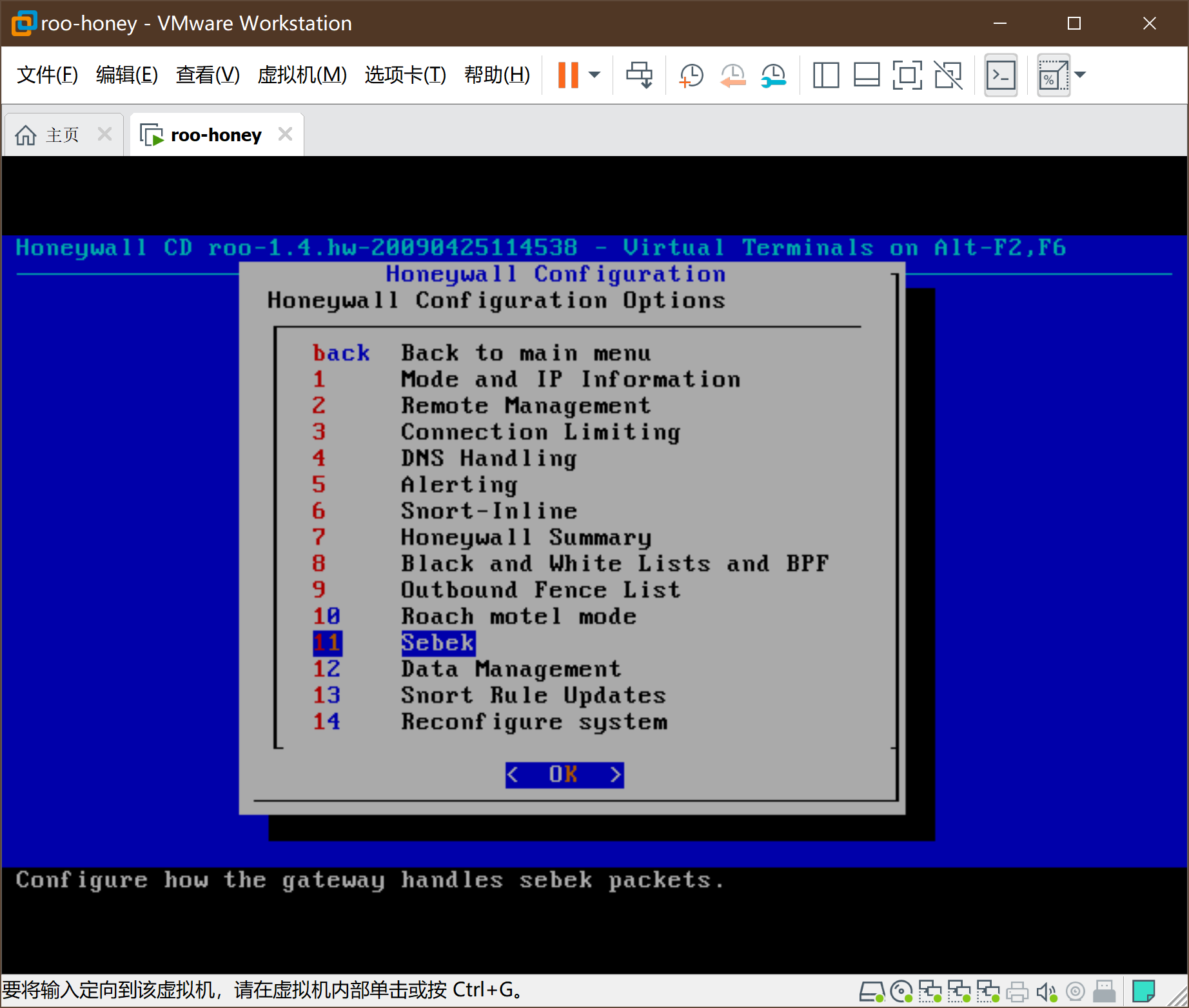
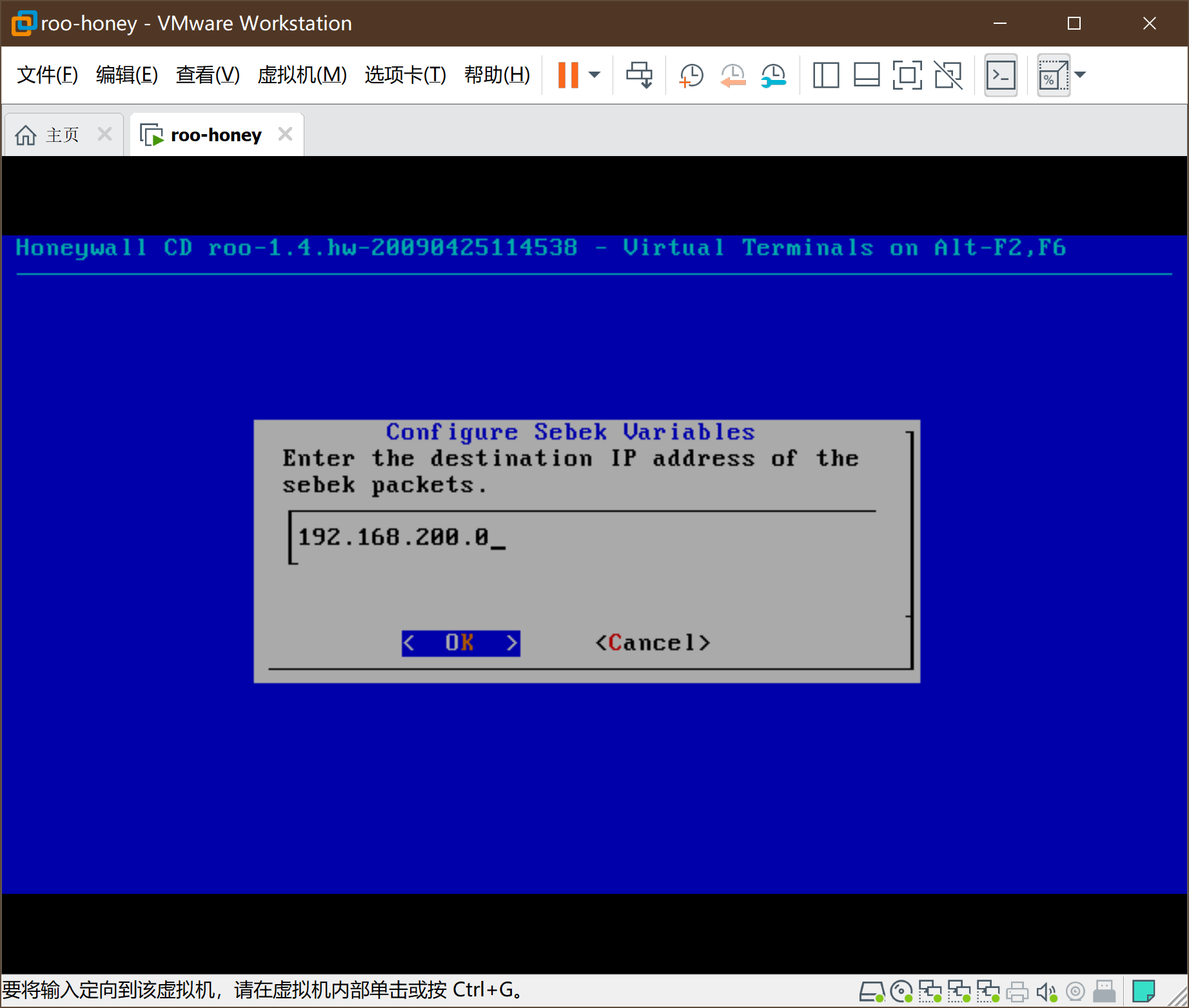
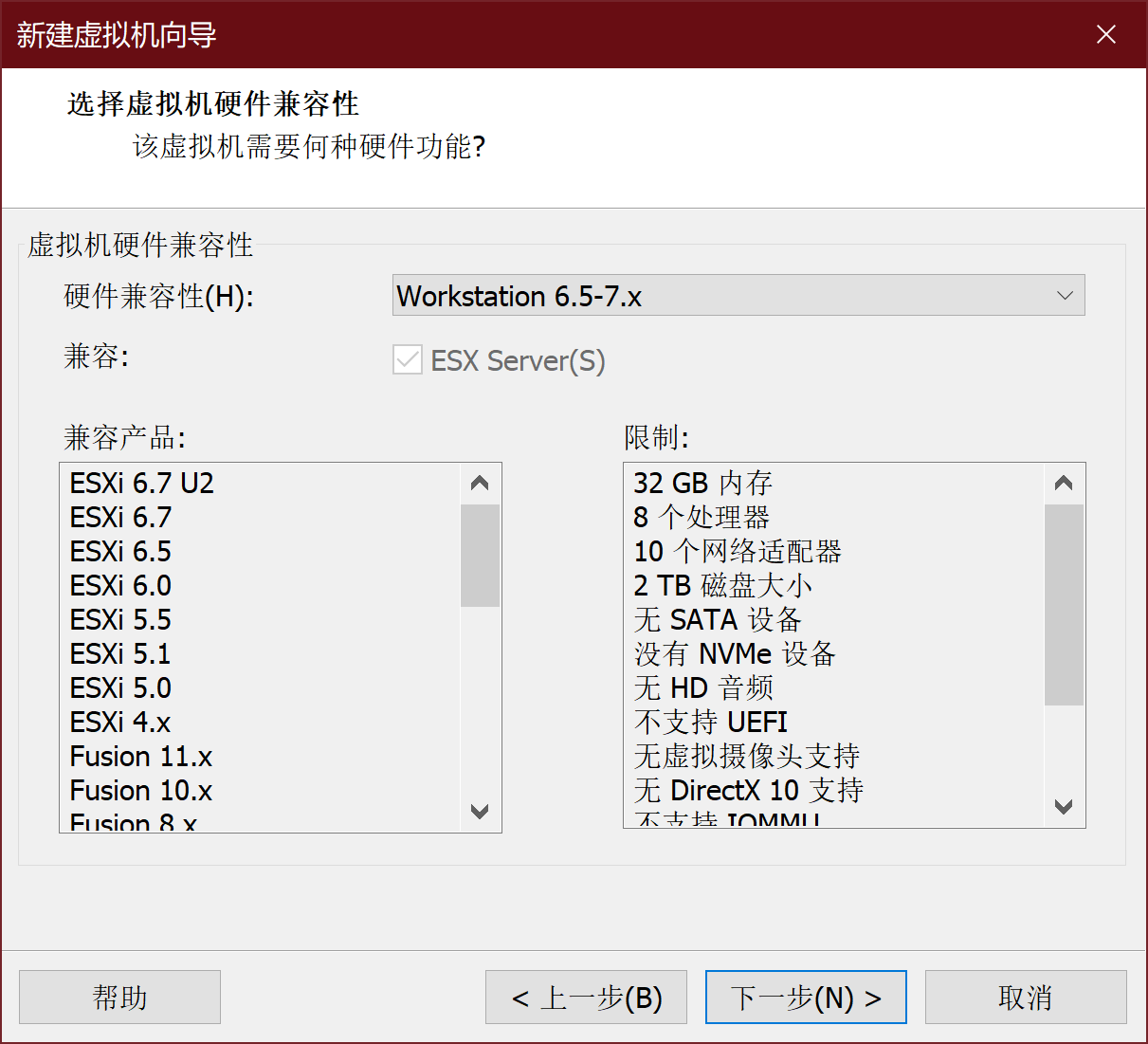
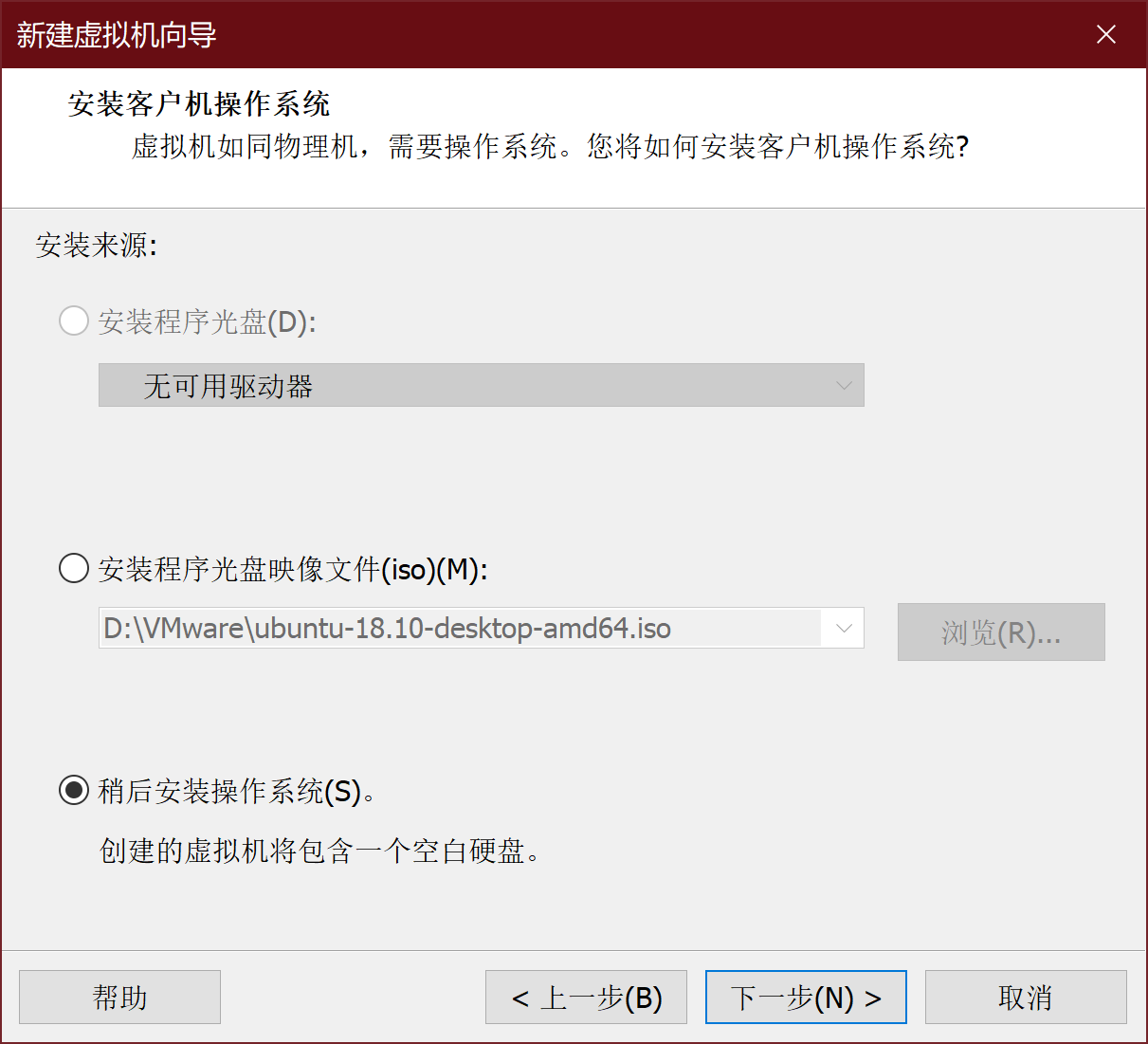
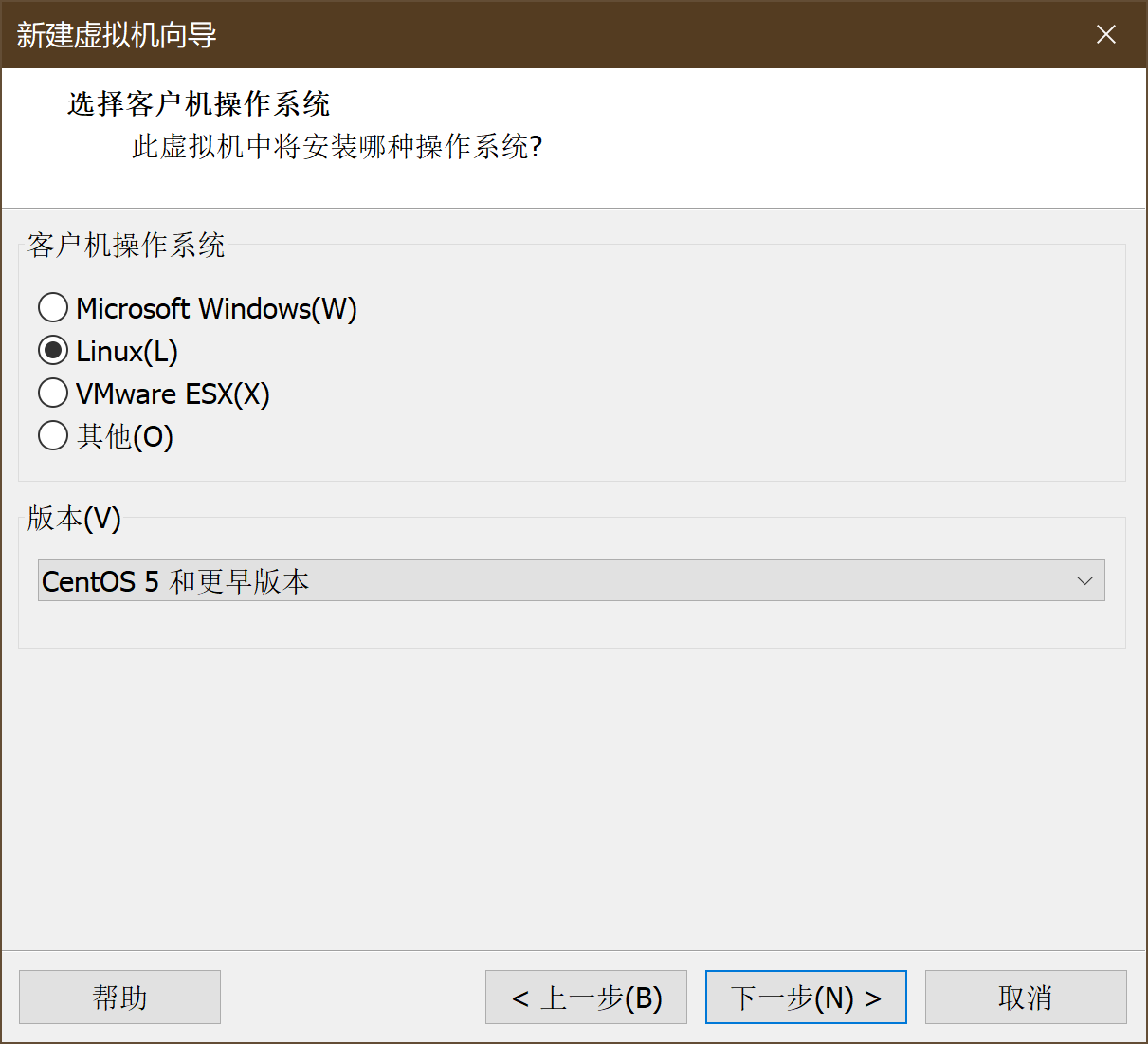
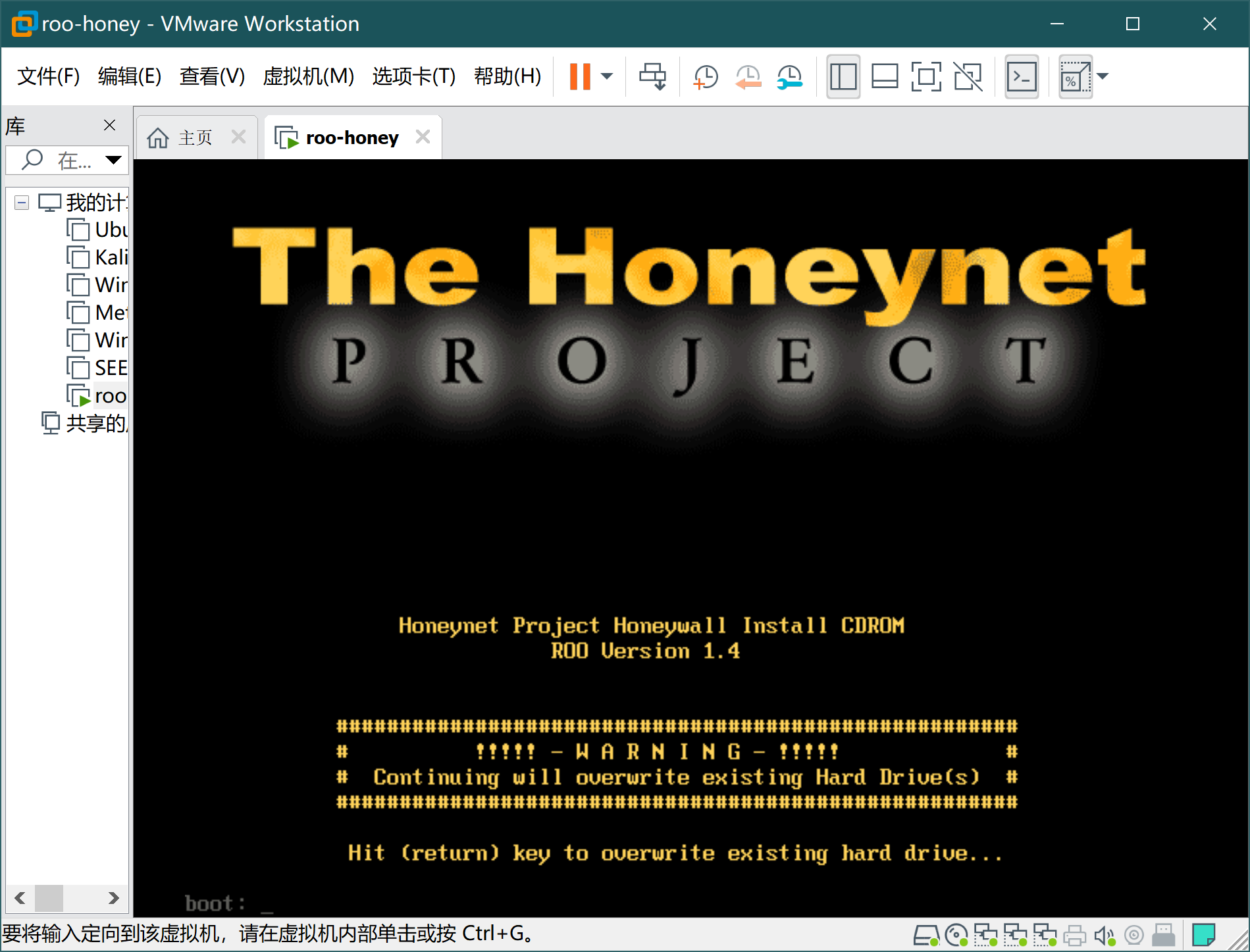
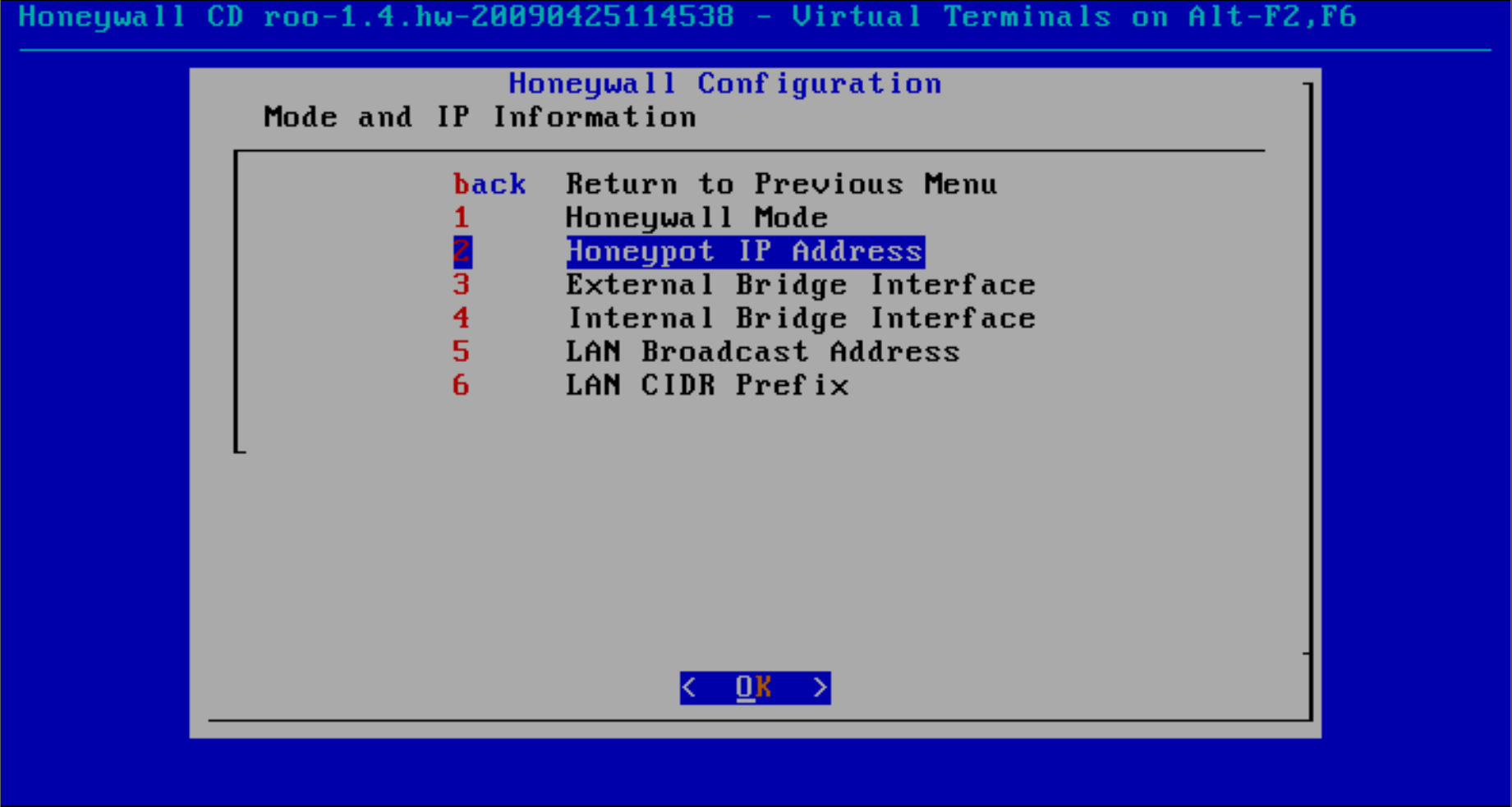
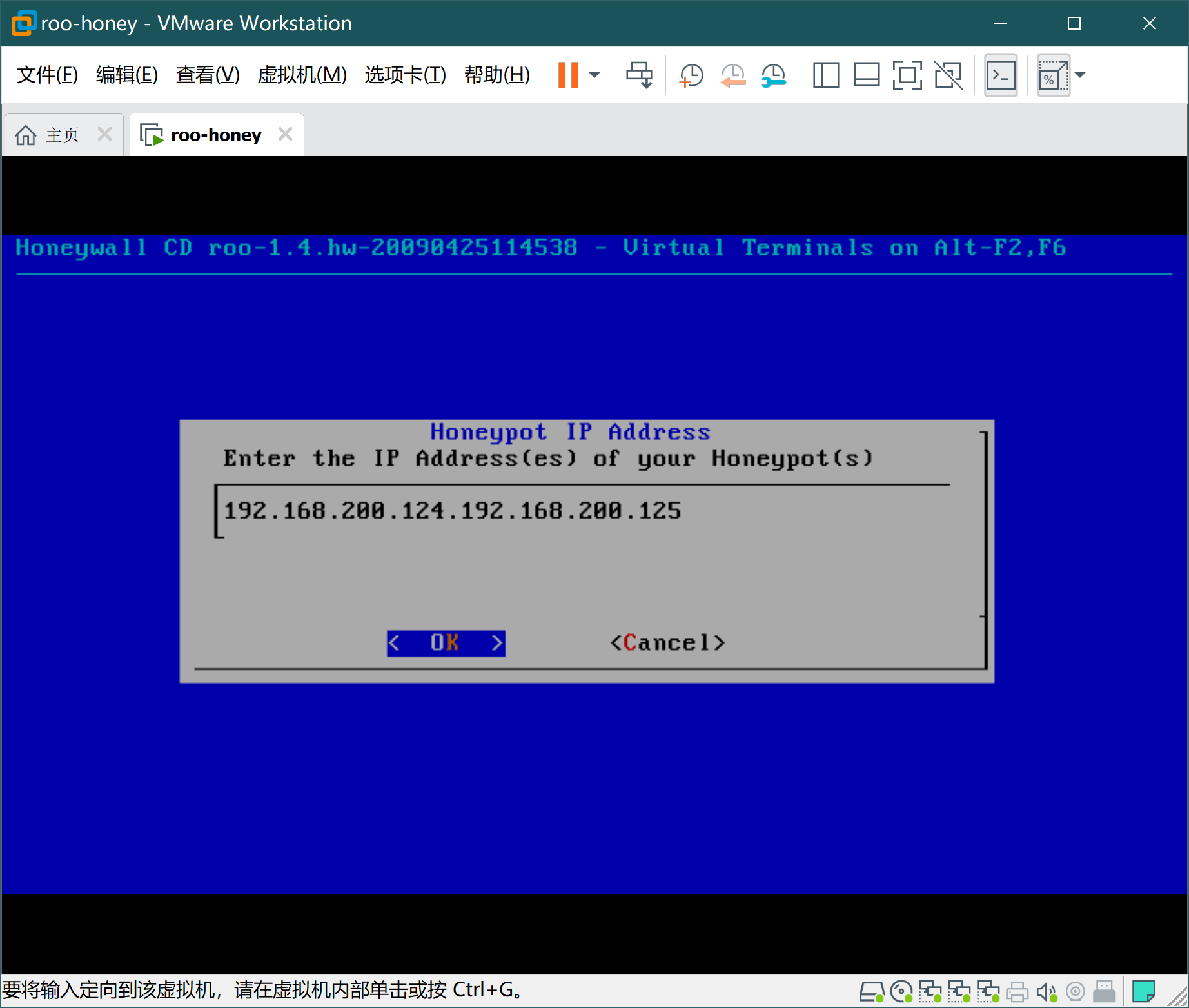
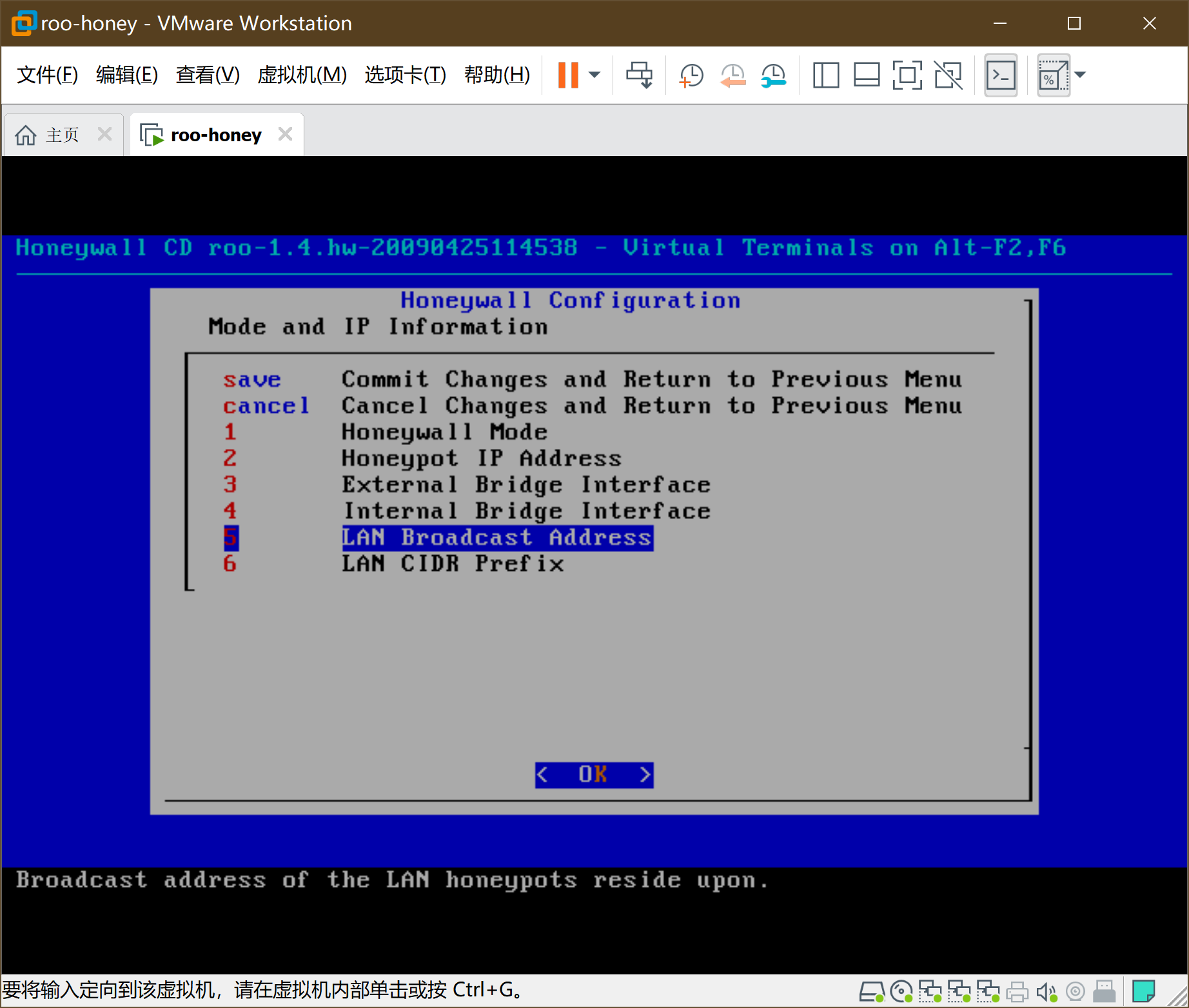
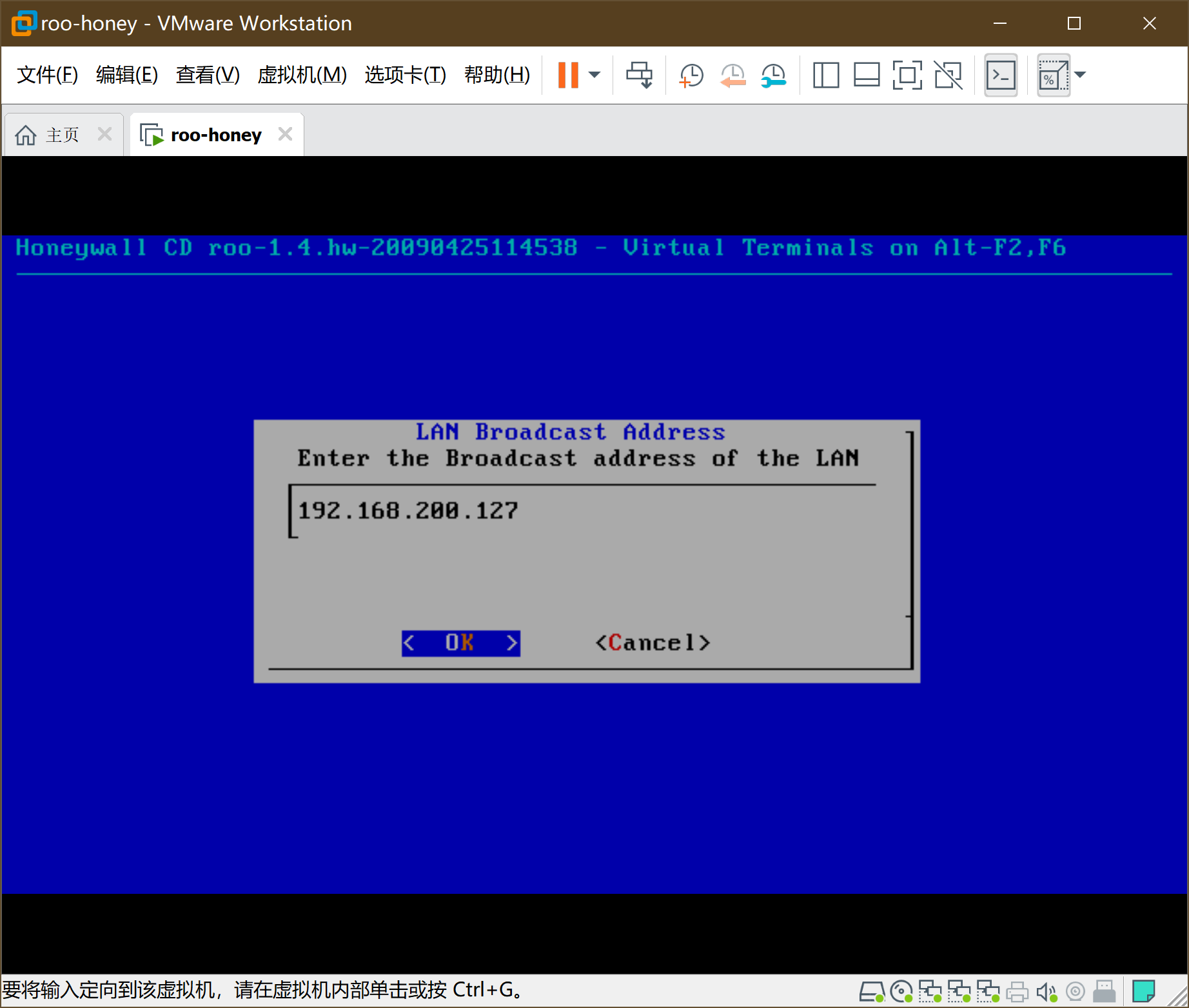
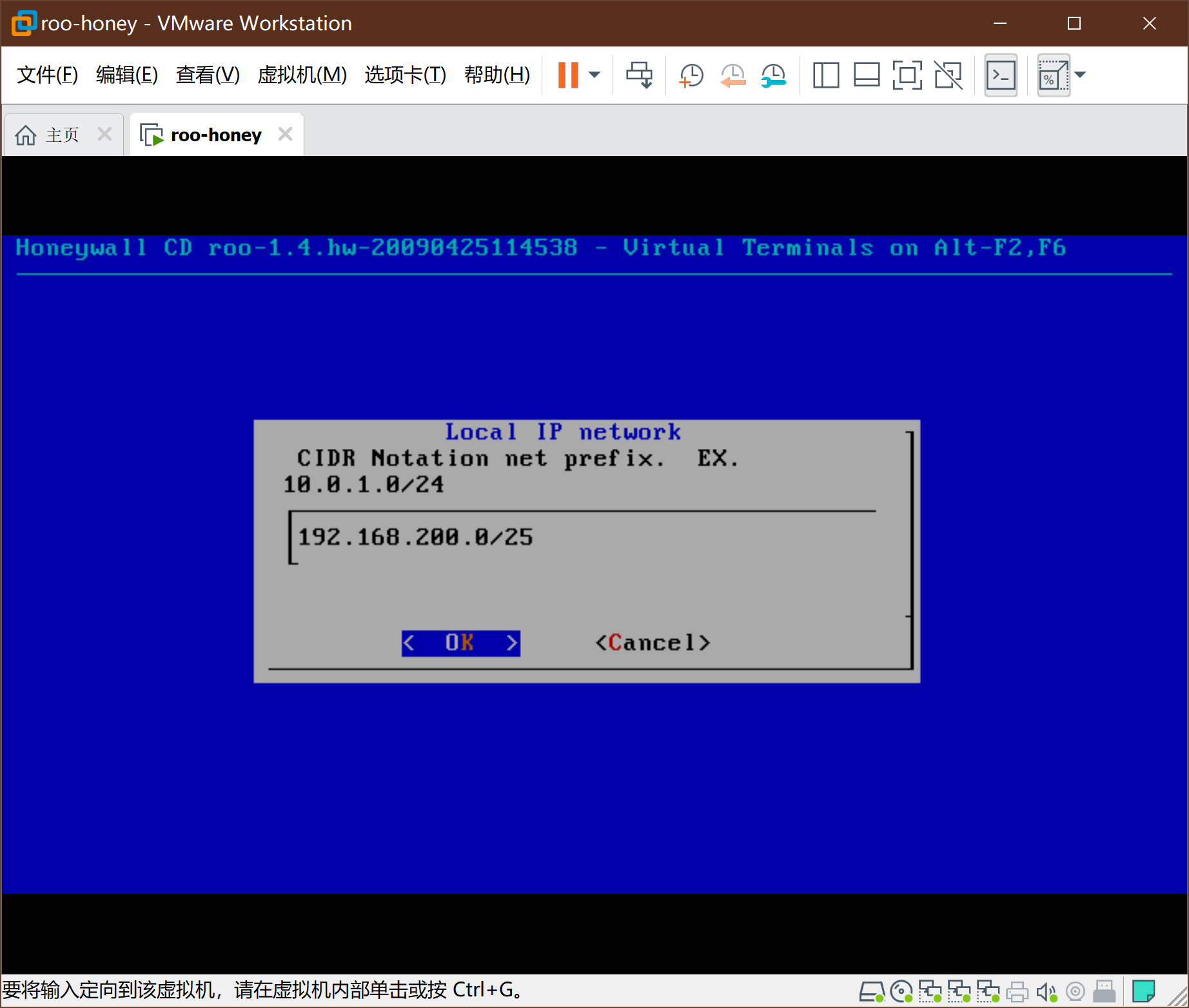
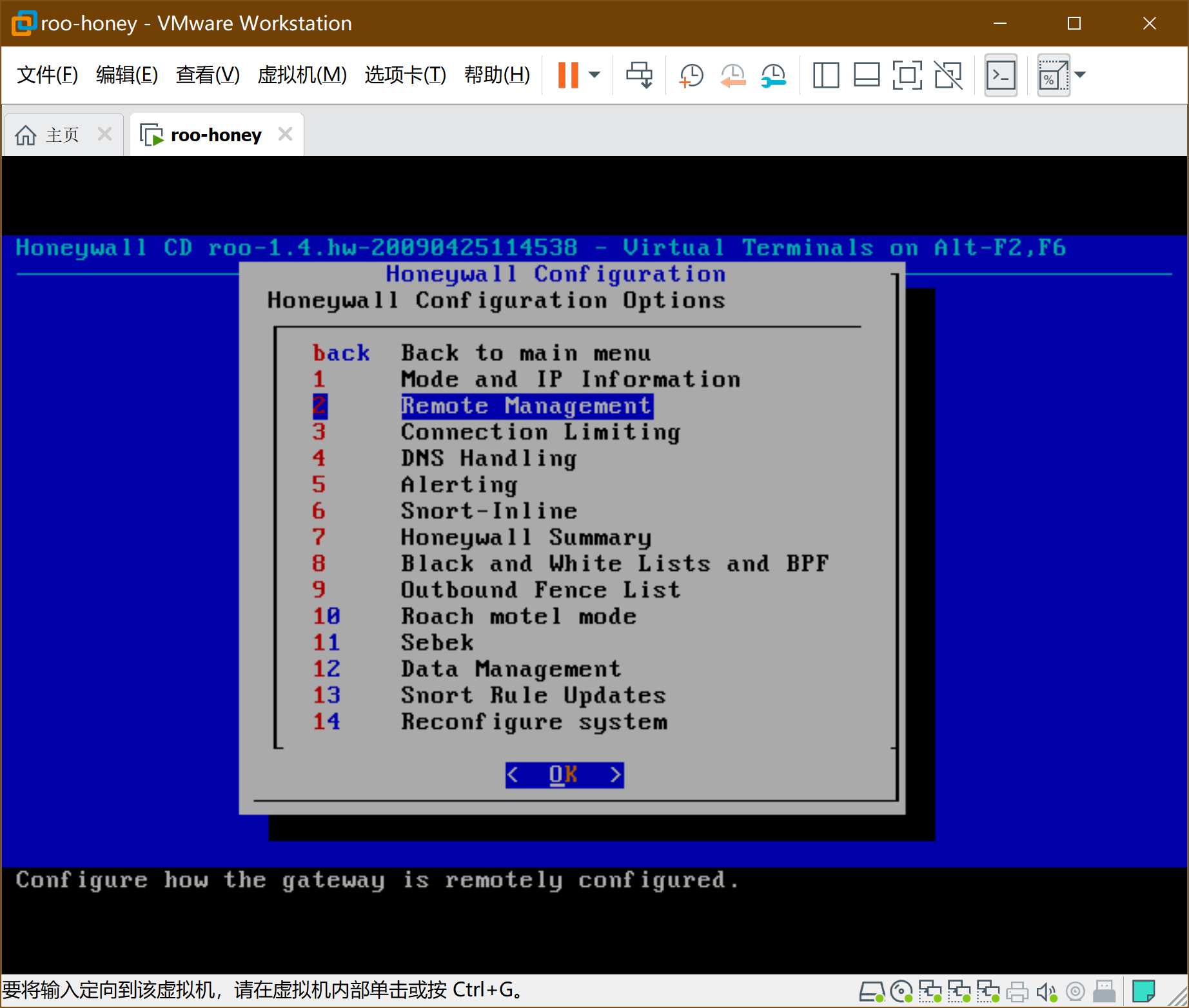
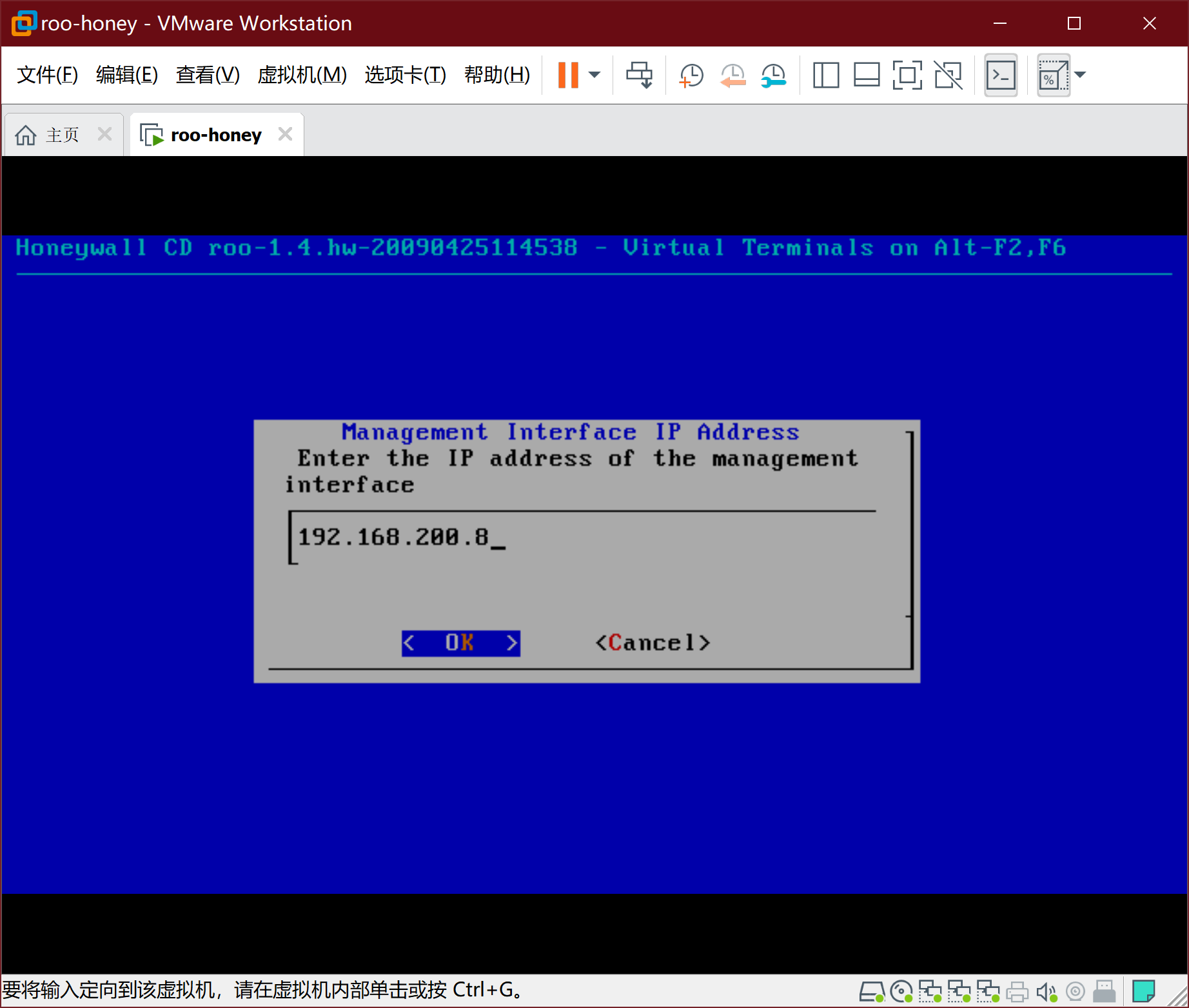
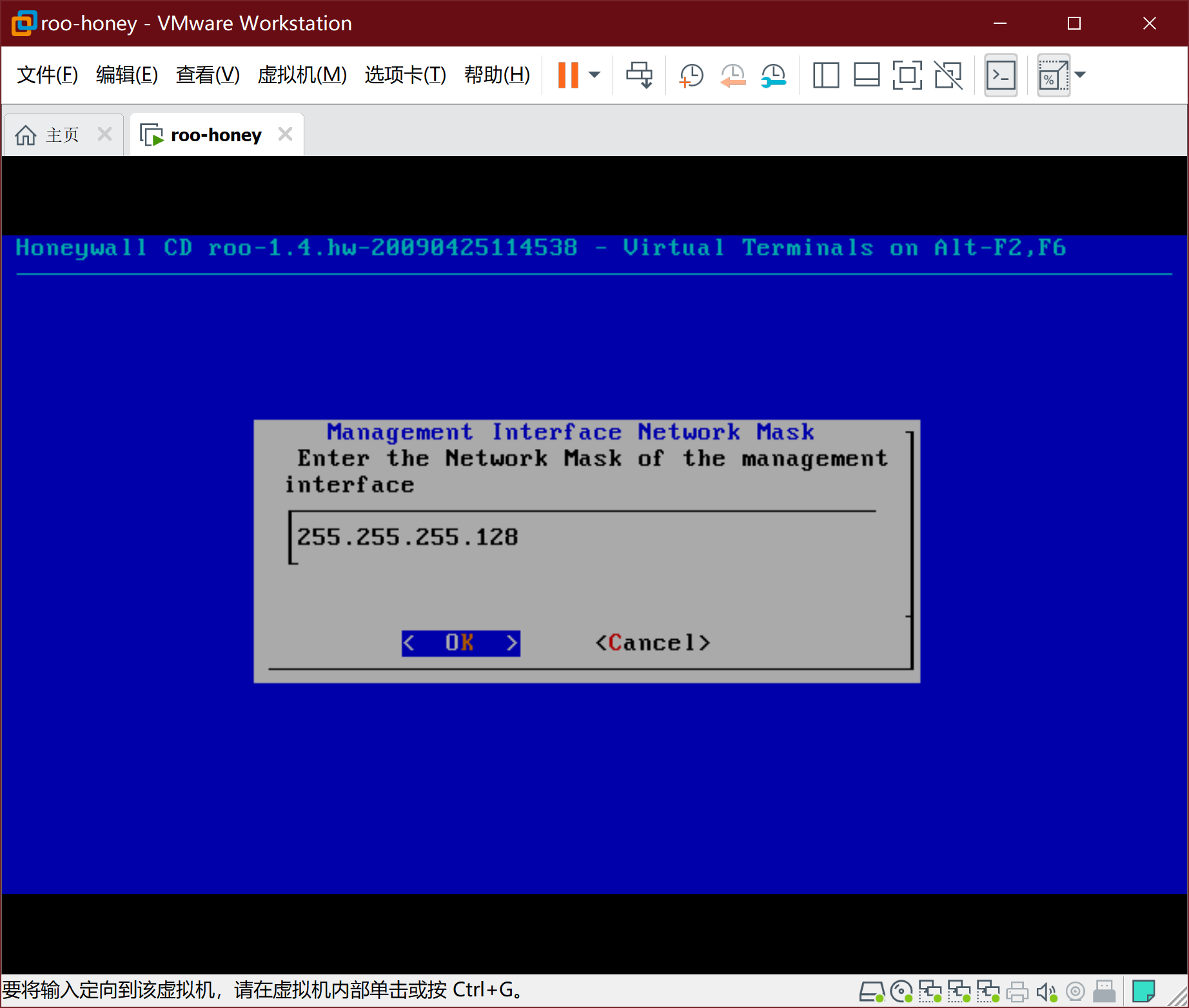
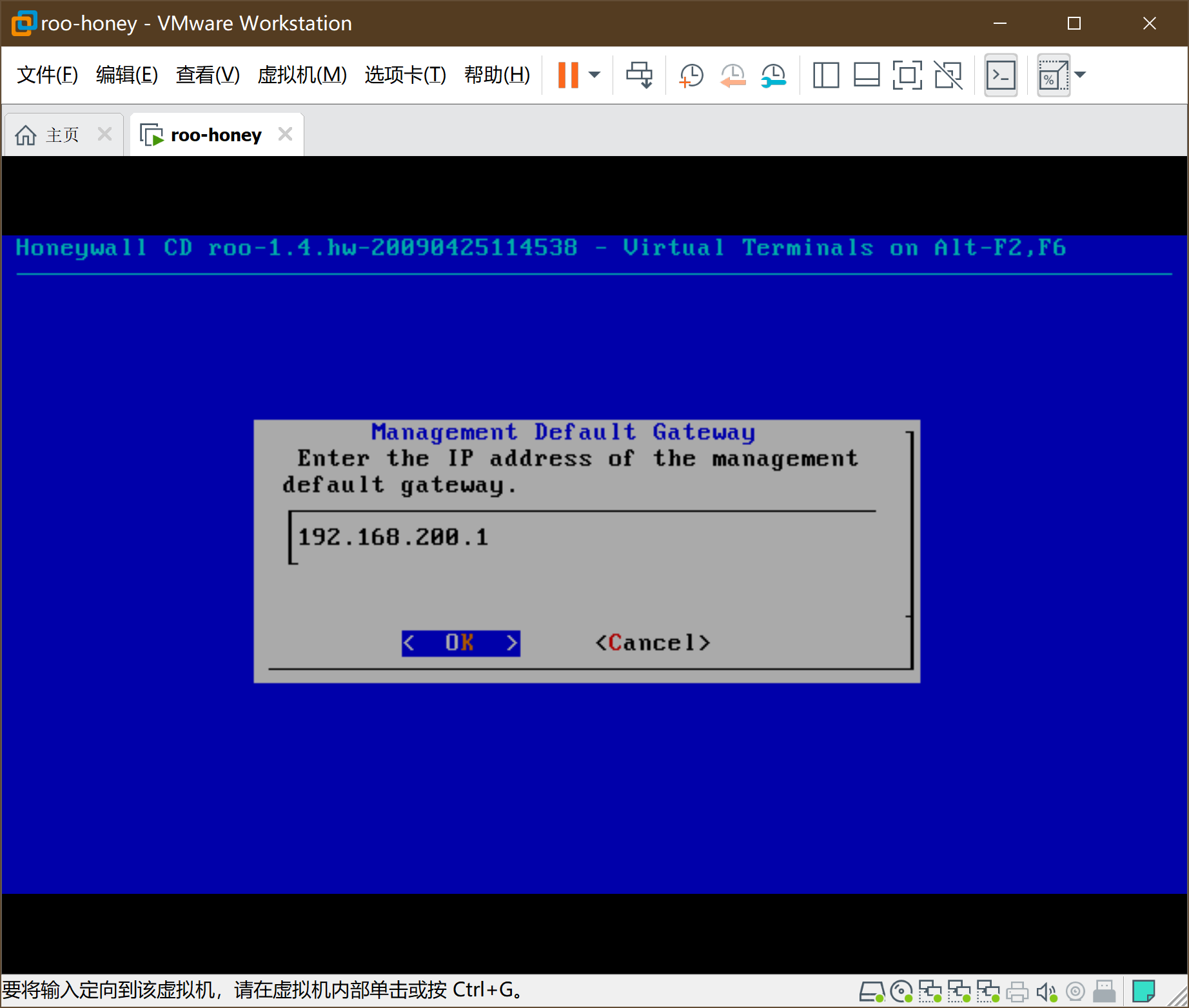
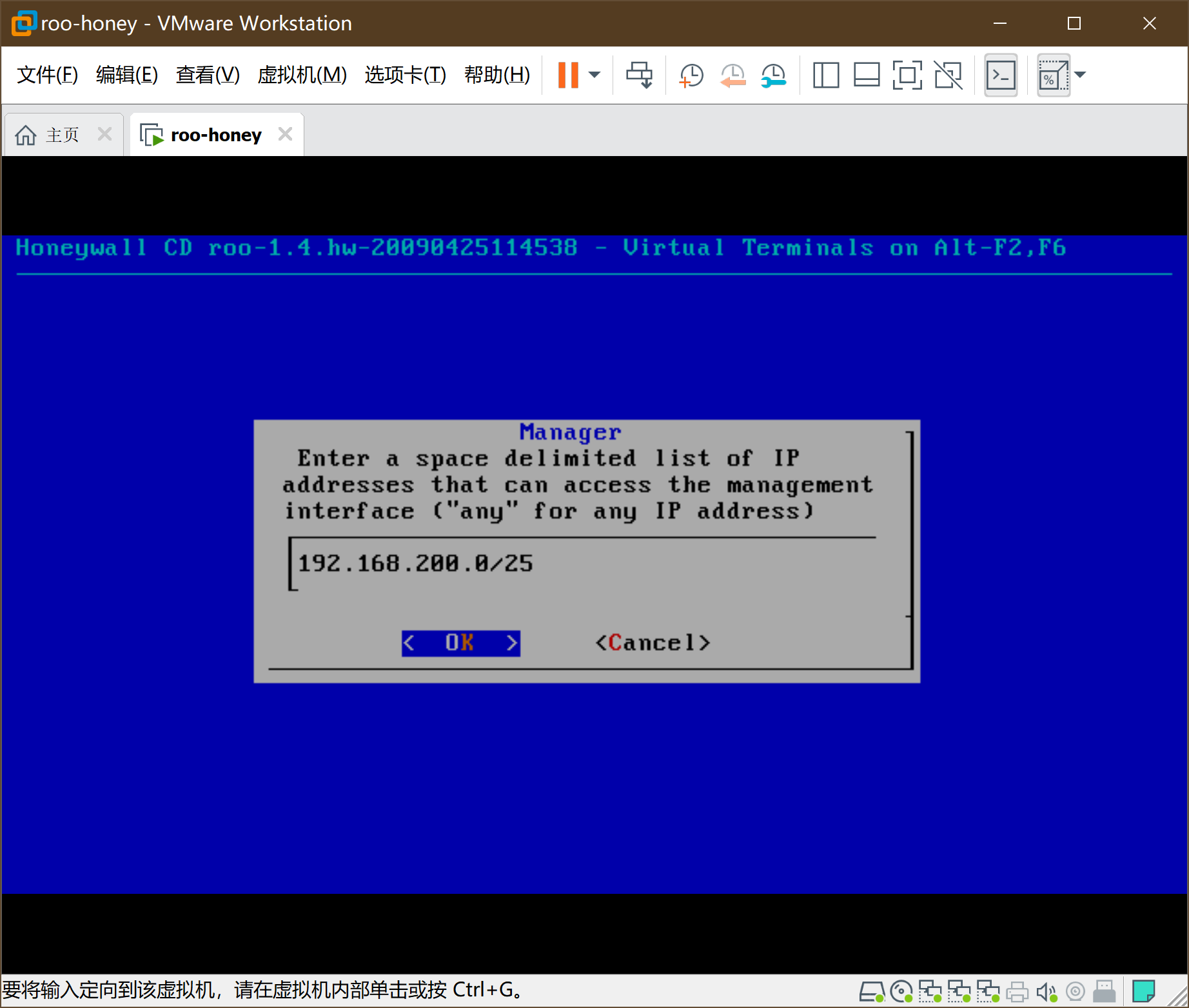
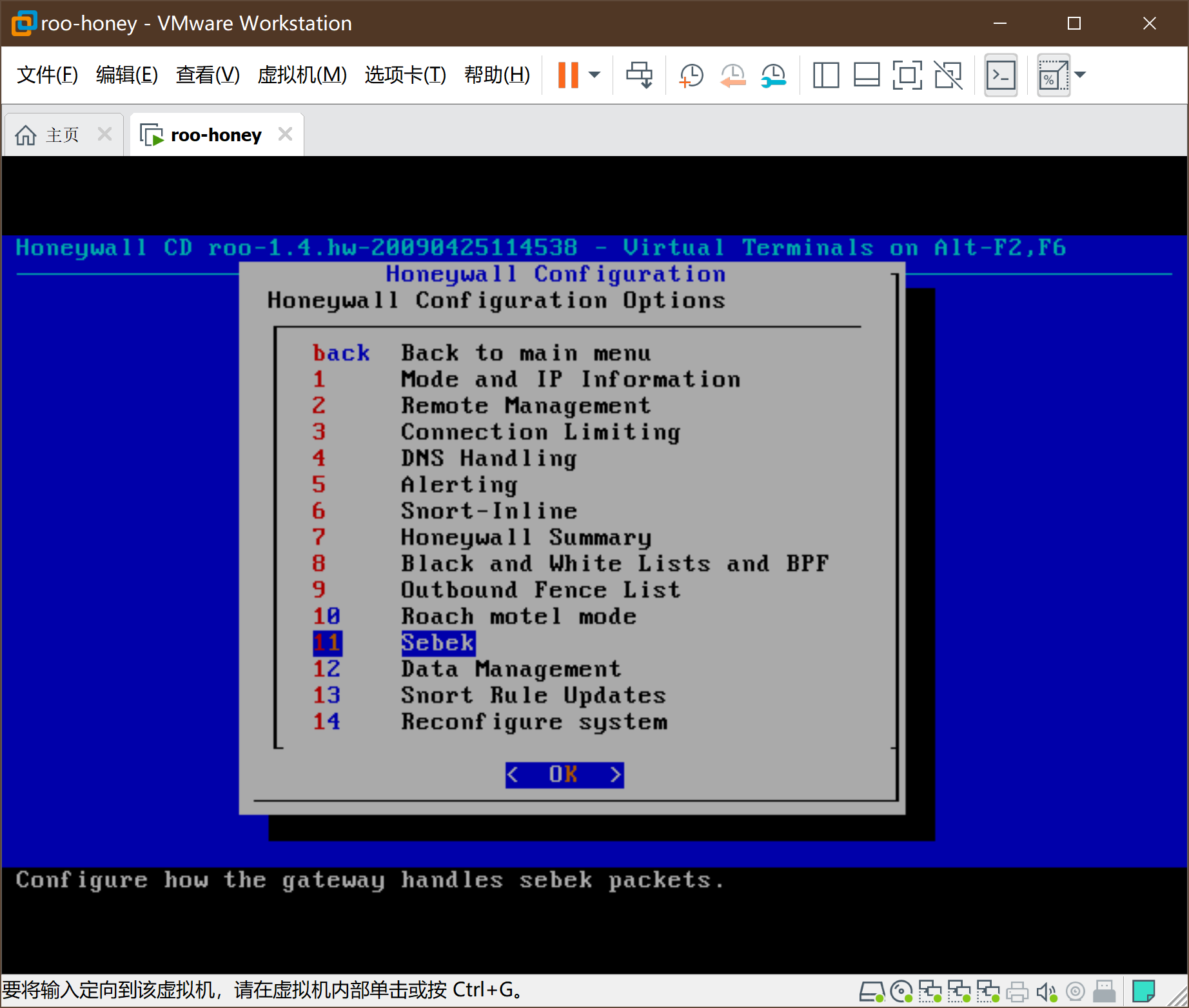
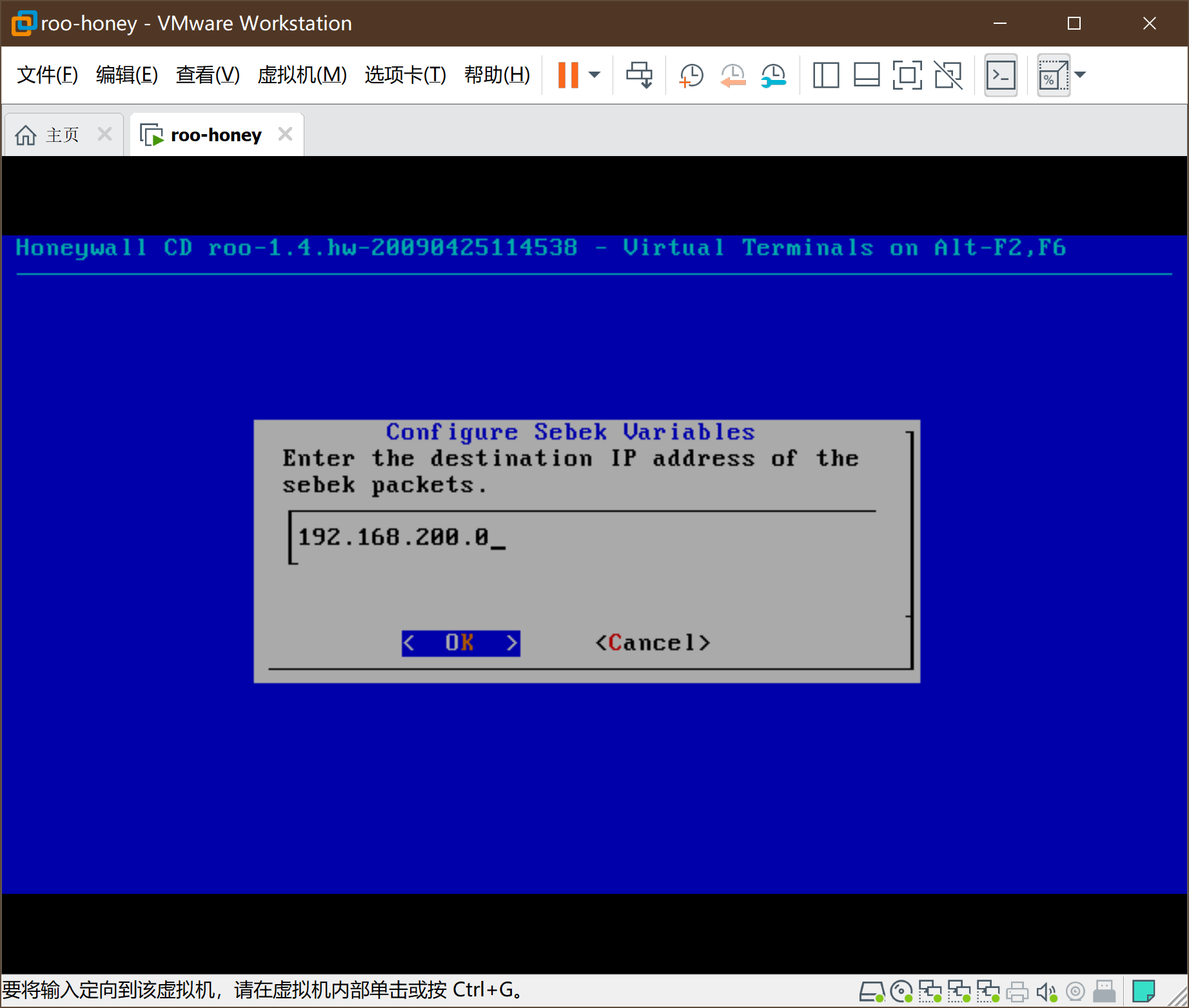
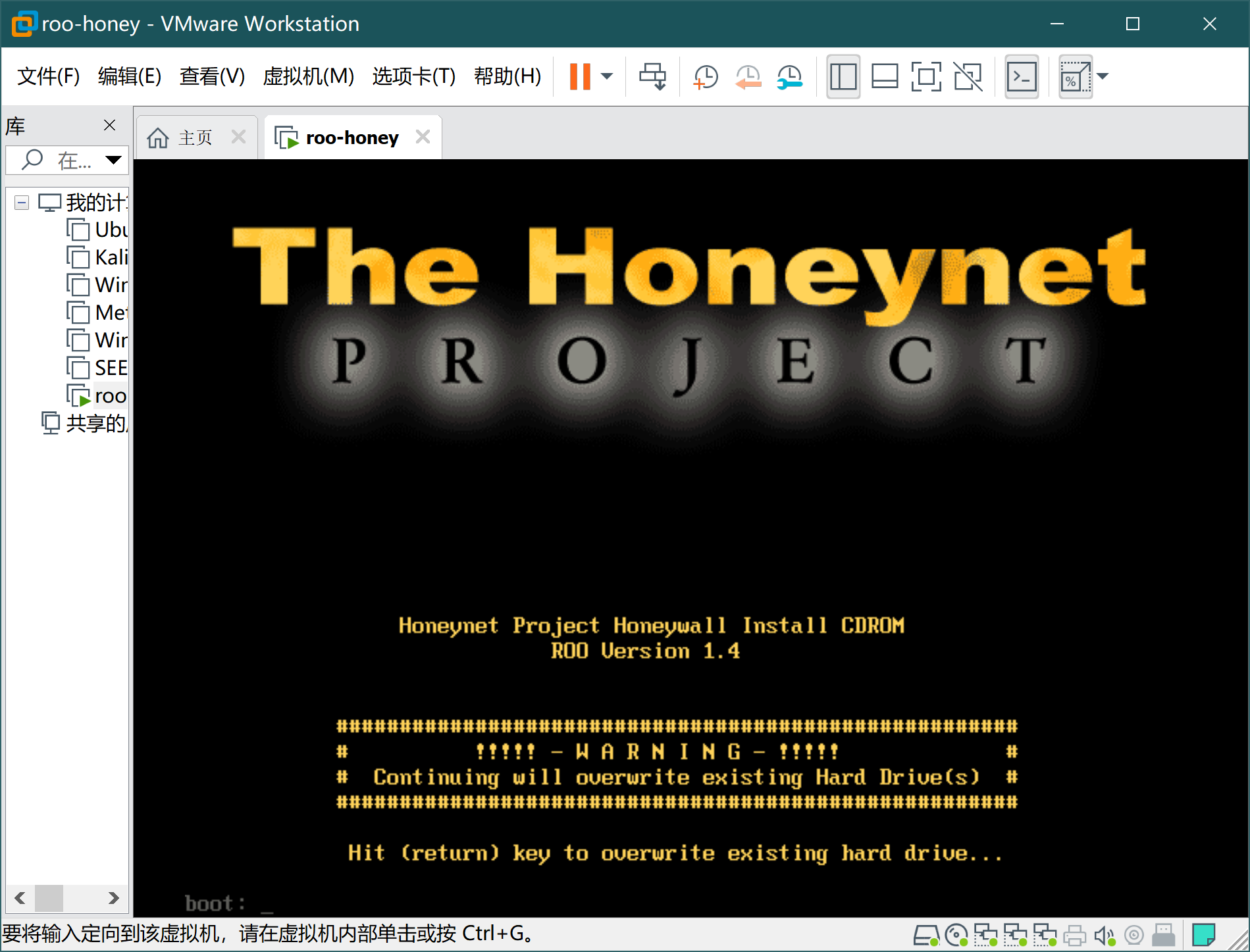
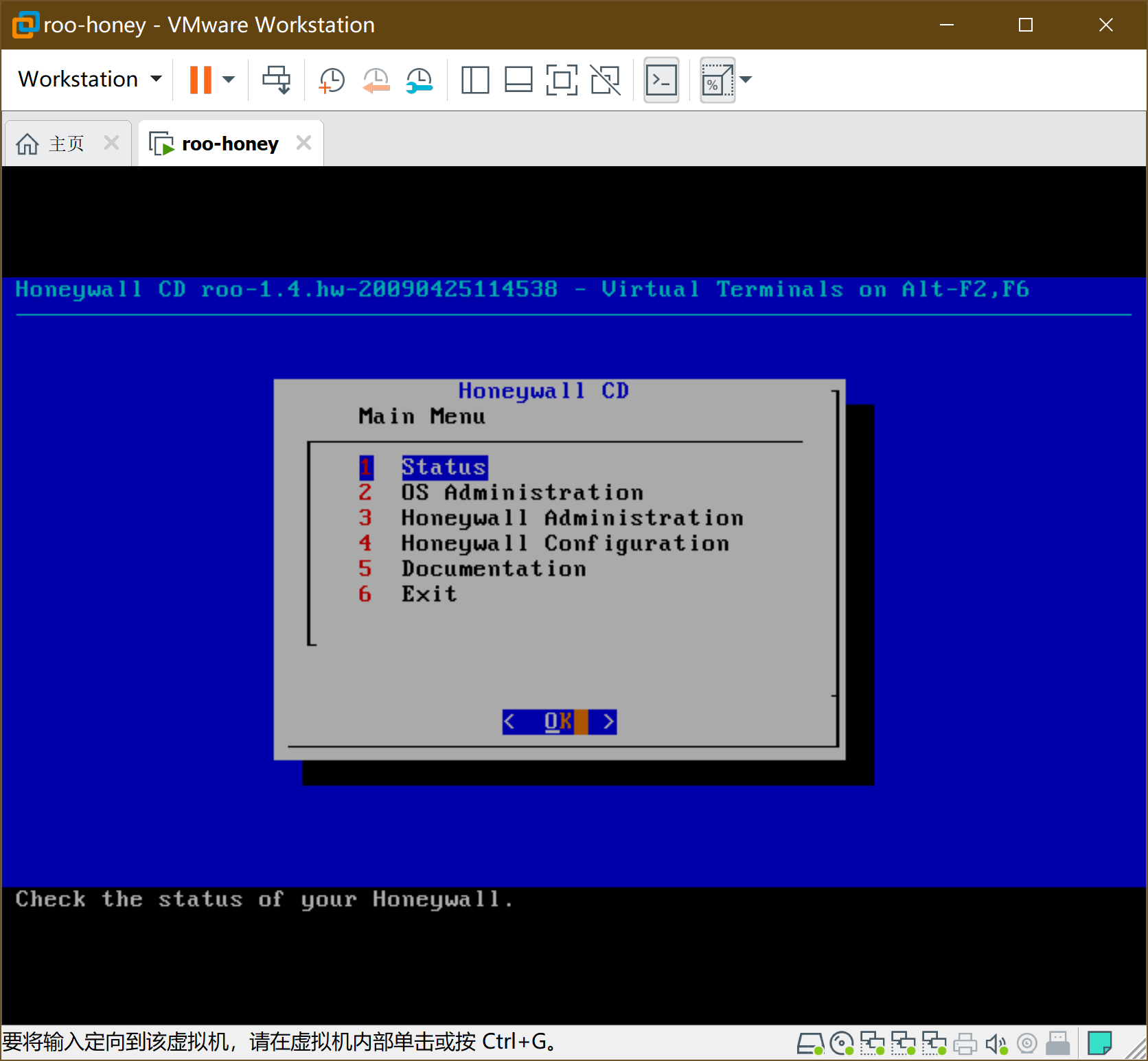
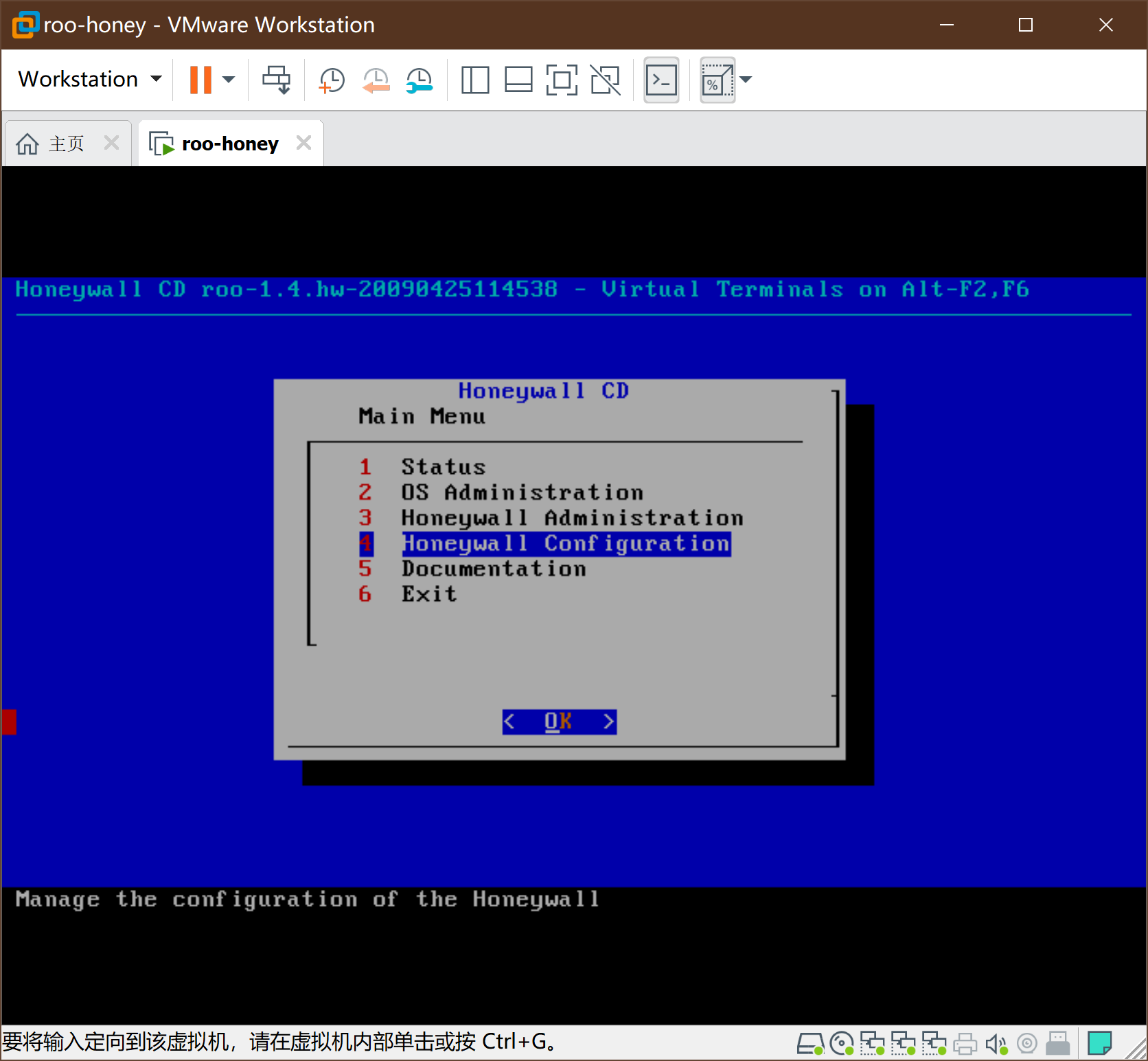
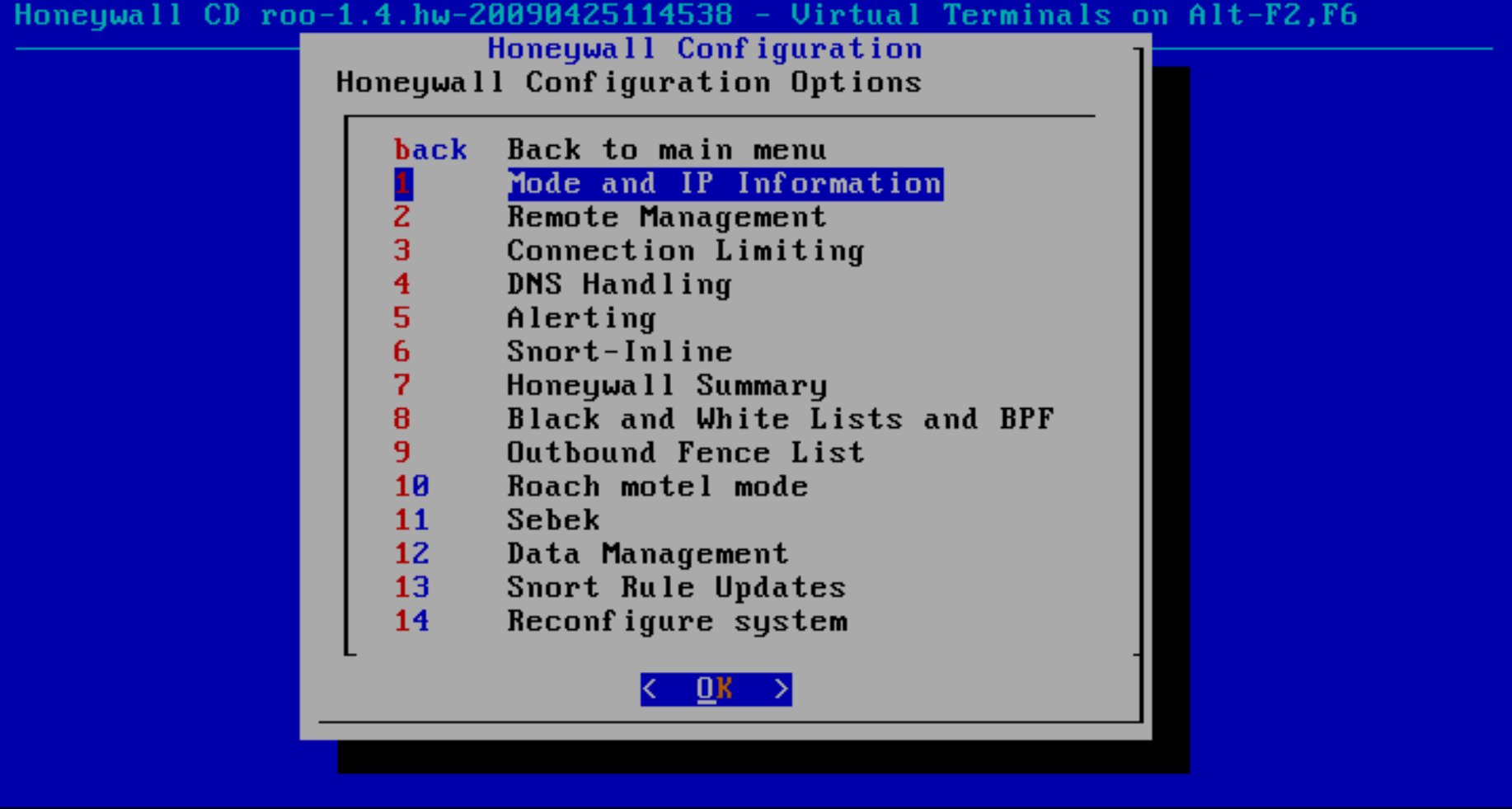
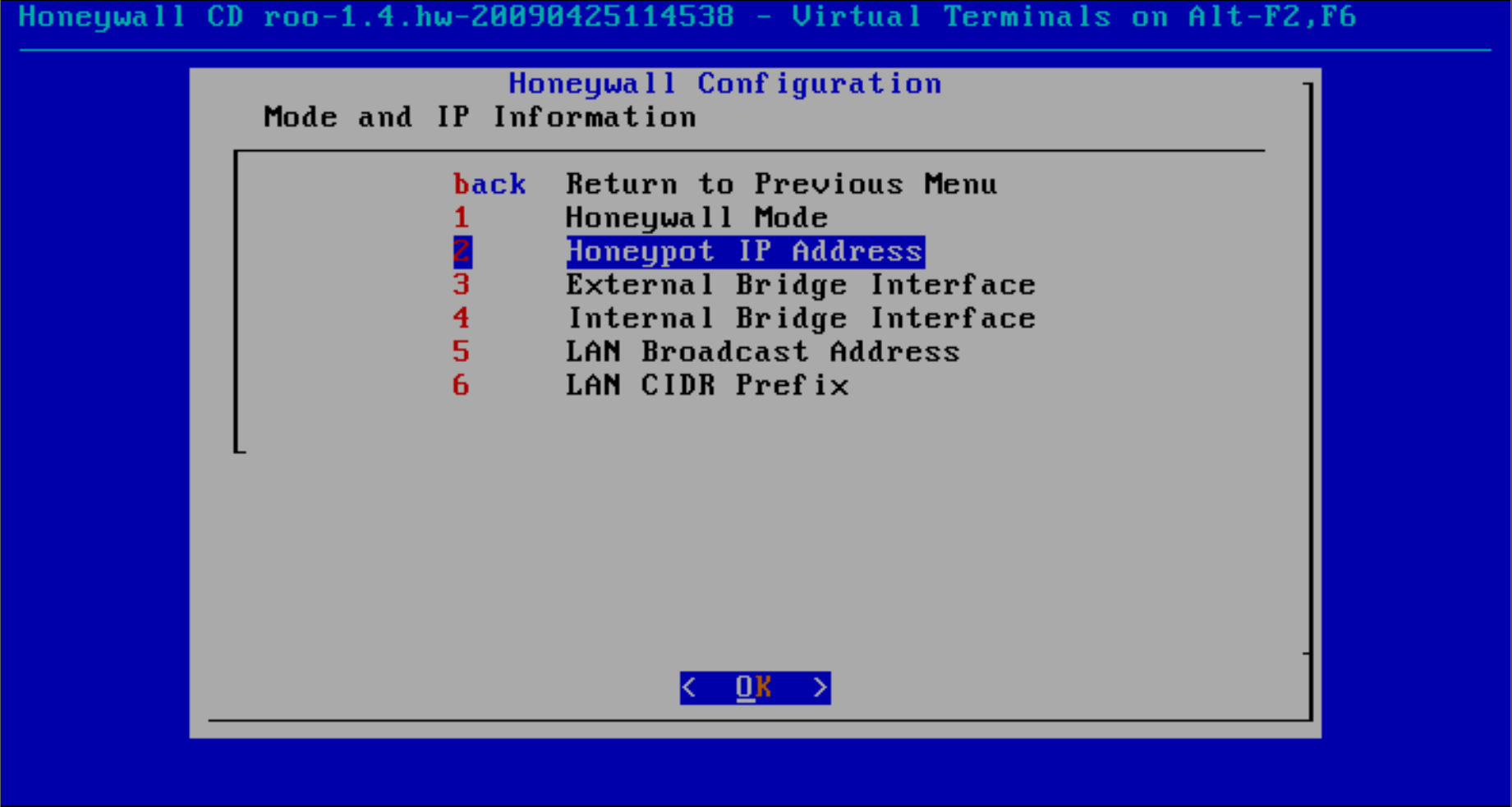
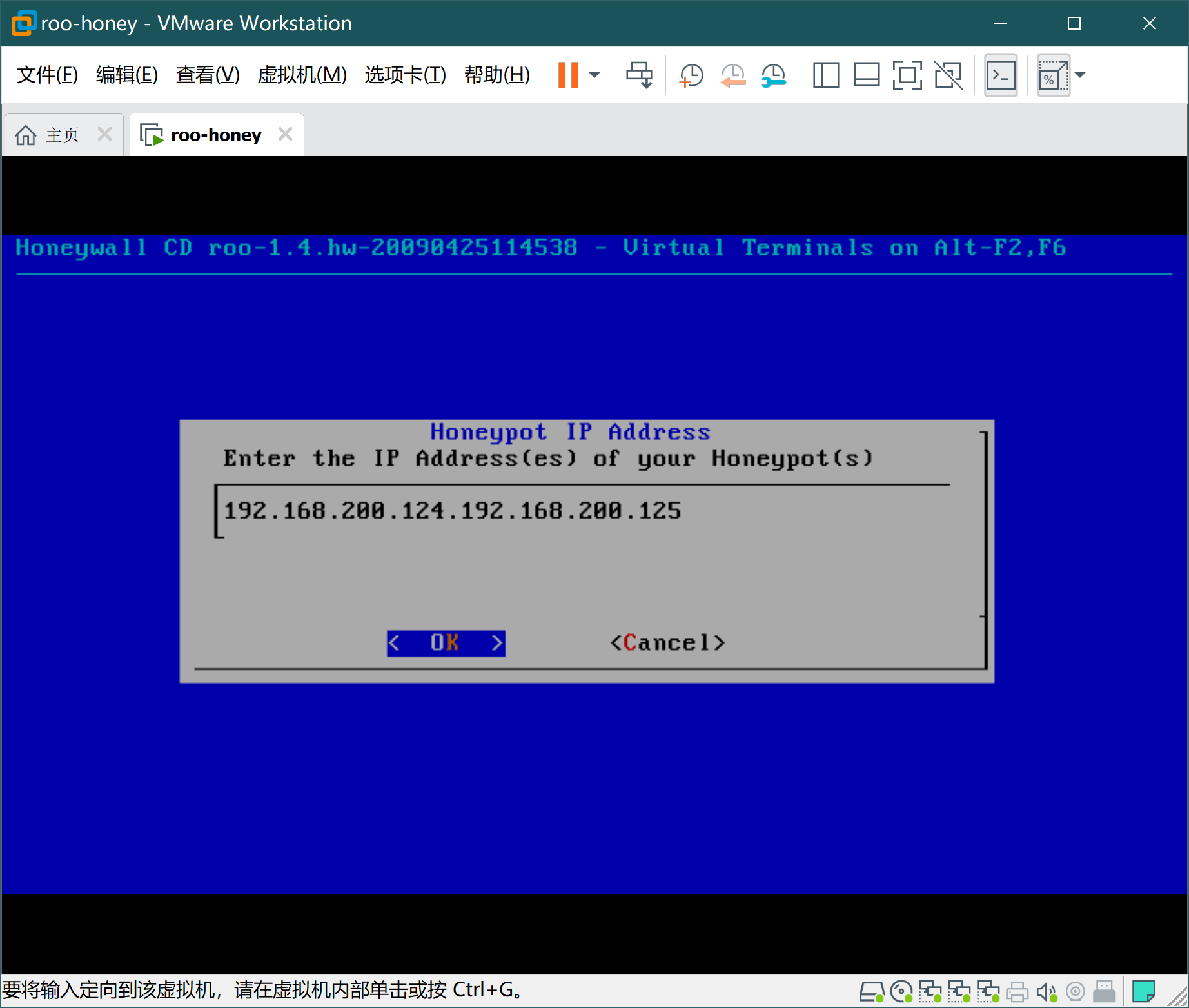
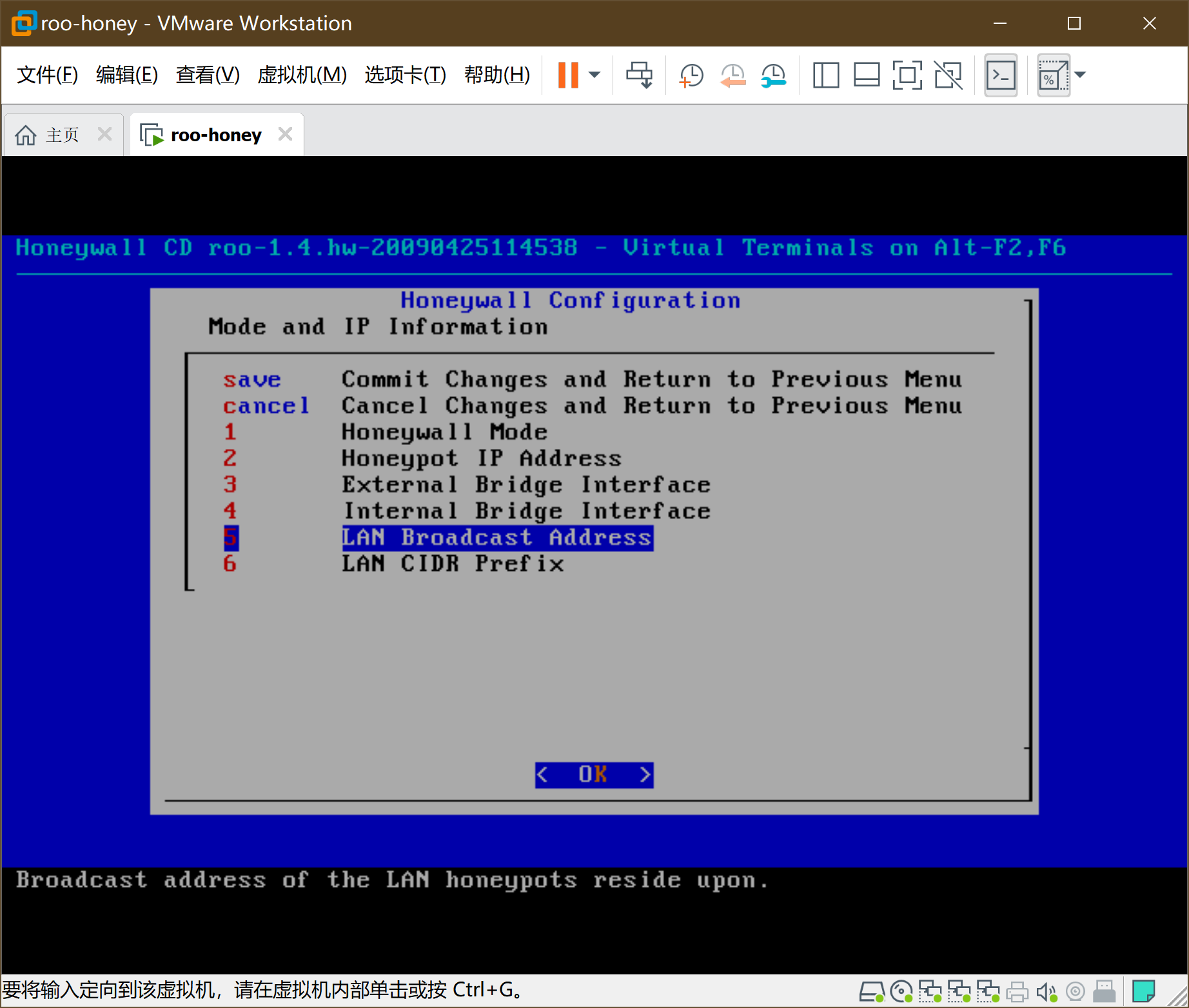
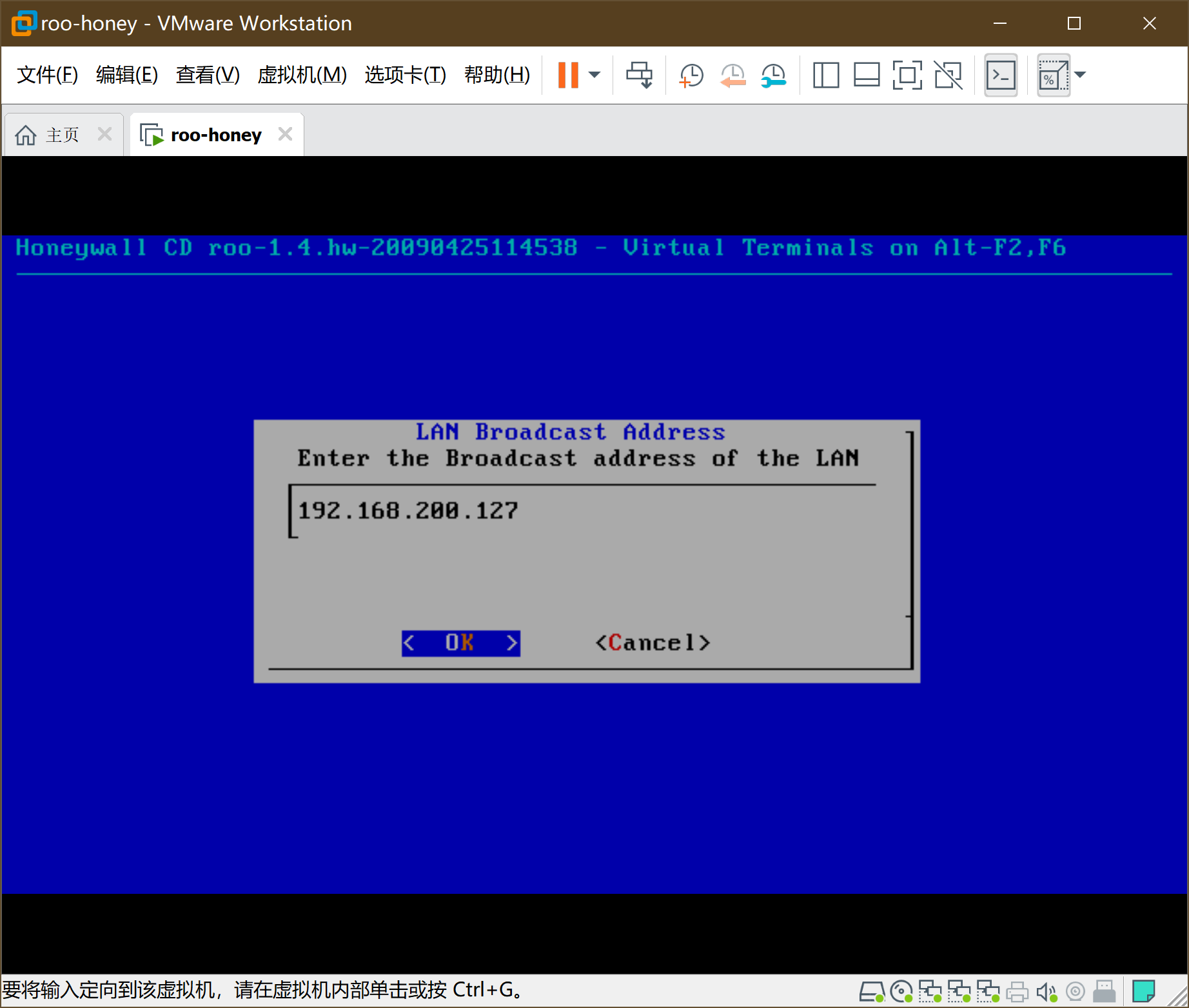
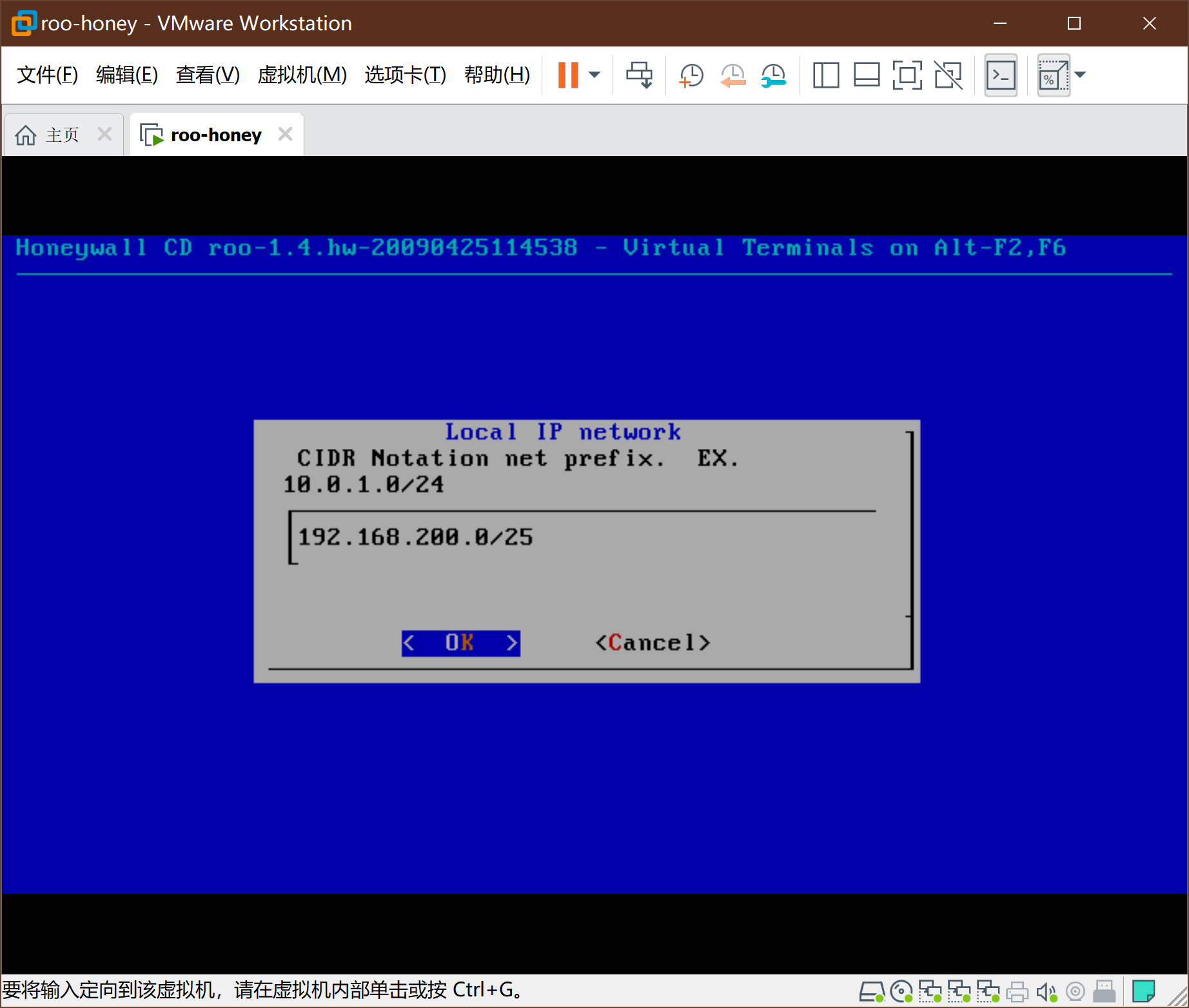
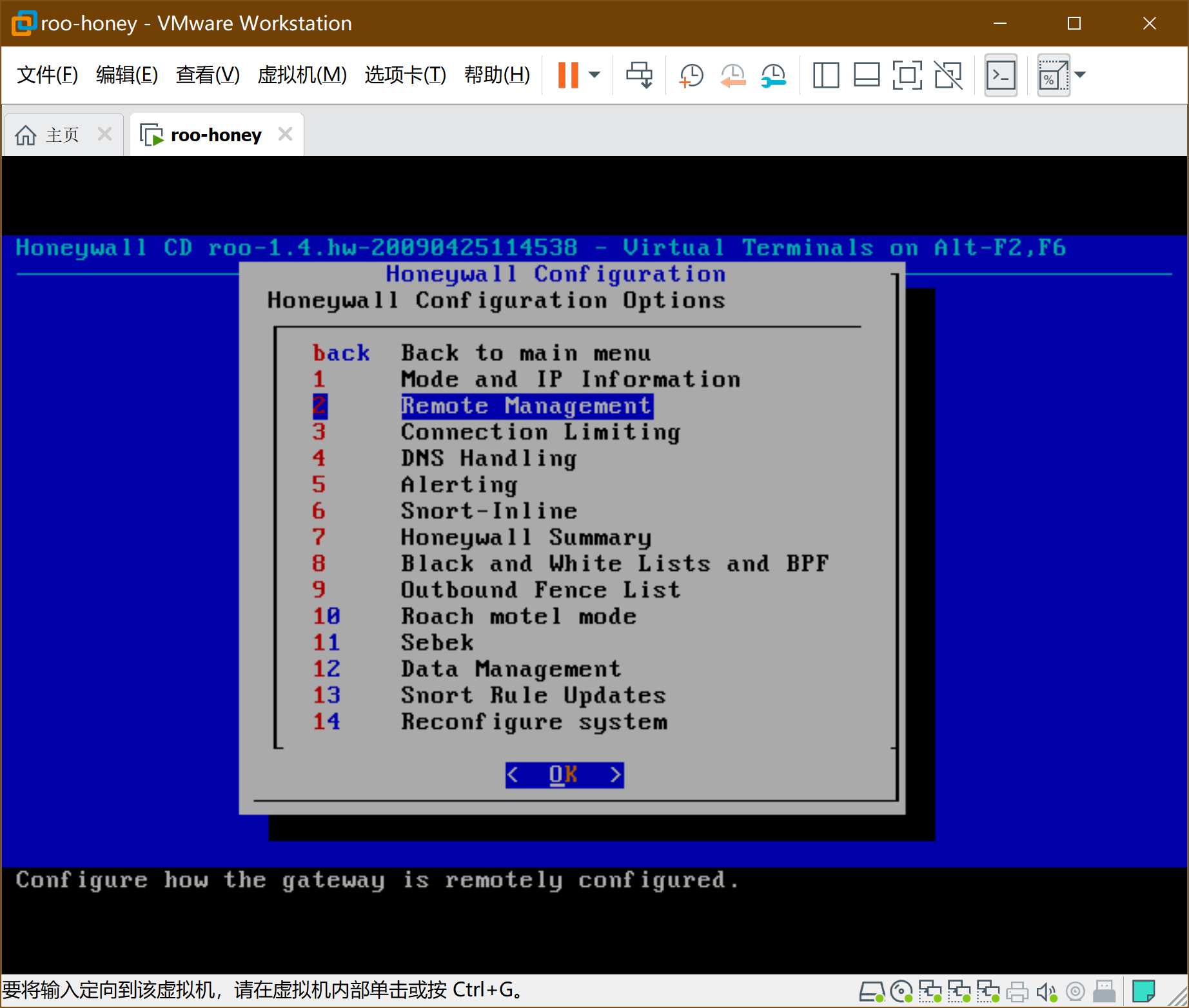
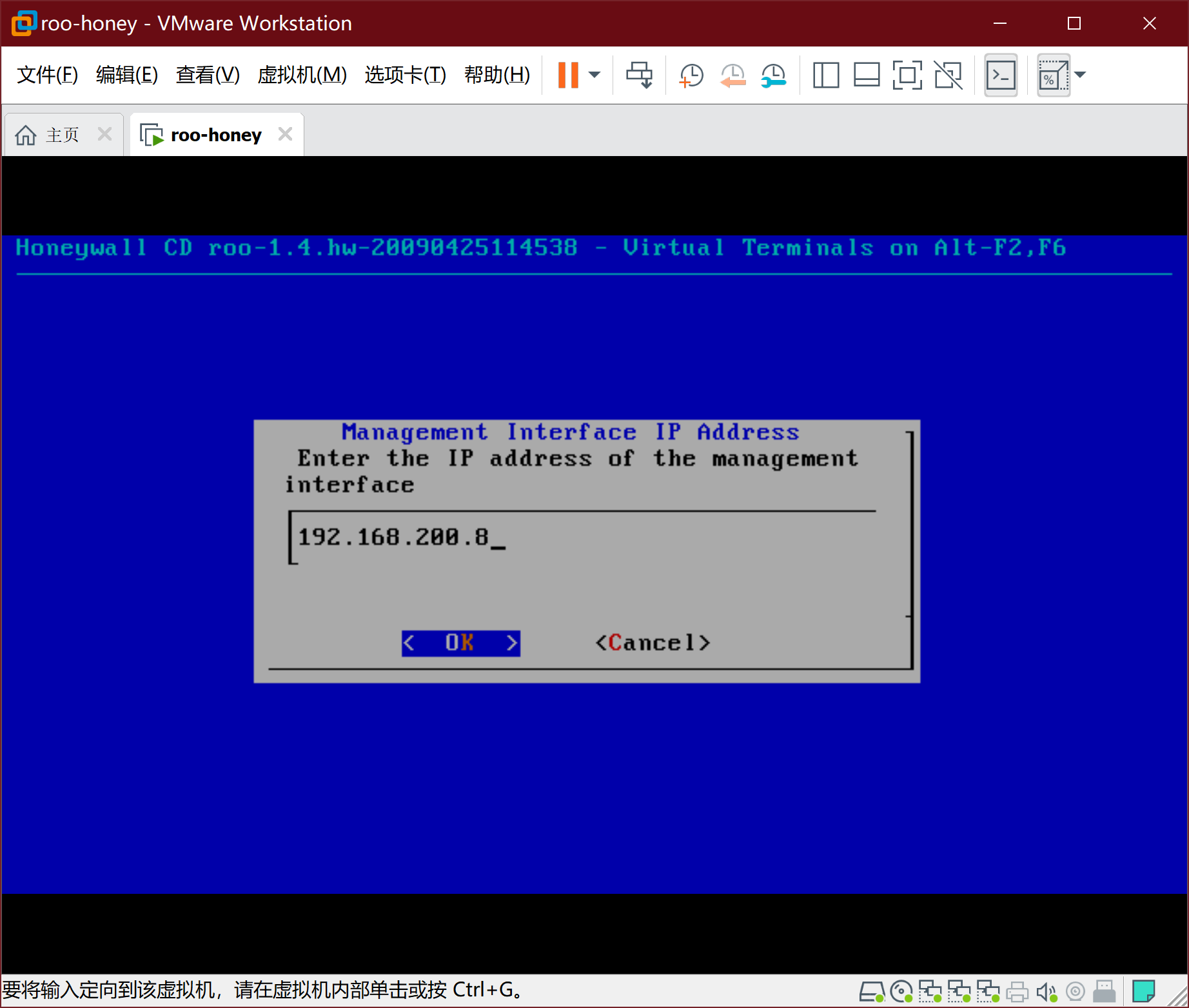
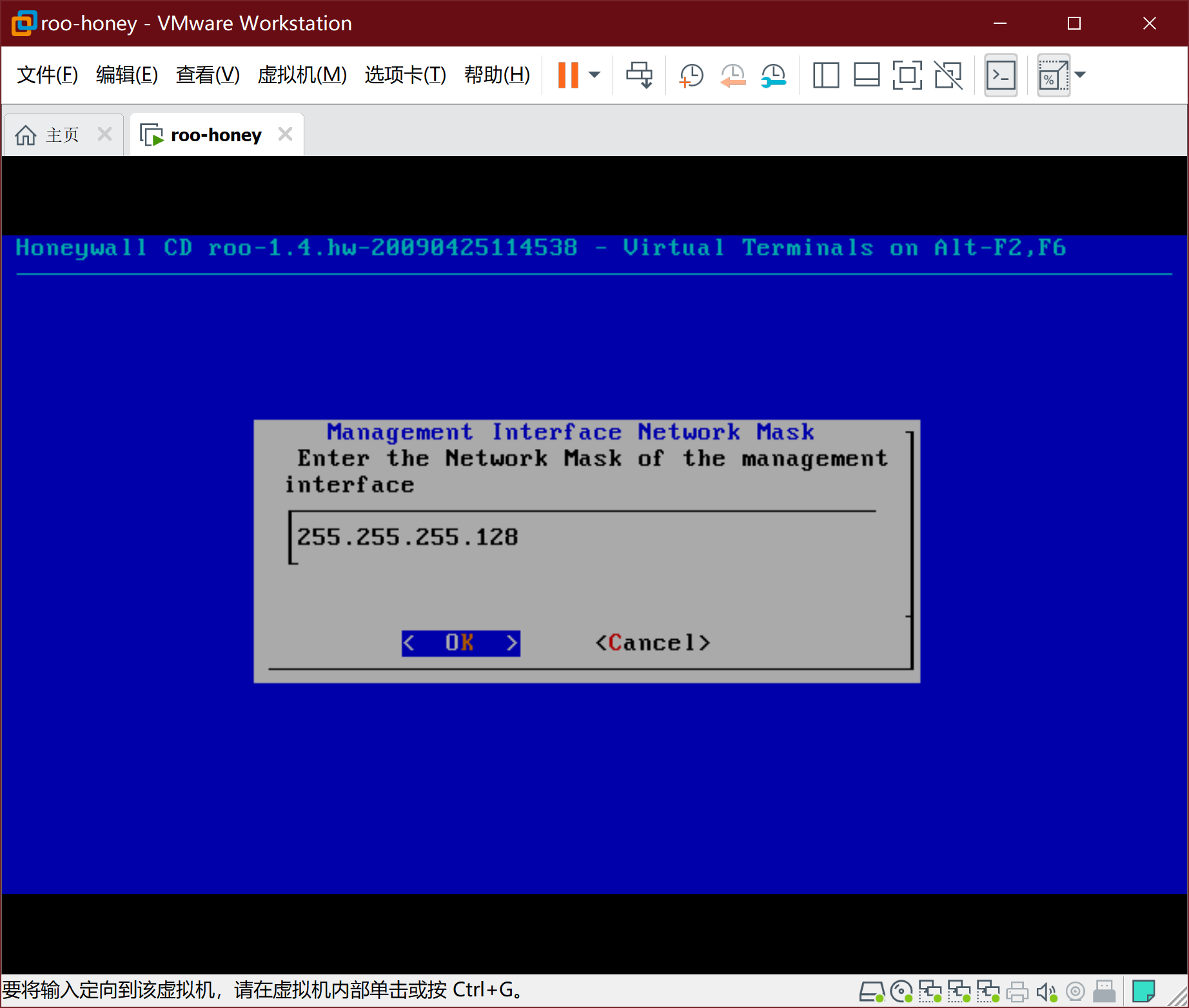
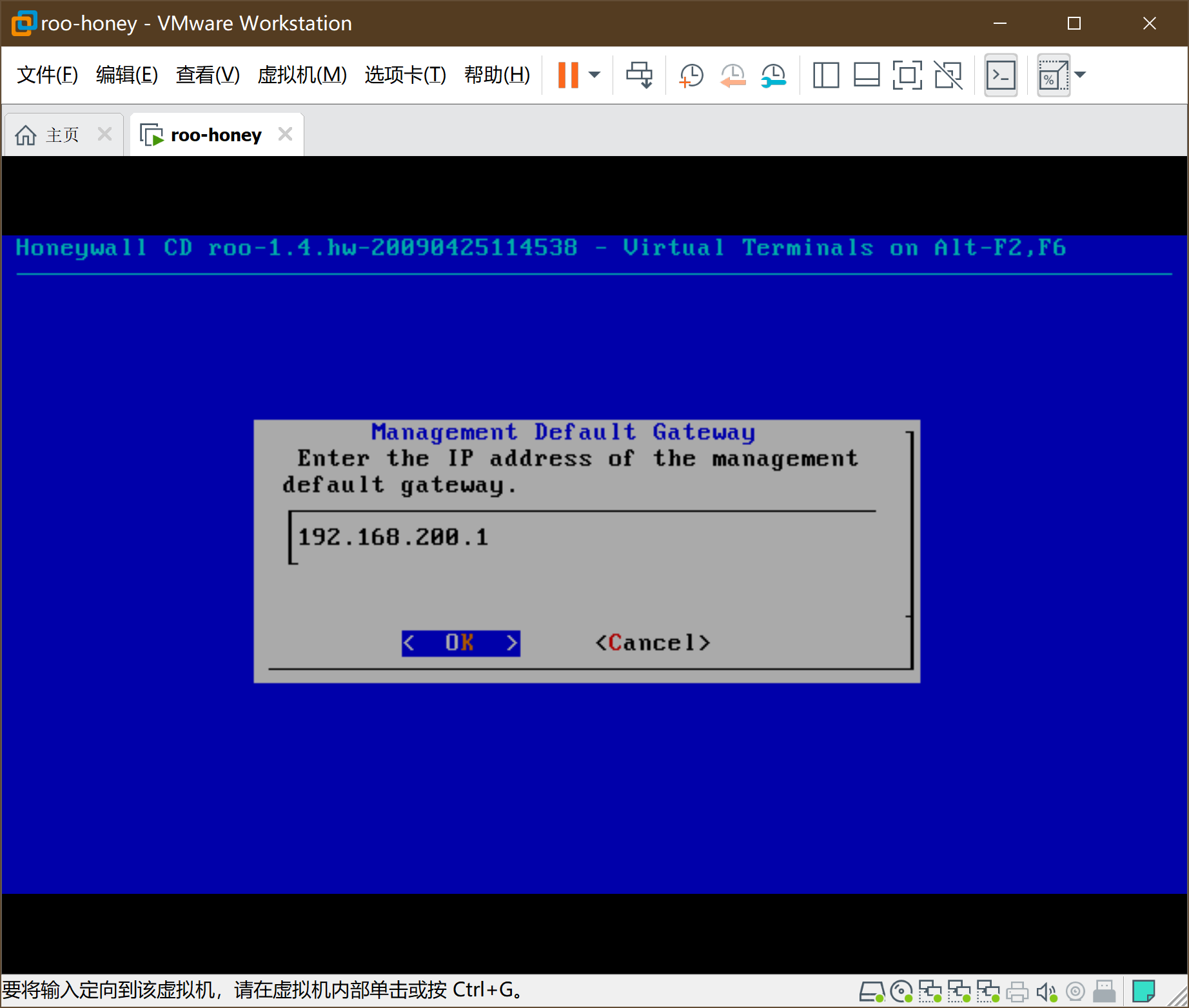
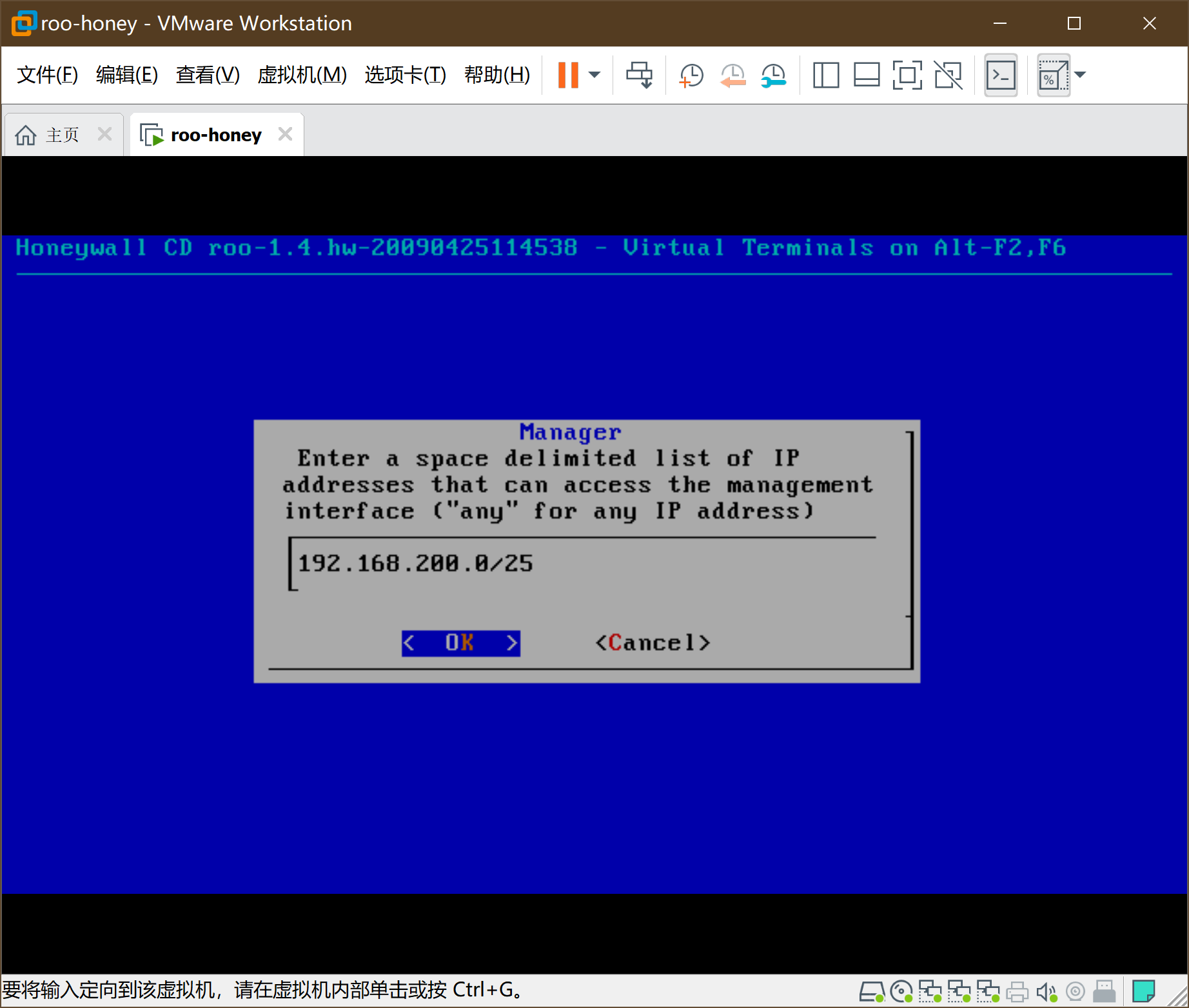
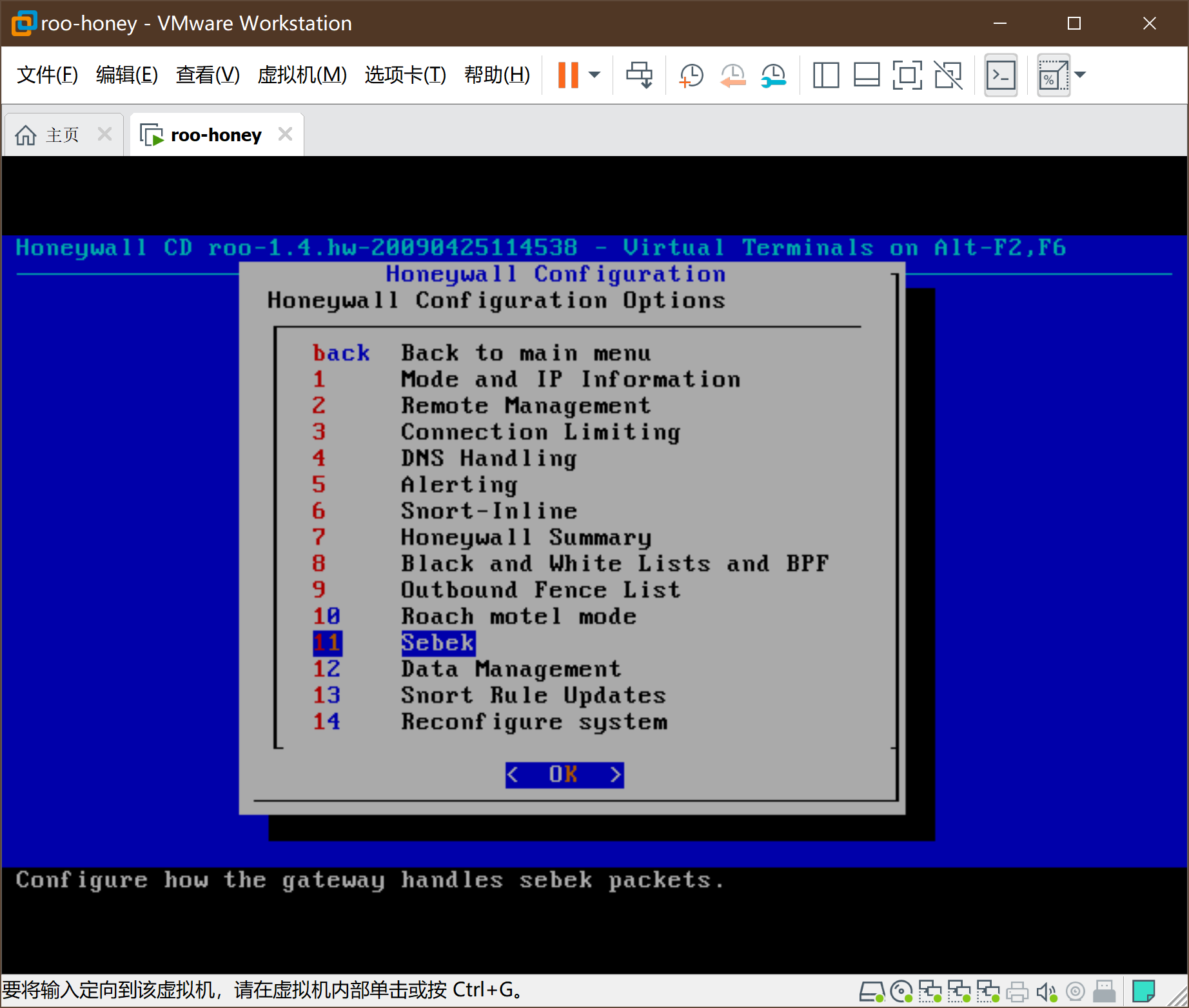
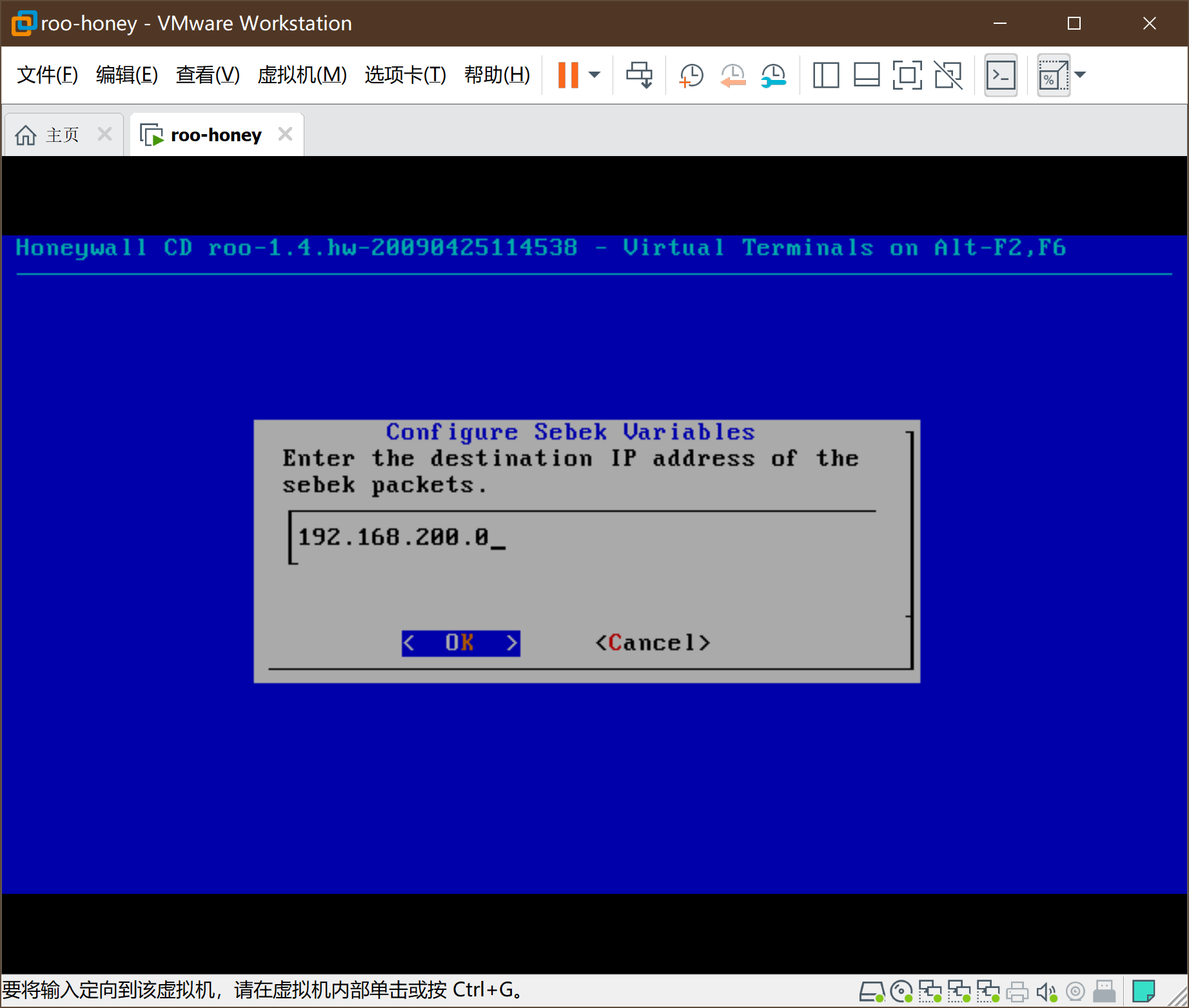
8、安装蜜罐网关
-
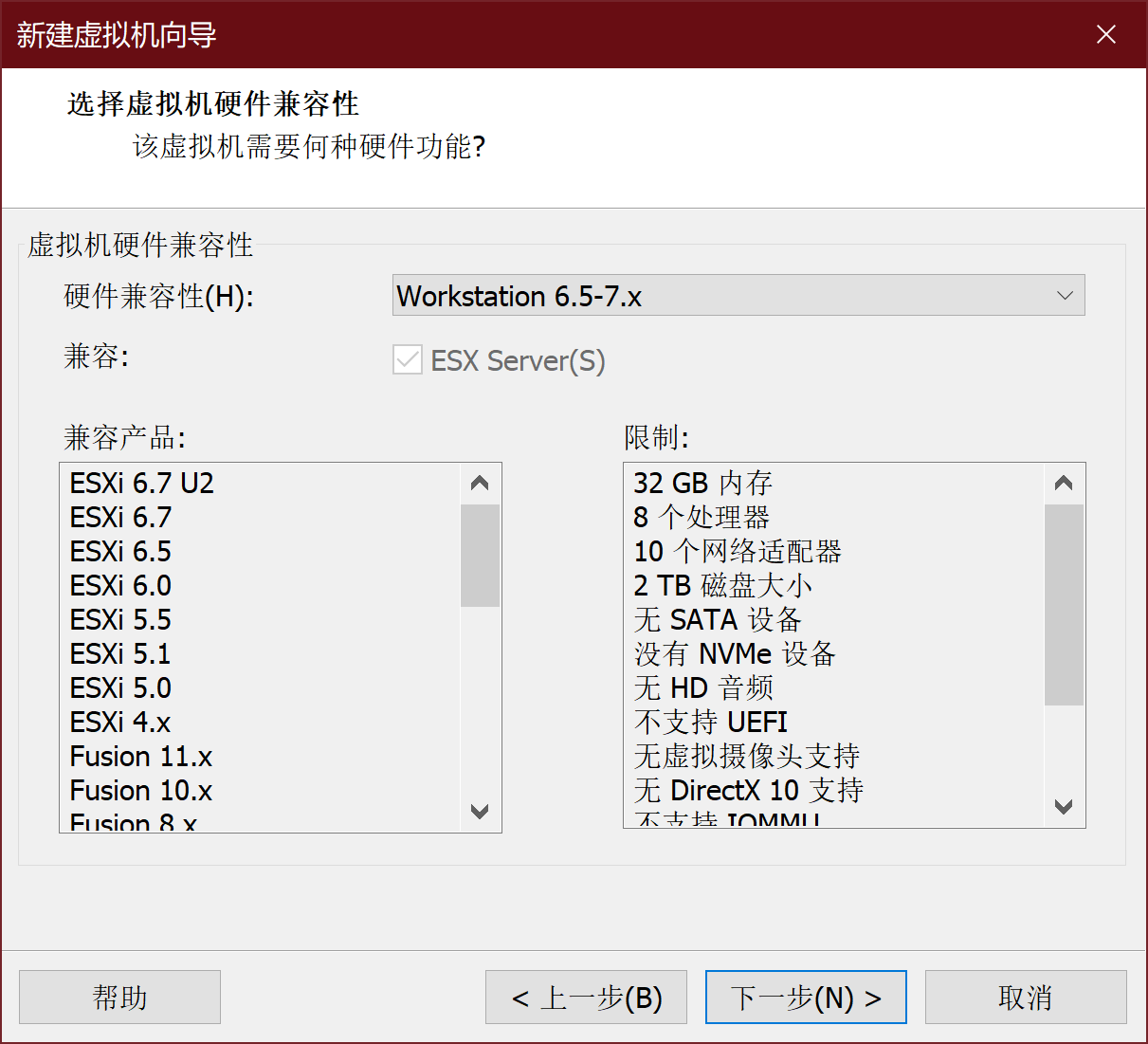
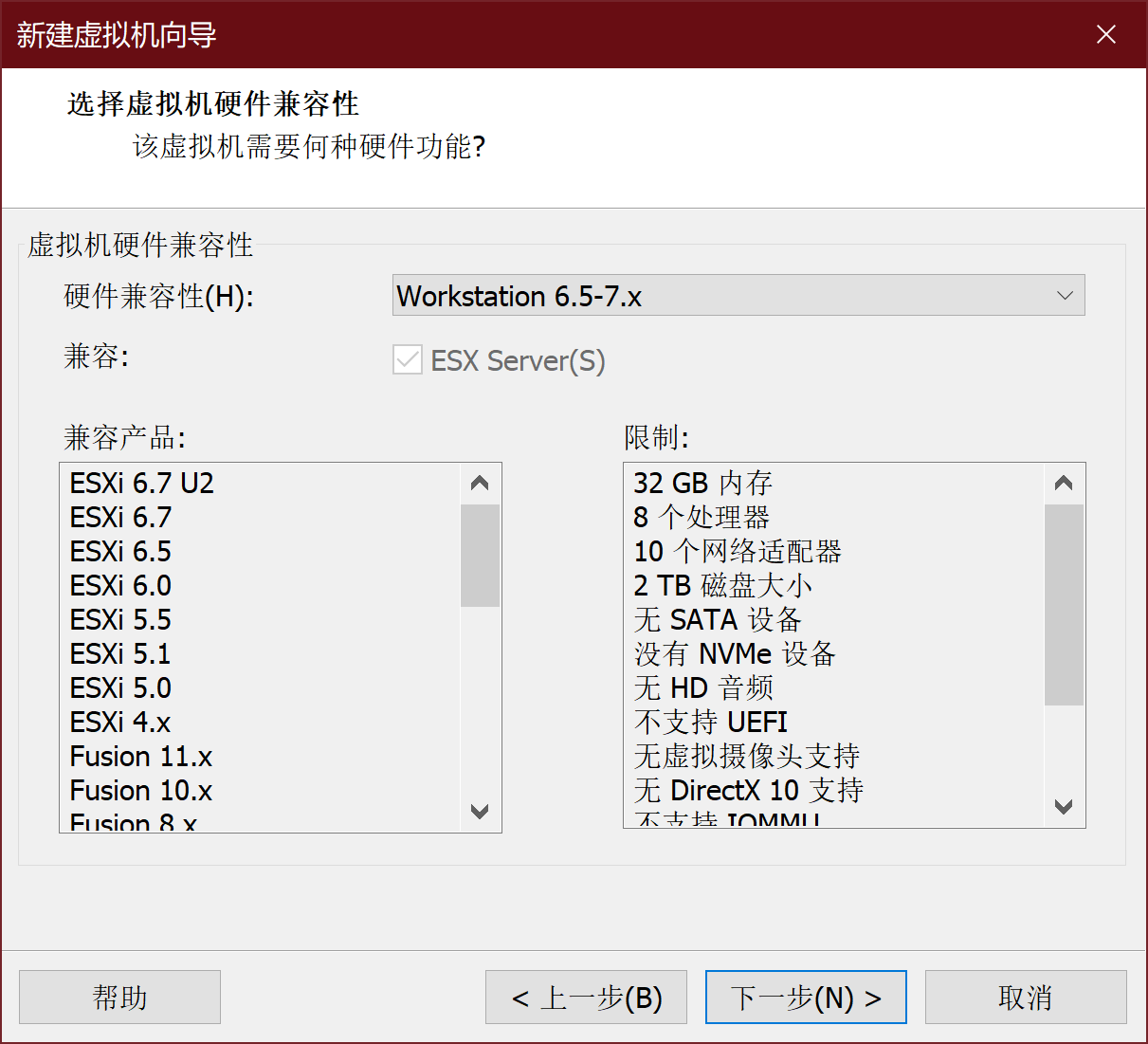
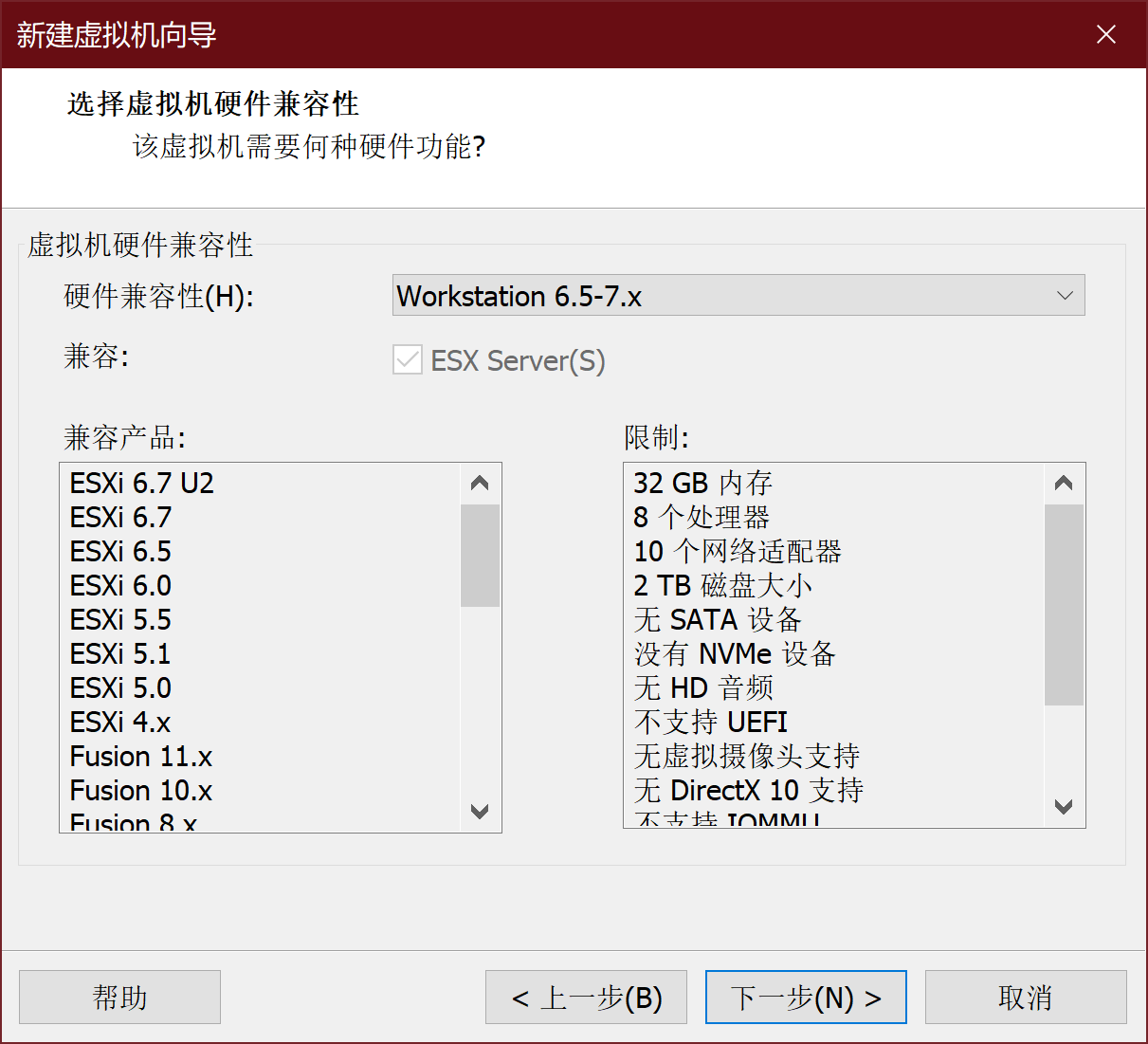
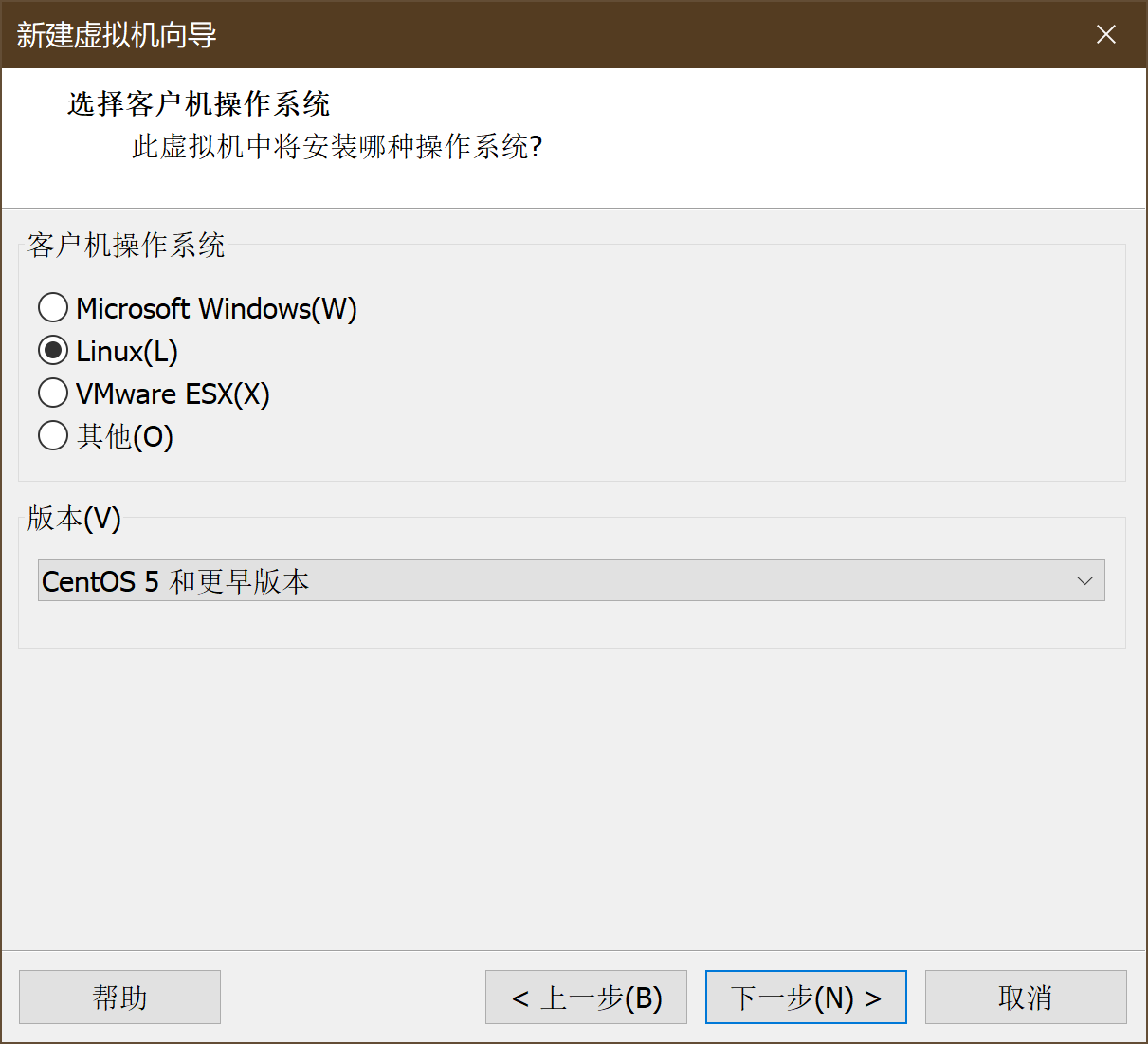
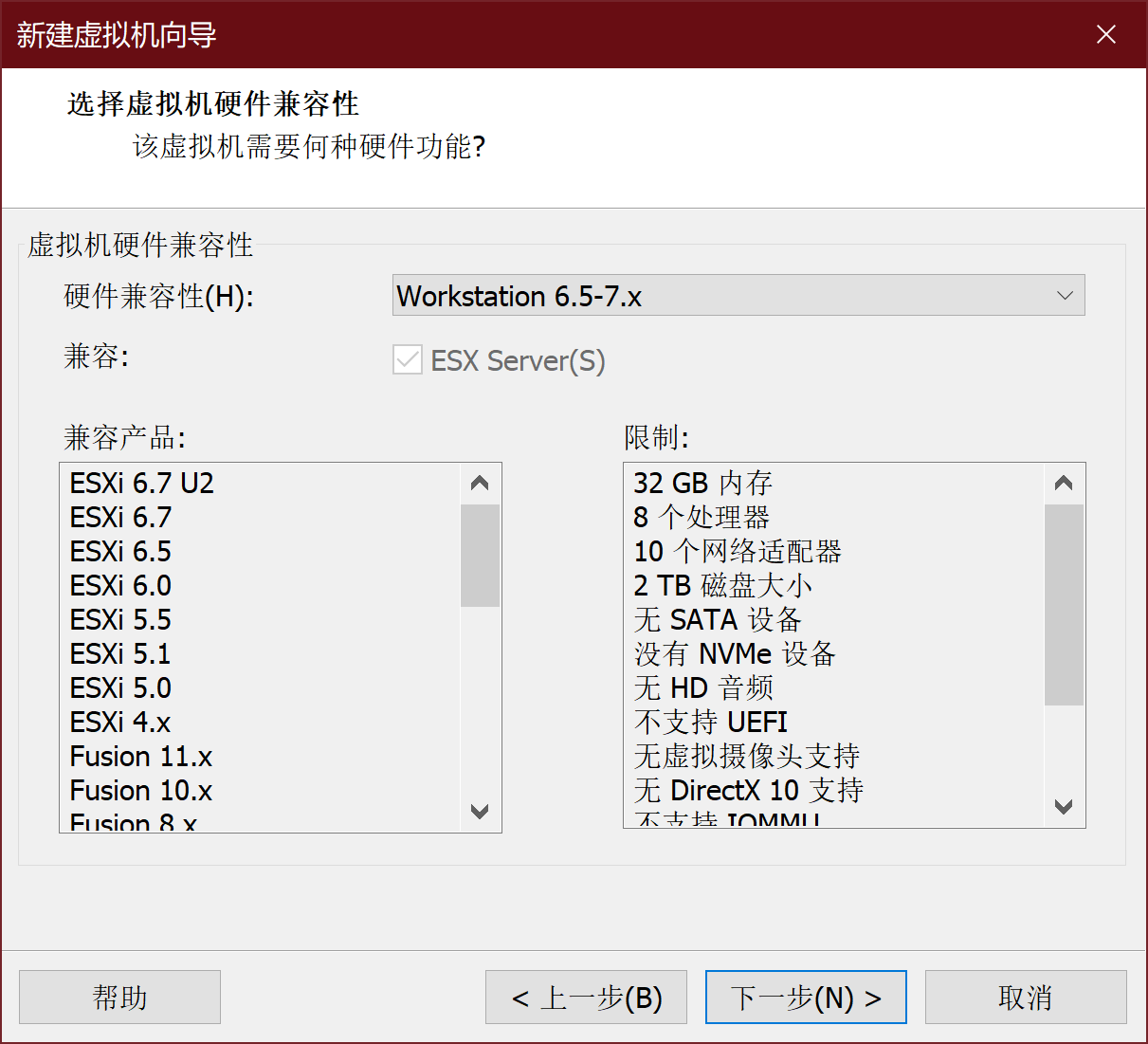
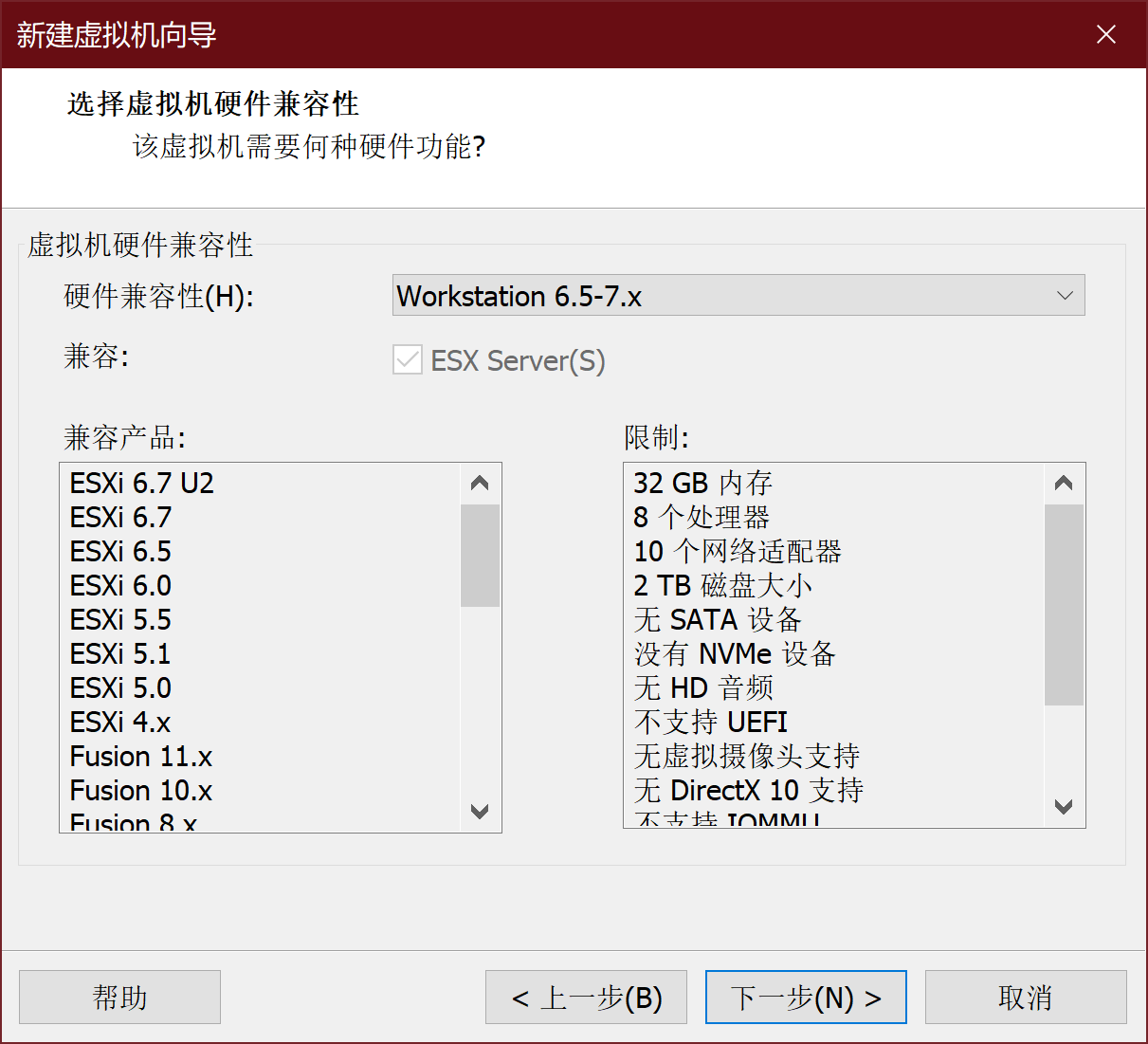
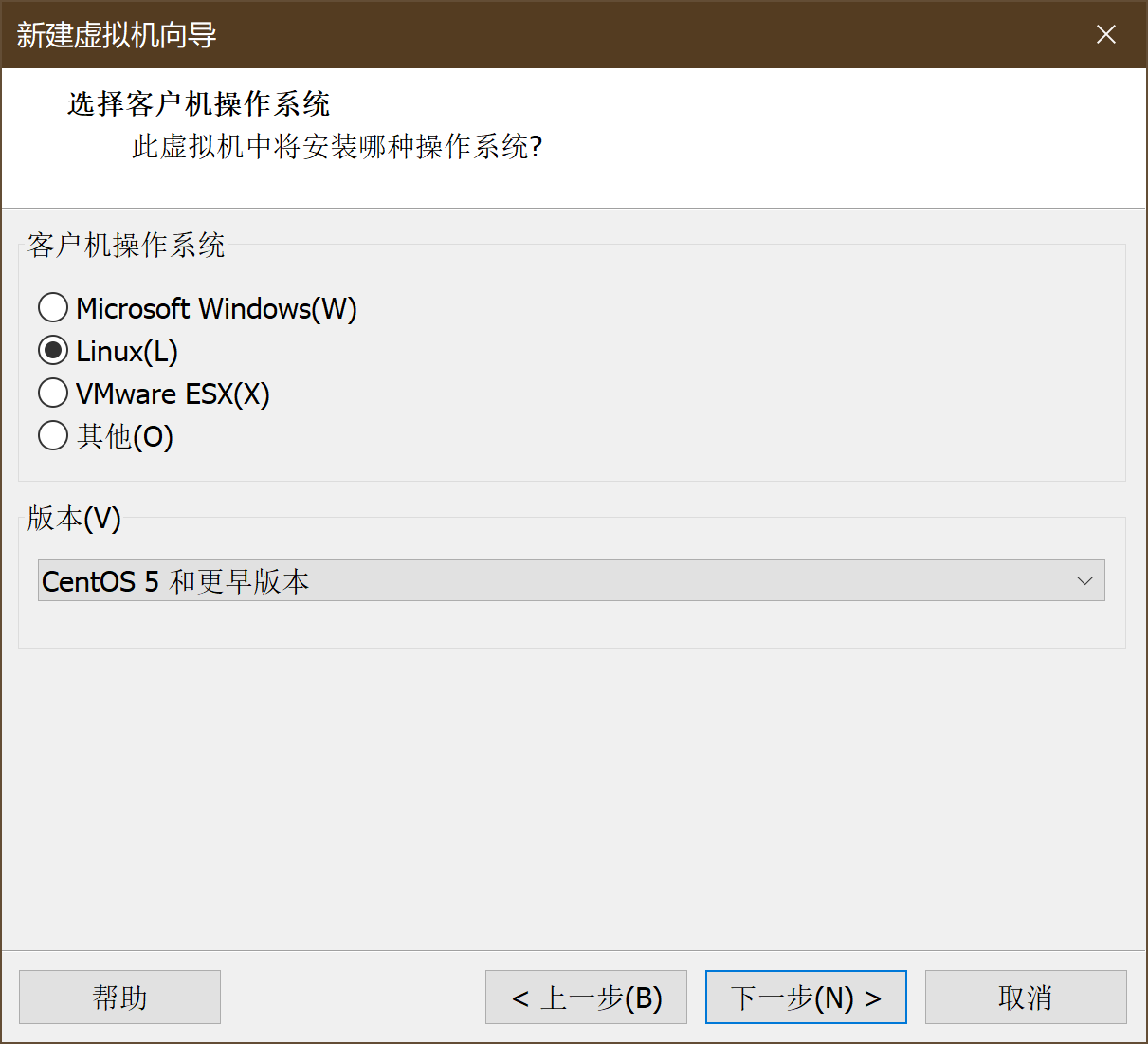
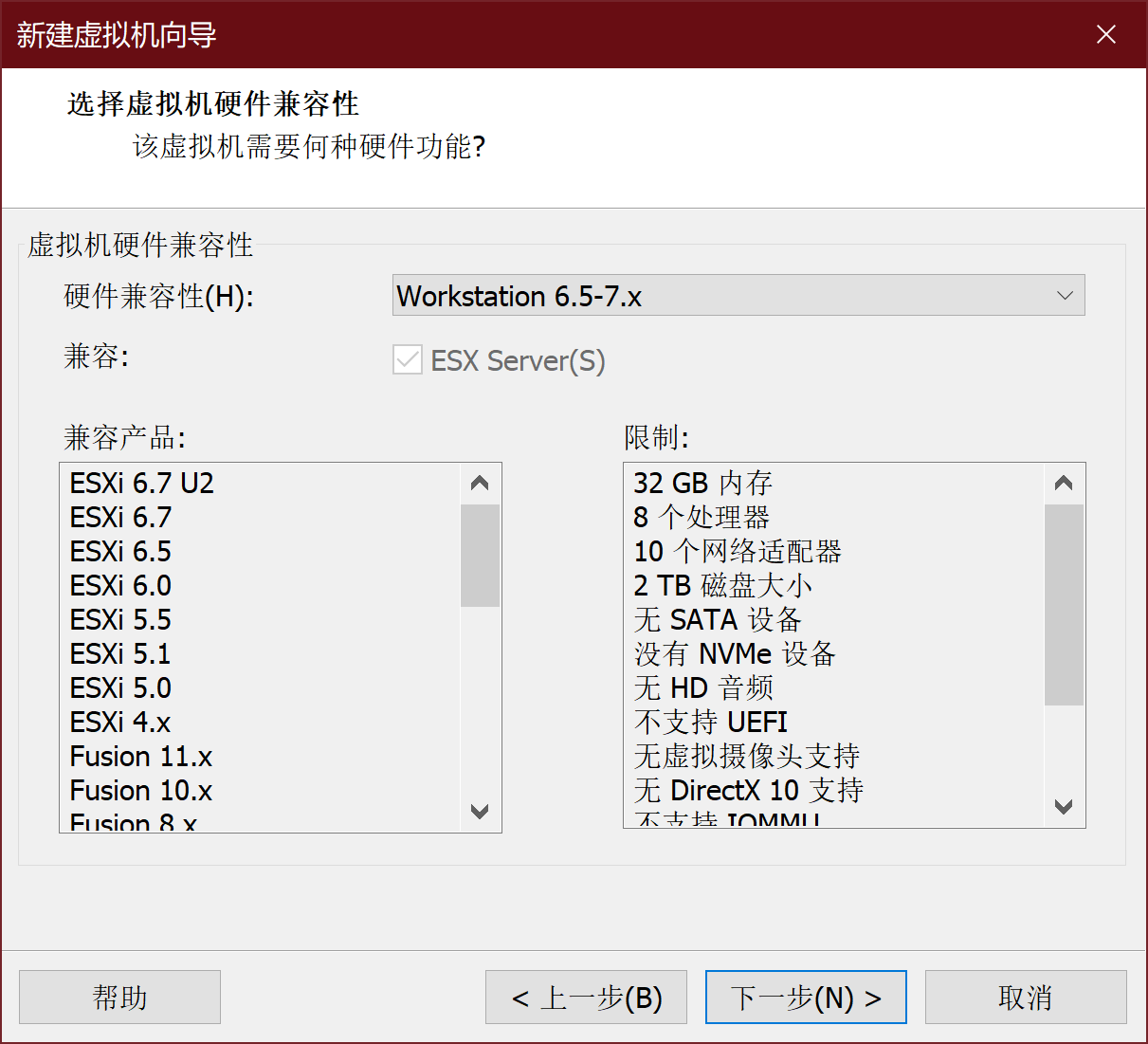
新建虚拟机->自定义->硬件兼容性
-
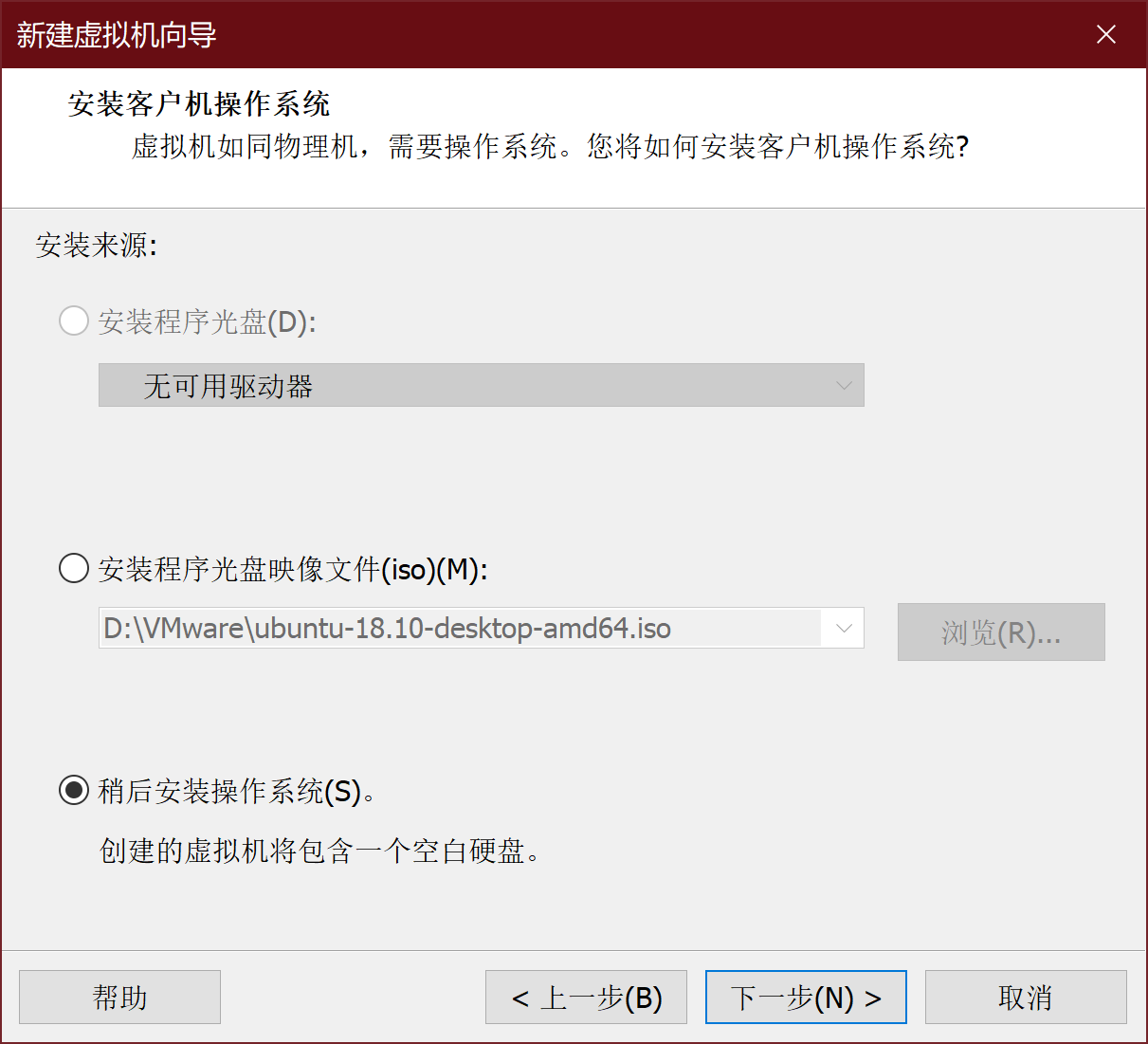
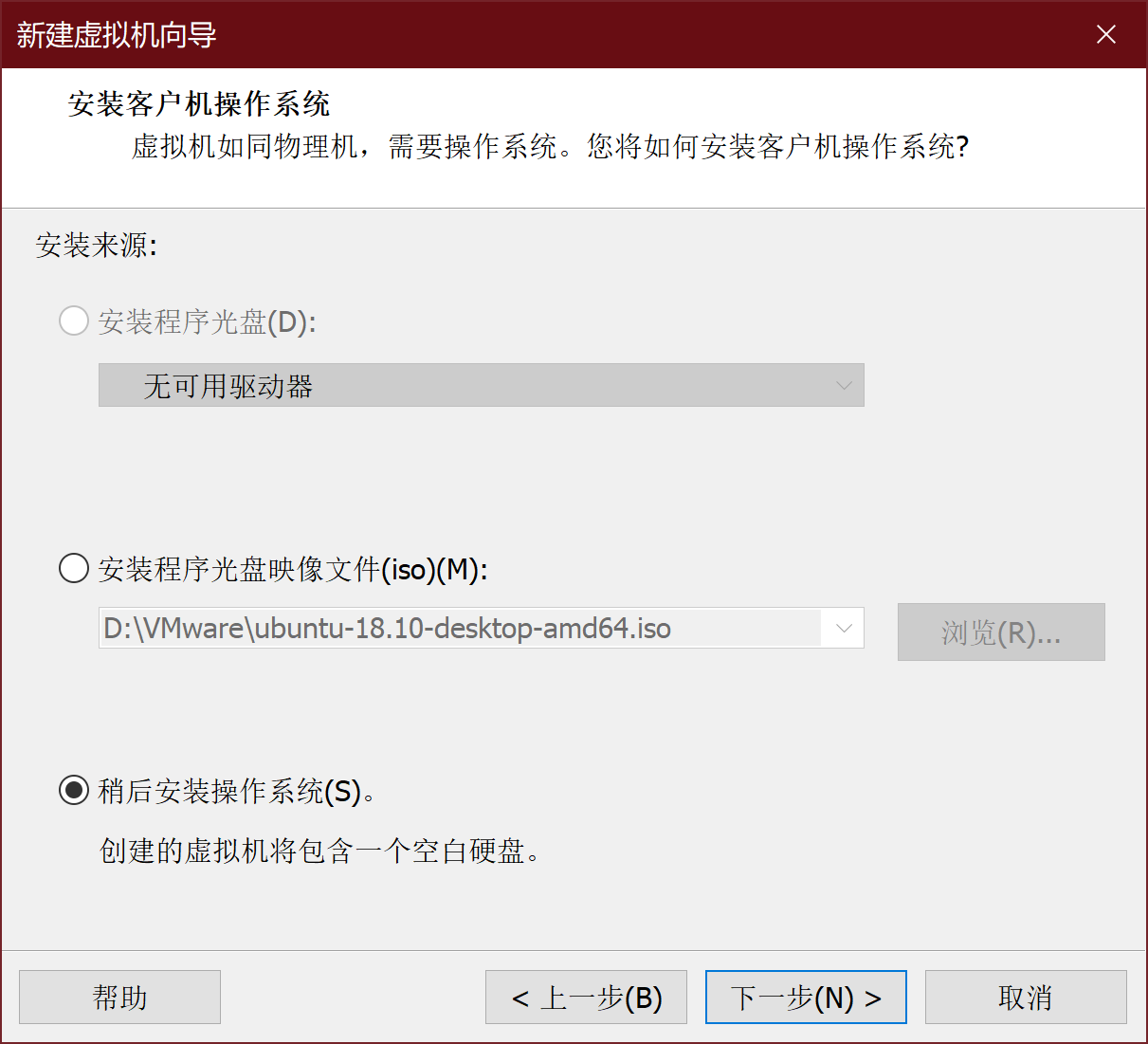
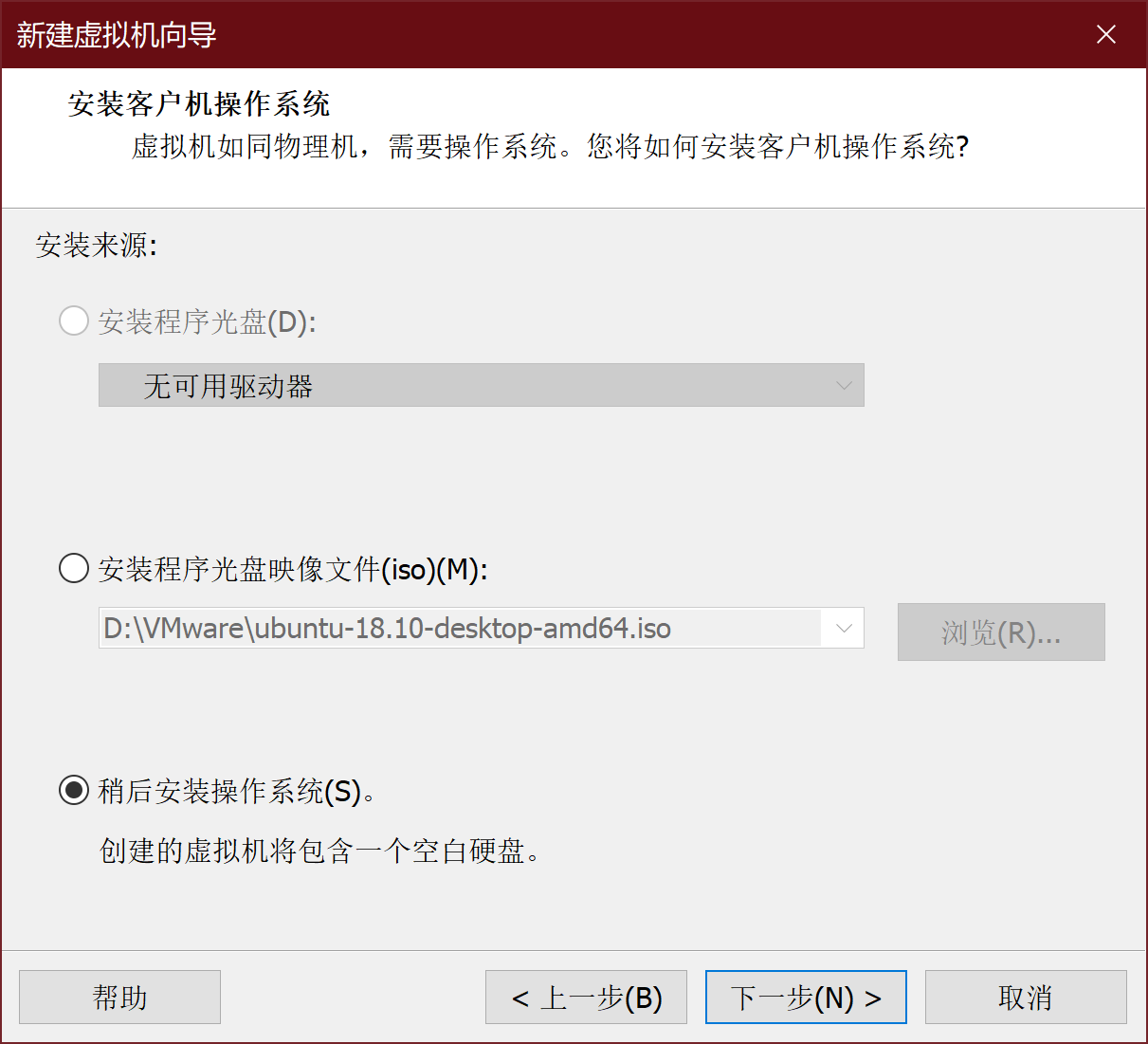
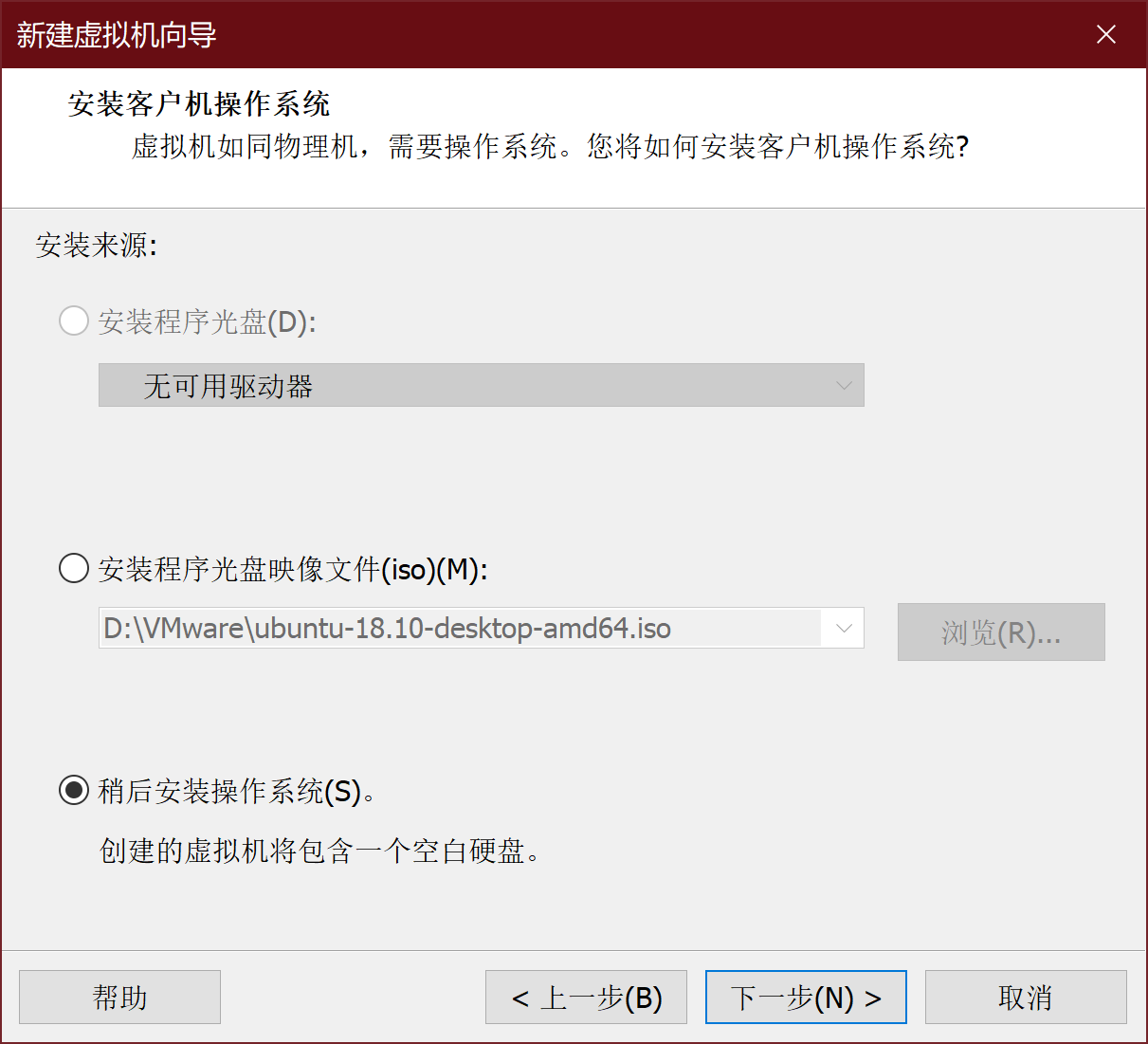
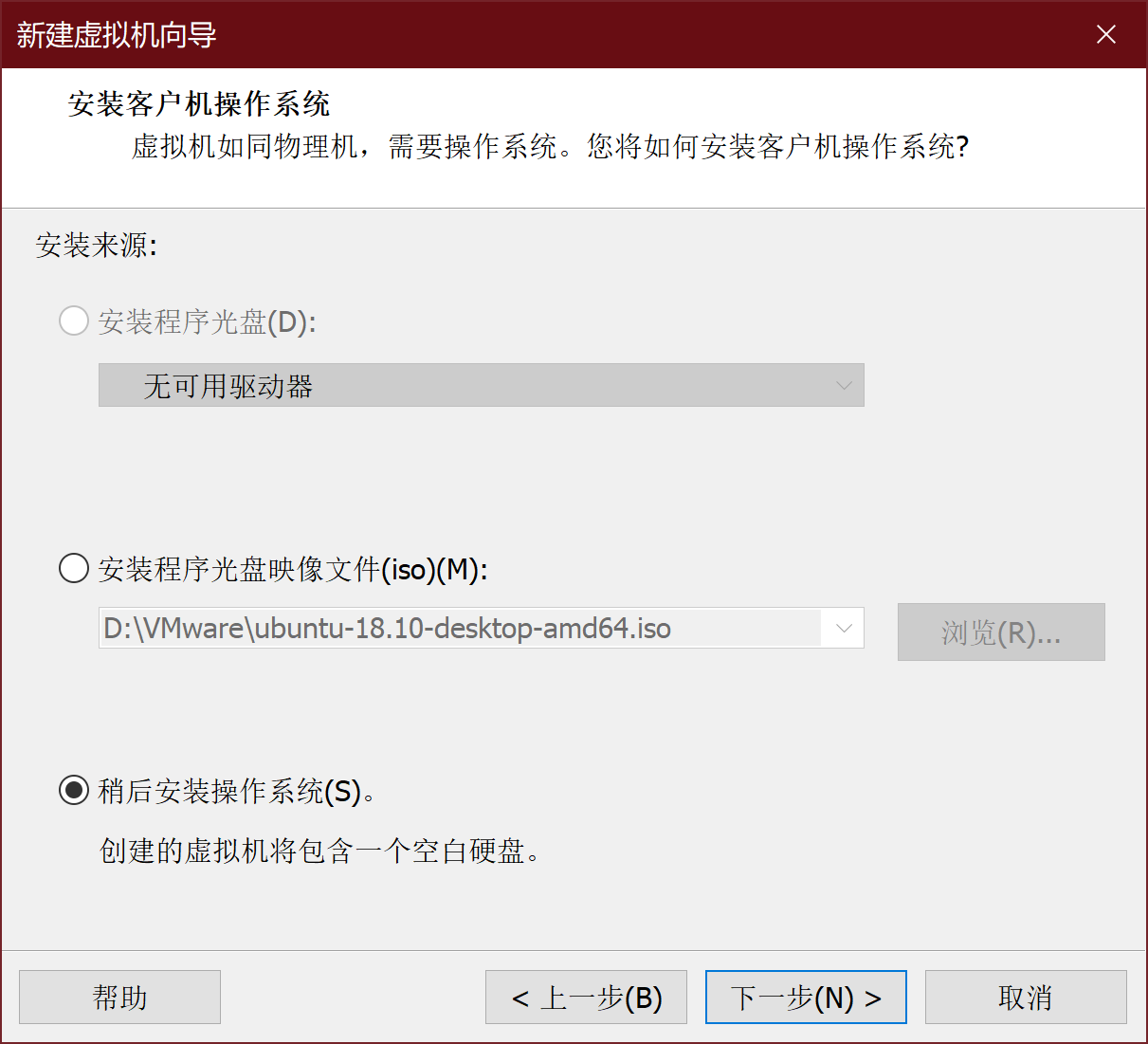
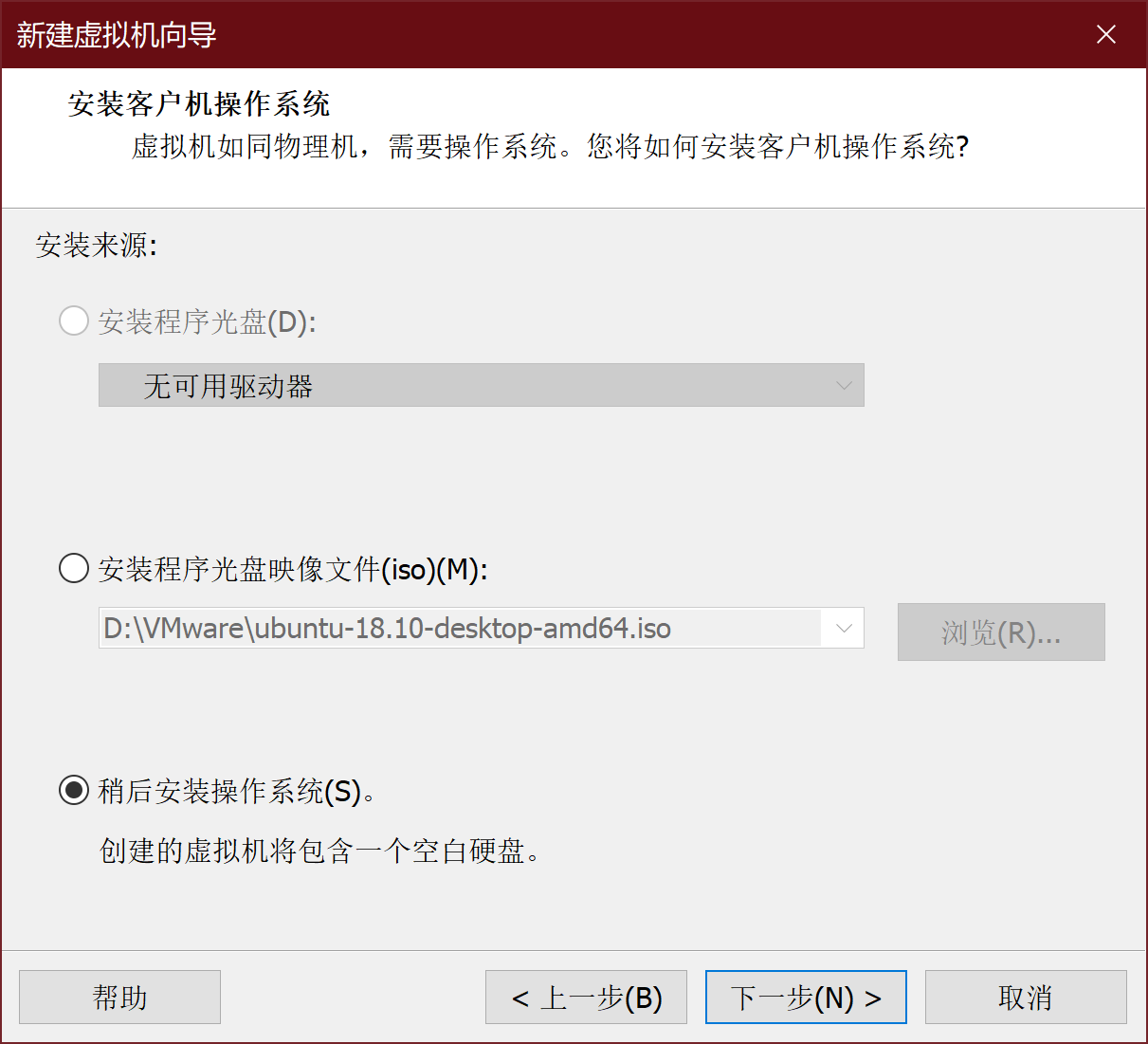
稍后安装操作系统
-
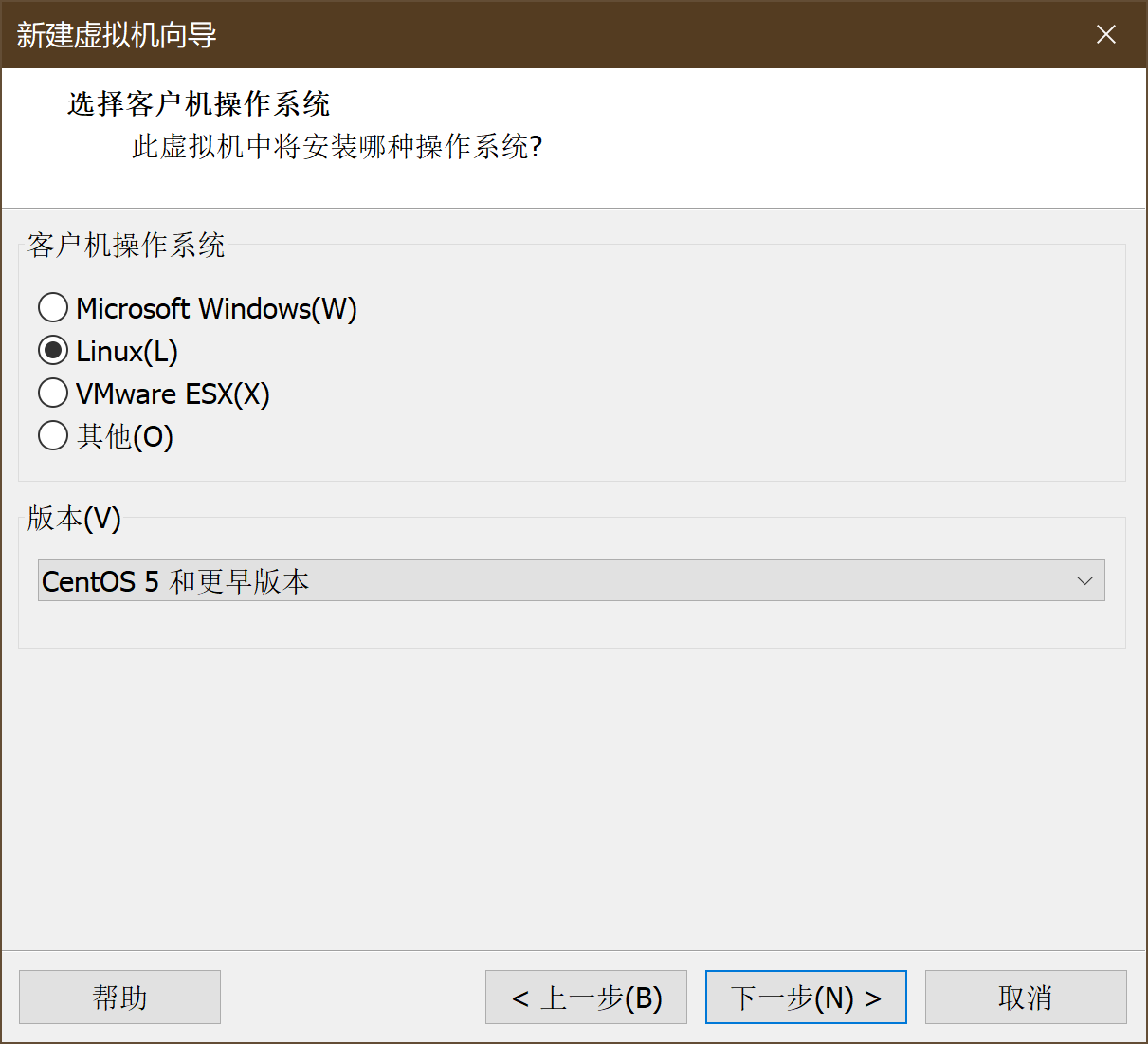
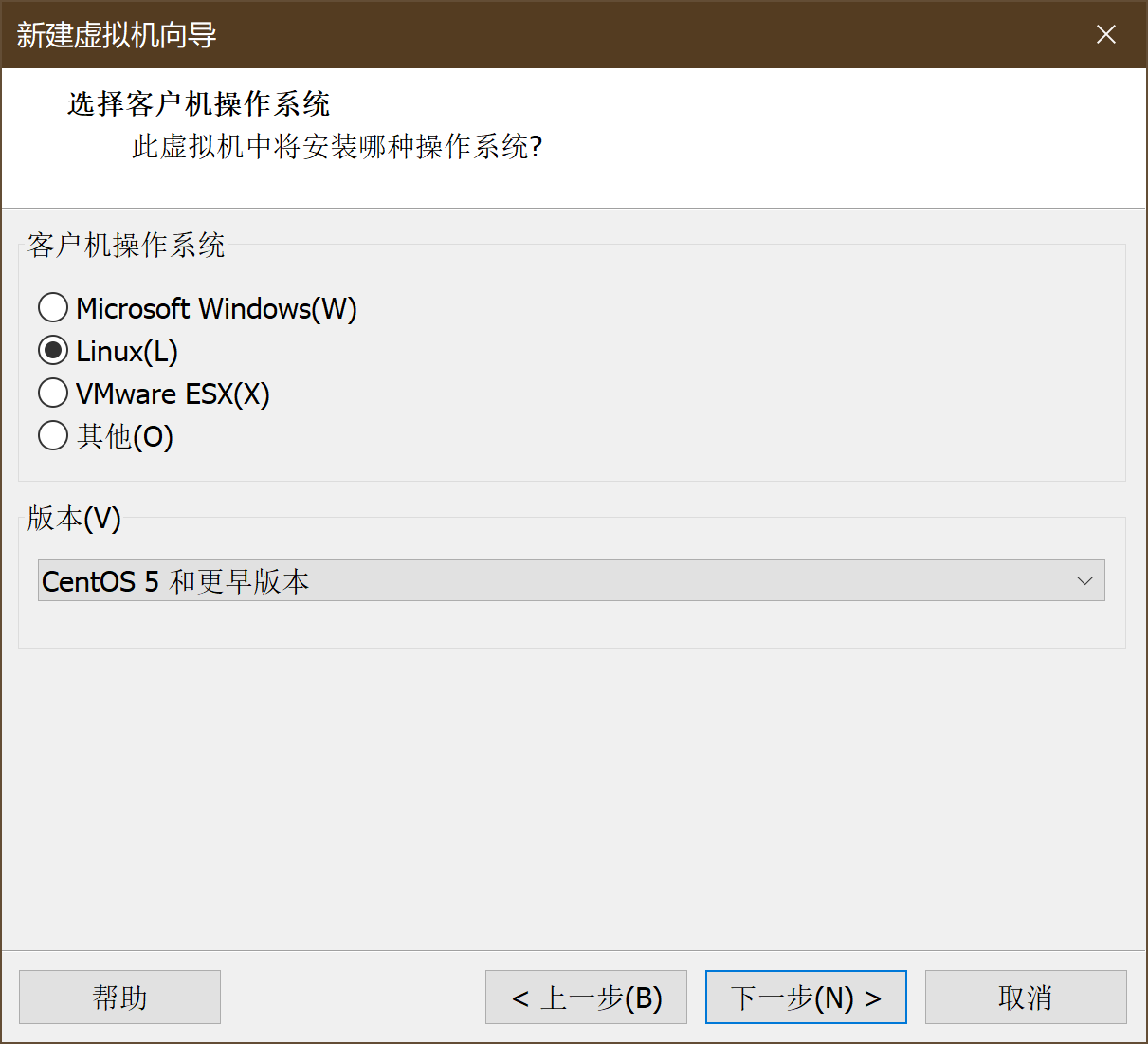
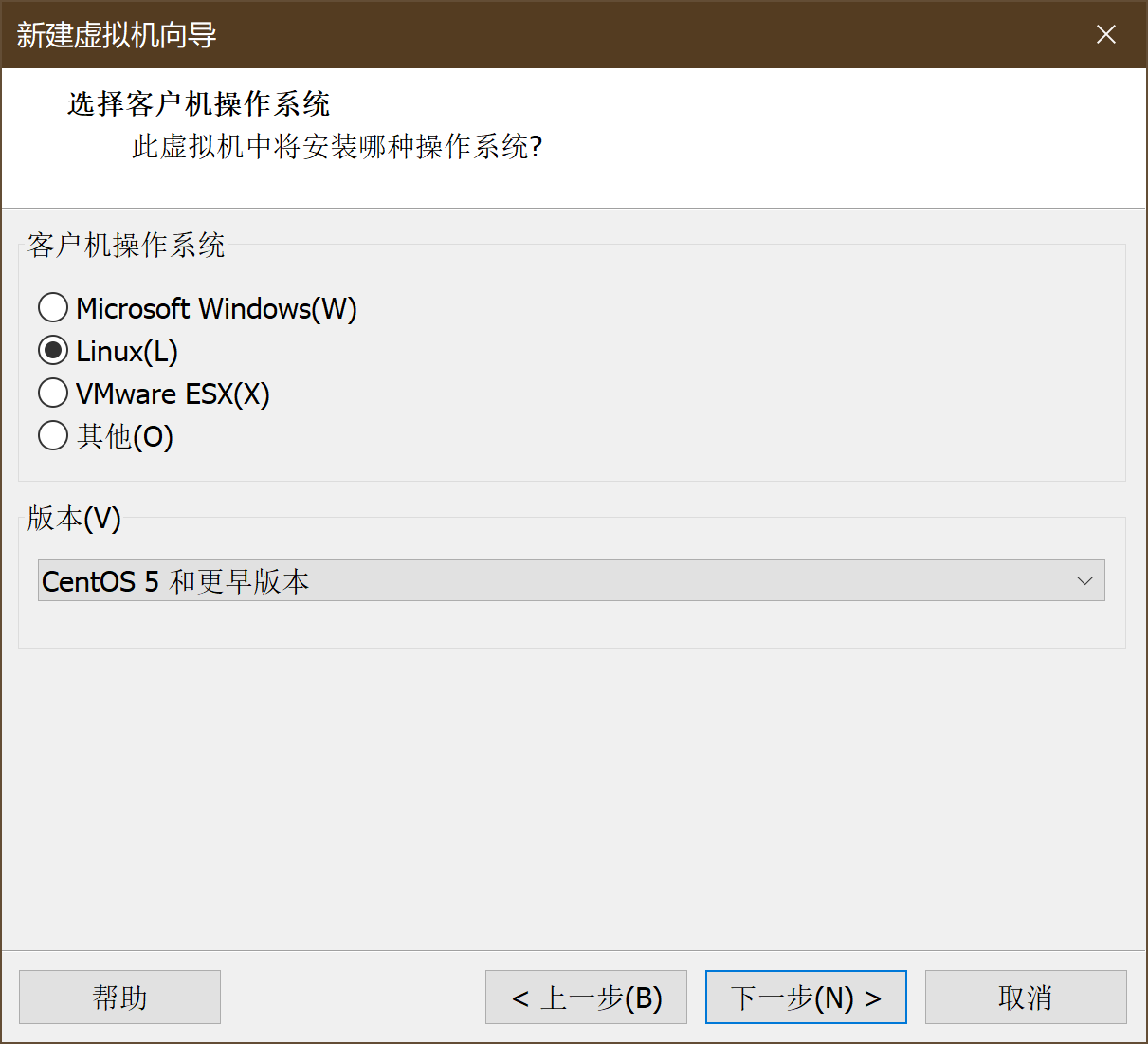
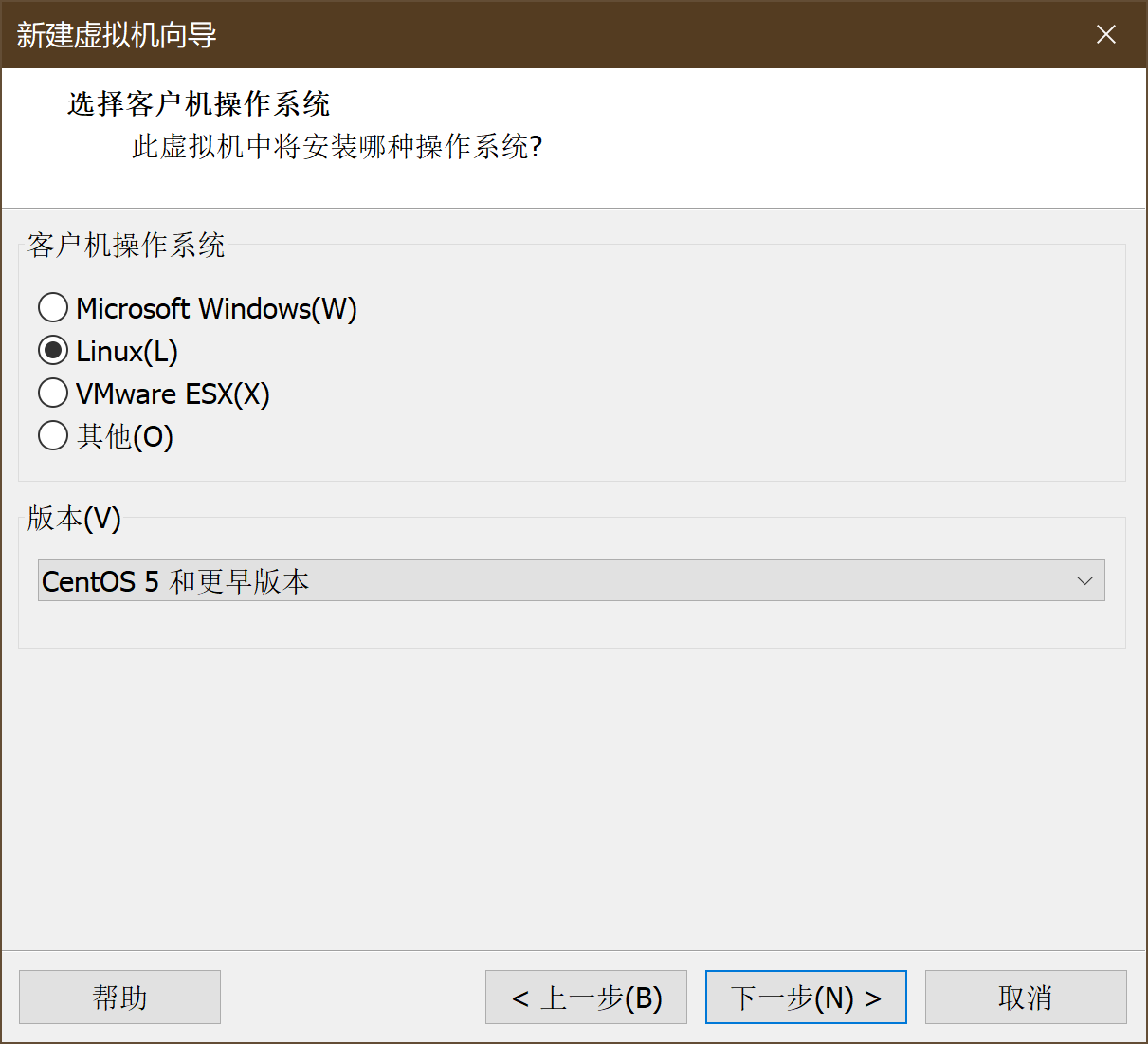
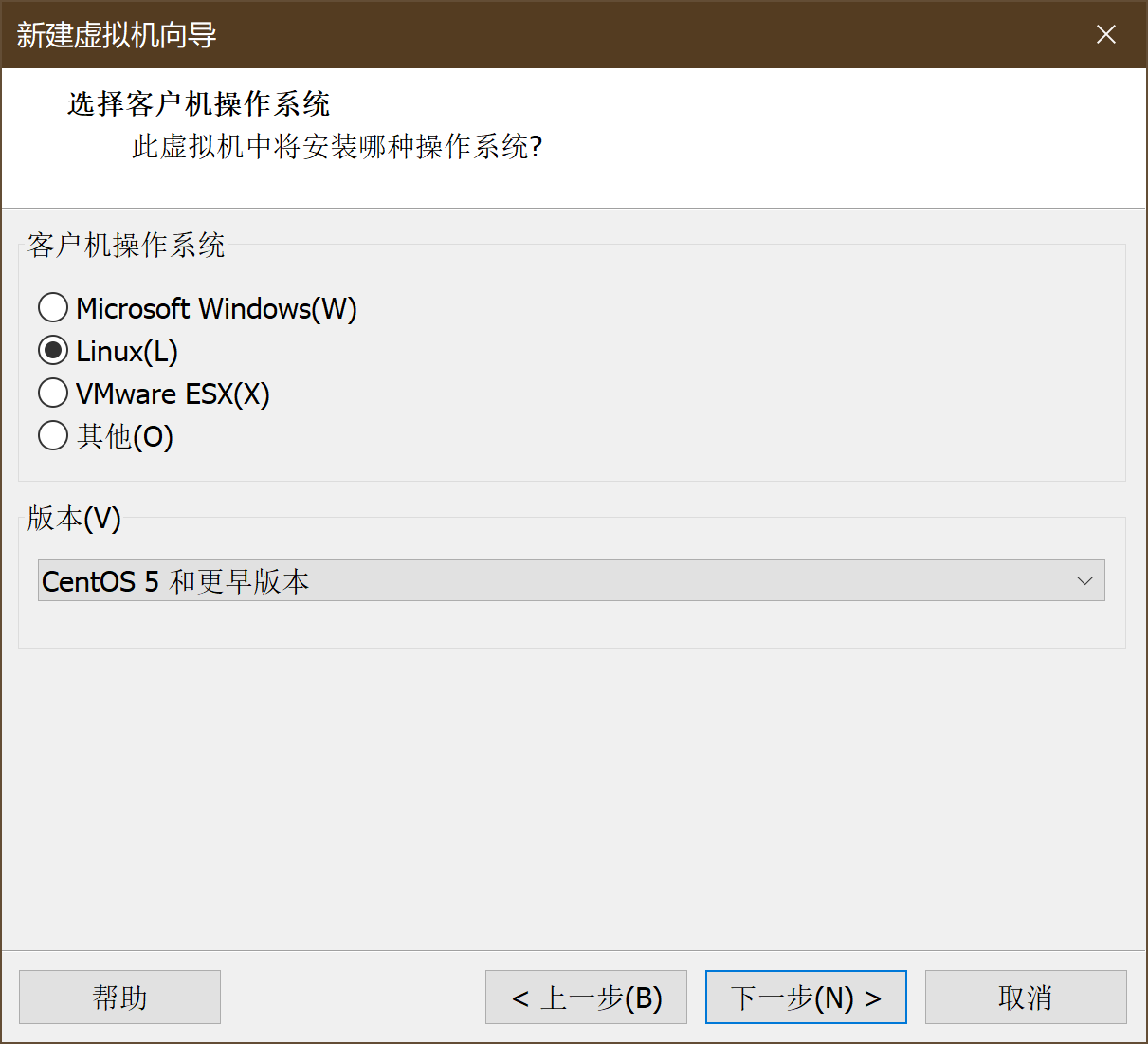
选择操作系统->编辑名称->下一步
-
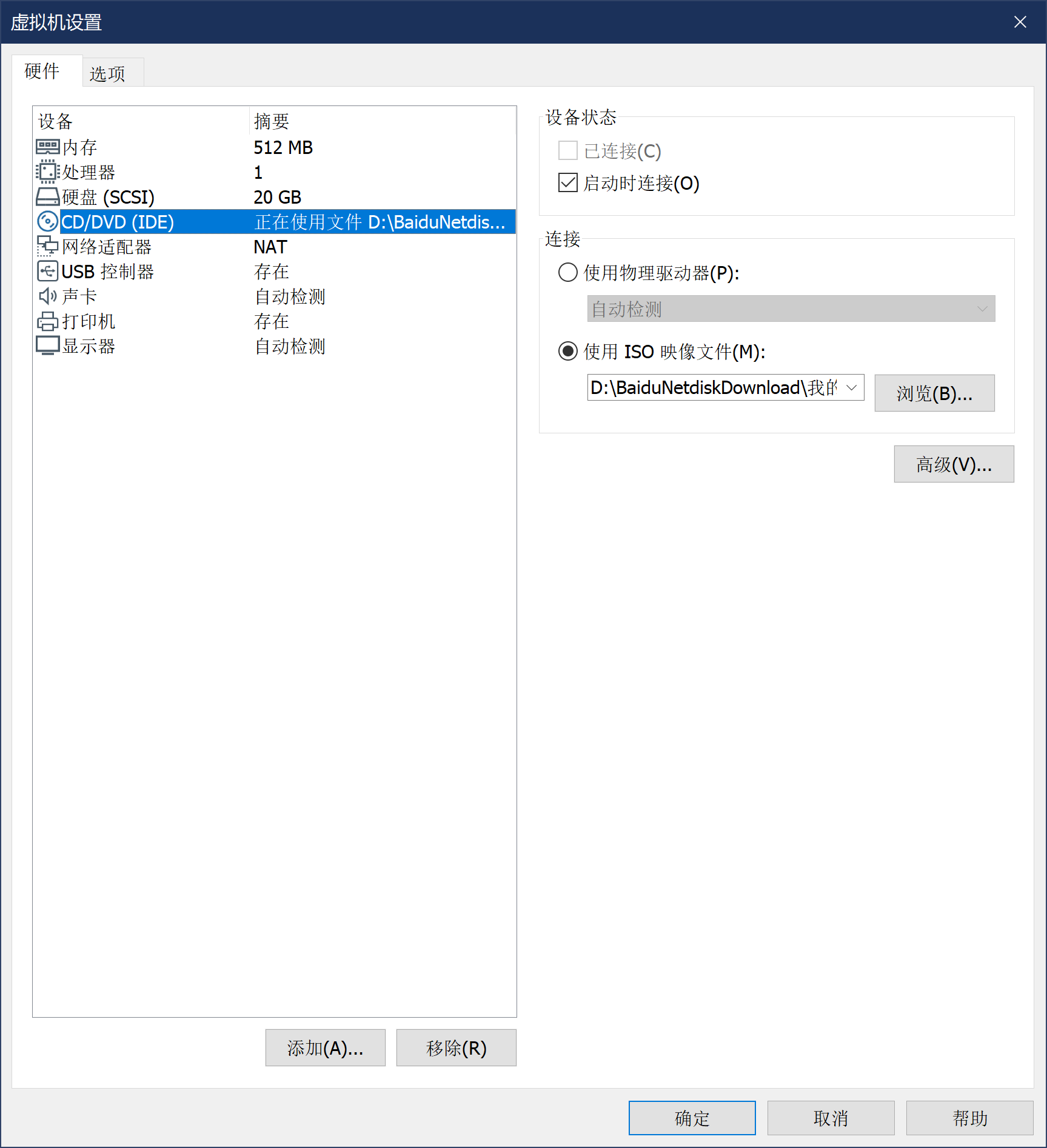
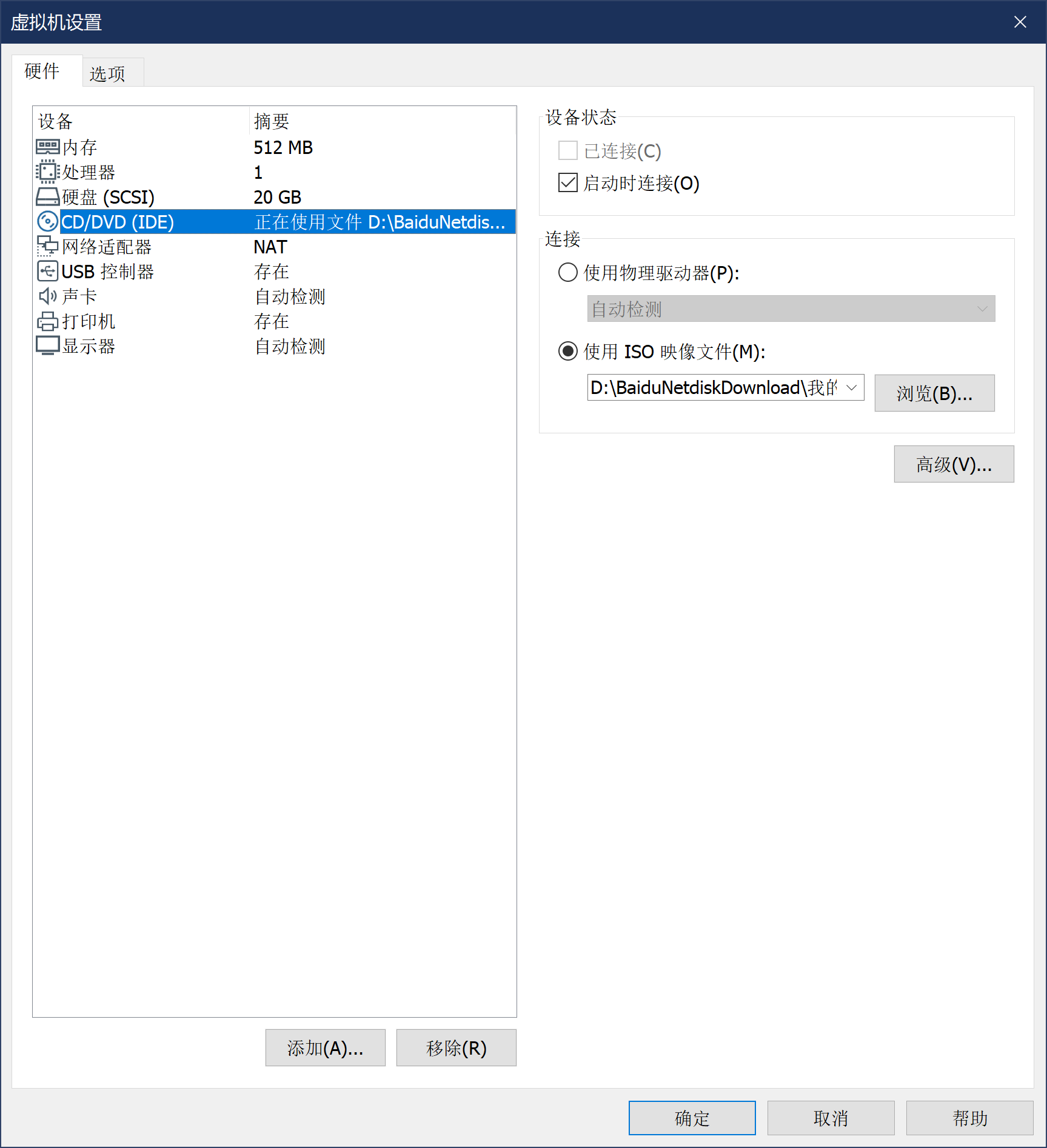
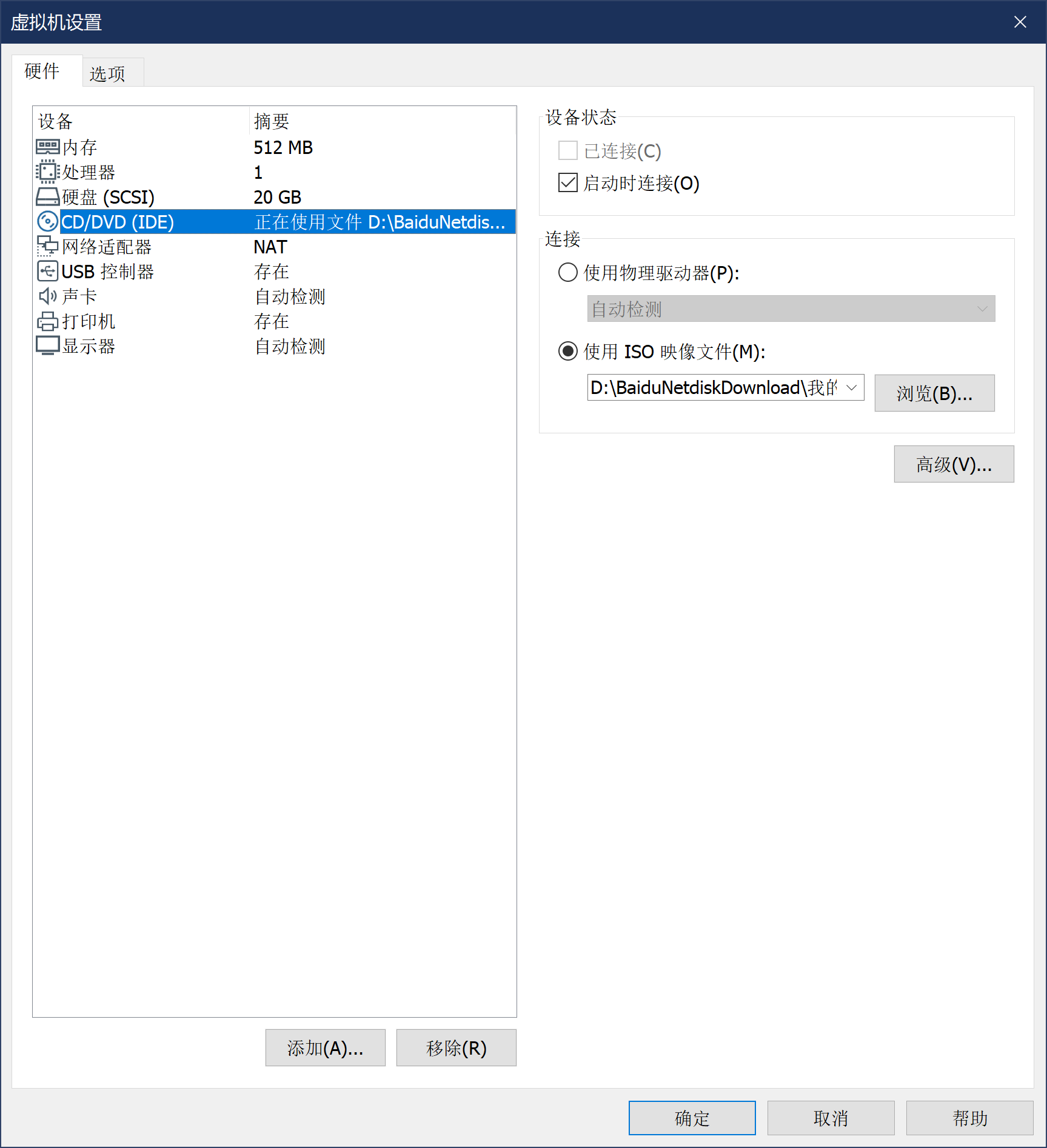
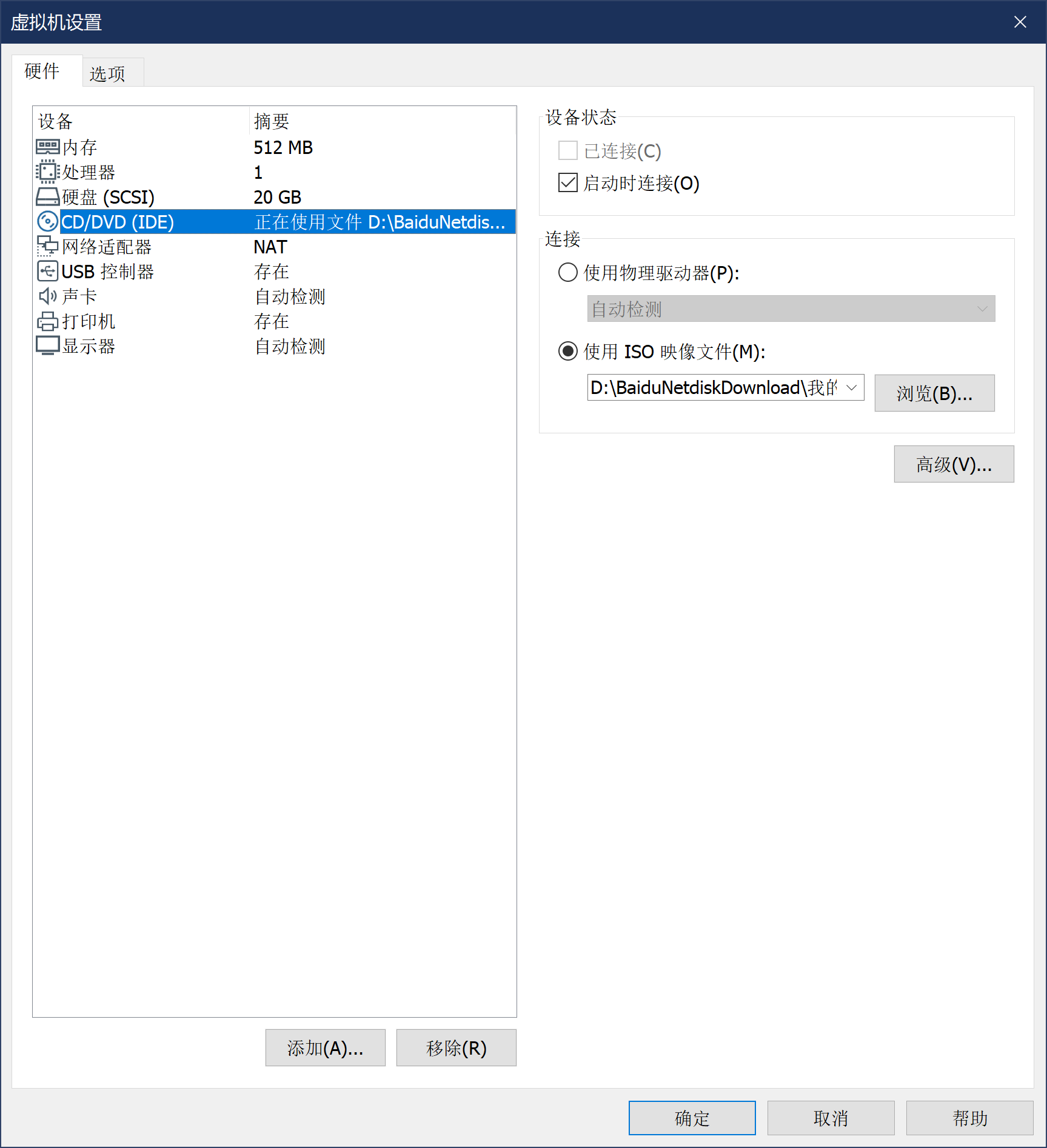
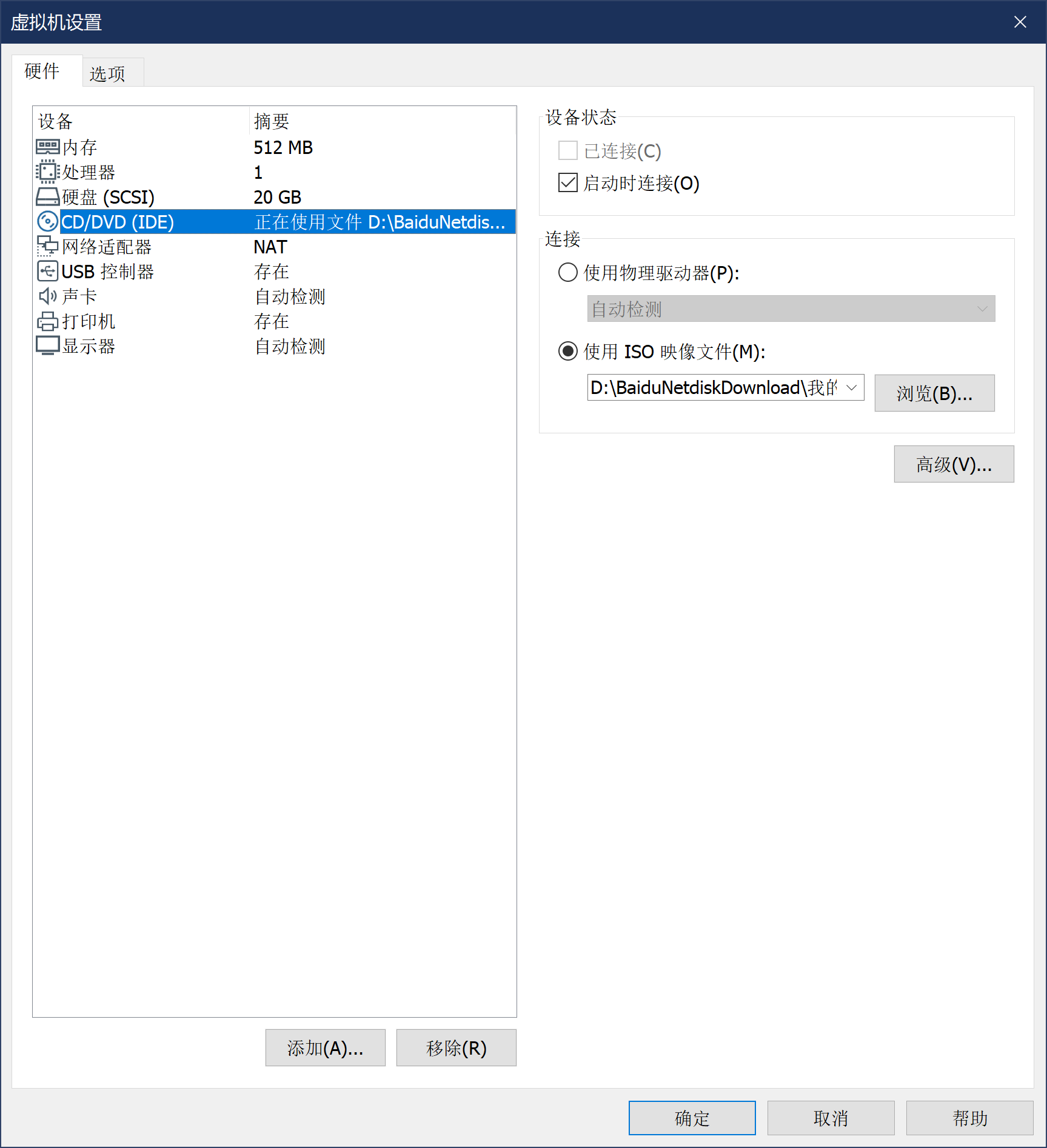
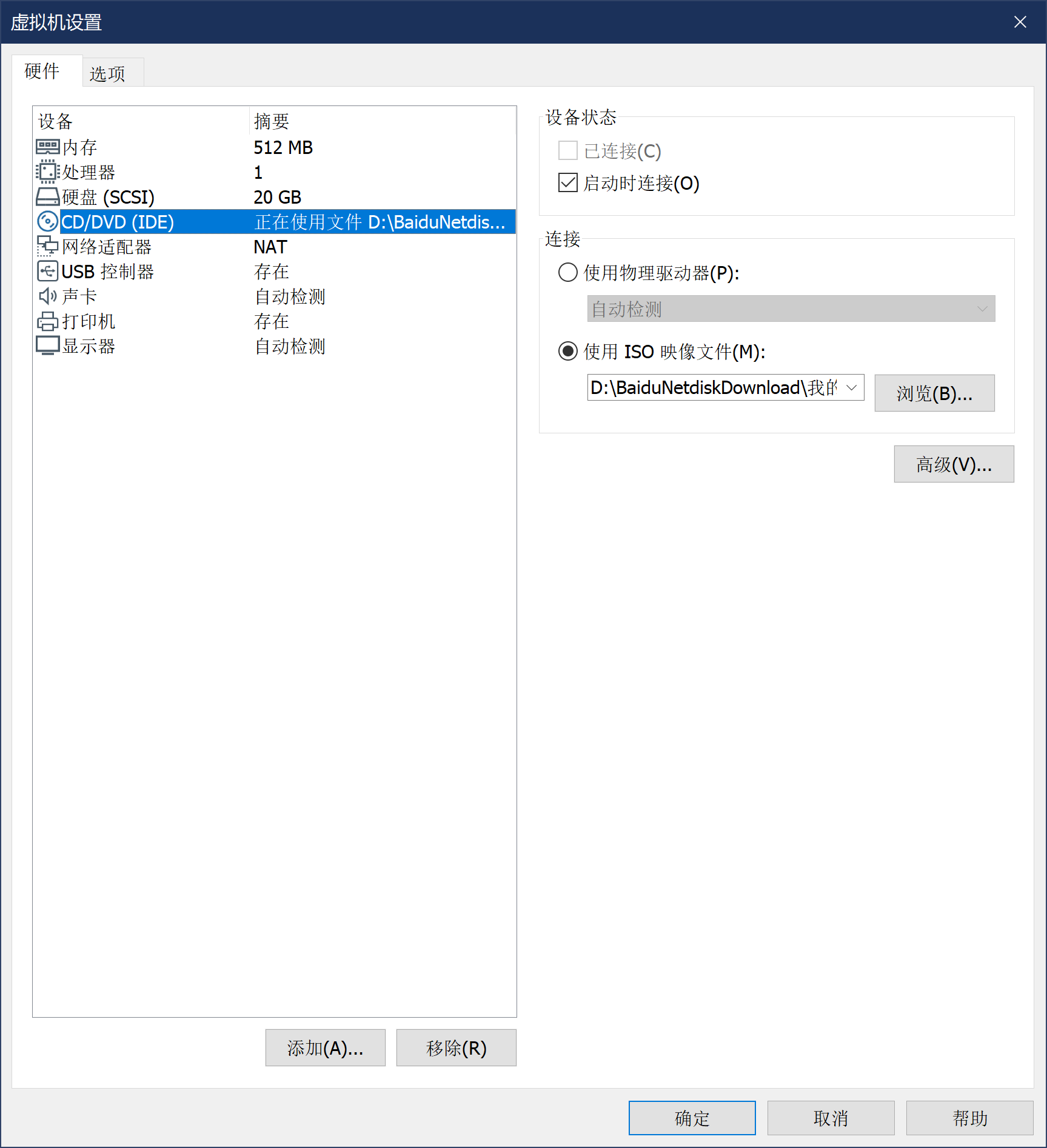
硬件设置->添加镜像
-
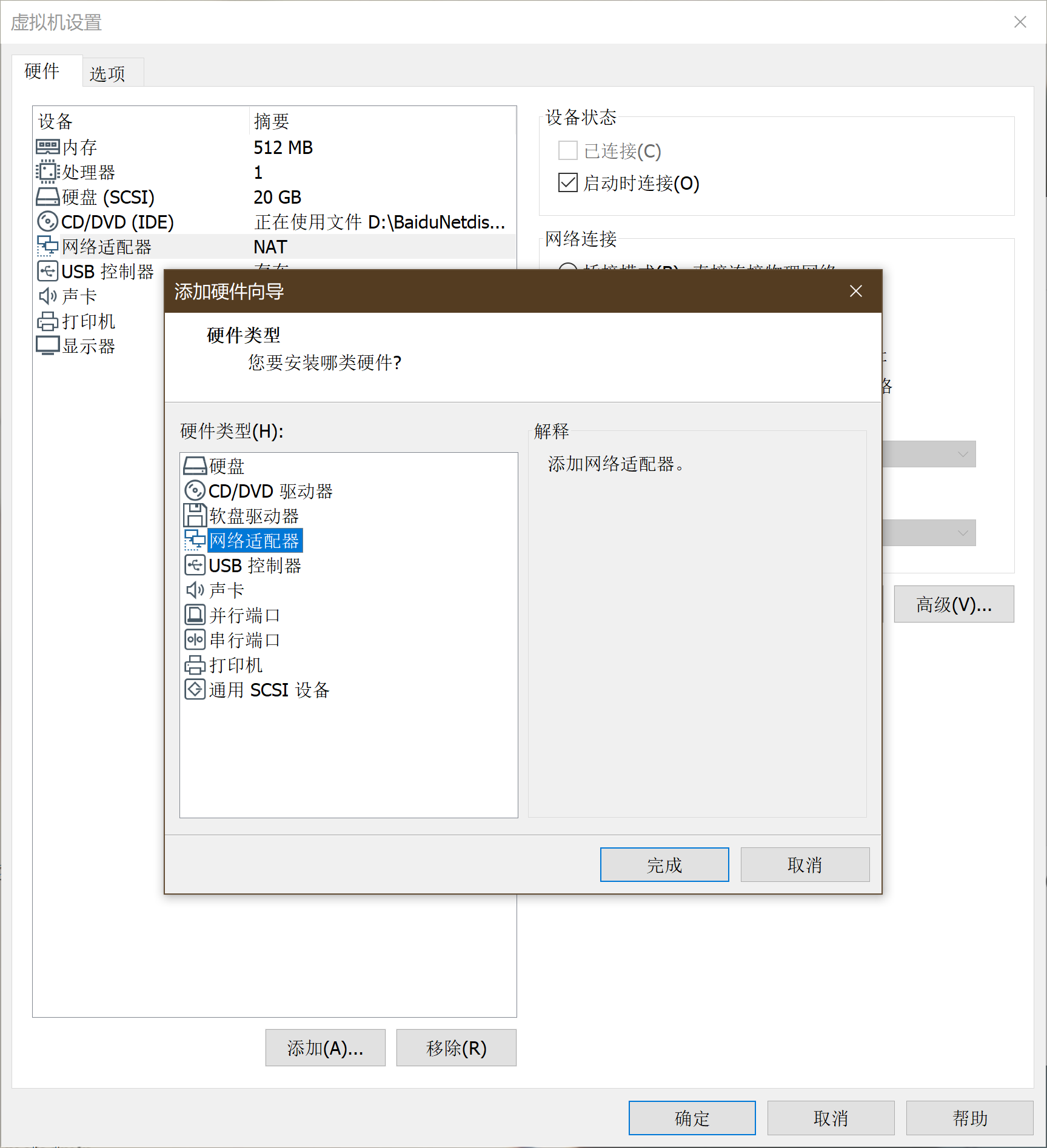
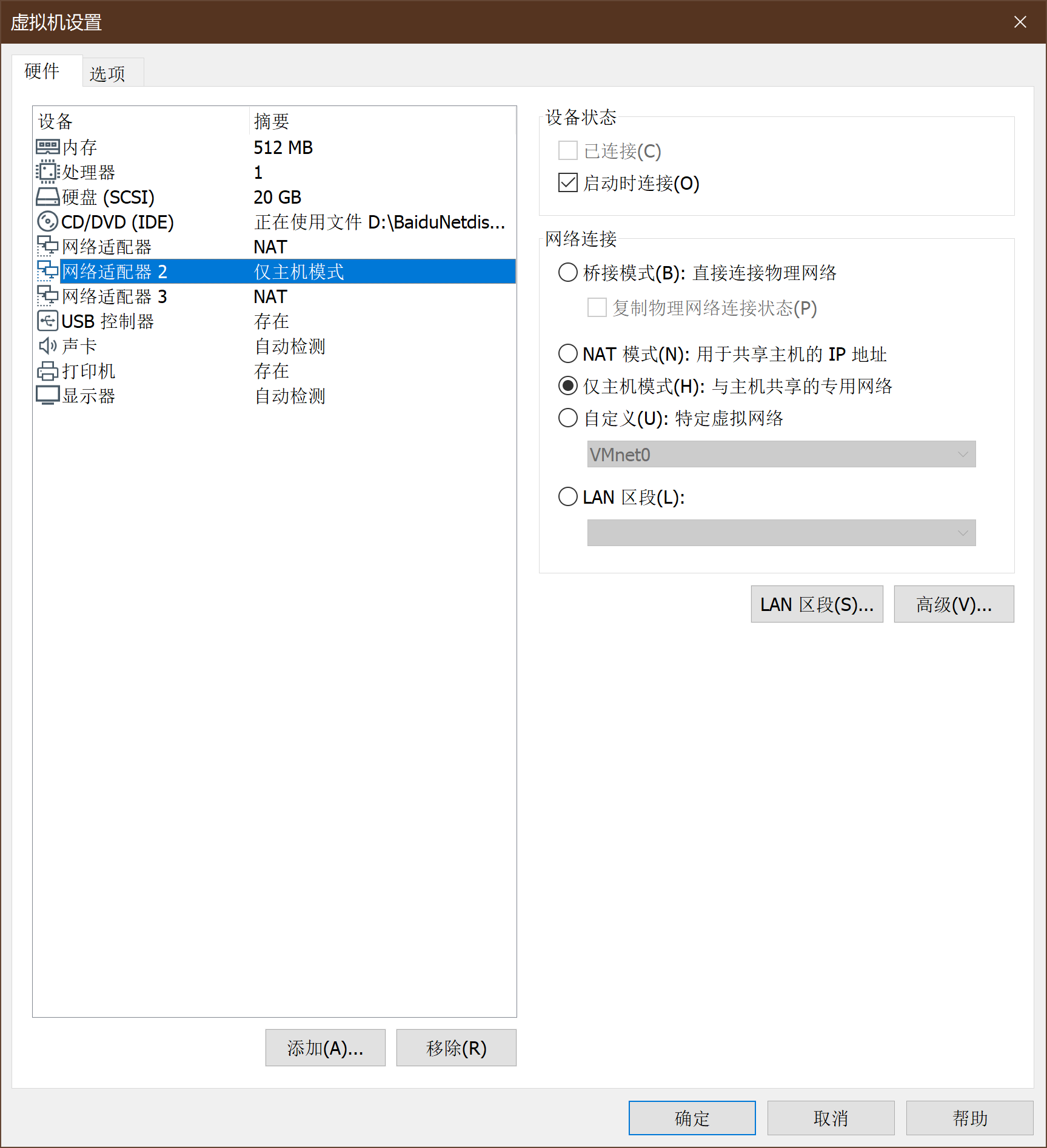
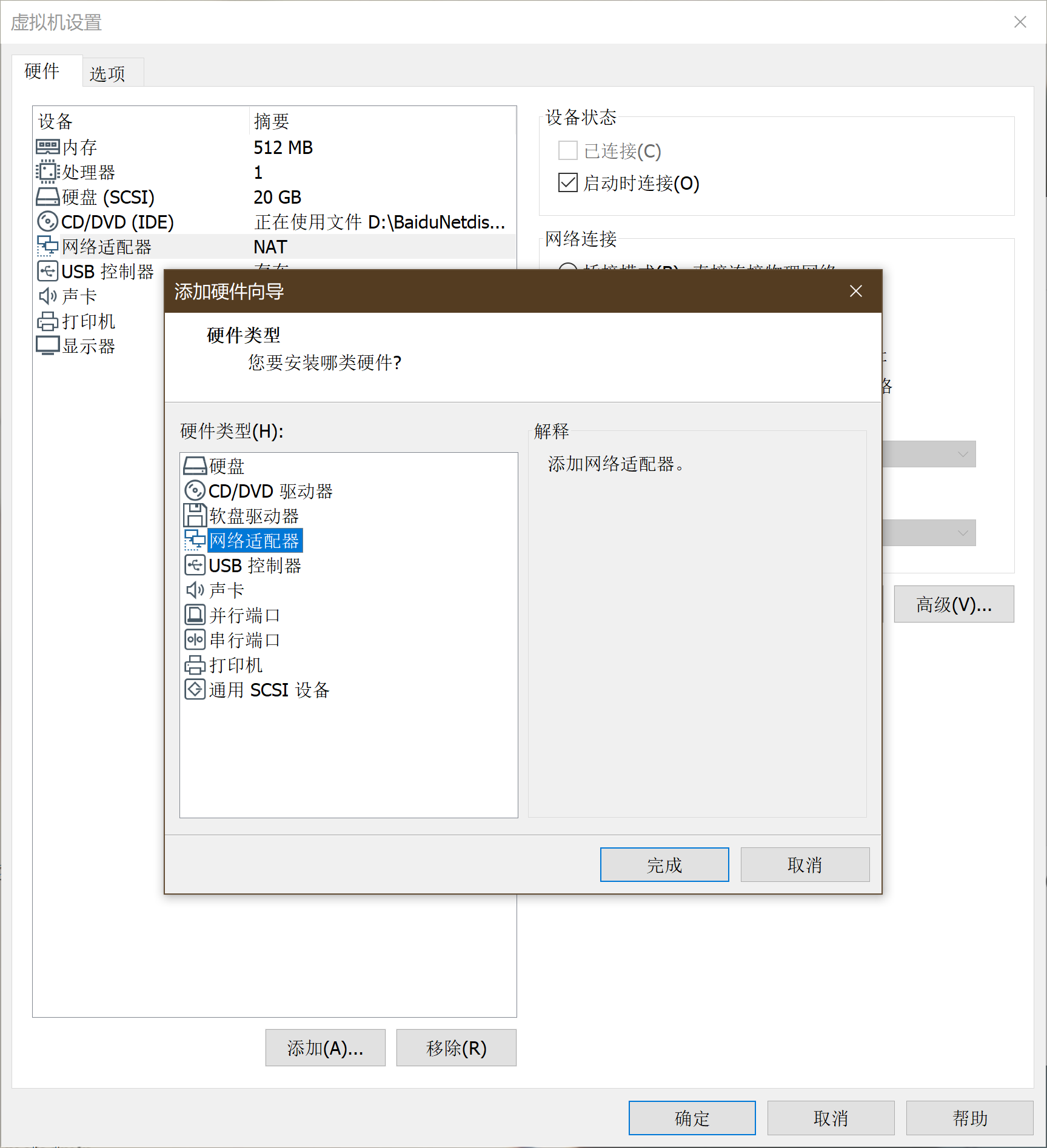
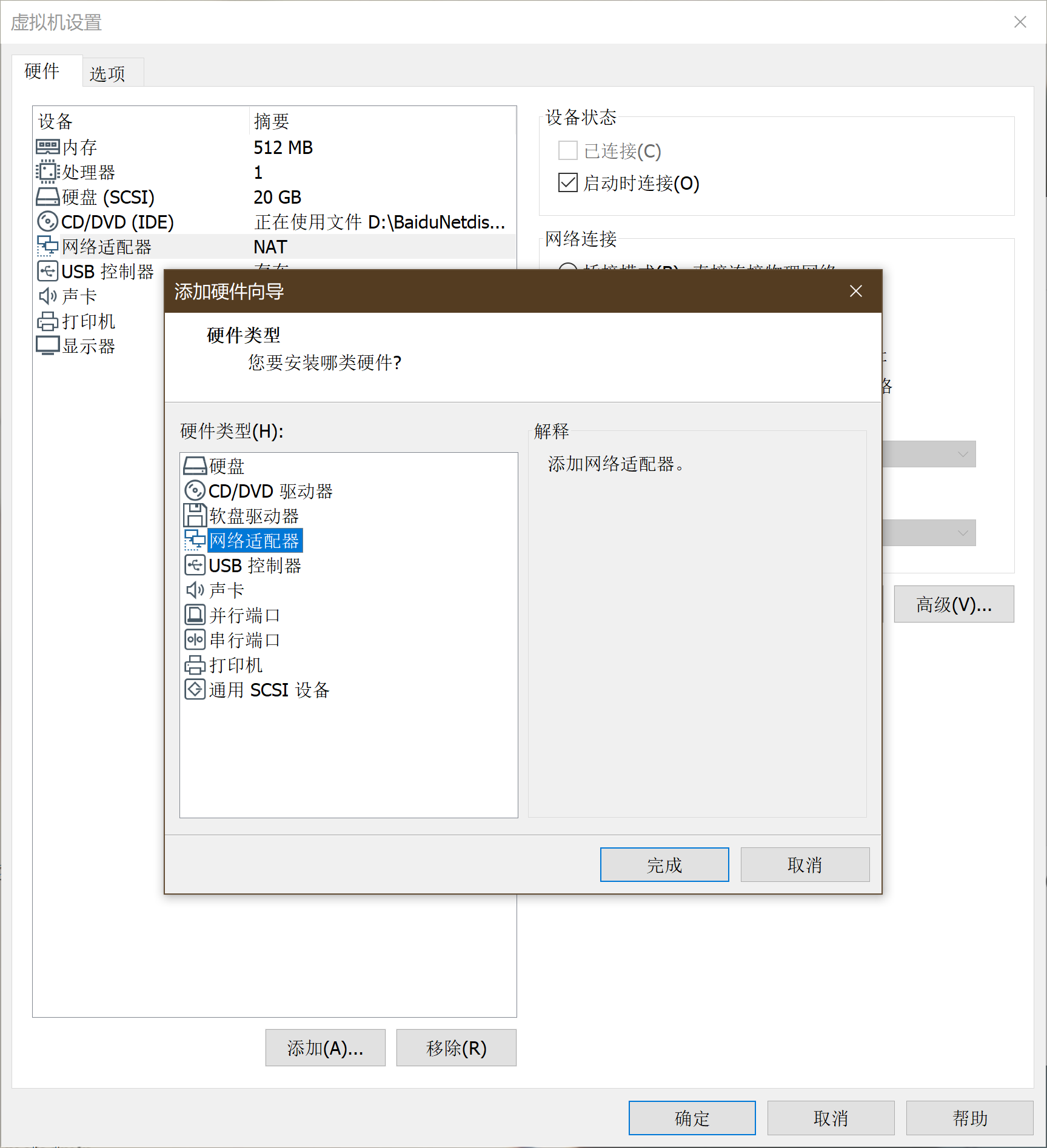
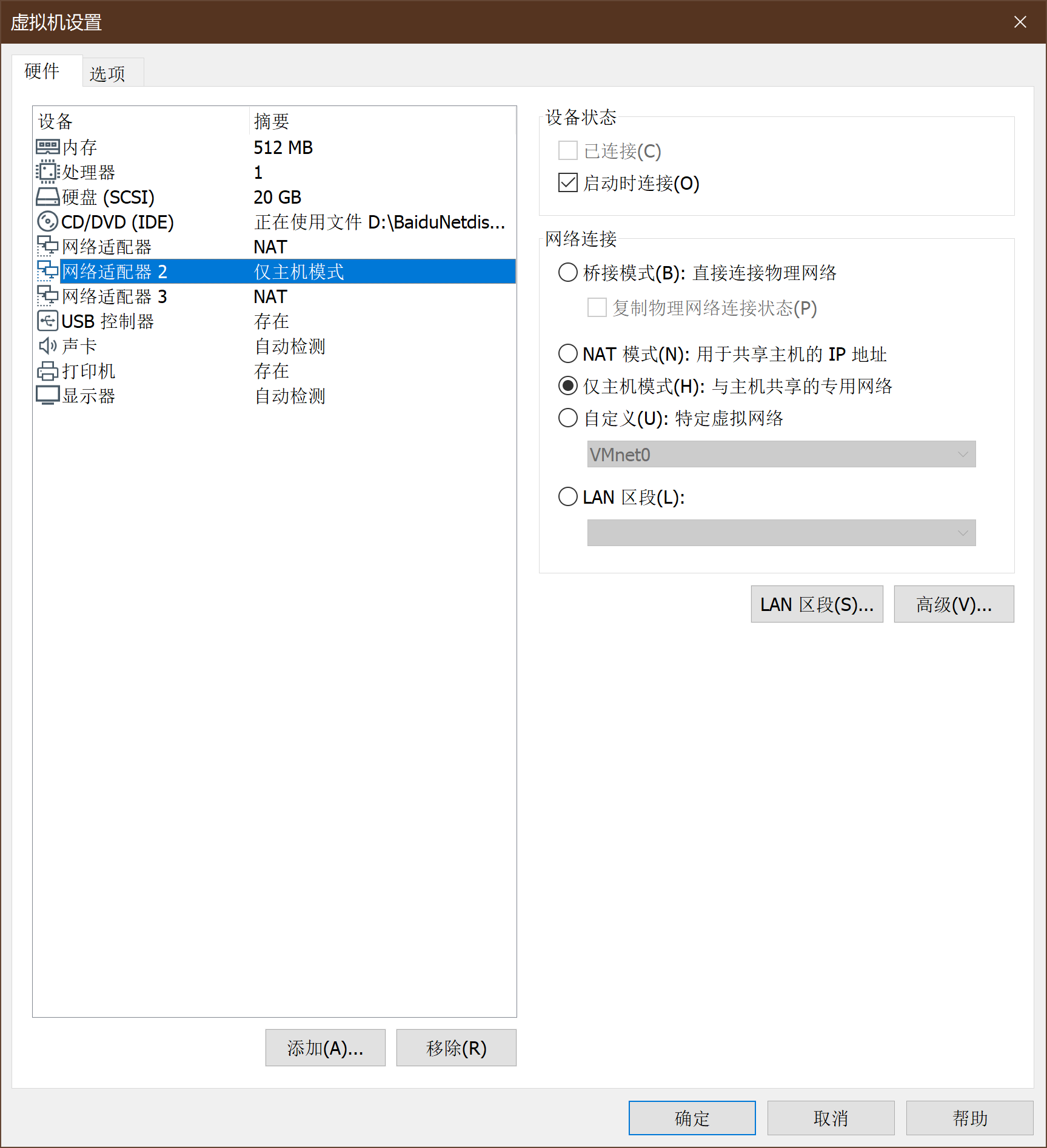
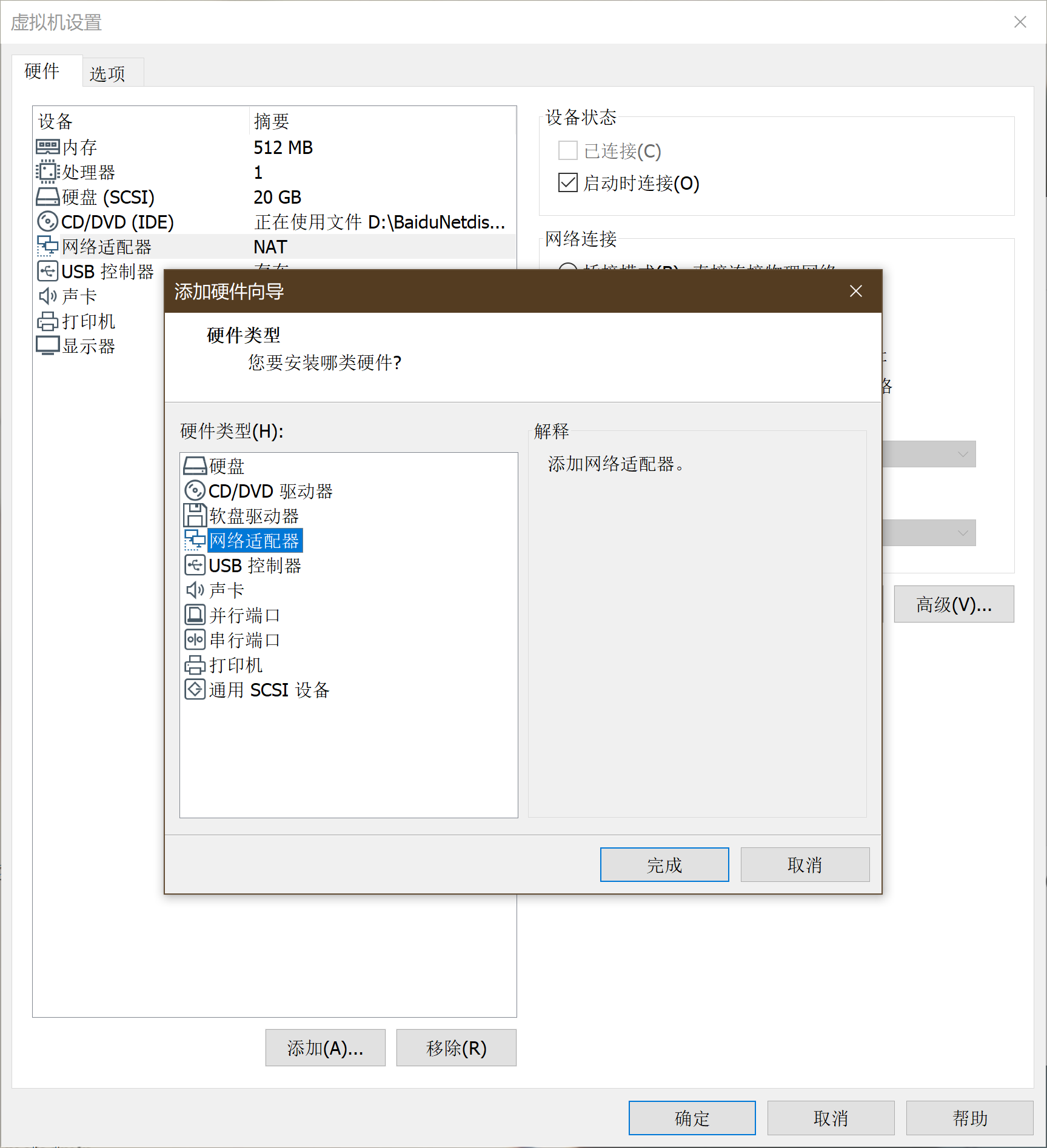
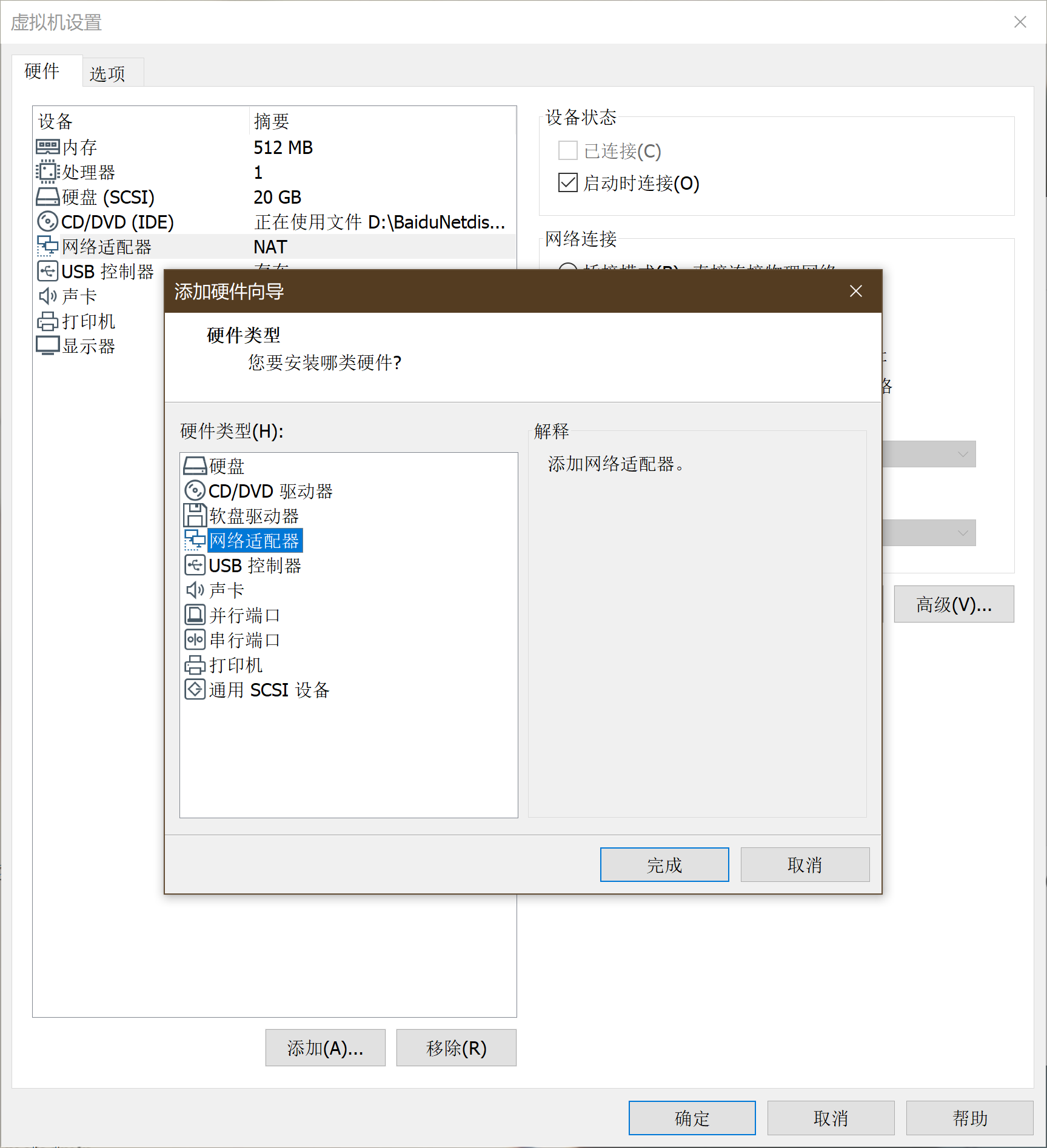
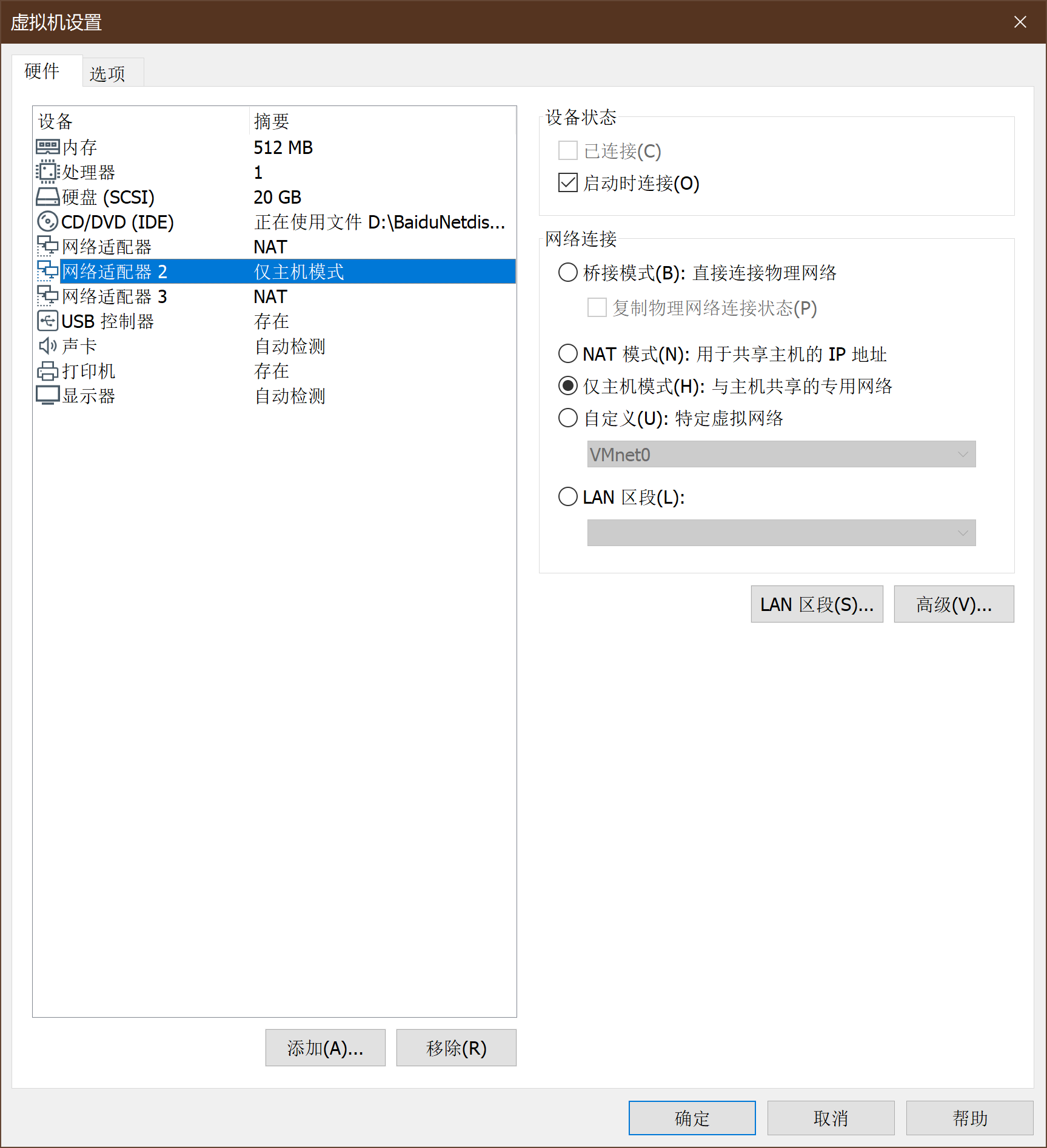
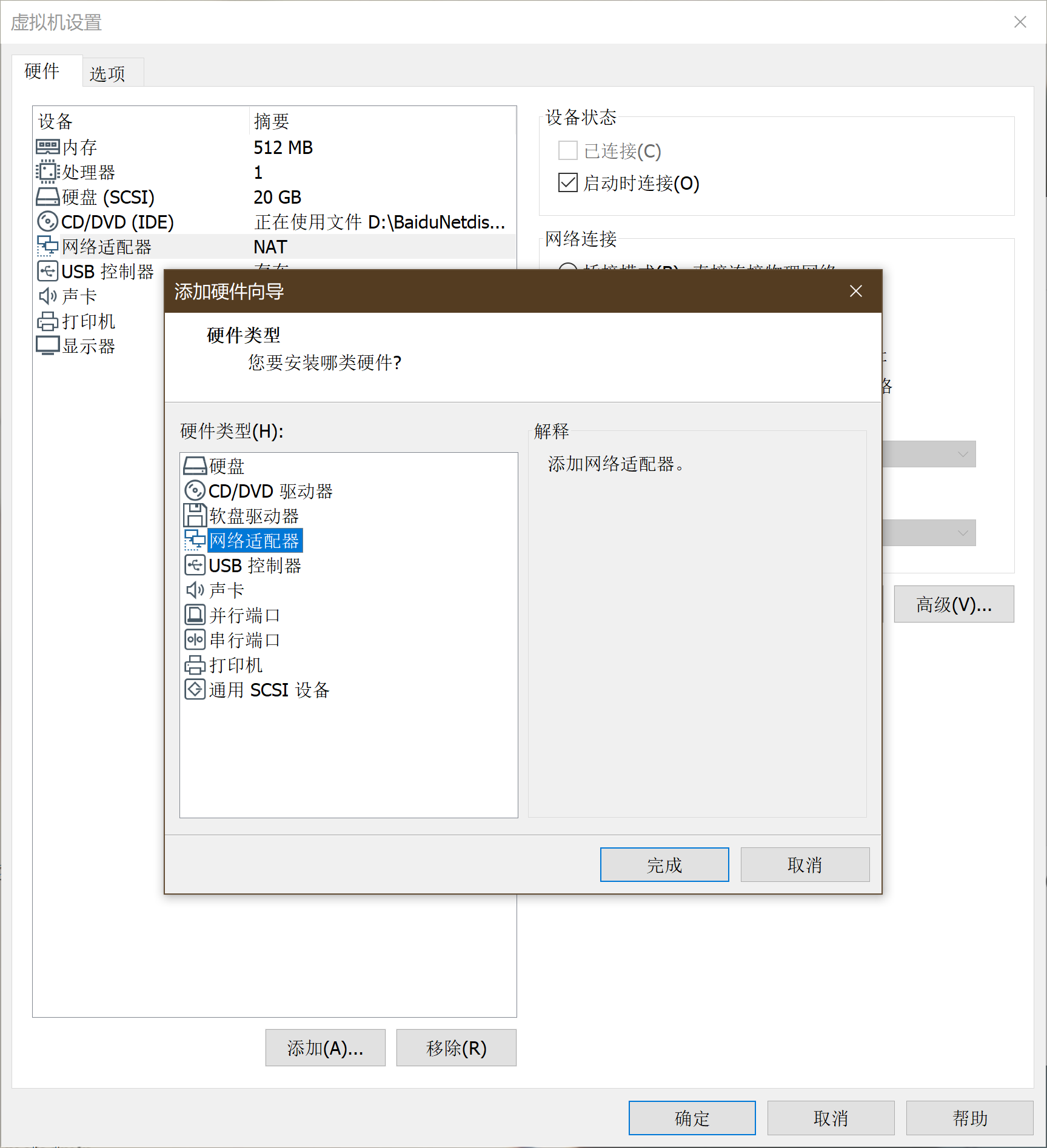
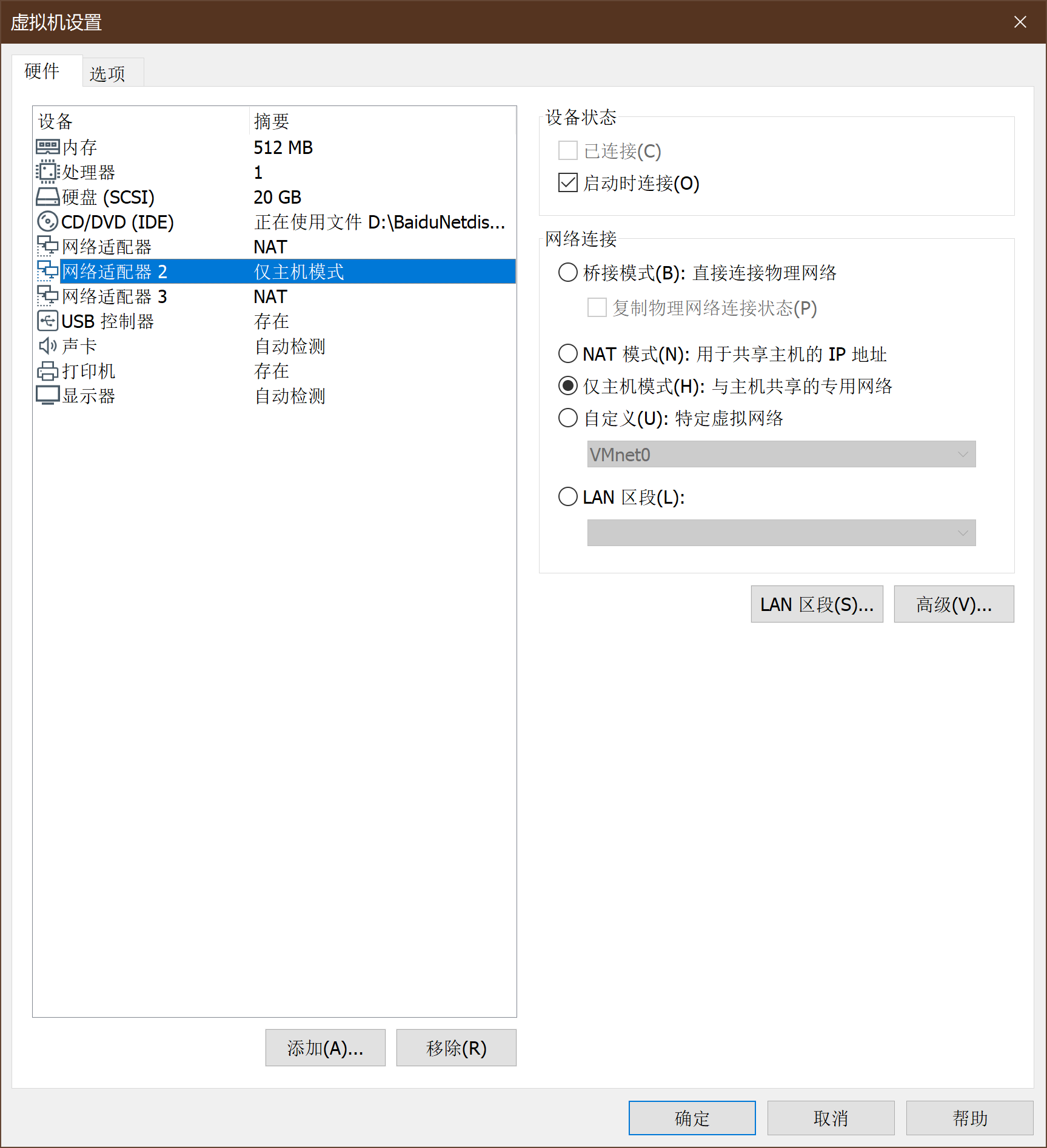
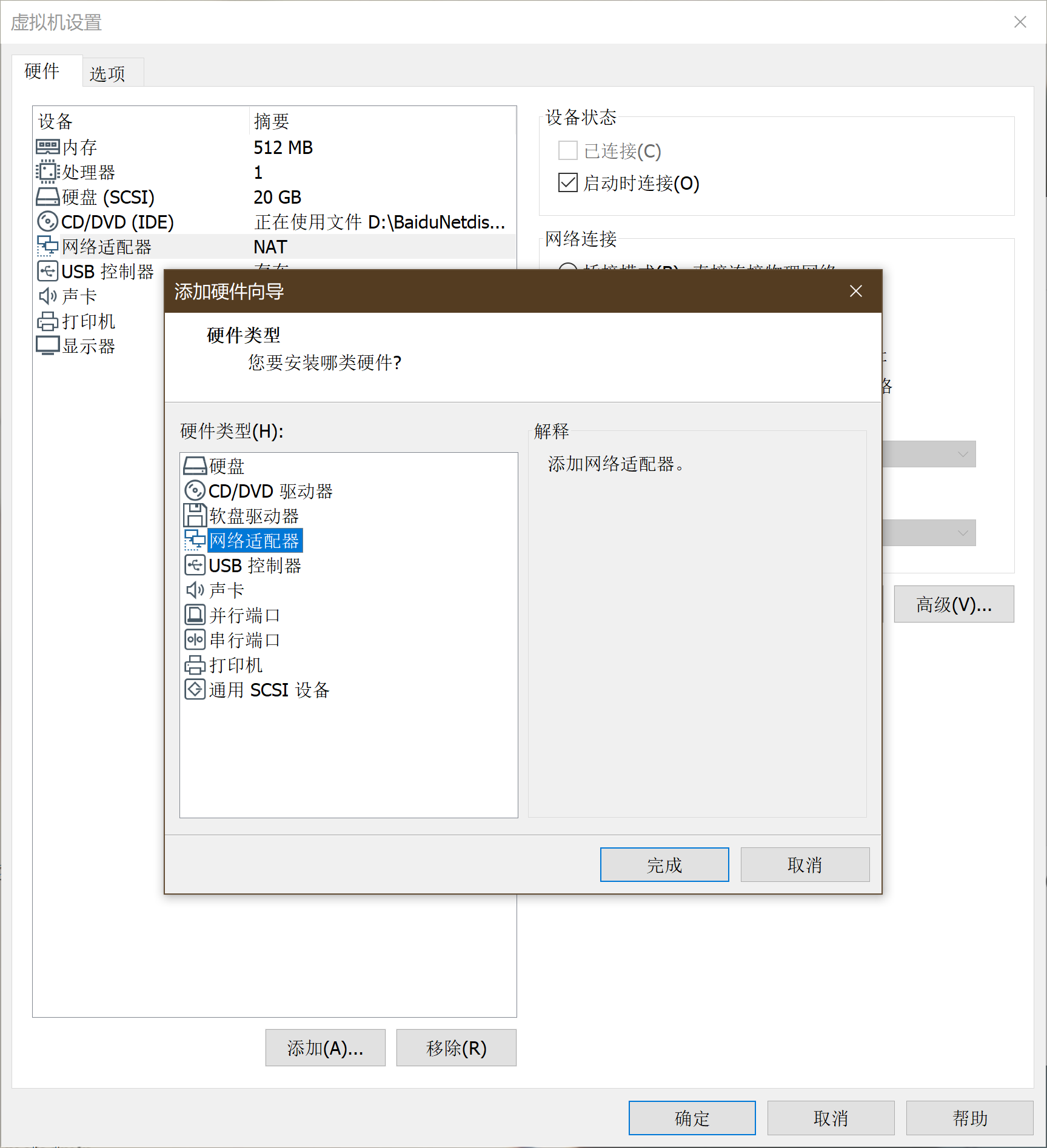
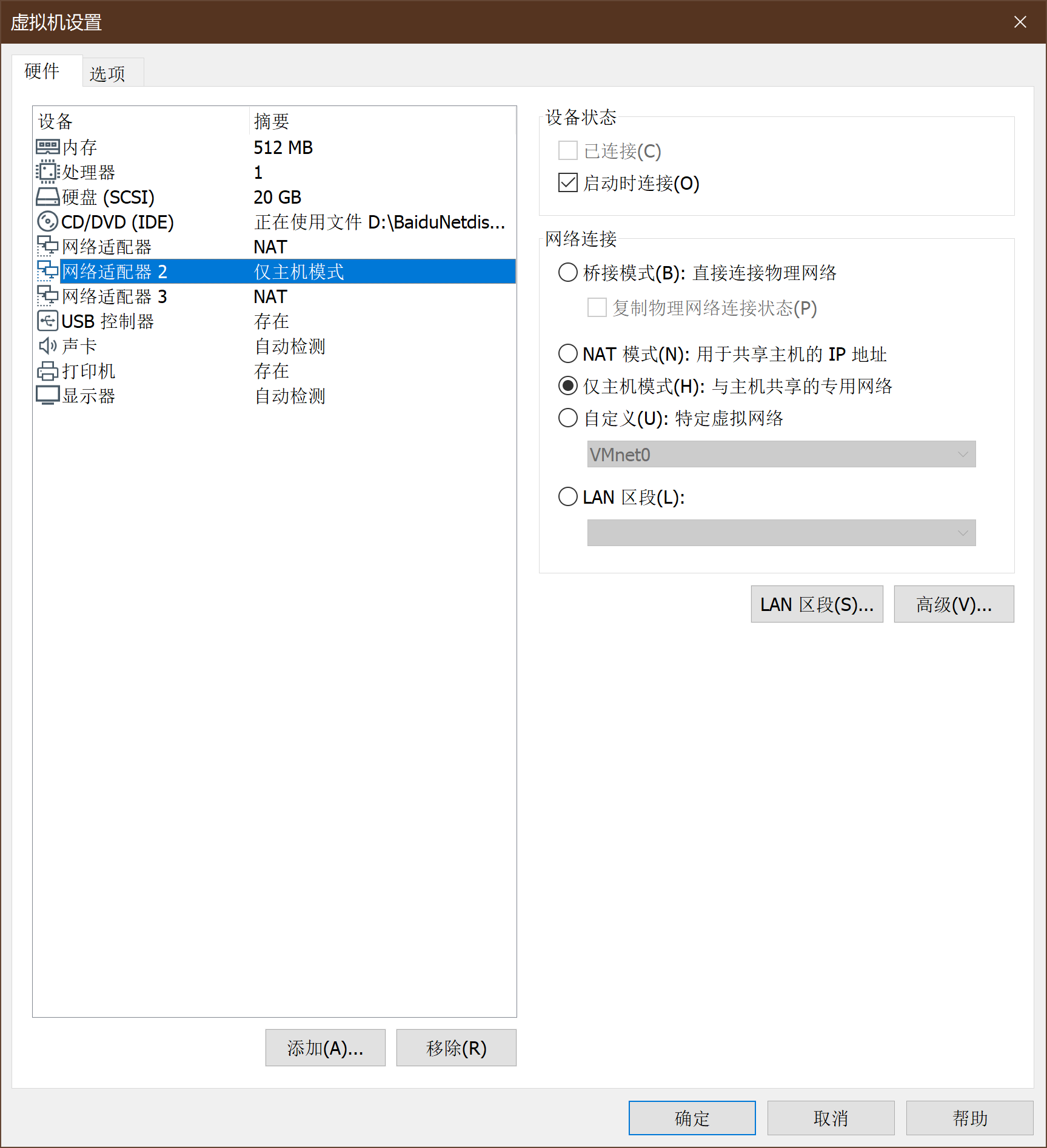
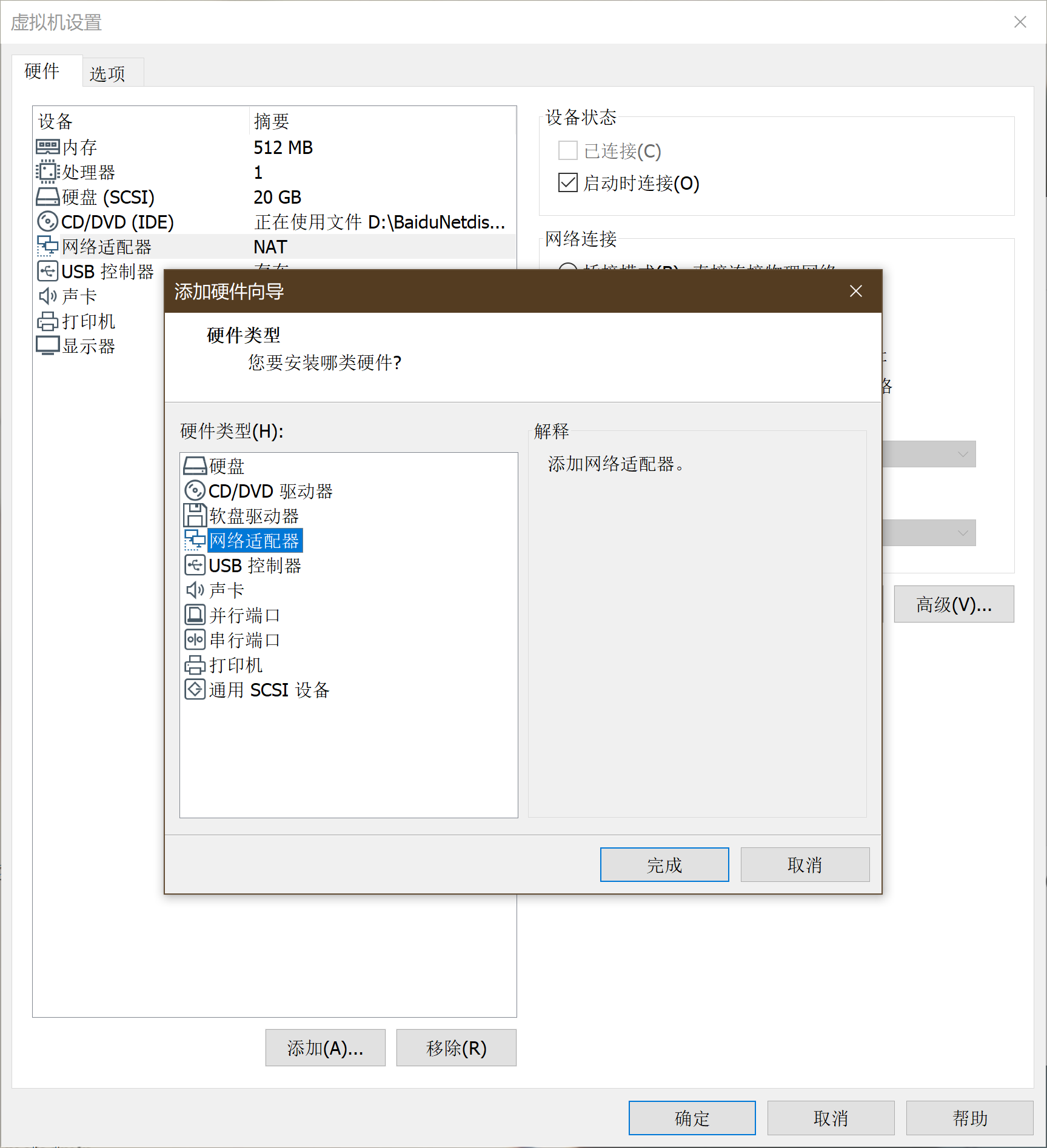
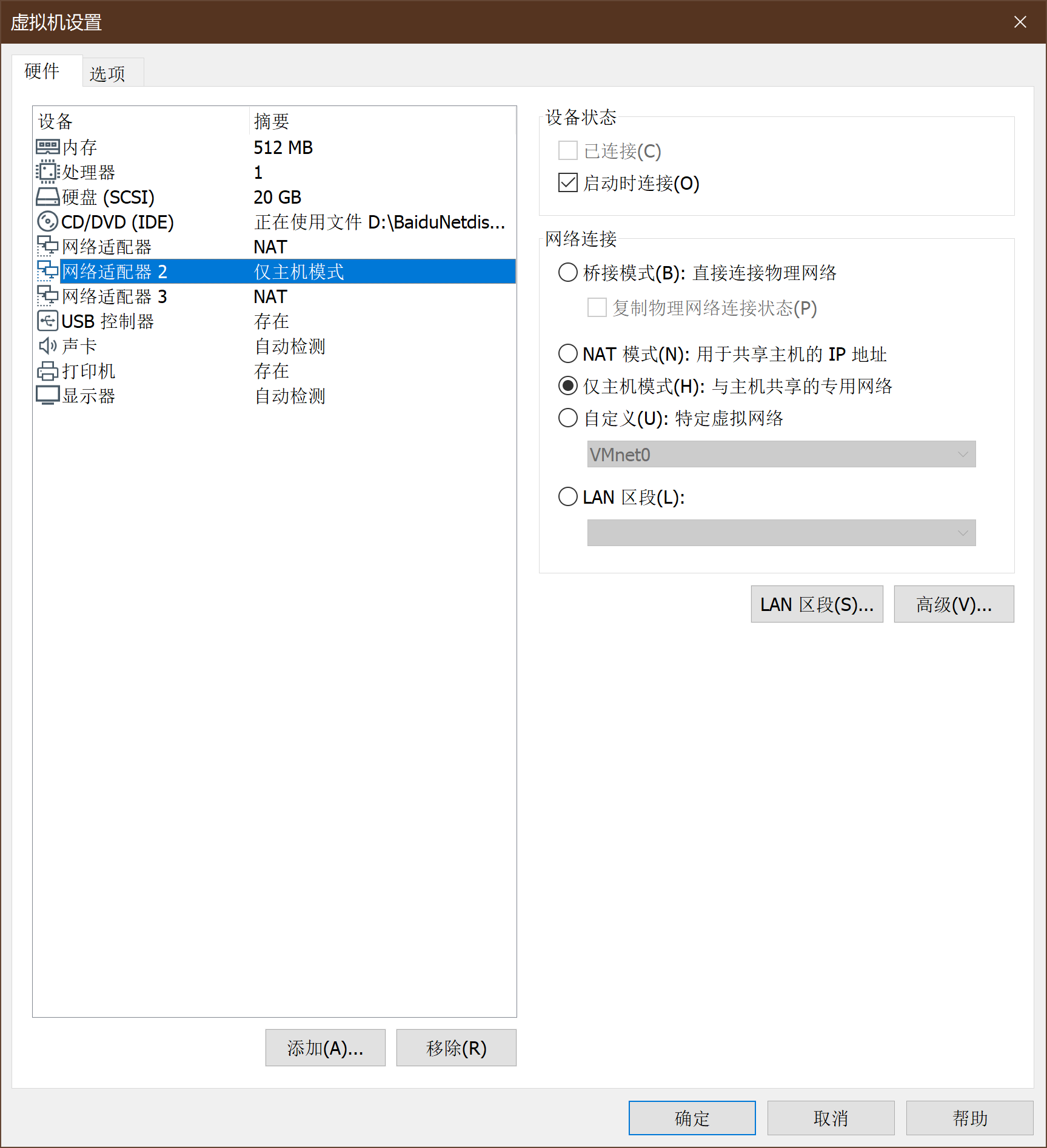
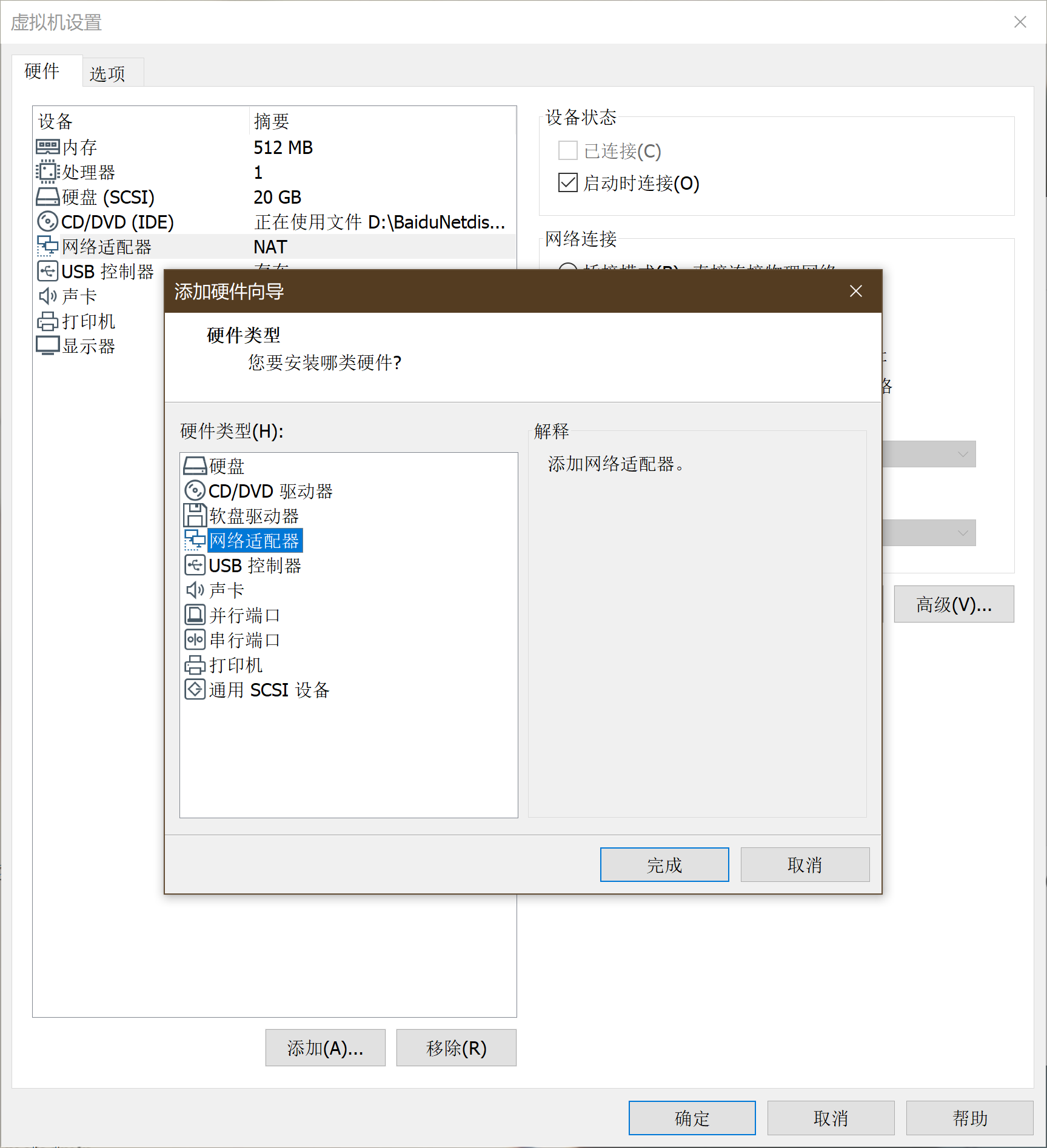
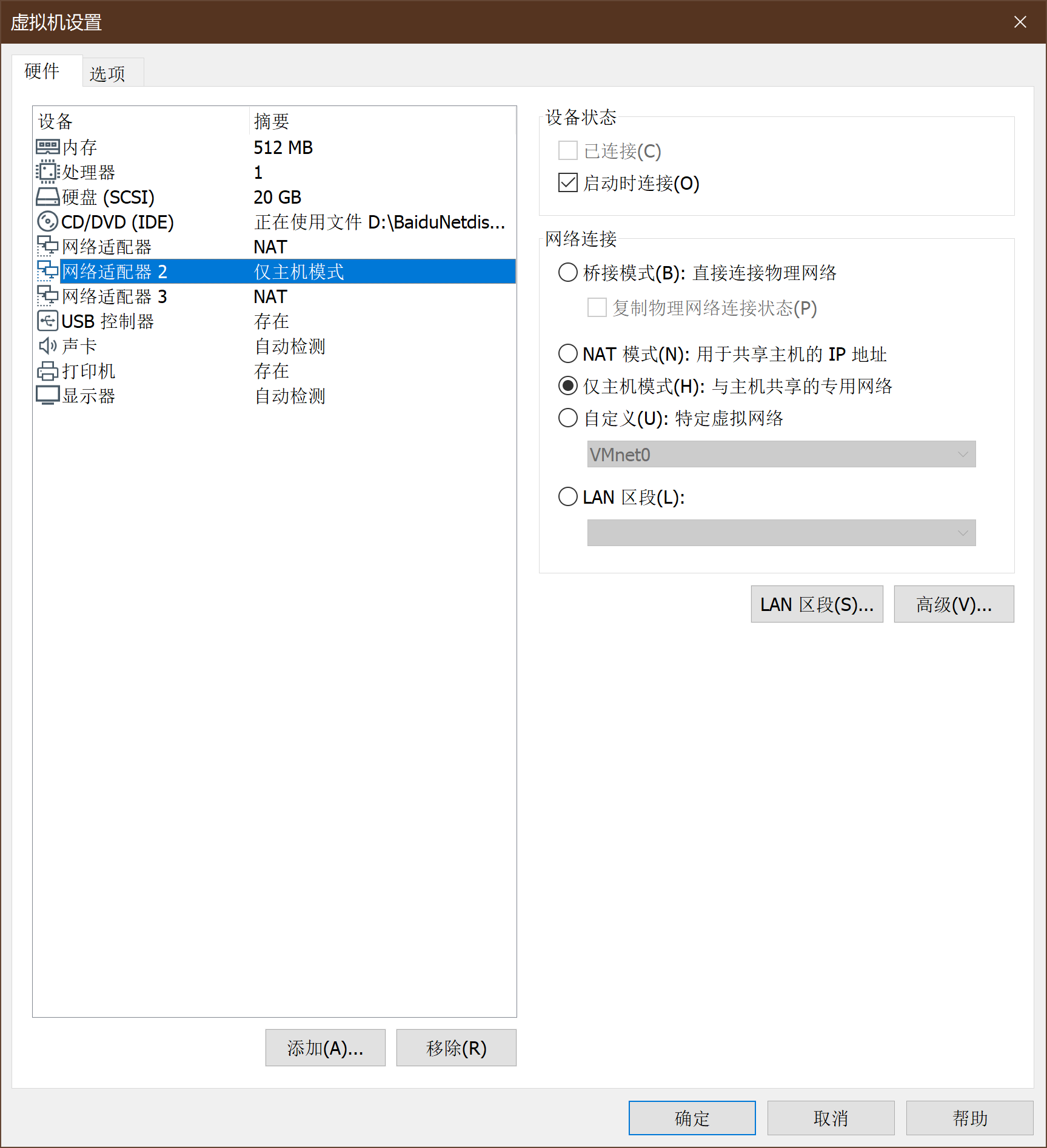
网络设置->添加两个网卡
-
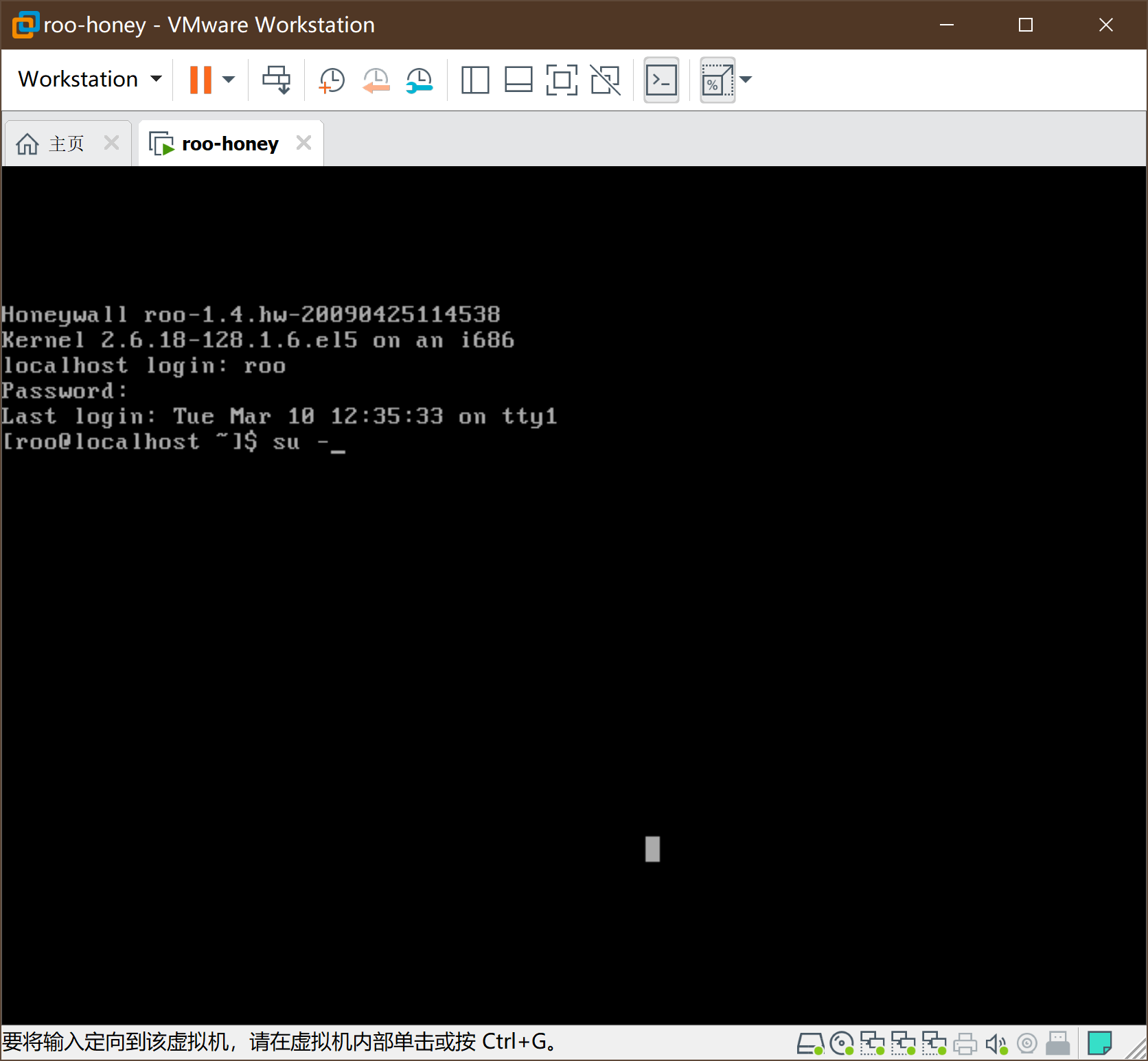
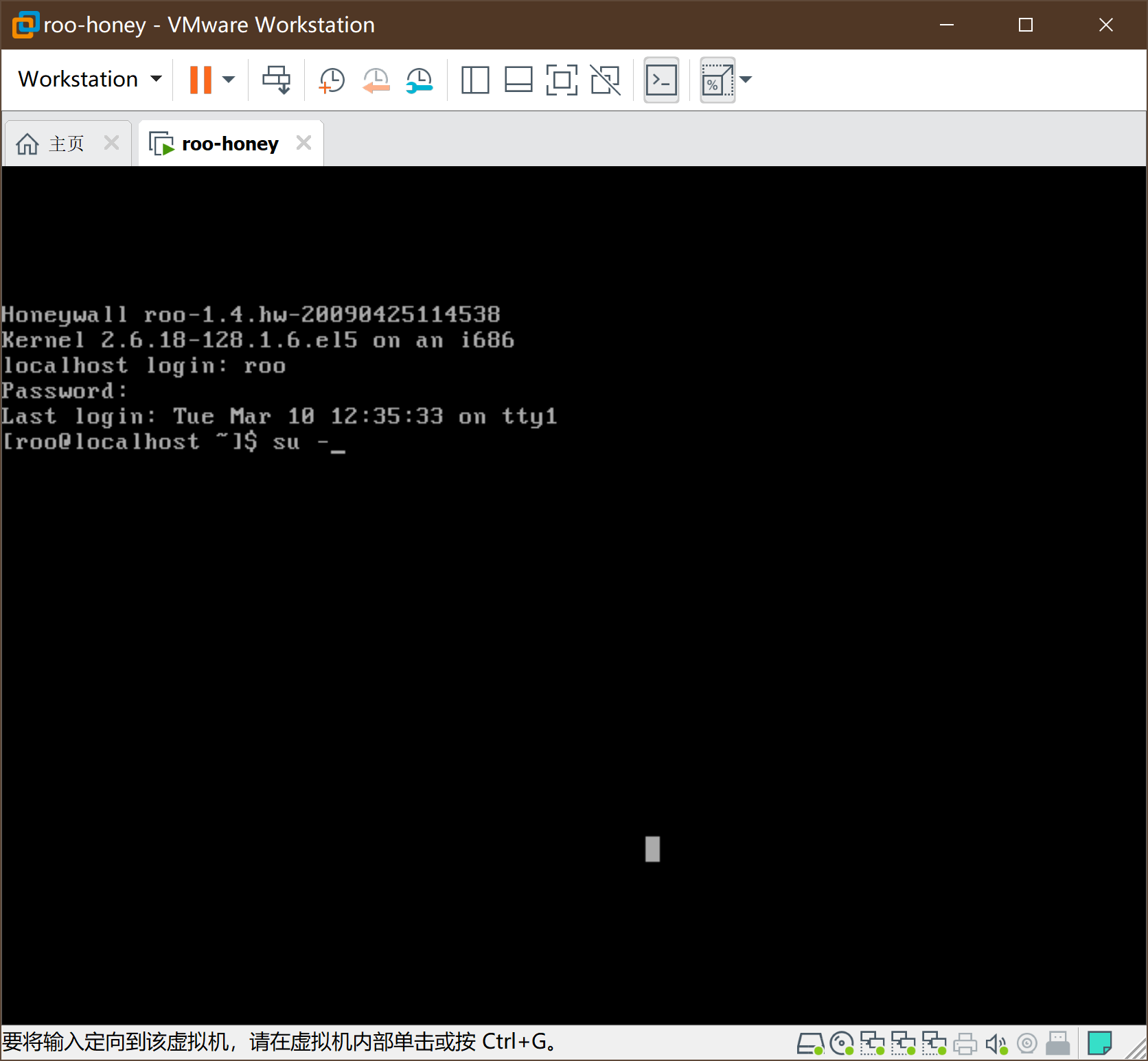
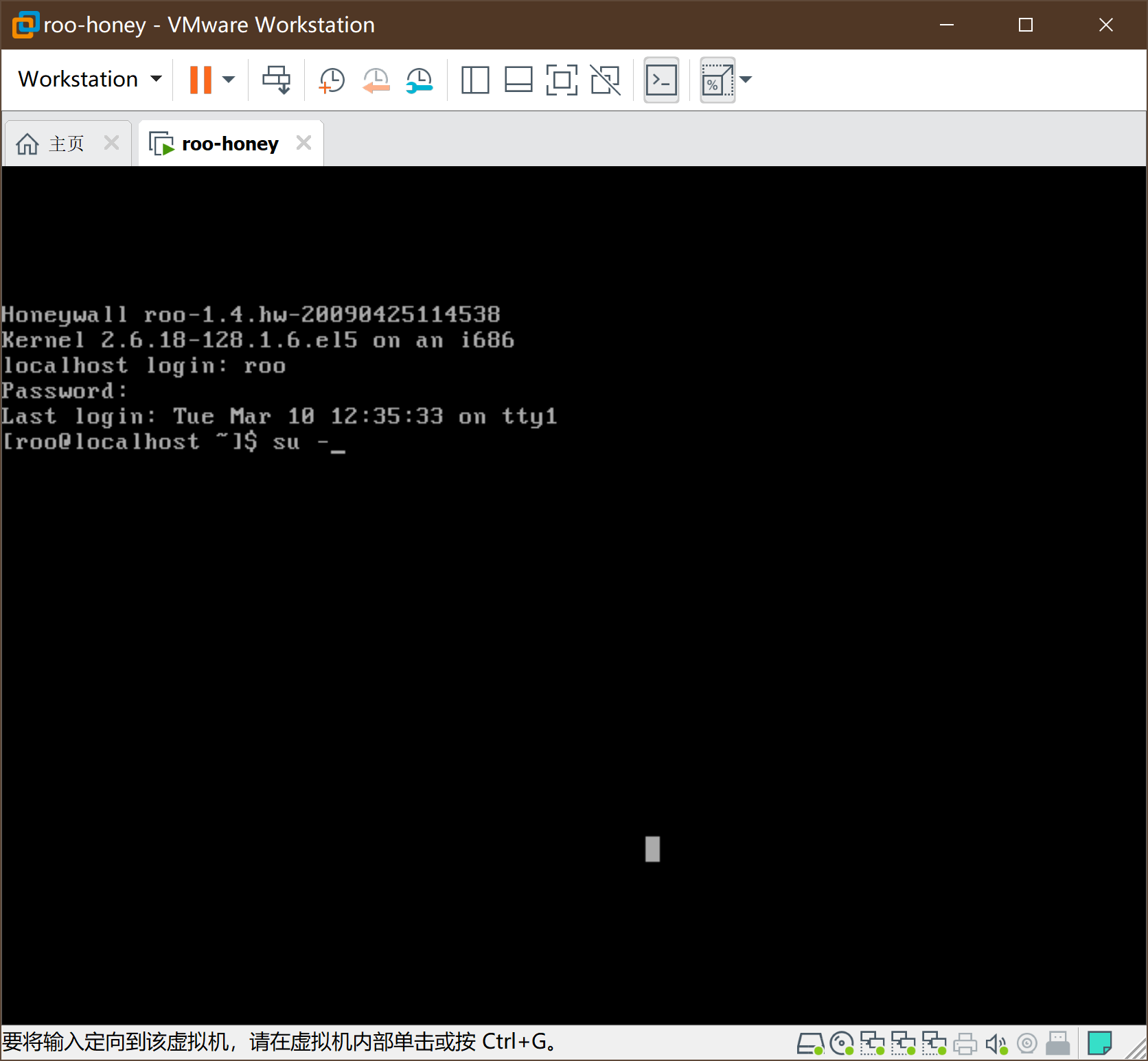
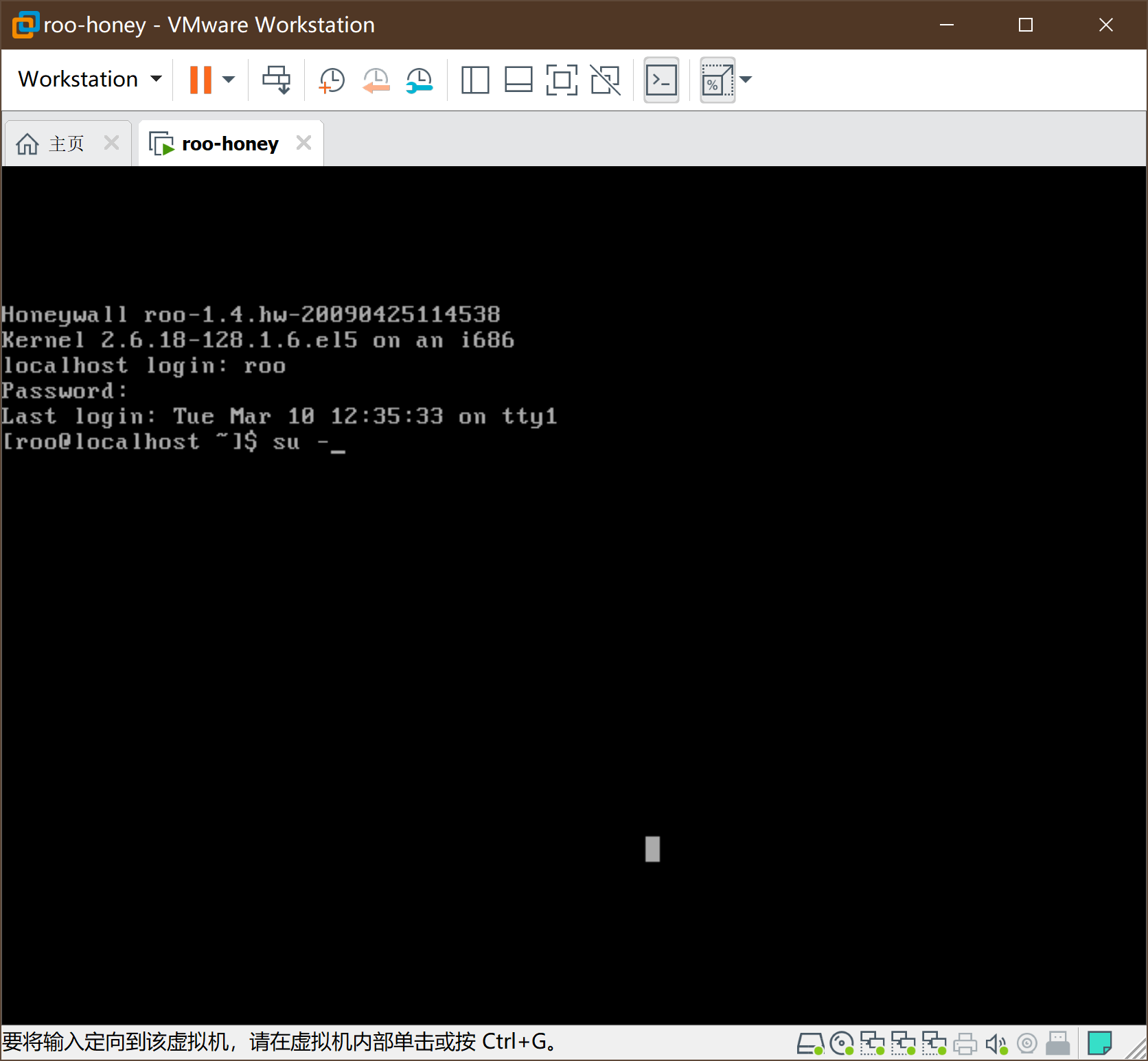
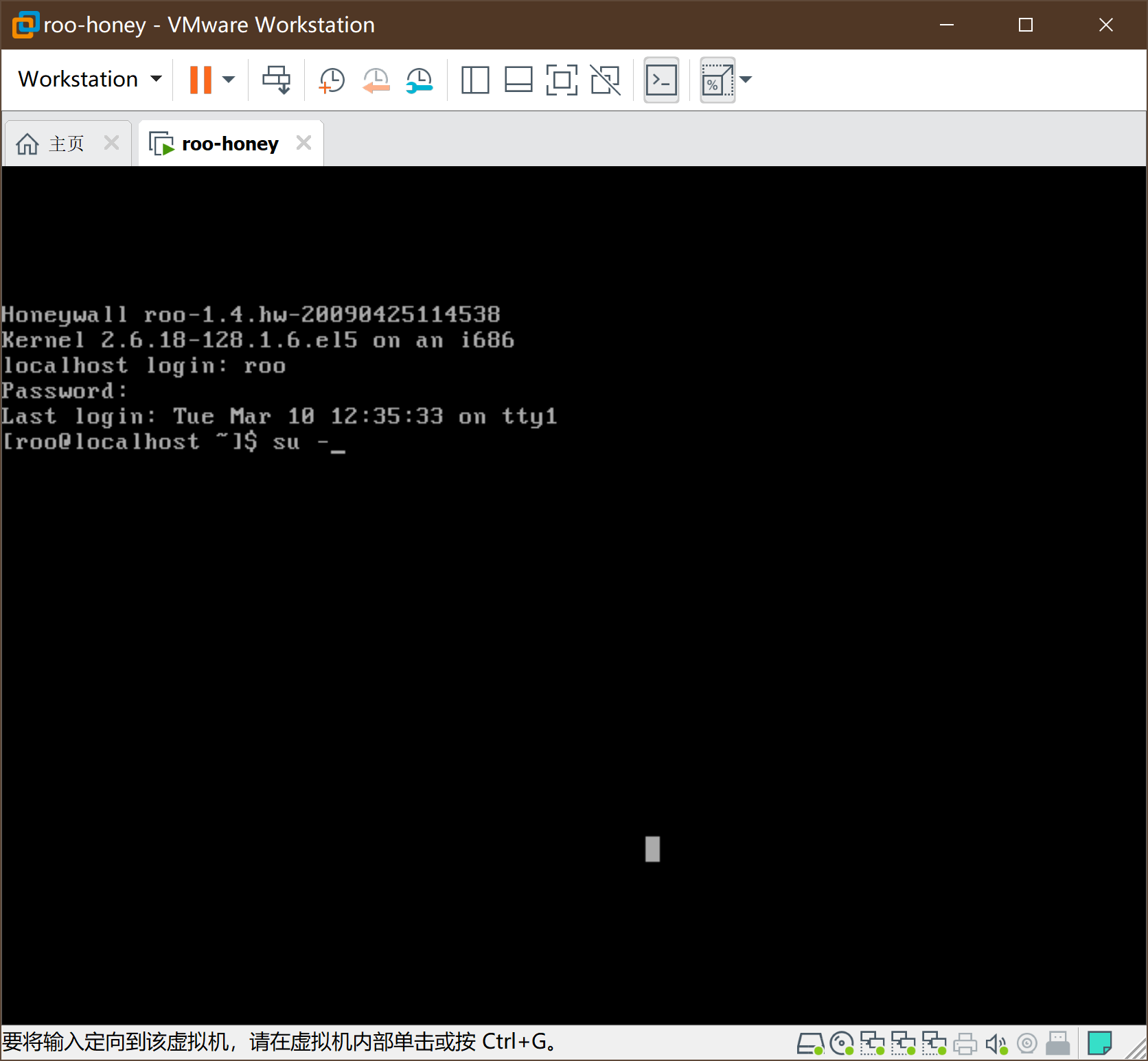
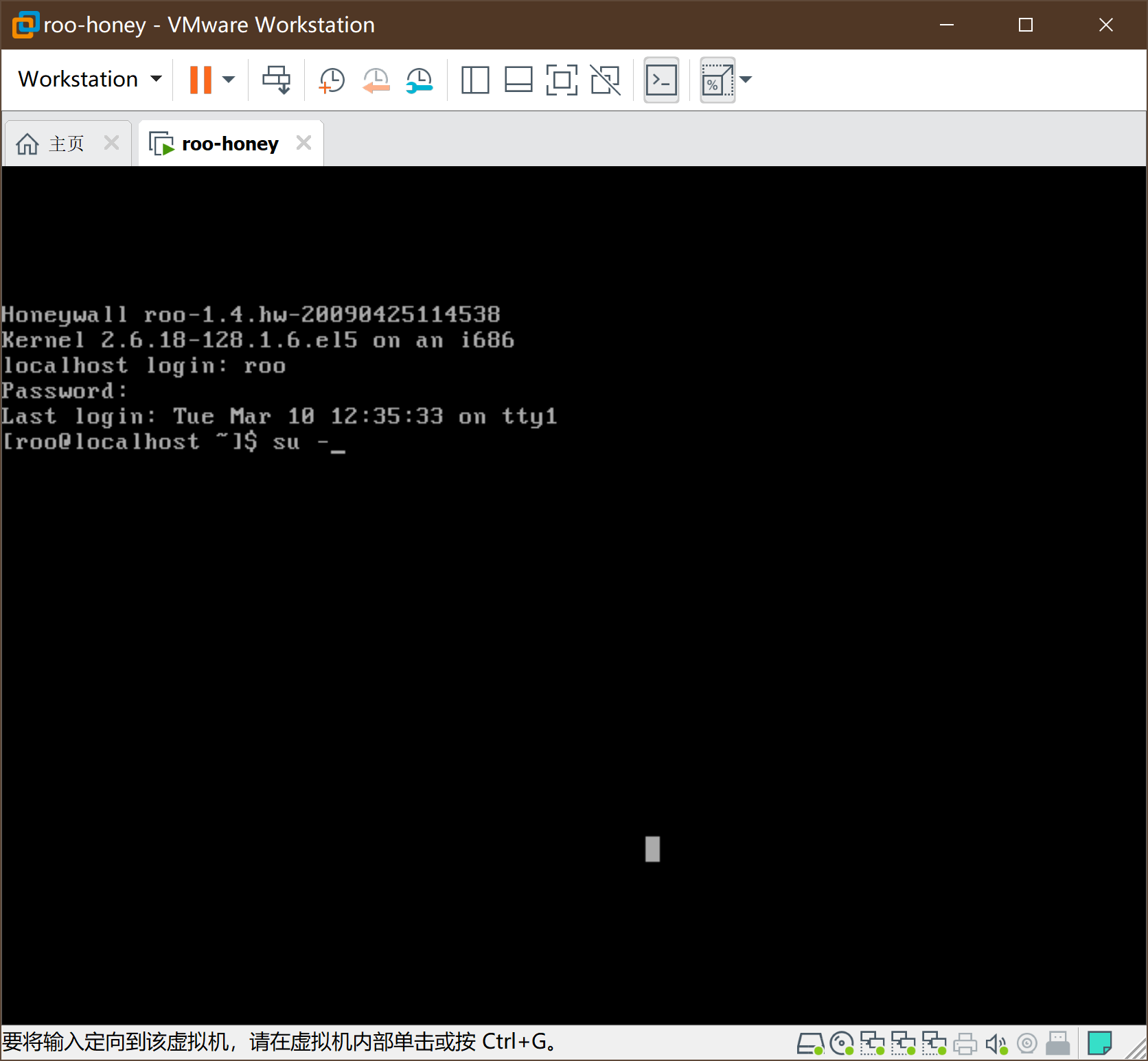
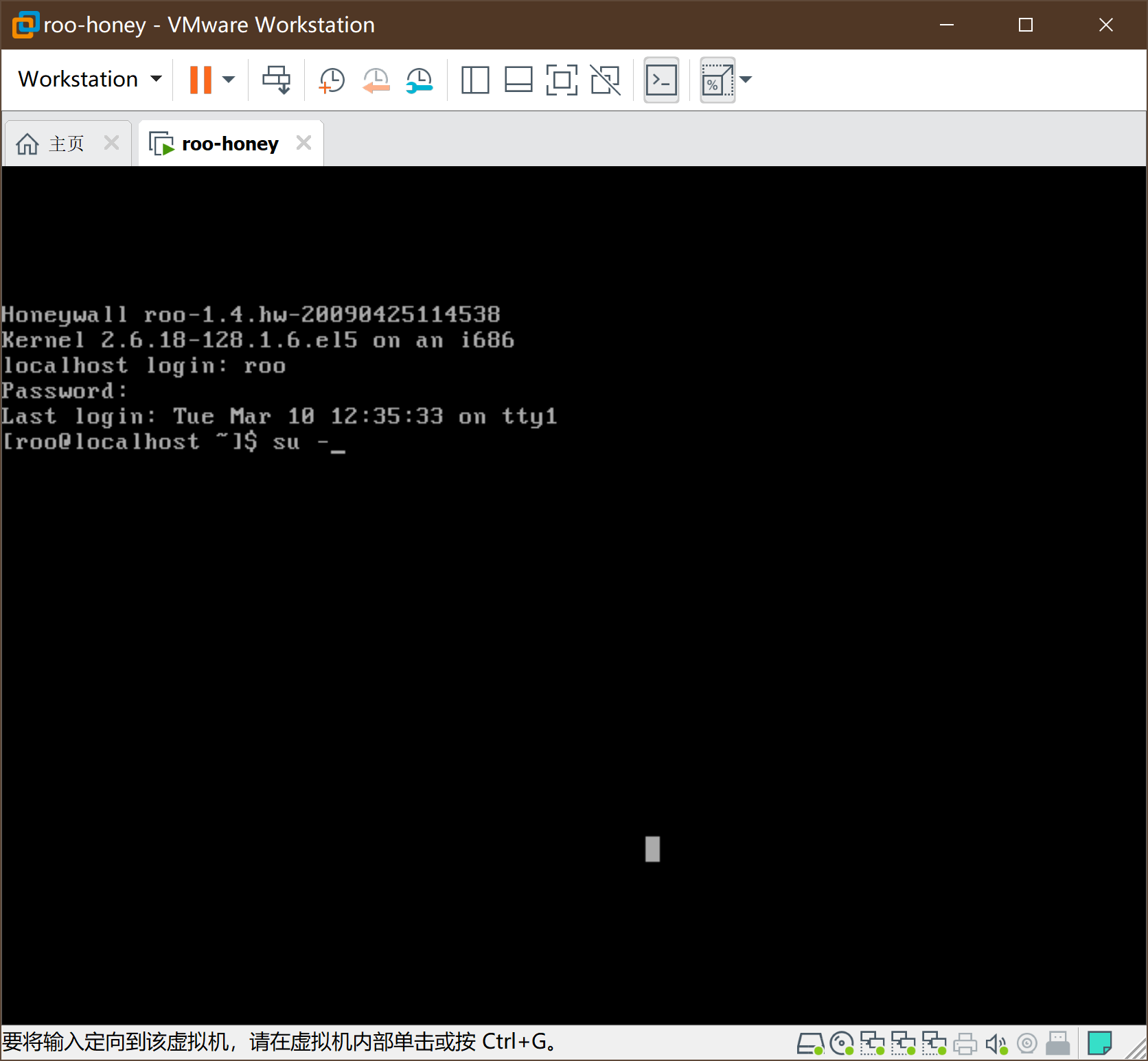
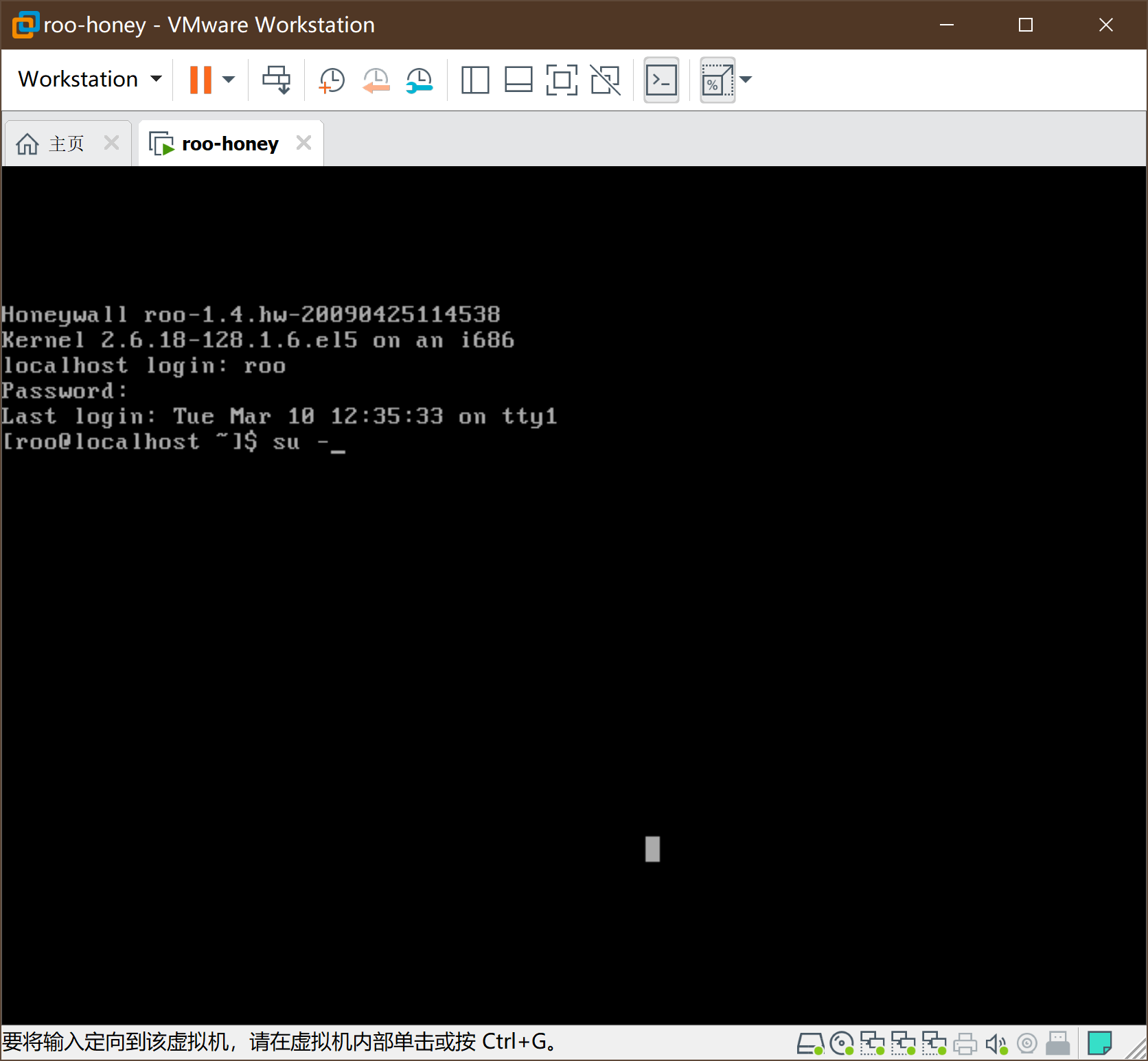
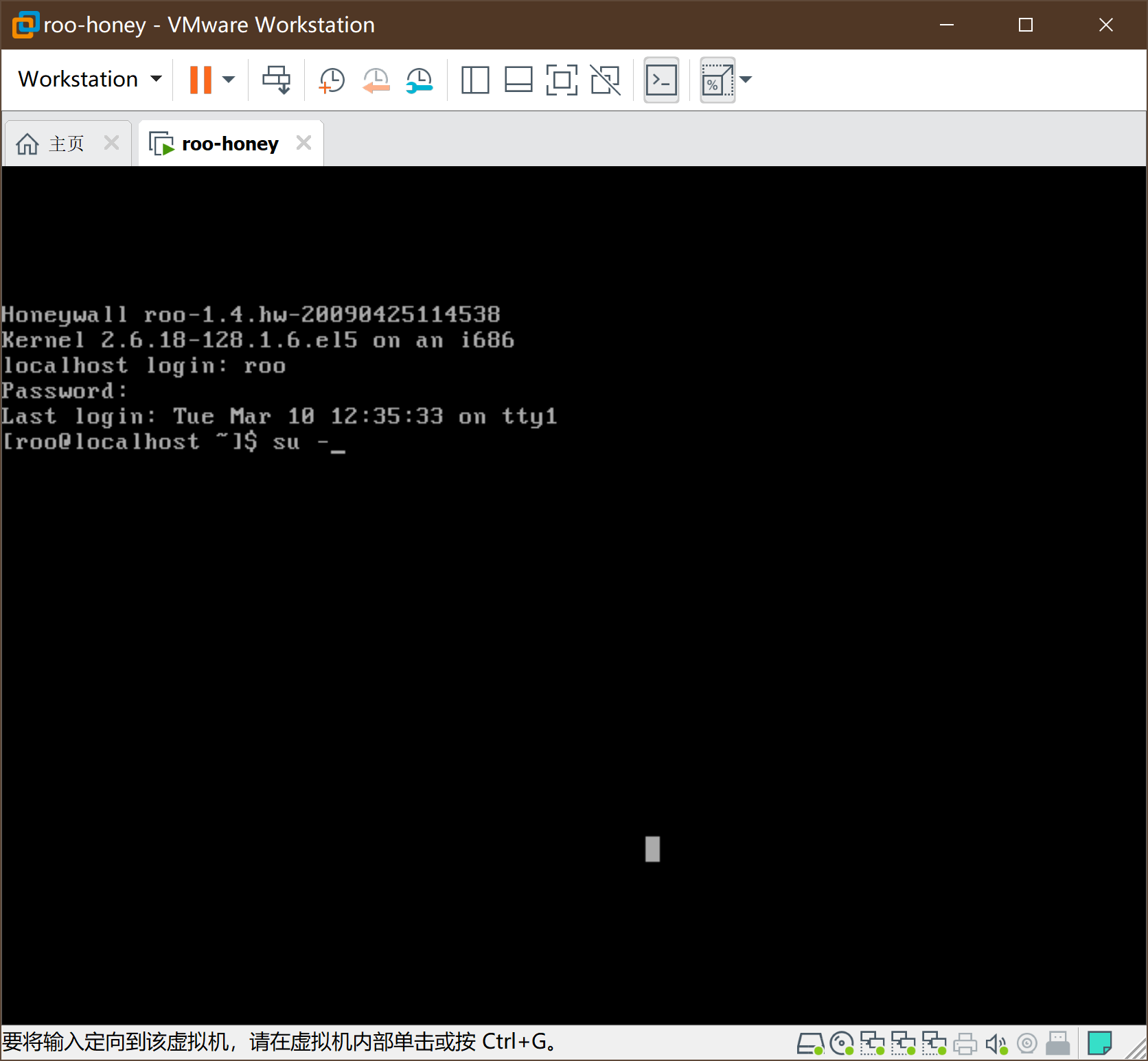
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
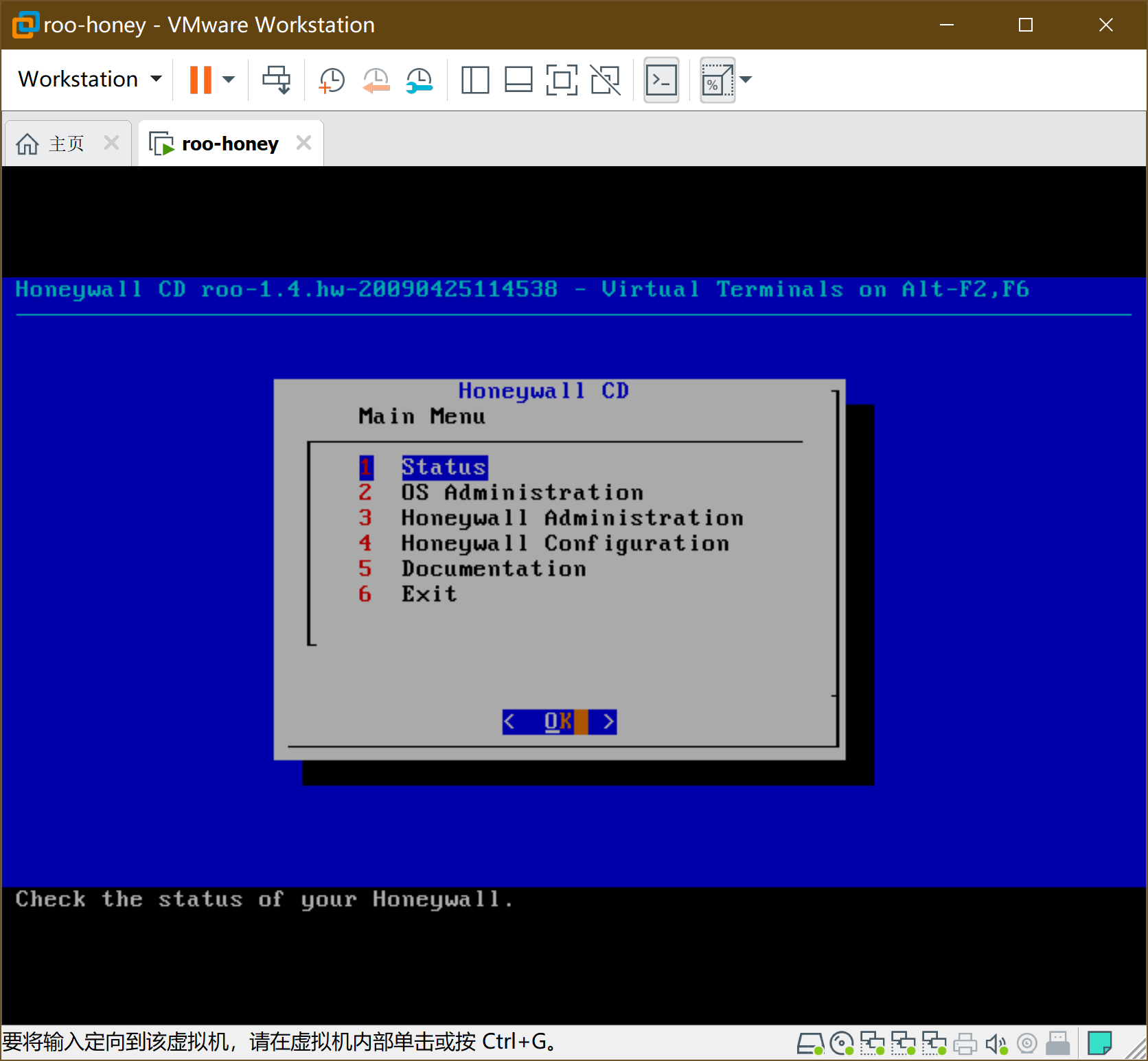
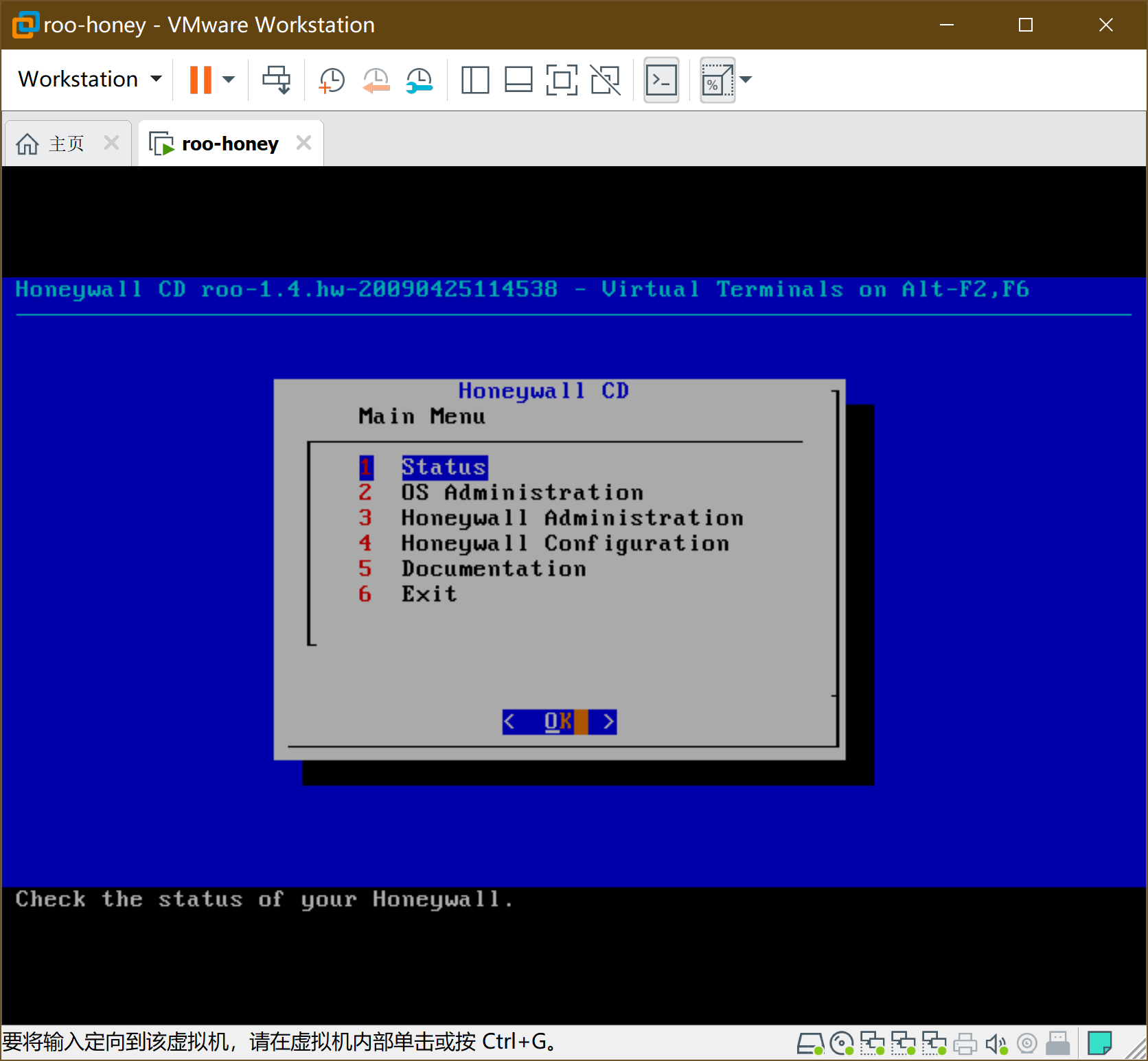
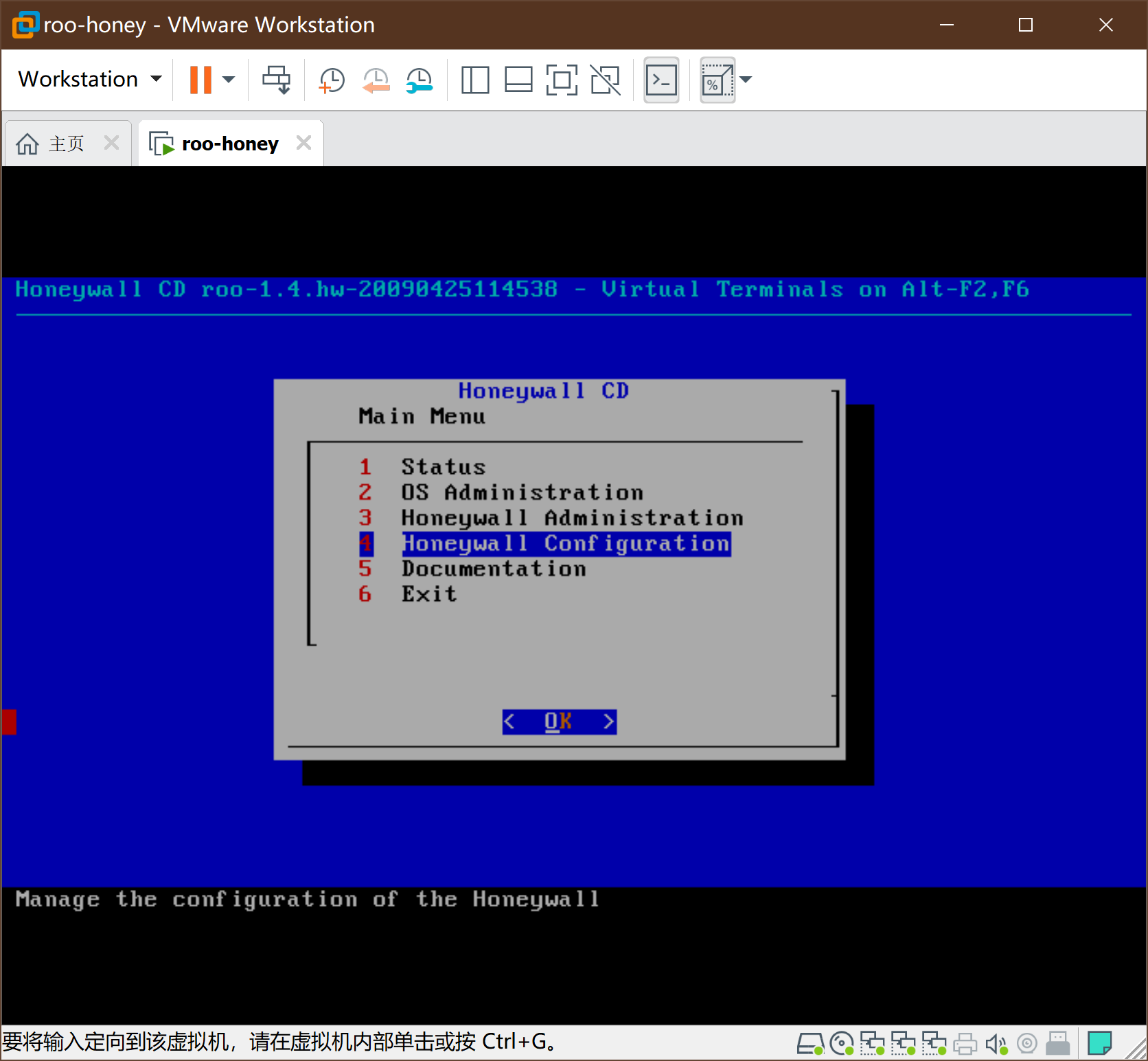
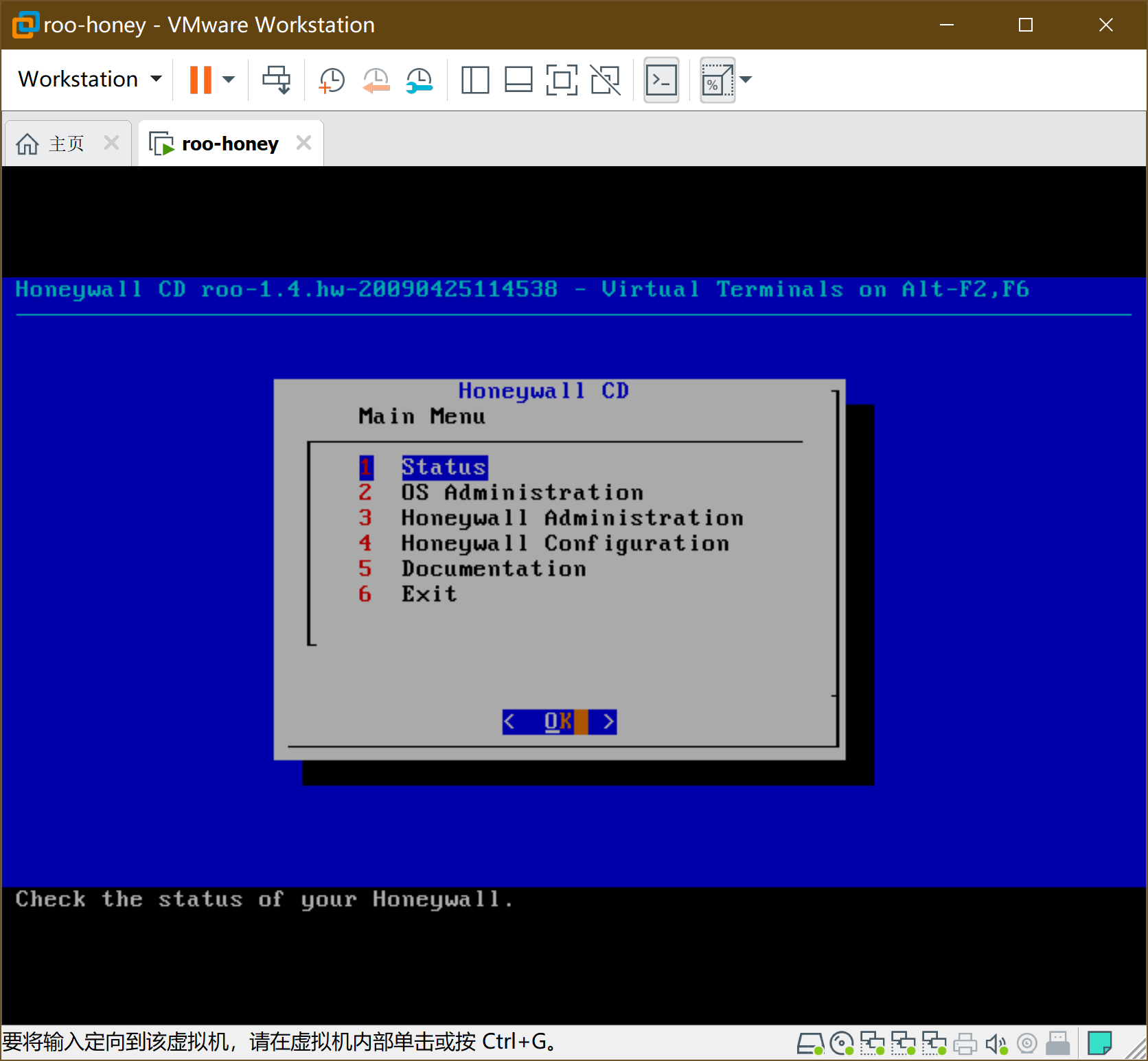
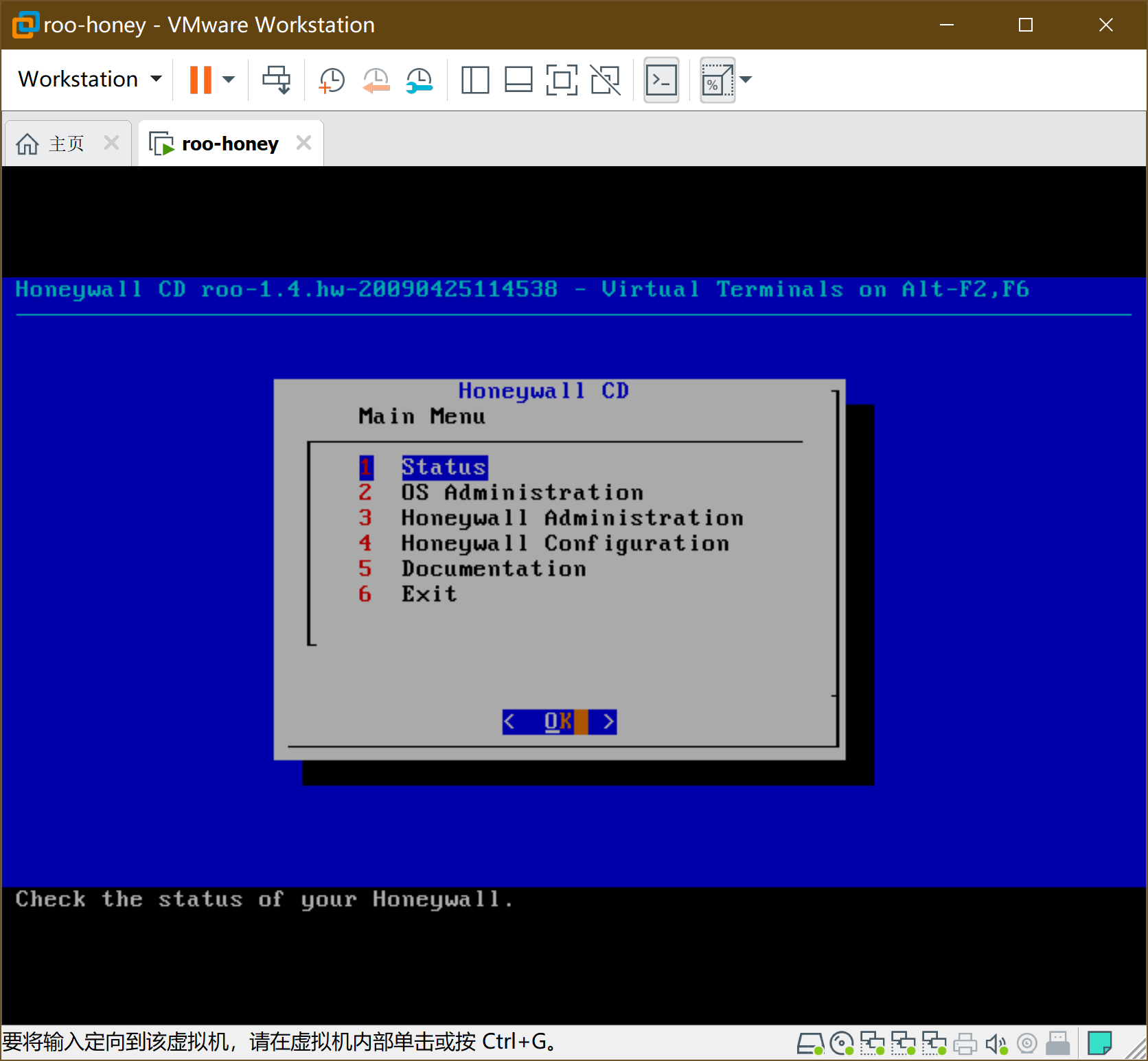
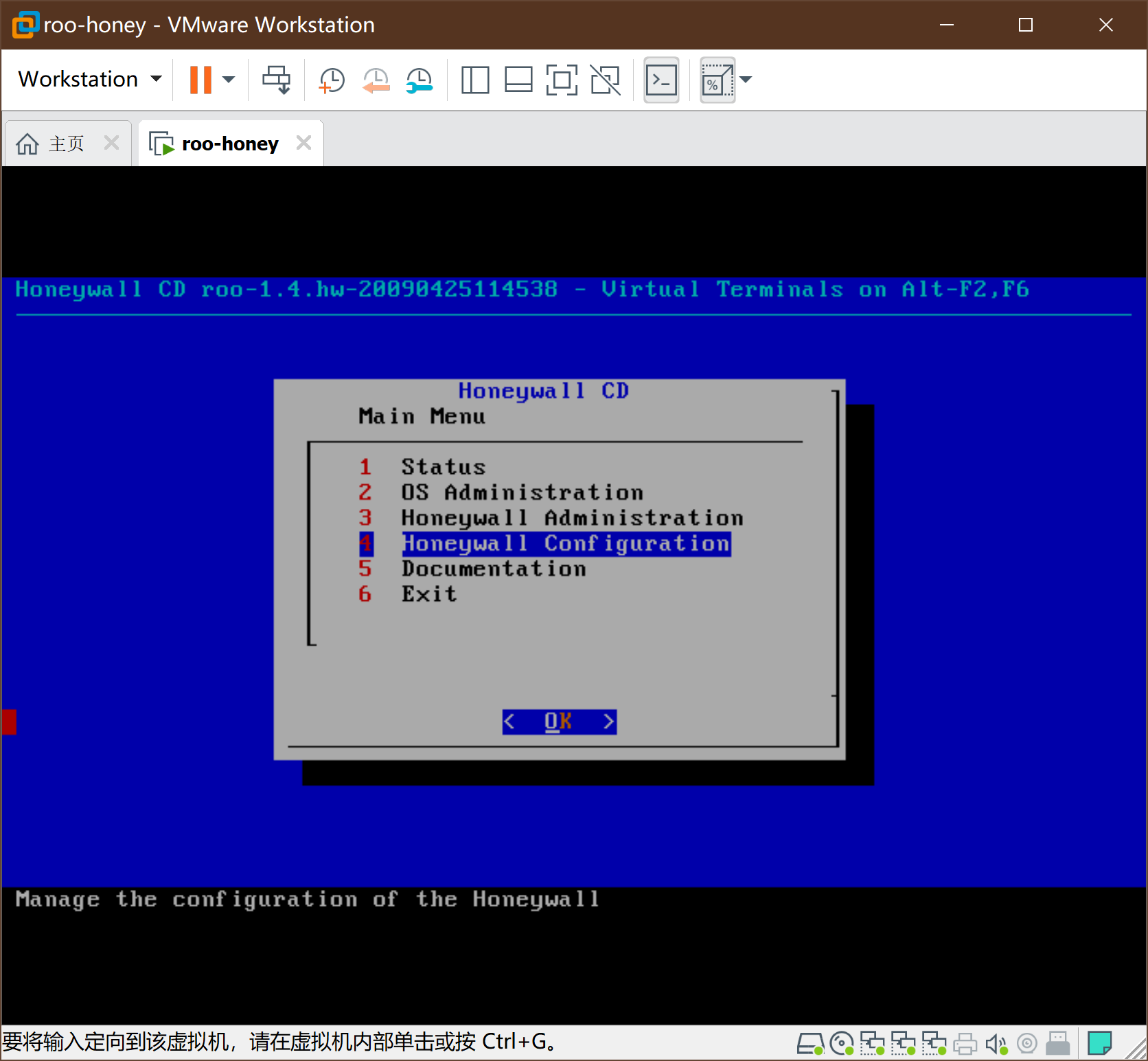
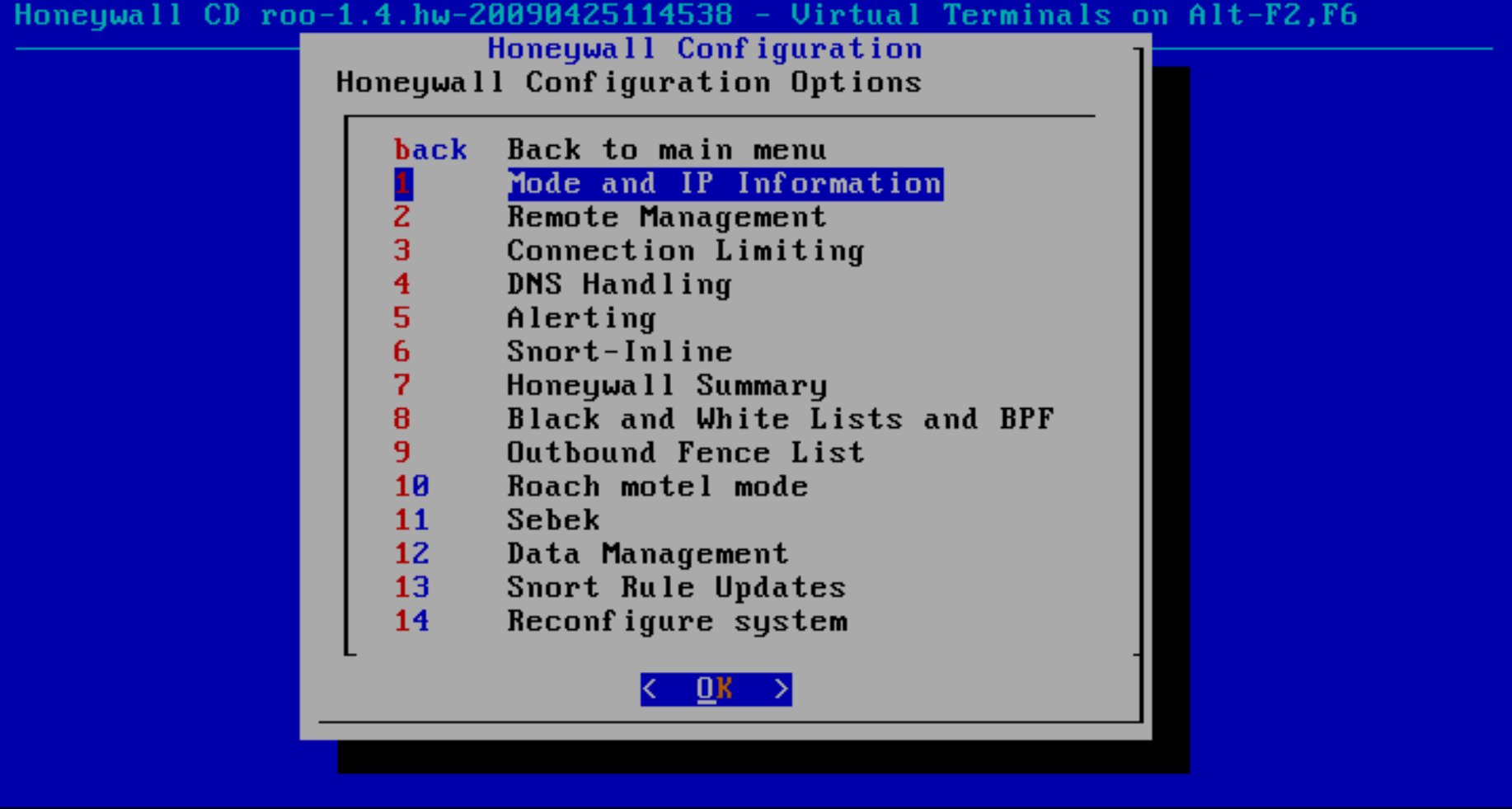
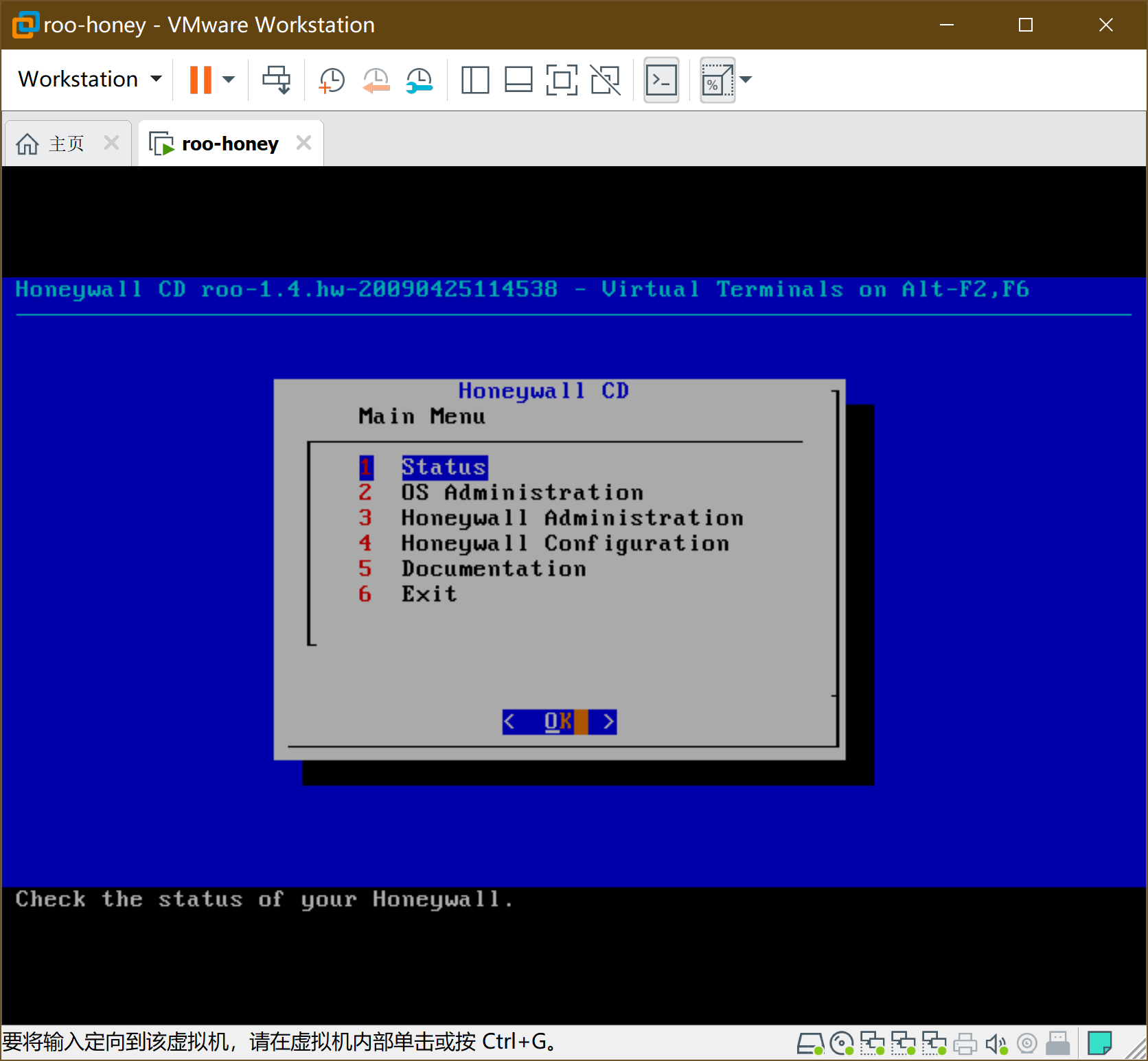
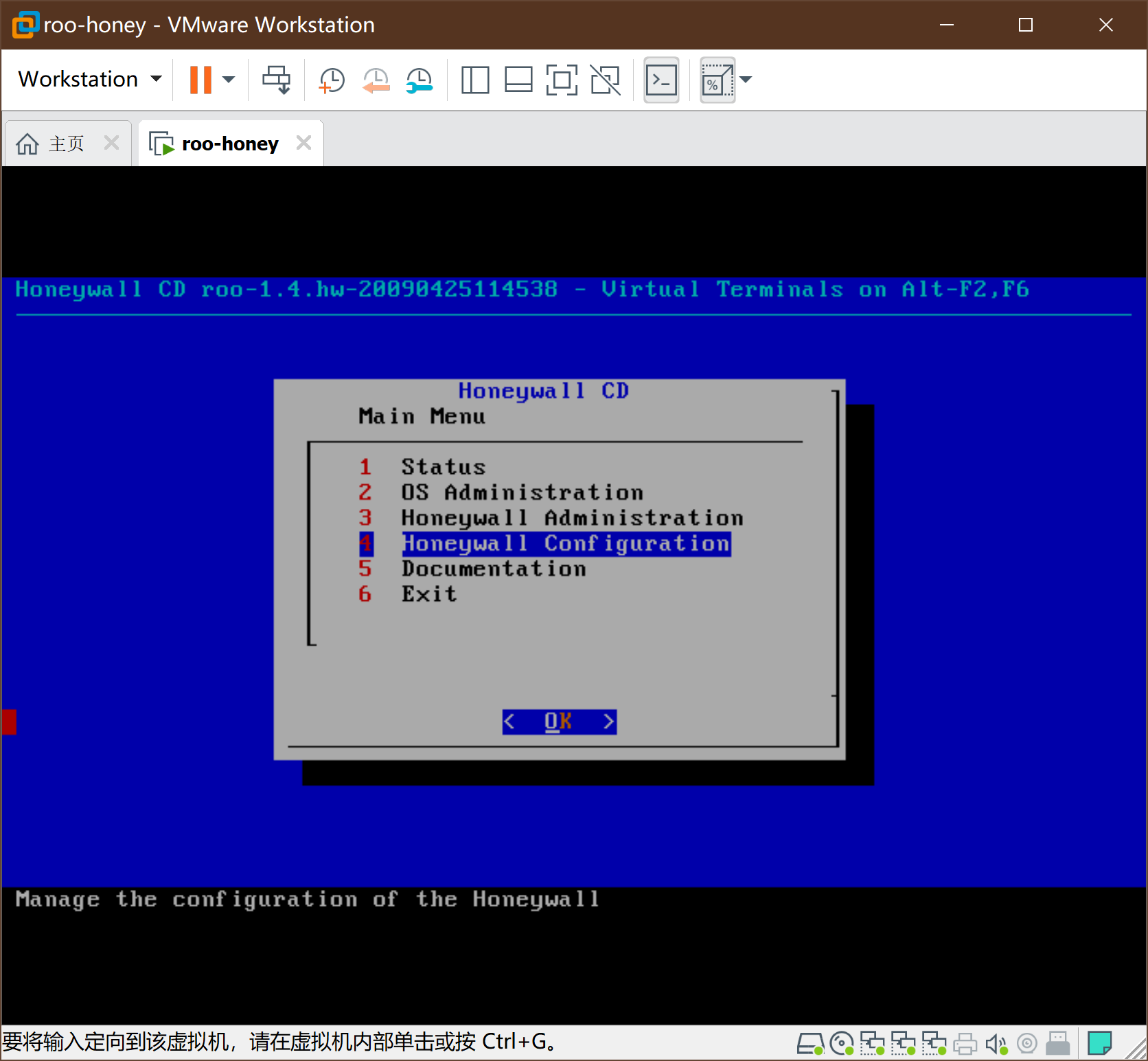
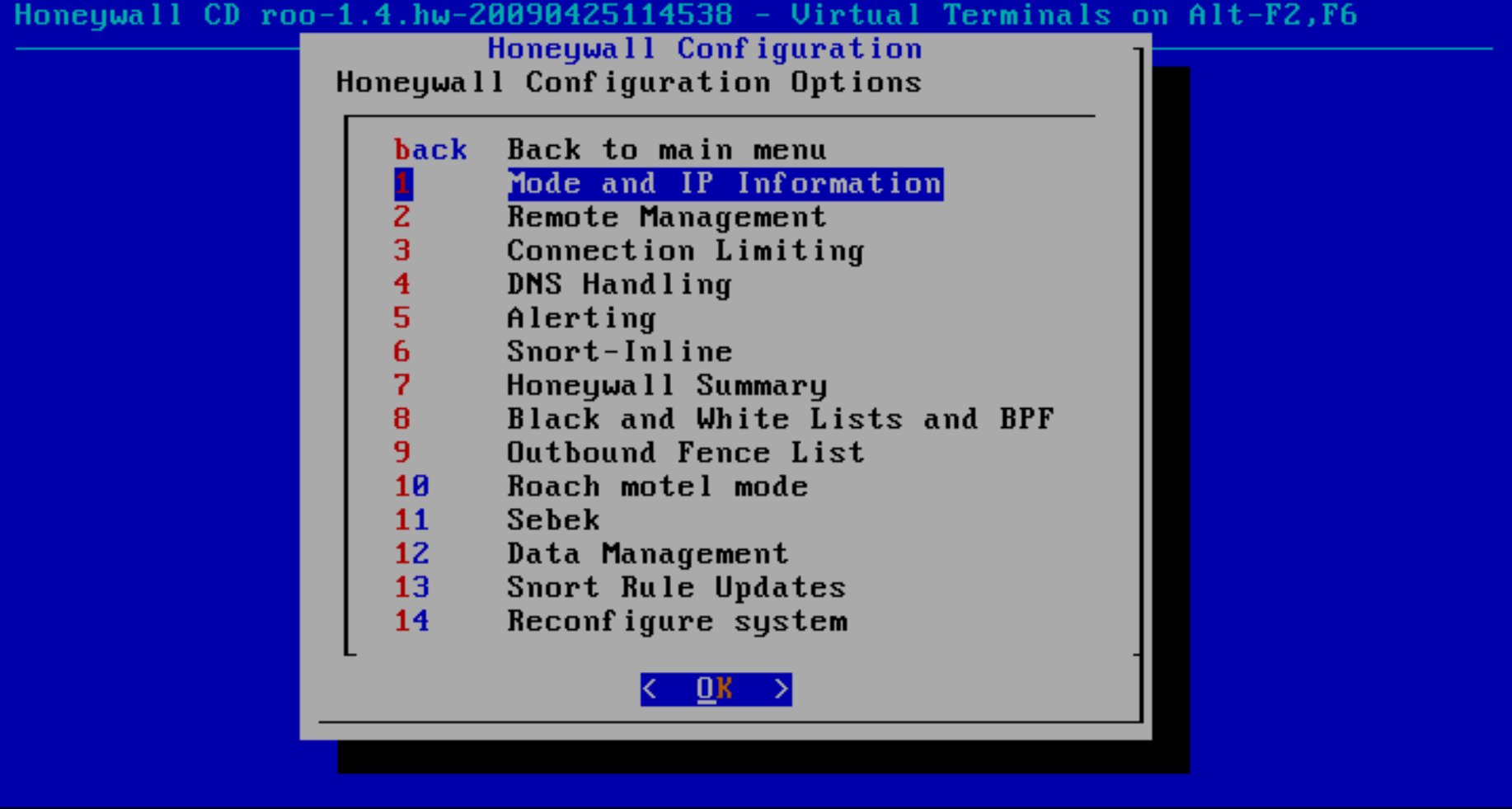
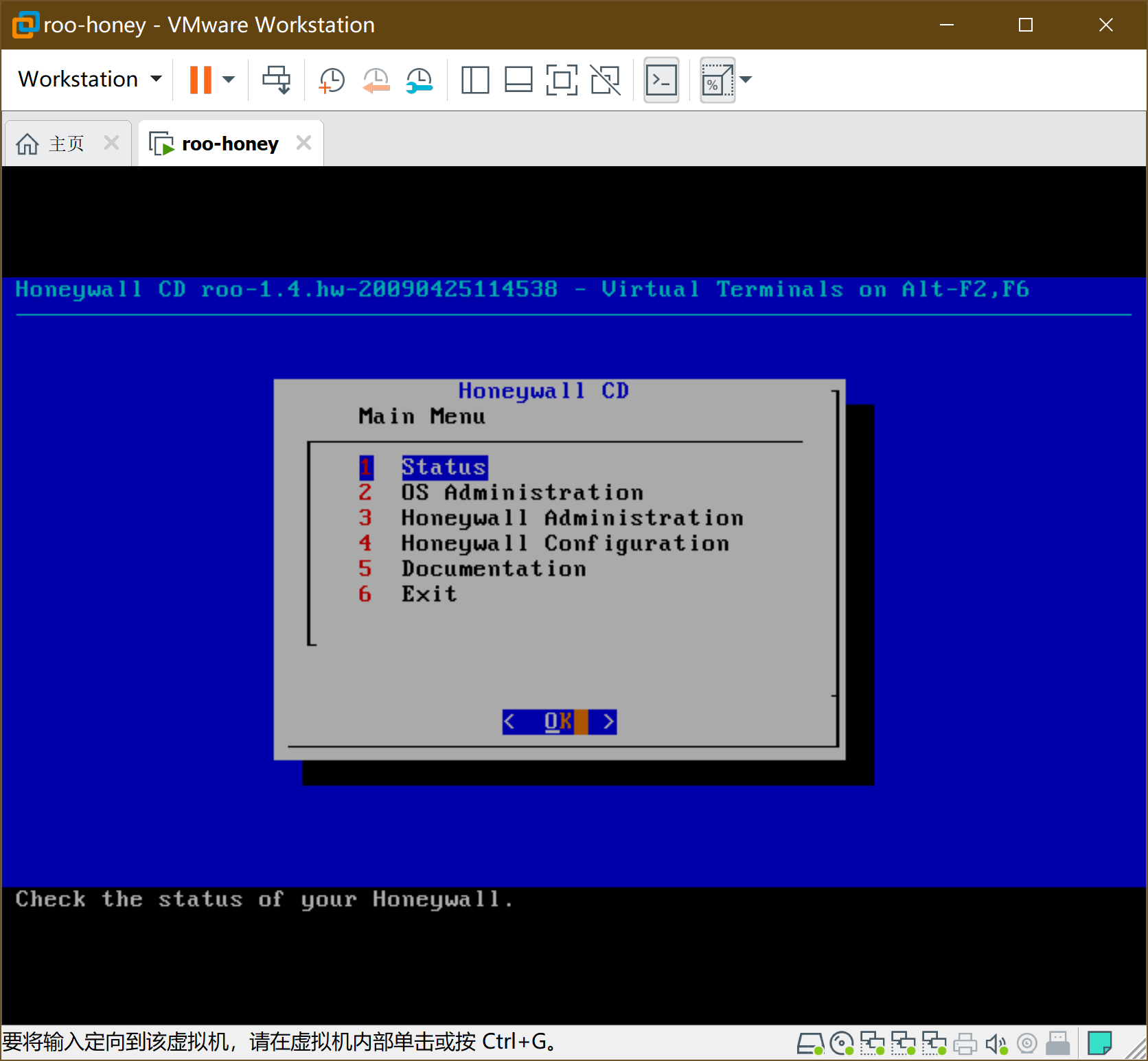
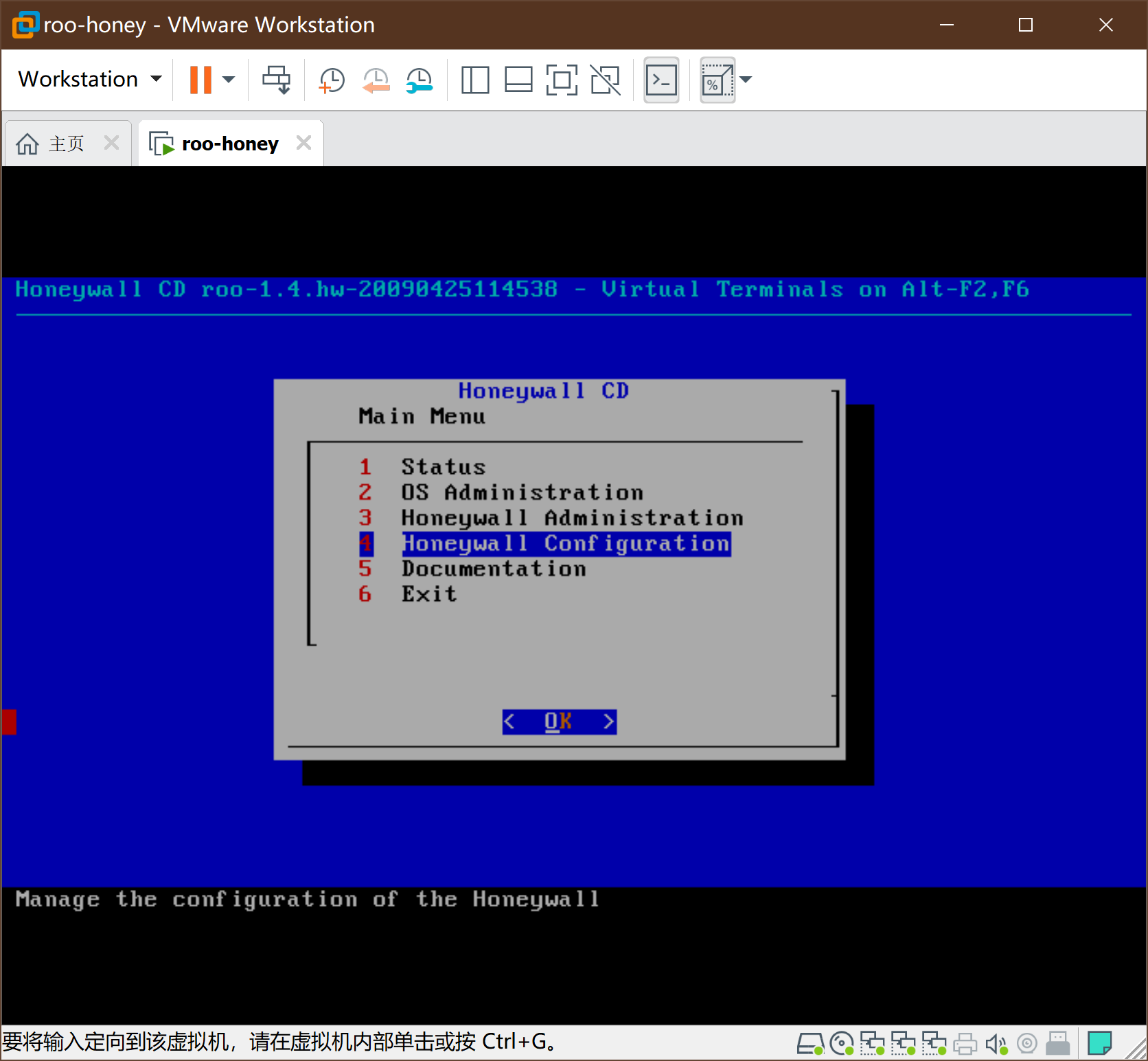
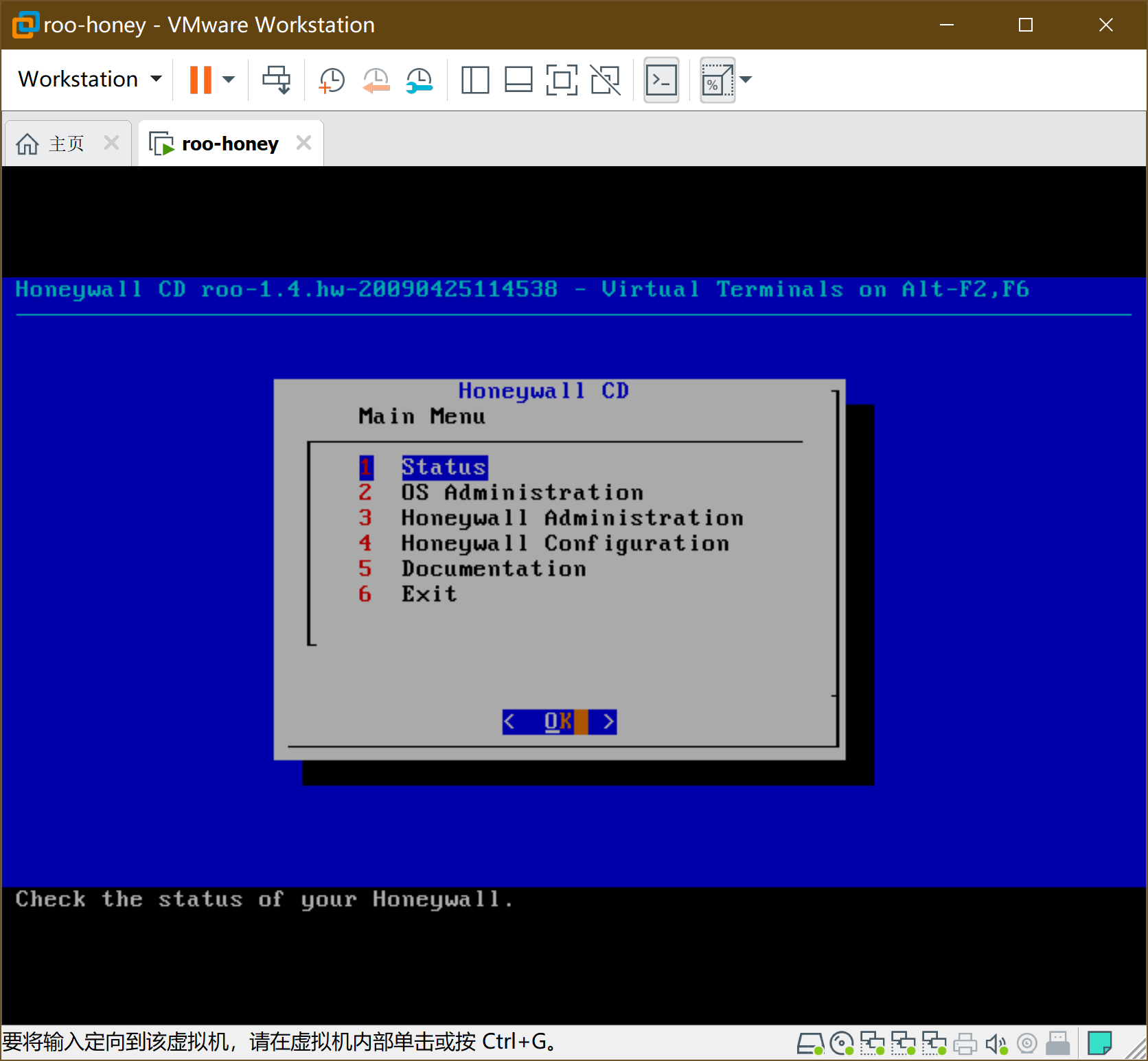
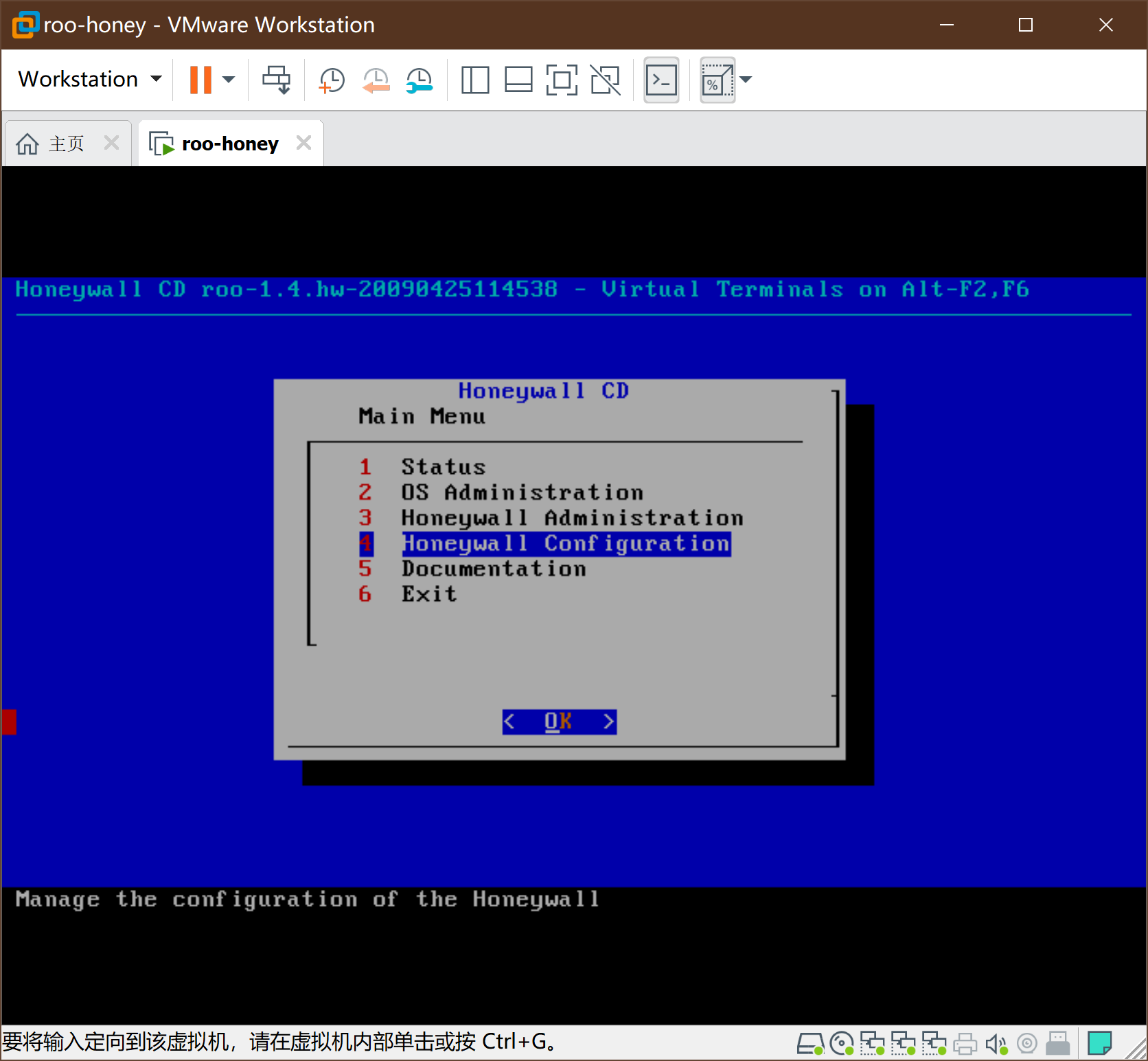
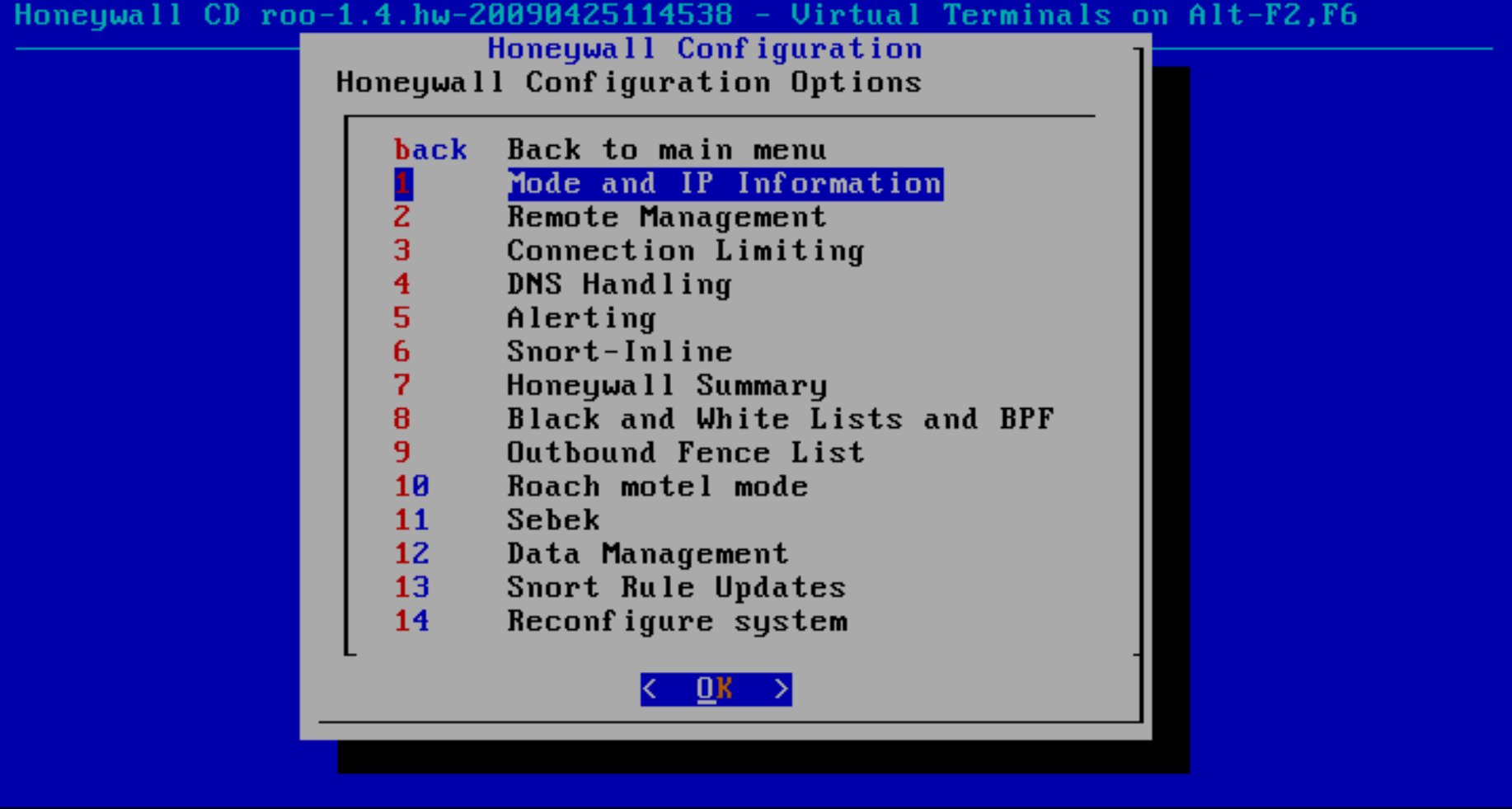
开始设置->初始化选default
-
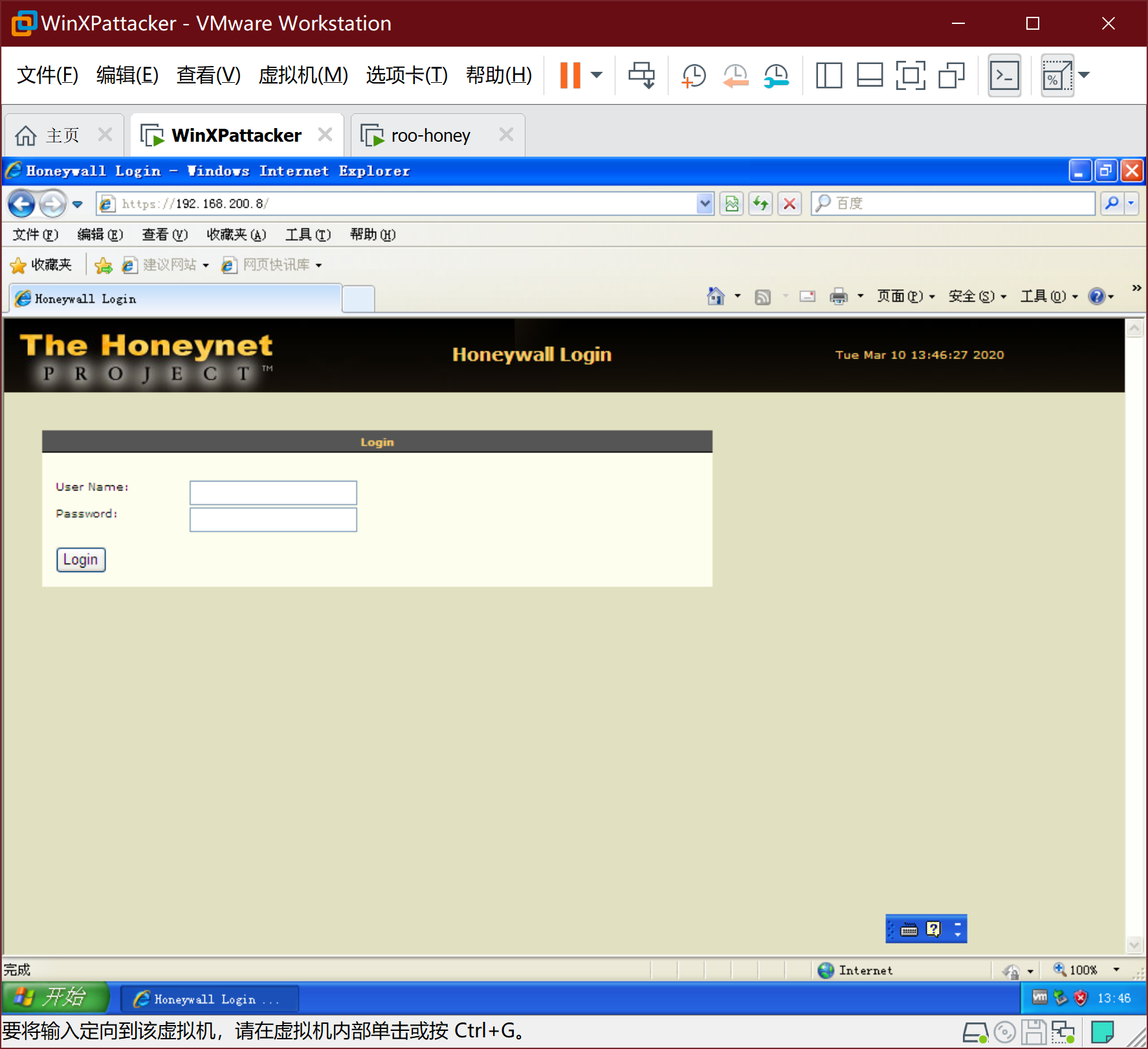
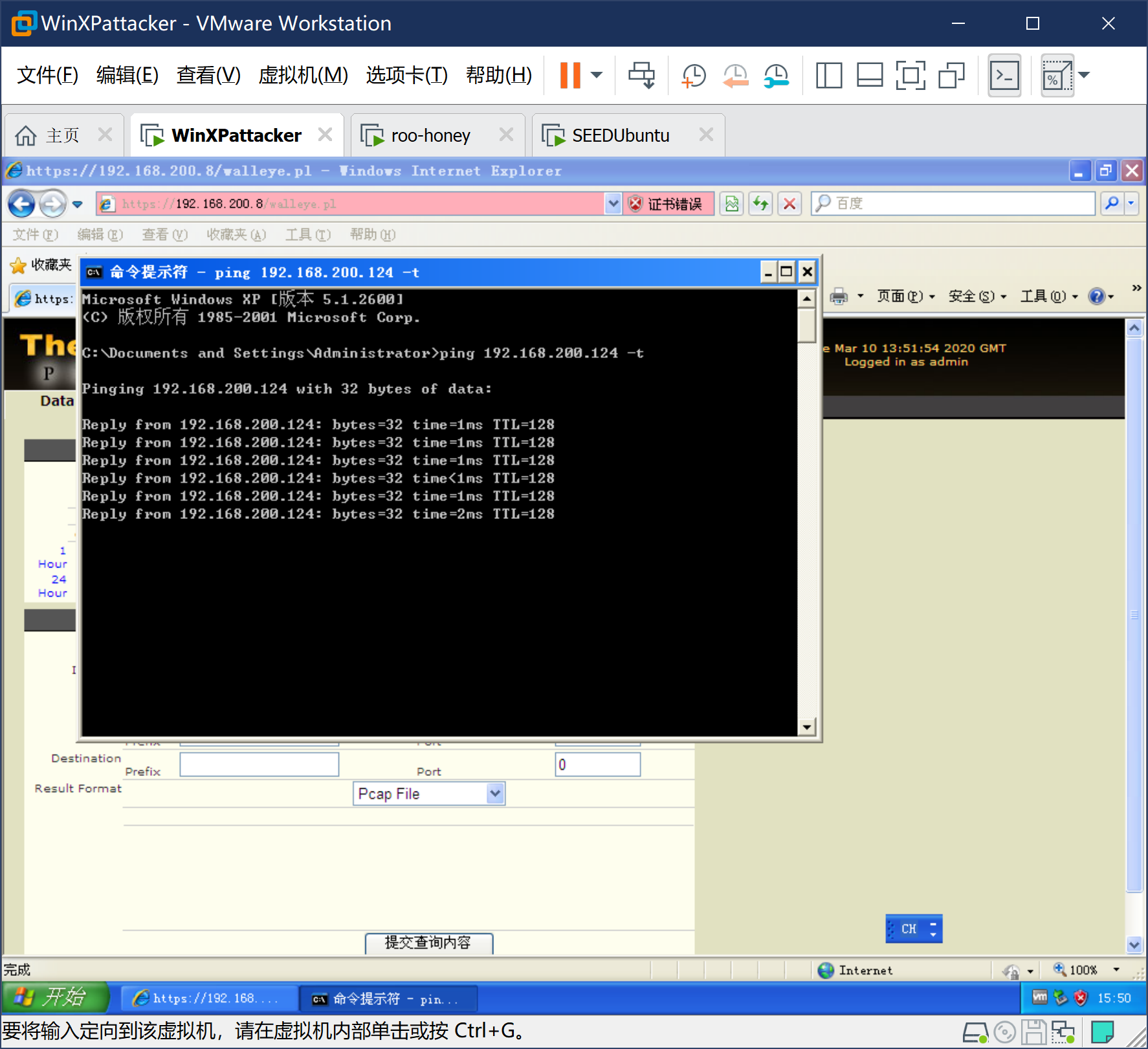
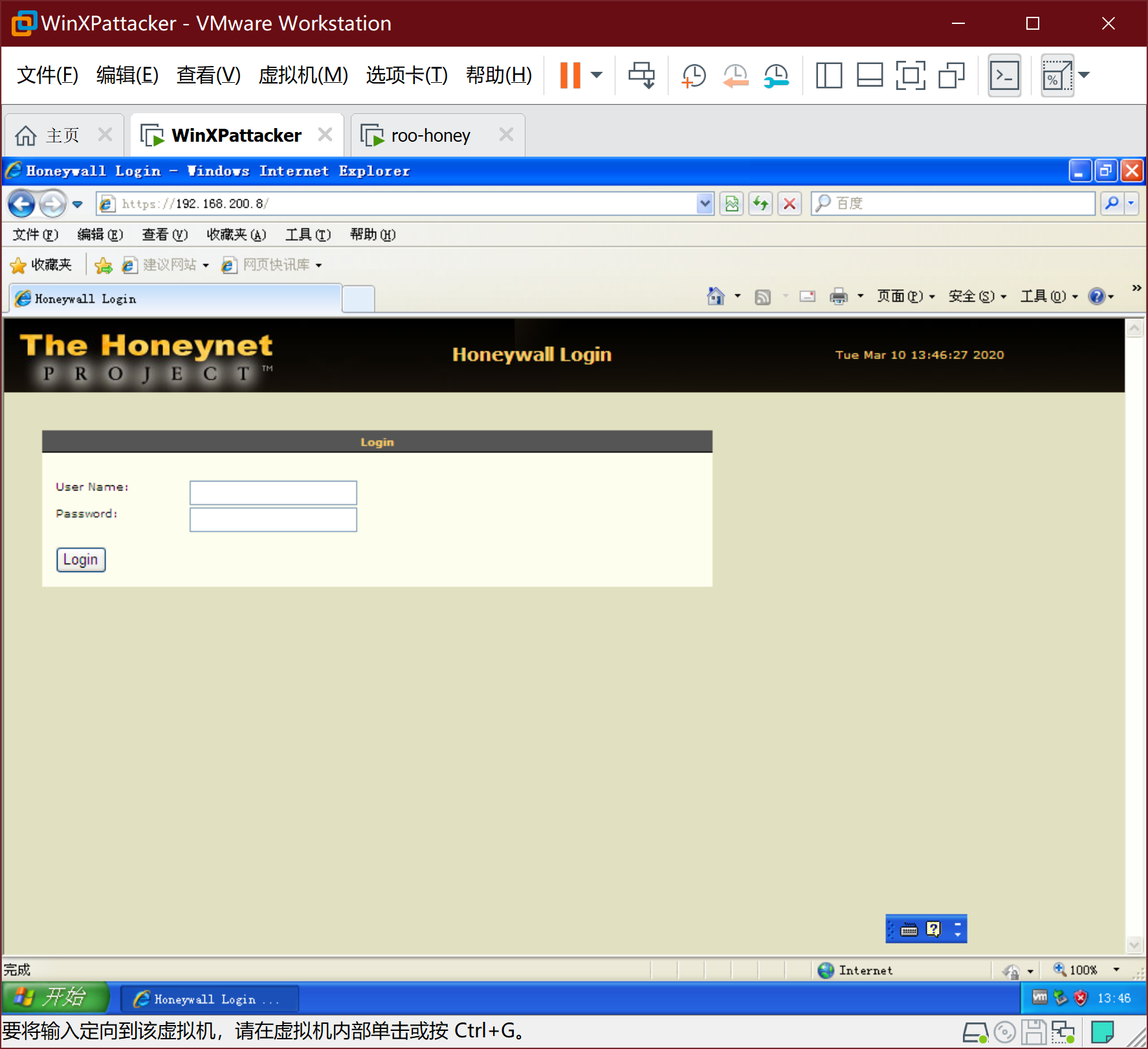
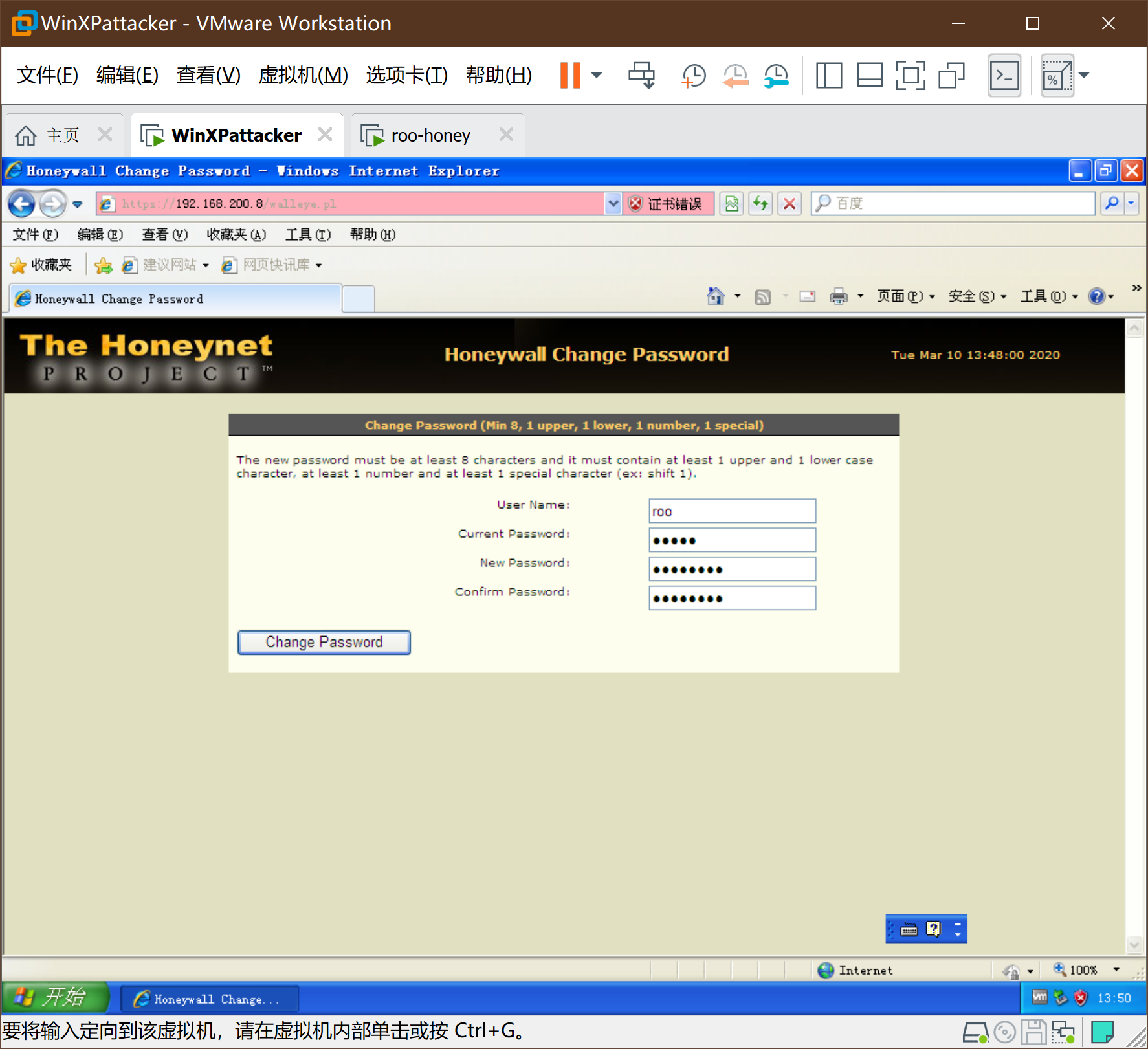
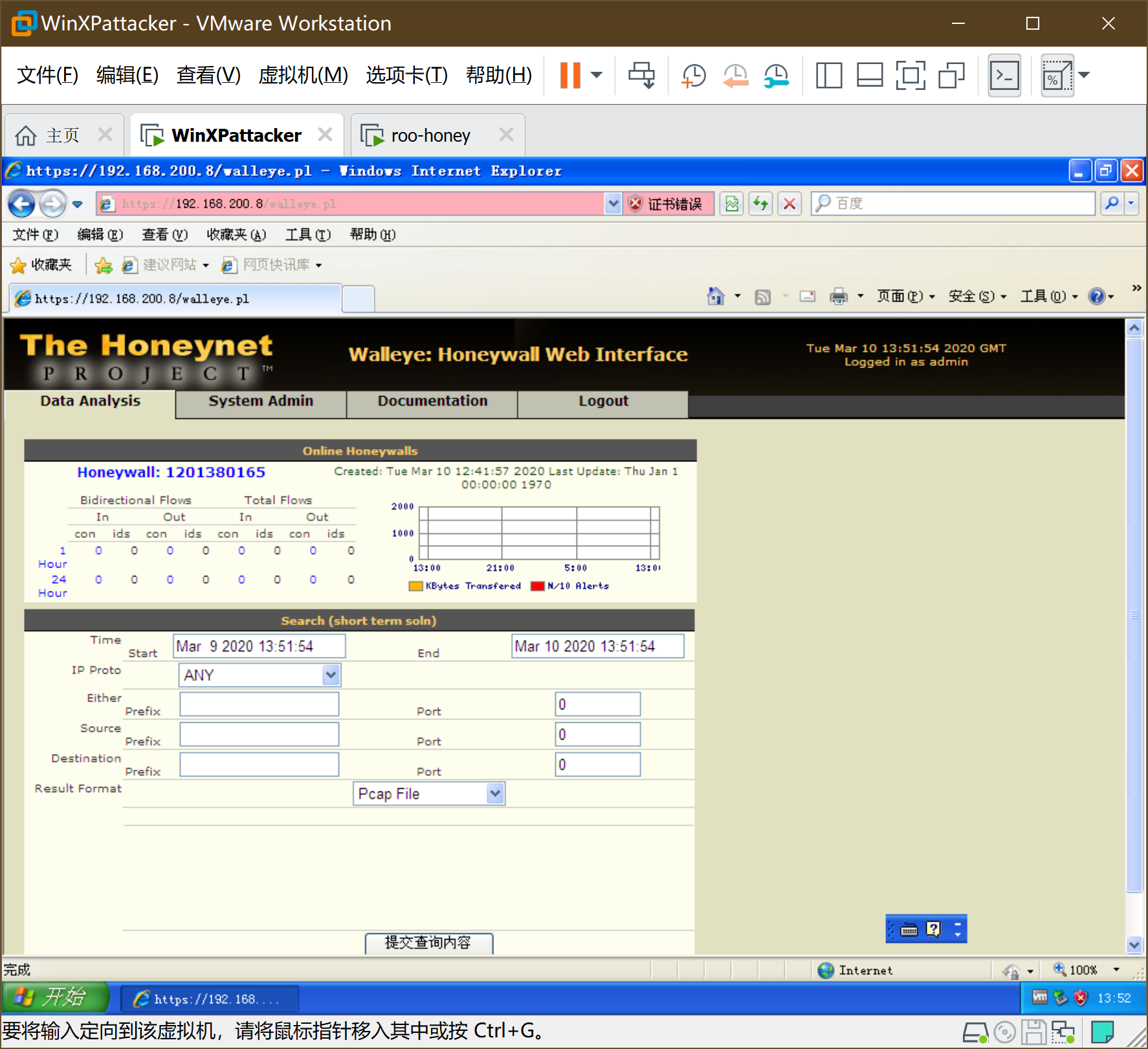
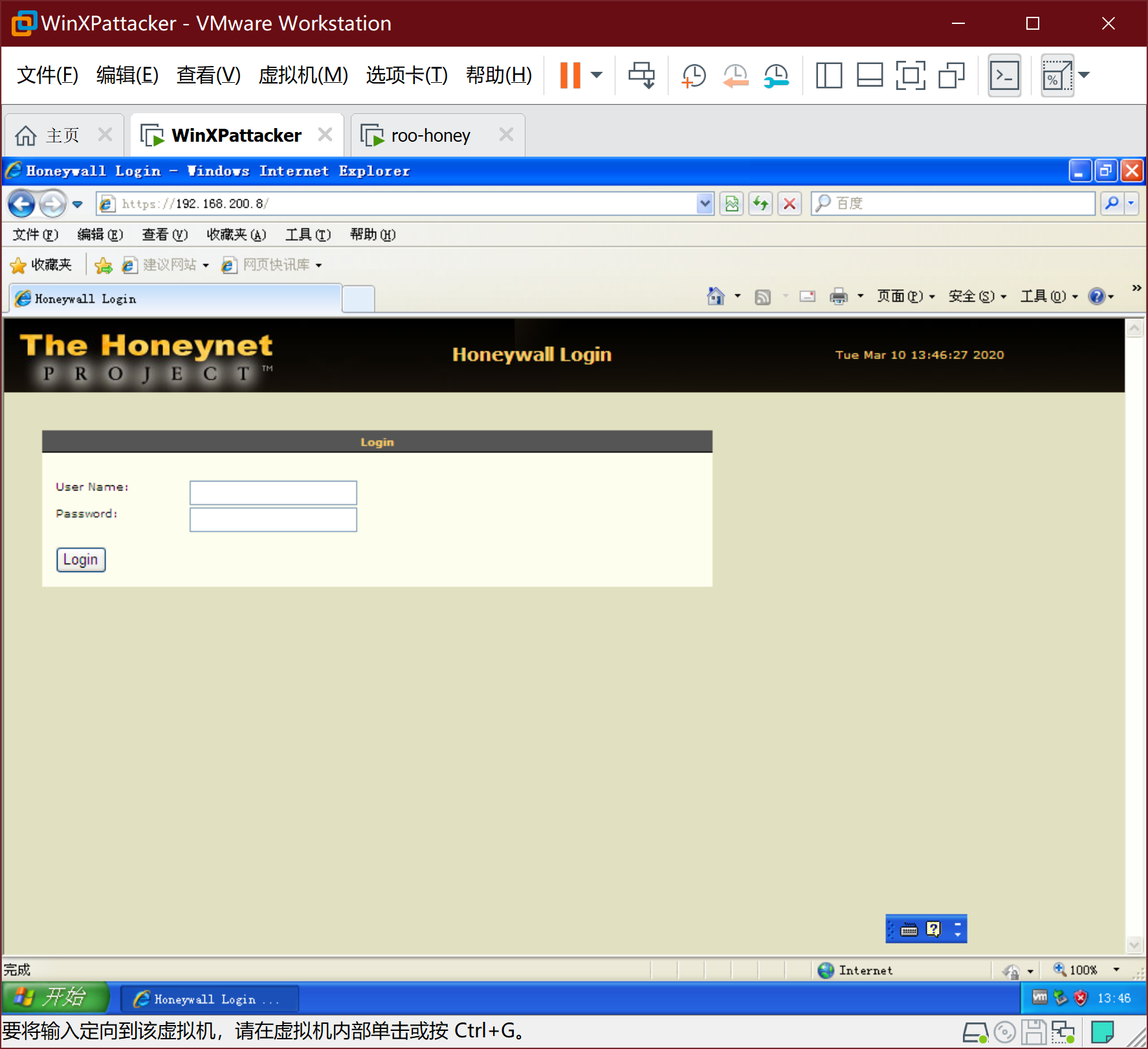
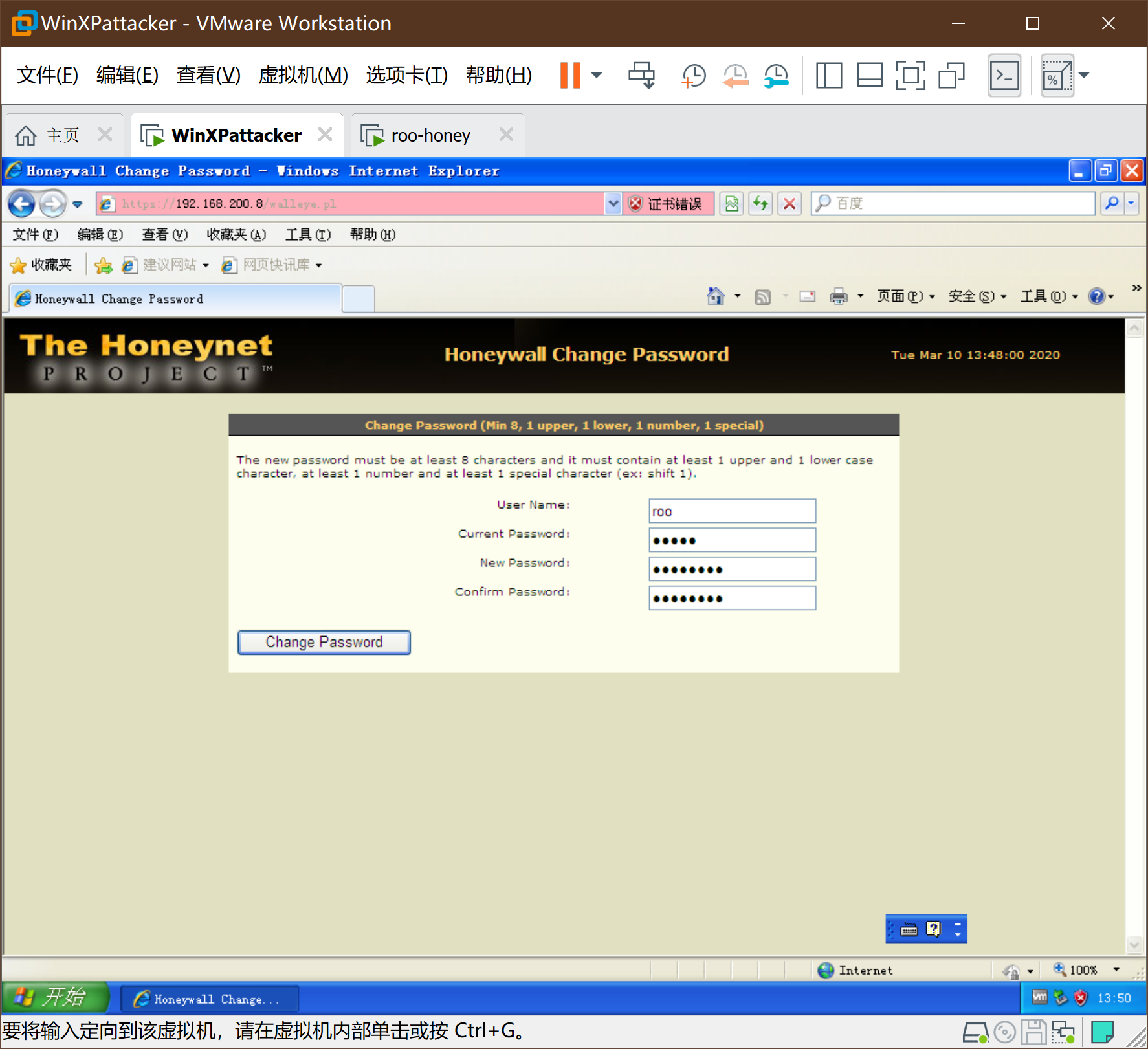
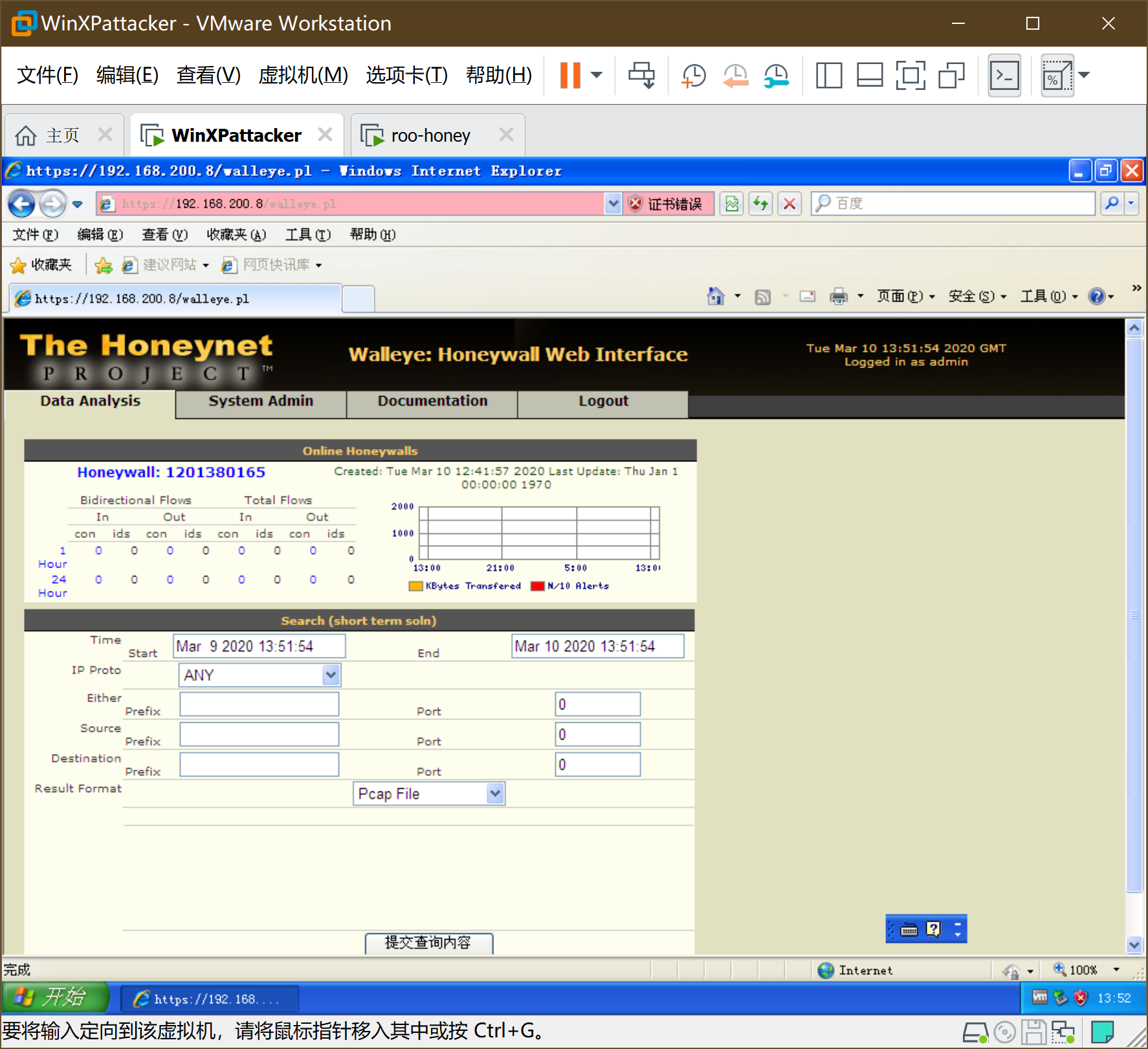
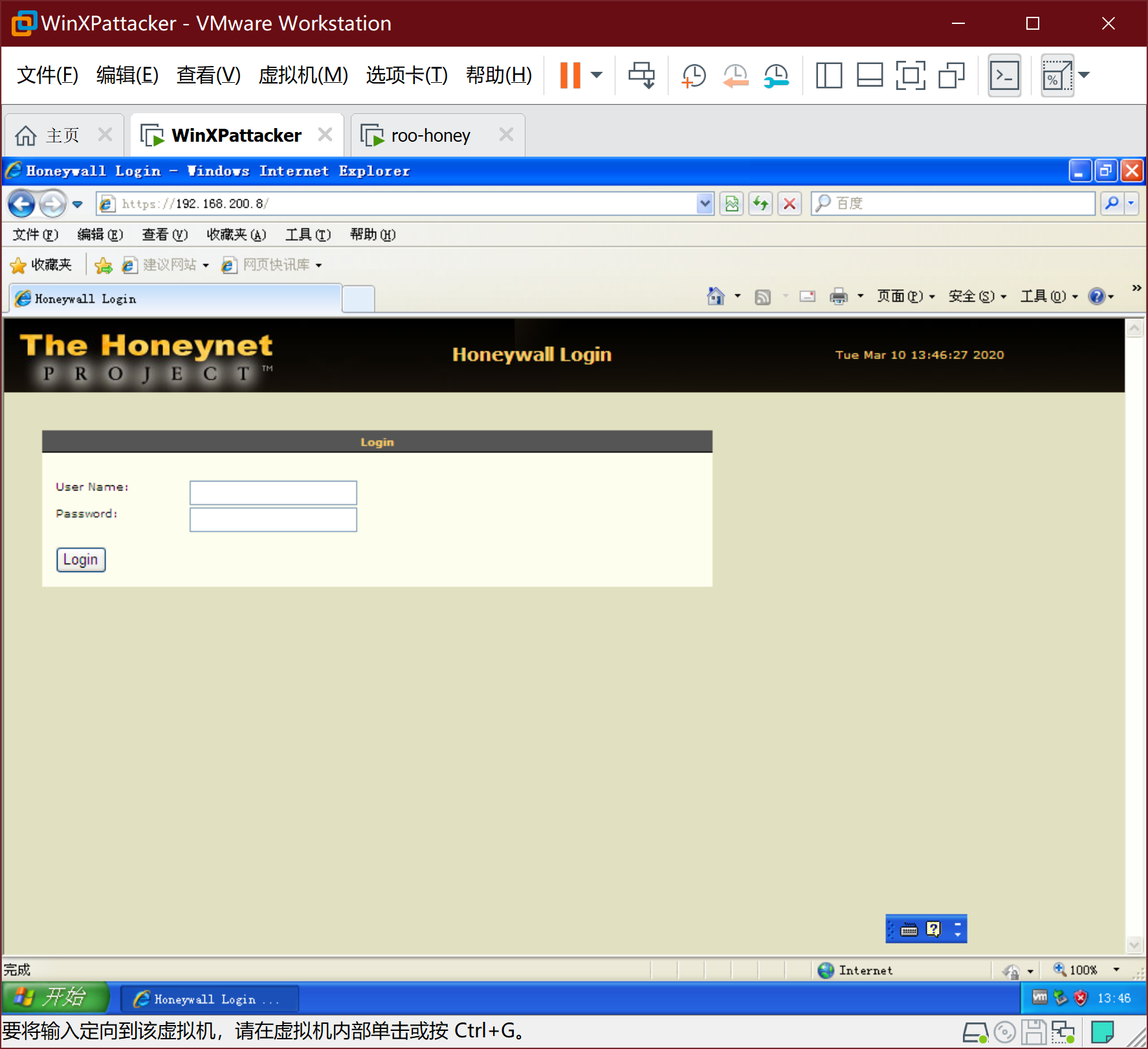
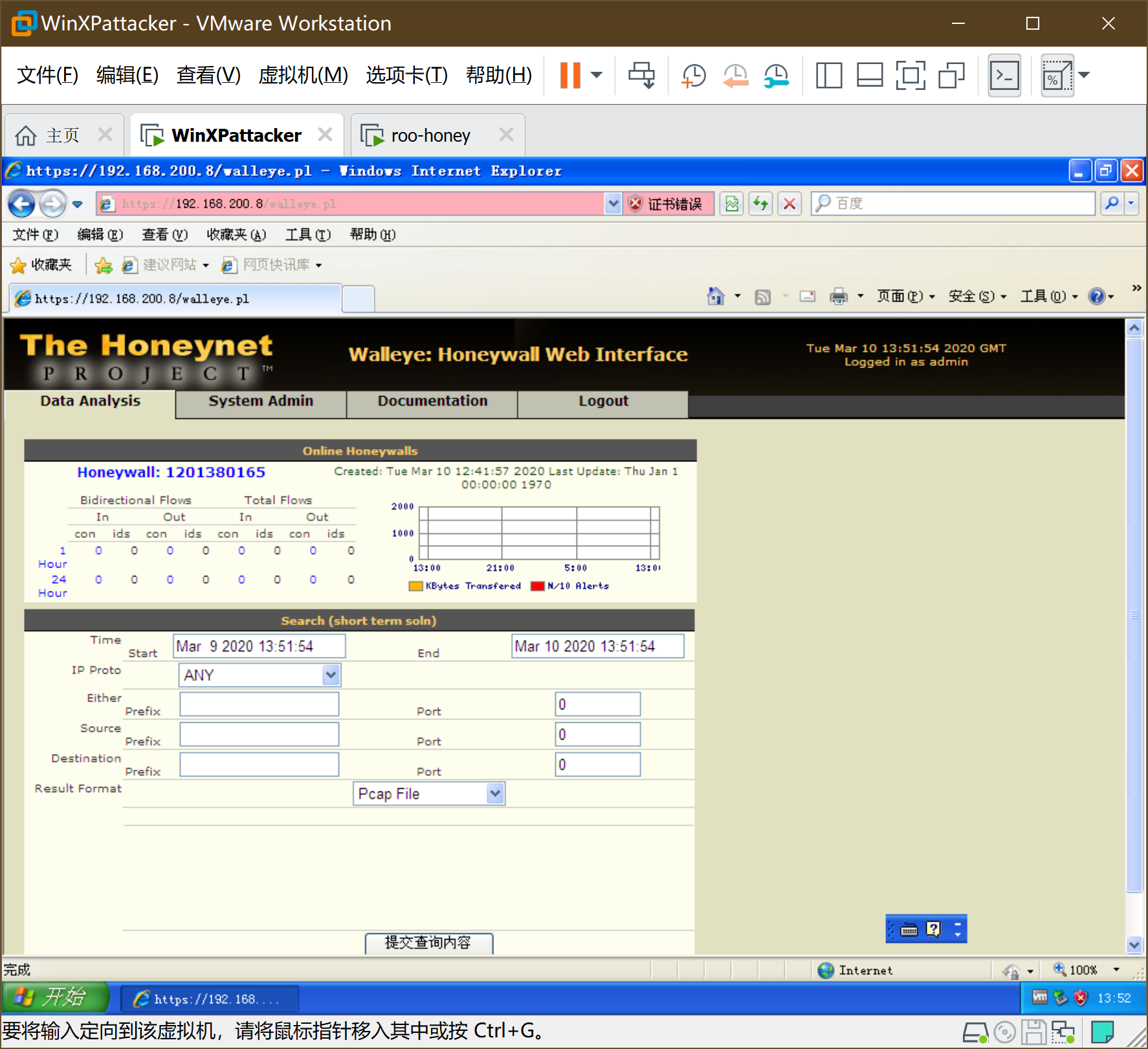
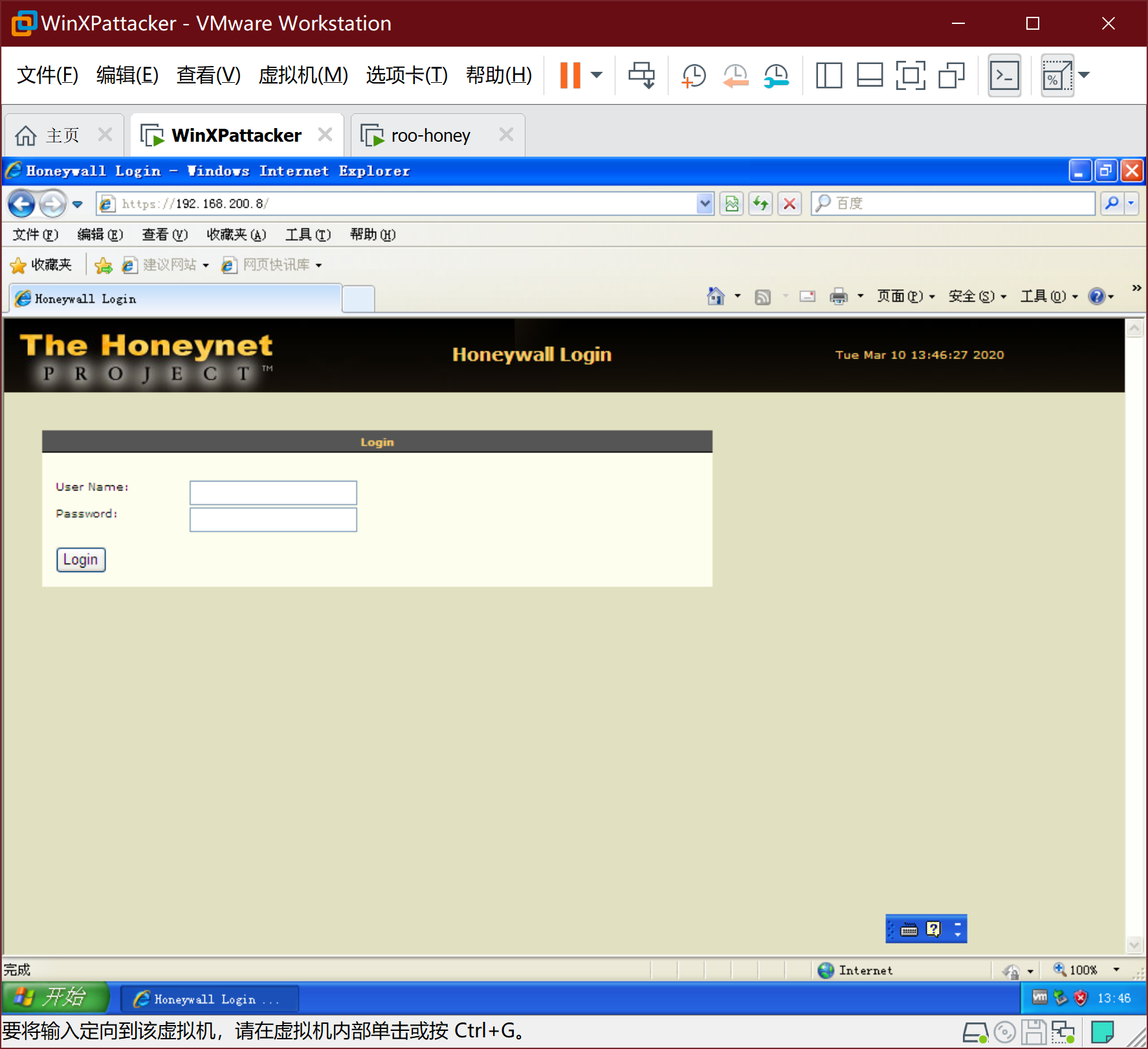
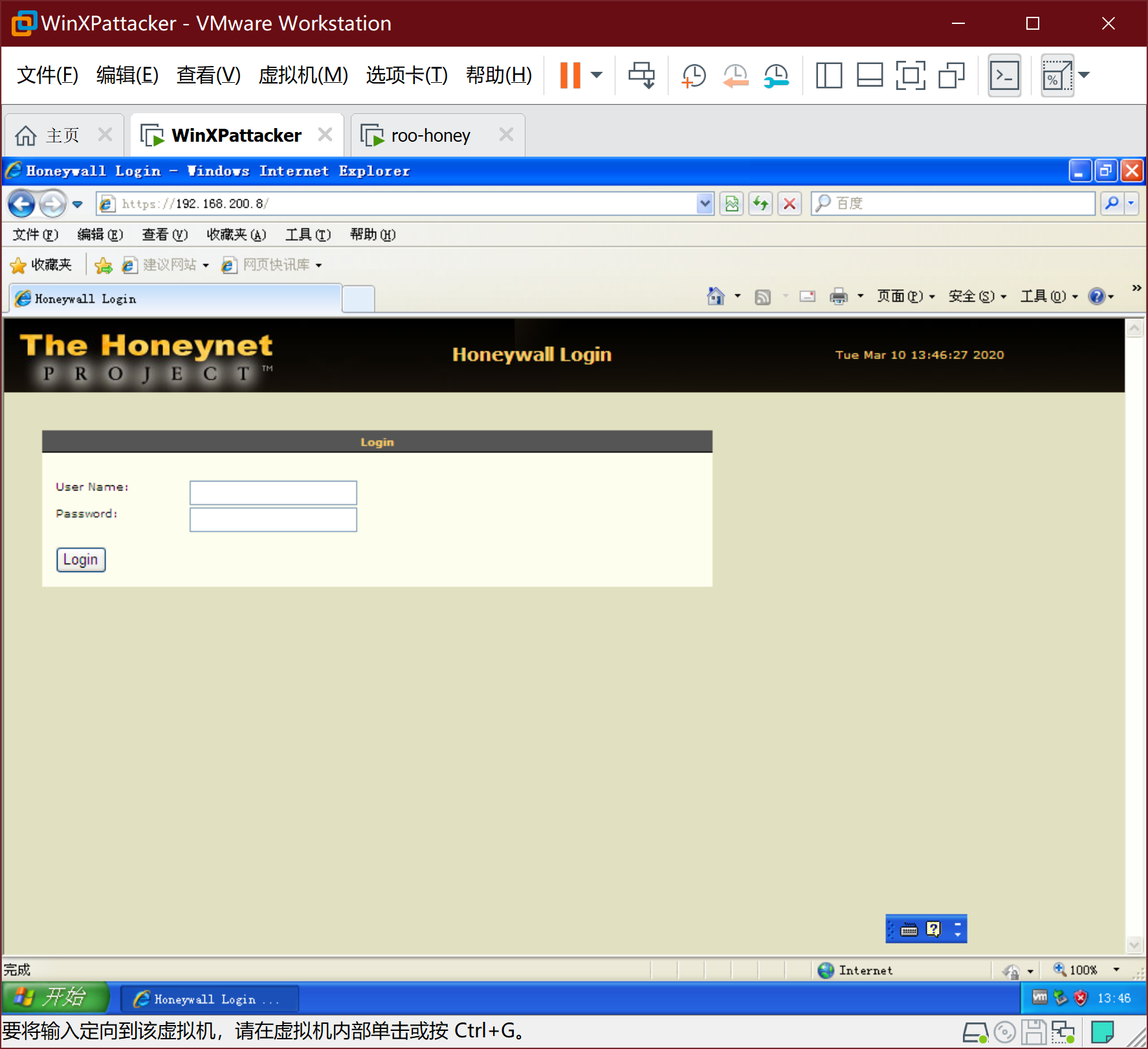
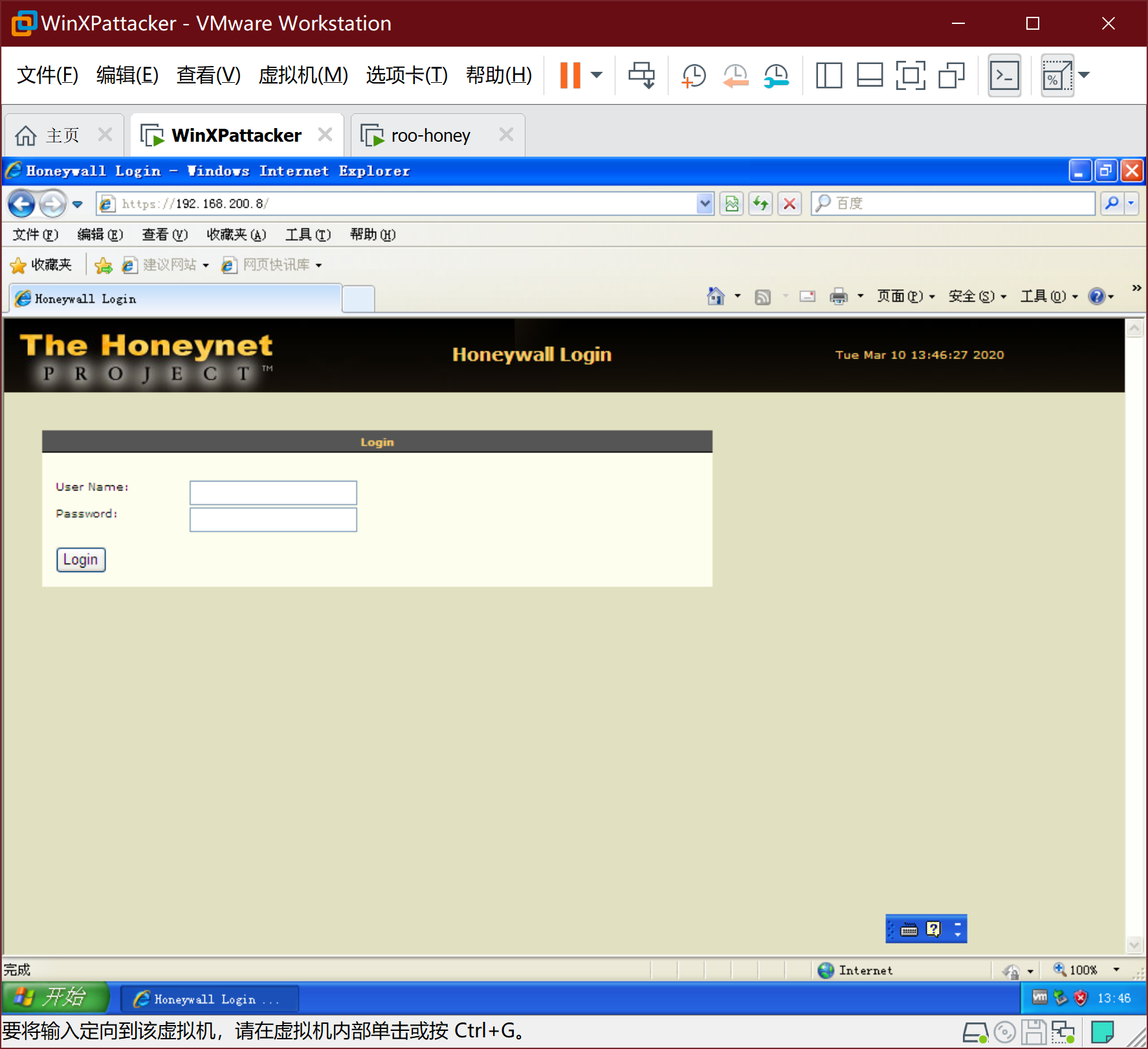
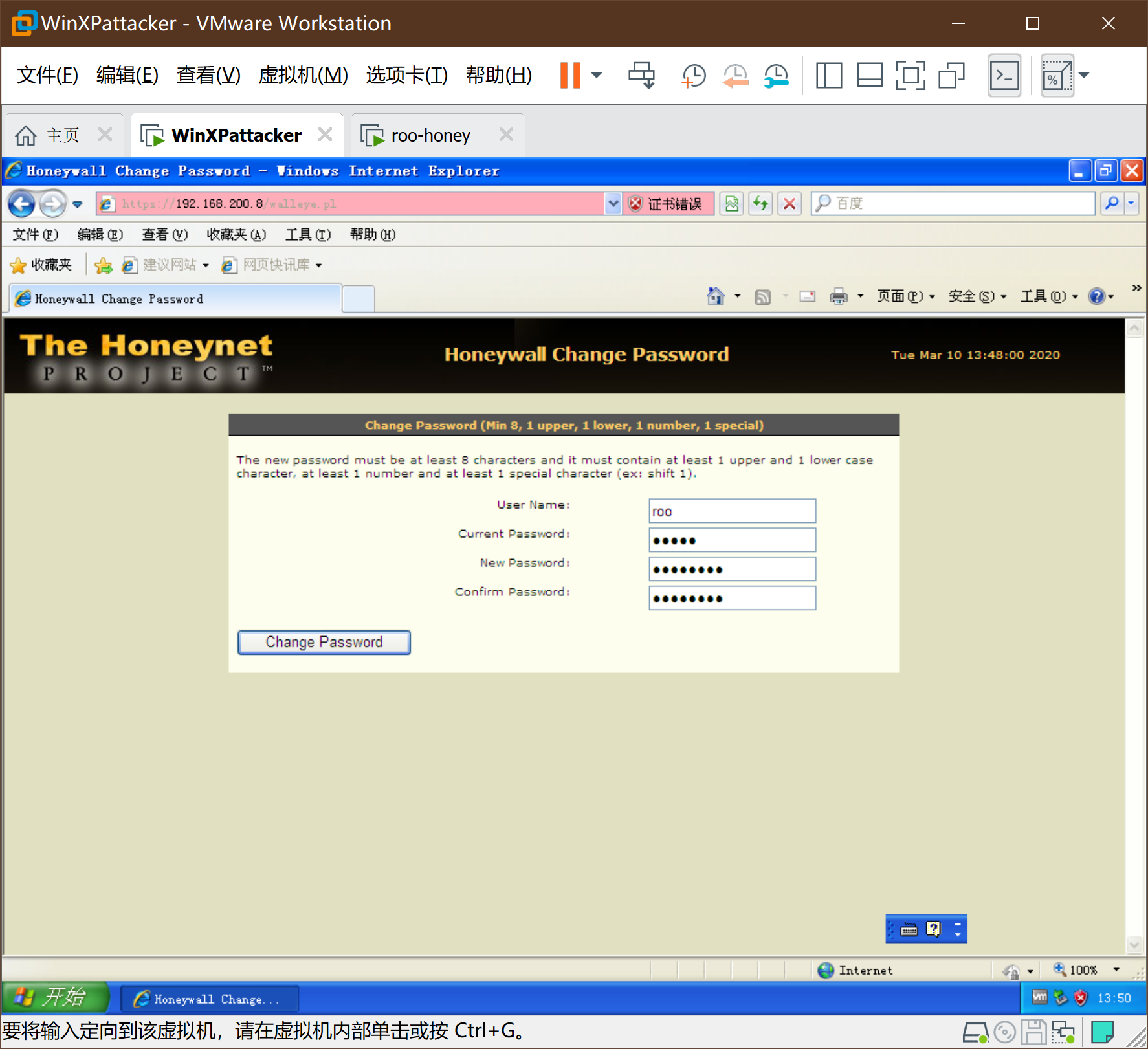
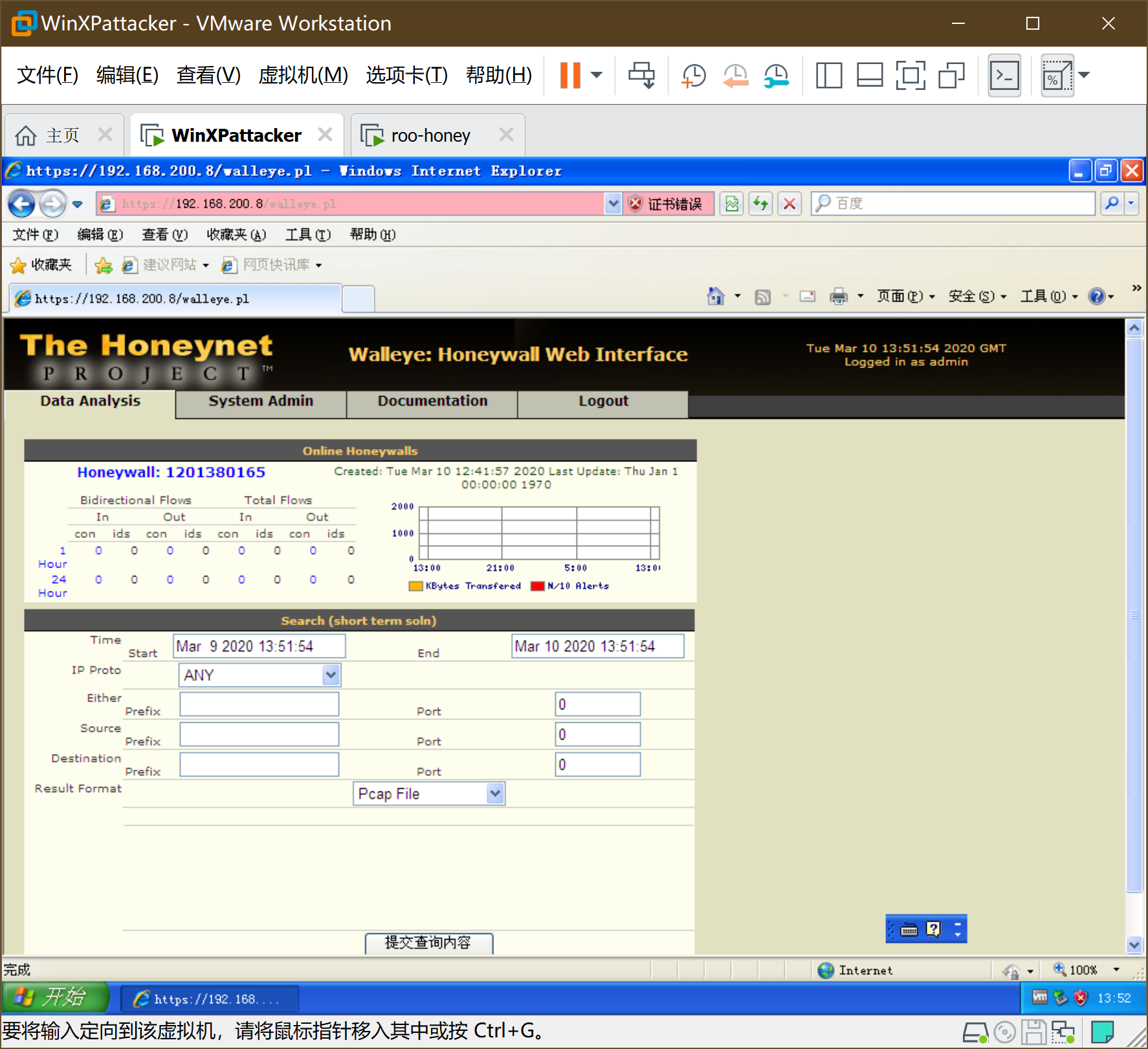
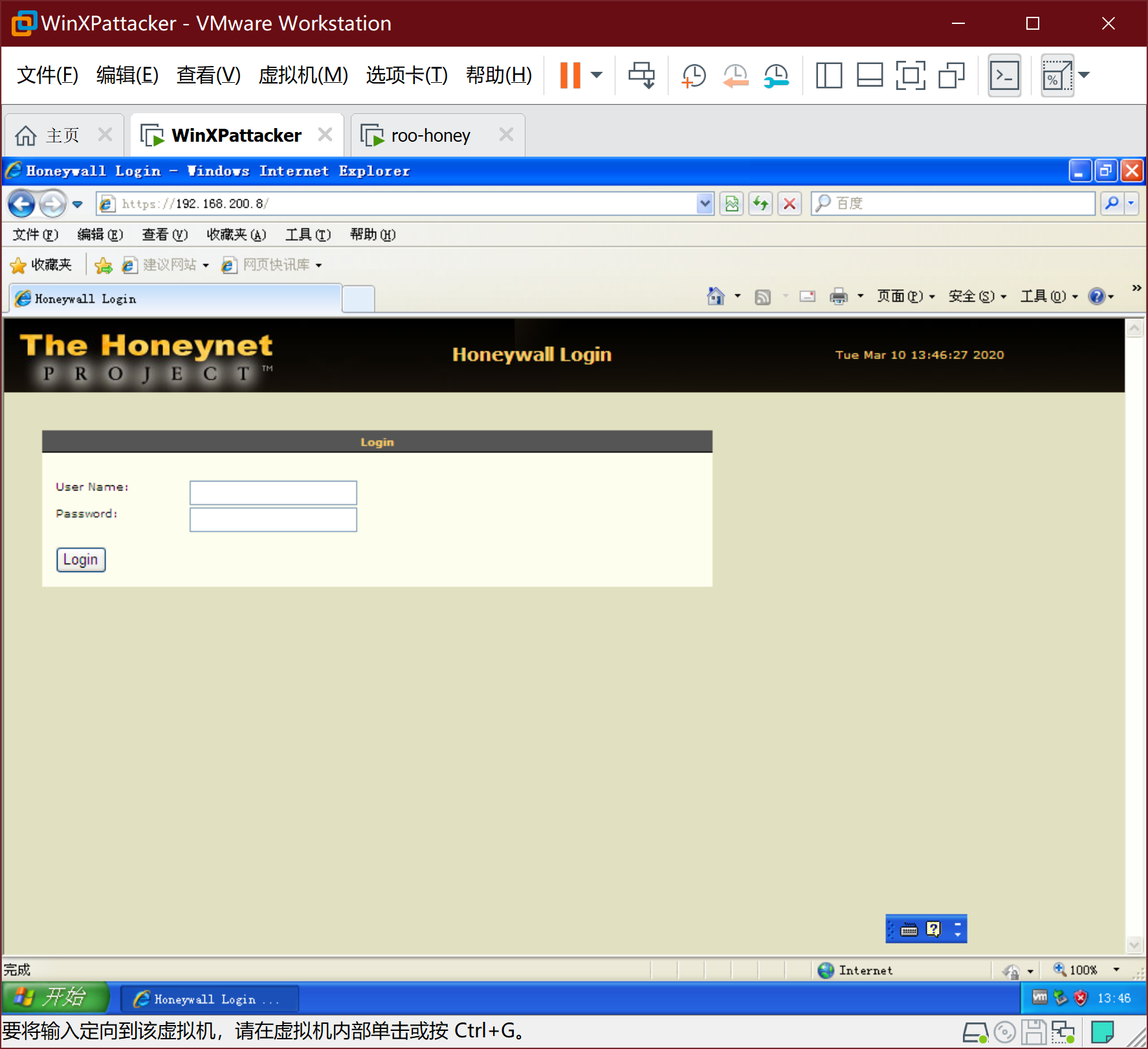
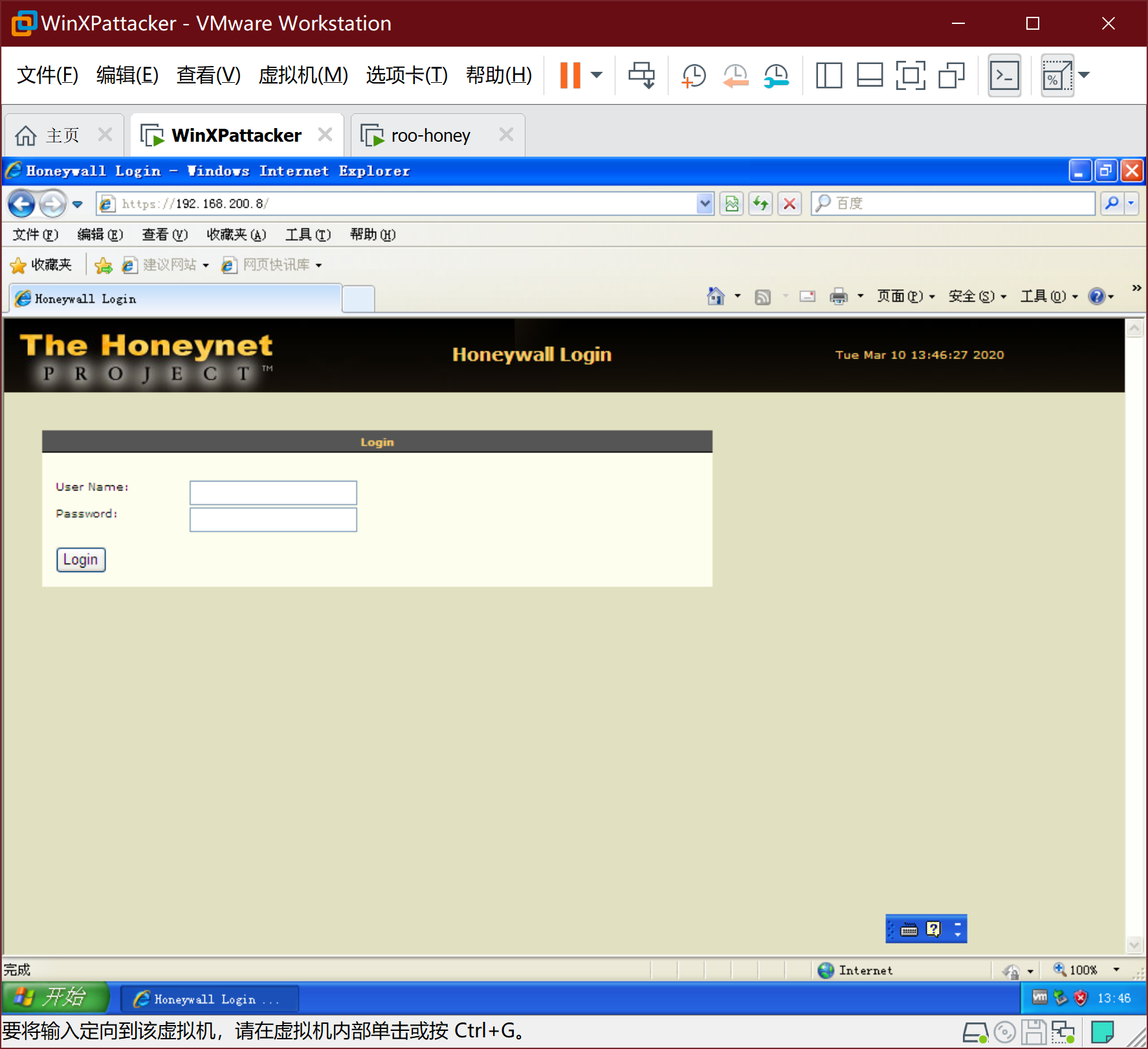
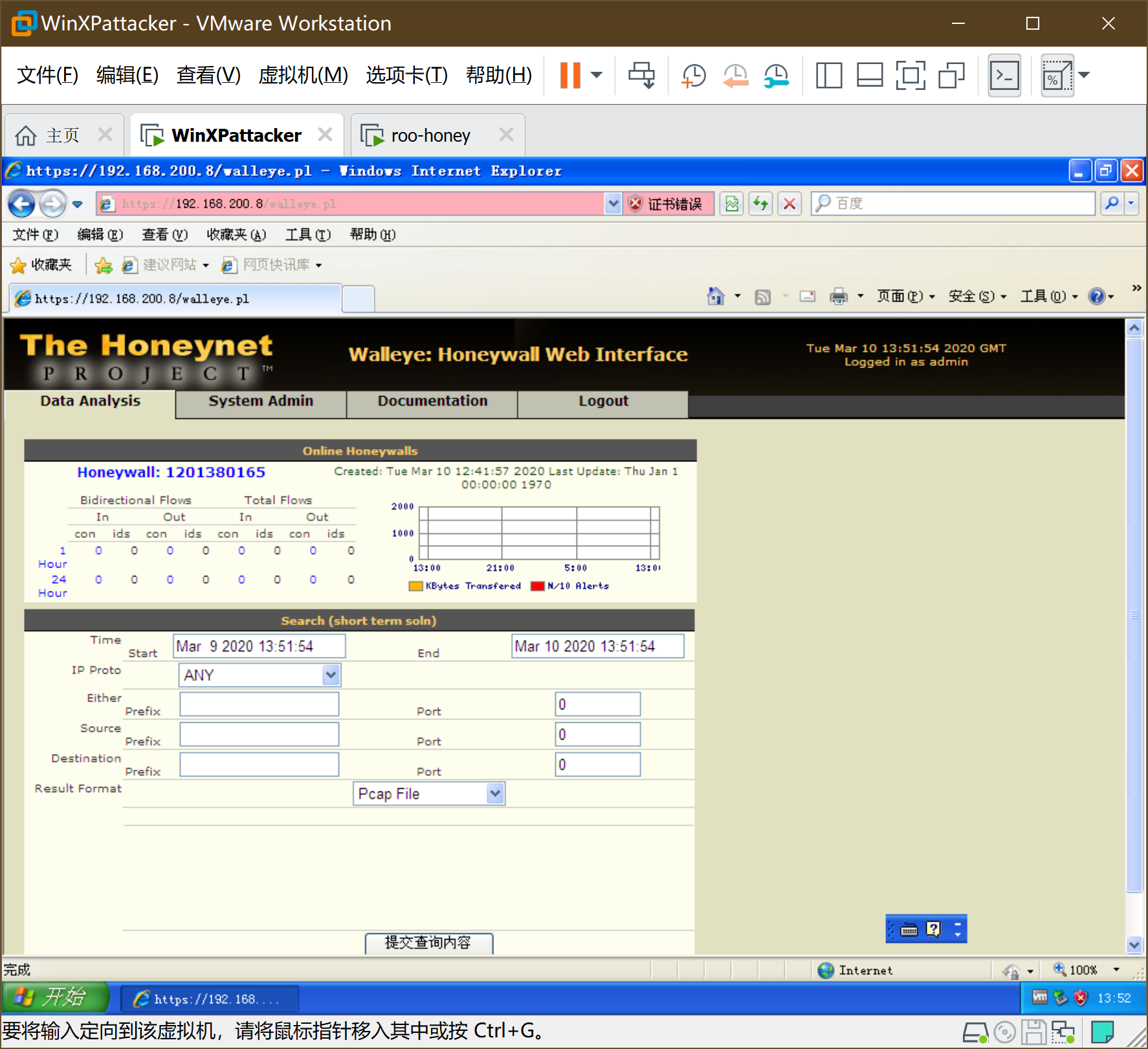
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
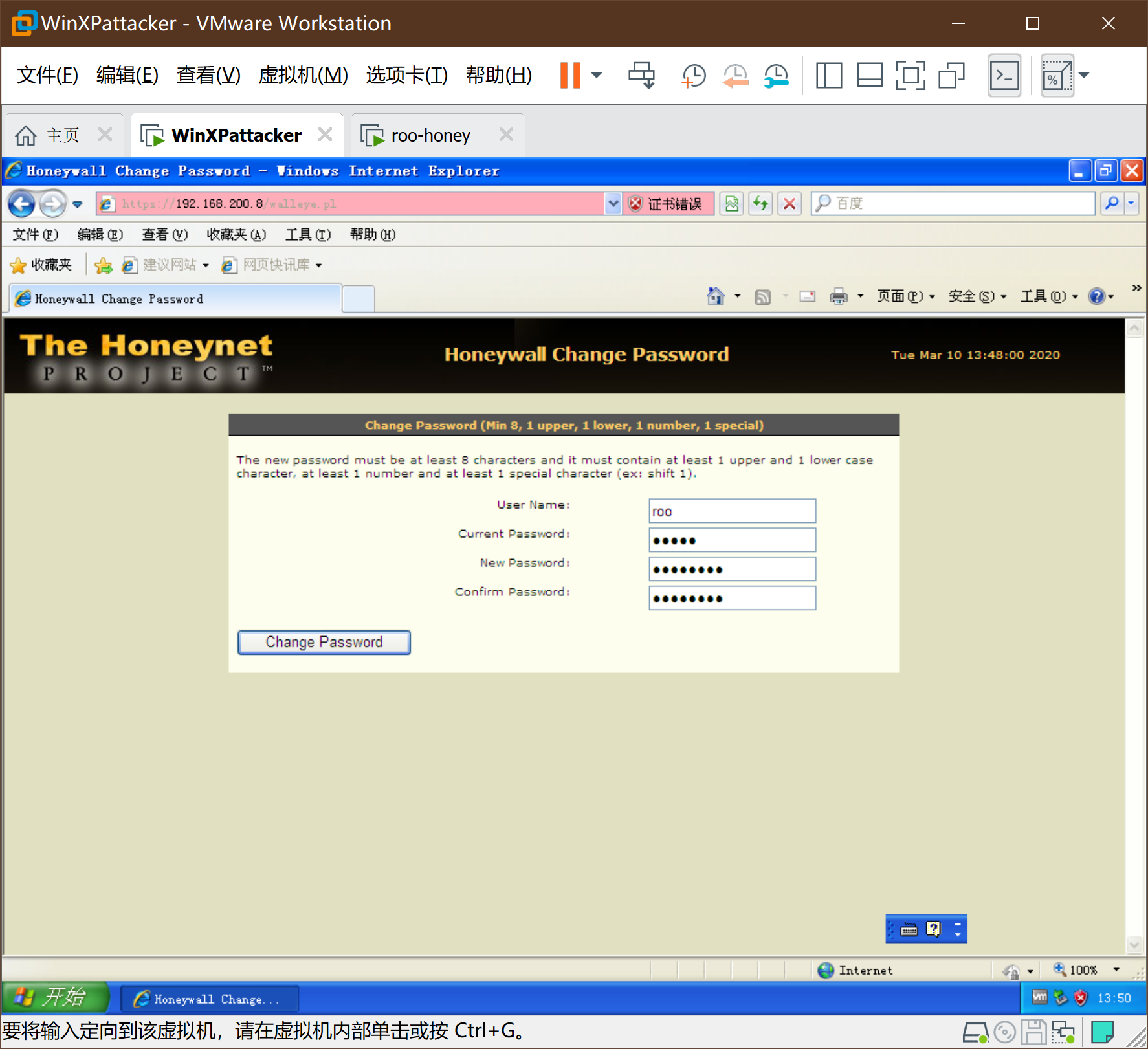
-
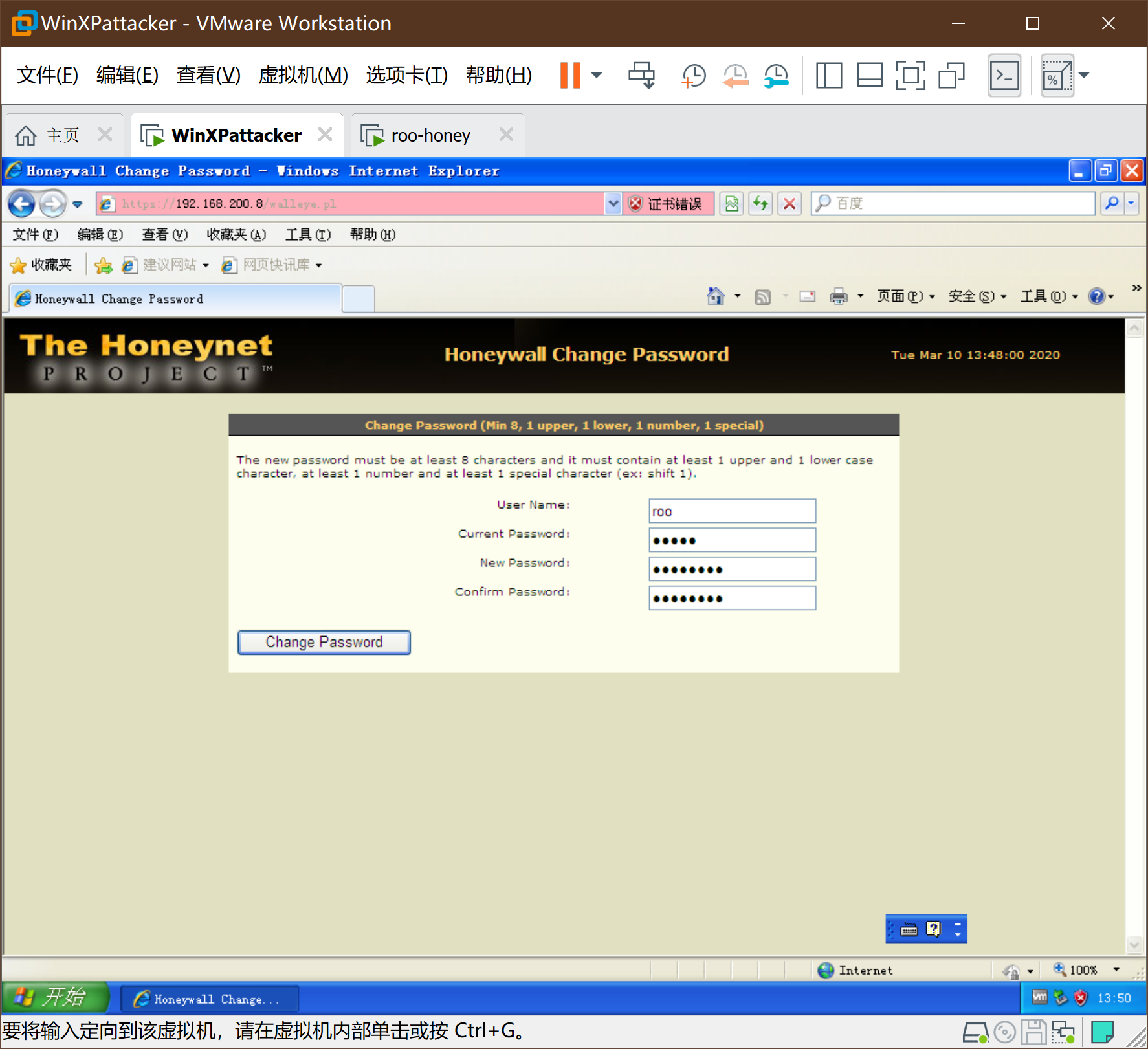
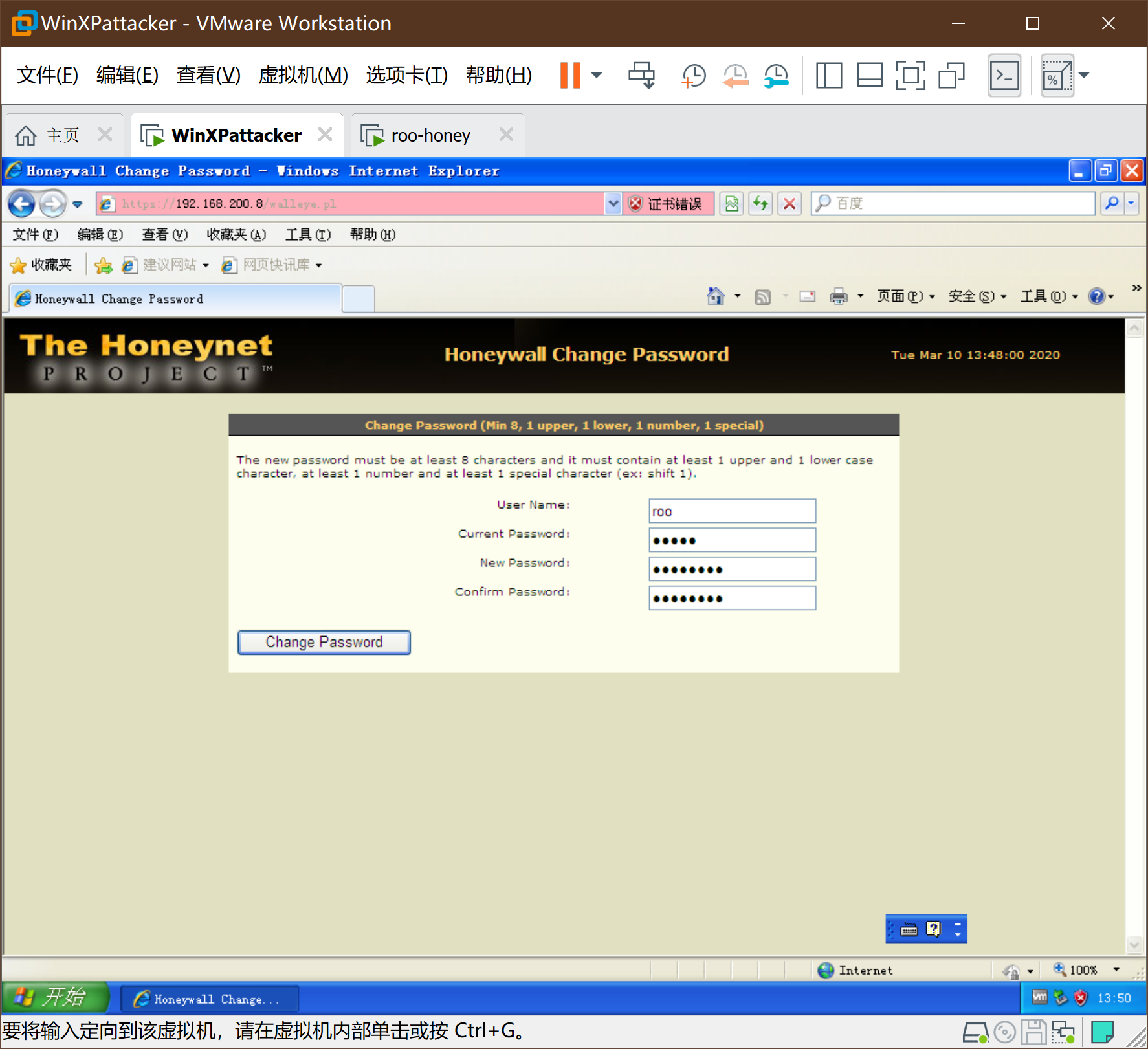
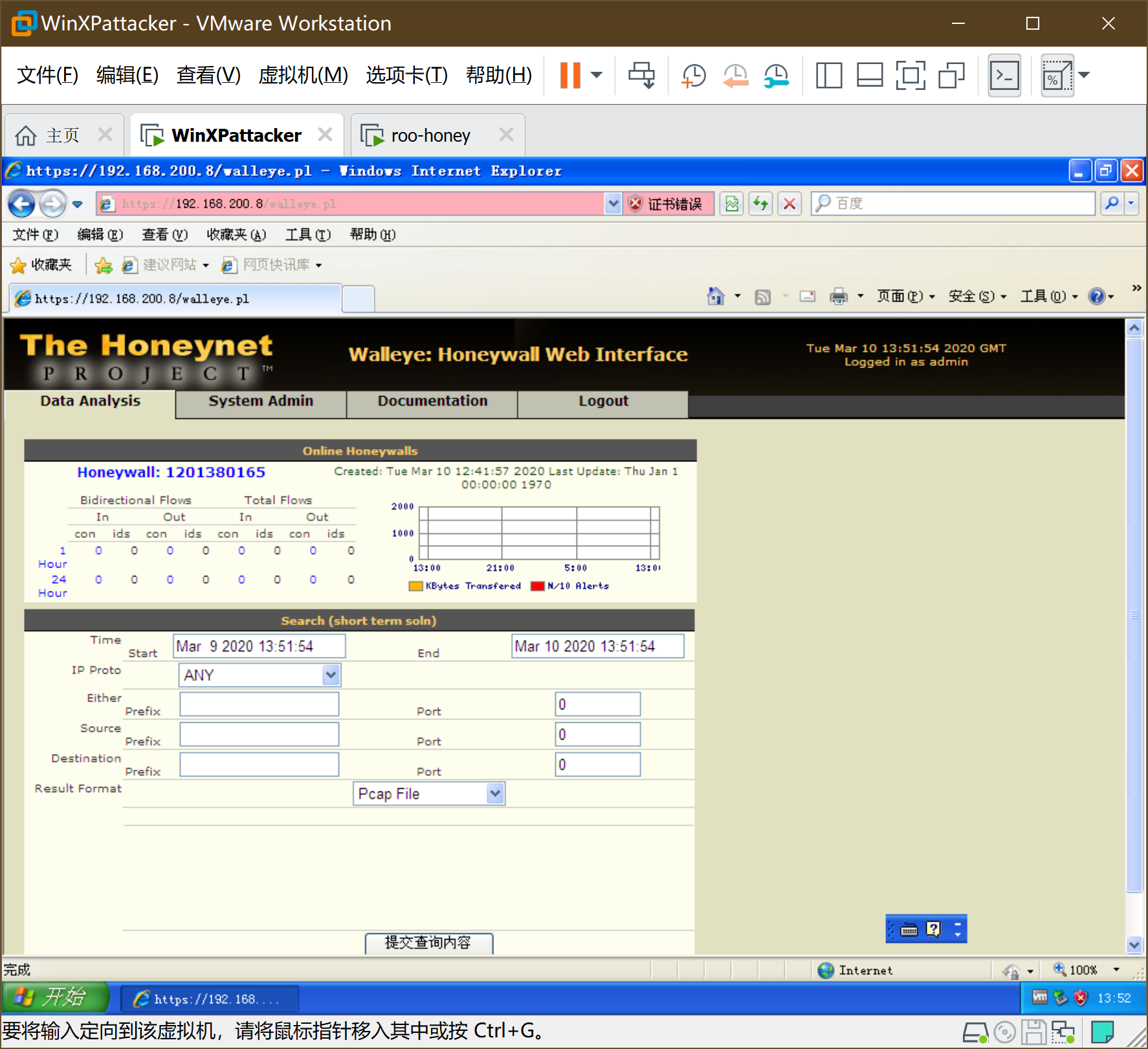
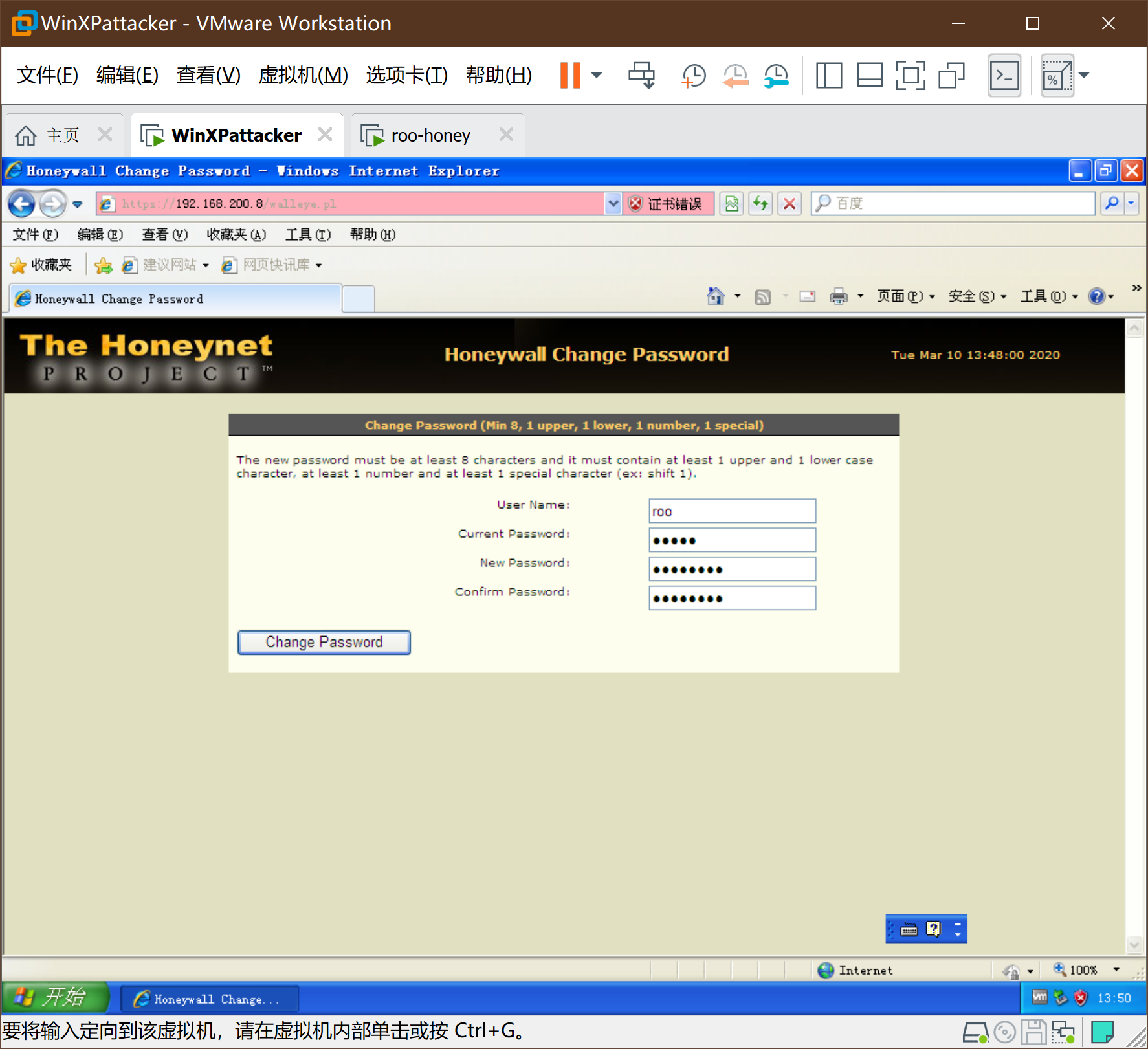
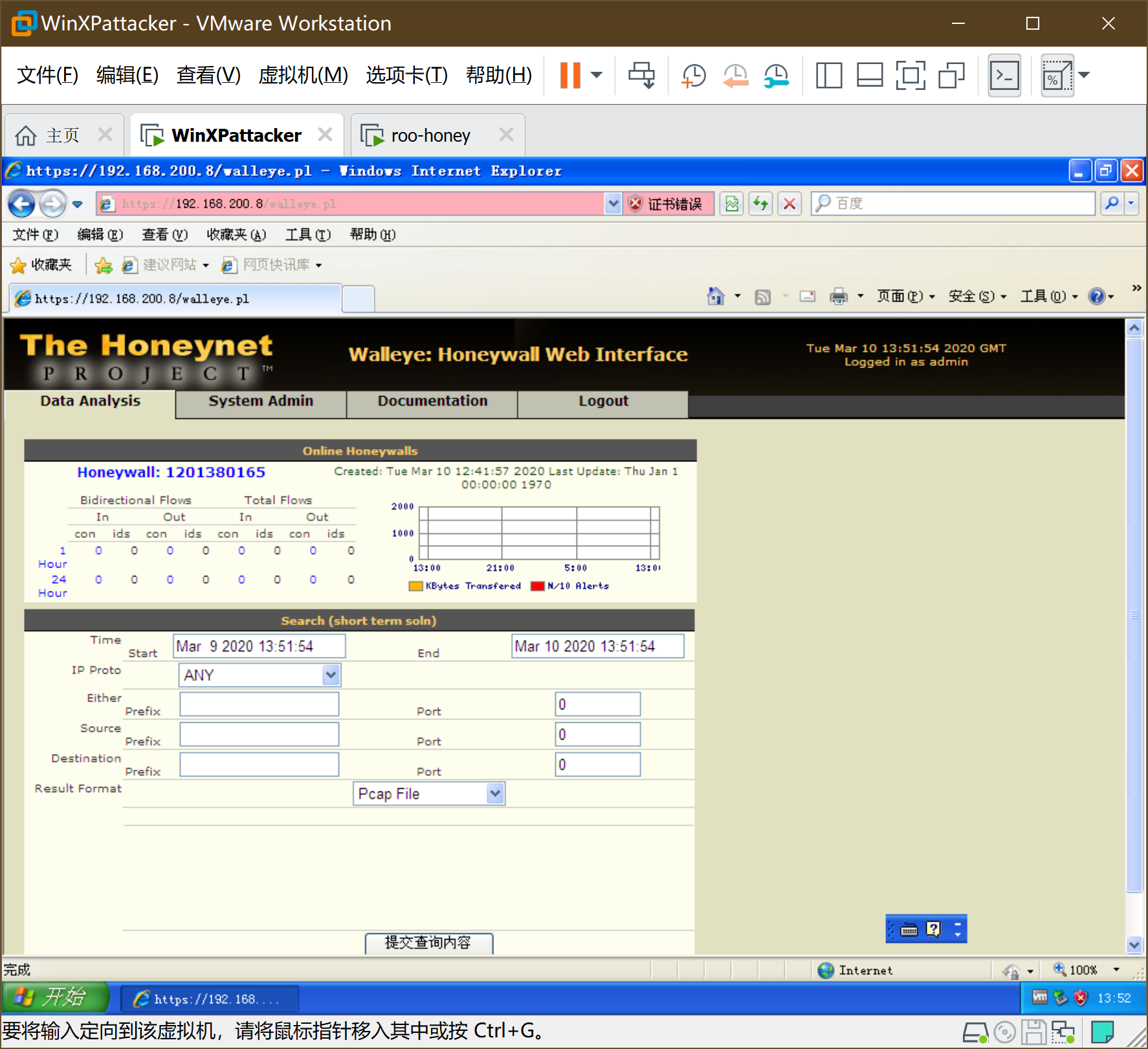
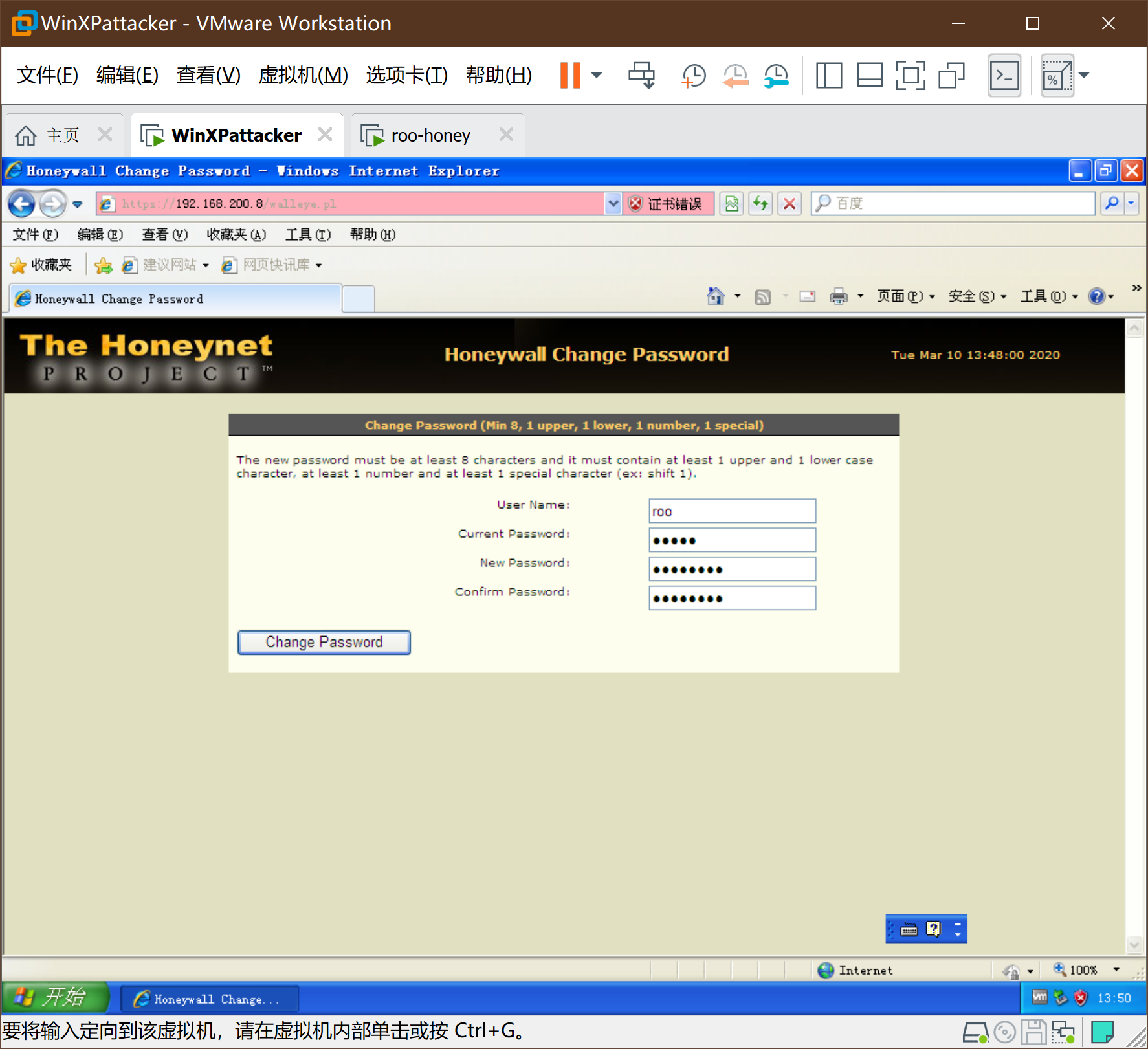
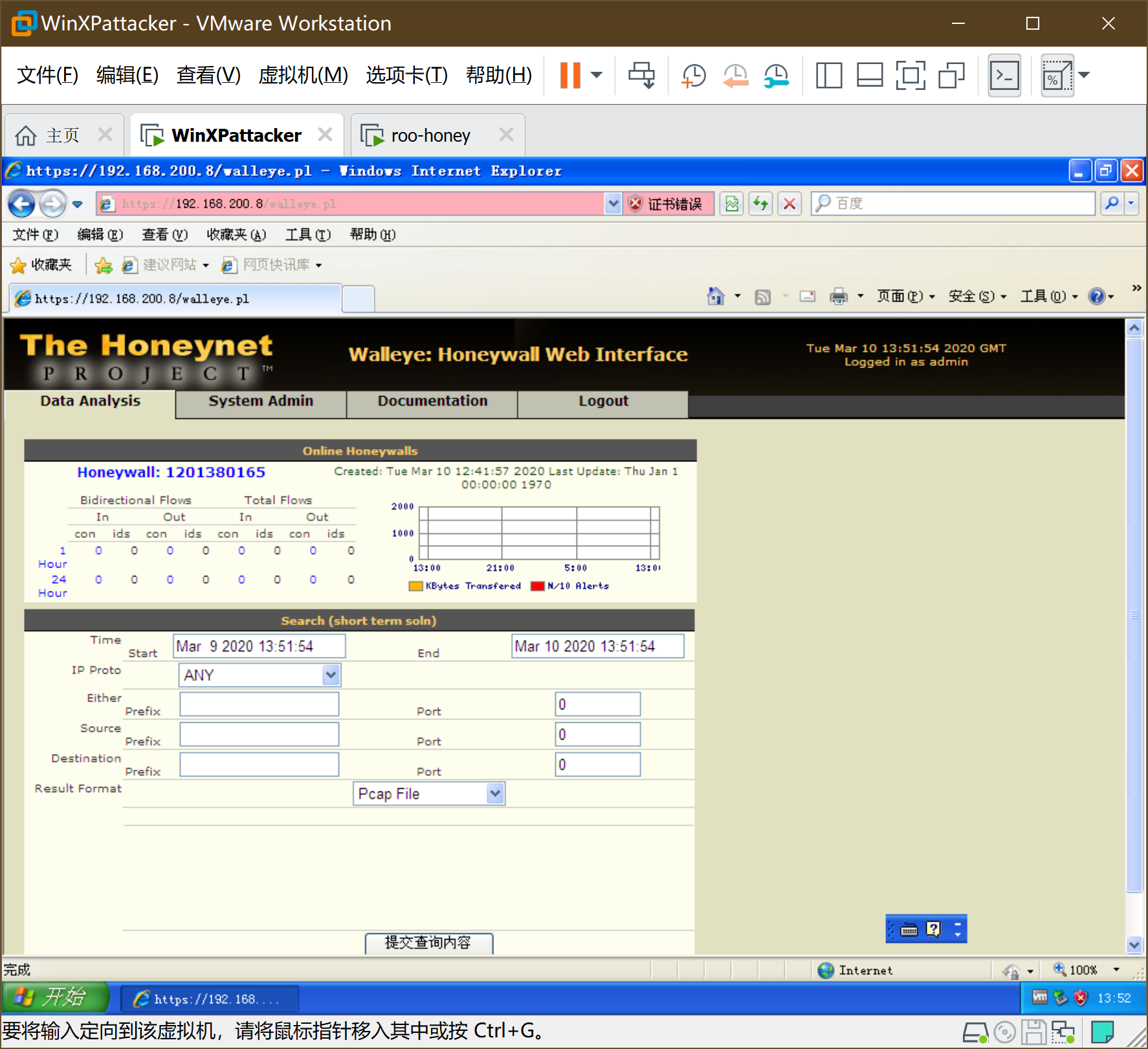
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
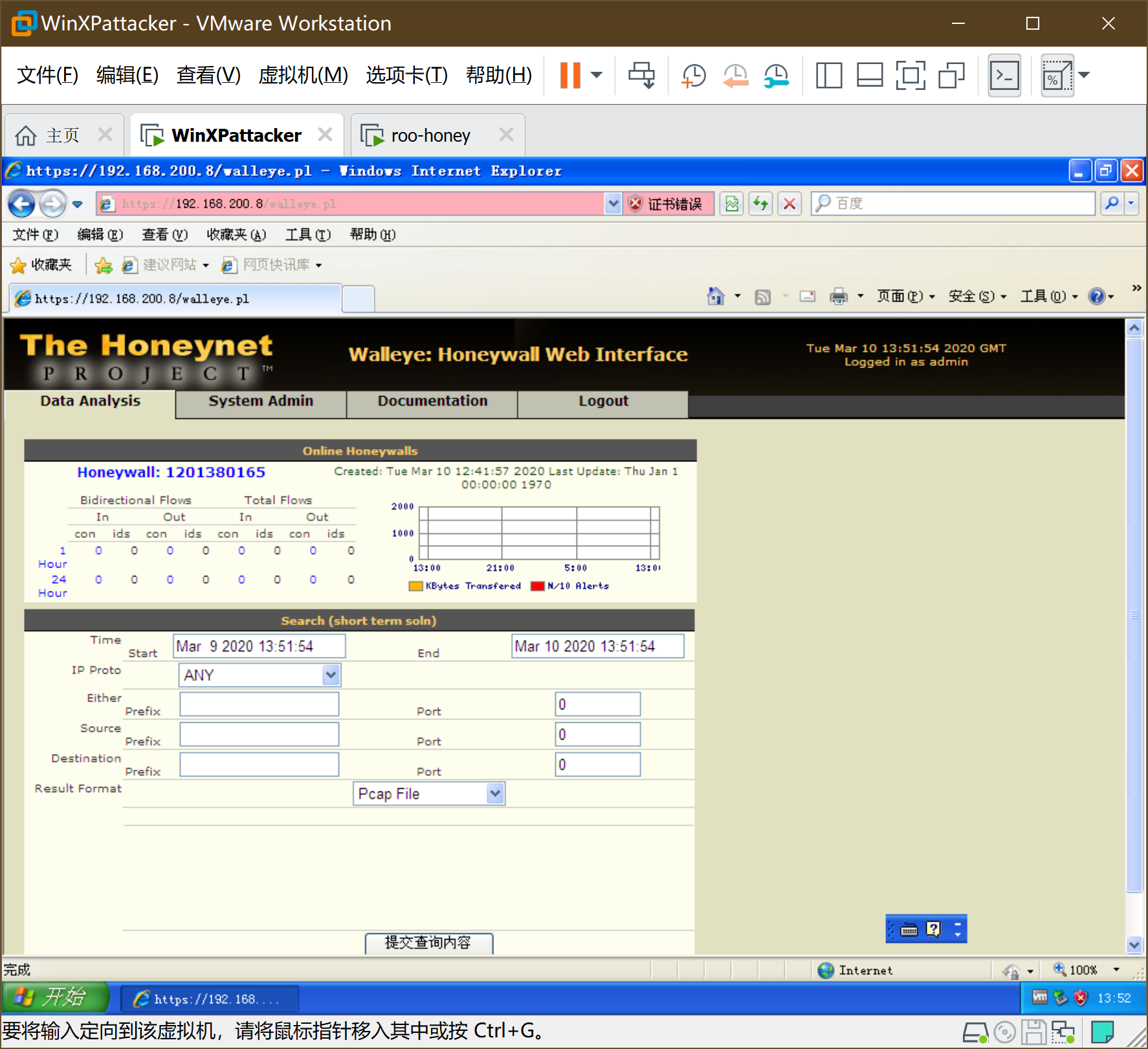
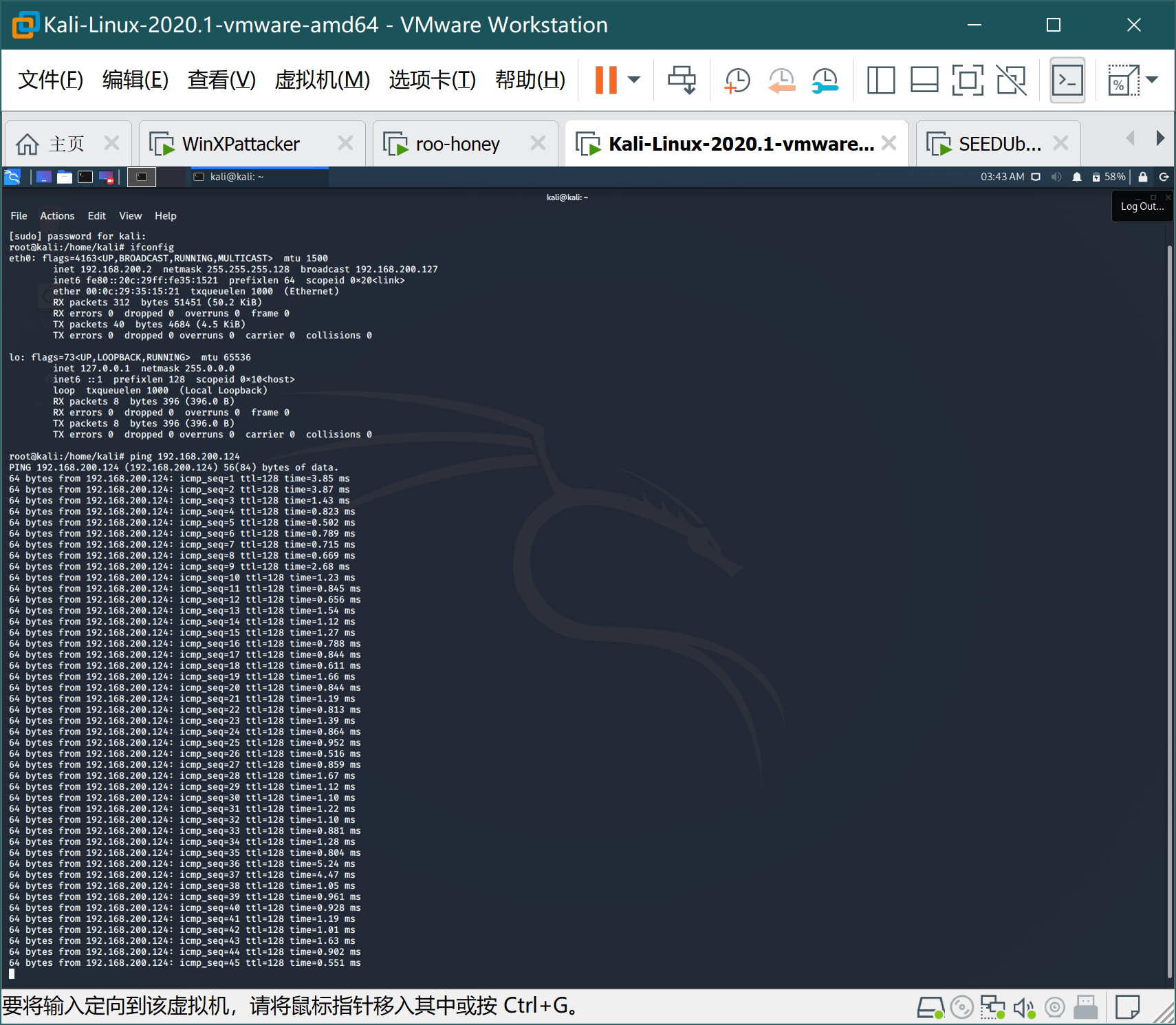
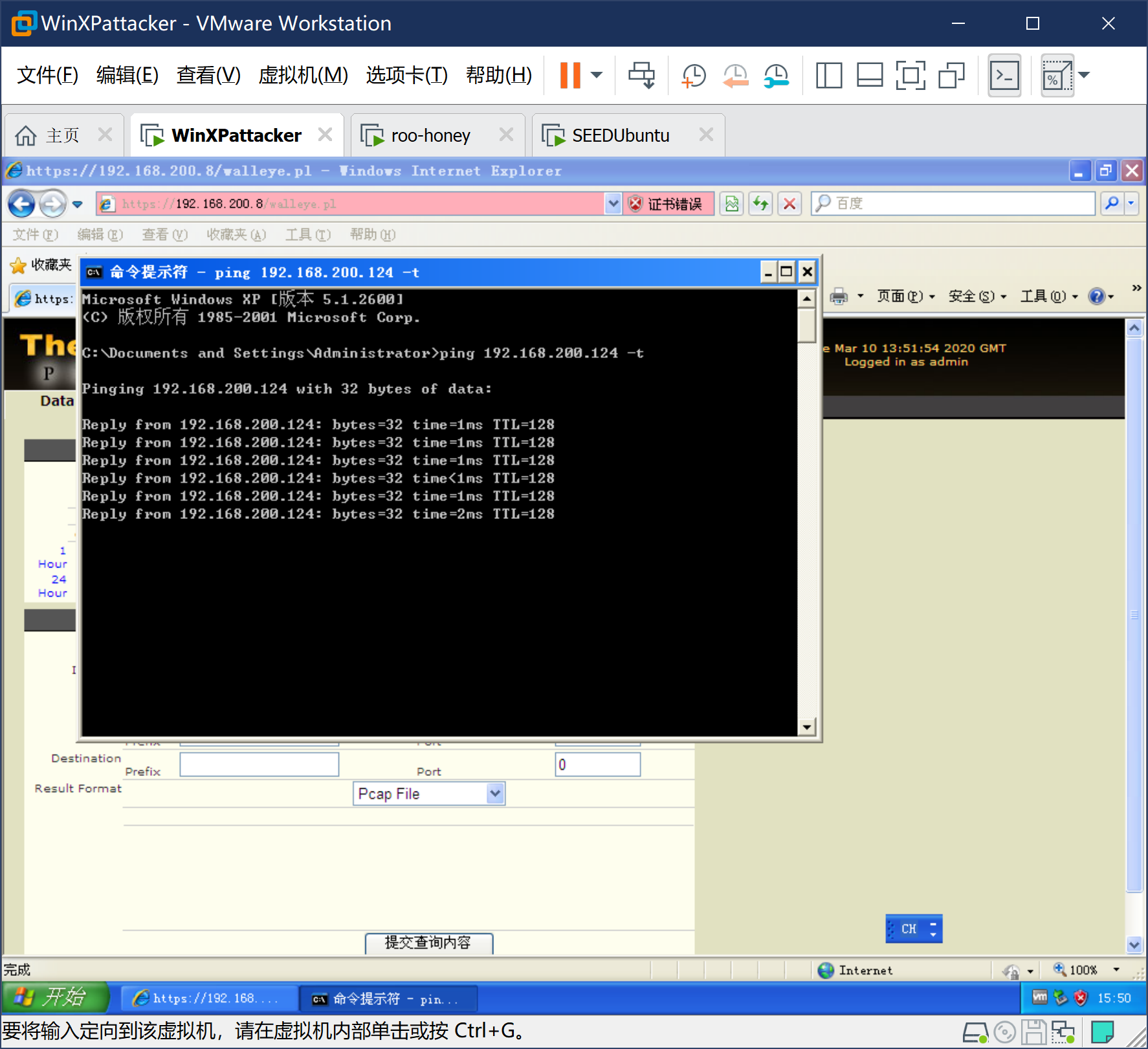
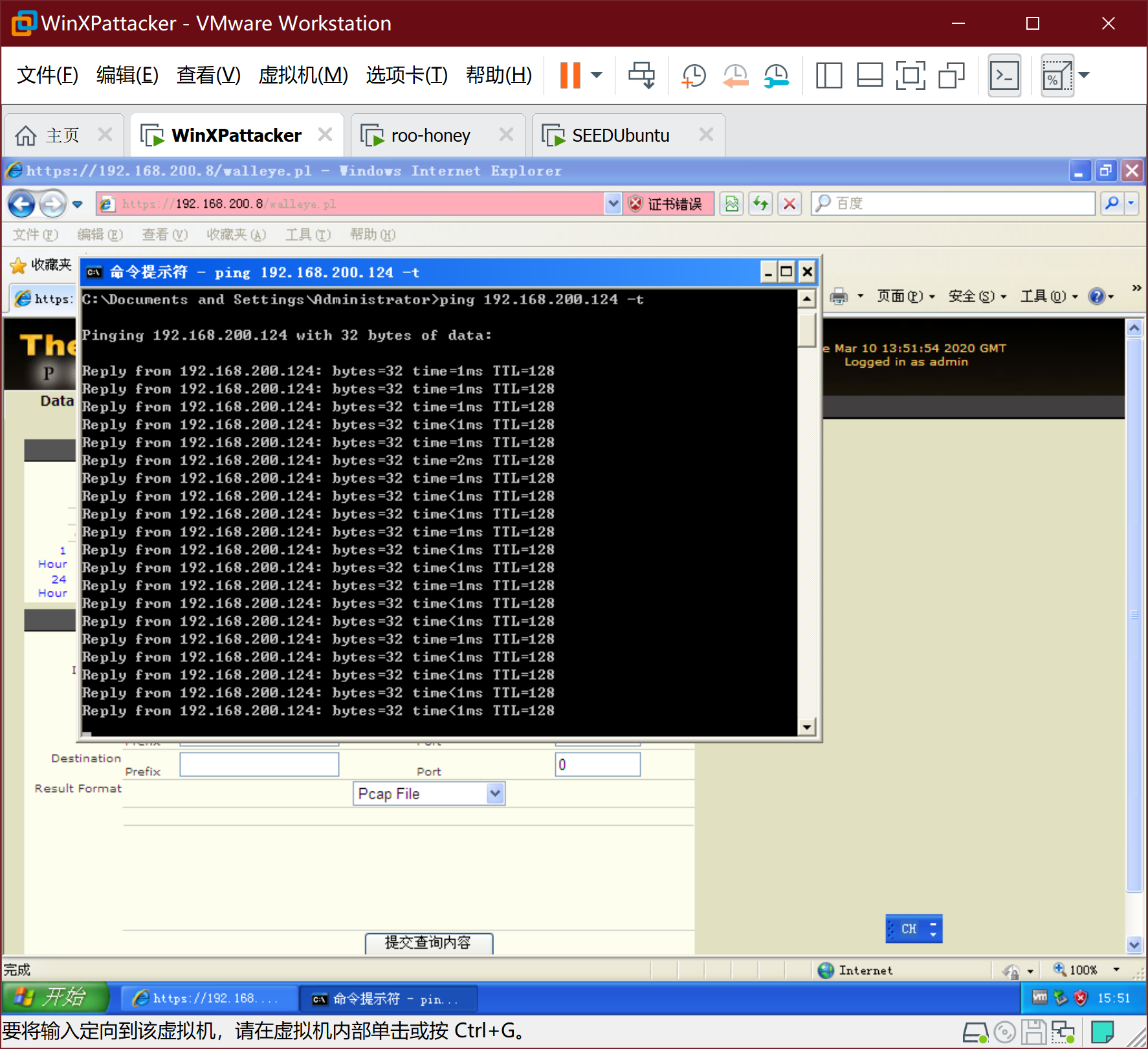
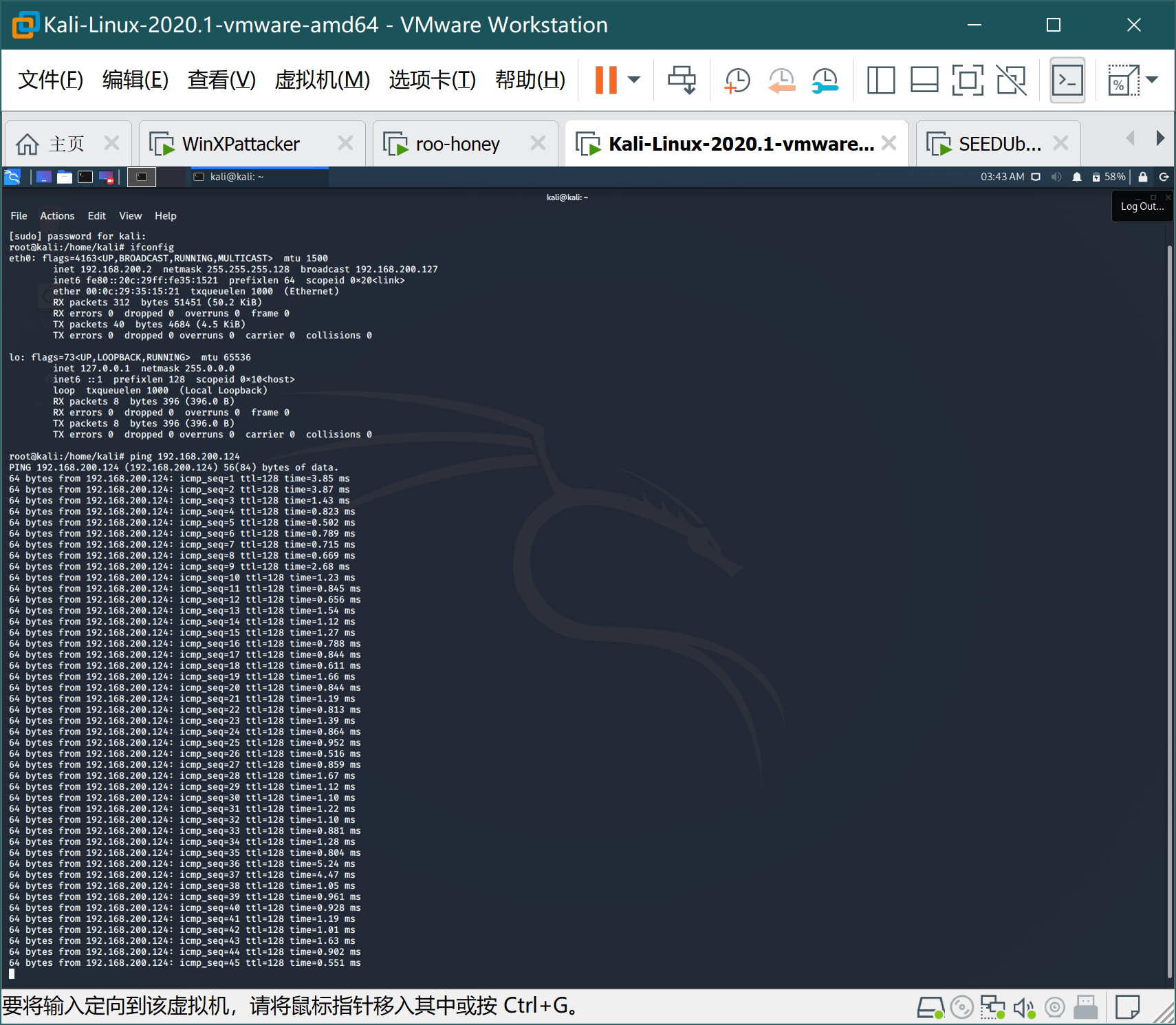
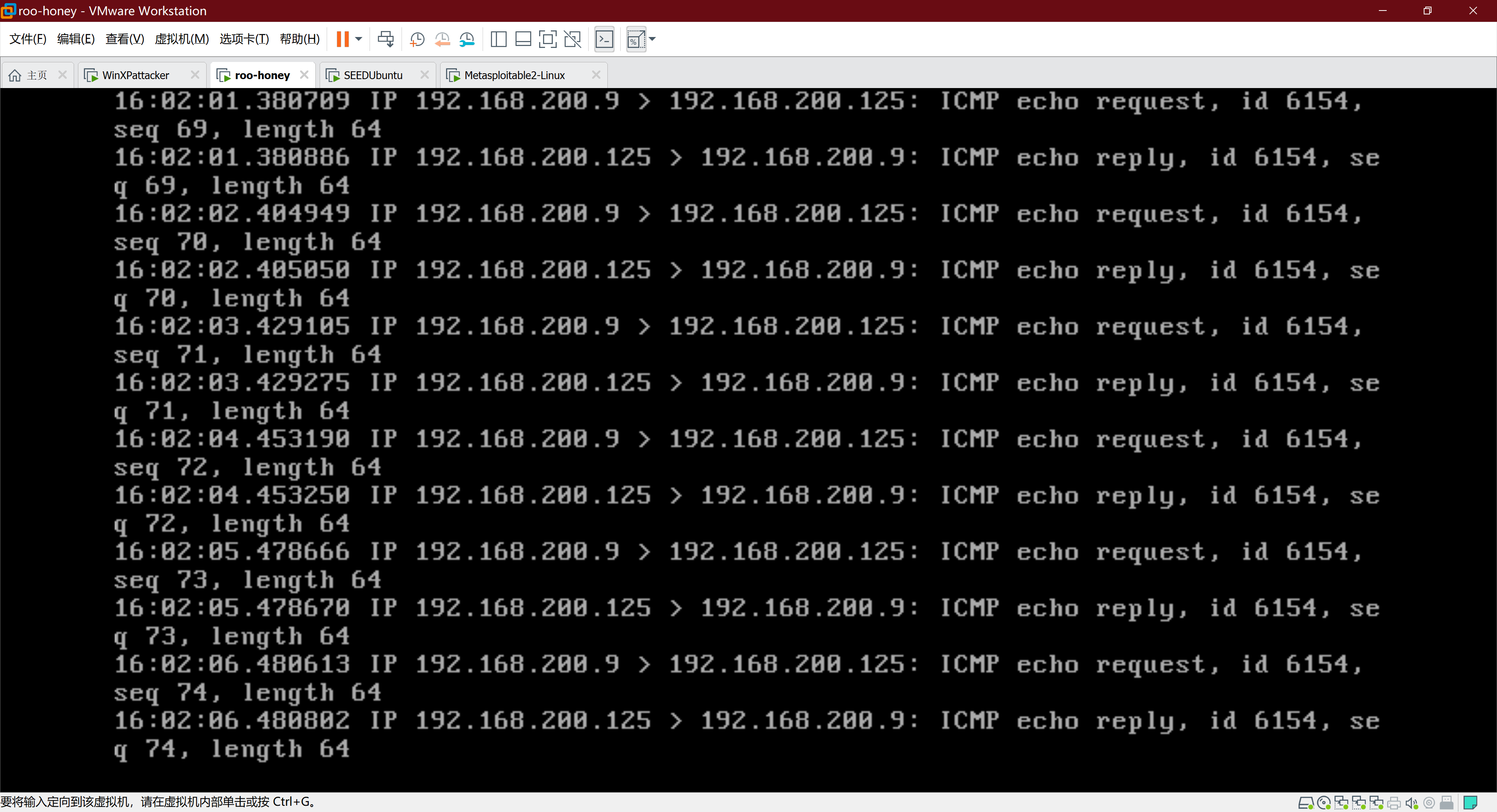
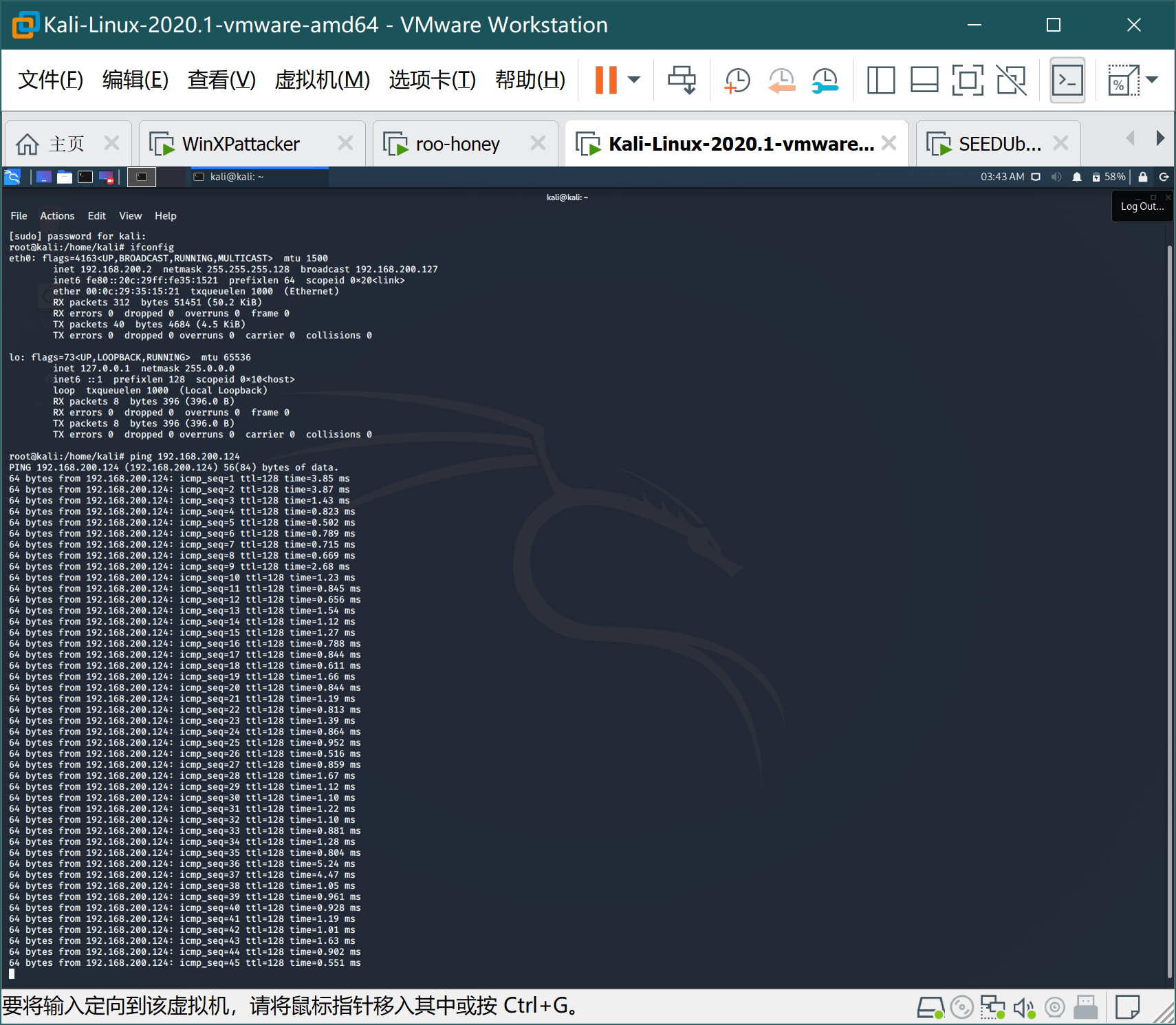
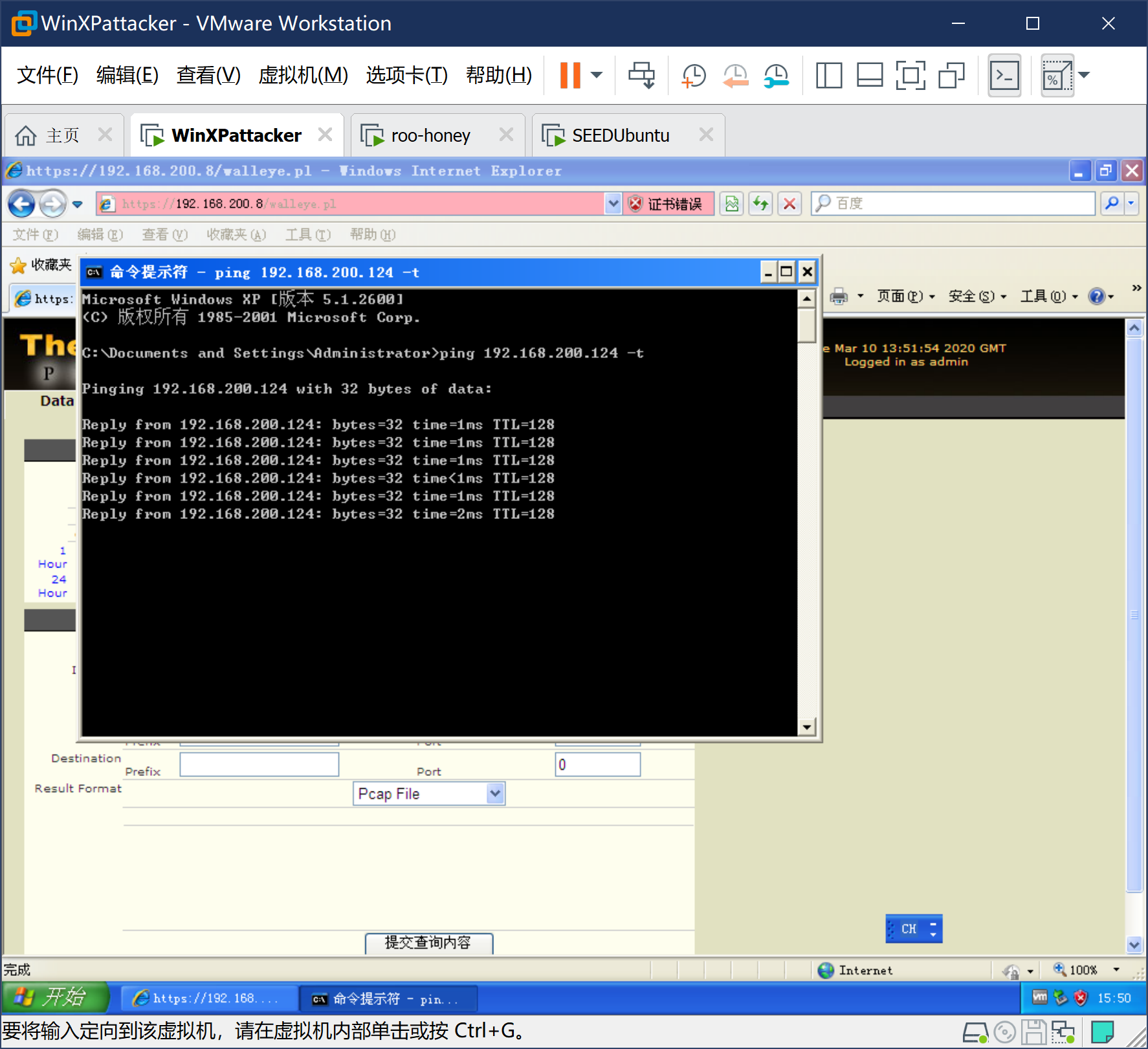
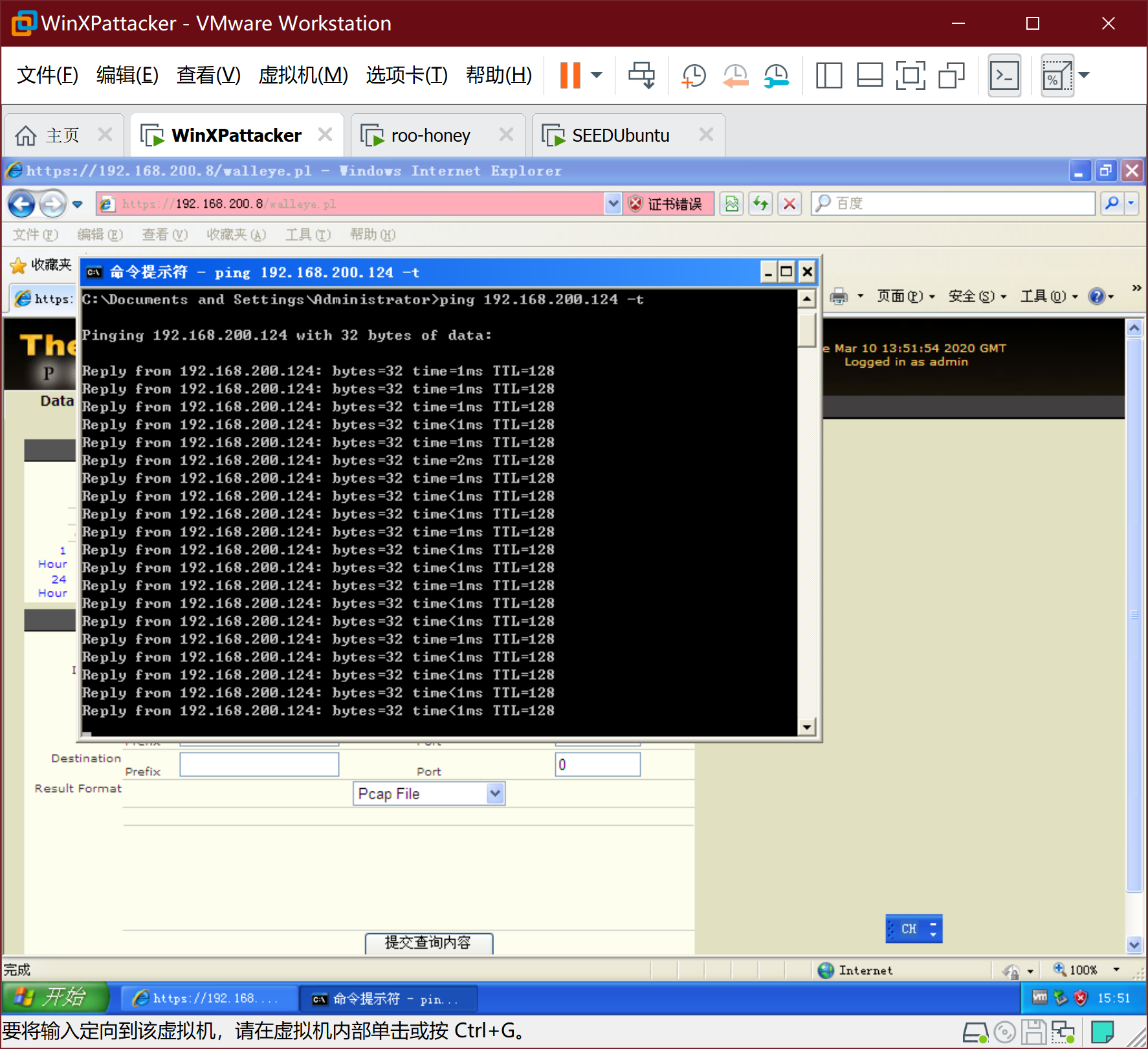
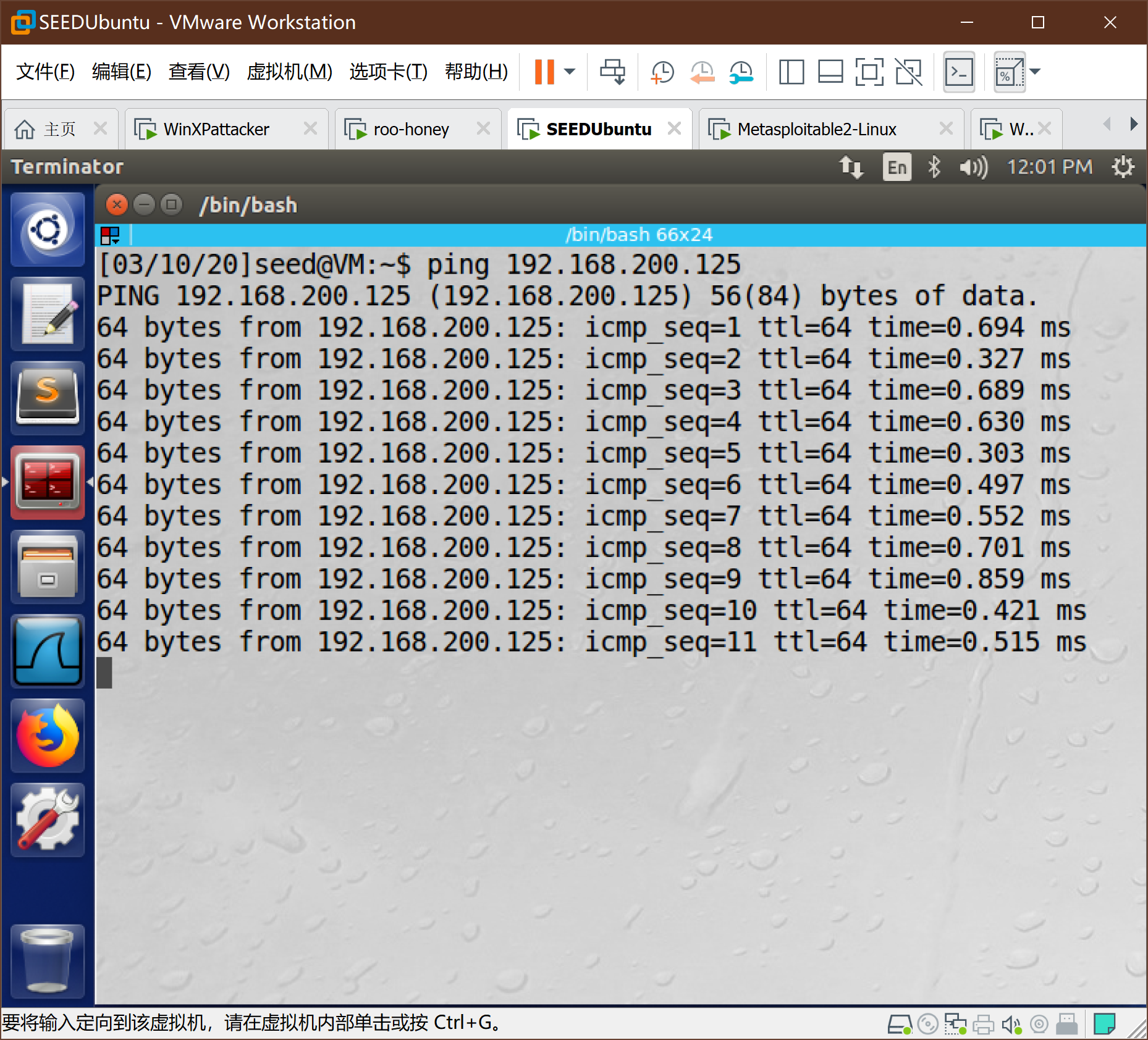
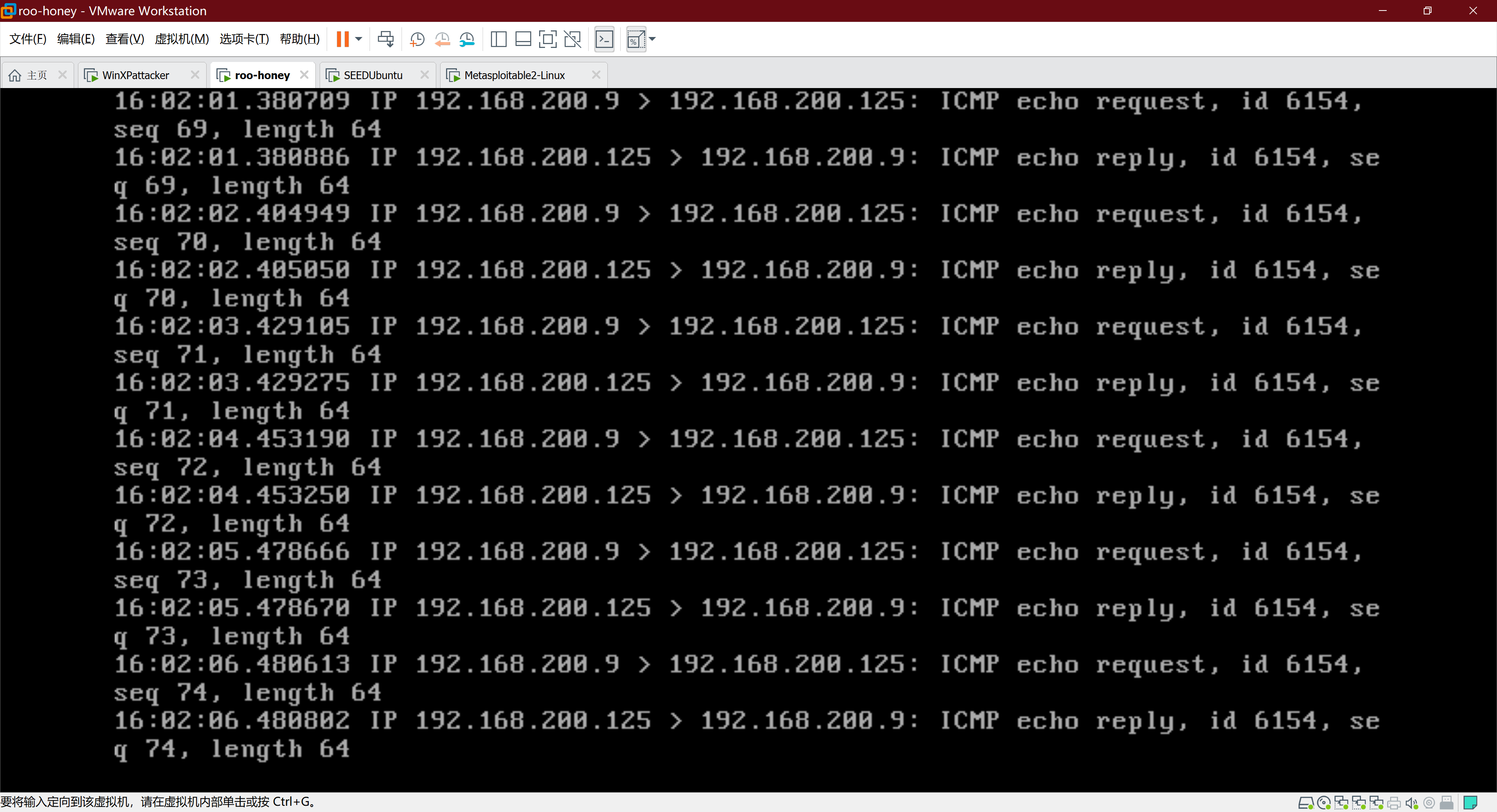
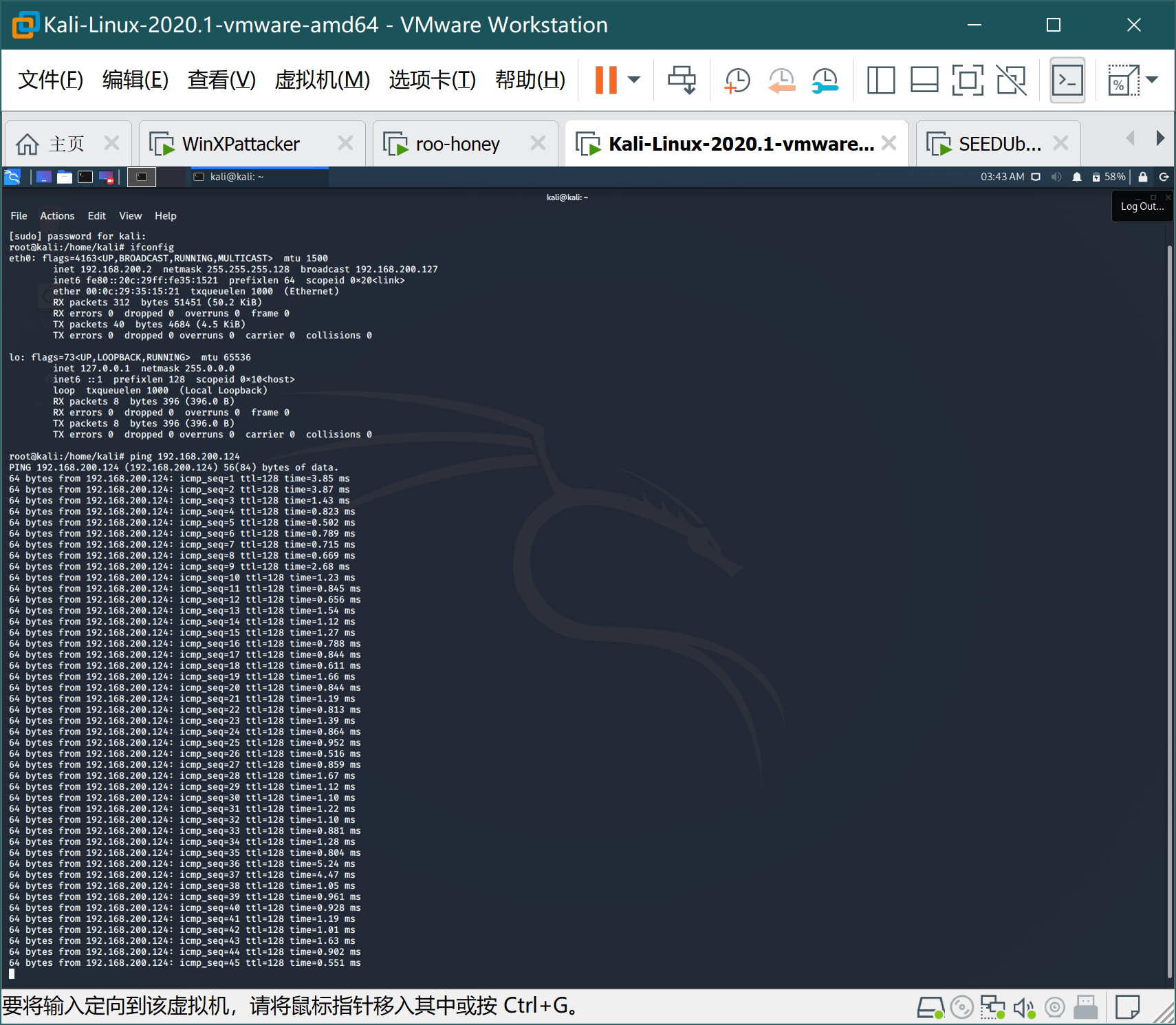
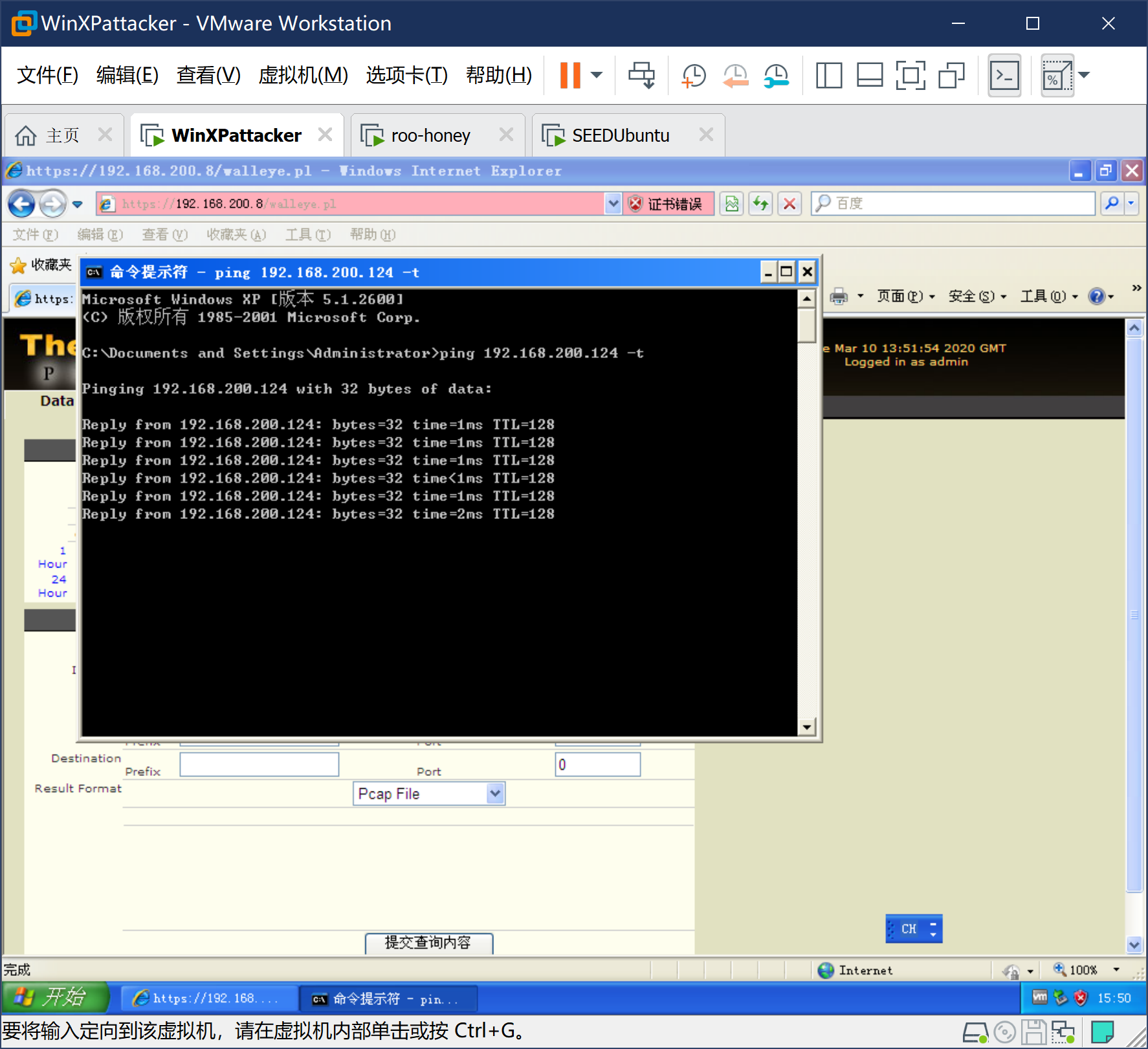
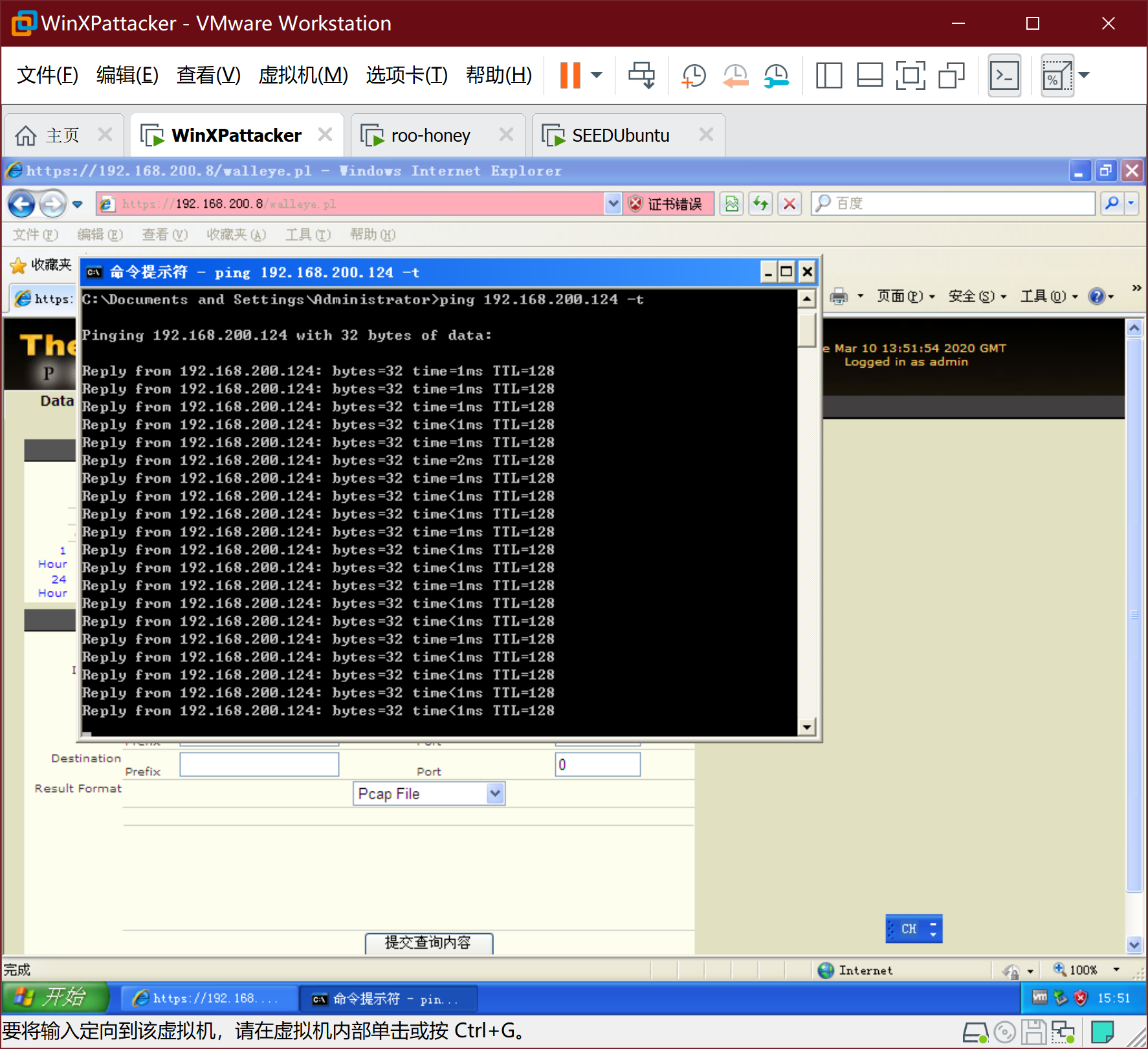
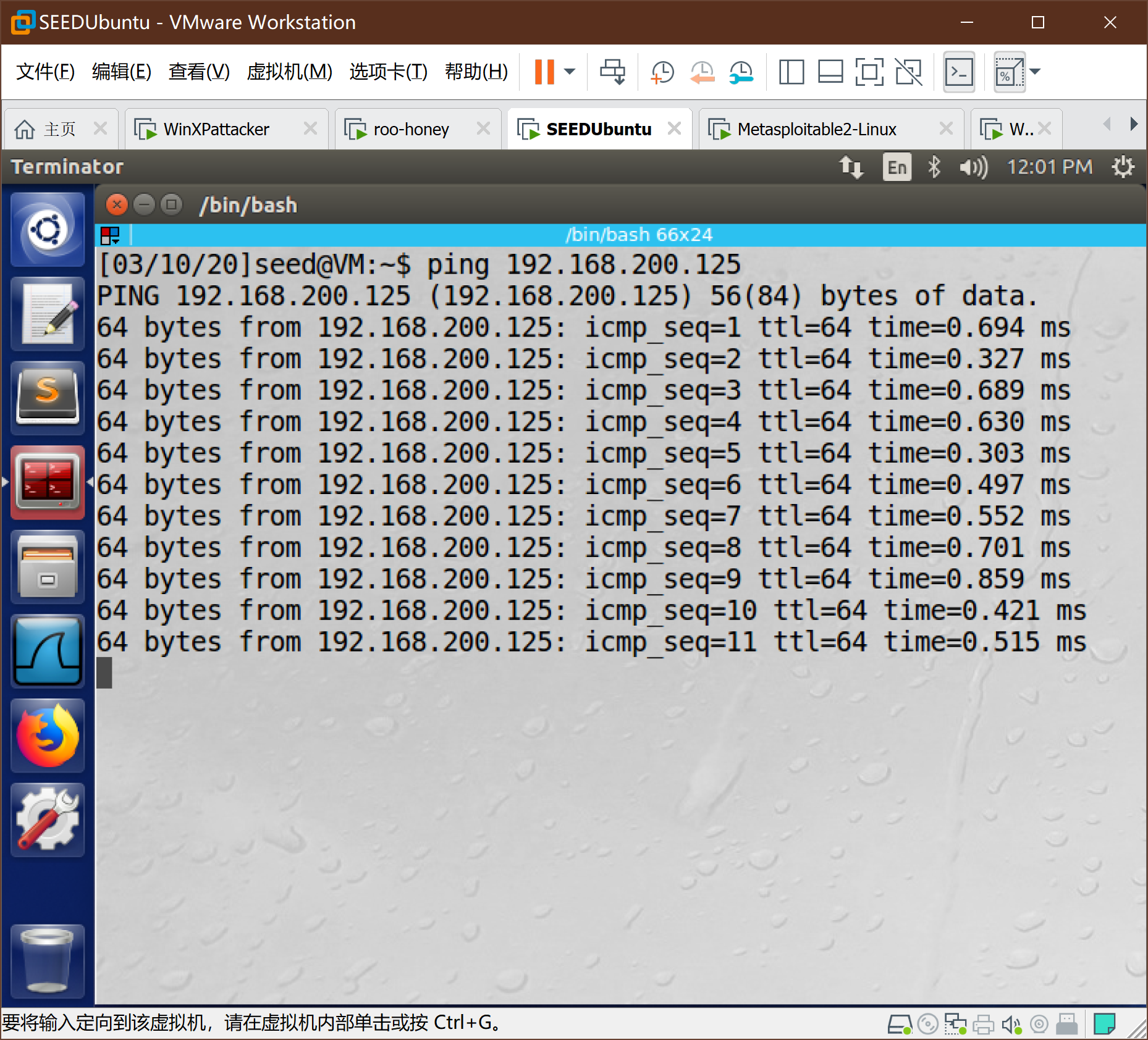
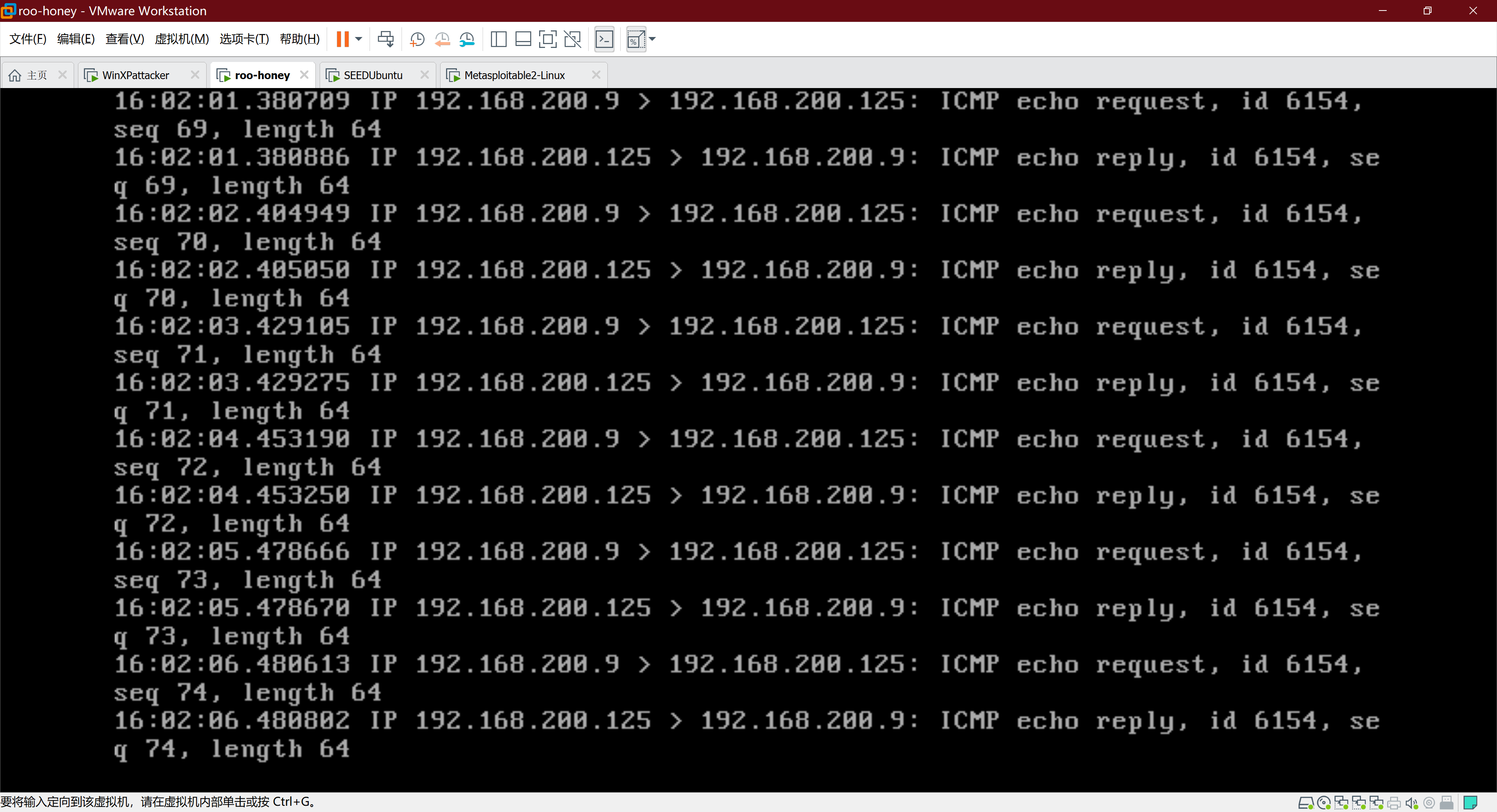
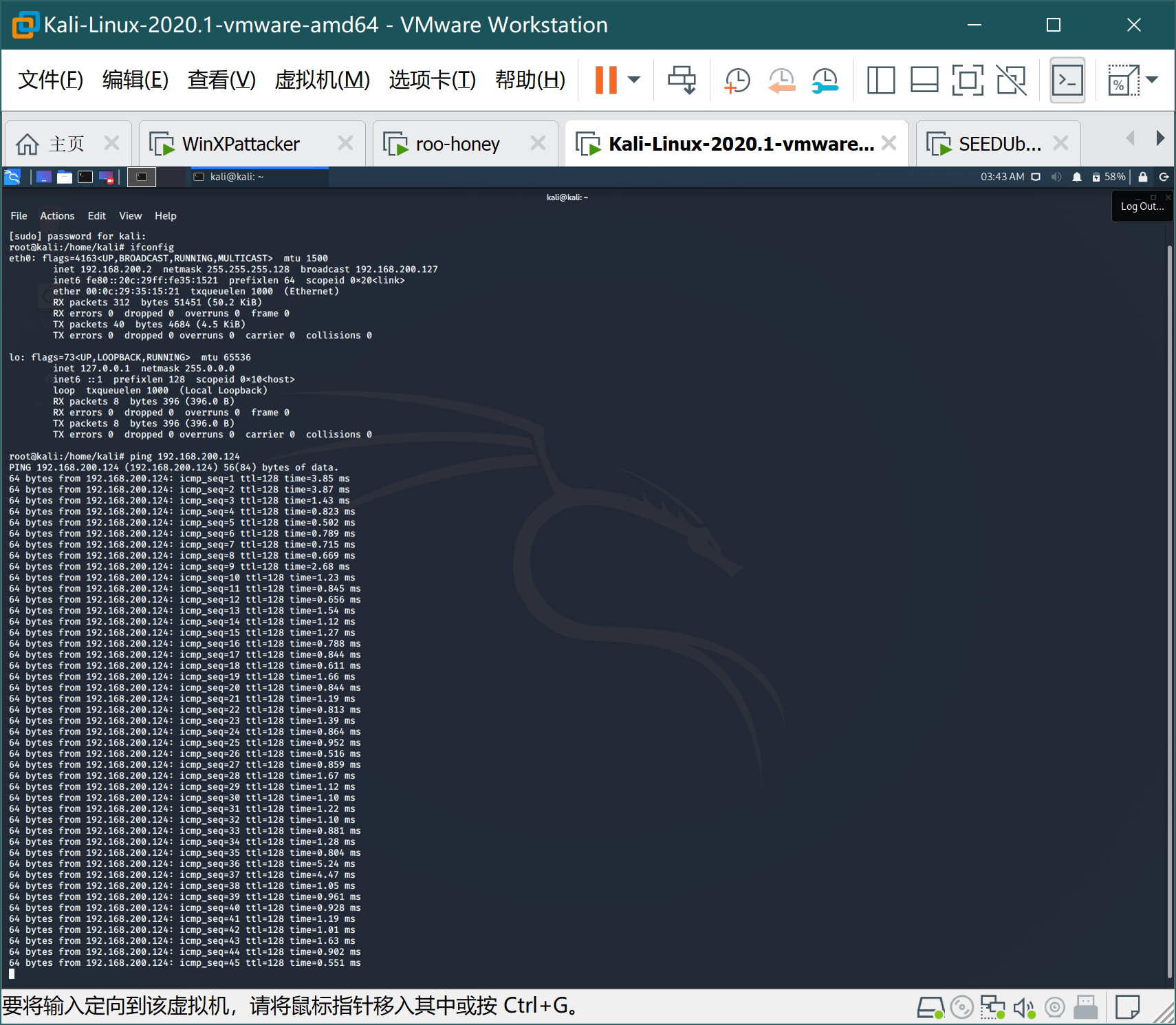
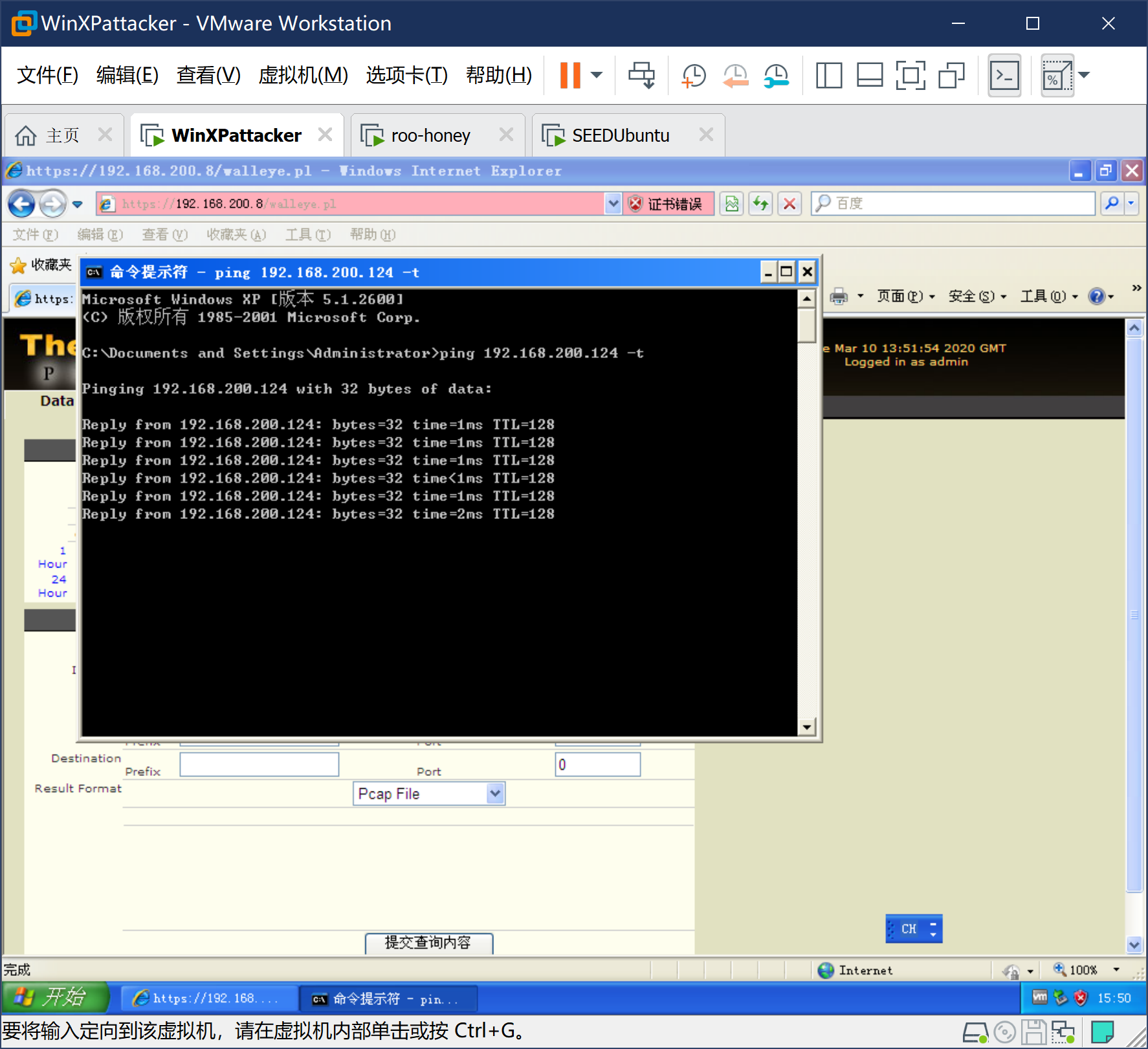
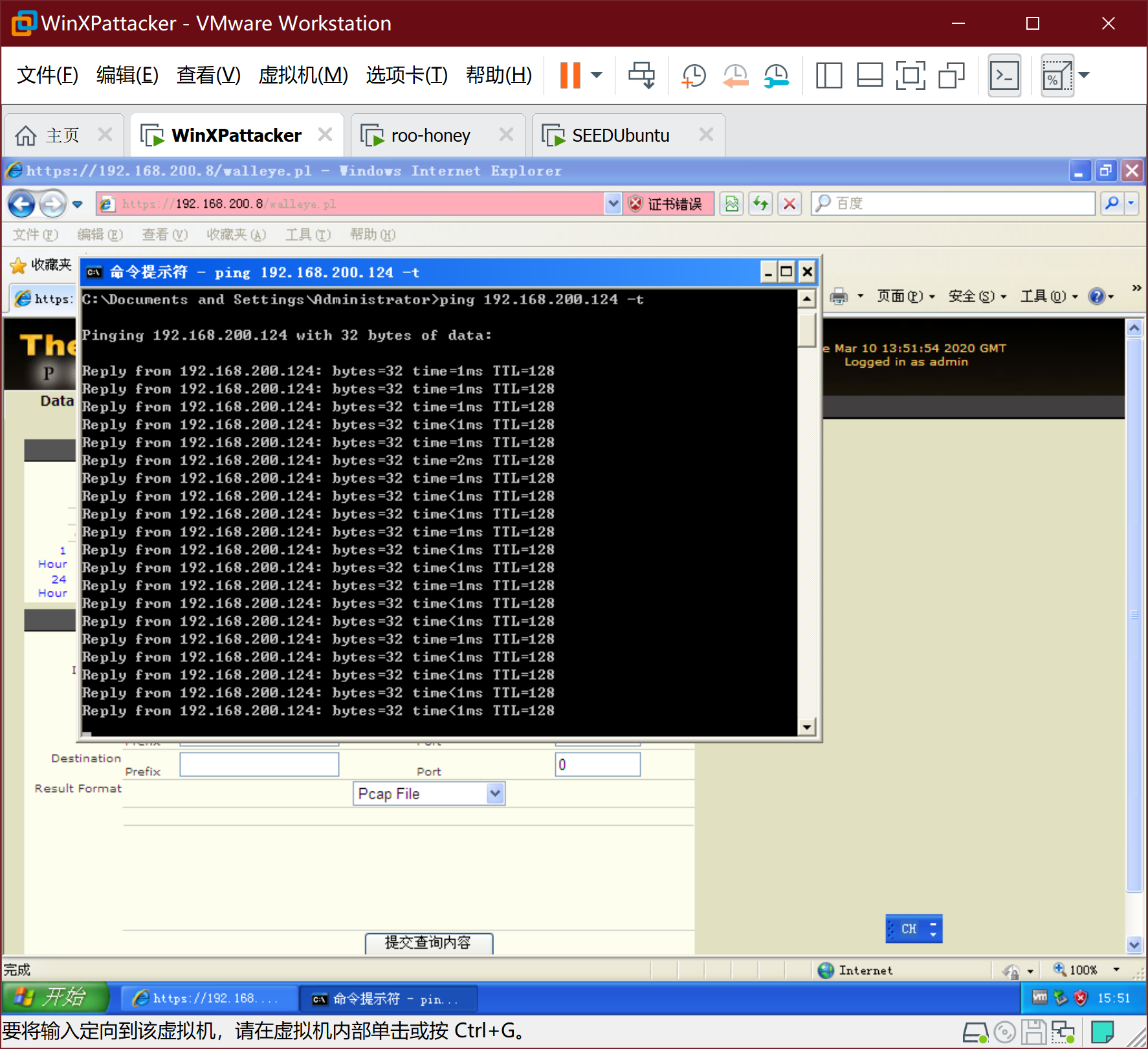
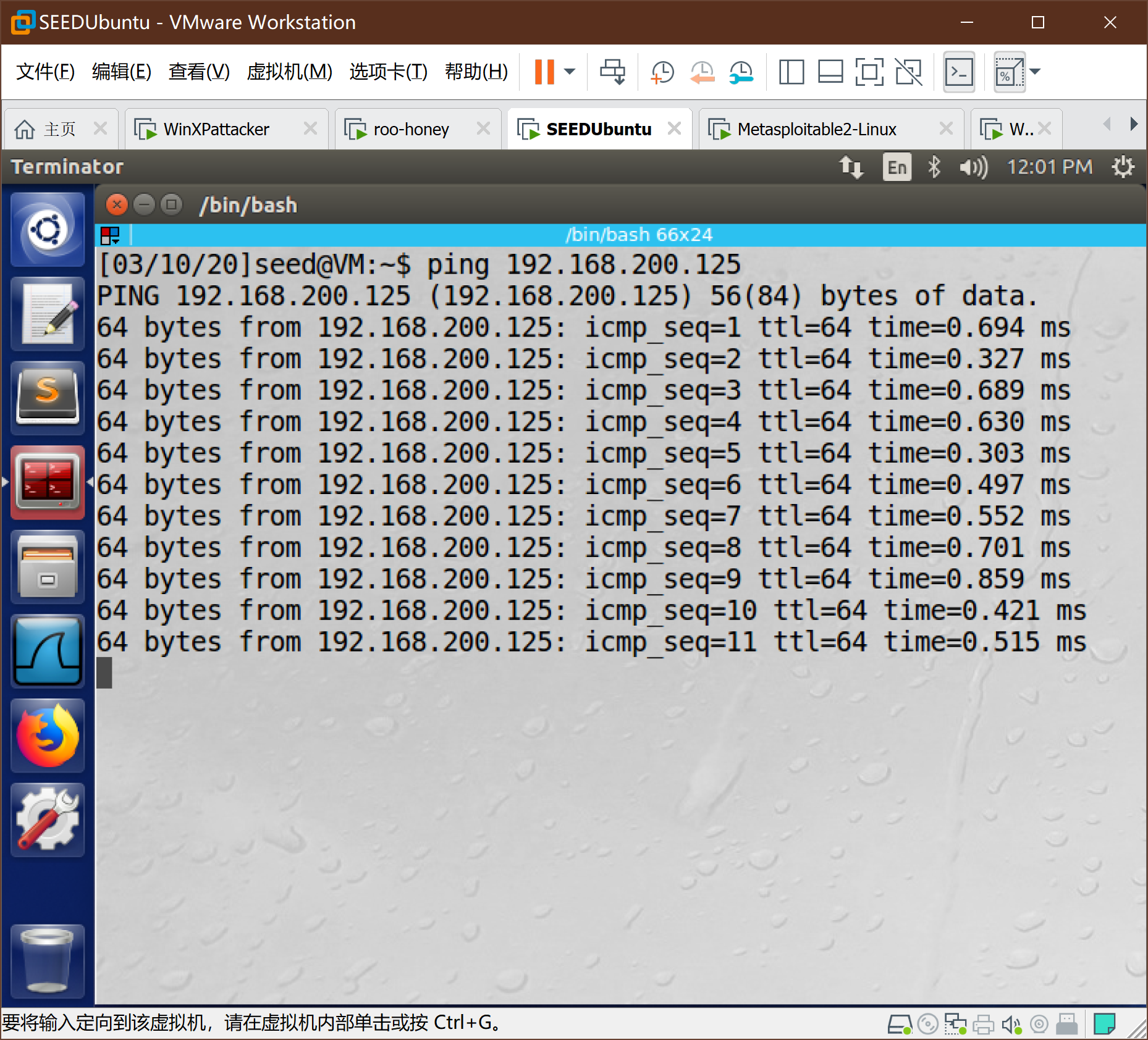
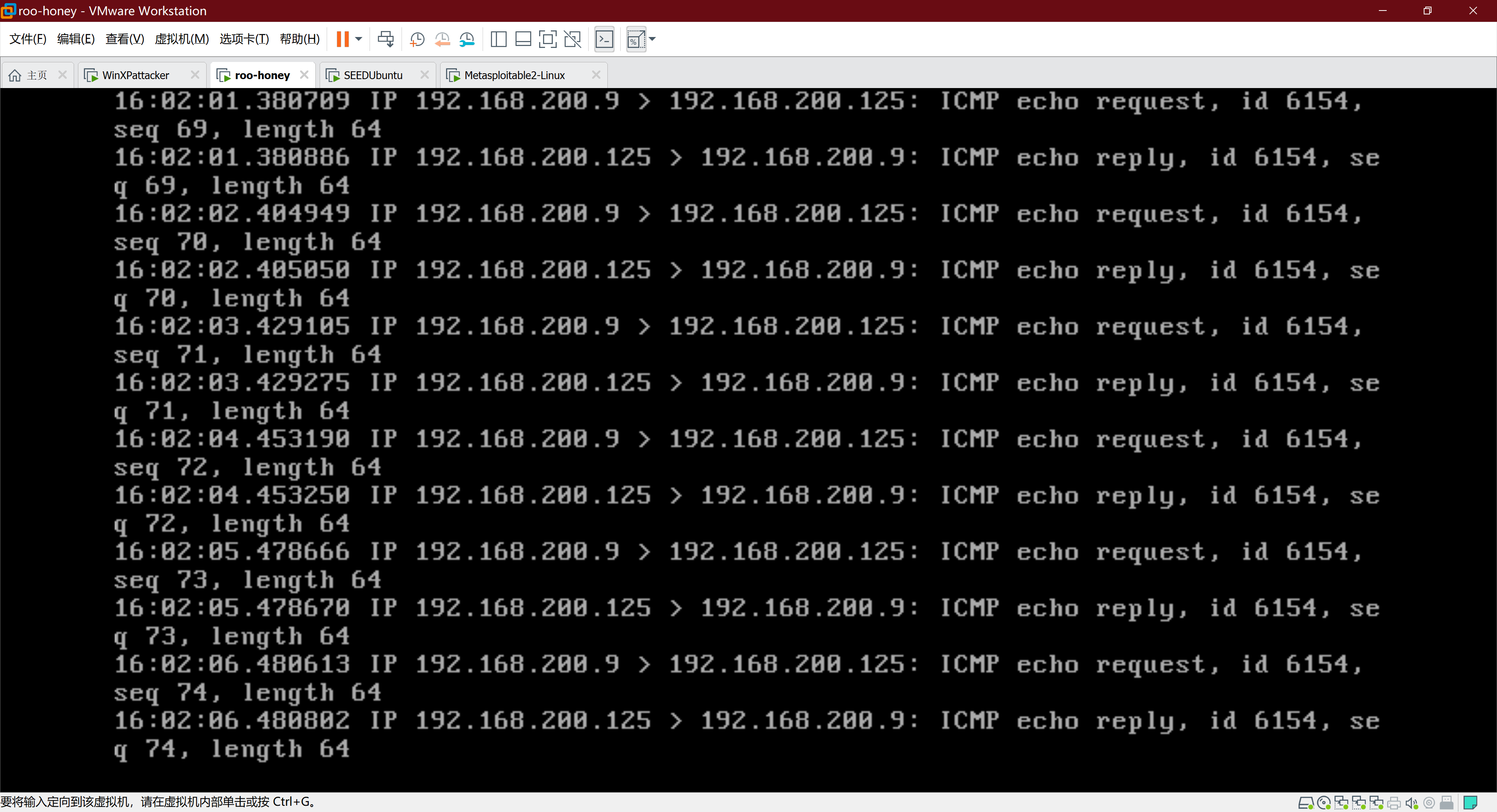
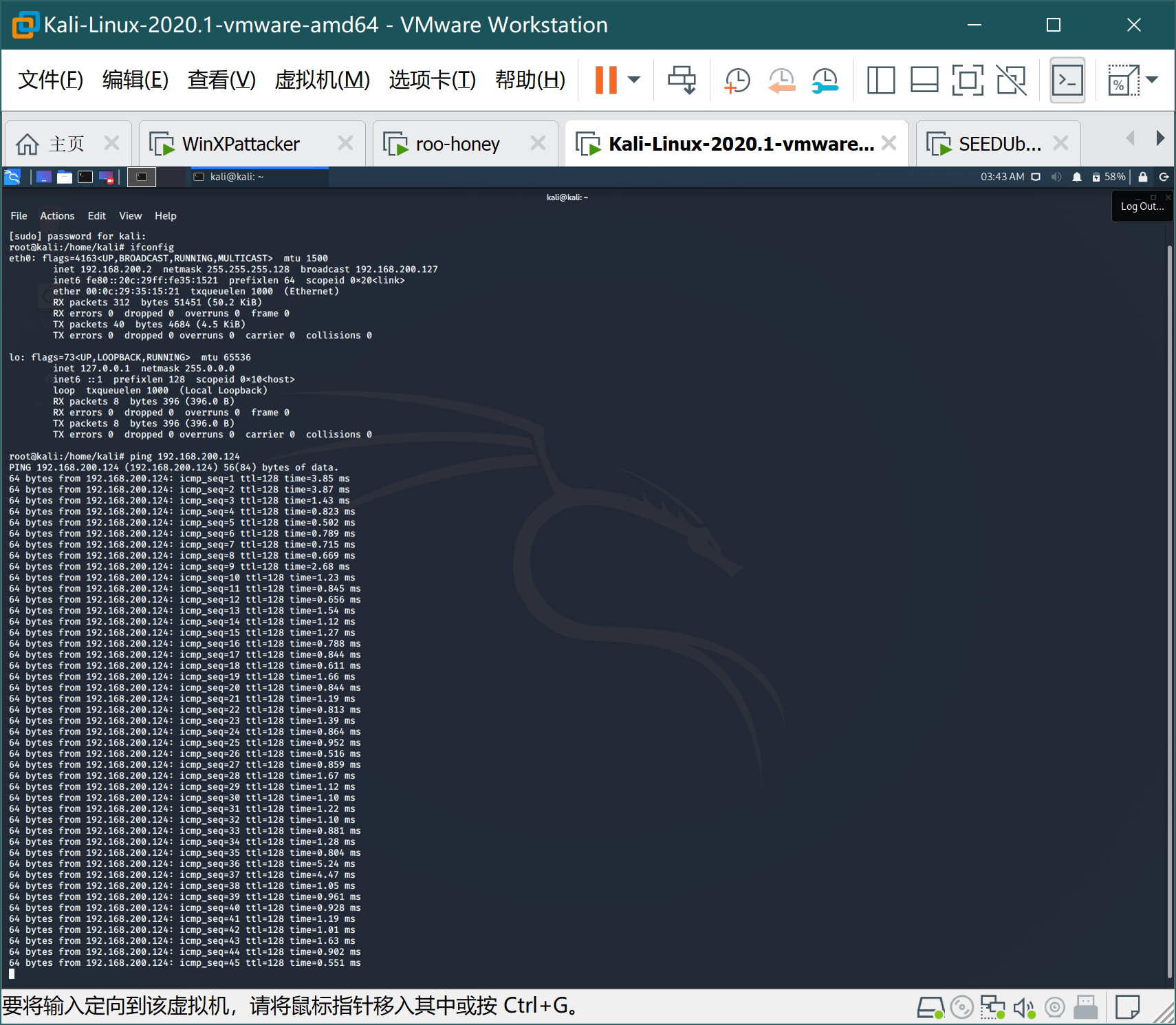
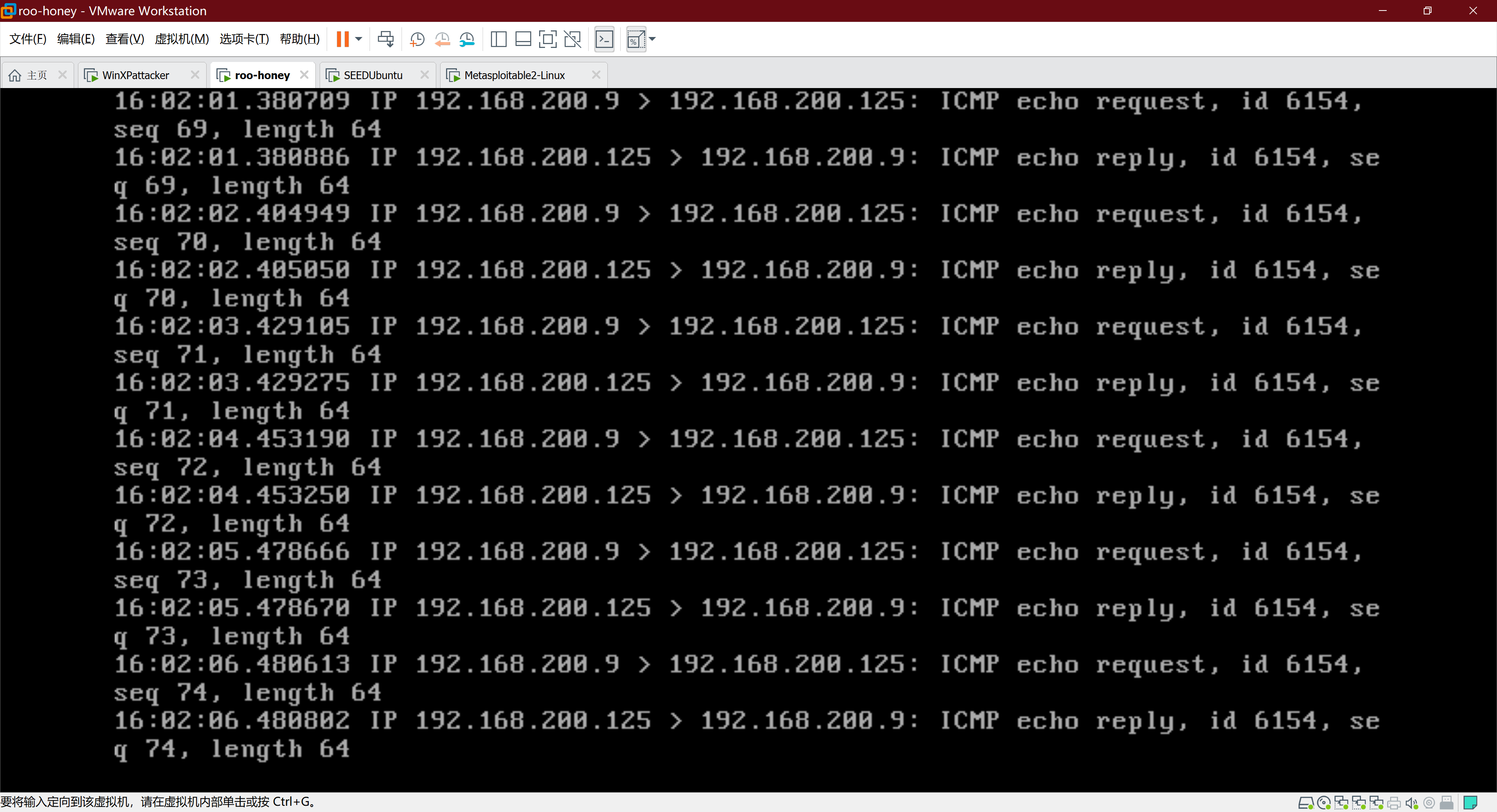
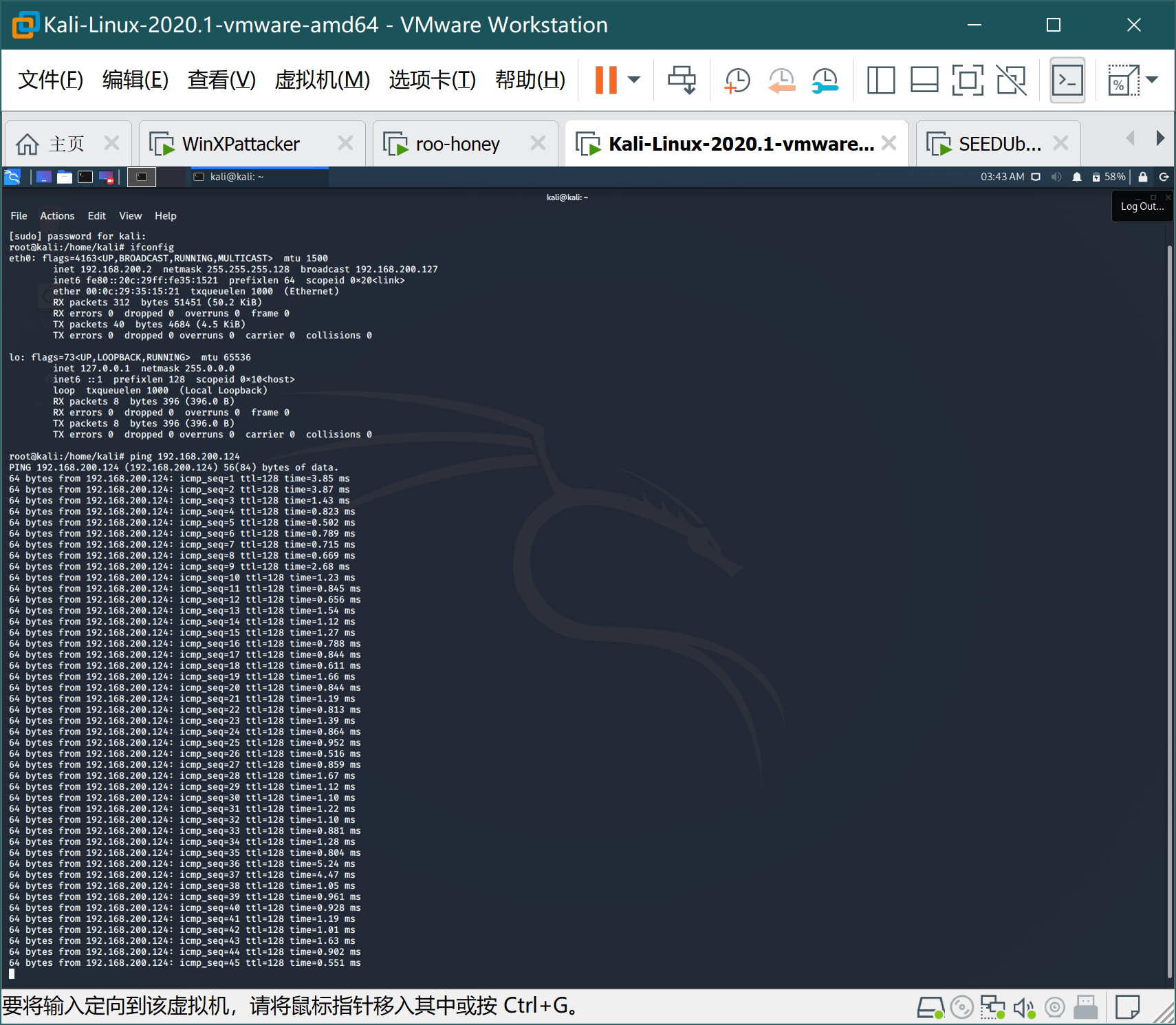
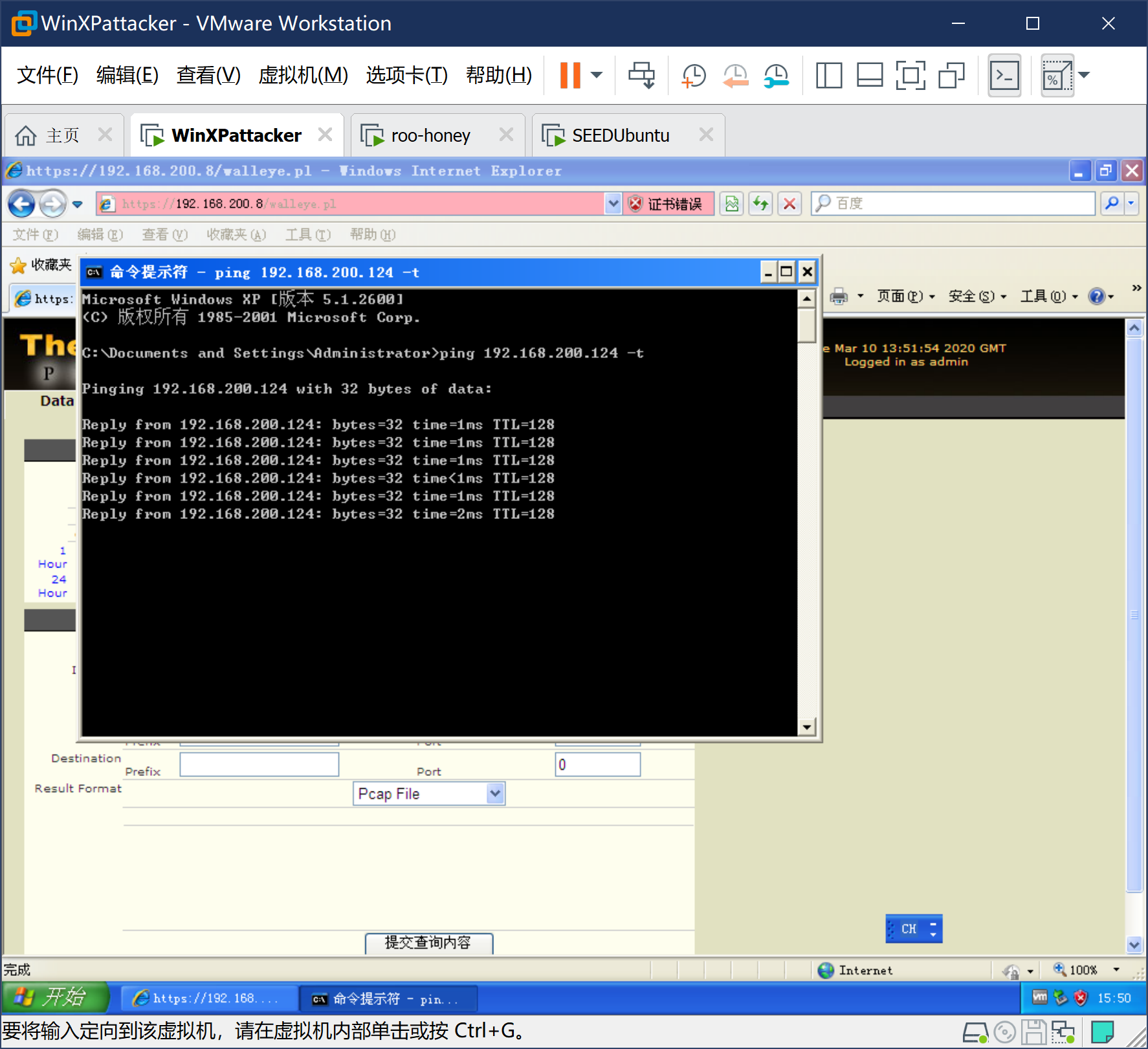
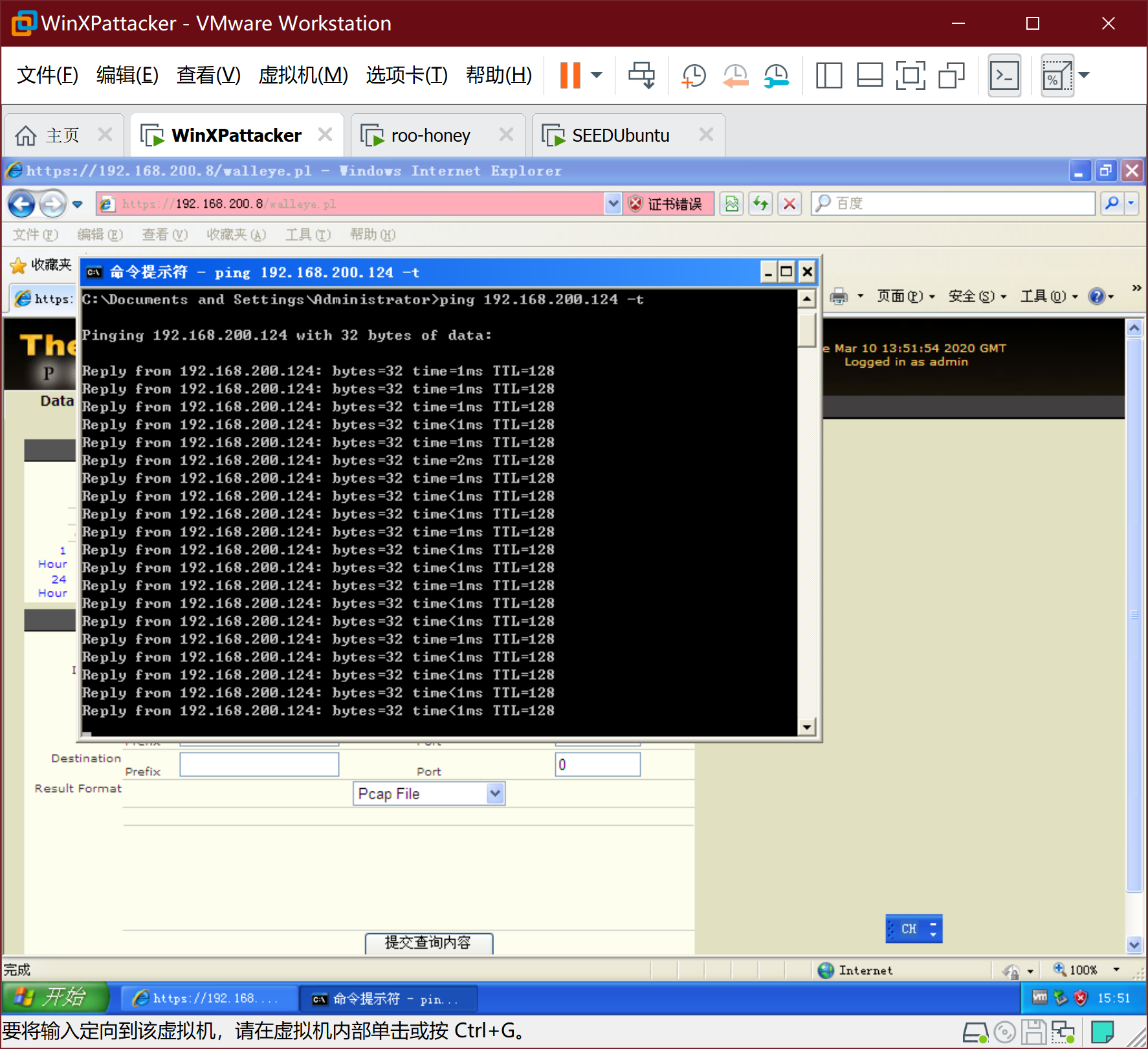
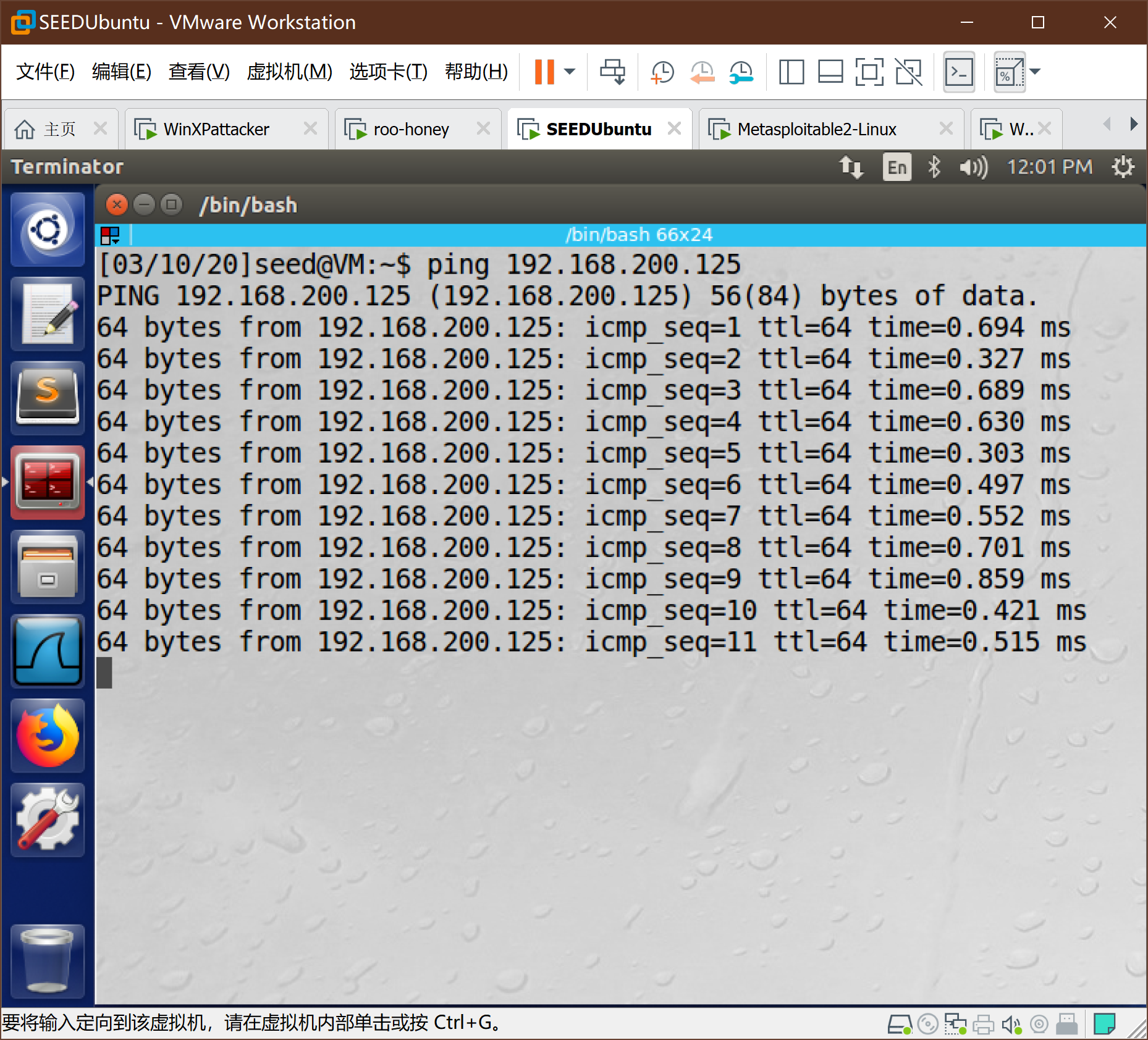
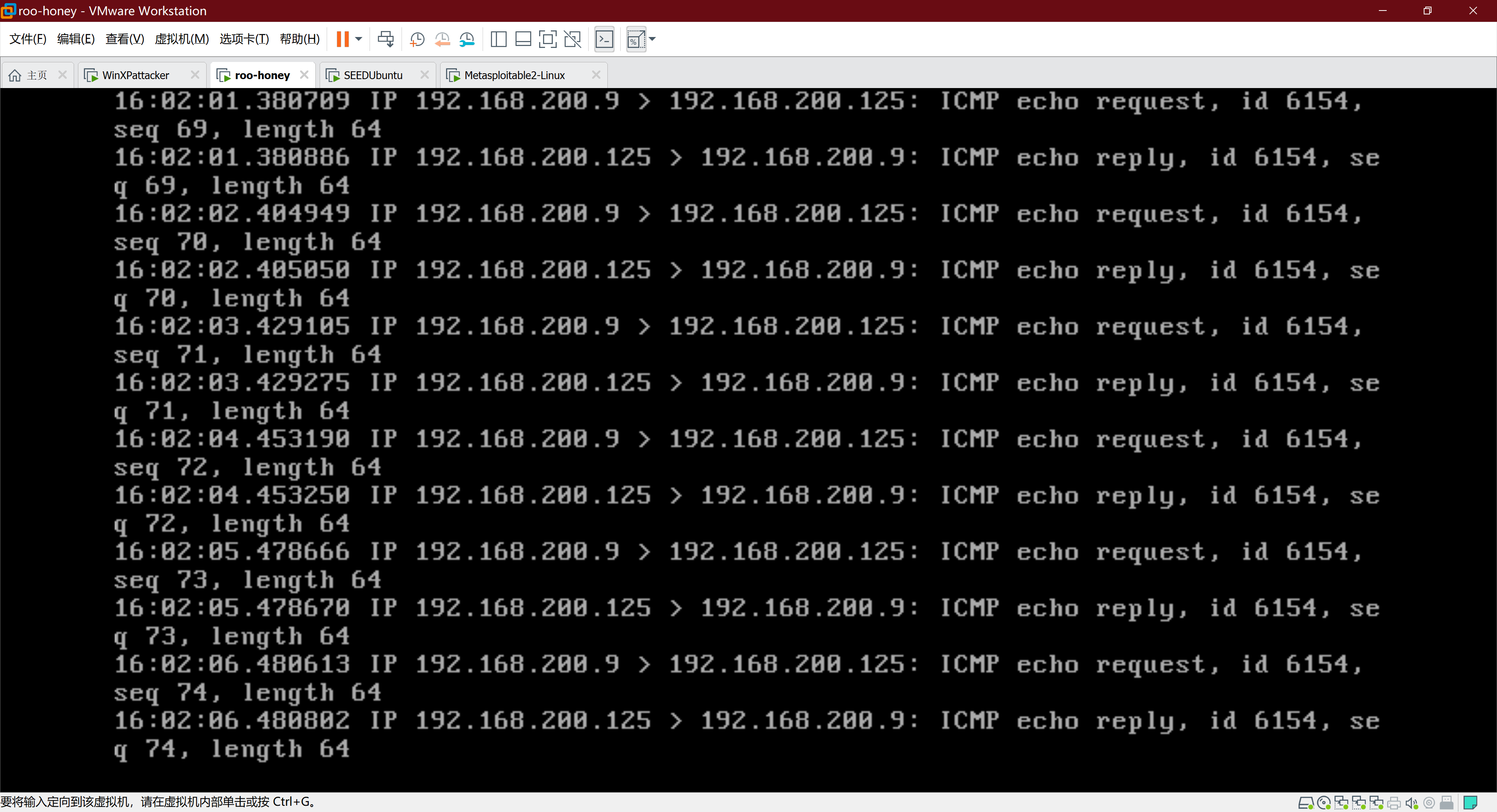
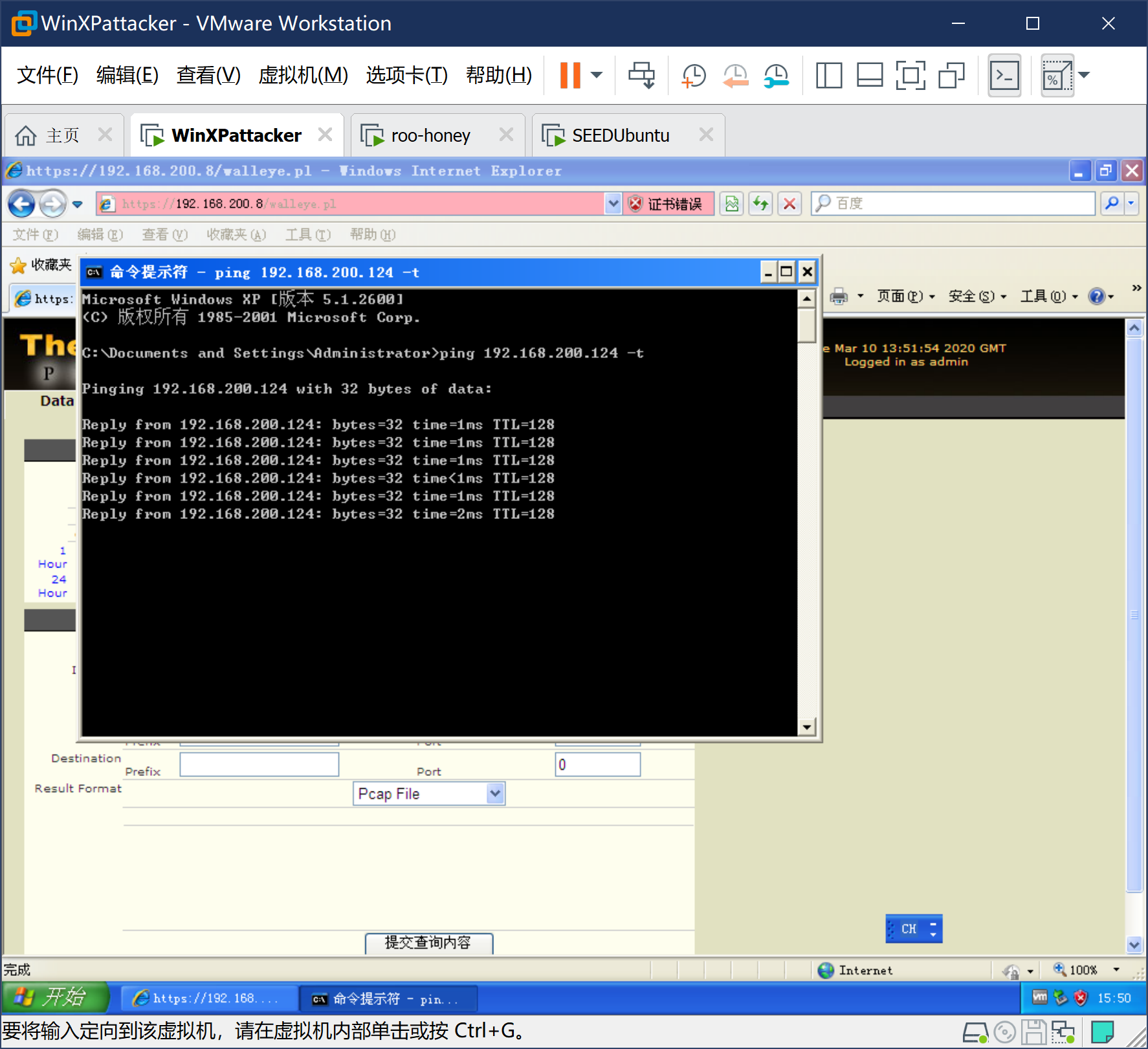
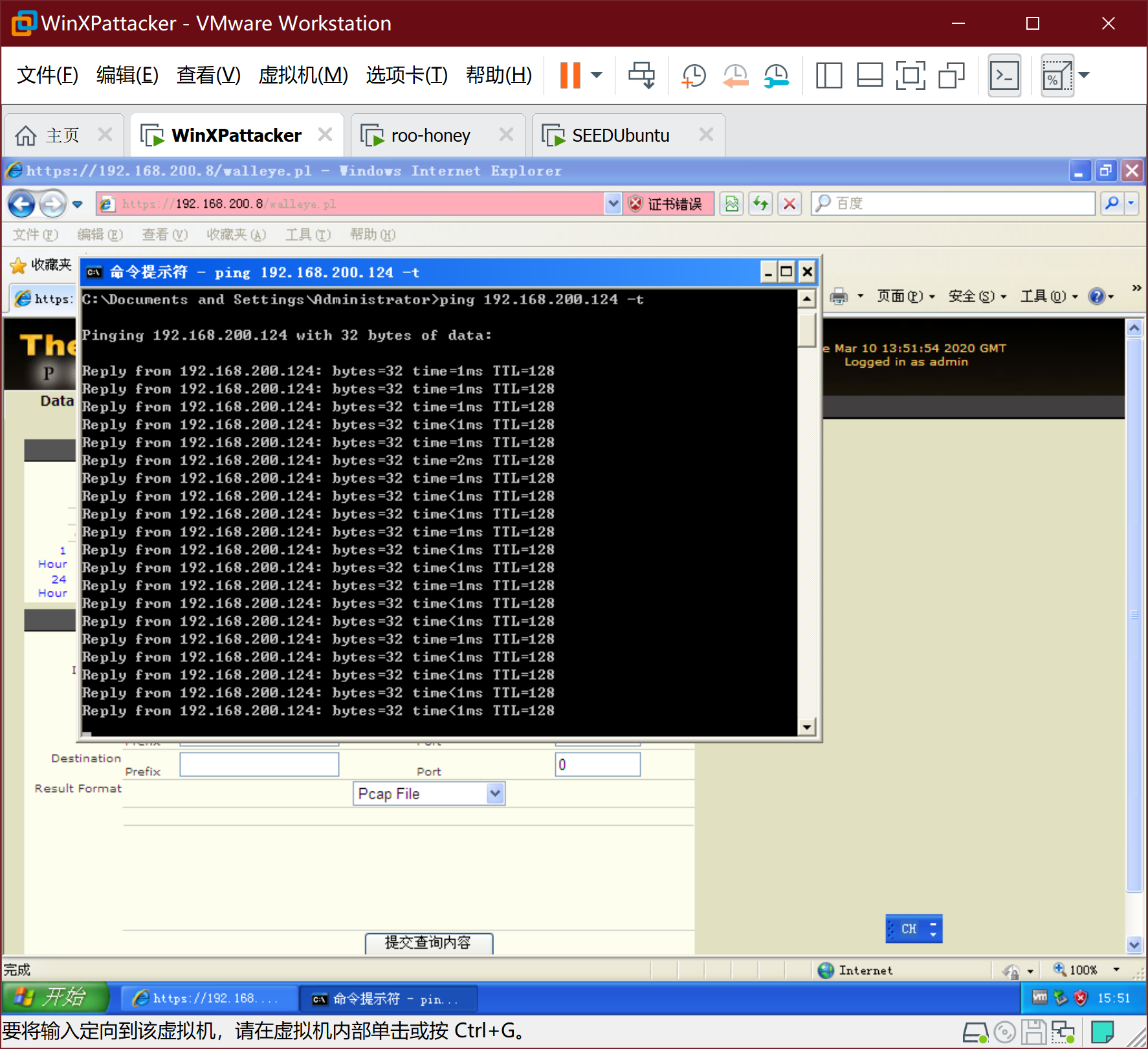
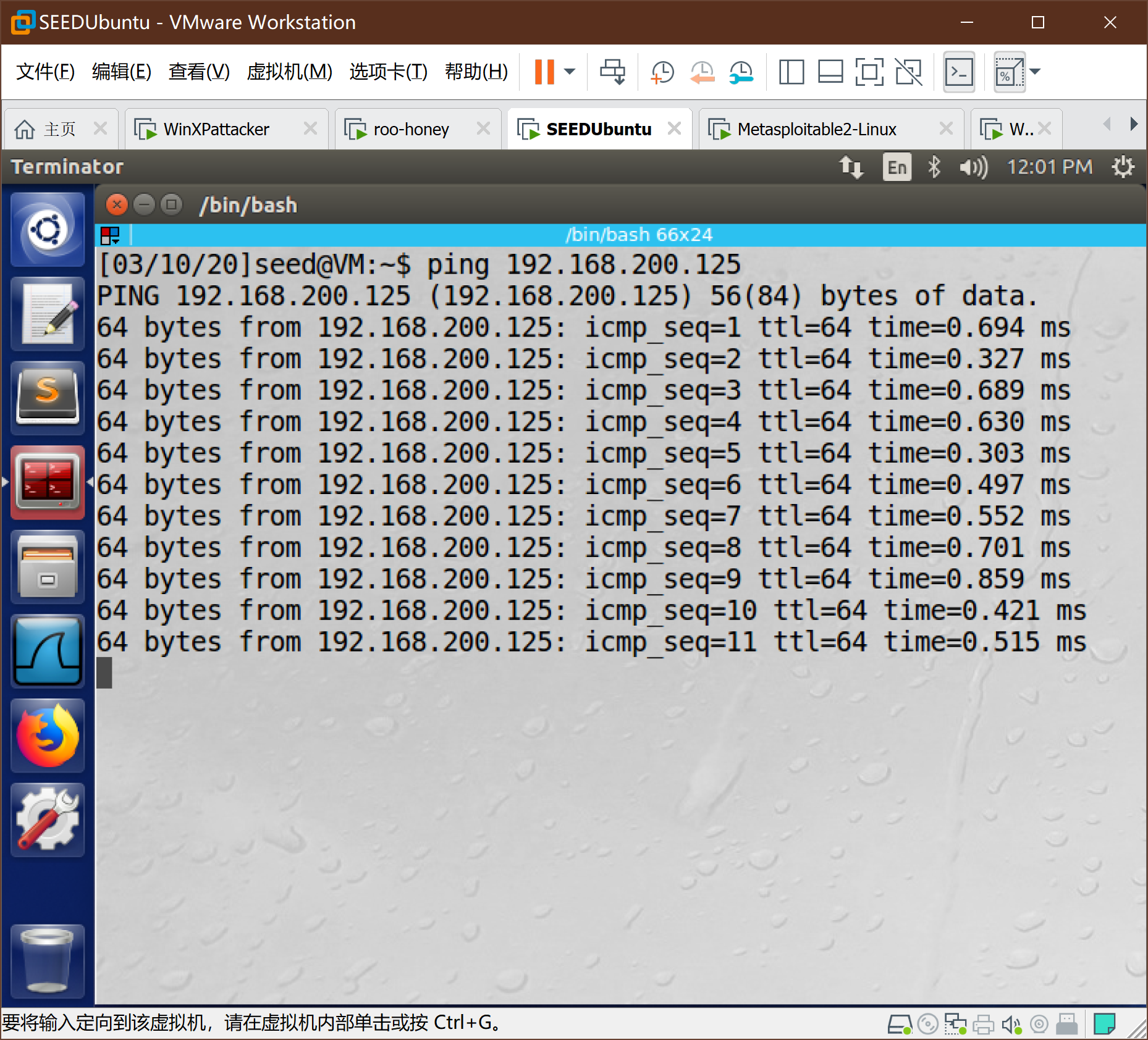
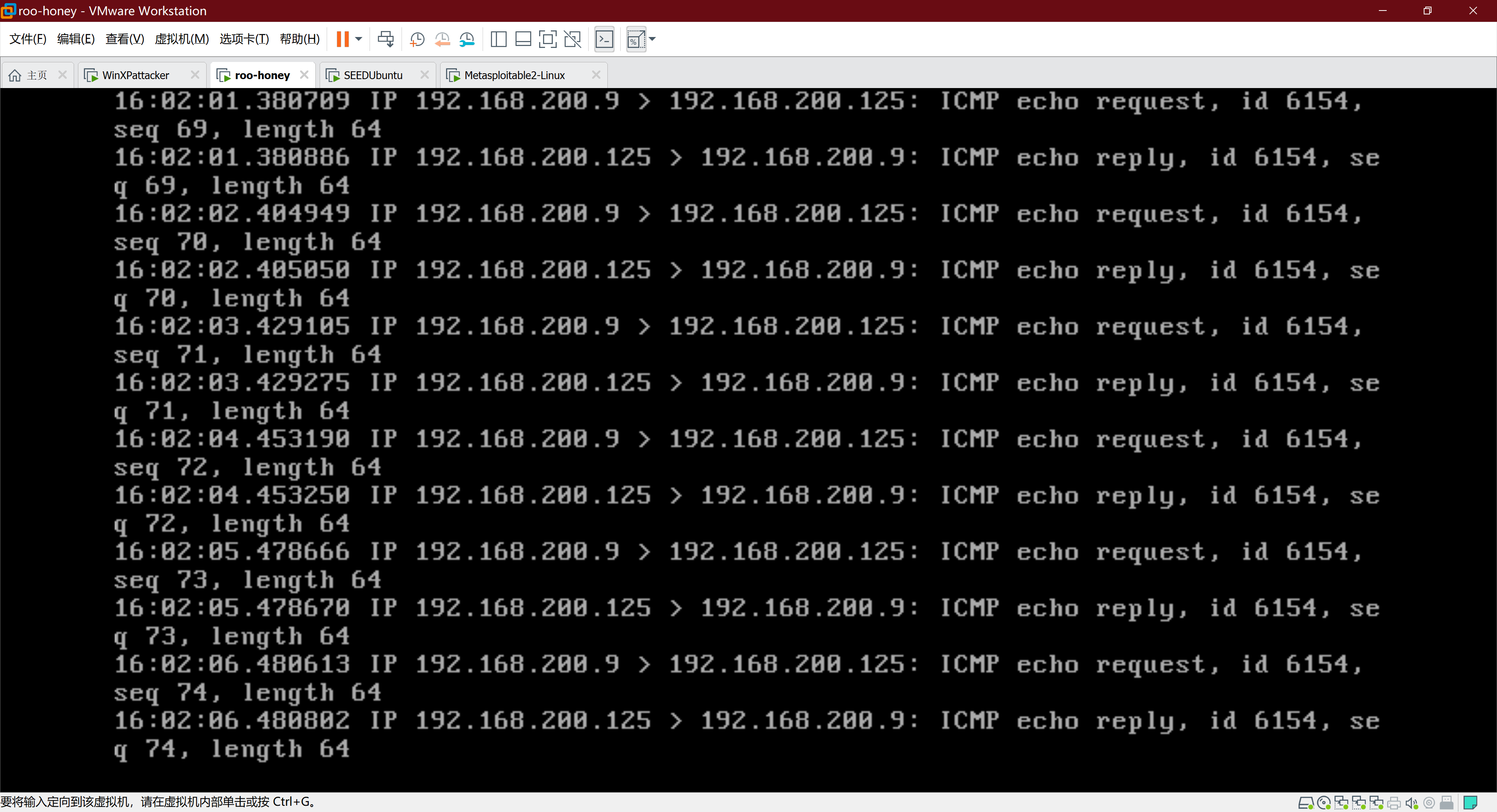
9、ping检验
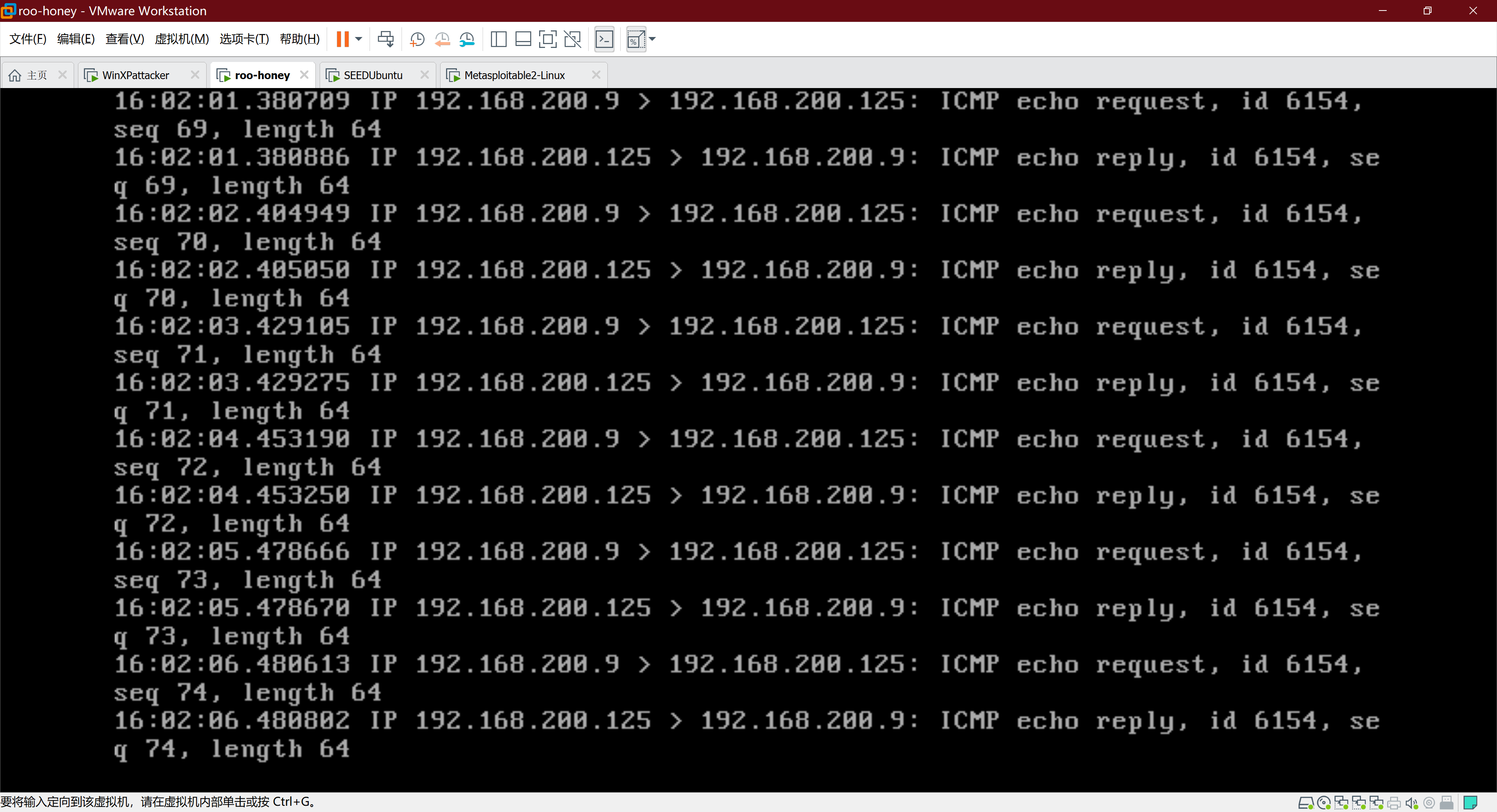
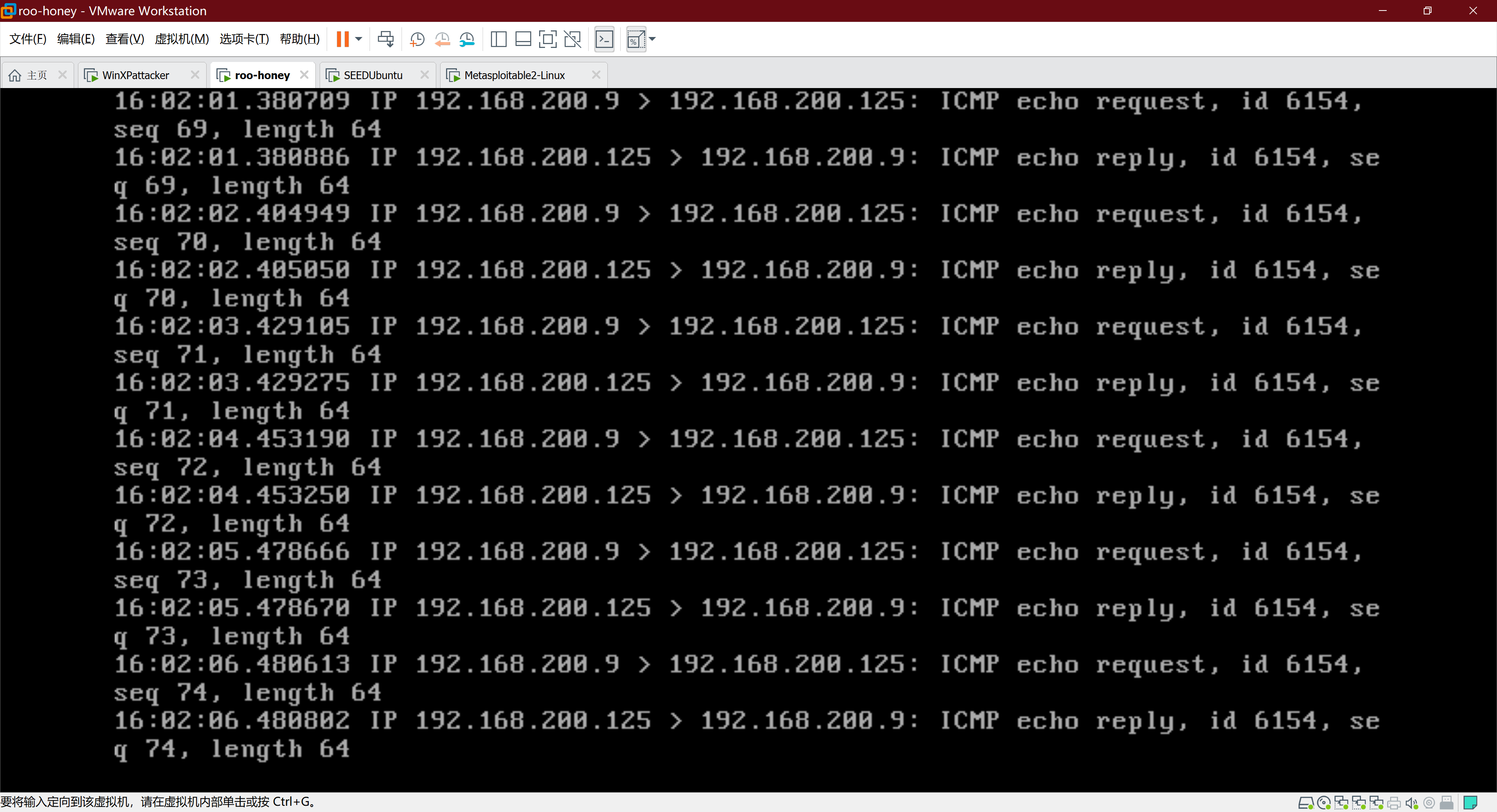
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
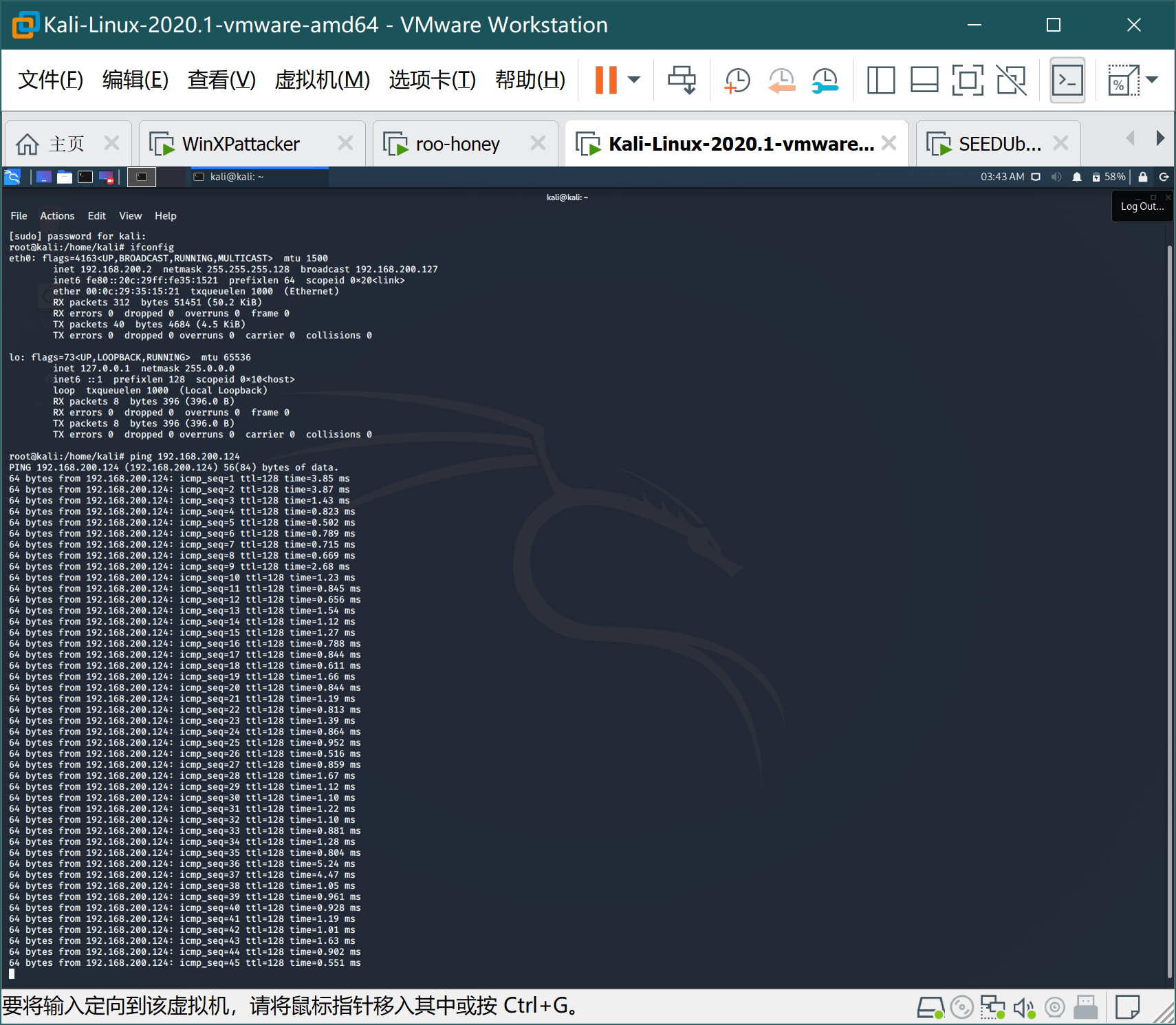
- Kali ping Win2kAerver
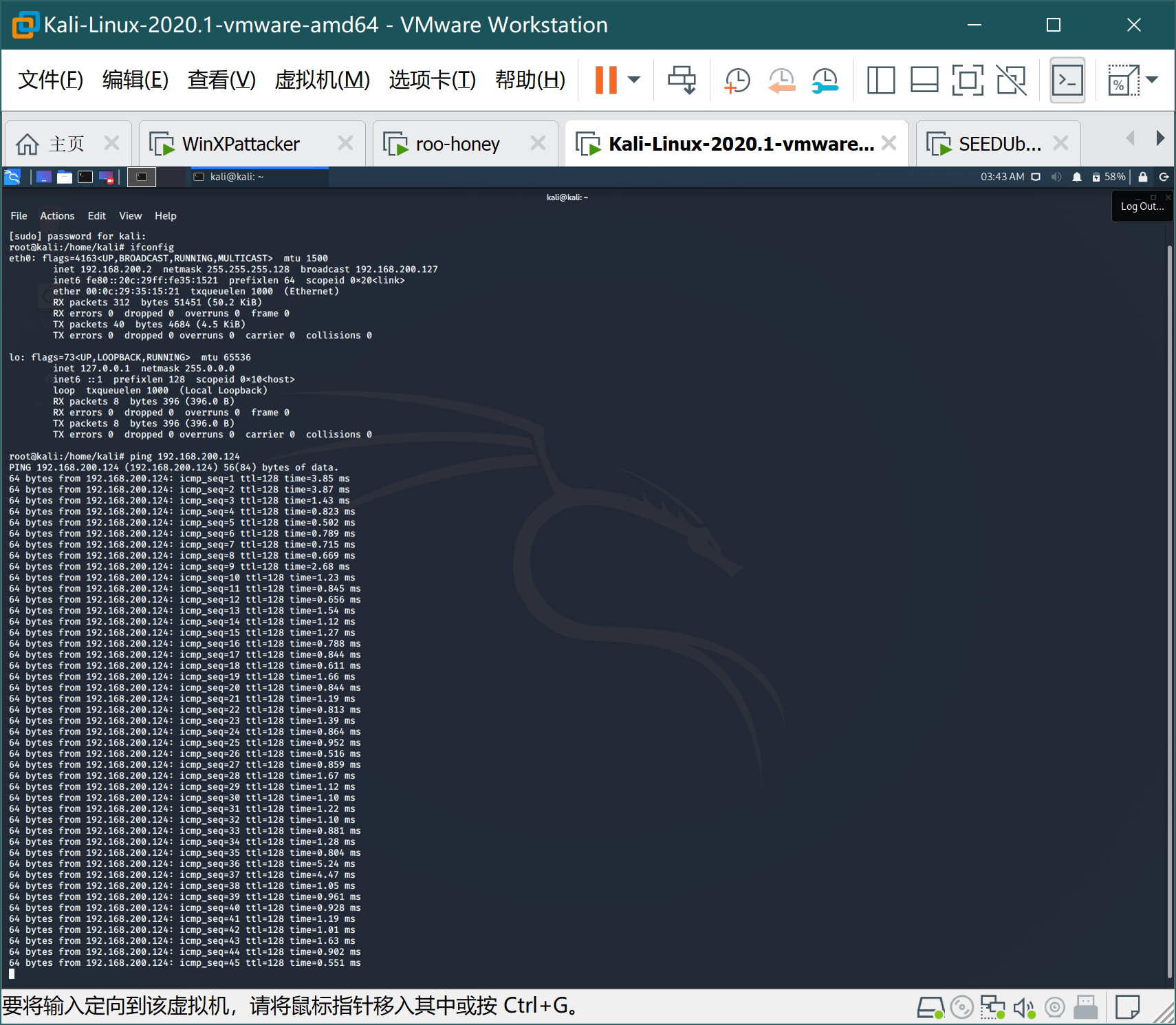
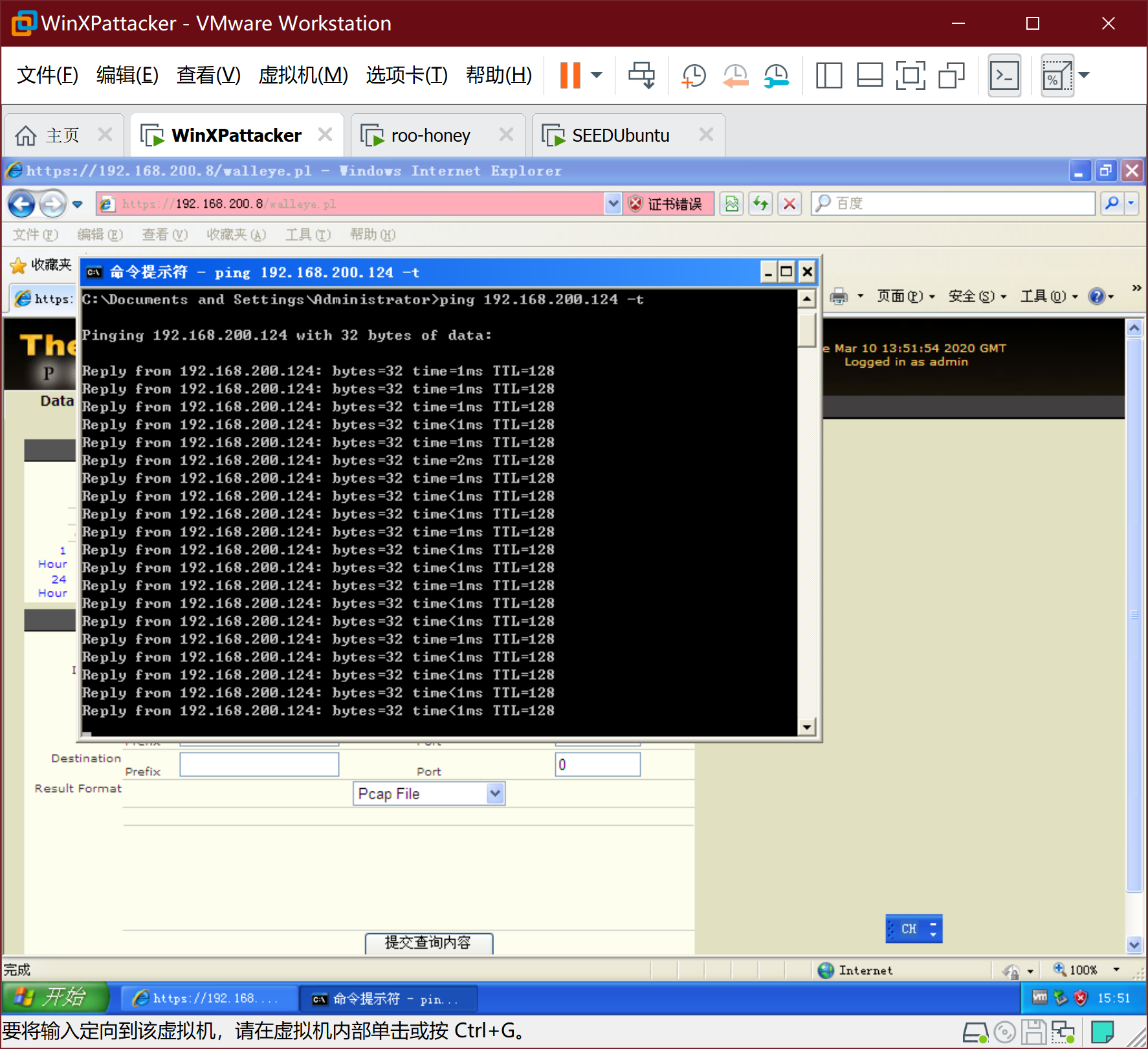
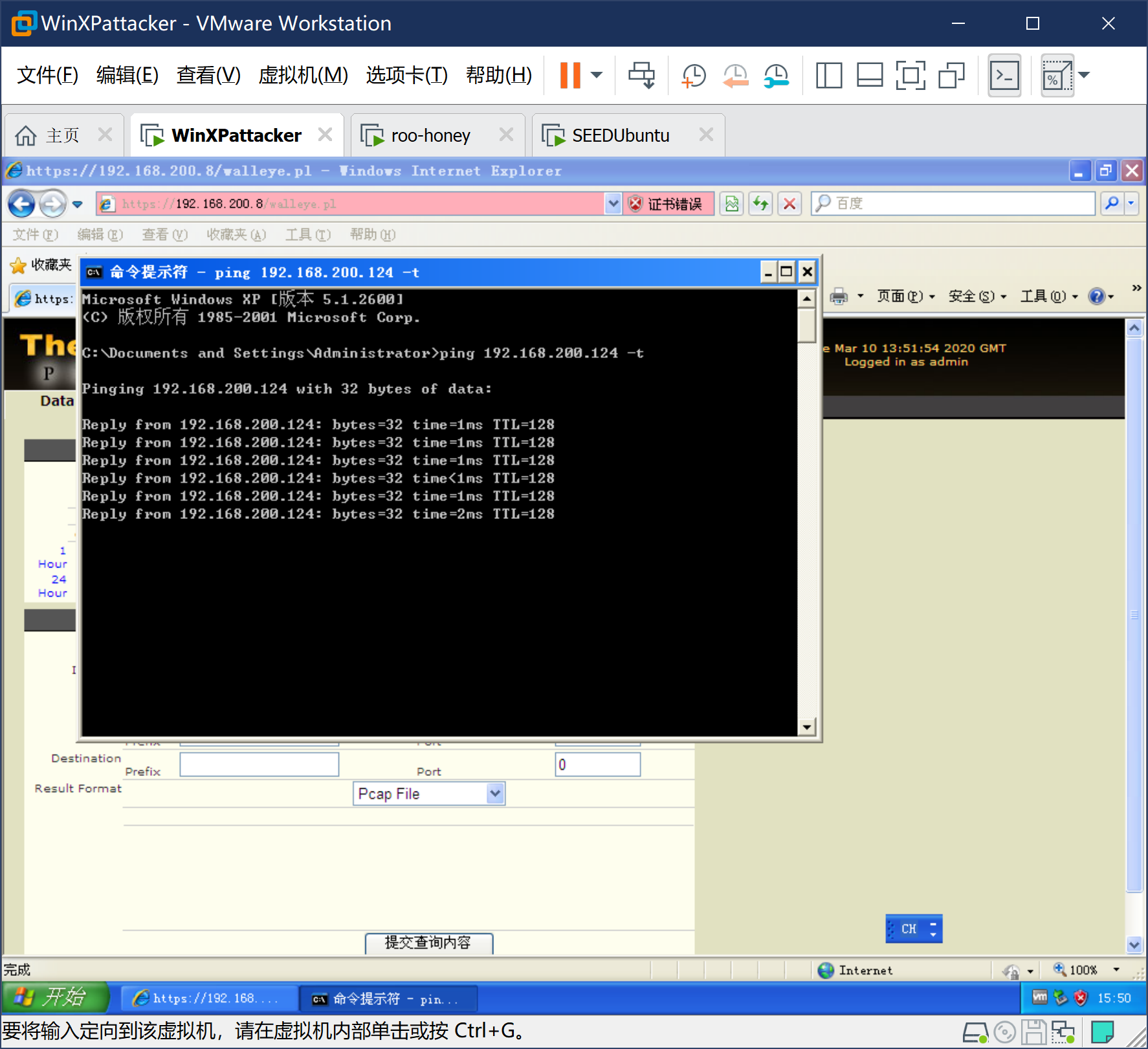
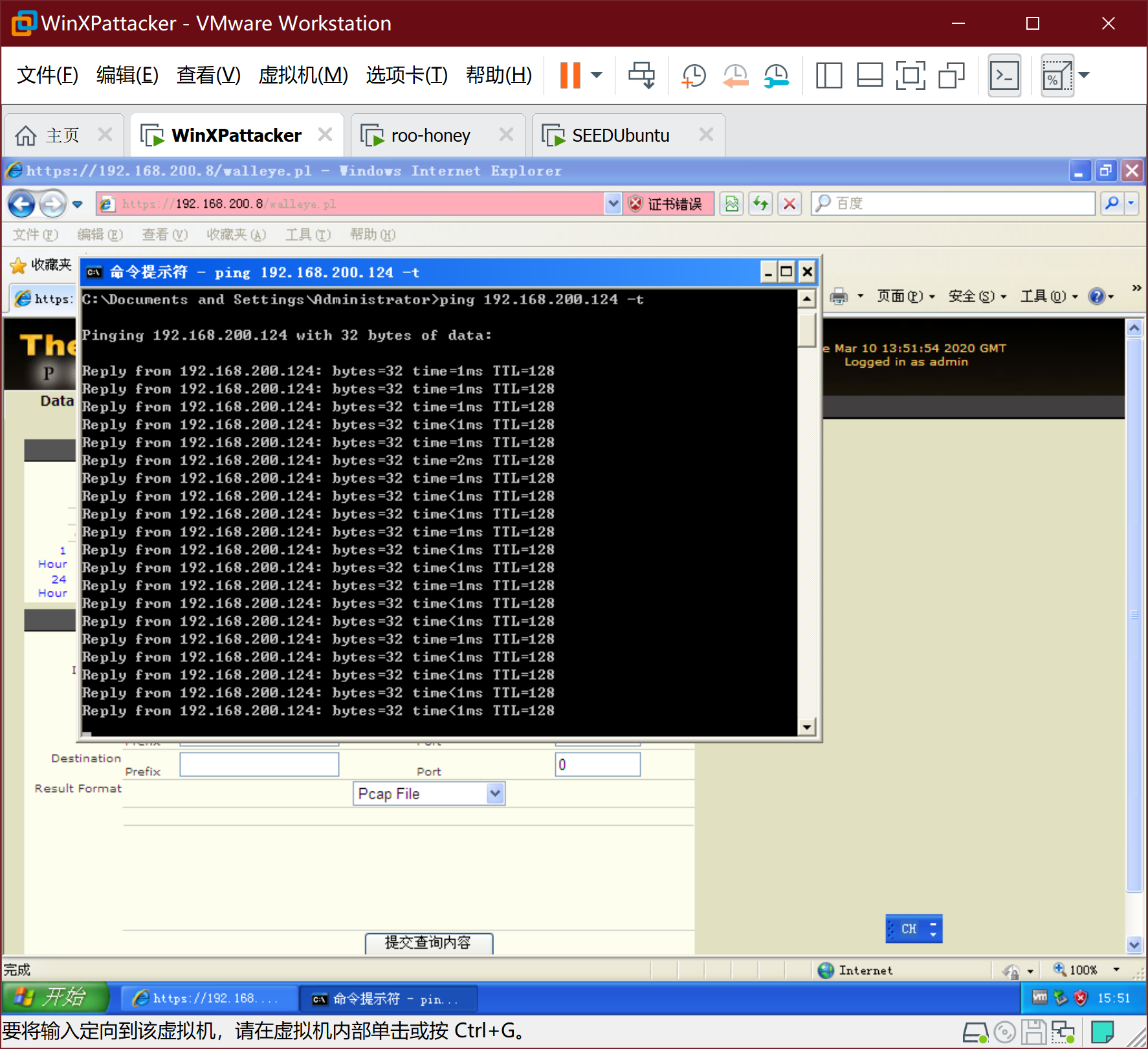
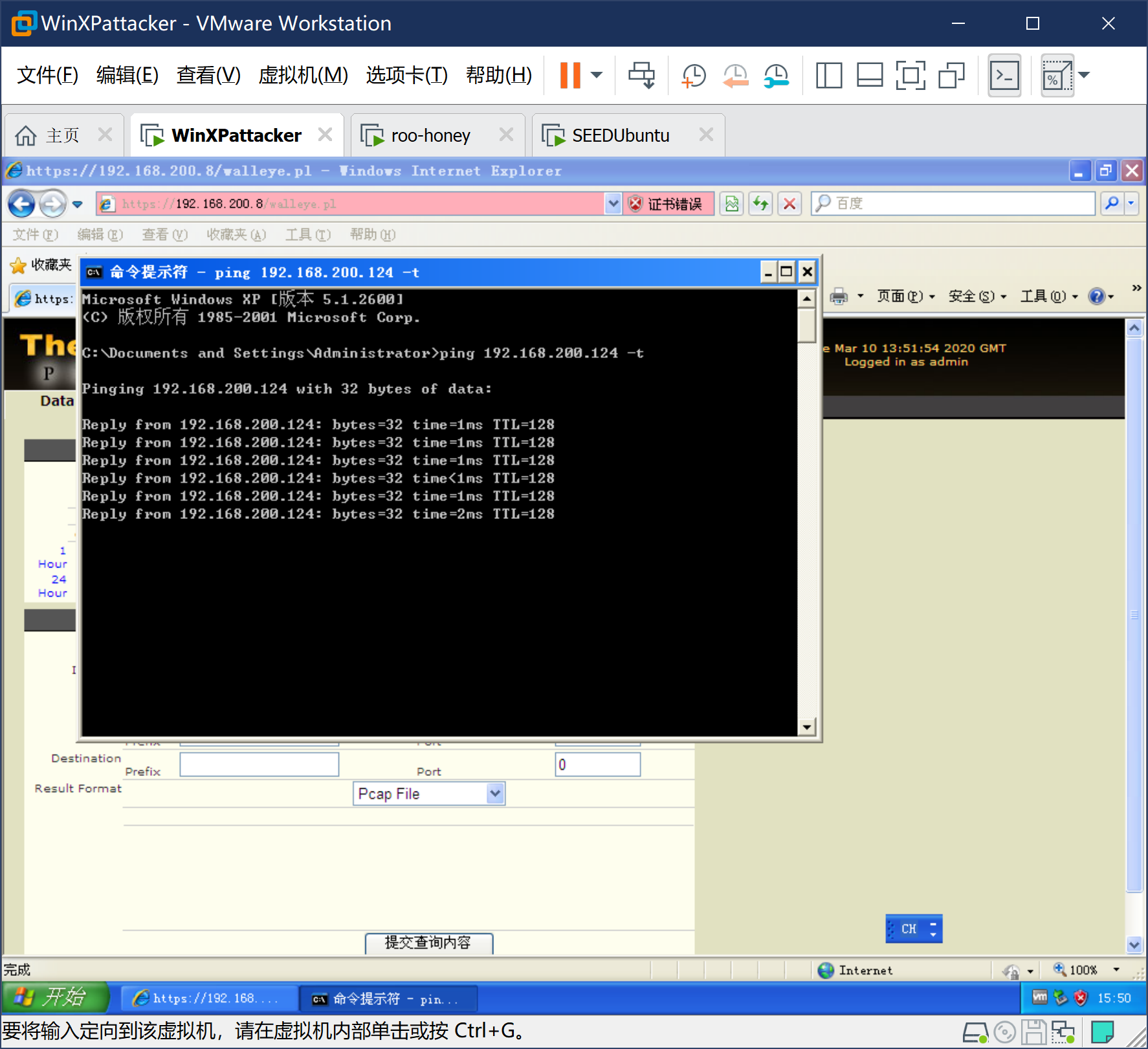
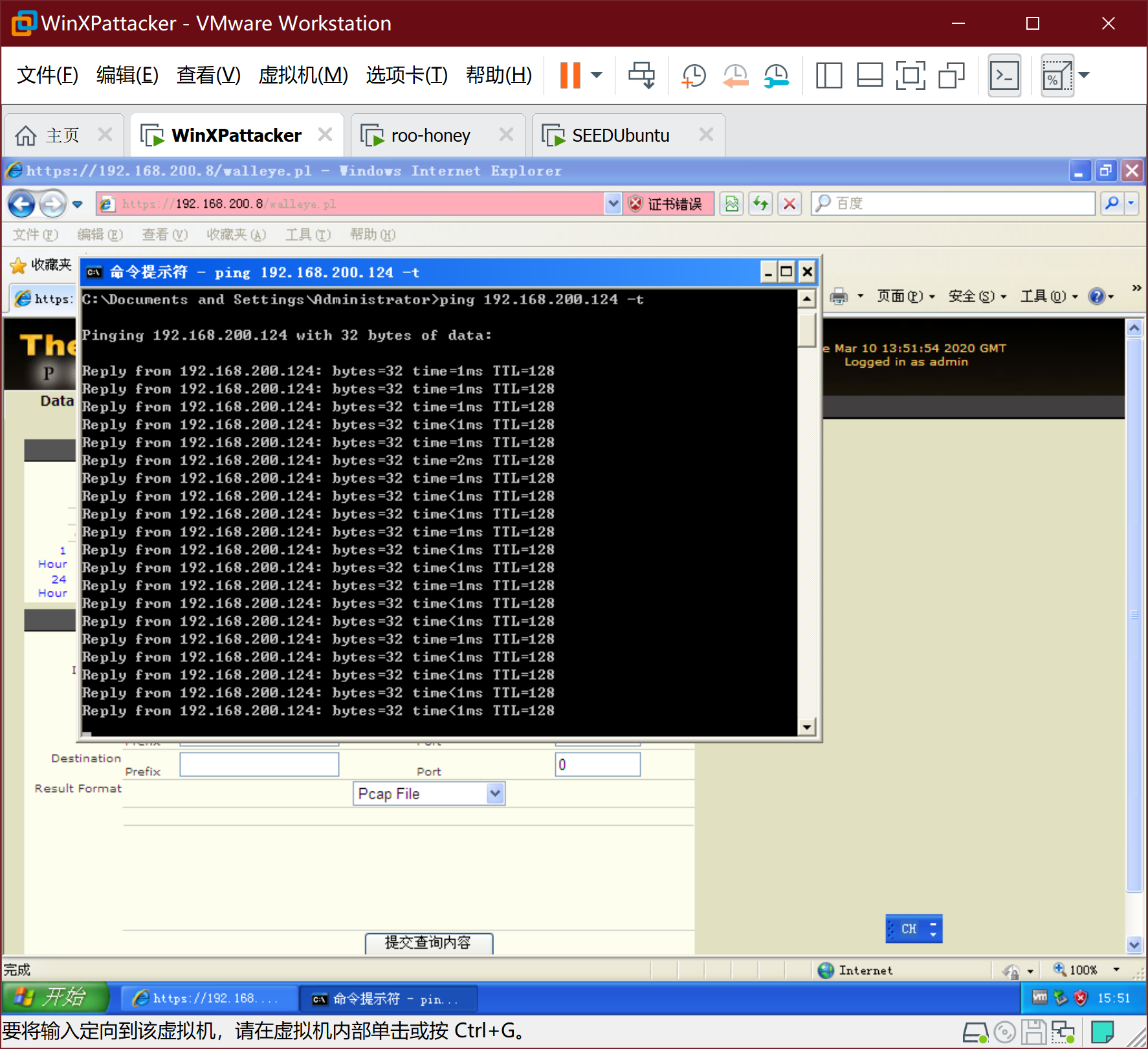
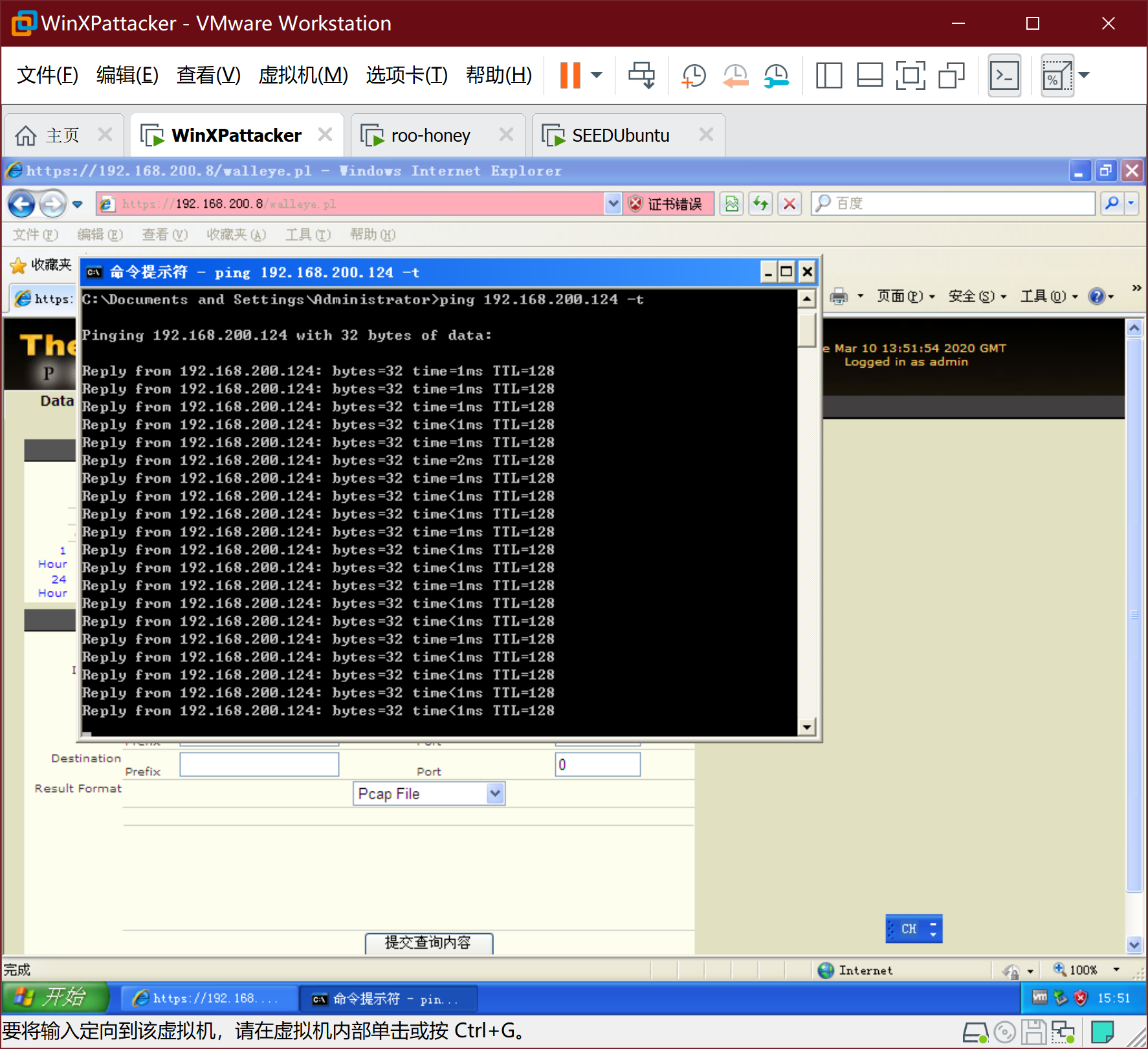
- WinXPattacker ping Win2kServer
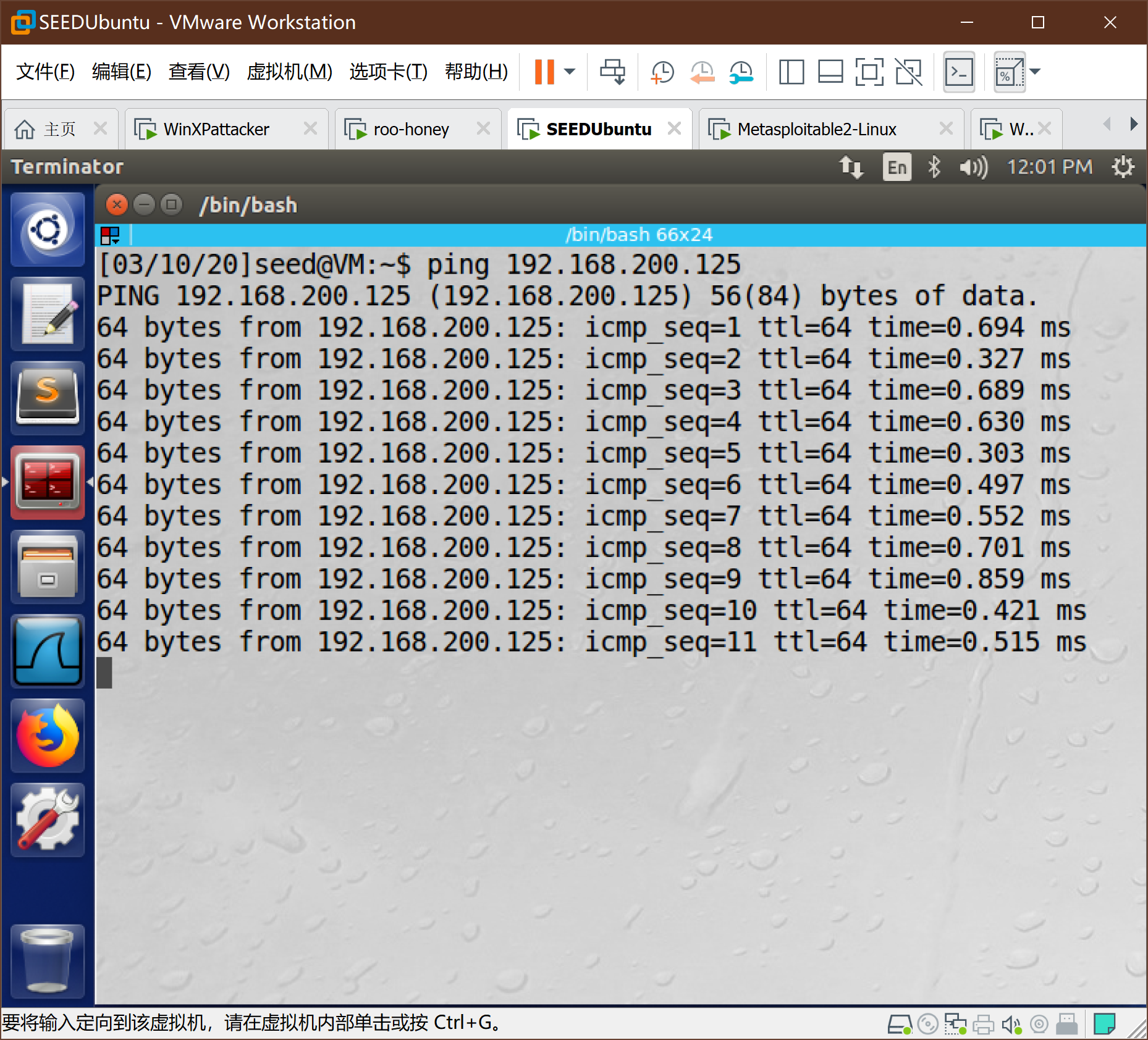
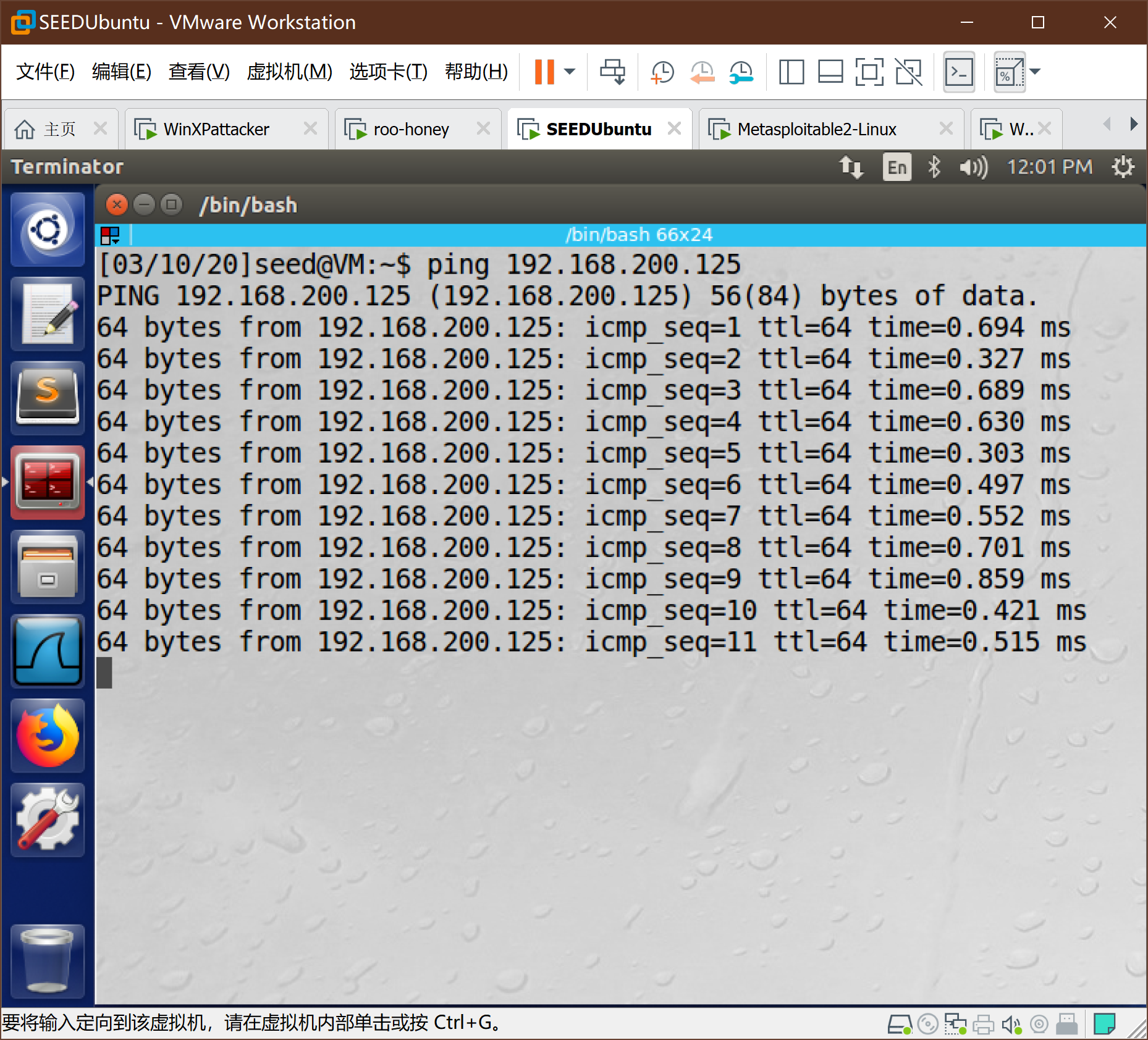
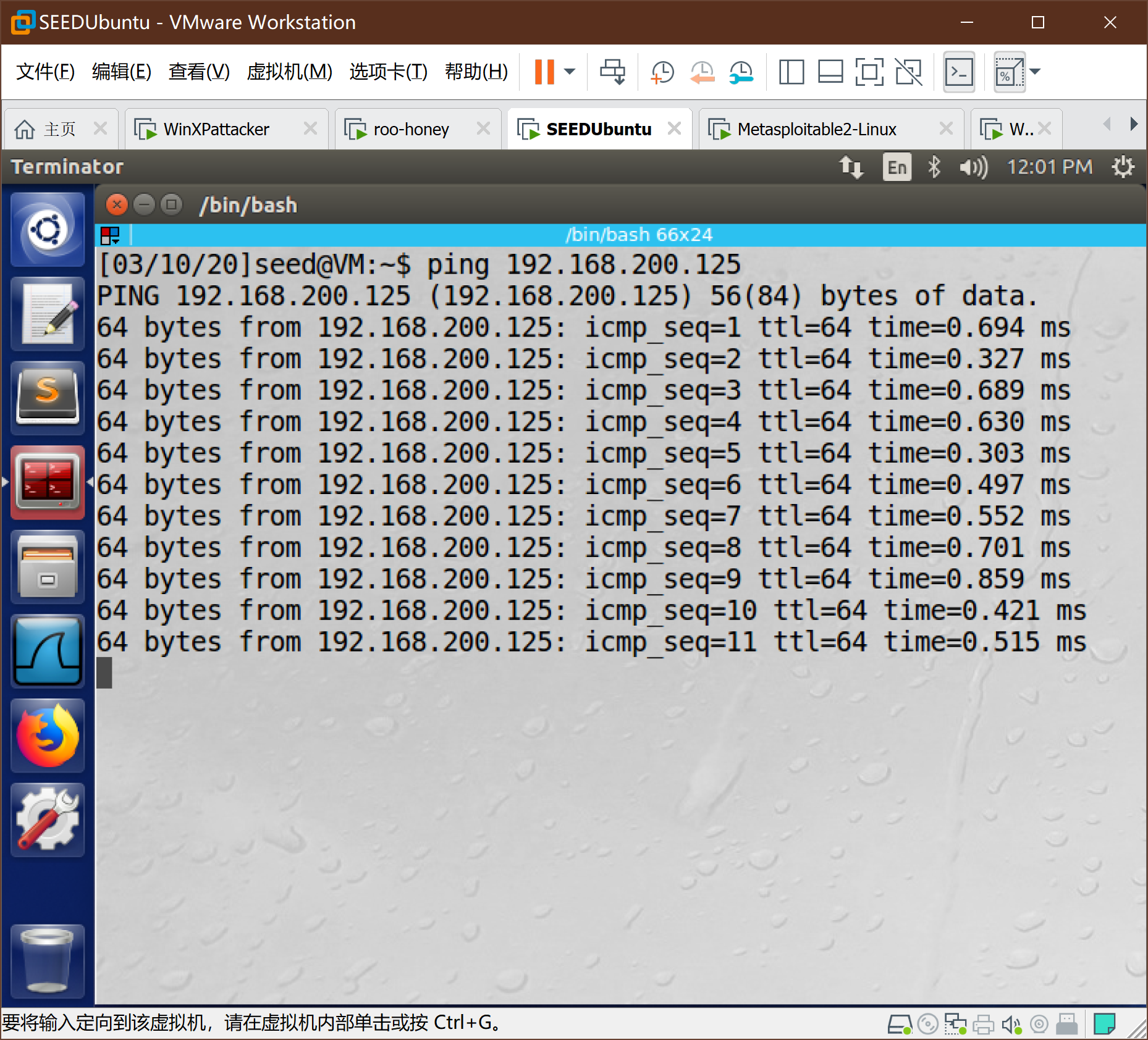
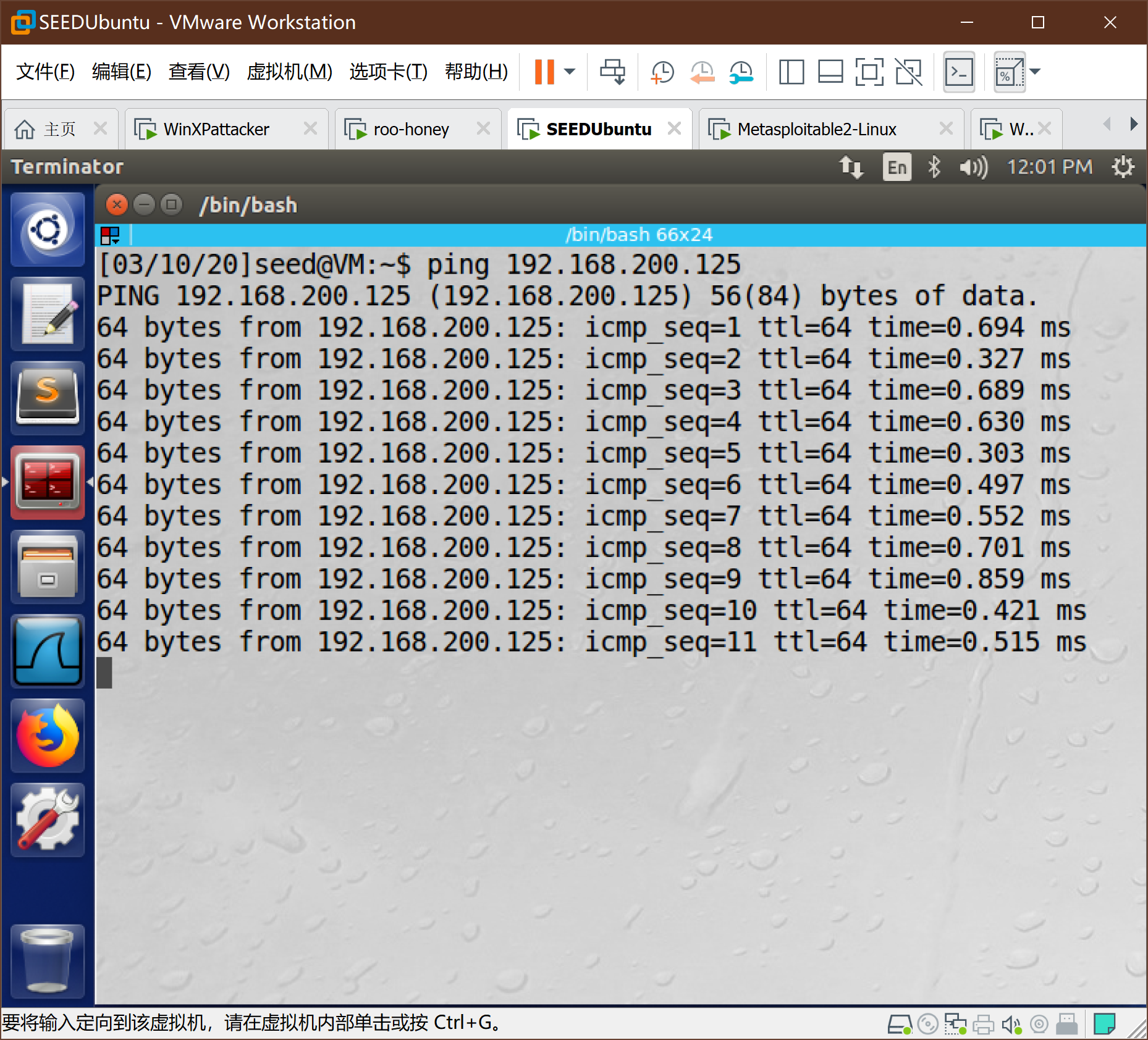
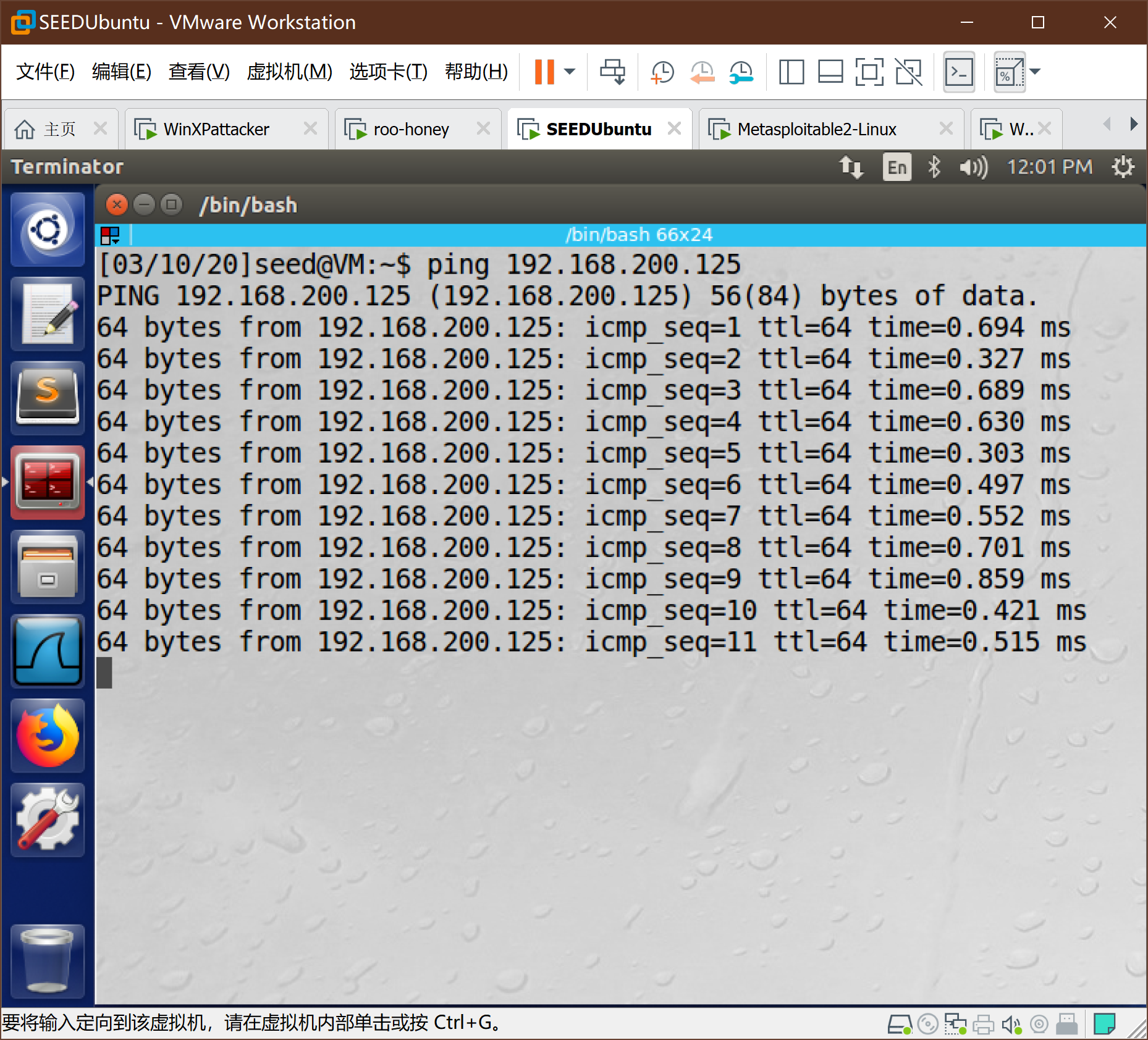
- SEEDUbuntu ping Metasploitable2-Linux
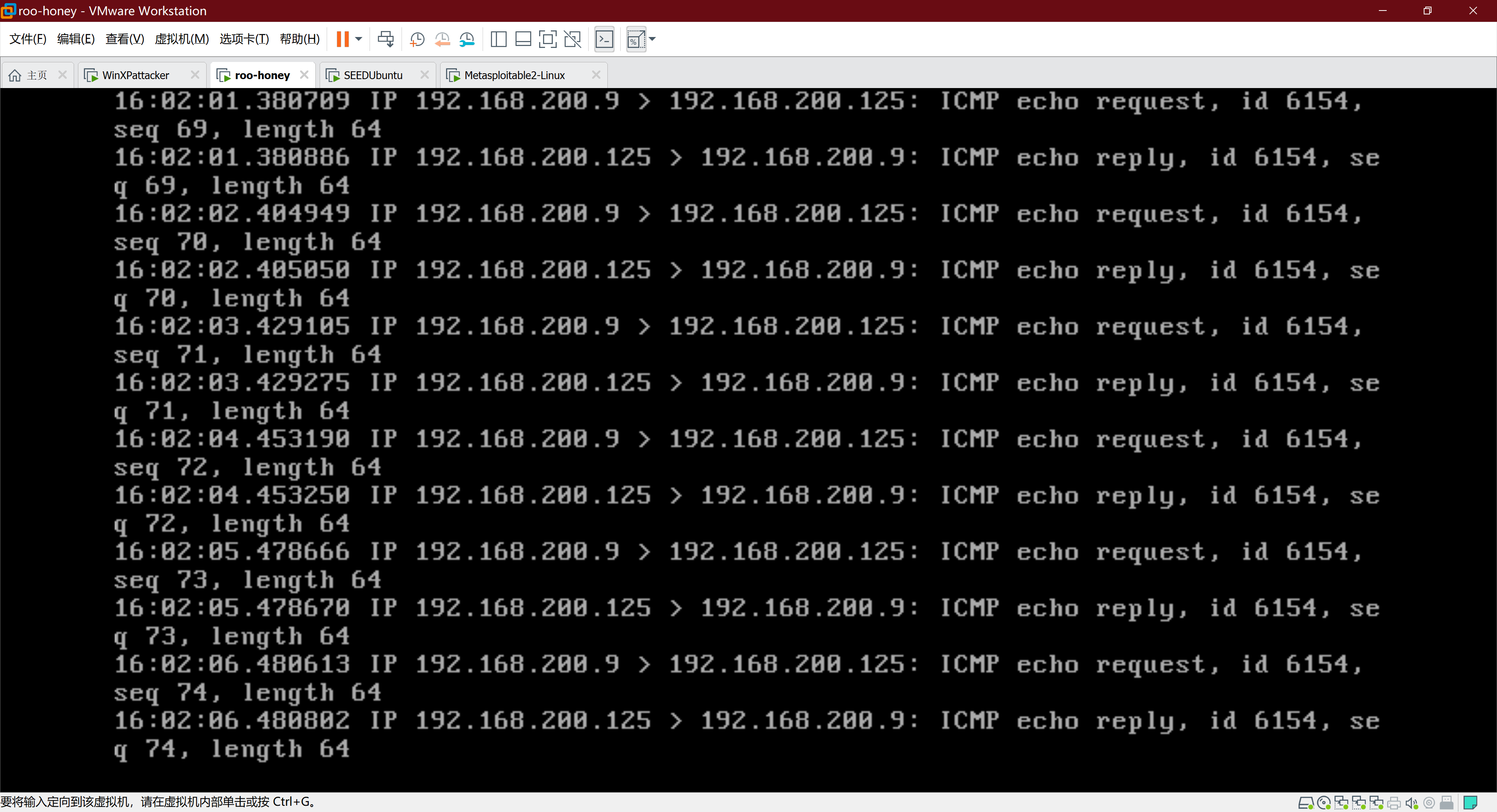
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
Copyright © 2020-2023
润新知
- 此作业所属课程:2019-2020-2-1991&1993《网络攻防实践》
- 本次作业要求:实践一 网络攻防环境的搭建
- 课程目标:学习网络攻防实践
- 本次作业在哪个方面帮助我实现目标:第二章 网络攻防实验环境
攻防环境搭建过程
1、网络架构
2、VM网络设置
-
其中,VMnet8的NAT设置:
-
VMnet8的DHCP设置:
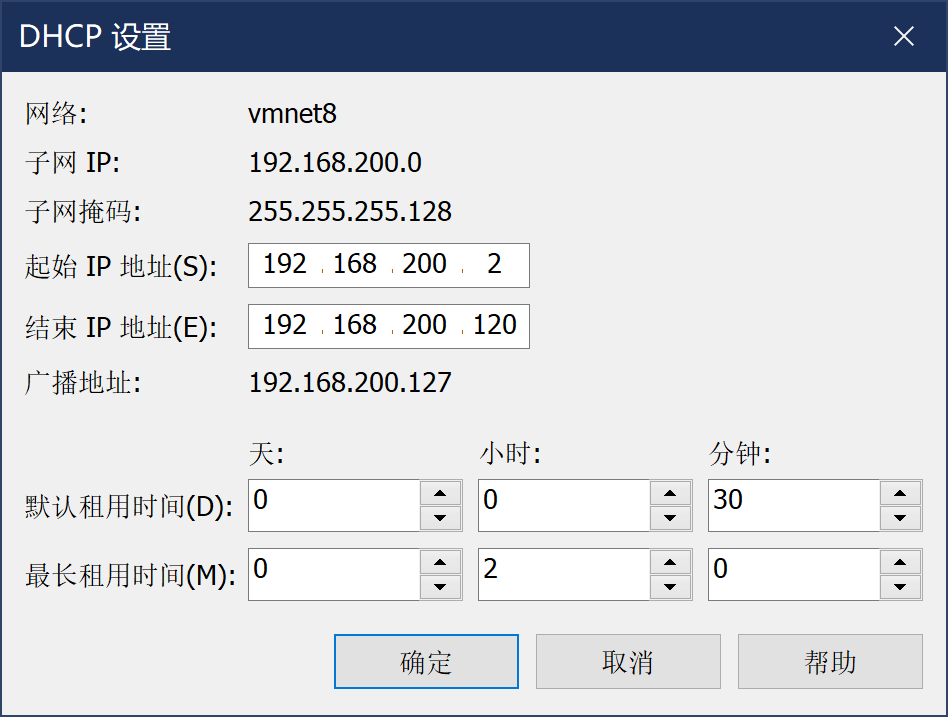
确定,网络适配器完成。
3、安装linux攻击机-Kail
-
kail以VM虚拟机vmx文件的形式提供,通过扫描虚拟机可以直接导入,如下图
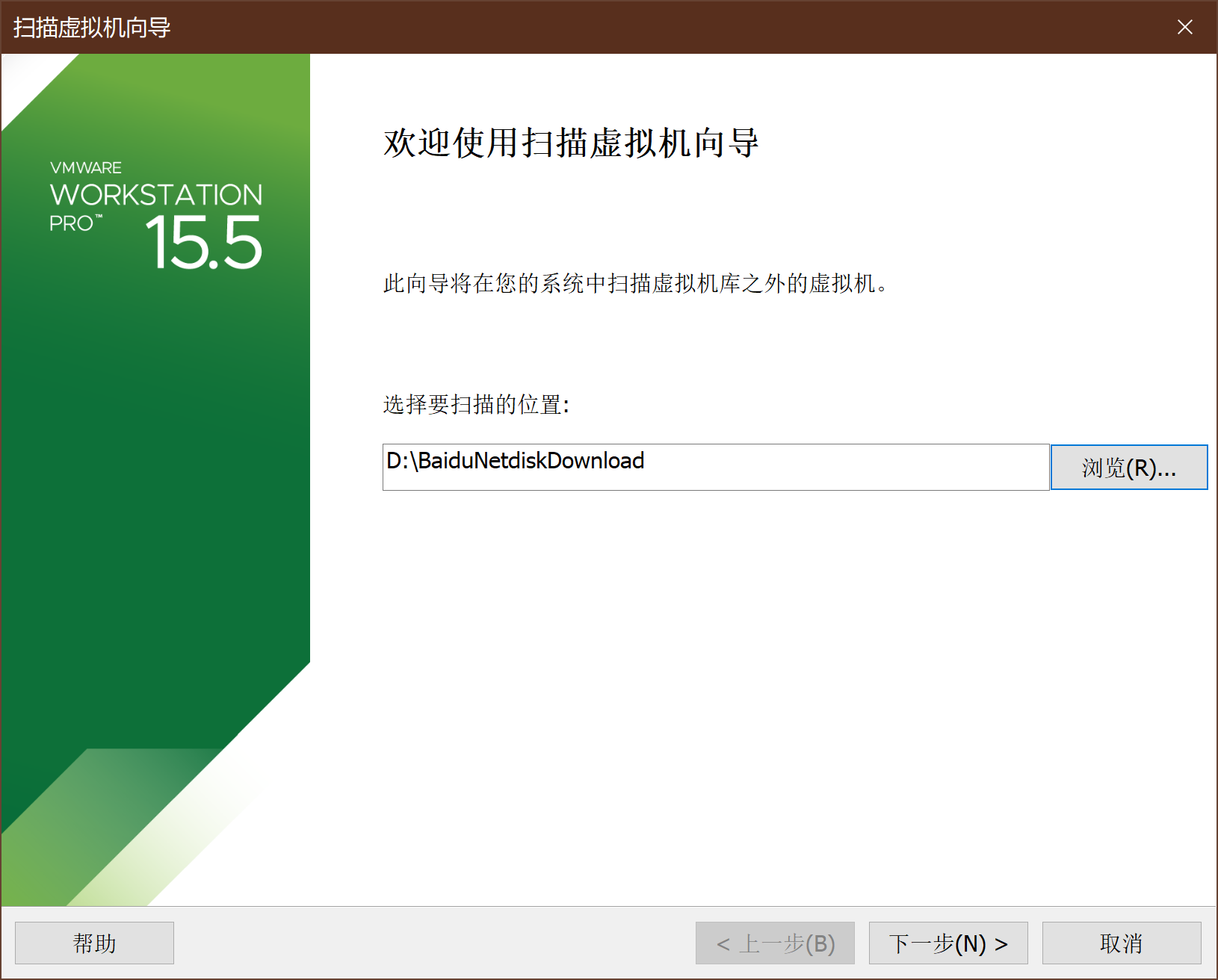
-
虚拟机设置
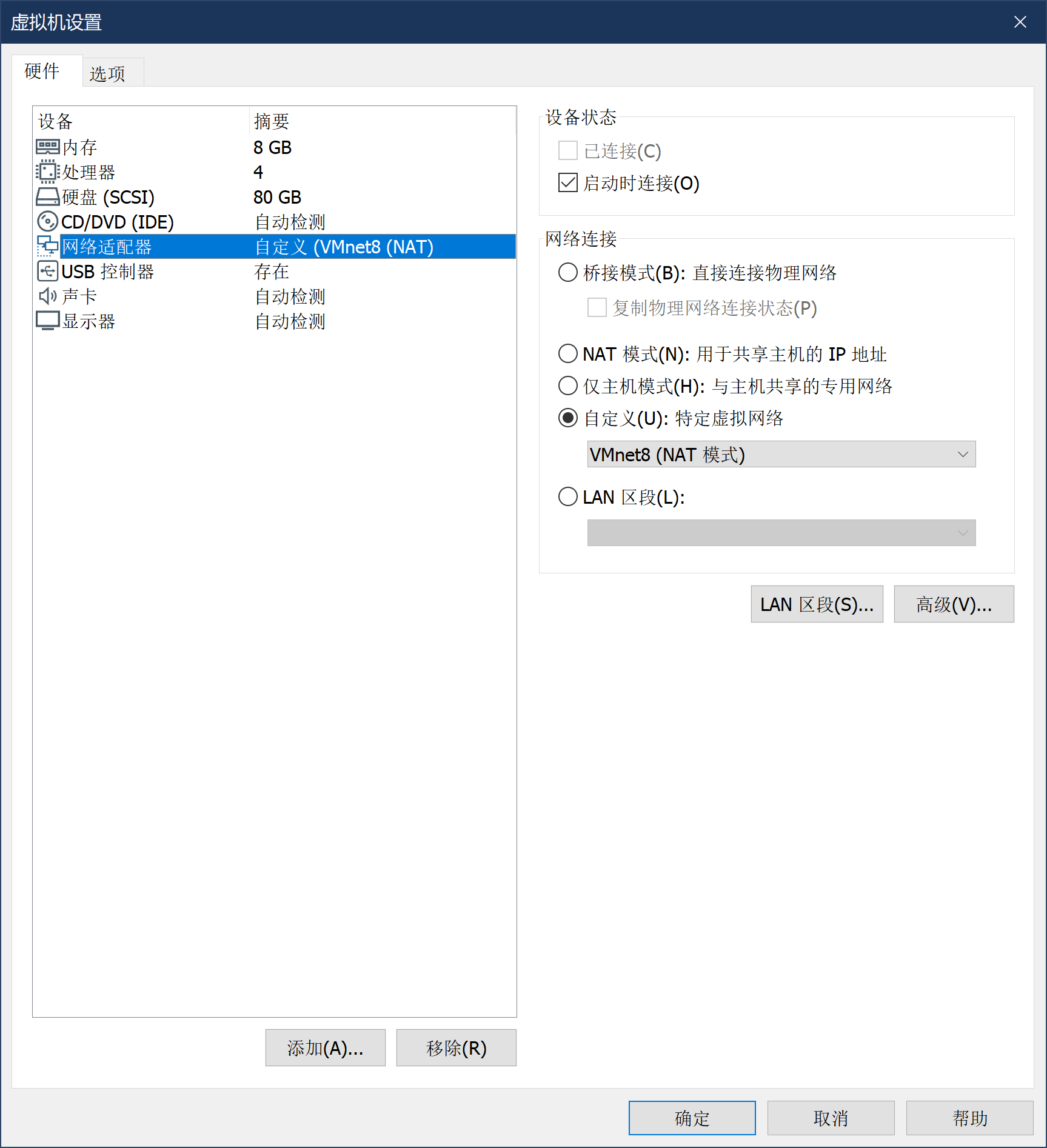
-
启动虚拟机,进行软件设置。Kali的默认用户名为kali,密码kali, root密码kali(先登录kali,后使用su进行提权,禁止直接root登录)

-
登录->提权->安装net-tools(ifconfig包)->查看网络信息。

4、安装Metasploitable2-Linux
-
Metasploitable2-Linux通过VM虚拟机镜像给定,导入方式与Kali相同。Metasploitable2-Linux的网卡设置如下:
-
进入系统,账号msfadmin,密码msfadmin。此处需要手动设置IP地址,具体命令如下:先通过sudo su命令提升权限(密码msfadmin)
-
执行如下命令
vim /etc/rc.local
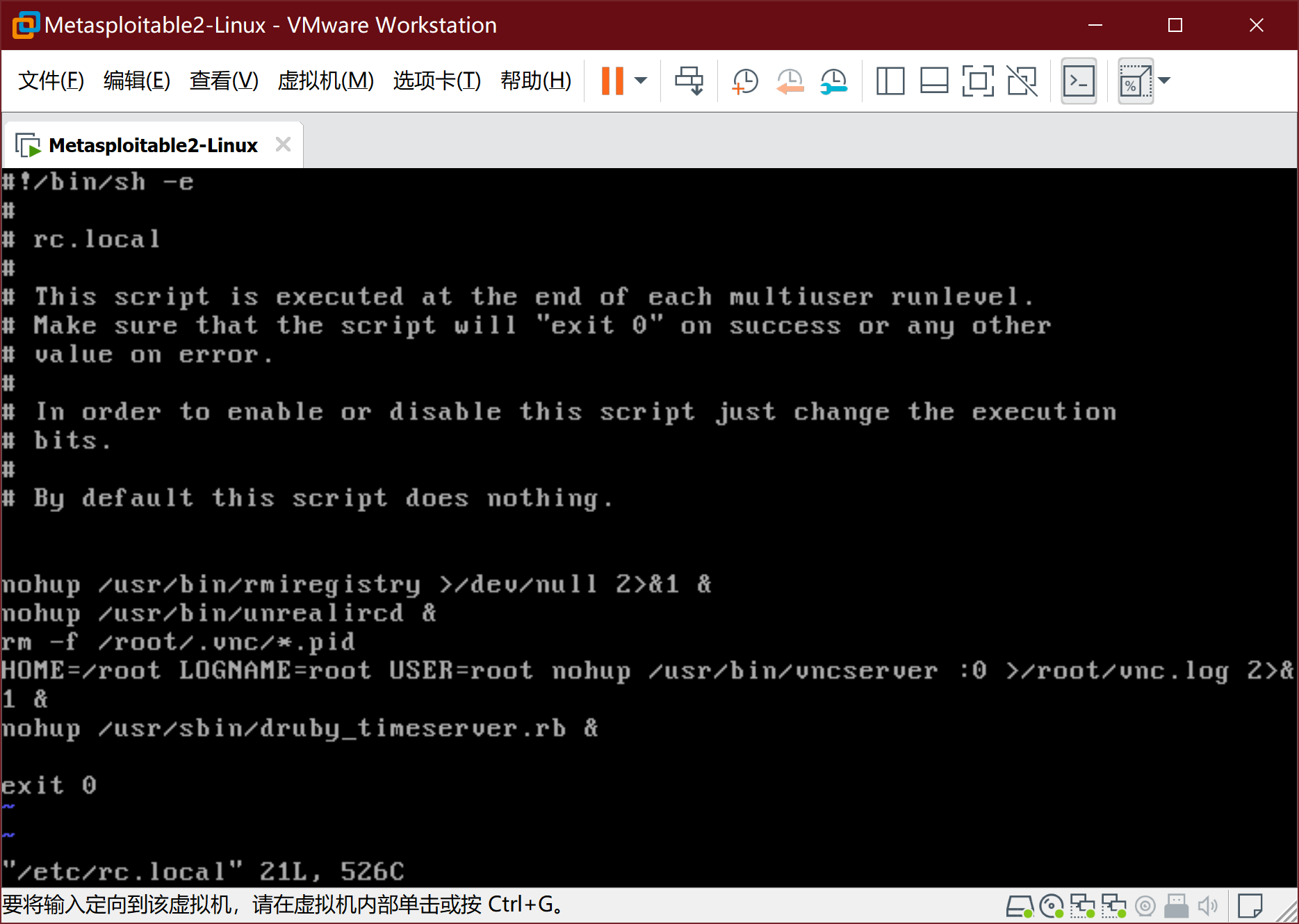
- 按i键进入编辑模式,在文件倒数第二行exit0之前, 插入以下两句
ifconfig eth0 192.168.200.125 netmask 255.255.255.128
route add default gw 192.168.200.1
-
按ESC键,再用 :wq 后回车。之后reboot重启:
-
通过ifconfig查看结果
5、安装windows攻击机-windows Attacker
-
WinXPattacker通过VM虚拟机镜像给定,导入方式与Kali相同。WinXPattacker的网卡设置如下:
-
进入系统 密码mima1234
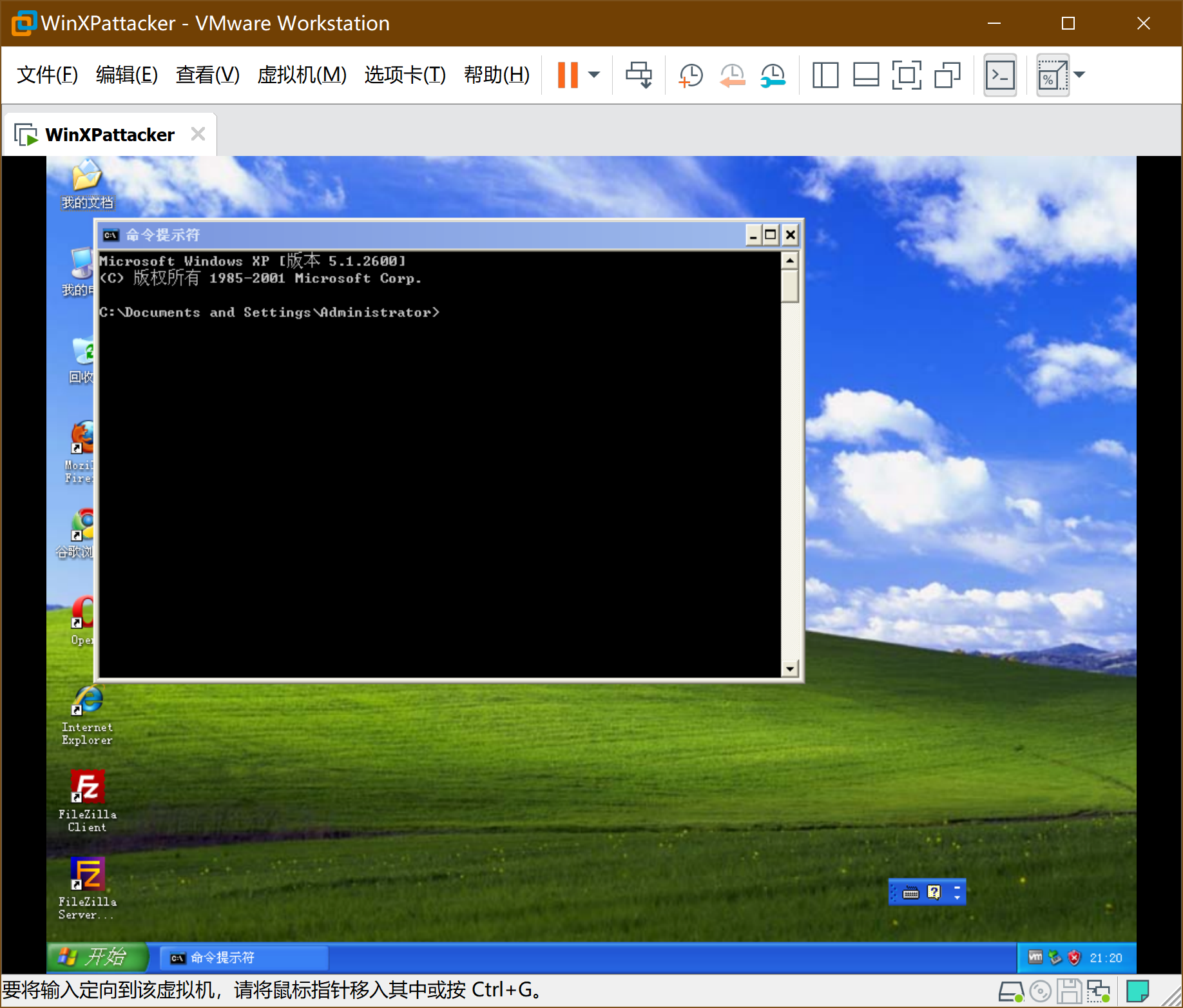
-
此时系统已经通过DHCP获得IP地址,不需要手动配置,但需要找到具体IP。通过ipconfig获得windowsattacker的ip地址:
6、安装windows靶机-win2kServer
-
win2kServer通过虚拟机镜像给予,导入方式和上文的Kali相同。安装之后通过VM的快捷键ALT+CTRL+DEL进入系统(直接发送会被主机拦截),账号administrator,密码mima1234。网卡设置如下:
-
打开虚拟机
7、SEEDUbuntu安装配置
-
SEEDUbuntu通过VM虚拟机vmdk磁盘镜像给定,选择新建虚拟机->自定义安装->兼容XX随便选->稍后安装系统->选择linux、版本ubuntu->名称(SEEDUbuntu)位置(D盘)->下一步->使用现有虚拟磁盘!!!选择seedubuntu的vmdk文件(SEEDUbuntu-16.04-32bit.vmdk)->下一步->保持现有格式。
-
SEEDUbuntu的网卡设置如下:
-
启动虚拟机,账户为seed 密码为dees,开机后通过su命令提权,密码为seedubuntu,ifconfig查看相关网络信息。
8、安装蜜罐网关
-
新建虚拟机->自定义->硬件兼容性
-
稍后安装操作系统
-
选择操作系统->编辑名称->下一步
-
硬件设置->添加镜像
-
网络设置->添加两个网卡
-
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
开始设置->初始化选default
-
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
-
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
9、ping检验
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
- WinXPattacker ping Win2kServer
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
Copyright © 2020-2023
润新知
1、网络架构
2、VM网络设置
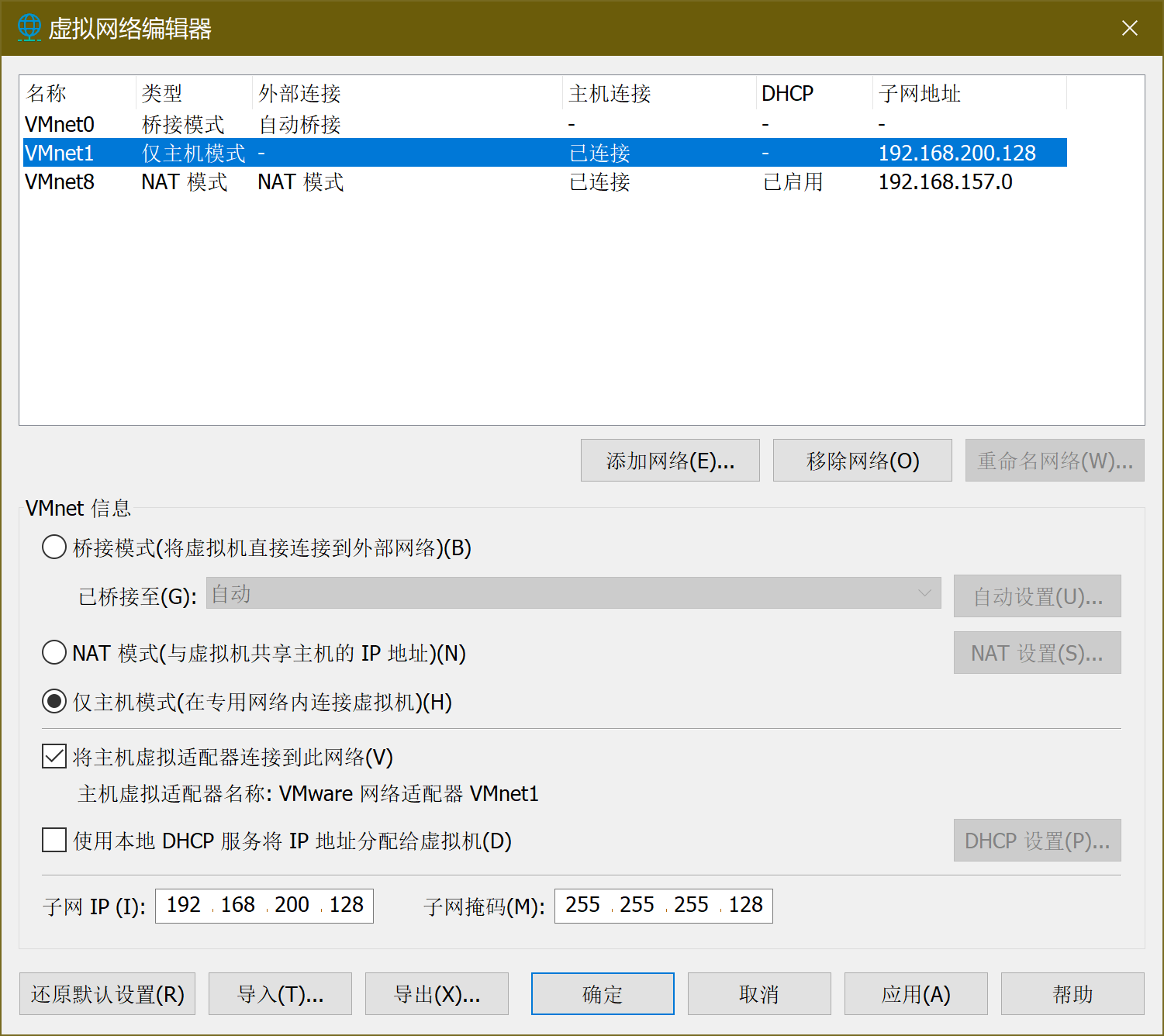
-
其中,VMnet8的NAT设置:
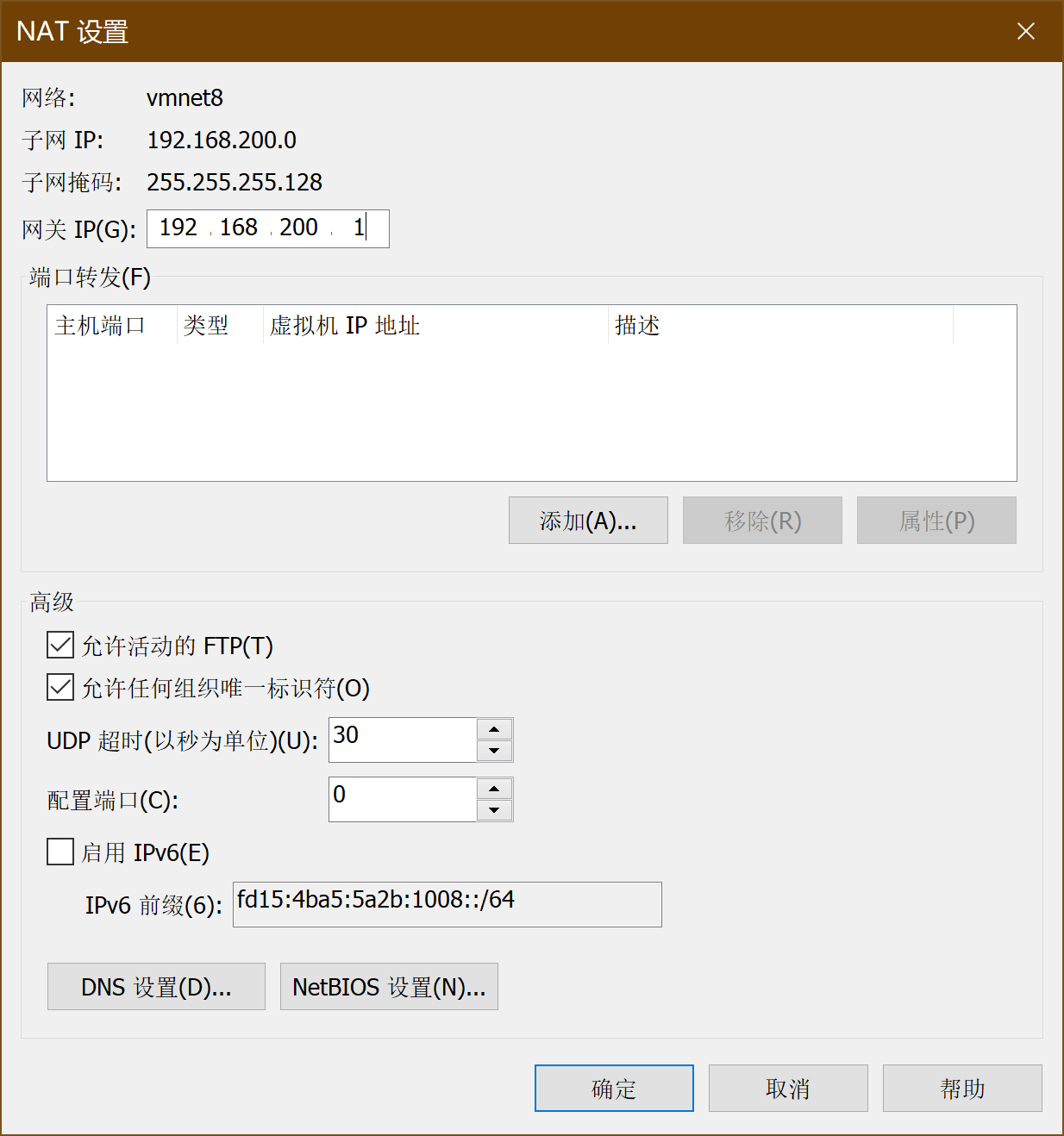
-
VMnet8的DHCP设置:
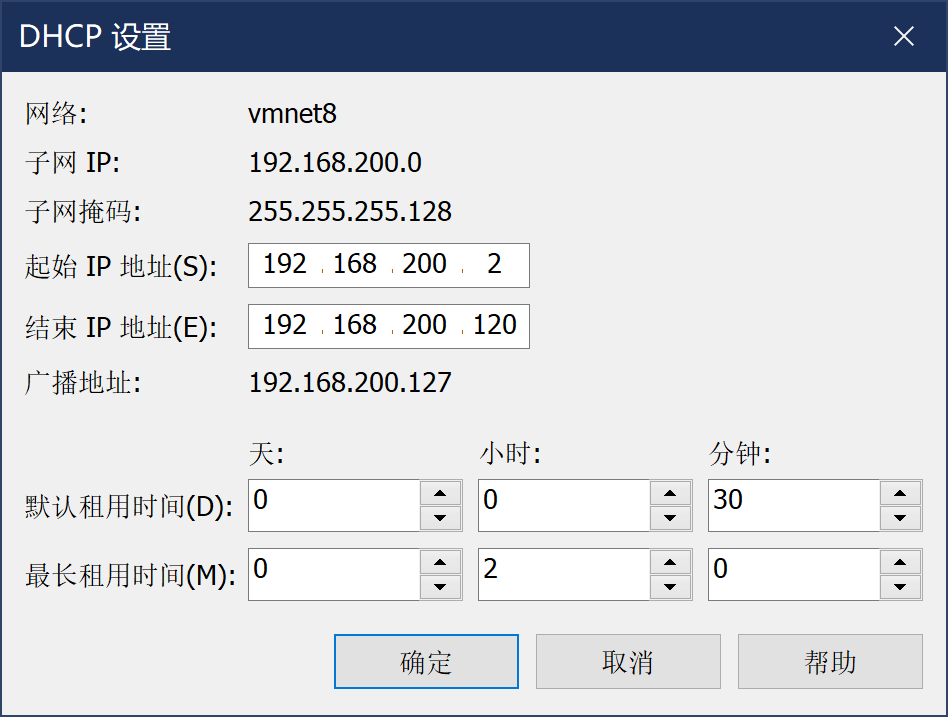
确定,网络适配器完成。
3、安装linux攻击机-Kail
-
kail以VM虚拟机vmx文件的形式提供,通过扫描虚拟机可以直接导入,如下图
-
虚拟机设置
-
启动虚拟机,进行软件设置。Kali的默认用户名为kali,密码kali, root密码kali(先登录kali,后使用su进行提权,禁止直接root登录)

-
登录->提权->安装net-tools(ifconfig包)->查看网络信息。

4、安装Metasploitable2-Linux
-
Metasploitable2-Linux通过VM虚拟机镜像给定,导入方式与Kali相同。Metasploitable2-Linux的网卡设置如下:
-
进入系统,账号msfadmin,密码msfadmin。此处需要手动设置IP地址,具体命令如下:先通过sudo su命令提升权限(密码msfadmin)
-
执行如下命令
vim /etc/rc.local
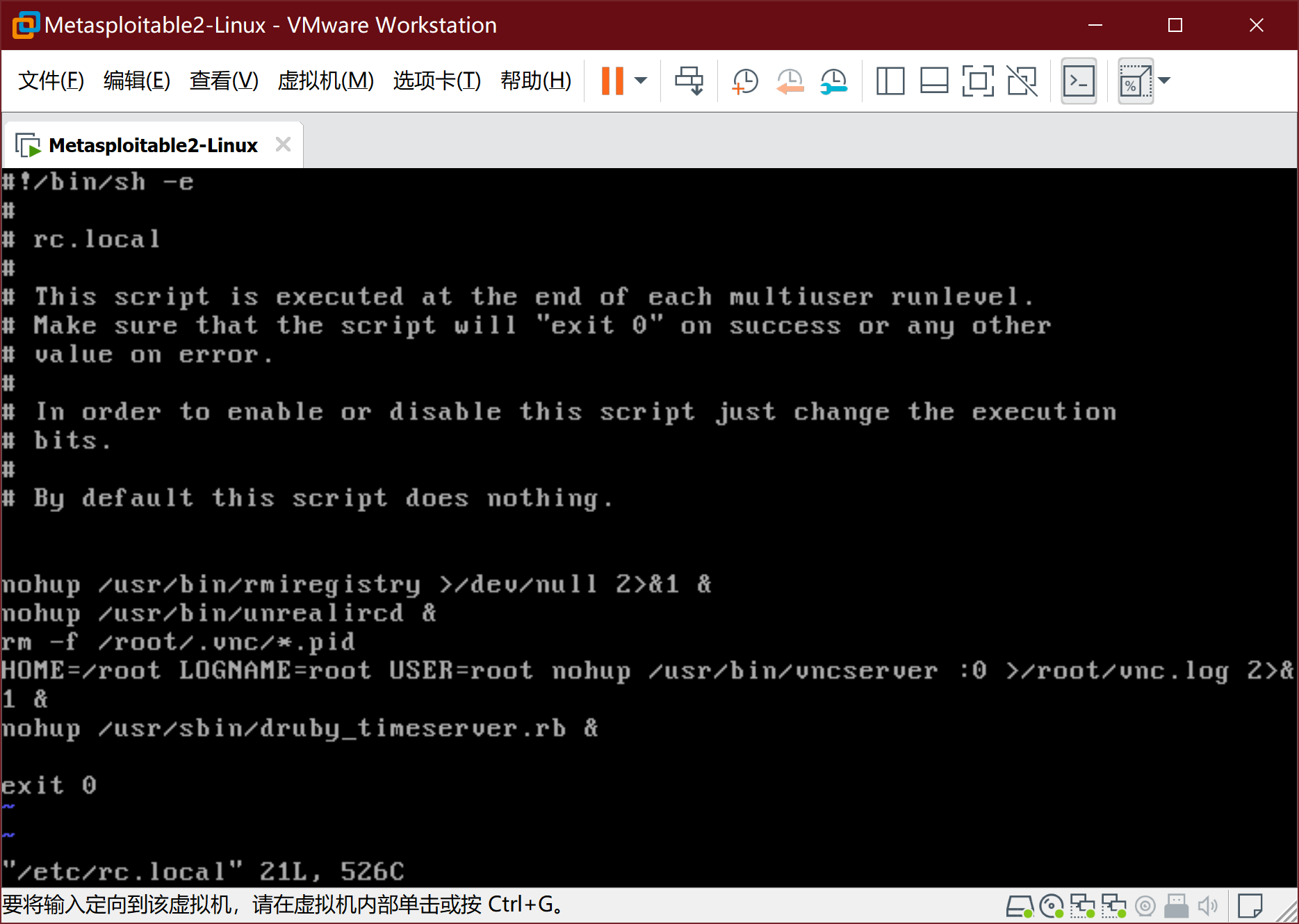
- 按i键进入编辑模式,在文件倒数第二行exit0之前, 插入以下两句
ifconfig eth0 192.168.200.125 netmask 255.255.255.128
route add default gw 192.168.200.1
-
按ESC键,再用 :wq 后回车。之后reboot重启:
-
通过ifconfig查看结果
5、安装windows攻击机-windows Attacker
-
WinXPattacker通过VM虚拟机镜像给定,导入方式与Kali相同。WinXPattacker的网卡设置如下:
-
进入系统 密码mima1234
-
此时系统已经通过DHCP获得IP地址,不需要手动配置,但需要找到具体IP。通过ipconfig获得windowsattacker的ip地址:
6、安装windows靶机-win2kServer
-
win2kServer通过虚拟机镜像给予,导入方式和上文的Kali相同。安装之后通过VM的快捷键ALT+CTRL+DEL进入系统(直接发送会被主机拦截),账号administrator,密码mima1234。网卡设置如下:
-
打开虚拟机
7、SEEDUbuntu安装配置
-
SEEDUbuntu通过VM虚拟机vmdk磁盘镜像给定,选择新建虚拟机->自定义安装->兼容XX随便选->稍后安装系统->选择linux、版本ubuntu->名称(SEEDUbuntu)位置(D盘)->下一步->使用现有虚拟磁盘!!!选择seedubuntu的vmdk文件(SEEDUbuntu-16.04-32bit.vmdk)->下一步->保持现有格式。
-
SEEDUbuntu的网卡设置如下:
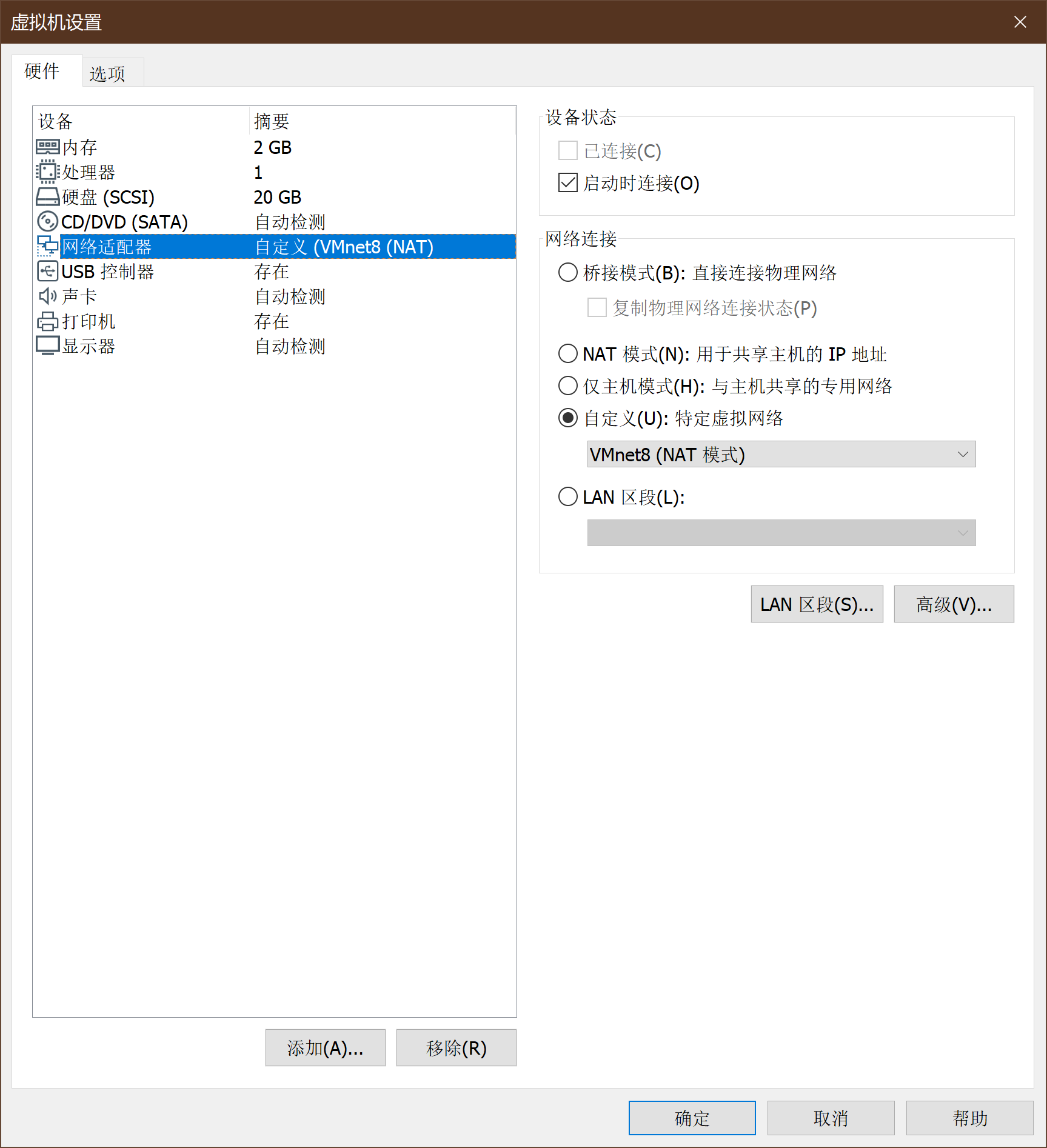
-
启动虚拟机,账户为seed 密码为dees,开机后通过su命令提权,密码为seedubuntu,ifconfig查看相关网络信息。
8、安装蜜罐网关
-
新建虚拟机->自定义->硬件兼容性
-
稍后安装操作系统
-
选择操作系统->编辑名称->下一步
-
硬件设置->添加镜像
-
网络设置->添加两个网卡
-
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
开始设置->初始化选default
-
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
-
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
9、ping检验
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
- WinXPattacker ping Win2kServer
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
Copyright © 2020-2023
润新知
-
kail以VM虚拟机vmx文件的形式提供,通过扫描虚拟机可以直接导入,如下图
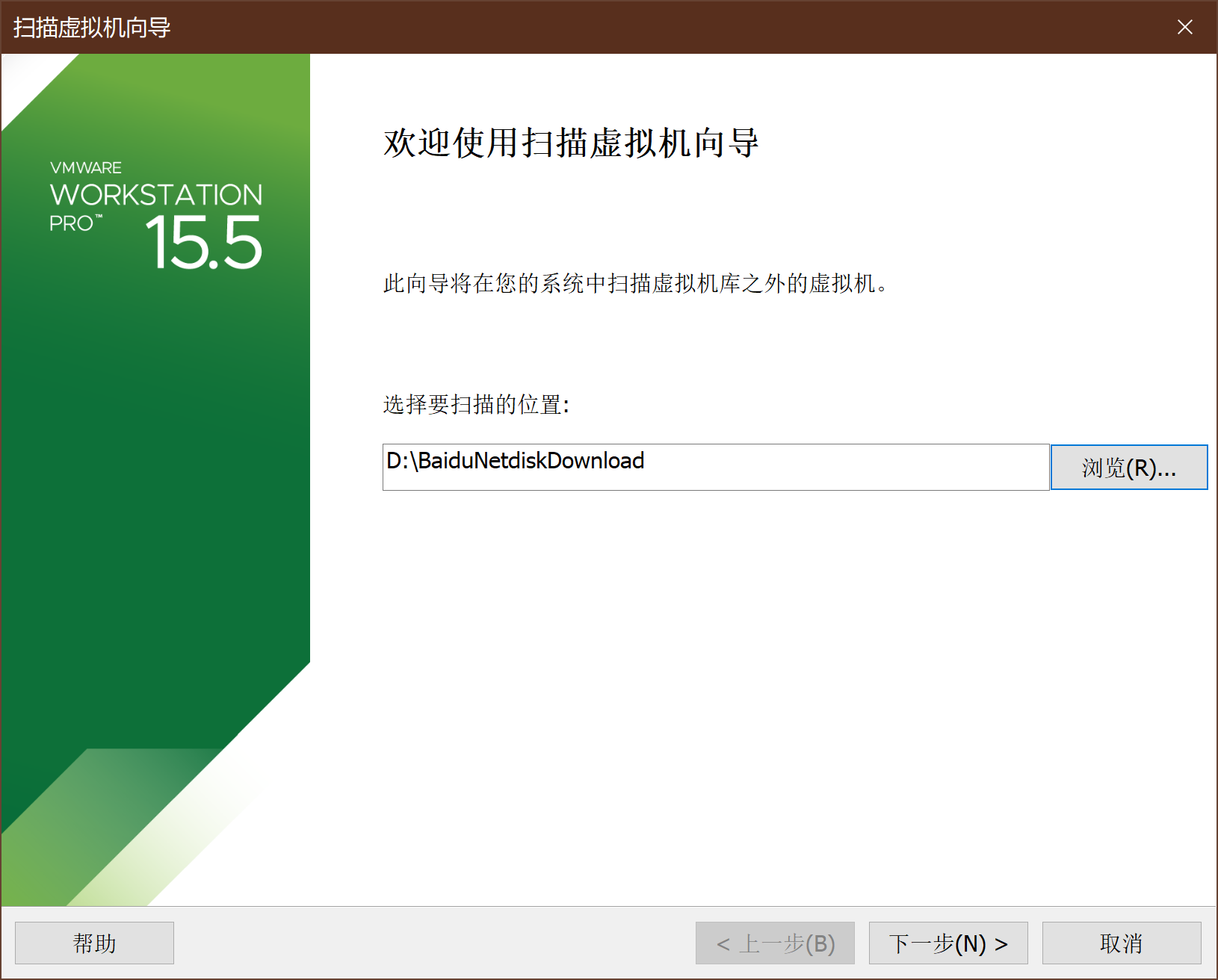
-
虚拟机设置
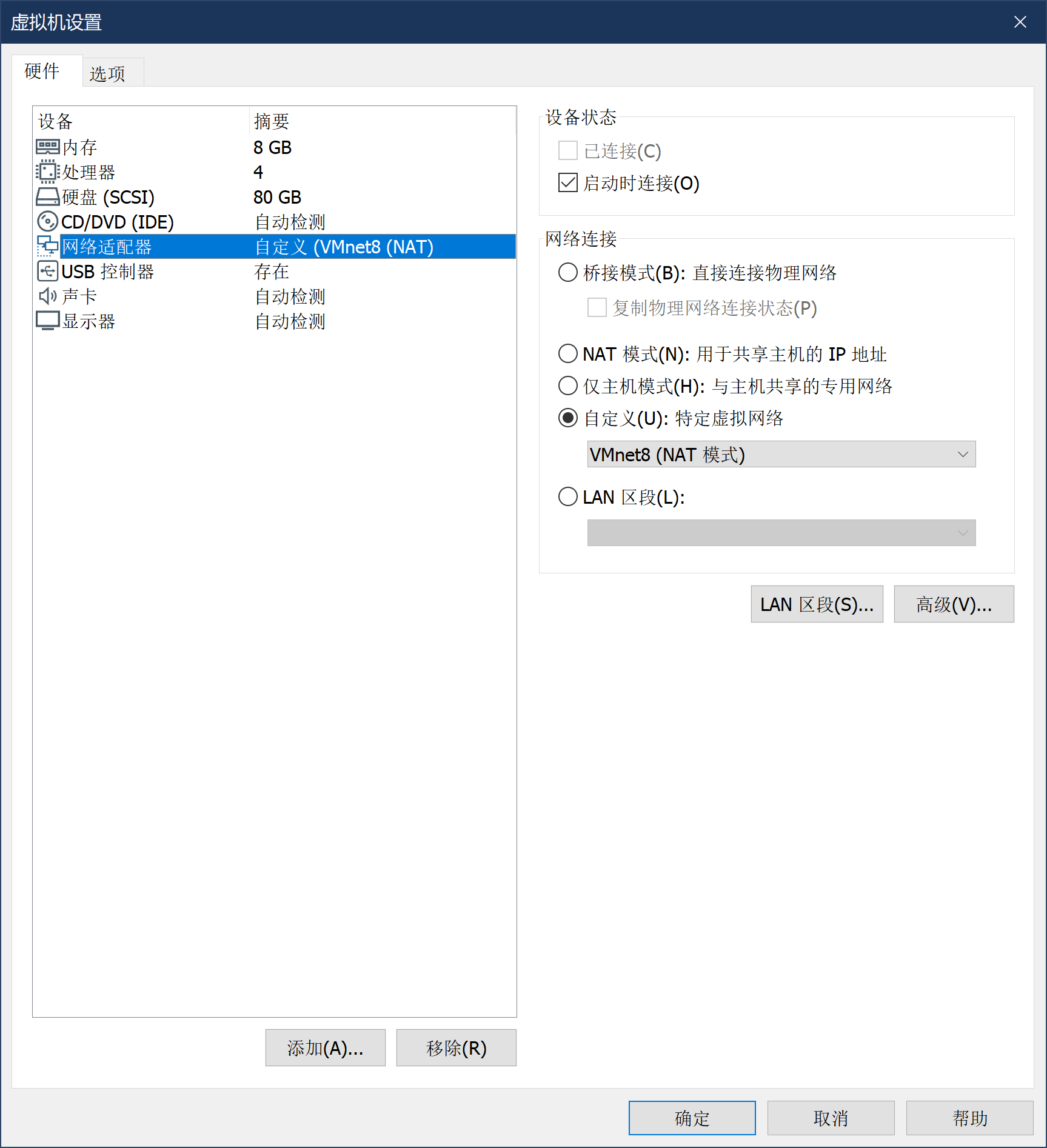
-
启动虚拟机,进行软件设置。Kali的默认用户名为kali,密码kali, root密码kali(先登录kali,后使用su进行提权,禁止直接root登录)

-
登录->提权->安装net-tools(ifconfig包)->查看网络信息。

4、安装Metasploitable2-Linux
-
Metasploitable2-Linux通过VM虚拟机镜像给定,导入方式与Kali相同。Metasploitable2-Linux的网卡设置如下:
-
进入系统,账号msfadmin,密码msfadmin。此处需要手动设置IP地址,具体命令如下:先通过sudo su命令提升权限(密码msfadmin)
-
执行如下命令
vim /etc/rc.local
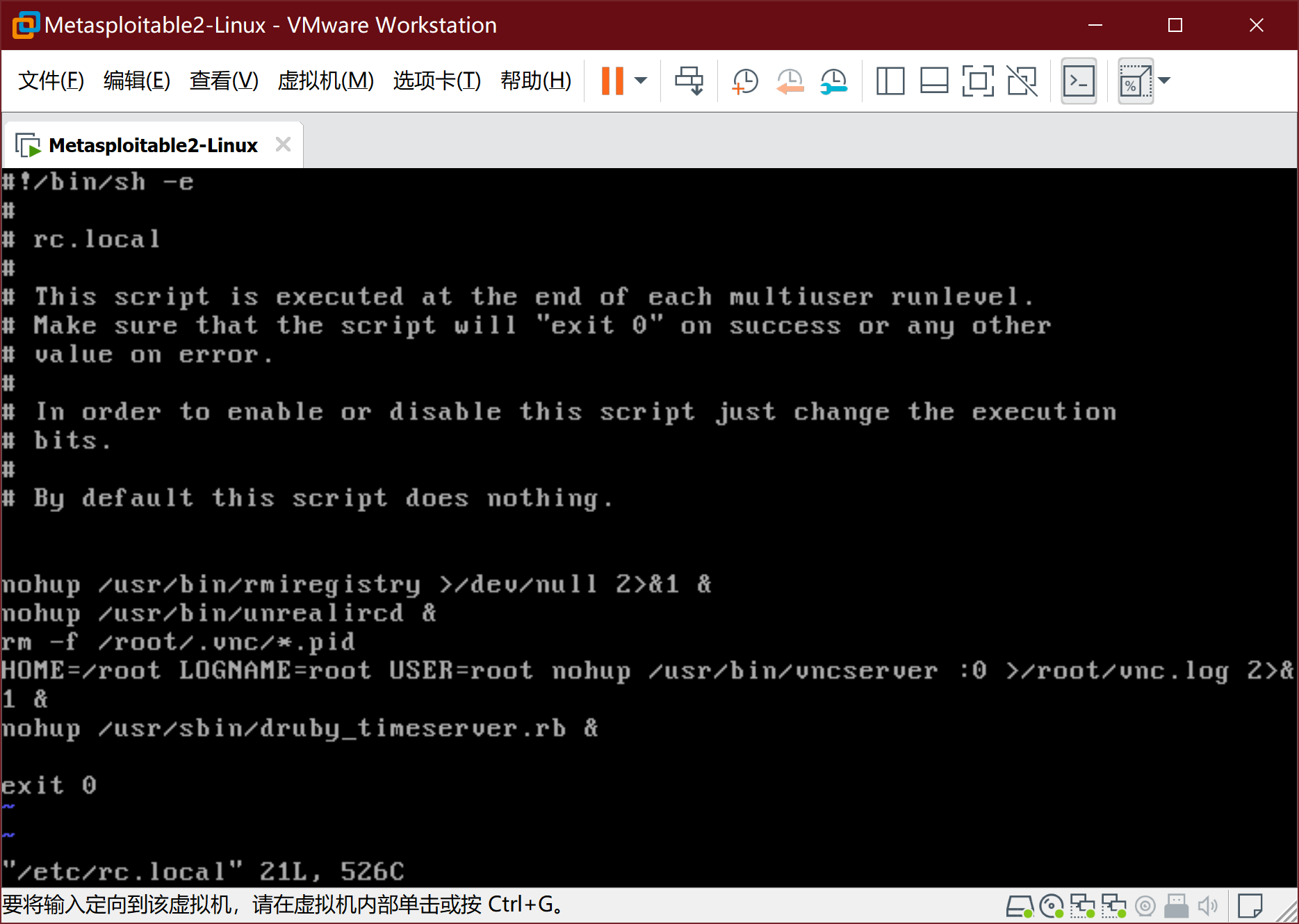
- 按i键进入编辑模式,在文件倒数第二行exit0之前, 插入以下两句
ifconfig eth0 192.168.200.125 netmask 255.255.255.128
route add default gw 192.168.200.1
-
按ESC键,再用 :wq 后回车。之后reboot重启:
-
通过ifconfig查看结果
5、安装windows攻击机-windows Attacker
-
WinXPattacker通过VM虚拟机镜像给定,导入方式与Kali相同。WinXPattacker的网卡设置如下:
-
进入系统 密码mima1234
-
此时系统已经通过DHCP获得IP地址,不需要手动配置,但需要找到具体IP。通过ipconfig获得windowsattacker的ip地址:
6、安装windows靶机-win2kServer
-
win2kServer通过虚拟机镜像给予,导入方式和上文的Kali相同。安装之后通过VM的快捷键ALT+CTRL+DEL进入系统(直接发送会被主机拦截),账号administrator,密码mima1234。网卡设置如下:
-
打开虚拟机
7、SEEDUbuntu安装配置
-
SEEDUbuntu通过VM虚拟机vmdk磁盘镜像给定,选择新建虚拟机->自定义安装->兼容XX随便选->稍后安装系统->选择linux、版本ubuntu->名称(SEEDUbuntu)位置(D盘)->下一步->使用现有虚拟磁盘!!!选择seedubuntu的vmdk文件(SEEDUbuntu-16.04-32bit.vmdk)->下一步->保持现有格式。
-
SEEDUbuntu的网卡设置如下:
-
启动虚拟机,账户为seed 密码为dees,开机后通过su命令提权,密码为seedubuntu,ifconfig查看相关网络信息。
8、安装蜜罐网关
-
新建虚拟机->自定义->硬件兼容性
-
稍后安装操作系统
-
选择操作系统->编辑名称->下一步
-
硬件设置->添加镜像
-
网络设置->添加两个网卡
-
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
开始设置->初始化选default
-
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
-
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
9、ping检验
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
- WinXPattacker ping Win2kServer
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
Copyright © 2020-2023
润新知
-
Metasploitable2-Linux通过VM虚拟机镜像给定,导入方式与Kali相同。Metasploitable2-Linux的网卡设置如下:
-
进入系统,账号msfadmin,密码msfadmin。此处需要手动设置IP地址,具体命令如下:先通过sudo su命令提升权限(密码msfadmin)
-
执行如下命令
vim /etc/rc.local
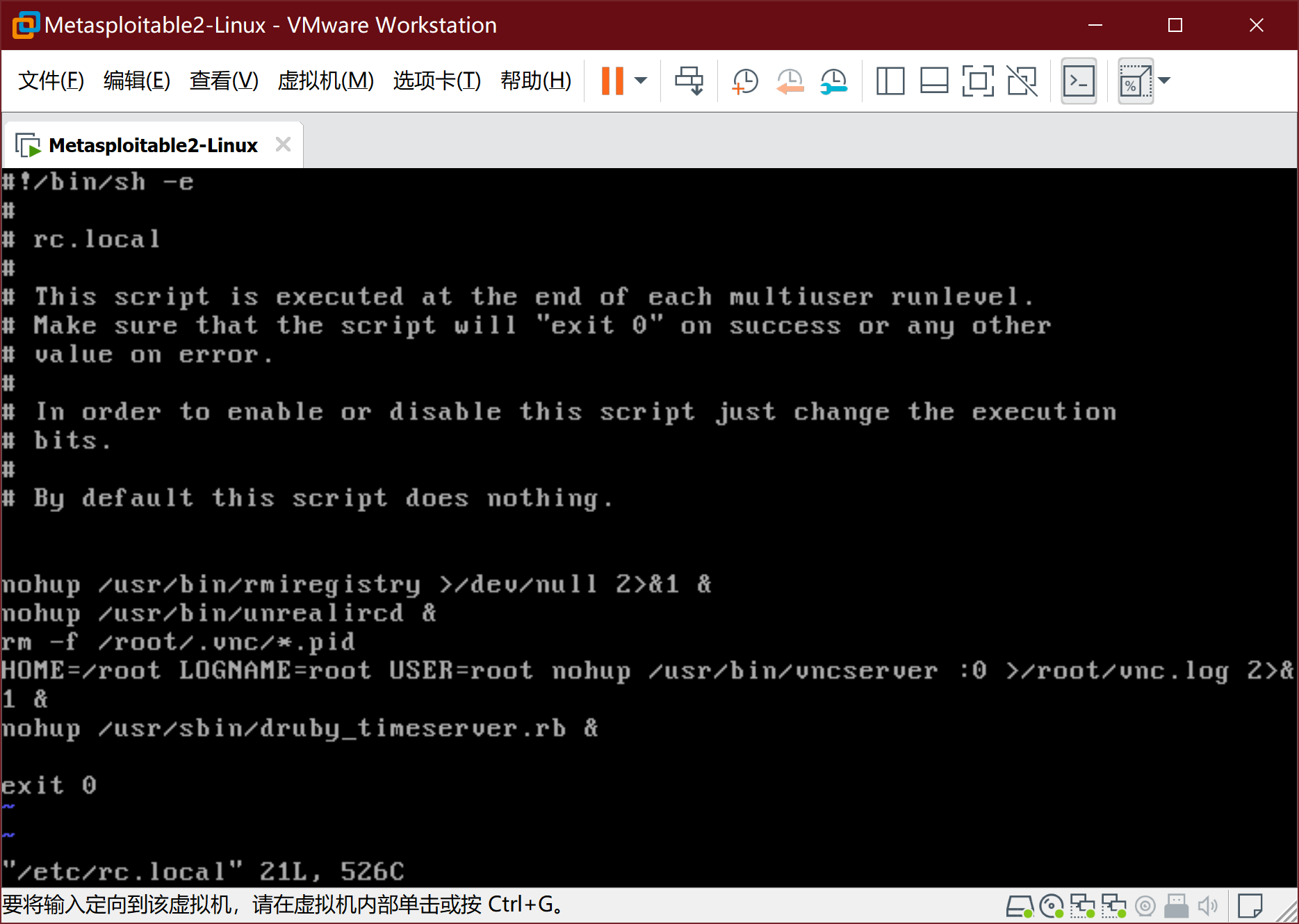
- 按i键进入编辑模式,在文件倒数第二行exit0之前, 插入以下两句
ifconfig eth0 192.168.200.125 netmask 255.255.255.128
route add default gw 192.168.200.1
-
按ESC键,再用 :wq 后回车。之后
reboot重启:
-
通过ifconfig查看结果
5、安装windows攻击机-windows Attacker
-
WinXPattacker通过VM虚拟机镜像给定,导入方式与Kali相同。WinXPattacker的网卡设置如下:
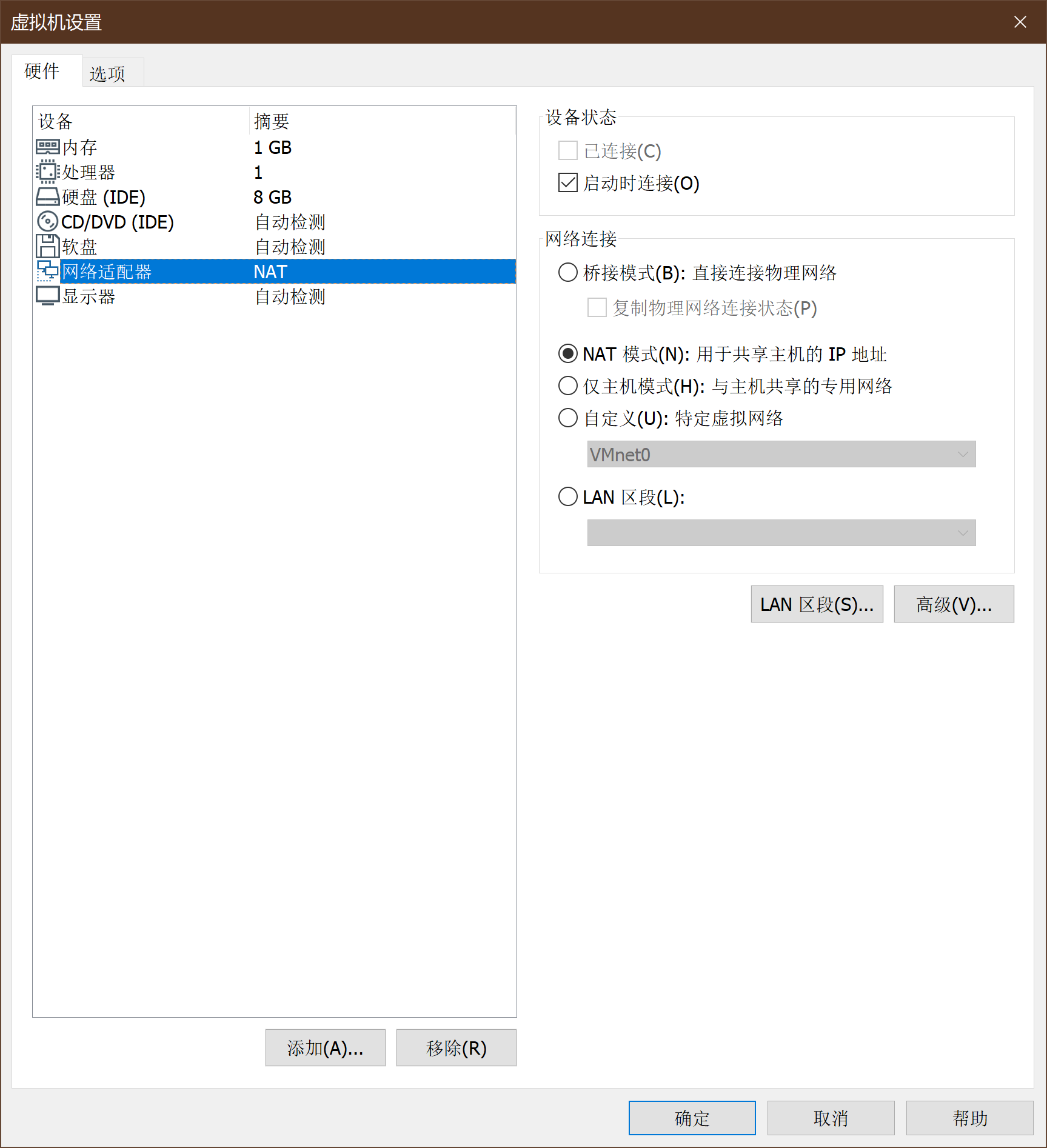
-
进入系统 密码mima1234
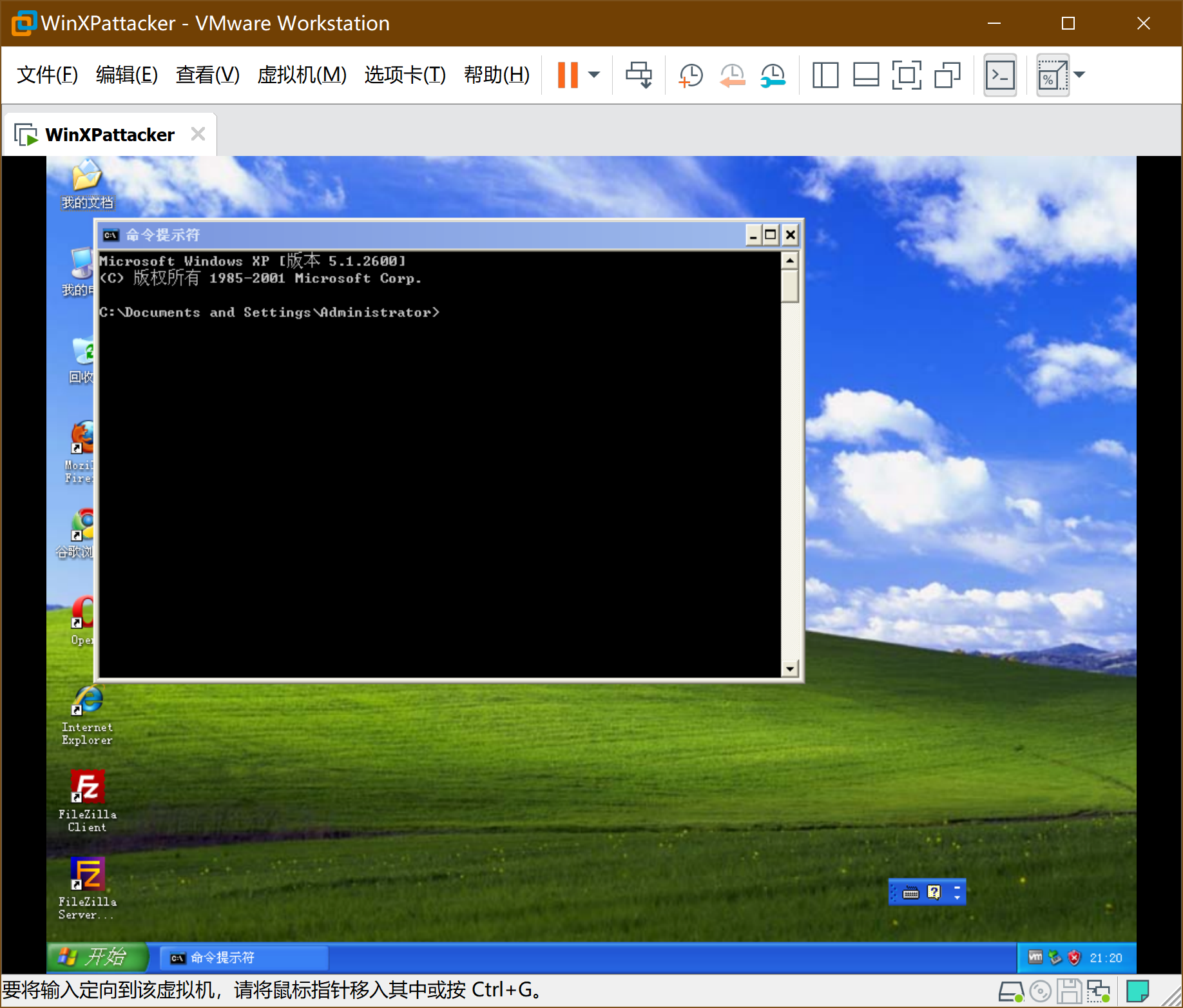
-
此时系统已经通过DHCP获得IP地址,不需要手动配置,但需要找到具体IP。通过ipconfig获得windowsattacker的ip地址:
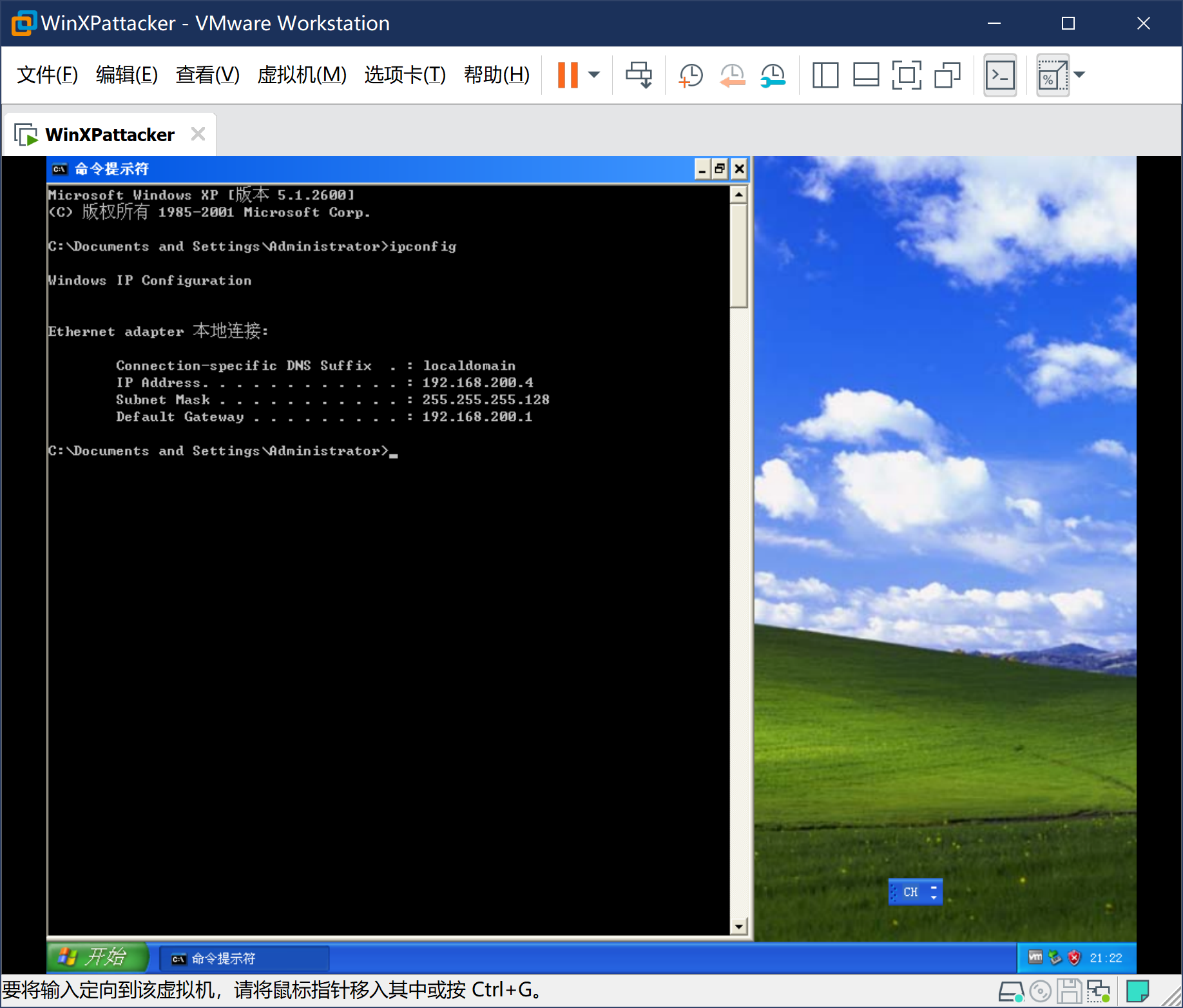
6、安装windows靶机-win2kServer
-
win2kServer通过虚拟机镜像给予,导入方式和上文的Kali相同。安装之后通过VM的快捷键ALT+CTRL+DEL进入系统(直接发送会被主机拦截),账号administrator,密码mima1234。网卡设置如下:
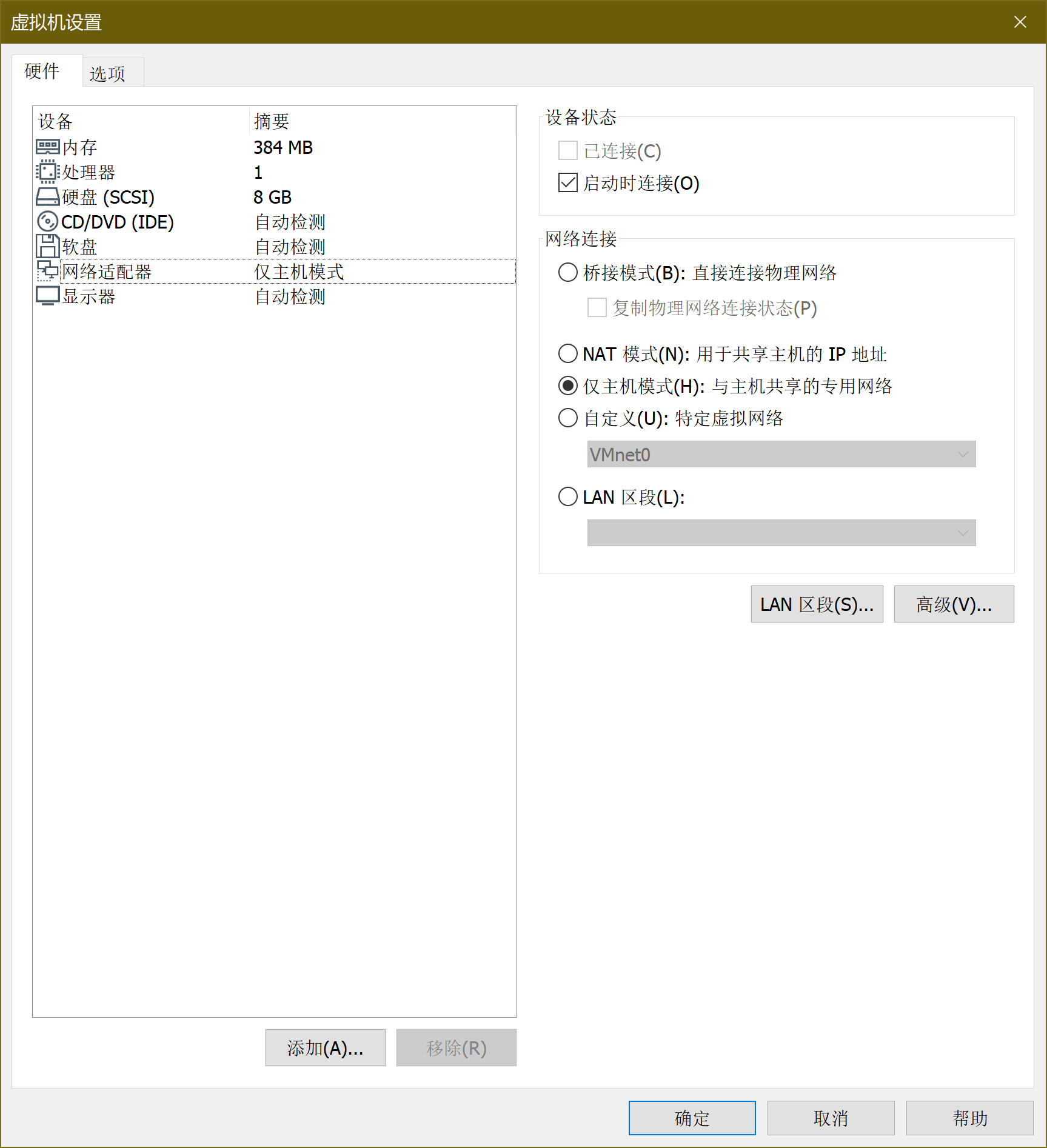
-
打开虚拟机
7、SEEDUbuntu安装配置
-
SEEDUbuntu通过VM虚拟机vmdk磁盘镜像给定,选择新建虚拟机->自定义安装->兼容XX随便选->稍后安装系统->选择linux、版本ubuntu->名称(SEEDUbuntu)位置(D盘)->下一步->使用现有虚拟磁盘!!!选择seedubuntu的vmdk文件(SEEDUbuntu-16.04-32bit.vmdk)->下一步->保持现有格式。
-
SEEDUbuntu的网卡设置如下:
-
启动虚拟机,账户为seed 密码为dees,开机后通过su命令提权,密码为seedubuntu,ifconfig查看相关网络信息。
8、安装蜜罐网关
-
新建虚拟机->自定义->硬件兼容性
-
稍后安装操作系统
-
选择操作系统->编辑名称->下一步
-
硬件设置->添加镜像
-
网络设置->添加两个网卡
-
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
开始设置->初始化选default
-
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
-
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
9、ping检验
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
- WinXPattacker ping Win2kServer
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
Copyright © 2020-2023
润新知
-
WinXPattacker通过VM虚拟机镜像给定,导入方式与Kali相同。WinXPattacker的网卡设置如下:
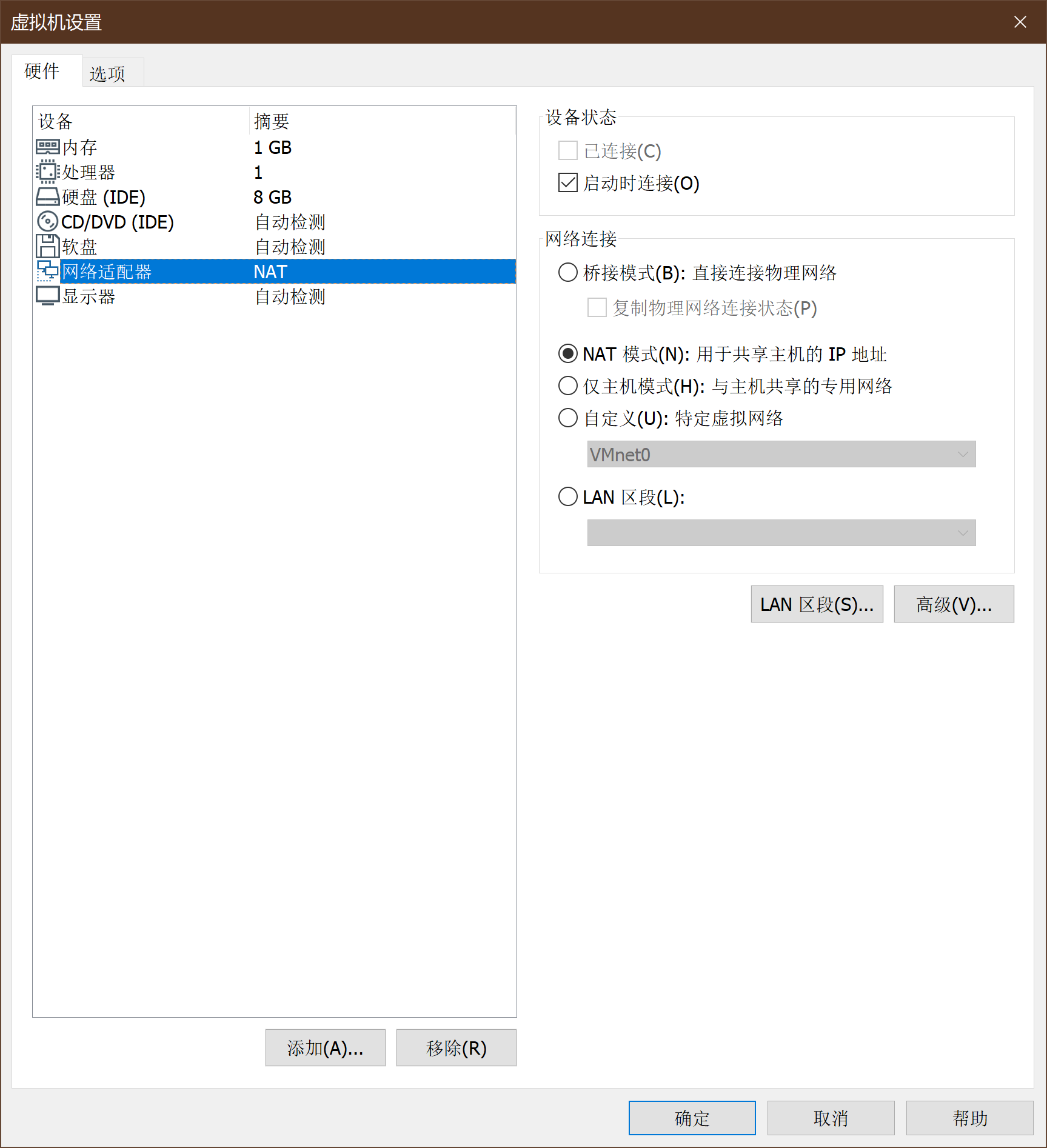
-
进入系统 密码mima1234
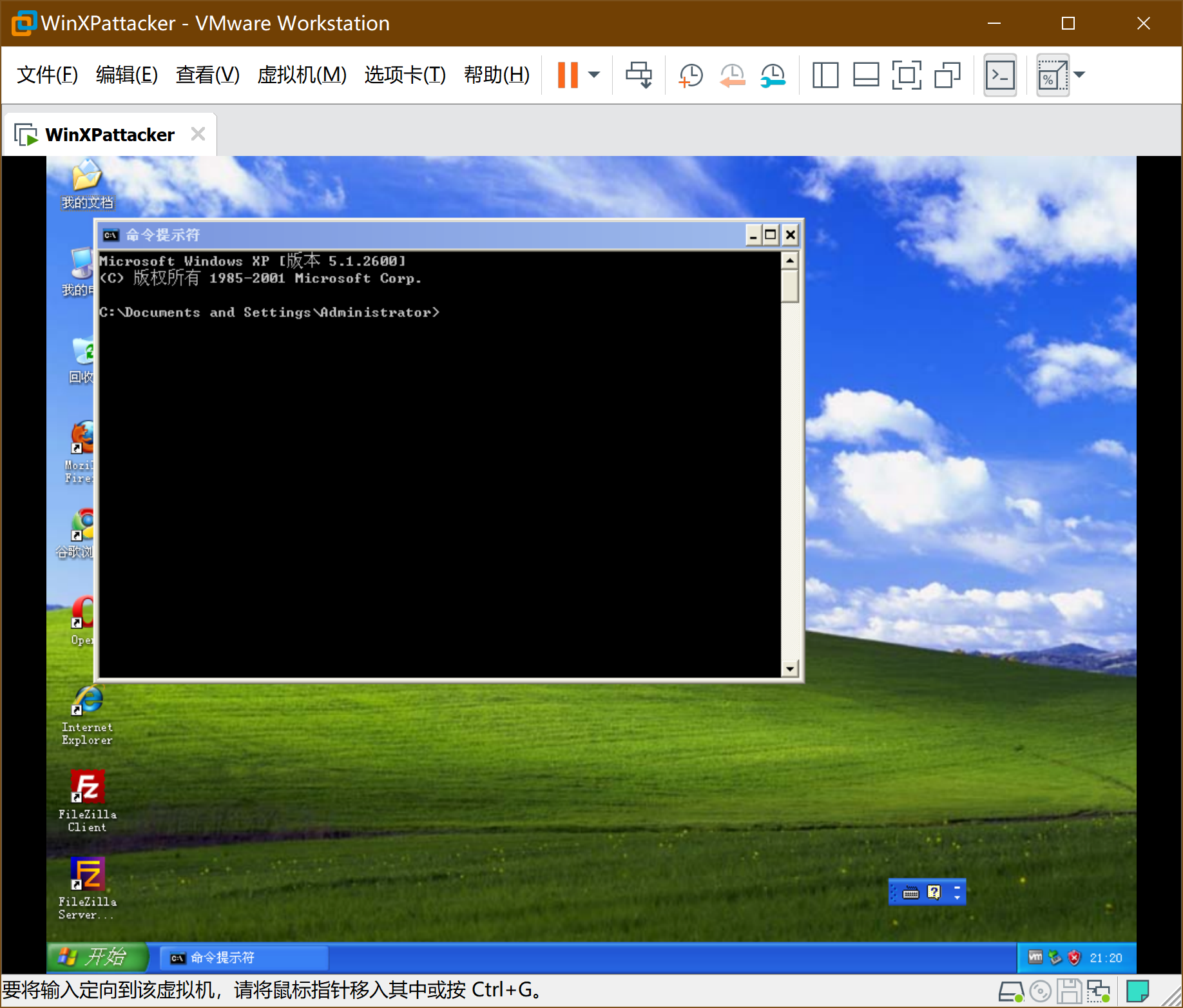
-
此时系统已经通过DHCP获得IP地址,不需要手动配置,但需要找到具体IP。通过ipconfig获得windowsattacker的ip地址:
6、安装windows靶机-win2kServer
-
win2kServer通过虚拟机镜像给予,导入方式和上文的Kali相同。安装之后通过VM的快捷键ALT+CTRL+DEL进入系统(直接发送会被主机拦截),账号administrator,密码mima1234。网卡设置如下:
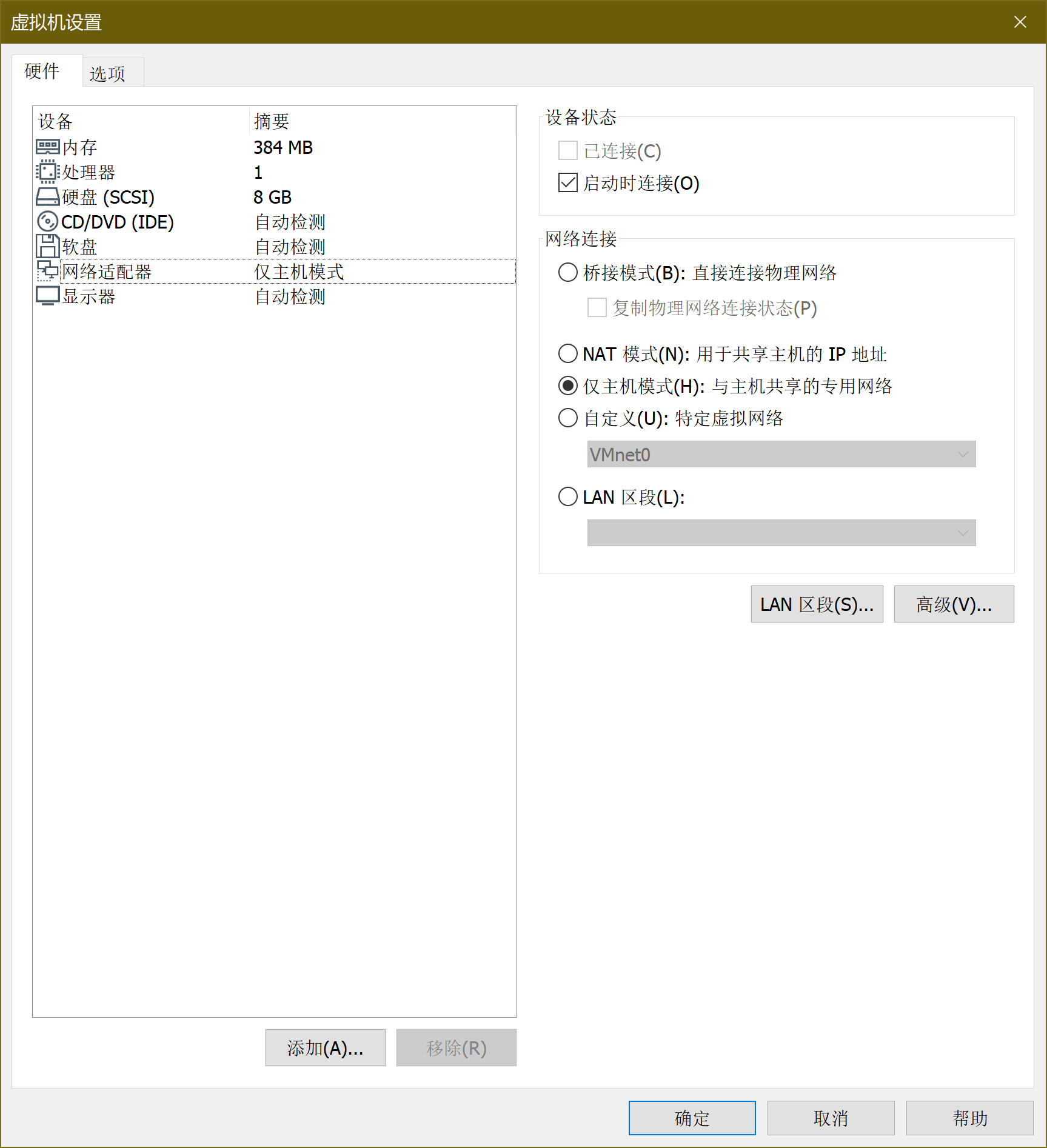
-
打开虚拟机
7、SEEDUbuntu安装配置
-
SEEDUbuntu通过VM虚拟机vmdk磁盘镜像给定,选择新建虚拟机->自定义安装->兼容XX随便选->稍后安装系统->选择linux、版本ubuntu->名称(SEEDUbuntu)位置(D盘)->下一步->使用现有虚拟磁盘!!!选择seedubuntu的vmdk文件(SEEDUbuntu-16.04-32bit.vmdk)->下一步->保持现有格式。
-
SEEDUbuntu的网卡设置如下:
-
启动虚拟机,账户为seed 密码为dees,开机后通过su命令提权,密码为seedubuntu,ifconfig查看相关网络信息。
8、安装蜜罐网关
-
新建虚拟机->自定义->硬件兼容性
-
稍后安装操作系统
-
选择操作系统->编辑名称->下一步
-
硬件设置->添加镜像
-
网络设置->添加两个网卡
-
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
开始设置->初始化选default
-
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
-
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
9、ping检验
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
- WinXPattacker ping Win2kServer
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
Copyright © 2020-2023
润新知
-
win2kServer通过虚拟机镜像给予,导入方式和上文的Kali相同。安装之后通过VM的快捷键ALT+CTRL+DEL进入系统(直接发送会被主机拦截),账号administrator,密码mima1234。网卡设置如下:
-
打开虚拟机
7、SEEDUbuntu安装配置
-
SEEDUbuntu通过VM虚拟机vmdk磁盘镜像给定,选择新建虚拟机->自定义安装->兼容XX随便选->稍后安装系统->选择linux、版本ubuntu->名称(SEEDUbuntu)位置(D盘)->下一步->使用现有虚拟磁盘!!!选择seedubuntu的vmdk文件(SEEDUbuntu-16.04-32bit.vmdk)->下一步->保持现有格式。
-
SEEDUbuntu的网卡设置如下:
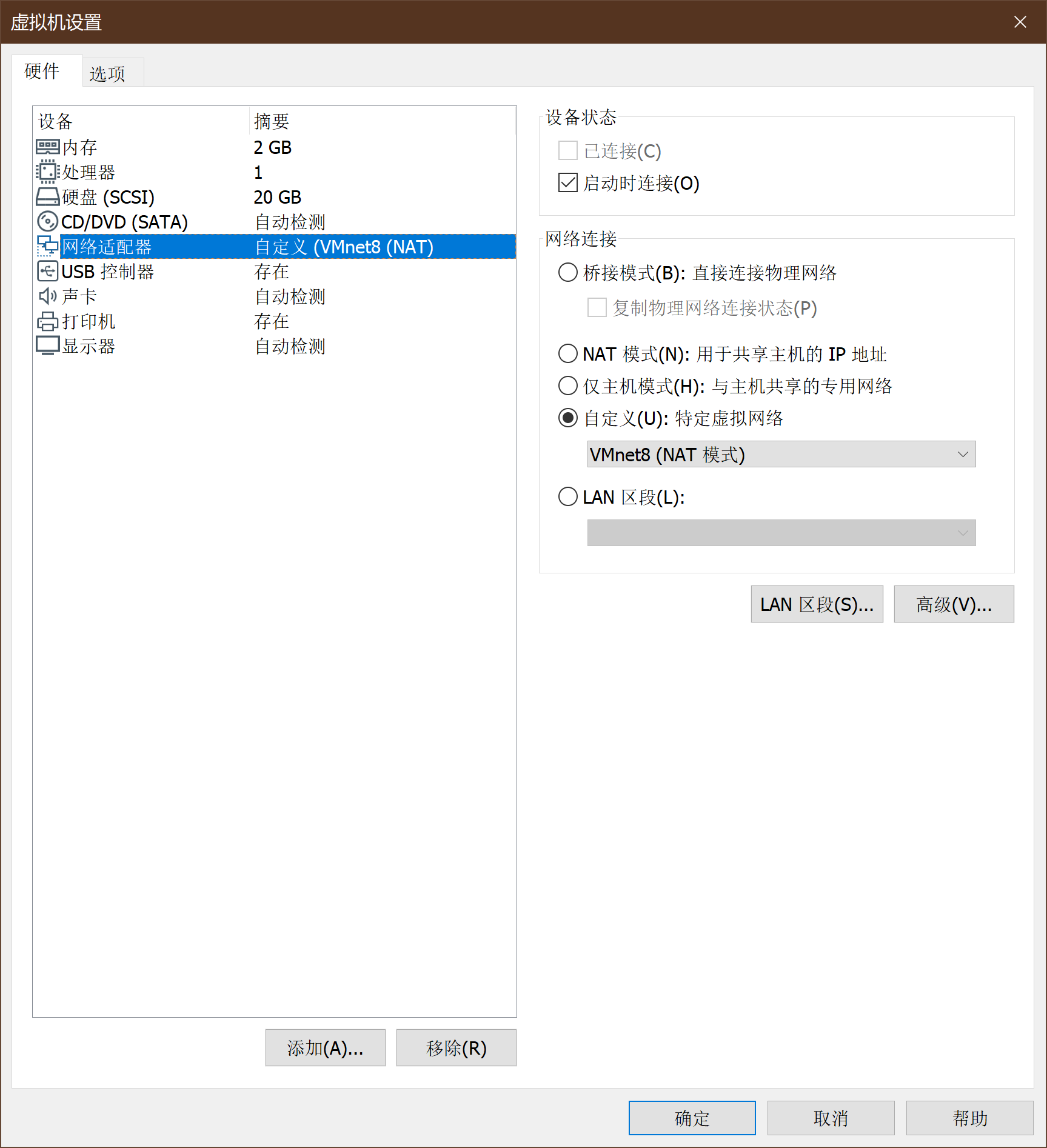
-
启动虚拟机,账户为seed 密码为dees,开机后通过su命令提权,密码为seedubuntu,ifconfig查看相关网络信息。
8、安装蜜罐网关
-
新建虚拟机->自定义->硬件兼容性
-
稍后安装操作系统
-
选择操作系统->编辑名称->下一步
-
硬件设置->添加镜像
-
网络设置->添加两个网卡
-
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
开始设置->初始化选default
-
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
-
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
9、ping检验
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
- WinXPattacker ping Win2kServer
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
Copyright © 2020-2023
润新知
-
SEEDUbuntu通过VM虚拟机vmdk磁盘镜像给定,选择新建虚拟机->自定义安装->兼容XX随便选->稍后安装系统->选择linux、版本ubuntu->名称(SEEDUbuntu)位置(D盘)->下一步->使用现有虚拟磁盘!!!选择seedubuntu的vmdk文件(SEEDUbuntu-16.04-32bit.vmdk)->下一步->保持现有格式。
-
SEEDUbuntu的网卡设置如下:
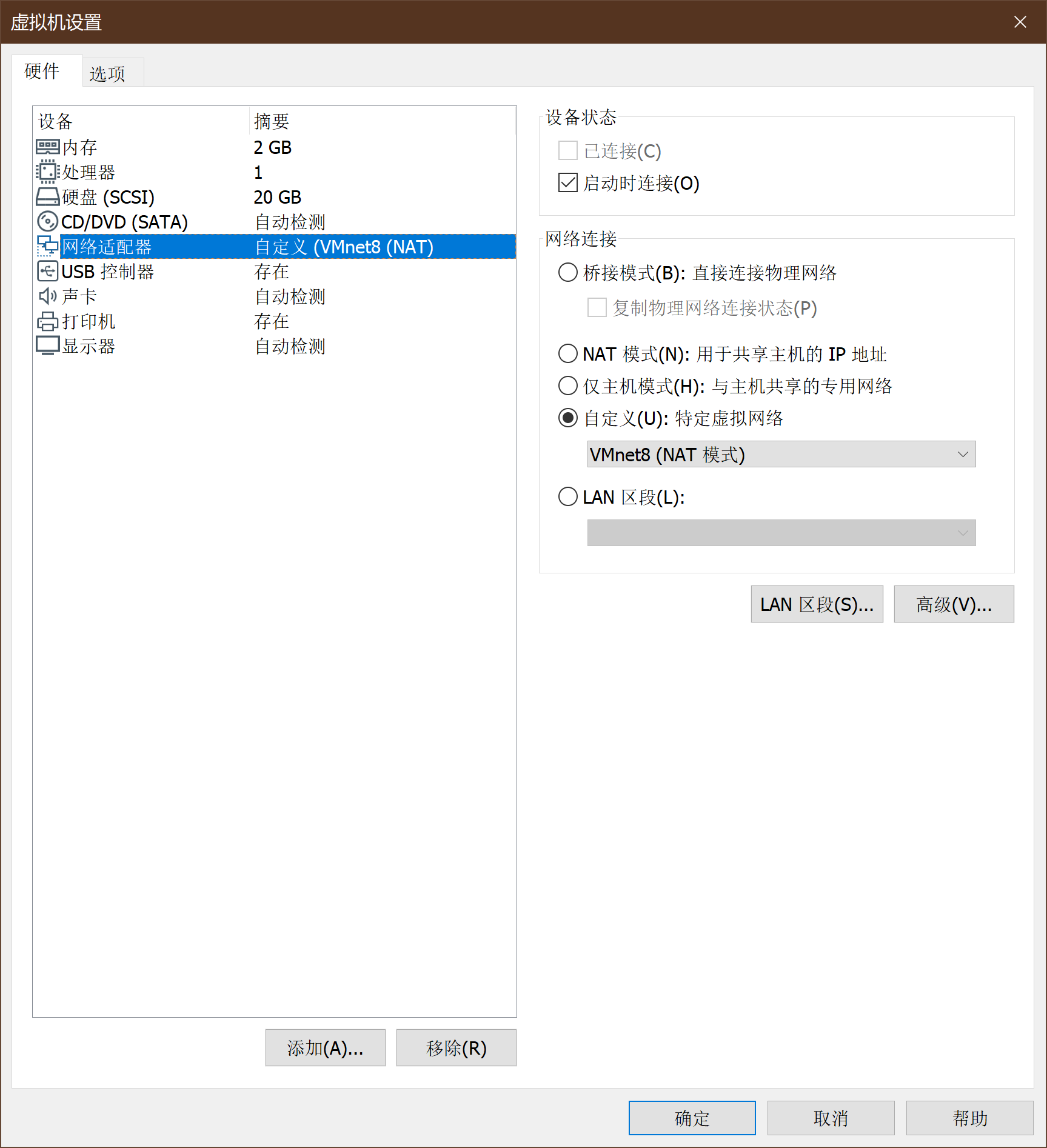
-
启动虚拟机,账户为seed 密码为dees,开机后通过su命令提权,密码为seedubuntu,ifconfig查看相关网络信息。
8、安装蜜罐网关
-
新建虚拟机->自定义->硬件兼容性
-
稍后安装操作系统
-
选择操作系统->编辑名称->下一步
-
硬件设置->添加镜像
-
网络设置->添加两个网卡
-
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
开始设置->初始化选default
-
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
-
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
9、ping检验
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
- WinXPattacker ping Win2kServer
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
-
新建虚拟机->自定义->硬件兼容性
-
稍后安装操作系统
-
选择操作系统->编辑名称->下一步
-
硬件设置->添加镜像
-
网络设置->添加两个网卡
-
开启虚拟机,账号roo,密码honey
-
使用su -提权(注意,有个-)密码honey
-
开始设置->初始化选default
-
现在回到上面提到的windowsAttacker中,浏览器打开https://192.168.200.8(注意这里是https!这里会告诉你证书过期存在风险, 选择打开就行)。
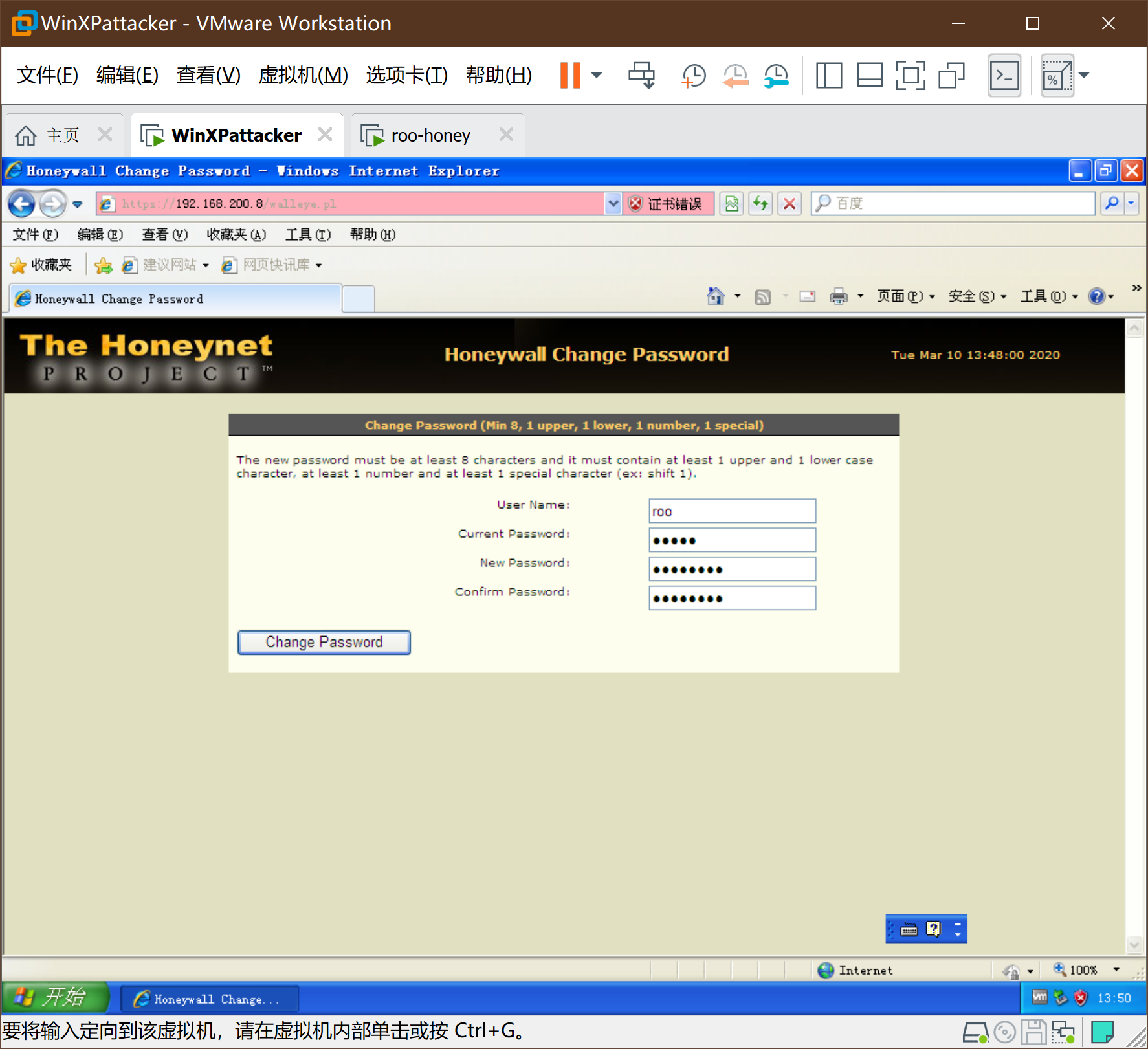
-
重置密码8位,有大小写,有数字,有特殊符号(Honey00@),确认后进入如下界面:
9、ping检验
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
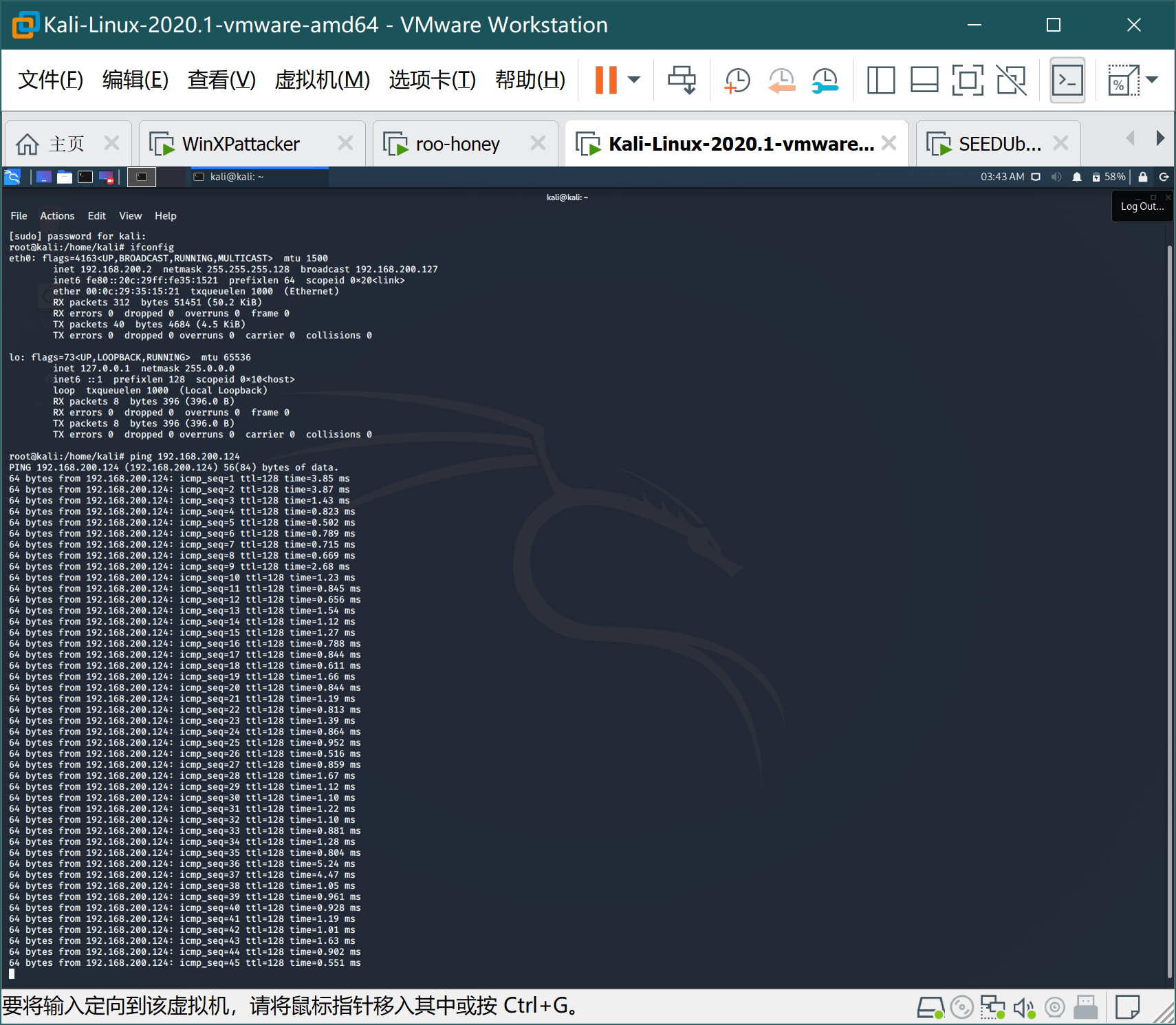
- WinXPattacker ping Win2kServer
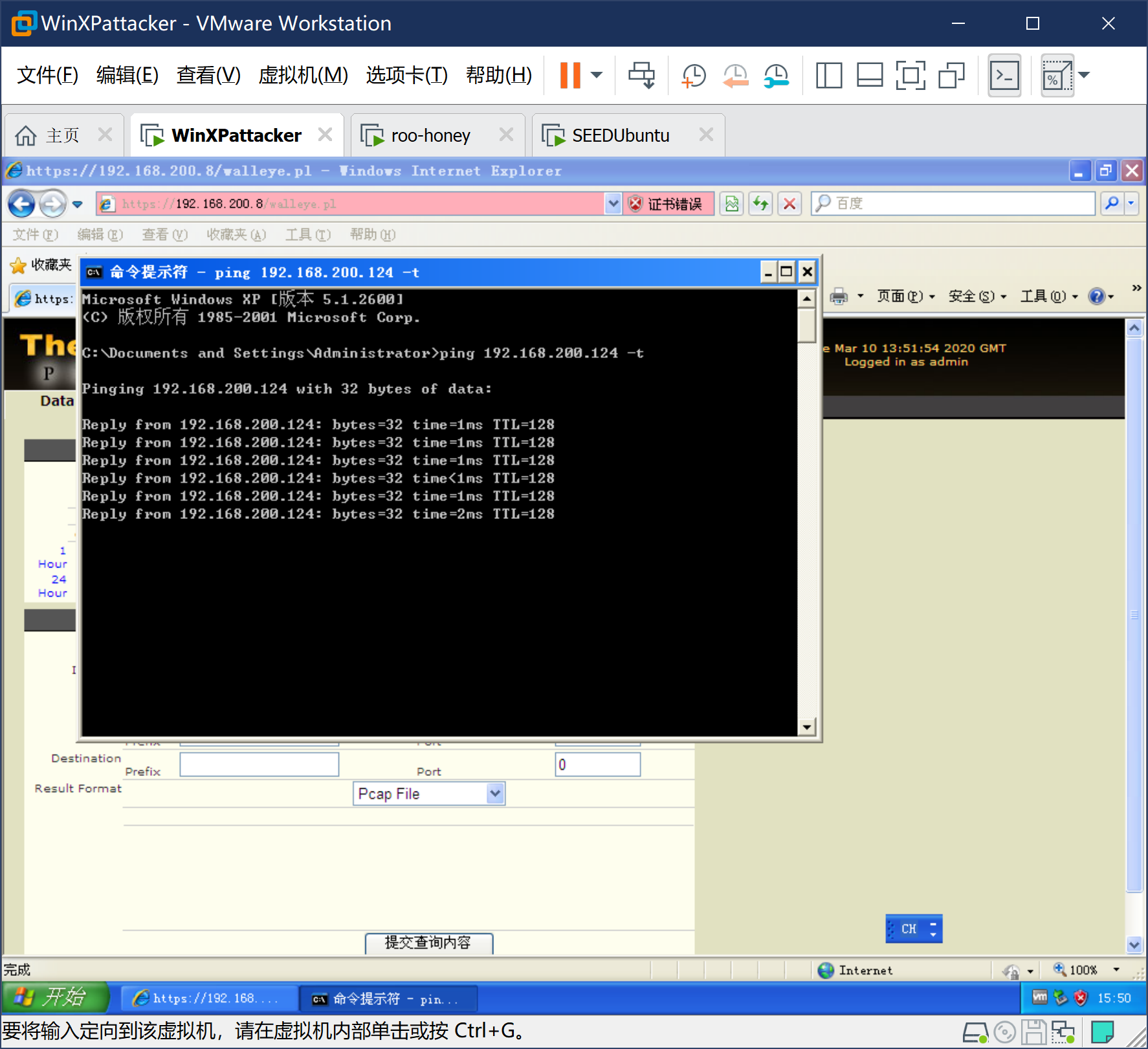
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
-
相关阅读:
为甚么 国企做互联网总做不起来?
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)
-
原文地址:https://www.cnblogs.com/hsj910/p/12448396.html
首先切换到roo中, 通过su -提权(注意有横线),运行命令tcpdump -i eth0 icmp
切换到任何一台攻击机中, ping任何一台靶机。
切换到任何一台靶机中, ping任何一台攻击机。
- Kali ping Win2kAerver
- WinXPattacker ping Win2kServer
- SEEDUbuntu ping Metasploitable2-Linux
- roo中tcpdump的信息,可以看到网桥的功能正常。
总结
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
本次作业提高了动手实践能力,还不得不买了百度网盘的会员,才得以把所有镜像文件下好,又怕出现自己解决不了的问题,所以基本按照孙启龙同学的作业步骤完成,特此感谢。
WEB开发:Java与Php对比
String中的CompareTo
String API
死锁(Deadlock)
100人100盏灯(详解)
debian、ubuntu安装metasploit通用方法
xman随机数相关题目
CTF辅助脚本
2019全国大学生信息安全竞赛ciscn-writeup(4web)