基于令牌的认证
我们知道WEB网站的身份验证一般通过session或者cookie完成的,登录成功后客户端发送的任何请求都带上cookie,服务端根据客户端发送来的cookie来识别用户。
WEB API使用这样的方法不是很适合,于是就有了基于令牌的认证,使用令牌认证有几个好处:可扩展性、松散耦合、移动终端调用比较简单等等,别人都用上了,你还有理由不用吗?
下面我们花个20分钟的时间来实现一个简单的WEB API token认证:
Step 1:安装所需的NuGet包:
打开NuGet包管理器控制台,然后输入如下指令:
Install-Package Microsoft.AspNet.WebApi.Owin -Version 5.1.2 Install-Package Microsoft.Owin.Host.SystemWeb -Version 2.1.0 Install-Package Microsoft.AspNet.Identity.Owin -Version 2.0.1
Install-Package Microsoft.Owin.Cors -Version 2.1.0
Install-Package EntityFramework -Version 6.0.0
Step 2 在项目根目录下添加Owin“Startup”类

1 using System; 2 using System.Web.Http; 3 4 using Owin; 5 using Microsoft.Owin; 6 using Microsoft.Owin.Security.OAuth; 7 using SqlSugar.WebApi; 8 9 [assembly: OwinStartup(typeof(WebApi.Startup))] 10 namespace WebApi 11 { 12 public class Startup 13 { 14 public void Configuration(IAppBuilder app) 15 { 16 HttpConfiguration config = new HttpConfiguration(); 17 ConfigureOAuth(app); 18 19 WebApiConfig.Register(config); 20 app.UseCors(Microsoft.Owin.Cors.CorsOptions.AllowAll); 21 app.UseWebApi(config); 22 } 23 24 public void ConfigureOAuth(IAppBuilder app) 25 { 26 OAuthAuthorizationServerOptions OAuthServerOptions = new OAuthAuthorizationServerOptions() 27 { 28 AllowInsecureHttp = true, 29 TokenEndpointPath = new PathString("/token"), 30 AccessTokenExpireTimeSpan = TimeSpan.FromDays(1), 31 Provider = new SimpleAuthorizationServerProvider() 32 }; 33 app.UseOAuthAuthorizationServer(OAuthServerOptions); 34 app.UseOAuthBearerAuthentication(new OAuthBearerAuthenticationOptions()); 35 } 36 } 37 }
Step 3:在项目根目录下添加验证类 SimpleAuthorizationServerProvider,为了简单用户的验证部分我们省略掉;

1 using System.Threading.Tasks; 2 using System.Security.Claims; 3 using Microsoft.Owin.Security.OAuth; 4 5 namespace WebApi 6 { 7 /// <summary> 8 /// Token验证 9 /// </summary> 10 public class SimpleAuthorizationServerProvider : OAuthAuthorizationServerProvider 11 { 12 public override async Task ValidateClientAuthentication(OAuthValidateClientAuthenticationContext context) 13 { 14 await Task.Factory.StartNew(() => context.Validated()); 15 } 16 17 public override async Task GrantResourceOwnerCredentials(OAuthGrantResourceOwnerCredentialsContext context) 18 { 19 await Task.Factory.StartNew(() => context.OwinContext.Response.Headers.Add("Access-Control-Allow-Origin", new[] { "*" })); 20 /* 21 * 对用户名、密码进行数据校验 22 using (AuthRepository _repo = new AuthRepository()) 23 { 24 IdentityUser user = await _repo.FindUser(context.UserName, context.Password); 25 26 if (user == null) 27 { 28 context.SetError("invalid_grant", "The user name or password is incorrect."); 29 return; 30 } 31 }*/ 32 33 var identity = new ClaimsIdentity(context.Options.AuthenticationType); 34 identity.AddClaim(new Claim("sub", context.UserName)); 35 identity.AddClaim(new Claim("role", "user")); 36 37 context.Validated(identity); 38 39 } 40 } 41 }
Step 4:让CORS起作用
在ASP.NET Web API中启用OAuth的Access Token验证非常简单,只需在相应的Controller或Action加上[Authorize]标记

1 [Authorize] 2 [HttpGet, Route("product/getList")] 3 public List<Entity.Sys_User> GetProductList() 4 { 5 throw new NotImplementedException(); 6 }
Step 5 : 请求 Token
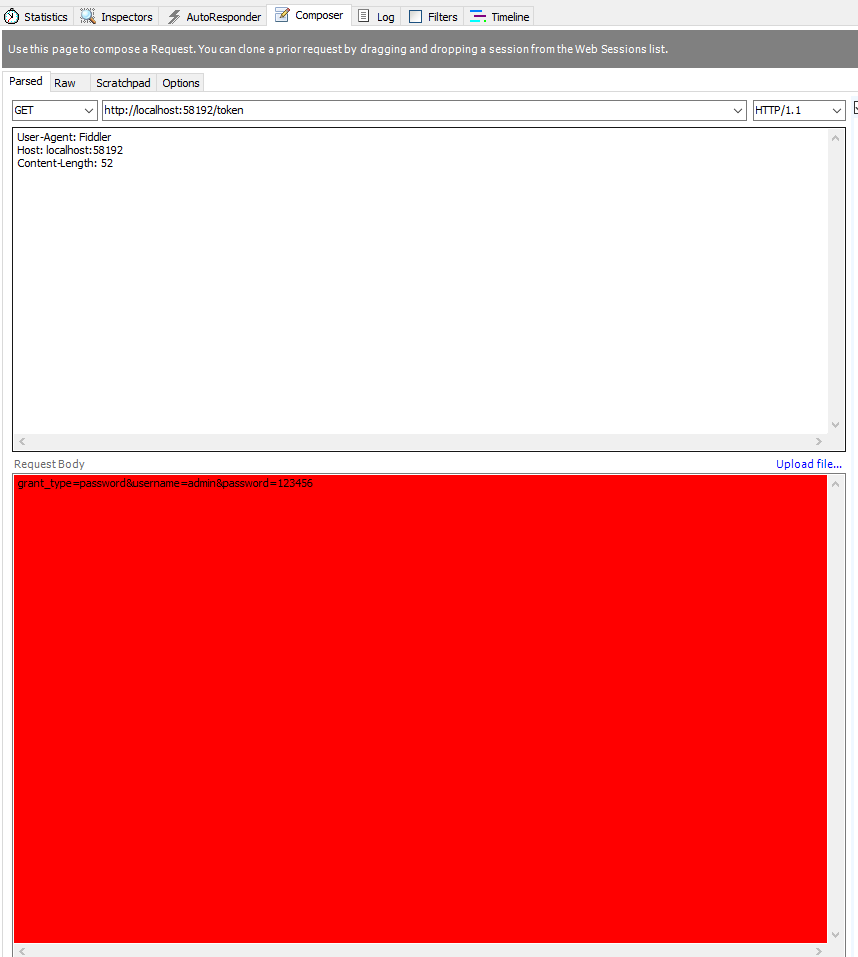
获取token, POST http://localhost:23477/token
参数BODY x-www-form-urlencoded 格式:
grant_type=password
username=admin
password=123456
返回状态200 结果为

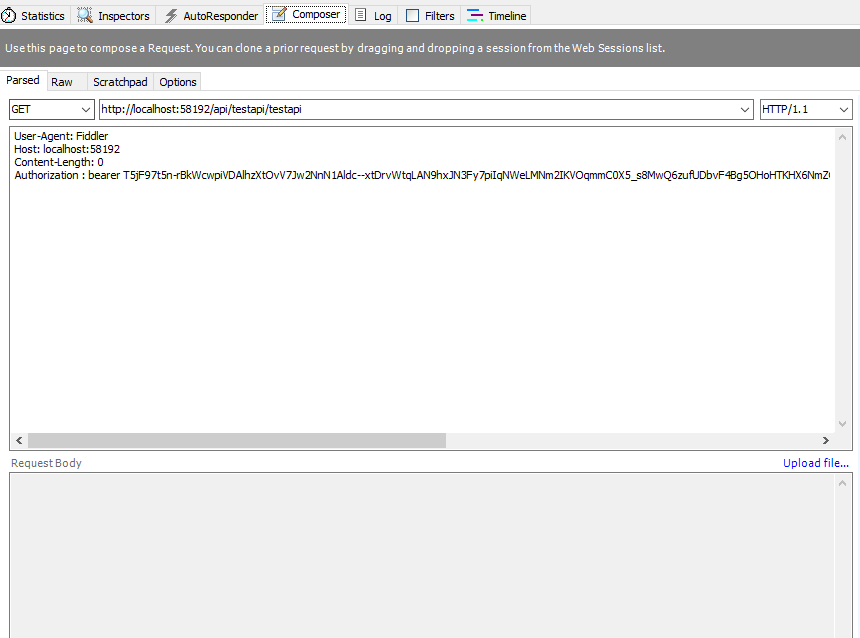
Step 5 调用api
只要在http请求头中加上Authorization:bearer Token就可以成功访问API就成功了:
GET http://localhost:58192/api/testapi/testapi
Authorization : bearer T5jF97t5n-rBkWcwpiVDAlhzXtOvV7Jw2NnN1Aldc--xtDrvWtqLAN9hxJN3Fy7piIqNWeLMNm2IKVOqmmC0X5_s8MwQ6zufUDbvF4Bg5OHoHTKHX6NmZGNrU4mjpCuPLtSbT5bh_gFOZHoIXXIKmqD3Wu1MyyKKNhj9XPEIkd9bl4E9AZ1wAt4dyUxmPVA_VKuN7UvYJ97TkO04XyGqmXGtfVWKfM75mNVYNhySWTg
结果为:

