(1).CA认证
CA全称Certificate Authority,通常翻译成认证权威或者认证中心,主要用途是为用户发放数字证书。认证中心(CA)的功能:证书发放、证书更新、证书撤销和证书验证。CA证书的作用:身份认证,实现数据的不可否认性。
CSR全称Cerificate Signing Request,中文名证书请求文件,是证书申请者在申请数字证书时由CSP(加密服务提供者)在生成私钥的同时也生成证书请求文件,证书申请者只要把CSR文件提交给证书颁发机构后,证书颁发机构使用其根证书的私钥签名就生成了证书文件,也就是颁发给用户的证书。
证书签名过程:1、服务器生成证书请求文件;2、认证中心确认申请者的身份真实性;3、认证中学使用根证书的私钥加密证书请求文件,生成证书;4、把证书传给申请者。
申请免费的CA认证可以选择:阿里云https://www.aliyun.com/product/cas?spm=5176.10695662.1171680.1.58564c0dMNos55,或FreeSSLhttps://freessl.cn/
1)实验环境
youxi1 192.168.5.101 CA认证中心
youxi2 192.168.5.102 服务器
2)由于没有真实域名,所以自己搭建一个CA认证中心,实际只要去申请一个就好了。
[root@youxi1 ~]# rpm -qf `which openssl`
openssl-1.0.2k-12.el7.x86_64 //openssl一般默认安装的
[root@youxi1 ~]# vim /etc/pki/tls/openssl.cnf
basicConstraints=CA:TRUE //第172行,让当前服务器成为CA认证中心
[root@youxi1 ~]# /etc/pki/tls/misc/CA -newca //新的CAche证书
CA certificate filename (or enter to create) //证书文件名,可以直接回车
Making CA certificate ...
Generating a 2048 bit RSA private key
................................+++
...................................................................+++
writing new private key to '/etc/pki/CA/private/./cakey.pem'
Enter PEM pass phrase: //保护私钥的密码,123456
Verifying - Enter PEM pass phrase: //重复密码,123456
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN //国家,只能2个字符
State or Province Name (full name) []:beijing //地区
Locality Name (eg, city) [Default City]:haidian //城市
Organization Name (eg, company) [Default Company Ltd]:test //组织名称,公司
Organizational Unit Name (eg, section) []:IT //部门
Common Name (eg, your name or your server's hostname) []:test.cn //通用名,名字或服务器主机名等
Email Address []:test@qq.com //邮箱
Please enter the following 'extra' attributes
to be sent with your certificate request //添加一个额外属性,让客户端发送CA证书请求文件时,要输入的密码
A challenge password []: //直接回车
An optional company name []: //回车
Using configuration from /etc/pki/tls/openssl.cnf //CA服务器的配置文件,上面修改的内容会添加到该配置文件中
Enter pass phrase for /etc/pki/CA/private/./cakey.pem: //输入私钥密码,123456
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number:
af:e0:dd:ca:39:32:8e:56
Validity
Not Before: Aug 15 07:30:27 2019 GMT
Not After : Aug 14 07:30:27 2022 GMT
Subject:
countryName = CN
stateOrProvinceName = beijing
organizationName = test
organizationalUnitName = IT
commonName = test.cn
emailAddress = test@qq.com
X509v3 extensions:
X509v3 Subject Key Identifier:
08:F1:6F:02:F1:A0:BD:71:1E:DF:F5:D1:F3:7B:40:05:3A:02:B5:7C
X509v3 Authority Key Identifier:
keyid:08:F1:6F:02:F1:A0:BD:71:1E:DF:F5:D1:F3:7B:40:05:3A:02:B5:7C
X509v3 Basic Constraints:
CA:TRUE
Certificate is to be certified until Aug 14 07:30:27 2022 GMT (1095 days)
Write out database with 1 new entries
Data Base Updated //搭建完成
[root@youxi1 ~]# cat /etc/pki/CA/cacert.pem
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
af:e0:dd:ca:39:32:8e:56
Signature Algorithm: sha256WithRSAEncryption
Issuer: C=CN, ST=beijing, O=test, OU=IT, CN=test.cn/emailAddress=test@qq.com //CA机构信息
Validity
Not Before: Aug 15 07:30:27 2019 GMT
Not After : Aug 14 07:30:27 2022 GMT
Subject: C=CN, ST=beijing, O=test, OU=IT, CN=test.cn/emailAddress=test@qq.com
Subject Public Key Info: //CA认证中心公钥信息
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:f5:b0:8d:1f:fd:12:2b:7c:d4:6d:75:c1:da:3e:
2c:92:87:22:1e:41:c9:21:bc:c7:bb:65:1f:1a:a4:
46:7f:d0:0d:22:11:fc:bf:49:9a:2a:b9:56:9a:14:
18:b9:6e:55:3b:06:25:49:80:38:58:1d:f8:89:62:
e6:e5:09:6a:61:7c:e8:c7:bc:be:f1:7c:86:e3:de:
1e:49:cf:6e:09:ac:cb:5a:58:f3:62:71:c7:05:4e:
5a:d7:ab:bb:03:35:49:f1:81:07:7b:82:99:75:a6:
28:c7:6d:aa:88:7b:82:d8:ac:ee:e7:e4:28:aa:8d:
e6:62:45:b9:6a:5a:49:49:40:65:e7:2f:69:d8:48:
2f:cb:a3:c3:01:af:b5:8e:0f:b5:68:0a:7b:64:4b:
6a:46:58:d6:f2:4d:02:51:ea:5c:4c:38:70:38:b6:
5d:fd:d7:da:af:3c:99:46:cb:40:02:7f:4d:a8:30:
98:4c:72:fd:80:7d:13:f5:42:6b:dd:3d:52:02:4b:
c2:6f:eb:5c:ca:63:76:1f:b4:5a:6c:e5:0c:fb:bc:
b6:32:44:d7:c4:7d:8a:6b:3f:58:56:9b:72:fd:74:
66:d9:a2:43:36:5c:a5:ea:91:49:07:14:a4:51:a8:
bb:94:9b:5d:72:1d:01:7e:89:eb:f5:ec:2b:3e:f5:
73:21
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Subject Key Identifier:
08:F1:6F:02:F1:A0:BD:71:1E:DF:F5:D1:F3:7B:40:05:3A:02:B5:7C
X509v3 Authority Key Identifier:
keyid:08:F1:6F:02:F1:A0:BD:71:1E:DF:F5:D1:F3:7B:40:05:3A:02:B5:7C
X509v3 Basic Constraints:
CA:TRUE
Signature Algorithm: sha256WithRSAEncryption
3d:c4:ae:3d:ee:22:c7:ff:e7:c2:54:9d:b1:f5:4b:a4:c9:46:
58:ec:e7:50:d8:48:66:39:8e:99:12:1b:f0:0a:37:86:03:61:
8d:21:dc:26:ca:48:9b:43:82:4a:fa:4f:ff:fb:04:66:ee:b2:
0f:44:63:e8:fc:d2:49:26:2a:4c:8a:3b:98:56:e5:86:70:3e:
b8:5b:be:91:e5:b5:8a:6b:1f:00:bc:15:b8:91:b4:66:ad:bf:
fe:1b:2e:83:3a:5e:6f:df:c5:96:38:8a:ba:b8:be:37:e7:2b:
77:e7:af:a8:c7:84:a8:09:0b:1a:b0:43:2d:c2:ae:56:8c:81:
09:d3:c0:52:63:e9:ec:04:f1:4e:23:c9:eb:16:36:7c:56:4f:
d3:11:06:a9:1c:27:b8:ed:84:04:7a:77:56:ca:8b:f2:1a:42:
c1:2f:8c:8d:06:ea:15:e5:08:d9:35:cb:c4:f1:c9:6a:f5:8b:
7e:be:46:71:2e:56:00:e7:c4:fe:18:98:cf:72:16:bd:da:fb:
b3:9b:03:fc:3c:e4:43:74:04:20:cf:7d:9f:6c:dd:76:bf:8c:
b7:e0:44:8a:2a:d7:c5:60:82:c9:cb:1d:80:5b:d1:de:04:d6:
dc:19:5a:aa:a9:1b:9d:d6:ed:d1:81:6d:68:10:90:e0:b5:7b:
e7:b6:64:42
-----BEGIN CERTIFICATE----- //私钥
MIIDpTCCAo2gAwIBAgIJAK/g3co5Mo5WMA0GCSqGSIb3DQEBCwUAMGkxCzAJBgNV
BAYTAkNOMRAwDgYDVQQIDAdiZWlqaW5nMQ0wCwYDVQQKDAR0ZXN0MQswCQYDVQQL
DAJJVDEQMA4GA1UEAwwHdGVzdC5jbjEaMBgGCSqGSIb3DQEJARYLdGVzdEBxcS5j
b20wHhcNMTkwODE1MDczMDI3WhcNMjIwODE0MDczMDI3WjBpMQswCQYDVQQGEwJD
TjEQMA4GA1UECAwHYmVpamluZzENMAsGA1UECgwEdGVzdDELMAkGA1UECwwCSVQx
EDAOBgNVBAMMB3Rlc3QuY24xGjAYBgkqhkiG9w0BCQEWC3Rlc3RAcXEuY29tMIIB
IjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA9bCNH/0SK3zUbXXB2j4skoci
HkHJIbzHu2UfGqRGf9ANIhH8v0maKrlWmhQYuW5VOwYlSYA4WB34iWLm5QlqYXzo
x7y+8XyG494eSc9uCazLWljzYnHHBU5a16u7AzVJ8YEHe4KZdaYox22qiHuC2Kzu
5+Qoqo3mYkW5alpJSUBl5y9p2Egvy6PDAa+1jg+1aAp7ZEtqRljW8k0CUepcTDhw
OLZd/dfarzyZRstAAn9NqDCYTHL9gH0T9UJr3T1SAkvCb+tcymN2H7RabOUM+7y2
MkTXxH2Kaz9YVpty/XRm2aJDNlyl6pFJBxSkUai7lJtdch0Bfonr9ewrPvVzIQID
AQABo1AwTjAdBgNVHQ4EFgQUCPFvAvGgvXEe3/XR83tABToCtXwwHwYDVR0jBBgw
FoAUCPFvAvGgvXEe3/XR83tABToCtXwwDAYDVR0TBAUwAwEB/zANBgkqhkiG9w0B
AQsFAAOCAQEAPcSuPe4ix//nwlSdsfVLpMlGWOznUNhIZjmOmRIb8Ao3hgNhjSHc
JspIm0OCSvpP//sEZu6yD0Rj6PzSSSYqTIo7mFblhnA+uFu+keW1imsfALwVuJG0
Zq2//hsugzpeb9/FljiKuri+N+crd+evqMeEqAkLGrBDLcKuVoyBCdPAUmPp7ATx
TiPJ6xY2fFZP0xEGqRwnuO2EBHp3VsqL8hpCwS+MjQbqFeUI2TXLxPHJavWLfr5G
cS5WAOfE/hiYz3IWvdr7s5sD/DzkQ3QEIM99n2zddr+Mt+BEiirXxWCCycsdgFvR
3gTW3Blaqqkbndbt0YFtaBCQ4LV757ZkQg==
-----END CERTIFICATE-----
说明:/etc/pki/tls/misc/CA -newcert|-newreq|-newreq-nodes|-newca|-sign|-verify
-newcert 新证书
-newreq 新请求
-newreq-nodes 新请求节点
-newca 新的CA证书
-sign 签证
-verify 验证
(2).Apache实现https
准备一个httpd,需要包含ssl模块
[root@youxi2 ~]# yum -y install httpd mod_ssl [root@youxi2 ~]# vim /etc/httpd/conf/httpd.conf ServerName 192.168.5.102:80 //第95行 [root@youxi2 ~]# systemctl start httpd.service [root@youxi2 ~]# firewall-cmd --permanent --zone=public --add-port=80/tcp success [root@youxi2 ~]# firewall-cmd --reload success
生成证书请求文件,并发给CA认证中心youxi1
//-des3使用des3加密算法;-out输出到指定地址 [root@youxi2 ~]# openssl genrsa -des3 -out /etc/httpd/conf.d/server.key Generating RSA private key, 2048 bit long modulus ................................................................................................+++ ....................+++ e is 65537 (0x10001) Enter pass phrase for /etc/httpd/conf.d/server.key: //输入保护私钥的密码,123456 Verifying - Enter pass phrase for /etc/httpd/conf.d/server.key: //重复密码 //-key指定私钥 [root@youxi2 ~]# openssl req -new -key /etc/httpd/conf.d/server.key -out /server.csr Enter pass phrase for /etc/httpd/conf.d/server.key: //输入保护私钥的密码(/etc/httpd/conf.d/server.key的),123456 You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- //通用名不能和CA一样,一般写域名 Country Name (2 letter code) [XX]:CN State or Province Name (full name) []:beijing Locality Name (eg, city) [Default City]:haidian Organization Name (eg, company) [Default Company Ltd]:test Organizational Unit Name (eg, section) []:IT Common Name (eg, your name or your server's hostname) []:test.com Email Address []:test@qq.com Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: //回车 An optional company name []: //回车 [root@youxi2 ~]# scp /server.csr 192.168.5.101:/ //发给CA认证中心 root@192.168.5.101's password: server.csr 100% 1029 127.4KB/s 00:00
CAche认证中心进行签名,再回传
[root@youxi1 ~]# openssl ca -keyfile /etc/pki/CA/private/cakey.pem -cert /etc/pki/CA/cacert.pem -in /server.csr -out /server.crt
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/cakey.pem: //cakey.pem的保护私钥的密码,123456
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number:
af:e0:dd:ca:39:32:8e:57
Validity
Not Before: Aug 15 08:45:17 2019 GMT
Not After : Aug 14 08:45:17 2020 GMT
Subject:
countryName = CN
stateOrProvinceName = beijing
organizationName = test
organizationalUnitName = IT
commonName = test.com
emailAddress = test@qq.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:TRUE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
B3:F5:B0:FE:43:AC:44:C9:7F:C6:B5:6F:5C:EA:B8:D1:04:36:1E:40
X509v3 Authority Key Identifier:
keyid:08:F1:6F:02:F1:A0:BD:71:1E:DF:F5:D1:F3:7B:40:05:3A:02:B5:7C
Certificate is to be certified until Aug 14 08:45:17 2020 GMT (365 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
[root@youxi1 ~]# scp /server.crt 192.168.5.102:/ //回传给服务器
root@192.168.5.102's password:
server.crt 100% 4547 1.8MB/s 00:00
配置Apache加载证书文件
[root@youxi2 ~]# cp /server.crt /etc/httpd/conf.d/ [root@youxi2 ~]# vim /etc/httpd/conf.d/ssl.conf SSLCertificateFile /etc/httpd/conf.d/server.crt //第100行,签名证书 SSLCertificateKeyFile /etc/httpd/conf.d/server.key/ /第107行,私钥 [root@youxi2 ~]# systemctl restart httpd Enter SSL pass phrase for 192.168.5.102:443 (RSA) : ****** [root@youxi2 ~]# yum -y install net-tools.x86_64 [root@youxi2 ~]# netstat -antup | grep 443 //查看443端口 tcp6 0 0 :::443 :::* LISTEN 2126/httpd [root@youxi2 ~]# firewall-cmd --permanent --zone=public --add-port=443/tcp success [root@youxi2 ~]# firewall-cmd --reload success
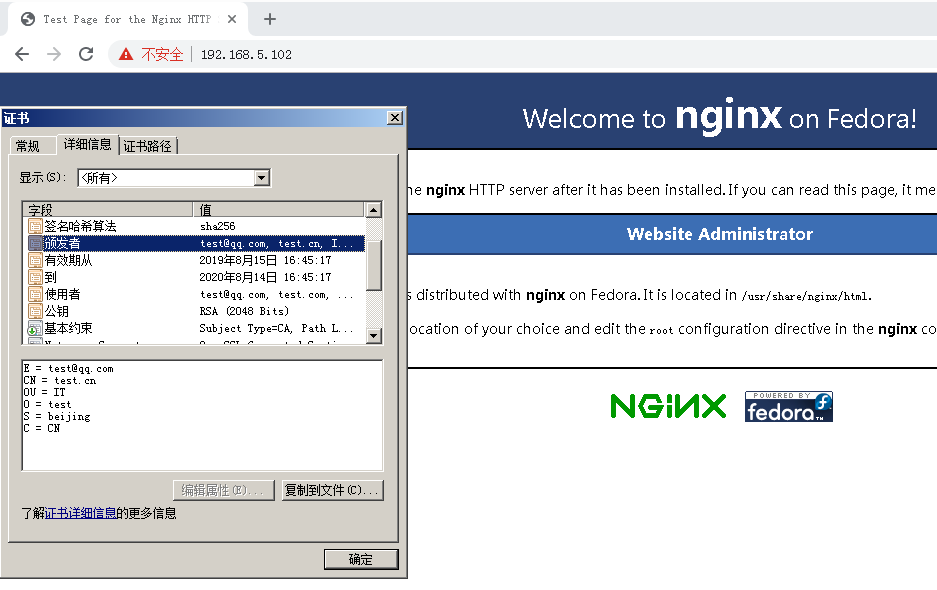
最后使用Windows查看

(3).nginx实现https
停掉Apache,安装nginx
[root@youxi2 ~]# systemctl stop httpd [root@youxi2 ~]# netstat -antup | grep 443 [root@youxi2 ~]# yum -y install nginx
配置nginx加载证书文件
[root@youxi2 ~]# vim /etc/nginx/conf.d/default.conf
server {
listen 443 ssl;
keepalive_timeout 70;
location / {
root /usr/share/nginx/html;
index index.html index.htm;
}
ssl_protocols TLSv1 TLSv1.1 TLSv1.2; #SSL支持的版本
ssl_ciphers AES128-SHA:AES256-SHA:RC4-SHA:DES-CBC3-SHA:RC4-MD5;
ssl_certificate /etc/httpd/conf.d/server.crt;
ssl_certificate_key /etc/httpd/conf.d/server.key;
ssl_session_cache shared:SSL:10m;
ssl_session_timeout 10m;
}
[root@youxi2 ~]# nginx -t
Enter PEM pass phrase:
nginx: the configuration file /etc/nginx/nginx.conf syntax is ok
nginx: configuration file /etc/nginx/nginx.conf test is successful
[root@youxi2 ~]# nginx
Enter PEM pass phrase:
[root@youxi2 ~]# netstat -antup | grep 443
tcp 0 0 0.0.0.0:443 0.0.0.0:* LISTEN 2436/nginx: master
最后在Windows上查看
(4).SSL四次握手
SSL全称Secure Socket Layer,中文名安全套接字层,通过一种机制在互联网上提供密钥传输。其主要目标是保证两个应用间通信数据的保密性和可靠性,可在服务器端和用户端同时支持的一种加密算法。目前主流版本SSLV2、SSLV3(常用)。
四次握手安全传输流程:
client---1.客户端请求一个安全的会话,协商加密算法--->server
<----------2.服务端将自己的证书传给客户端----------
3.客户端用浏览中存放CA的根证书检测server证书,确认server是我要访问的网站。客户端使用CA根证书中的公钥解密server的证书,从而得到server的公钥;然后客户端生成一把对称的加密密钥,用server的公钥加密这个对称的加密密钥发给server。 后期使用对称密钥加密数据。
------------------------------------------------->
4.server使用私钥解密,得到对称的加密密钥。从而,使用对称的加密密钥来进行安全快速传输数据。这里使用对称加密数据,是因为对称加密和解密速度快。
<------------------------------------------------>
总结:SSL四次握手流程整体分两个过程。过程1, 确认身份;过程2,生成一把对称加密密钥,传输数据。