推荐两篇都可以编译完成:
openssl-1.0.2m.tar.gz
http://blog.csdn.net/liang19890820/article/details/51658574
openssl-1.0.2n.tar.gz
http://blog.csdn.net/haolovekun/article/details/78781557
备份一下:
系统:windows 7 x64
openssl版本:openssl-1.0.2n.tar.gz
编译器:vs2015
1、下载安装perl
1)下载路径:
http://www.activestate.com/activeperl/downloads/
2)测试:
进入perl安装目录的eg文件夹,执行“perl example.pl”若显示“Hello from ActivePerl!”,则说明Perl安装成功。如下图所示:

2、下载openssl源码
1)下载路径:
http://www.openssl.org/source/
下载好文件,压缩包解压到c盘openssl文件夹
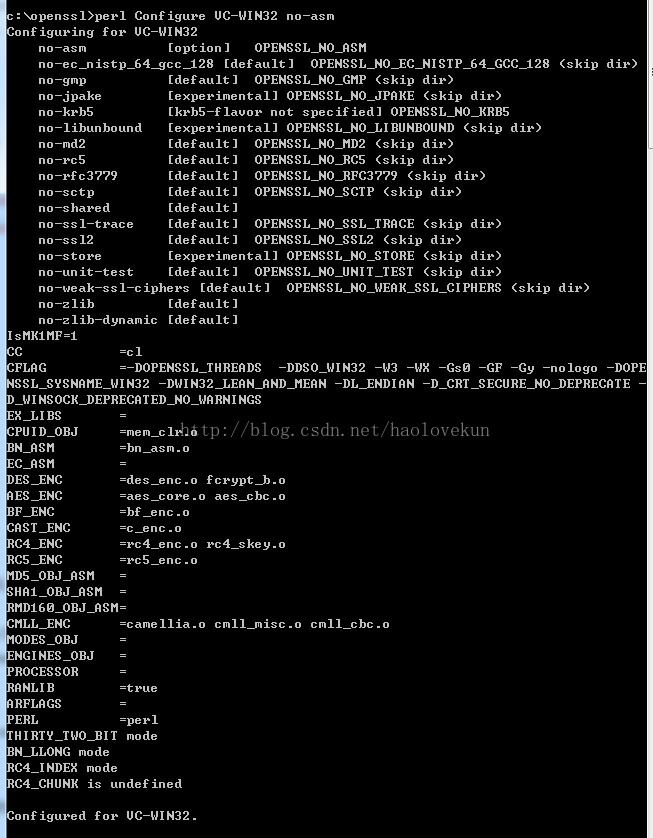
2)运行“VS2015 开发人员命令提示“进入C盘下openssl目录运行perl Configure VC-WIN32 no-asm
3)运行命令 msdo_ms.bat

4)运行命令 nmake -f ms tdll.mak
编译时报错:
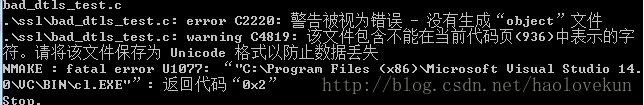
解决方法:
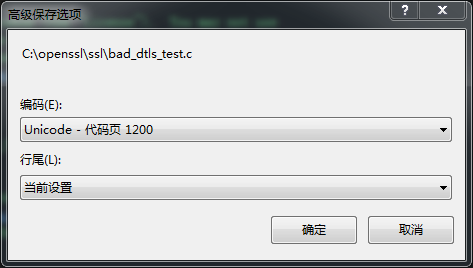
用VS2015打开C:opensslssl目录下的bad_dtls_test.c文件
然后选择文件->高级保存选项 把编码改成 Unicode -代码页 1200
点击确定,然后保存文件,在重新输入 nmake -f ms tdll.mak 编译成功
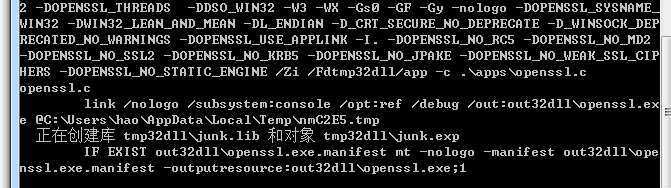
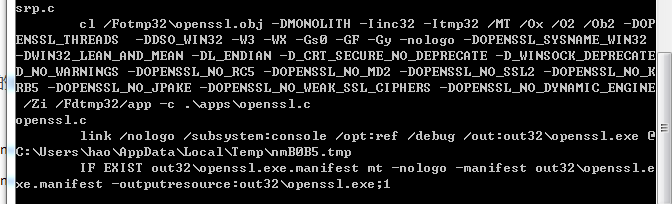
5)在运行命令 nmake -f ms t.mak
编译成功:
以上openssl已经编译成功了,可以用一下命令进行测试以及清除:
测试动态库:
nmake -f ms
tdll.mak test
测试静态库:
nmake -f ms
t.mak test
安装动态库:
nmake -f ms
tdll.mak install
安装静态库:
nmake -f ms
t.mak install
清除上次动态库的编译,以便重新编译:
nmake -f ms
tdll.mak clean
清除上次静态库的编译,以便重新编译:
nmake -f ms
t.mak clean
----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
注意:项目中使用OpenSSL的静态链接库则需要生成no-asm的静态链接库,否则可能一运行就崩溃
#pragma comment(lib, "libeay32.lib") #pragma comment(lib, "ssleay32.lib")
如果编译过程中还有其他的问题,多百度一下
其中n是最新的,是m的修复几个漏洞的版本具体可以查看CHANGES文件
Changes between 1.0.2m and 1.0.2n [7 Dec 2017] *) Read/write after SSL object in error state OpenSSL 1.0.2 (starting from version 1.0.2b) introduced an "error state" mechanism. The intent was that if a fatal error occurred during a handshake then OpenSSL would move into the error state and would immediately fail if you attempted to continue the handshake. This works as designed for the explicit handshake functions (SSL_do_handshake(), SSL_accept() and SSL_connect()), however due to a bug it does not work correctly if SSL_read() or SSL_write() is called directly. In that scenario, if the handshake fails then a fatal error will be returned in the initial function call. If SSL_read()/SSL_write() is subsequently called by the application for the same SSL object then it will succeed and the data is passed without being decrypted/encrypted directly from the SSL/TLS record layer. In order to exploit this issue an application bug would have to be present that resulted in a call to SSL_read()/SSL_write() being issued after having already received a fatal error. This issue was reported to OpenSSL by David Benjamin (Google). (CVE-2017-3737) [Matt Caswell] *) rsaz_1024_mul_avx2 overflow bug on x86_64 There is an overflow bug in the AVX2 Montgomery multiplication procedure used in exponentiation with 1024-bit moduli. No EC algorithms are affected. Analysis suggests that attacks against RSA and DSA as a result of this defect would be very difficult to perform and are not believed likely. Attacks against DH1024 are considered just feasible, because most of the work necessary to deduce information about a private key may be performed offline. The amount of resources required for such an attack would be significant. However, for an attack on TLS to be meaningful, the server would have to share the DH1024 private key among multiple clients, which is no longer an option since CVE-2016-0701. This only affects processors that support the AVX2 but not ADX extensions like Intel Haswell (4th generation). This issue was reported to OpenSSL by David Benjamin (Google). The issue was originally found via the OSS-Fuzz project. (CVE-2017-3738) [Andy Polyakov]