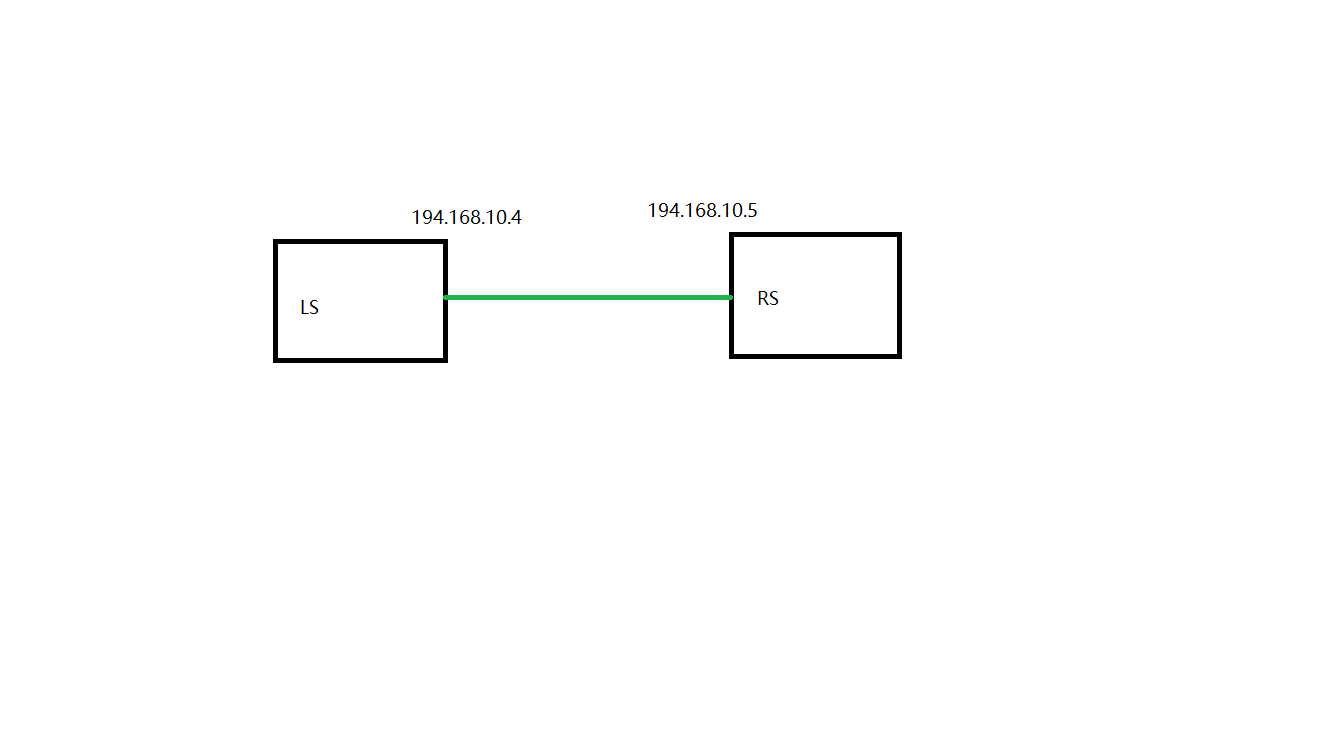
拓扑如下
基本的IP配置就不说了,直接写重点,在LS上配置
#配置SA ip xfrm state add src 194.168.10.4 dst 194.168.10.5 proto esp spi 0x00004005 mode tunnel auth md5 0xa87ff679a2f3e71d9181a67b7542122c enc des 0xa2f3e71d9181a67b ip xfrm state add src 194.168.10.5 dst 194.168.10.4 proto esp spi 0x00005004 mode tunnel auth md5 0xa87ff679a2f3e71d9181a67b7542122c enc des 0xa2f3e71d9181a67b #配置SP ip xfrm policy add src 194.168.10.4 dst 194.168.10.5 dir out tmpl src 194.168.10.4 dst 194.168.10.5 proto esp mode tunnel ip xfrm policy add src 194.168.10.5 dst 194.168.10.4 dir in tmpl src 194.168.10.5 dst 194.168.10.4 proto esp mode tunnel
在RS上配置
#配置SA ip xfrm state add src 194.168.10.4 dst 194.168.10.5 proto esp spi 0x00004005 mode tunnel auth md5 0xa87ff679a2f3e71d9181a67b7542122c enc des 0xa2f3e71 d9181a67b ip xfrm state add src 194.168.10.5 dst 194.168.10.4 proto esp spi 0x00005004 mode tunnel auth md5 0xa87ff679a2f3e71d9181a67b7542122c enc des 0xa2f3e71 d9181a67b #配置SP ip xfrm policy add src 194.168.10.4 dst 194.168.10.5 dir in tmpl src 194.168.10.4 dst 194.168.10.5 proto esp mode tunnel ip xfrm policy add src 194.168.10.5 dst 194.168.10.4 dir out tmpl src 194.168.10.5 dst 194.168.10.4 proto esp mode tunnel
这就可以了,从RS上ping LS,用tcpdump抓包结果如下
23:28:21.300088 IP 194.168.10.5 > 194.168.10.4: ESP(spi=0x00005004,seq=0x8), length 116 23:28:21.300354 IP 194.168.10.4 > 194.168.10.5: ESP(spi=0x00004005,seq=0x9), length 116 23:28:21.300354 IP 194.168.10.4 > 194.168.10.5: ICMP echo reply, id 4873, seq 1, length 64 23:28:22.301986 IP 194.168.10.5 > 194.168.10.4: ESP(spi=0x00005004,seq=0x9), length 116 23:28:22.302366 IP 194.168.10.4 > 194.168.10.5: ESP(spi=0x00004005,seq=0xa), length 116 23:28:22.302366 IP 194.168.10.4 > 194.168.10.5: ICMP echo reply, id 4873, seq 2, length 64 23:28:23.302824 IP 194.168.10.5 > 194.168.10.4: ESP(spi=0x00005004,seq=0xa), length 116 23:28:23.303139 IP 194.168.10.4 > 194.168.10.5: ESP(spi=0x00004005,seq=0xb), length 116 23:28:23.303139 IP 194.168.10.4 > 194.168.10.5: ICMP echo reply, id 4873, seq 3, length 64 23:28:24.304512 IP 194.168.10.5 > 194.168.10.4: ESP(spi=0x00005004,seq=0xb), length 116 23:28:24.305172 IP 194.168.10.4 > 194.168.10.5: ESP(spi=0x00004005,seq=0xc), length 116 23:28:24.305172 IP 194.168.10.4 > 194.168.10.5: ICMP echo reply, id 4873, seq 4, length 64
证明已经走ipsec加密了,这种用法太简陋了,有点徒手玩火的感觉,可以自己做实验玩,不要在实际环境中用,毕竟手工处理密钥不方便,而且隧道的运行情况也不太好监测。还是推荐用openswan。