一、简介
s_server是openssl提供的一个SSL服务程序。使用此程序前,需要生成各种证书。本命令可以用来测试ssl客户端,比如各种浏览器的https协议支持
二、语法
openssl s_server [-accept port] [-context id] [-verify depth] [-Verify depth] [-crl_check] [-crl_check_all] [-cert filename] [-certform DER|PEM] [-key filename] [-keyform DER|PEM] [-pass arg] [-dcert filename] [-dcertform DER|PEM ] [-dkey keyfile] [-dkeyform DER|PEM ] [-dpass arg] [-dhparam filename] [-name_curve arg][-nbio] [-nbio_test] [-crlf] [-debug] [-msg] [-state] [-CApath directory] [-CAfile filename] [-nocert] [-cipher cipherlist] [-quiet] [-no_tmp_rsa] [-ssl2] [-ssl3] [-tls1_1] [-tls1_2] [-tls1] [-dtls1] [-timeout] [-mtu] [-chain] [-no_ssl2][-no_ssl3] [-no_tls1] [-no_tls1_1] [-no_tls1_2] [-no_dhe] [-no_ecdhe][-bugs] [-hack] [-www] [-WWW] [-HTTP][-engine id] [-tlsextdebug] [-no_ticket] [-id_prefix arg] [-rand file(s)]
选项
-accept arg - port to accept on (default is 4433) -context arg - set session ID context -verify arg - turn on peer certificate verification -Verify arg - turn on peer certificate verification, must have a cert. -cert arg - certificate file to use (default is server.pem) -crl_check - check the peer certificate has not been revoked by its CA. The CRL(s) are appended to the certificate file -crl_check_all - check the peer certificate has not been revoked by its CA or any other CRL in the CA chain. CRL(s) are appened to the the certificate file. -certform arg - certificate format (PEM or DER) PEM default -key arg - Private Key file to use, in cert file if not specified (default is server.pem) -keyform arg - key format (PEM, DER or ENGINE) PEM default -pass arg - private key file pass phrase source -dcert arg - second certificate file to use (usually for DSA) -dcertform x - second certificate format (PEM or DER) PEM default -dkey arg - second private key file to use (usually for DSA) -dkeyform arg - second key format (PEM, DER or ENGINE) PEM default -dpass arg - second private key file pass phrase source -dhparam arg - DH parameter file to use, in cert file if not specified or a default set of parameters is used -named_curve arg - Elliptic curve name to use for ephemeral ECDH keys. Use "openssl ecparam -list_curves" for all names (default is nistp256). -nbio - Run with non-blocking IO -nbio_test - test with the non-blocking test bio -crlf - convert LF from terminal into CRLF -debug - Print more output -msg - Show protocol messages -state - Print the SSL states -CApath arg - PEM format directory of CA's -CAfile arg - PEM format file of CA's -trusted_first - Use trusted CA's first when building the trust chain -nocert - Don't use any certificates (Anon-DH) -cipher arg - play with 'openssl ciphers' to see what goes here -serverpref - Use server's cipher preferences -quiet - No server output -no_tmp_rsa - Do not generate a tmp RSA key -psk_hint arg - PSK identity hint to use -psk arg - PSK in hex (without 0x) -ssl2 - Just talk SSLv2 -ssl3 - Just talk SSLv3 -tls1_2 - Just talk TLSv1.2 -tls1_1 - Just talk TLSv1.1 -tls1 - Just talk TLSv1 -dtls1 - Just talk DTLSv1 -timeout - Enable timeouts -mtu - Set link layer MTU -chain - Read a certificate chain -no_ssl2 - Just disable SSLv2 -no_ssl3 - Just disable SSLv3 -no_tls1 - Just disable TLSv1 -no_tls1_1 - Just disable TLSv1.1 -no_tls1_2 - Just disable TLSv1.2 -no_dhe - Disable ephemeral DH -no_ecdhe - Disable ephemeral ECDH -bugs - Turn on SSL bug compatibility -www - Respond to a 'GET /' with a status page -WWW - Respond to a 'GET /<path> HTTP/1.0' with file ./<path> -HTTP - Respond to a 'GET /<path> HTTP/1.0' with file ./<path> with the assumption it contains a complete HTTP response. -engine id - Initialise and use the specified engine -id_prefix arg - Generate SSL/TLS session IDs prefixed by 'arg' -rand file:file:... -servername host - servername for HostName TLS extension -servername_fatal - on mismatch send fatal alert (default warning alert) -cert2 arg - certificate file to use for servername (default is server2.pem) -key2 arg - Private Key file to use for servername, in cert file if not specified (default is server2.pem) -tlsextdebug - hex dump of all TLS extensions received -no_ticket - disable use of RFC4507bis session tickets -legacy_renegotiation - enable use of legacy renegotiation (dangerous) -nextprotoneg arg - set the advertised protocols for the NPN extension (comma-separated list) -use_srtp profiles - Offer SRTP key management with a colon-separated profile list -keymatexport label - Export keying material using label -keymatexportlen len - Export len bytes of keying material (default 20)
三、实例
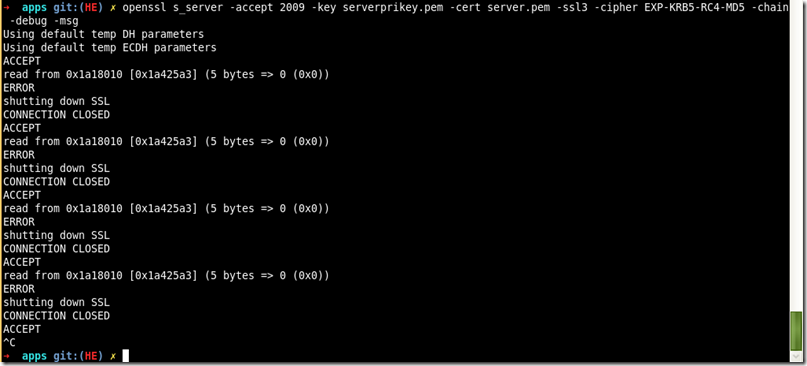
1、启动s_server服务(站点证书及私钥,证书链,协议版本,算法组合)
openssl s_server -accept 2009 -key serverprikey.pem -cert server.pem -ssl3 -cipher EXP-KRB5-RC4-MD5 -chain -debug -msg