AES的C语言实现入门版
AES分组密码算法中明文分组位128bits,密钥分组可以为128,192,256bits。AES也是由最基本的变换单位——“轮”多次迭代而成的。我们将 AES 中的轮变换计为 Round(State, RoundKey),State 表示消息矩阵;RoundKey 表示轮密钥矩阵。一轮的完成将改变 State 矩阵中的元素,称为改变它的状态。对于加密来说,输入到第一轮中的 State 就是明文消息矩阵,最后一轮输出的 State 就是对应的密文消息矩阵。
AES 的轮(除最后一轮外)变换有四个不同的变换组成,这些变化我们称之为内部轮函数, AES 的轮可表示成如下形式:
Round(State, RoundKey){
SubBytes(State);
ShiftRows(State):
MixColumns(State);
AddRoundKey(State,RoundKey);
}
其中:ByteSub(State)称为字节代替变换、ShiftRow(State)称为行移位变、MixColumn(State)为列混合变换以及 AddRoundKey (State, RoundKey )为与子密钥与。最后一轮略微的不同,将其记作 FinalRoundKey(State, RoundKey),相当于前面的Round(State, RoundKey)去掉 MixColumns(State)。
加密过程:

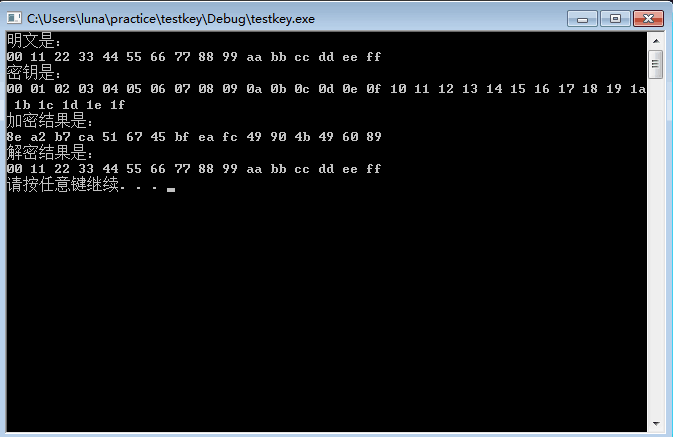
加密过程的伪代码:
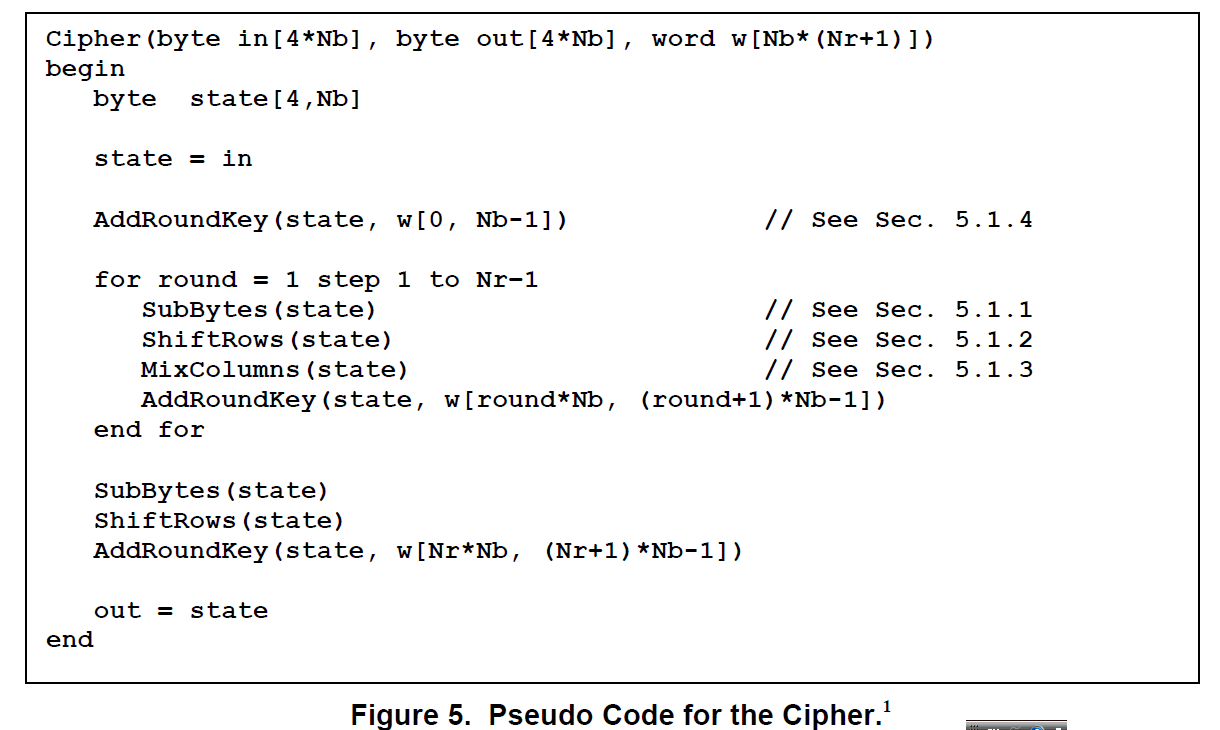
解密过程的伪代码:
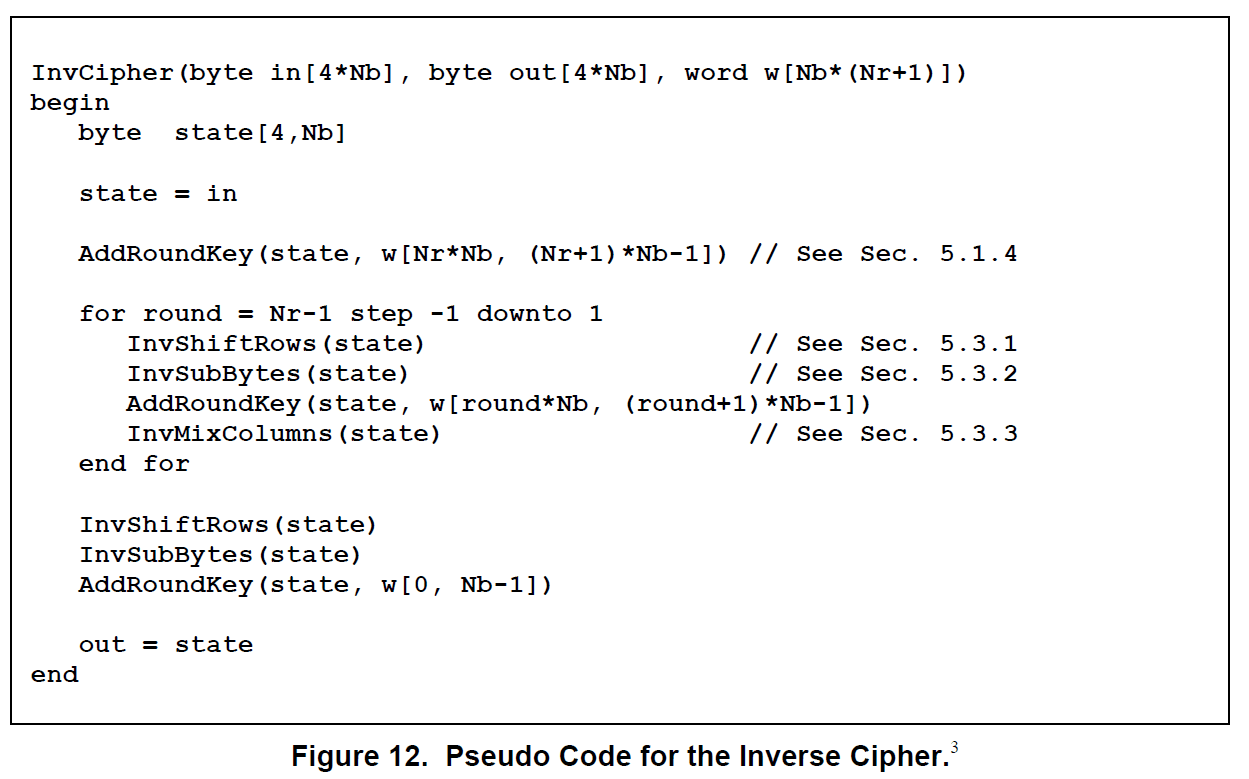
其中密钥长度不同,轮数不同,密钥编排扩展过程有所不同:
下面是完整代码:
#include "aes.h" const unsigned char sBox[16][16] = { 0x63, 0x7c, 0x77, 0x7b, 0xf2, 0x6b, 0x6f, 0xc5, 0x30, 0x01, 0x67, 0x2b, 0xfe, 0xd7, 0xab, 0x76, 0xca, 0x82, 0xc9, 0x7d, 0xfa, 0x59, 0x47, 0xf0, 0xad, 0xd4, 0xa2, 0xaf, 0x9c, 0xa4, 0x72, 0xc0, 0xb7, 0xfd, 0x93, 0x26, 0x36, 0x3f, 0xf7, 0xcc, 0x34, 0xa5, 0xe5, 0xf1, 0x71, 0xd8, 0x31, 0x15, 0x04, 0xc7, 0x23, 0xc3, 0x18, 0x96, 0x05, 0x9a, 0x07, 0x12, 0x80, 0xe2, 0xeb, 0x27, 0xb2, 0x75, 0x09, 0x83, 0x2c, 0x1a, 0x1b, 0x6e, 0x5a, 0xa0, 0x52, 0x3b, 0xd6, 0xb3, 0x29, 0xe3, 0x2f, 0x84, 0x53, 0xd1, 0x00, 0xed, 0x20, 0xfc, 0xb1, 0x5b, 0x6a, 0xcb, 0xbe, 0x39, 0x4a, 0x4c, 0x58, 0xcf, 0xd0, 0xef, 0xaa, 0xfb, 0x43, 0x4d, 0x33, 0x85, 0x45, 0xf9, 0x02, 0x7f, 0x50, 0x3c, 0x9f, 0xa8, 0x51, 0xa3, 0x40, 0x8f, 0x92, 0x9d, 0x38, 0xf5, 0xbc, 0xb6, 0xda, 0x21, 0x10, 0xff, 0xf3, 0xd2, 0xcd, 0x0c, 0x13, 0xec, 0x5f, 0x97, 0x44, 0x17, 0xc4, 0xa7, 0x7e, 0x3d, 0x64, 0x5d, 0x19, 0x73, 0x60, 0x81, 0x4f, 0xdc, 0x22, 0x2a, 0x90, 0x88, 0x46, 0xee, 0xb8, 0x14, 0xde, 0x5e, 0x0b, 0xdb, 0xe0, 0x32, 0x3a, 0x0a, 0x49, 0x06, 0x24, 0x5c, 0xc2, 0xd3, 0xac, 0x62, 0x91, 0x95, 0xe4, 0x79, 0xe7, 0xc8, 0x37, 0x6d, 0x8d, 0xd5, 0x4e, 0xa9, 0x6c, 0x56, 0xf4, 0xea, 0x65, 0x7a, 0xae, 0x08, 0xba, 0x78, 0x25, 0x2e, 0x1c, 0xa6, 0xb4, 0xc6, 0xe8, 0xdd, 0x74, 0x1f, 0x4b, 0xbd, 0x8b, 0x8a, 0x70, 0x3e, 0xb5, 0x66, 0x48, 0x03, 0xf6, 0x0e, 0x61, 0x35, 0x57, 0xb9, 0x86, 0xc1, 0x1d, 0x9e, 0xe1, 0xf8, 0x98, 0x11, 0x69, 0xd9, 0x8e, 0x94, 0x9b, 0x1e, 0x87, 0xe9, 0xce, 0x55, 0x28, 0xdf, 0x8c, 0xa1, 0x89, 0x0d, 0xbf, 0xe6, 0x42, 0x68, 0x41, 0x99, 0x2d, 0x0f, 0xb0, 0x54, 0xbb, 0x16 }; const unsigned char inv_sBox[16][16] = { 0x52, 0x09, 0x6a, 0xd5, 0x30, 0x36, 0xa5, 0x38, 0xbf, 0x40, 0xa3, 0x9e, 0x81, 0xf3, 0xd7, 0xfb, 0x7c, 0xe3, 0x39, 0x82, 0x9b, 0x2f, 0xff, 0x87, 0x34, 0x8e, 0x43, 0x44, 0xc4, 0xde, 0xe9, 0xcb, 0x54, 0x7b, 0x94, 0x32, 0xa6, 0xc2, 0x23, 0x3d, 0xee, 0x4c, 0x95, 0x0b, 0x42, 0xfa, 0xc3, 0x4e, 0x08, 0x2e, 0xa1, 0x66, 0x28, 0xd9, 0x24, 0xb2, 0x76, 0x5b, 0xa2, 0x49, 0x6d, 0x8b, 0xd1, 0x25, 0x72, 0xf8, 0xf6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xd4, 0xa4, 0x5c, 0xcc, 0x5d, 0x65, 0xb6, 0x92, 0x6c, 0x70, 0x48, 0x50, 0xfd, 0xed, 0xb9, 0xda, 0x5e, 0x15, 0x46, 0x57, 0xa7, 0x8d, 0x9d, 0x84, 0x90, 0xd8, 0xab, 0x00, 0x8c, 0xbc, 0xd3, 0x0a, 0xf7, 0xe4, 0x58, 0x05, 0xb8, 0xb3, 0x45, 0x06, 0xd0, 0x2c, 0x1e, 0x8f, 0xca, 0x3f, 0x0f, 0x02, 0xc1, 0xaf, 0xbd, 0x03, 0x01, 0x13, 0x8a, 0x6b, 0x3a, 0x91, 0x11, 0x41, 0x4f, 0x67, 0xdc, 0xea, 0x97, 0xf2, 0xcf, 0xce, 0xf0, 0xb4, 0xe6, 0x73, 0x96, 0xac, 0x74, 0x22, 0xe7, 0xad, 0x35, 0x85, 0xe2, 0xf9, 0x37, 0xe8, 0x1c, 0x75, 0xdf, 0x6e, 0x47, 0xf1, 0x1a, 0x71, 0x1d, 0x29, 0xc5, 0x89, 0x6f, 0xb7, 0x62, 0x0e, 0xaa, 0x18, 0xbe, 0x1b, 0xfc, 0x56, 0x3e, 0x4b, 0xc6, 0xd2, 0x79, 0x20, 0x9a, 0xdb, 0xc0, 0xfe, 0x78, 0xcd, 0x5a, 0xf4, 0x1f, 0xdd, 0xa8, 0x33, 0x88, 0x07, 0xc7, 0x31, 0xb1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xec, 0x5f, 0x60, 0x51, 0x7f, 0xa9, 0x19, 0xb5, 0x4a, 0x0d, 0x2d, 0xe5, 0x7a, 0x9f, 0x93, 0xc9, 0x9c, 0xef, 0xa0, 0xe0, 0x3b, 0x4d, 0xae, 0x2a, 0xf5, 0xb0, 0xc8, 0xeb, 0xbb, 0x3c, 0x83, 0x53, 0x99, 0x61, 0x17, 0x2b, 0x04, 0x7e, 0xba, 0x77, 0xd6, 0x26, 0xe1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0c, 0x7d }; const unsigned char Rcon[16] = { 0x00, 0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1b, 0x36, 0xd8, 0xab, 0x4d, 0x9a, 0x2f };//轮常量表 void SubBytes(unsigned char* in, const unsigned char table[16][16]){//字节替换 for (int i = 0; i < 16; i++) in[i] = table[in[i] >> 4][in[i] & 0x0F]; } void ShiftRows(unsigned char* in){//进行行移位 unsigned char buffer[4] = { 0 }; for (int i = 1; i < 4; i++){ for (int j = 0; j < 4; j++) buffer[j] = in[((i + j) * 4 + i) % 16]; for (int j = 0; j < 4; j++) in[4 * j + i] = buffer[j]; } } void InvShiftRows(unsigned char* in){ unsigned char buffer[4] = { 0 }; for (int i = 1; i < 4; i++){ for (int j = 0; j < 4; j++) buffer[j] = in[(4 * (4 - i + j) + i) % 16]; for (int j = 0; j < 4; j++) in[4 * j + i] = buffer[j]; } } unsigned char x2time(unsigned char a){//有限域*2乘法 The x2time() function unsigned char res = (a << 1) ^ ((a & 0x80) ? 0x1b : 0x00); return res; } unsigned char x3time(unsigned char a){//3:0011 return (x2time(a) ^ a); } unsigned char x4time(unsigned char a){//4:0100 return (x2time(x2time(a))); } unsigned char x8time(unsigned char a){//8:1000 return (x2time(x2time(x2time(a)))); } unsigned char x9time(unsigned char a){//9:1001 return (x8time(a) ^ a); } unsigned char xBtime(unsigned char a){//B:1011 return (x8time(a) ^ x3time(a)); } unsigned char xDtime(unsigned char a){//D:1101 return (x8time(a) ^ x4time(a) ^ a); } unsigned char xEtime(unsigned char a){//E:1110 return (x8time(a) ^ x4time(a) ^ x2time(a)); } void MixColumn(unsigned char* in){//进行列混合 unsigned char tmp[4] = { 0 }; for (int i = 0; i < 4; i++, in += 4){ tmp[0] = x2time(in[0]) ^ x3time(in[1]) ^ in[2] ^ in[3]; tmp[1] = in[0] ^ x2time(in[1]) ^ x3time(in[2]) ^ in[3]; tmp[2] = in[0] ^ in[1] ^ x2time(in[2]) ^ x3time(in[3]); tmp[3] = x3time(in[0]) ^ in[1] ^ in[2] ^ x2time(in[3]); memcpy(in, tmp, 4); } } void InvMixColumn(unsigned char* in){//逆向列混合 unsigned char tmp[4] = { 0 }; for (int i = 0; i < 4; i++, in += 4){ tmp[0] = xEtime(in[0]) ^ xBtime(in[1]) ^ xDtime(in[2]) ^ x9time(in[3]); tmp[1] = x9time(in[0]) ^ xEtime(in[1]) ^ xBtime(in[2]) ^ xDtime(in[3]); tmp[2] = xDtime(in[0]) ^ x9time(in[1]) ^ xEtime(in[2]) ^ xBtime(in[3]); tmp[3] = xBtime(in[0]) ^ xDtime(in[1]) ^ x9time(in[2]) ^ xEtime(in[3]); memcpy(in, tmp, 4); } } void AddRoundKey(unsigned char* in, const unsigned char* key){ for (int i = 0; i < 16; i++) in[i] ^= key[i]; } void rotWord(unsigned char* in){//将一个字进行左移循环一个单位 unsigned char tmp = in[0]; memcpy(in, in + 1, 3); in[3] = tmp; } void subWord(unsigned char* in){//每一个字进行字节替换 for (int i = 0; i < 4; i++) in[i] = sBox[in[i] >> 4][in[i] & 0x0F]; } static unsigned char roundKey[240] = { 0 };//最多是256bits,进行14轮迭代,roundKey中有15组,每一组16byte,最多是240bytes void SetKey(const unsigned char* key, const int Nk){ int Nr = Nk + 6; memcpy(roundKey, key, 4 * Nk);//将最初的key拷贝到roundKey数组的最开始,每一个乘上4因为按字来计算,1字=4byte for (int i = Nk; i < (Nr + 1) * 4; i++){ unsigned char buffer[4] = { 0 }; memcpy(buffer, roundKey + (i - 1) * 4, 4); if (i%Nk == 0){ rotWord(buffer); subWord(buffer); buffer[0] ^= Rcon[i / Nk]; } if ((i%Nk == 4) && Nk>6) subWord(buffer); for (int j = 0; j < 4; j++) roundKey[4 * i + j] = buffer[j] ^ roundKey[(i - Nk) * 4 + j]; } } void encryptAES(unsigned char* out, const unsigned char* in, const unsigned char* key, const int keyLen){ int Nk = keyLen >> 2; int Nr = Nk + 6; SetKey(key, Nk); memcpy(out, in, 16); AddRoundKey(out, roundKey); for (int i = 1; i <= Nr; i++){//进行Nr轮变换,最后一个Nr轮不进行列混合 SubBytes(out, sBox); ShiftRows(out); if (i != Nr) MixColumn(out); AddRoundKey(out, roundKey + 16 * i); } } void decryptAES(unsigned char* out, const unsigned char* in, const unsigned char* key, const int keyLen){ int Nk = keyLen >> 2; int Nr = Nk + 6; SetKey(key, Nk); memcpy(out, in, 16); AddRoundKey(out, roundKey + Nr * 16); for (int i = Nr - 1; i >= 0; i--){ InvShiftRows(out); SubBytes(out, inv_sBox); AddRoundKey(out, roundKey + 16 * i); if (i != 0) InvMixColumn(out); } }
aes.h头文件:
#pragma once #include <stdio.h> #include <stdlib.h> #include <stdint.h> #include <string.h> #ifdef __cplusplus extern "C"{ #endif void encryptAES(unsigned char* out, const unsigned char* in, const unsigned char* key, const int keyLen); void decryptAES(unsigned char* out, const unsigned char* in, const unsigned char* key, const int keyLen); #ifdef __cplusplus } #endif
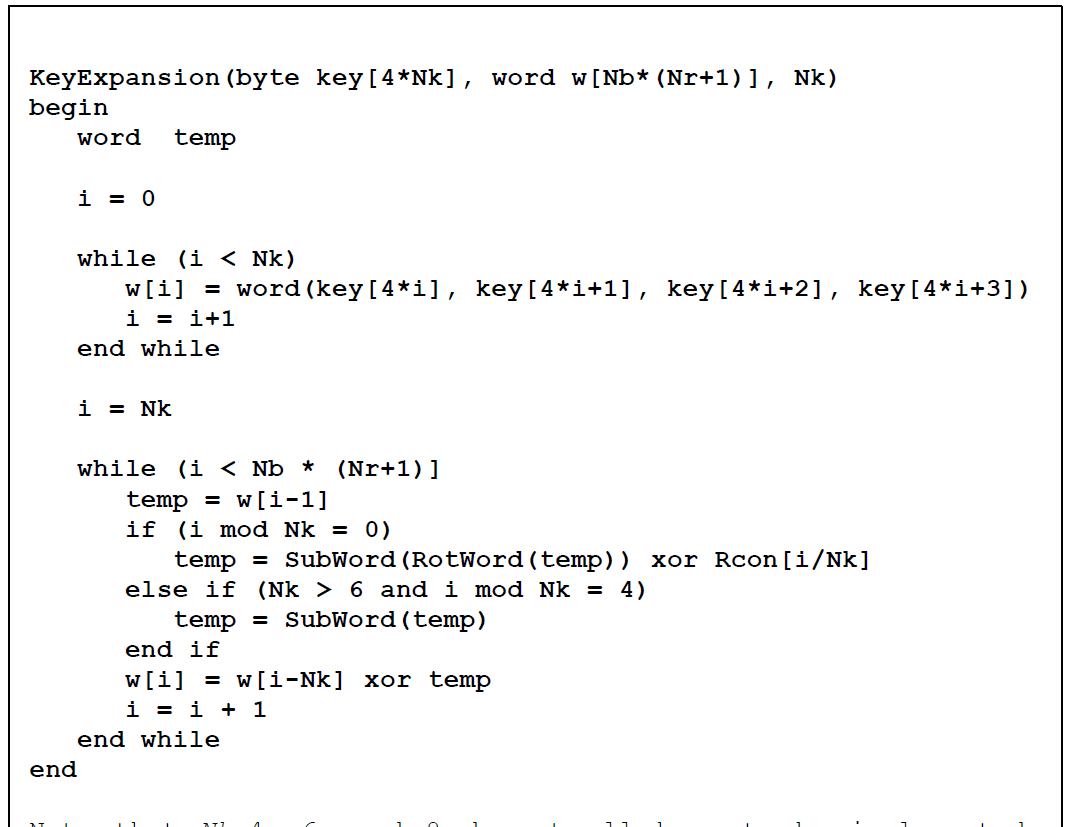
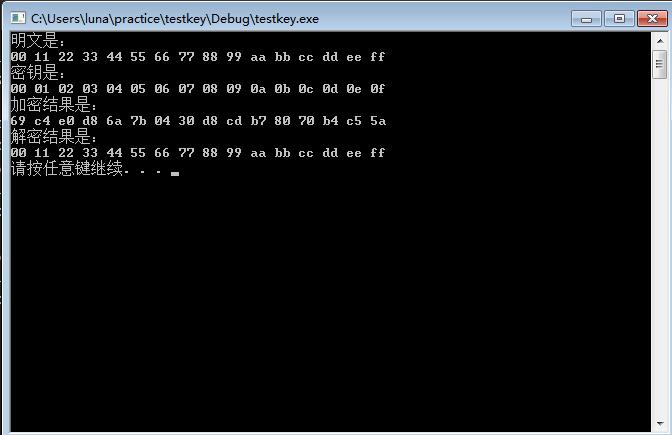
运行结果:
密钥是128Bits时:
密钥是192bits时:

密钥是256bits时: